| File name: | 119cafc86fcec7d56685aa283cef488f45d5781c476bb12b3d1893307a4db5d6.apk |
| Full analysis: | https://app.any.run/tasks/73ae8251-2a54-4277-b98a-2b6911a18b70 |
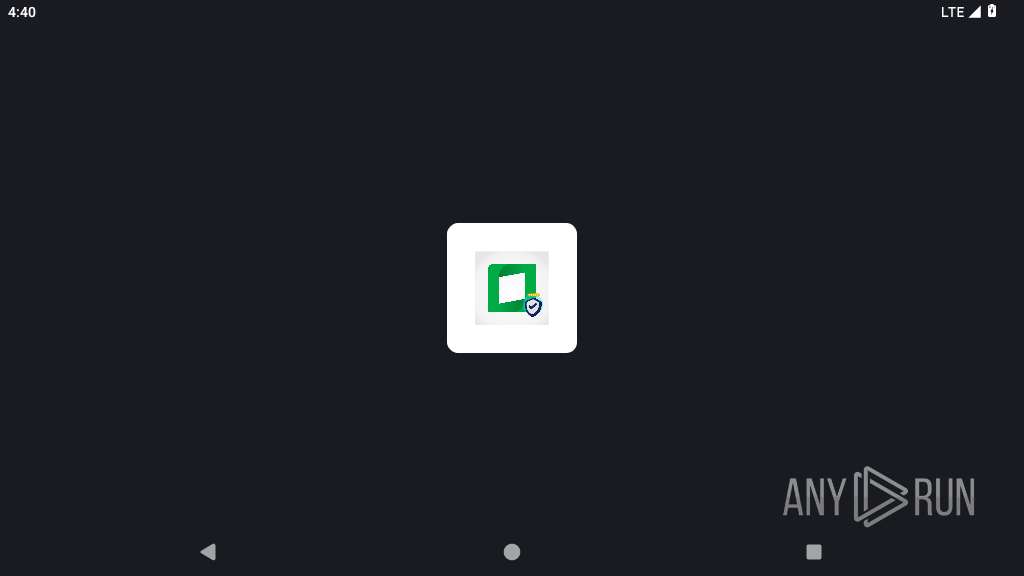
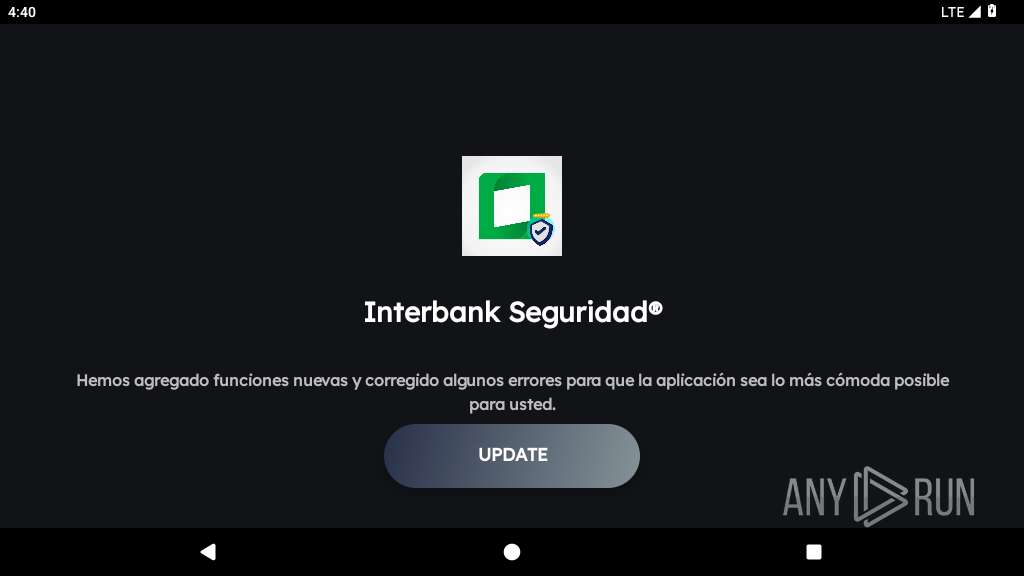
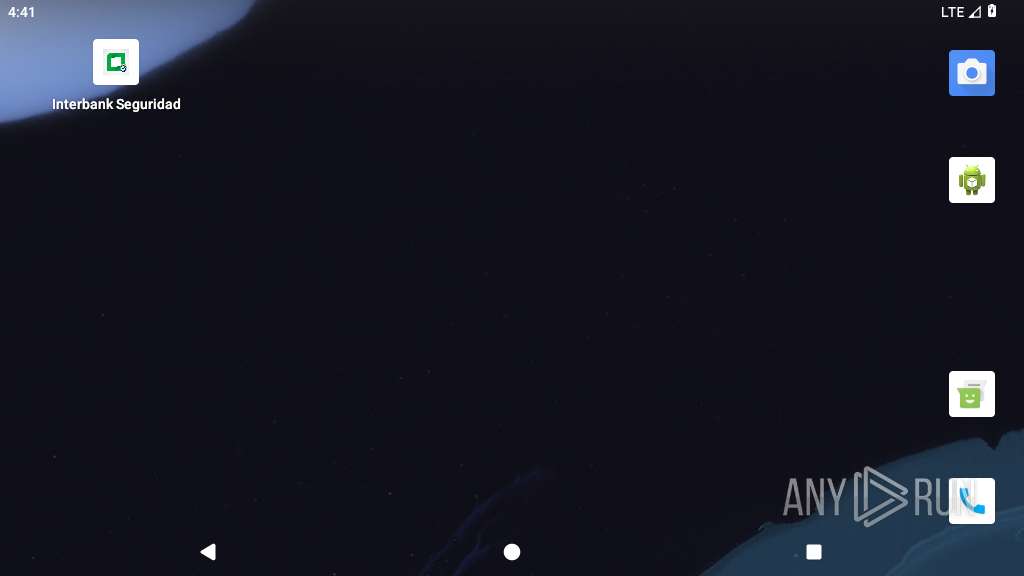
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2025, 16:39:36 |
| OS: | Android 14 |
| Indicators: | |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with AndroidManifest.xml |
| MD5: | FBF090A4AFACCEC57FB82C75277CE2AA |
| SHA1: | 8642FB93B62FA7BFFBC90B0297A63830383F0B0E |
| SHA256: | 119CAFC86FCEC7D56685AA283CEF488F45D5781C476BB12B3D1893307A4DB5D6 |
| SSDEEP: | 98304:114xZ48uMg9YVMTRKHC4SSZPrlNm0yefQOSybaW8TY+hcM3Af9pX32eaa4J5ekRv:ELWS7f8IpywzuvH |
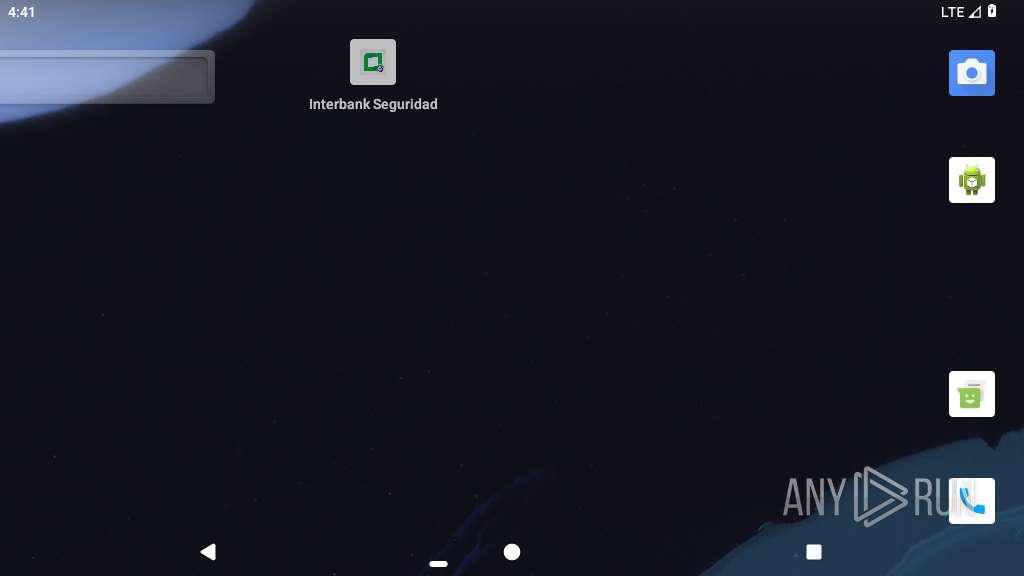
MALICIOUS
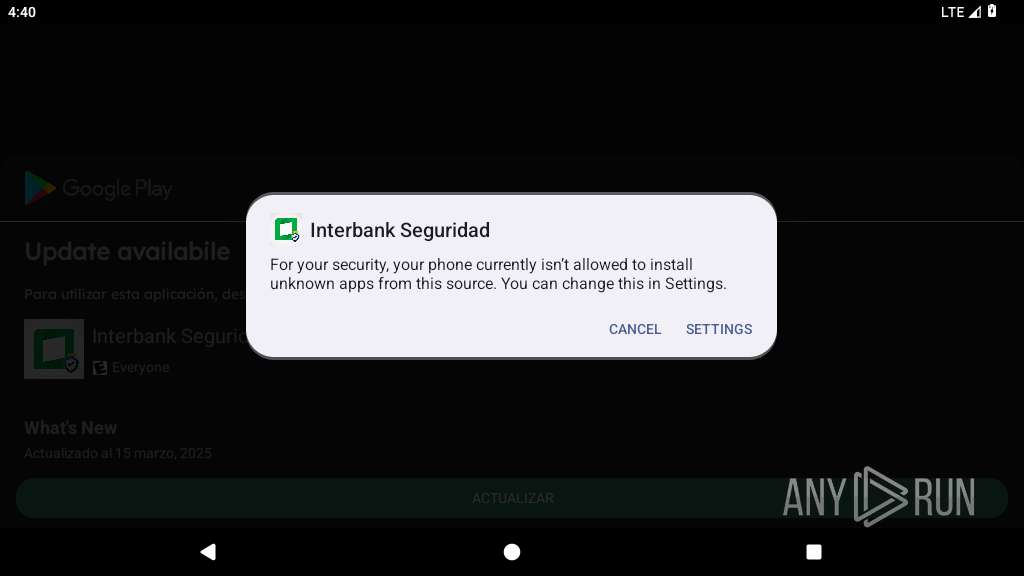
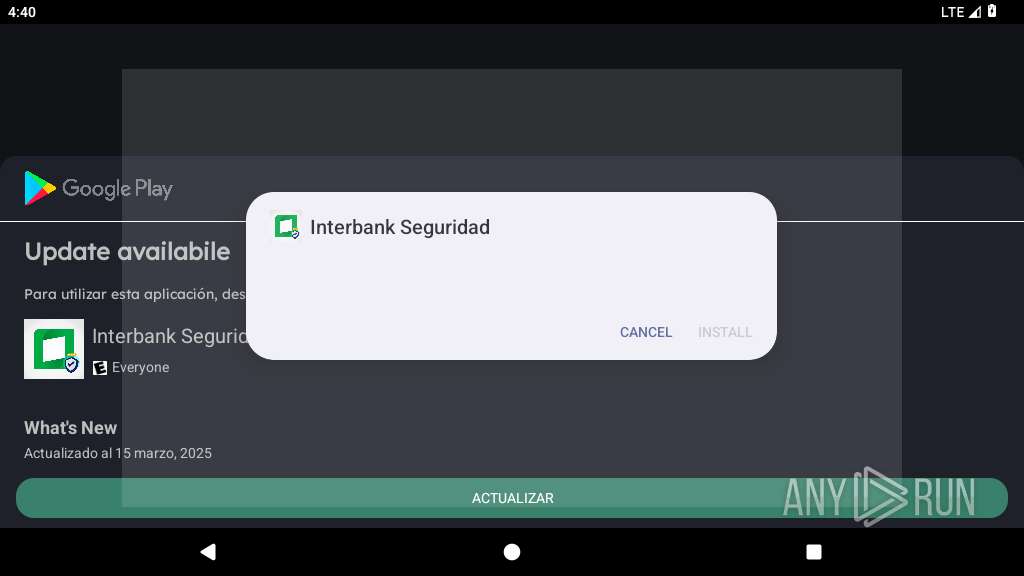
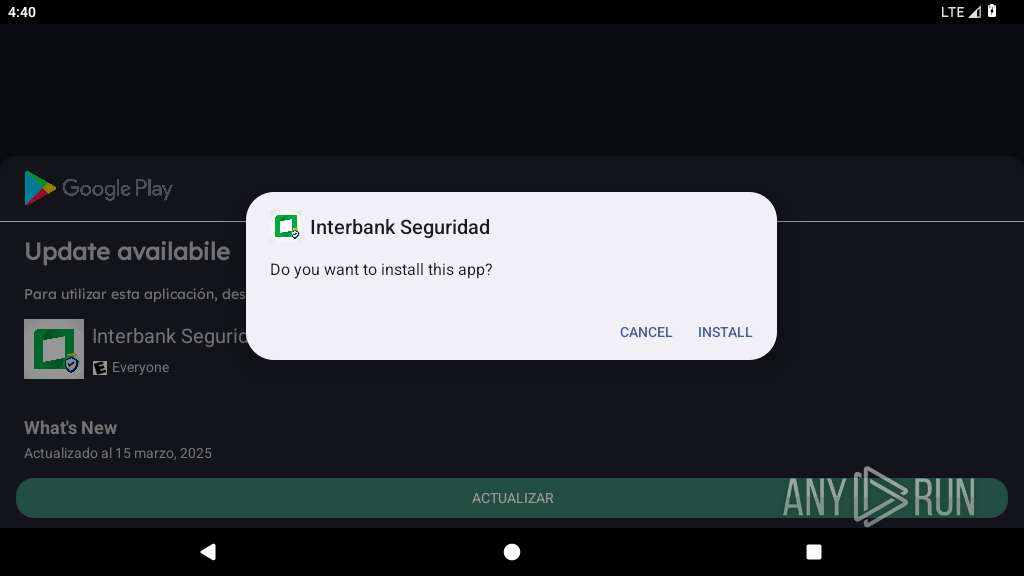
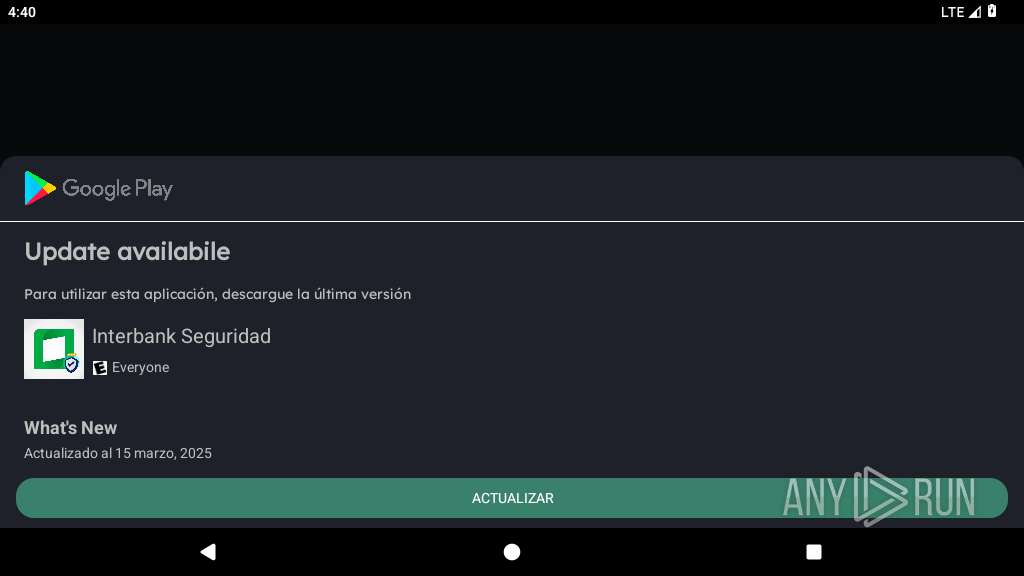
Initiates background APK installation
- app_process64 (PID: 2249)
Uses APIs to record audio and video from various sources
