| download: | You_Are_An_Idiot |
| Full analysis: | https://app.any.run/tasks/f3357b9e-0a27-4d4b-907f-b452ef0f5e10 |
| Verdict: | Suspicious activity |
| Analysis date: | March 09, 2018, 21:58:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | 9CD7E031723F18B708CDFBB4FE943A1D |
| SHA1: | 1A0C8F2DCF0B07DAC0733C2E640A348FC3255C8E |
| SHA256: | 11966E37B5C55188365DAEBD607E0C340523B37DA6B8D4815A9155624D6DDCD6 |
| SSDEEP: | 6144:JIRm1Igu5uqufuqutujuWuPugu5uLueuUuNuVLhM8enHwdO/:JIRmtJ |
MALICIOUS
Changes settings of System certificates
- iexplore.exe (PID: 3296)
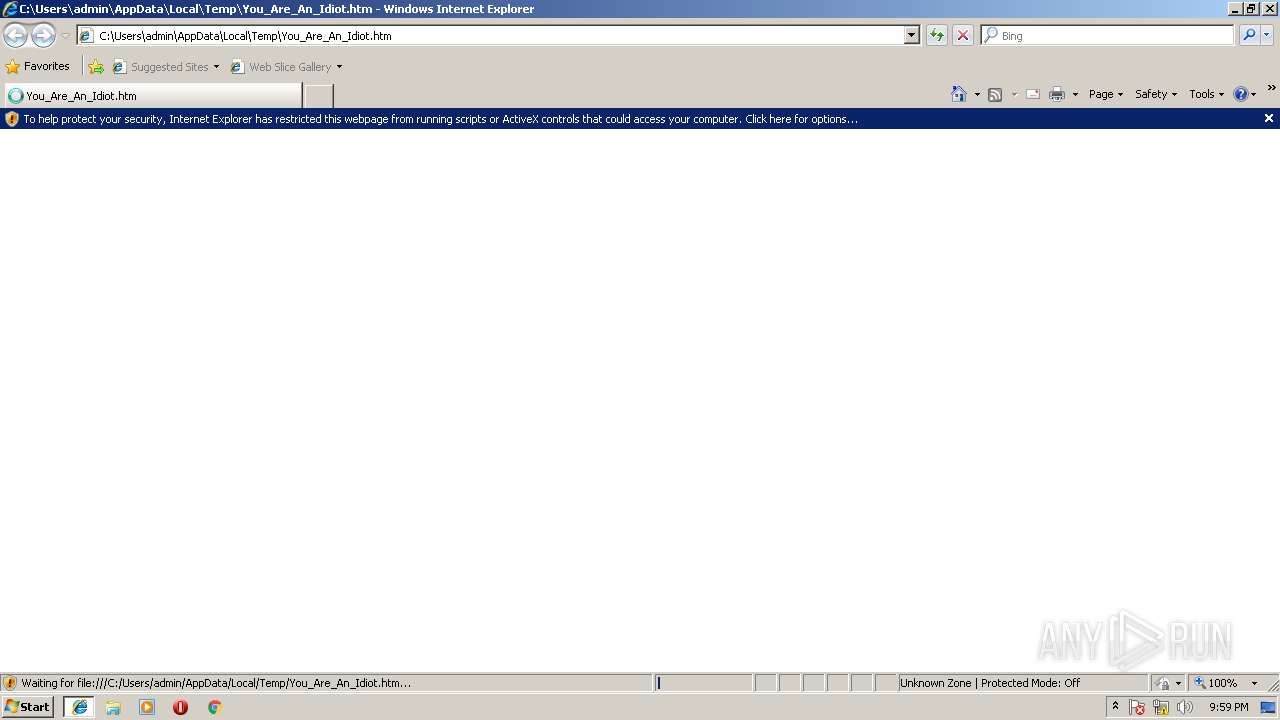
Changes internet zones settings
- iexplore.exe (PID: 2920)
SUSPICIOUS
Creates files in the user directory
- iexplore.exe (PID: 3296)
Writes to a desktop.ini file (may be used to cloak folders)
- iexplore.exe (PID: 2920)
Reads internet explorer settings
- iexplore.exe (PID: 3296)
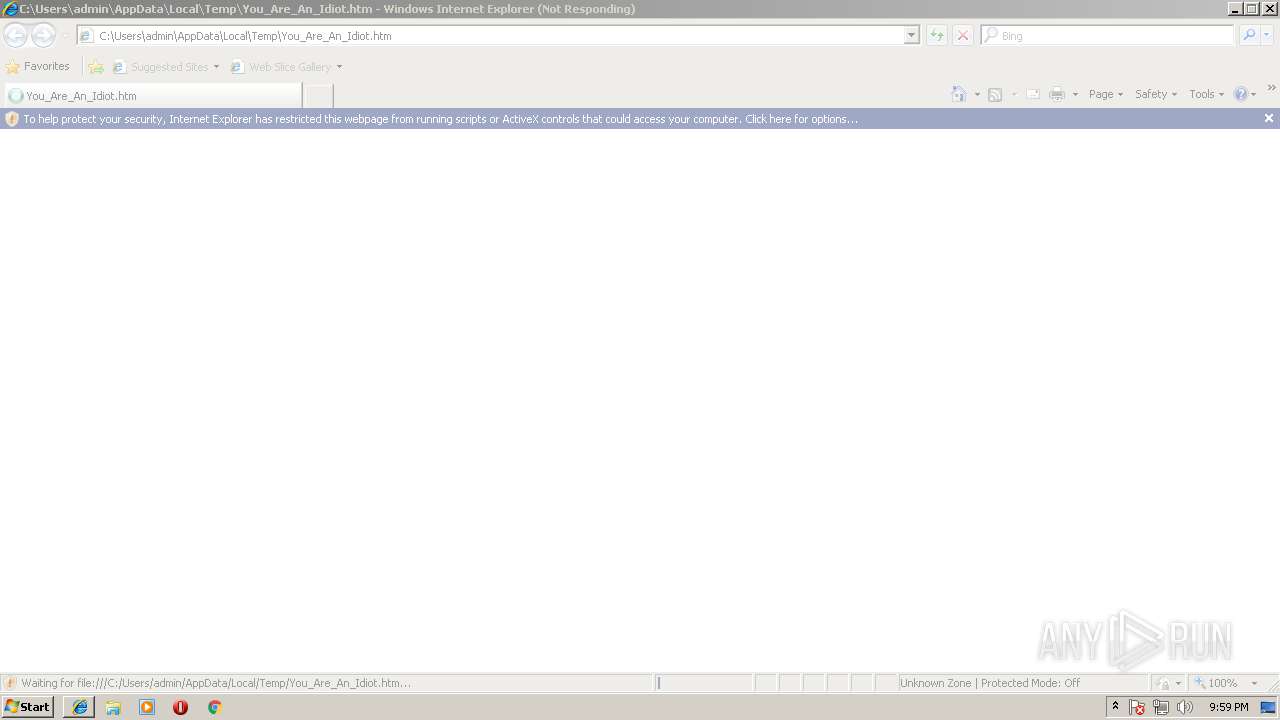
Starts Internet Explorer
- iexplore.exe (PID: 2920)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3296)
INFO
Dropped object may contain URL's
- iexplore.exe (PID: 3296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| ContentType: | text/html; charset=UTF-8 |
|---|---|
| viewport: | width=device-width, initial-scale=1.0, user-scalable=yes |
| Generator: | MediaWiki 1.19.24 |
| Keywords: | Malware Wiki,malware,You Are An Idiot,Trojan,Microsoft Windows,Malware,Virus |
| Description: | You Are An Idiot is a trojan website on Microsoft Windows. It is from the family Trojan:JS... |
| twitterCard: | summary |
| twitterSite: | @getfandom |
| twitterUrl: | http://malware.wikia.com/wiki/You_Are_An_Idiot |
| twitterTitle: | You Are An Idiot | Malware Wiki | FANDOM powered by Wikia |
| twitterDescription: | You Are An Idiot is a trojan website on Microsoft Windows. It is from the family Trojan:JS/NoBrain. It is the successor of Joke:Win32.Idiot. However, this malware will not delete files or anything... |
| Title: | You Are An Idiot | Malware Wiki | FANDOM powered by Wikia |
| appleItunesApp: | app-id=422467074, app-arguments=http://malware.wikia.com/wiki/You_Are_An_Idiot |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2920 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\You_Are_An_Idiot.htm | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1073807364 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3296 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2920 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
353
Read events
267
Write events
85
Delete events
1
Modification events
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005B000000090000000000000000000000000000000400000000000000108E82C8479FD301000000000000000000000000020000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001C00000000000000000000000000000000000000000000000000000000000000170000000000000000000000000000000000FFFFC0A8640B000000000000000002000000C0A8640B0000000000000000000000000000000000000000000000000C00000C37D0000010A73800D8703600000000000000000000000000000000000000000000000000000000000000000000000000000000000000000081F800009000230090002300380023000000000000702C000A00000000000000F8412C00 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {174A66BB-23E5-11E8-943E-5254004AAD21} |
Value: 0 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E20703000500090015003B0009003602 | |||
Executable files
0
Suspicious files
8
Text files
3
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GZH9GIXH\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3296 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabEEE1.tmp | — | |
MD5:— | SHA256:— | |||
| 3296 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarEEE2.tmp | — | |
MD5:— | SHA256:— | |||
| 3296 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@scorecardresearch[1].txt | — | |
MD5:— | SHA256:— | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC74B389B938BDA8C.TMP | — | |
MD5:— | SHA256:— | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD9171B27CB4B4717.TMP | — | |
MD5:— | SHA256:— | |||
| 3296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5457A8CE4B2A7499F8299A013B6E1C7C_CE50F893881D43DC0C815E4D80FAF2B4 | binary | |
MD5:— | SHA256:— | |||
| 3296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5080DC7A65DB6A5960ECD874088F3328_2908F682DFC81A793BD240CF29711C77 | der | |
MD5:— | SHA256:— | |||
| 3296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5080DC7A65DB6A5960ECD874088F3328_2908F682DFC81A793BD240CF29711C77 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
34
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 178.255.83.1:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQLqIKj6Gi5thHaqKC1ECU9aXsCRQQUmvMr2s%2BtT7YvuypISCoStxtCwSQCEAwVv1ET25DRN9Laswdl4Rw%3D | GB | der | 471 b | whitelisted |
— | — | GET | 200 | 178.255.83.1:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | GB | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 151.101.192.194:443 | beacon.wikia-services.com | Fastly | US | suspicious |
— | — | 74.120.188.194:443 | slot1-images.wikia.nocookie.net | — | US | unknown |
— | — | 95.172.94.12:445 | pixel.quantserve.com | Quantcast Corporation | GB | unknown |
— | — | 95.172.94.17:445 | pixel.quantserve.com | Quantcast Corporation | GB | unknown |
— | — | 178.255.83.1:80 | ocsp.usertrust.com | CCANET Limited | GB | unknown |
— | — | 2.19.43.224:443 | sb.scorecardresearch.com | Akamai International B.V. | — | whitelisted |
— | — | 95.172.94.59:445 | pixel.quantserve.com | Quantcast Corporation | GB | unknown |
— | — | 95.172.94.49:445 | pixel.quantserve.com | Quantcast Corporation | GB | unknown |
— | — | 95.172.94.47:445 | pixel.quantserve.com | Quantcast Corporation | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
slot1-images.wikia.nocookie.net |
| suspicious |
beacon.wikia-services.com |
| suspicious |
sb.scorecardresearch.com |
| shared |
pixel.quantserve.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |