| File name: | LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe |
| Full analysis: | https://app.any.run/tasks/3312a5b3-ce06-4e21-aaa5-889ec107cf78 |
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2025, 14:00:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 708347E5DC9A73F21B6D3940B5474522 |
| SHA1: | D3934E09F73C905C9B6E8AD333B8035BE5151E85 |
| SHA256: | 1196AF815FD4A57D61F2013E52635EA9E92F18A183D1F90DD5F280CB6378081F |
| SSDEEP: | 98304:LWKHpwDoX7mC+1l/57ukGv43my5tL6mbJHa61erzMfHCjhnOMmYWZHRi1OjtbJhu:C |
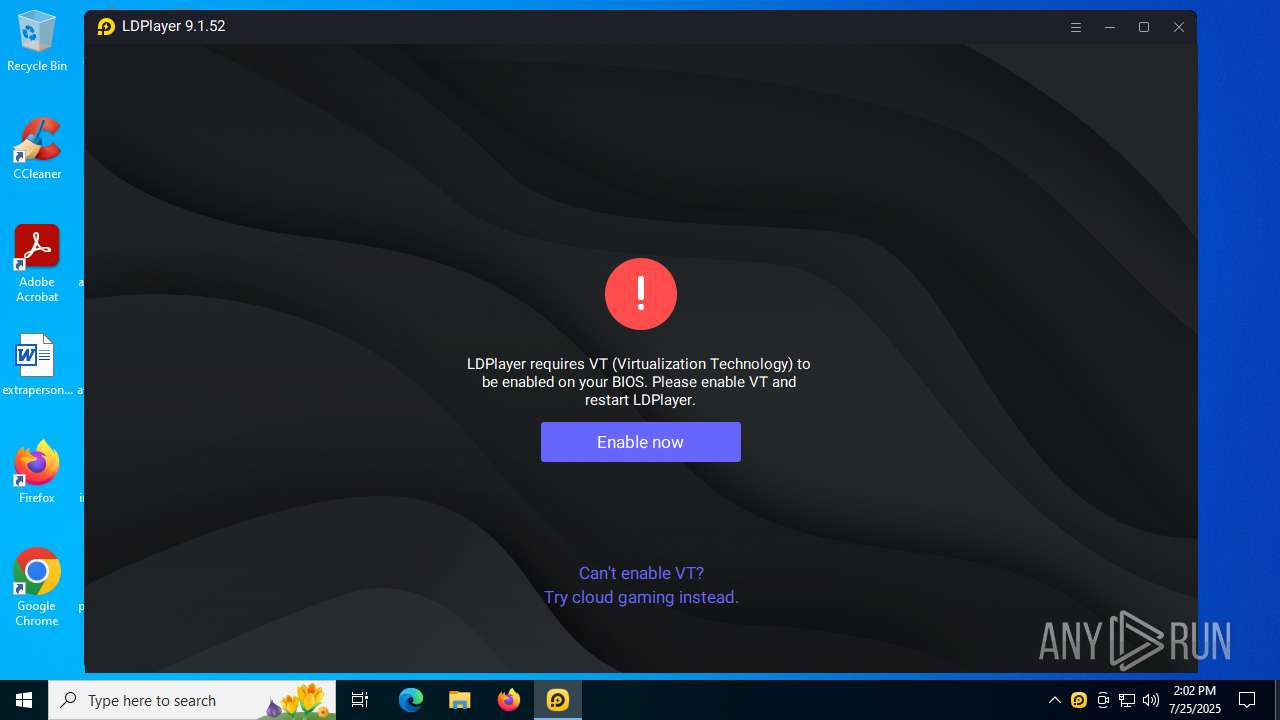
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- dnrepairer.exe (PID: 4512)
Starts NET.EXE for service management
- dnrepairer.exe (PID: 4512)
- net.exe (PID: 1300)
GENERIC has been found (auto)
- LDPlayer_0900015201.exe (PID: 4120)
SUSPICIOUS
Reads security settings of Internet Explorer
- LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe (PID: 1100)
- LDPlayer_0900015201.exe (PID: 4120)
- dnplayer.exe (PID: 4820)
The process drops C-runtime libraries
- LDPlayer_0900015201.exe (PID: 4120)
- dnrepairer.exe (PID: 4512)
- dnplayer.exe (PID: 4820)
Executable content was dropped or overwritten
- dnrepairer.exe (PID: 4512)
- dnplayer.exe (PID: 4820)
- LDPlayer_0900015201.exe (PID: 4120)
Takes ownership (TAKEOWN.EXE)
- dnrepairer.exe (PID: 4512)
- LDPlayer_0900015201.exe (PID: 4120)
Uses ICACLS.EXE to modify access control lists
- dnrepairer.exe (PID: 4512)
- LDPlayer_0900015201.exe (PID: 4120)
Process drops legitimate windows executable
- dnrepairer.exe (PID: 4512)
- dnplayer.exe (PID: 4820)
- LDPlayer_0900015201.exe (PID: 4120)
Drops a system driver (possible attempt to evade defenses)
- dnrepairer.exe (PID: 4512)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3740)
- regsvr32.exe (PID: 6736)
Creates a new Windows service
- sc.exe (PID: 4552)
Starts POWERSHELL.EXE for commands execution
- dnrepairer.exe (PID: 4512)
Windows service management via SC.EXE
- sc.exe (PID: 5616)
- sc.exe (PID: 5960)
- sc.exe (PID: 1728)
There is functionality for taking screenshot (YARA)
- dnrepairer.exe (PID: 4512)
- dnplayer.exe (PID: 4820)
Creates a software uninstall entry
- LDPlayer_0900015201.exe (PID: 4120)
The process checks if it is being run in the virtual environment
- conhost.exe (PID: 1132)
- conhost.exe (PID: 6460)
- conhost.exe (PID: 3876)
There is functionality for VM detection VirtualBox (YARA)
- dnplayer.exe (PID: 4820)
Drops 7-zip archiver for unpacking
- LDPlayer_0900015201.exe (PID: 4120)
The process creates files with name similar to system file names
- LDPlayer_0900015201.exe (PID: 4120)
There is functionality for communication over UDP network (YARA)
- dnplayer.exe (PID: 4820)
INFO
Creates files or folders in the user directory
- LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe (PID: 1100)
- LDPlayer_0900015201.exe (PID: 4120)
- dnrepairer.exe (PID: 4512)
- dnplayer.exe (PID: 4820)
Checks supported languages
- LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe (PID: 1100)
- LDPlayer_0900015201.exe (PID: 4120)
- dnrepairer.exe (PID: 4512)
- Ld9BoxSVC.exe (PID: 3736)
- driverconfig.exe (PID: 5020)
- dnplayer.exe (PID: 4820)
- Ld9BoxSVC.exe (PID: 3396)
- vbox-img.exe (PID: 2716)
- vbox-img.exe (PID: 3652)
- vbox-img.exe (PID: 1604)
- Ld9BoxHeadless.exe (PID: 3820)
- Ld9BoxHeadless.exe (PID: 5372)
- identity_helper.exe (PID: 7444)
- Ld9BoxHeadless.exe (PID: 2220)
- Ld9BoxHeadless.exe (PID: 2128)
- Ld9BoxHeadless.exe (PID: 2596)
Checks proxy server information
- LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe (PID: 1100)
- LDPlayer_0900015201.exe (PID: 4120)
- slui.exe (PID: 4224)
- dnplayer.exe (PID: 4820)
Reads the computer name
- LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe (PID: 1100)
- LDPlayer_0900015201.exe (PID: 4120)
- Ld9BoxSVC.exe (PID: 3736)
- dnplayer.exe (PID: 4820)
- Ld9BoxSVC.exe (PID: 3396)
- Ld9BoxHeadless.exe (PID: 3820)
- Ld9BoxHeadless.exe (PID: 2220)
- Ld9BoxHeadless.exe (PID: 5372)
- Ld9BoxHeadless.exe (PID: 2596)
- Ld9BoxHeadless.exe (PID: 2128)
- identity_helper.exe (PID: 7444)
Reads the software policy settings
- LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe (PID: 1100)
- LDPlayer_0900015201.exe (PID: 4120)
- slui.exe (PID: 4224)
- dnplayer.exe (PID: 4820)
Reads the machine GUID from the registry
- LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe (PID: 1100)
- LDPlayer_0900015201.exe (PID: 4120)
- dnrepairer.exe (PID: 4512)
- dnplayer.exe (PID: 4820)
The sample compiled with english language support
- dnrepairer.exe (PID: 4512)
- dnplayer.exe (PID: 4820)
- LDPlayer_0900015201.exe (PID: 4120)
Creates files in the program directory
- dnrepairer.exe (PID: 4512)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6384)
- powershell.exe (PID: 5236)
- powershell.exe (PID: 2112)
Reads CPU info
- dnplayer.exe (PID: 4820)
Application launched itself
- msedge.exe (PID: 3584)
The sample compiled with chinese language support
- LDPlayer_0900015201.exe (PID: 4120)
Reads Environment values
- identity_helper.exe (PID: 7444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:07:07 02:47:49+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 2083840 |
| InitializedDataSize: | 1360384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16b6f1 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (0009) |
| CharacterSet: | Unicode |
| CompanyName: | JUST OKAY |
| FileDescription: | JUST OKAY |
| FileVersion: | 1.0.0.6 |
| InternalName: | JUST OKAY |
| LegalCopyright: | Copyright (C) 2024 |
| OriginalFileName: | JUST OKAY |
| ProductName: | JUST OKAY |
| ProductVersion: | 1.0.0.6 |
Total processes
293
Monitored processes
142
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "regsvr32" "C:\Program Files\ldplayer9box\x86\VBoxClient-x86.dll" /s | C:\Windows\SysWOW64\regsvr32.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 952 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1100 | "C:\Users\admin\AppData\Local\Temp\LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe" | C:\Users\admin\AppData\Local\Temp\LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | explorer.exe | ||||||||||||
User: admin Company: JUST OKAY Integrity Level: HIGH Description: JUST OKAY Exit code: 18349336 Version: 1.0.0.6 Modules
| |||||||||||||||
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | vbox-img.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | takeown.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | "net" start cryptsvc | C:\Windows\SysWOW64\net.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1440 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Ld9BoxHeadless.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1488 | "regsvr32" Wintrust.dll /s | C:\Windows\SysWOW64\regsvr32.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1604 | "C:\Program Files\ldplayer9box\vbox-img.exe" setuuid --filename "C:\LDPlayer\LDPlayer9\vms\leidian0\data.vmdk" --uuid 20160302-cccc-cccc-0eee-000000000000 | C:\Program Files\ldplayer9box\vbox-img.exe | — | dnplayer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: VirtualBox Virtual Disk Utility Exit code: 0 Version: 6.1.36.152435 Modules
| |||||||||||||||
| 1636 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | takeown.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
39 385
Read events
38 884
Write events
477
Delete events
24
Modification events
| (PID) Process: | (1100) LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\lden |
| Operation: | write | Name: | pcmac |
Value: b8cfc726683ad98cad9b5ec15f00cc1a | |||
| (PID) Process: | (1100) LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1100) LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1100) LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4120) LDPlayer_0900015201.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\ld\dnplayer_en |
| Operation: | write | Name: | pcid |
Value: b8cfc726683ad98cad9b5ec15f00cc1a | |||
| (PID) Process: | (2120) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\Usages\1.3.6.1.5.5.7.3.3 |
| Operation: | write | Name: | DefaultId |
Value: {00AAC56B-CD44-11D0-8CC2-00C04FC295EE} | |||
| (PID) Process: | (2120) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\FinalPolicy\{00AAC56B-CD44-11D0-8CC2-00C04FC295EE} |
| Operation: | write | Name: | $DLL |
Value: WINTRUST.DLL | |||
| (PID) Process: | (2120) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\FinalPolicy\{00AAC56B-CD44-11D0-8CC2-00C04FC295EE} |
| Operation: | write | Name: | $Function |
Value: SoftpubAuthenticode | |||
| (PID) Process: | (2120) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\Initialization\{64B9D180-8DA2-11CF-8736-00AA00A485EB} |
| Operation: | write | Name: | $DLL |
Value: WINTRUST.DLL | |||
| (PID) Process: | (2120) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\Initialization\{64B9D180-8DA2-11CF-8736-00AA00A485EB} |
| Operation: | write | Name: | $Function |
Value: SoftpubInitialize | |||
Executable files
428
Suspicious files
378
Text files
185
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1100 | LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | C:\LDPlayer\LDPlayer9\LDPlayer_0900015201.exe.part0 | — | |
MD5:— | SHA256:— | |||
| 1100 | LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | C:\LDPlayer\LDPlayer9\LDPlayer_0900015201.exe.part1 | — | |
MD5:— | SHA256:— | |||
| 1100 | LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | C:\LDPlayer\LDPlayer9\LDPlayer_0900015201.exe | — | |
MD5:— | SHA256:— | |||
| 4120 | LDPlayer_0900015201.exe | C:\Users\admin\AppData\Roaming\XuanZhi\fonts\NotoSans-Regular.otf | — | |
MD5:— | SHA256:— | |||
| 4120 | LDPlayer_0900015201.exe | C:\LDPlayer\LDPlayer9\data-3G.vmdk | — | |
MD5:— | SHA256:— | |||
| 4120 | LDPlayer_0900015201.exe | C:\LDPlayer\LDPlayer9\data.vmdk | — | |
MD5:— | SHA256:— | |||
| 4120 | LDPlayer_0900015201.exe | C:\LDPlayer\LDPlayer9\dnresource.rcc | — | |
MD5:— | SHA256:— | |||
| 4120 | LDPlayer_0900015201.exe | C:\LDPlayer\LDPlayer9\appName.text | text | |
MD5:B88F5E1E8443F65538D157DB8E3FFBA3 | SHA256:E69EAB737FCA991062800CB339B6D3900B21AAD13C8B4C5614DCB068DBDFBD40 | |||
| 4120 | LDPlayer_0900015201.exe | C:\LDPlayer\LDPlayer9\data\data.ini | text | |
MD5:17E952AE90EE25B3D324B0C9DC256F36 | SHA256:2320035DC5C47C3E016E5681CB8F4940AD4DCCCD34271D55FB84A1DDE02D37E5 | |||
| 4120 | LDPlayer_0900015201.exe | C:\LDPlayer\LDPlayer9\fonts\Roboto-Regular.otf | ttf | |
MD5:4ACD5F0E312730F1D8B8805F3699C184 | SHA256:72336333D602F1C3506E642E0D0393926C0EC91225BF2E4D216FCEBD82BB6CB5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
371
DNS requests
350
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1100 | LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | GET | 200 | 104.18.21.213:80 | http://r11.c.lencr.org/62.crl | unknown | — | — | whitelisted |
1100 | LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSXi0cW5bD2WLrmnasWibg2OuPDpgQUVXRPsnJP9WC6UNHX5lFcmgGHGtcCEAaLh8TalJ4a1%2BN4jLQPsGY%3D | unknown | — | — | whitelisted |
1100 | LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ5rEWLwbJFq%2FmAU80sm7E%3D | unknown | — | — | whitelisted |
1468 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
888 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
888 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
4120 | LDPlayer_0900015201.exe | GET | 200 | 8.209.111.156:80 | http://apien.ldmnq.com/statisticsMnqEvent?sv=0900015201&openid=3040&m=b8cfc726683ad98cad9b5ec15f00cc1a&event_key=install&event_value=&event_type=player&z=1753452114 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2992 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1100 | LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | 23.213.161.8:443 | files.ldrescdn.com | Akamai International B.V. | DE | unknown |
1100 | LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | 104.18.21.213:80 | r11.c.lencr.org | CLOUDFLARENET | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1100 | LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | 8.209.111.156:443 | apien.ldmnq.com | Alibaba US Technology Co., Ltd. | DE | whitelisted |
1100 | LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1100 | LDPlayer9_ens_com.cloudplay.cloudgames.platform_3040_ld.exe | 23.213.161.28:443 | res.ldrescdn.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
files.ldrescdn.com |
| unknown |
r11.c.lencr.org |
| whitelisted |
apien.ldmnq.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
res.ldrescdn.com |
| unknown |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2200 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
6104 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6104 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6104 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6104 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6104 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6104 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
Process | Message |
|---|---|
dnplayer.exe | audio wait from recv
|
Ld9BoxHeadless.exe | ldutils myhook enter |
Ld9BoxHeadless.exe | ldutils backgroundPreread enter |
Ld9BoxHeadless.exe | ldutils backgroundPreread leave |
Ld9BoxHeadless.exe | ldutils myhook enter |
Ld9BoxHeadless.exe | ldutils backgroundPreread enter |
Ld9BoxHeadless.exe | ldutils backgroundPreread leave |
Ld9BoxHeadless.exe | ldutils myhook enter |
Ld9BoxHeadless.exe | ldutils backgroundPreread enter |
Ld9BoxHeadless.exe | ldutils backgroundPreread leave |