- app_process64 (PID: 2393)
SUSPICIOUS
Accesses external device storage files
- app_process64 (PID: 2249)
- app_process64 (PID: 2393)
Abuses foreground service for persistence
- app_process64 (PID: 2393)
Starts a service
- app_process64 (PID: 2393)
Retrieves a list of running services
- app_process64 (PID: 2393)
Launches a new activity
- app_process64 (PID: 2393)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2393)
Detects when screen powers off
- app_process64 (PID: 2393)
Acquires a wake lock to keep the device awake
- app_process64 (PID: 2393)
Creates a WakeLock to manage power state
- app_process64 (PID: 2393)
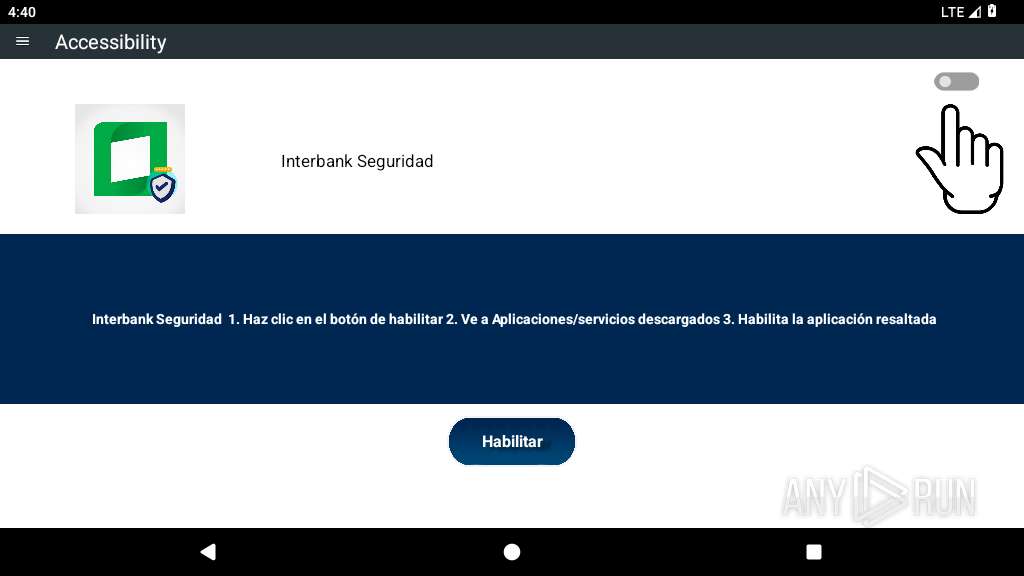
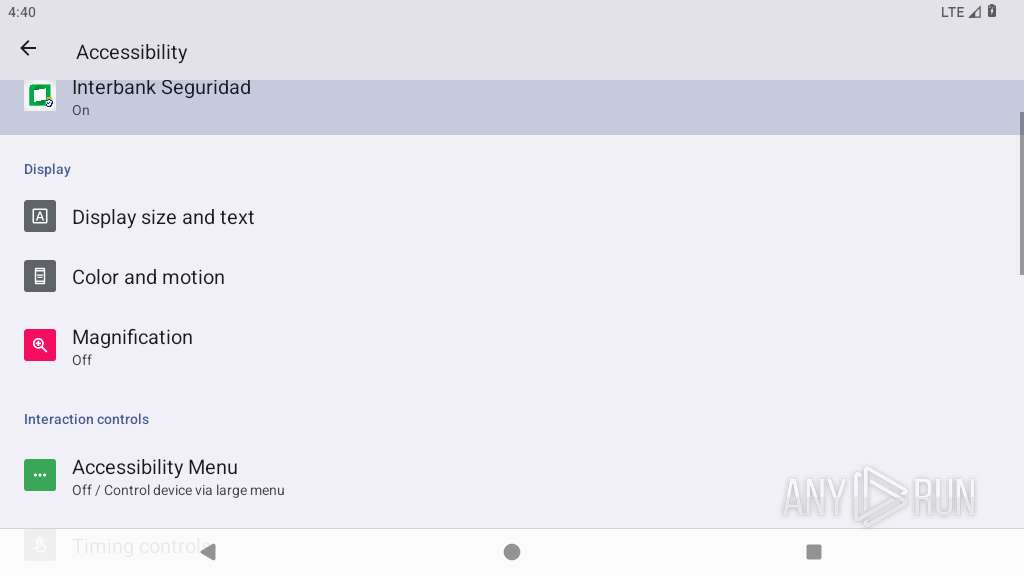
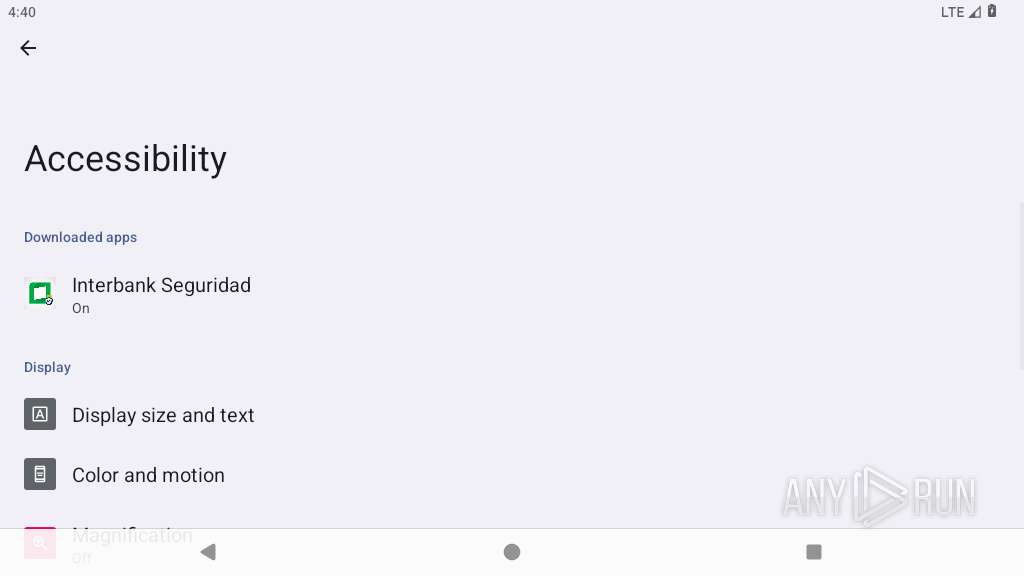
Intercepts events for accessibility services
- app_process64 (PID: 2393)
Performs UI accessibility actions without user input
- app_process64 (PID: 2393)
Leverages accessibility to control apps
- app_process64 (PID: 2393)
Checks exemption from battery optimization
- app_process64 (PID: 2393)
Checks if the device's lock screen is showing
- app_process64 (PID: 2393)
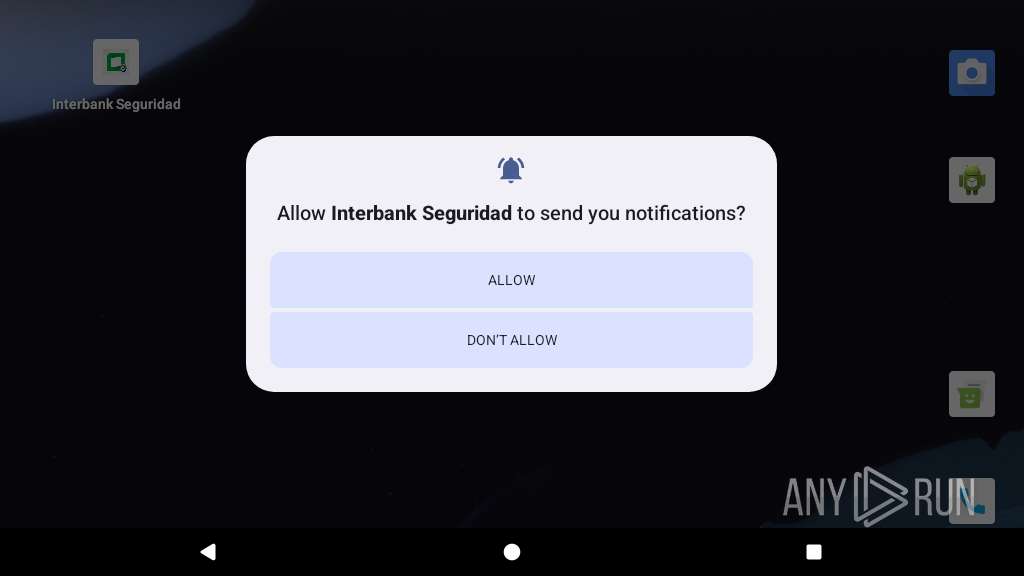
Triggers notification to user
- app_process64 (PID: 2393)
Requests access to accessibility settings
- app_process64 (PID: 2393)
Overlays content on other applications
- app_process64 (PID: 2393)
Updates the value of a system setting
- app_process64 (PID: 2393)
Prevents its uninstallation by user
- app_process64 (PID: 2393)
Connects to unusual port
- app_process64 (PID: 2393)
INFO
Dynamically registers broadcast event listeners
- app_process64 (PID: 2249)
- app_process64 (PID: 2393)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2393)
Creates and writes local files
- app_process64 (PID: 2393)
Verifies whether the device is connected to the internet
- app_process64 (PID: 2393)
Retrieves the value of a secure system setting
- app_process64 (PID: 2393)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | Unknown (22682) |
| ZipModifyDate: | 2025:03:31 14:02:14 |
| ZipCRC: | 0x05d0d574 |
| ZipCompressedSize: | 5653 |
| ZipUncompressedSize: | 16152 |
| ZipFileName: | AndroidManifest.xml |
Total processes
133
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 343 | /system/bin/netd | /system/bin/netd | init | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2249 | com.system.myaplication | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2382 | /apex/com.android.art/bin/artd | /apex/com.android.art/bin/artd | — | init |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2385 | /apex/com.android.art/bin/dex2oat32 --zip-fd=6 --zip-location=/data/app/~~oqtIPCKVfIorxXF3aBc00A==/com.gibson.holdings-UvGdbBx0S-0AtAbs1LH4Tg==/base.apk --oat-fd=7 --oat-location=/data/app/~~oqtIPCKVfIorxXF3aBc00A==/com.gibson.holdings-UvGdbBx0S-0AtAbs1LH4Tg==/oat/arm64/base.odex --output-vdex-fd=8 --swap-fd=9 --class-loader-context-fds=10 --class-loader-context=PCL[]{PCL[/system/framework/android.test.base.jar]} --classpath-dir=/data/app/~~oqtIPCKVfIorxXF3aBc00A==/com.gibson.holdings-UvGdbBx0S-0AtAbs1LH4Tg== --instruction-set=arm64 --instruction-set-features=default --instruction-set-variant=cortex-a53 --compiler-filter=verify --compilation-reason=install --compact-dex-level=none --max-image-block-size=524288 --resolve-startup-const-strings=true --generate-mini-debug-info --runtime-arg -Xtarget-sdk-version:29 --runtime-arg -Xhidden-api-policy:enabled --runtime-arg -Xms64m --runtime-arg -Xmx512m --comments=app-version-name:35.73.6.38,app-version-code:3573638,art-version:340090000 | /apex/com.android.art/bin/dex2oat32 | — | artd |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2393 | com.gibson.holdings | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2445 | com.android.systemui.accessibility.accessibilitymenu | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2756 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2770 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2805 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
442
Text files
873
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2393 | app_process64 | /data/user/0/com.gibson.holdings/shared_prefs/com.gibson.holdings.xml | xml | |
MD5:— | SHA256:— | |||
| 2393 | app_process64 | /storage/emulated/0/Config/sys/apps/log/log-2025-04-01.txt | text | |
MD5:— | SHA256:— | |||
| 2393 | app_process64 | /data/user/0/com.gibson.holdings/shared_prefs/com.gibson.holdings_preferences.xml | xml | |
MD5:— | SHA256:— | |||
| 2393 | app_process64 | /data/user/0/com.gibson.holdings/shared_prefs/WebViewChromiumPrefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2393 | app_process64 | /data/user/0/com.gibson.holdings/app_webview/Default/Local Storage/leveldb/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 2393 | app_process64 | /data/user/0/com.gibson.holdings/app_webview/Default/Local Storage/leveldb/CURRENT | text | |
MD5:— | SHA256:— | |||
| 2393 | app_process64 | /data/user/0/com.gibson.holdings/app_webview/Default/Local Storage/leveldb/000001.dbtmp | text | |
MD5:— | SHA256:— | |||
| 2393 | app_process64 | /data/user/0/com.gibson.holdings/cache/WebView/Default/HTTP Cache/Code Cache/webui_js/index | binary | |
MD5:— | SHA256:— | |||
| 2393 | app_process64 | /data/user/0/com.gibson.holdings/cache/WebView/Default/HTTP Cache/Code Cache/wasm/index | binary | |
MD5:— | SHA256:— | |||
| 2393 | app_process64 | /data/user/0/com.gibson.holdings/cache/WebView/Default/HTTP Cache/Code Cache/wasm/index-dir/temp-index | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
177
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 142.250.179.195:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
447 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 8.8.8.8:443 | — | — | — | malicious |
— | — | 216.239.35.4:123 | time.android.com | — | — | whitelisted |
— | — | 8.8.8.8:853 | — | GOOGLE | US | malicious |
— | — | 142.250.179.196:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.179.195:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 142.250.27.81:443 | — | GOOGLE | US | unknown |
575 | app_process64 | 216.239.35.8:123 | time.android.com | — | — | whitelisted |
575 | app_process64 | 216.239.35.12:123 | time.android.com | — | — | whitelisted |
575 | app_process64 | 216.239.35.0:123 | time.android.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivitycheck.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
2Ab1V9-dnsotls-ds.metric.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |