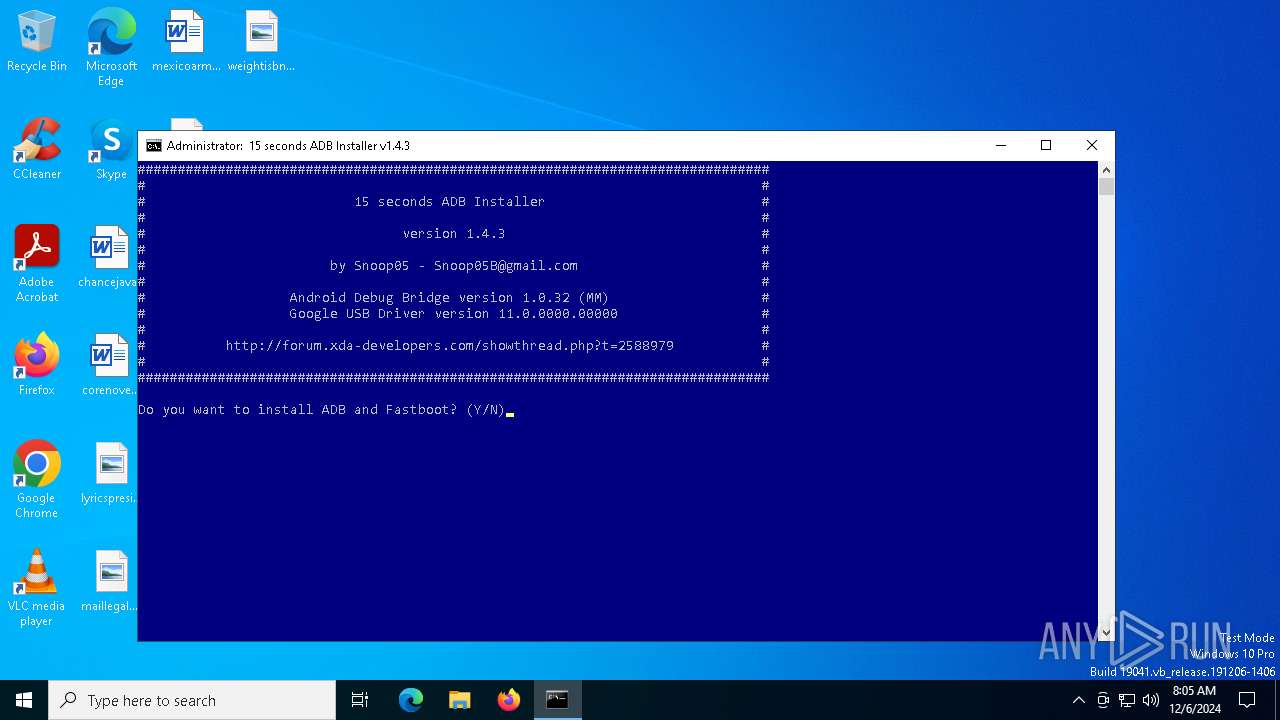
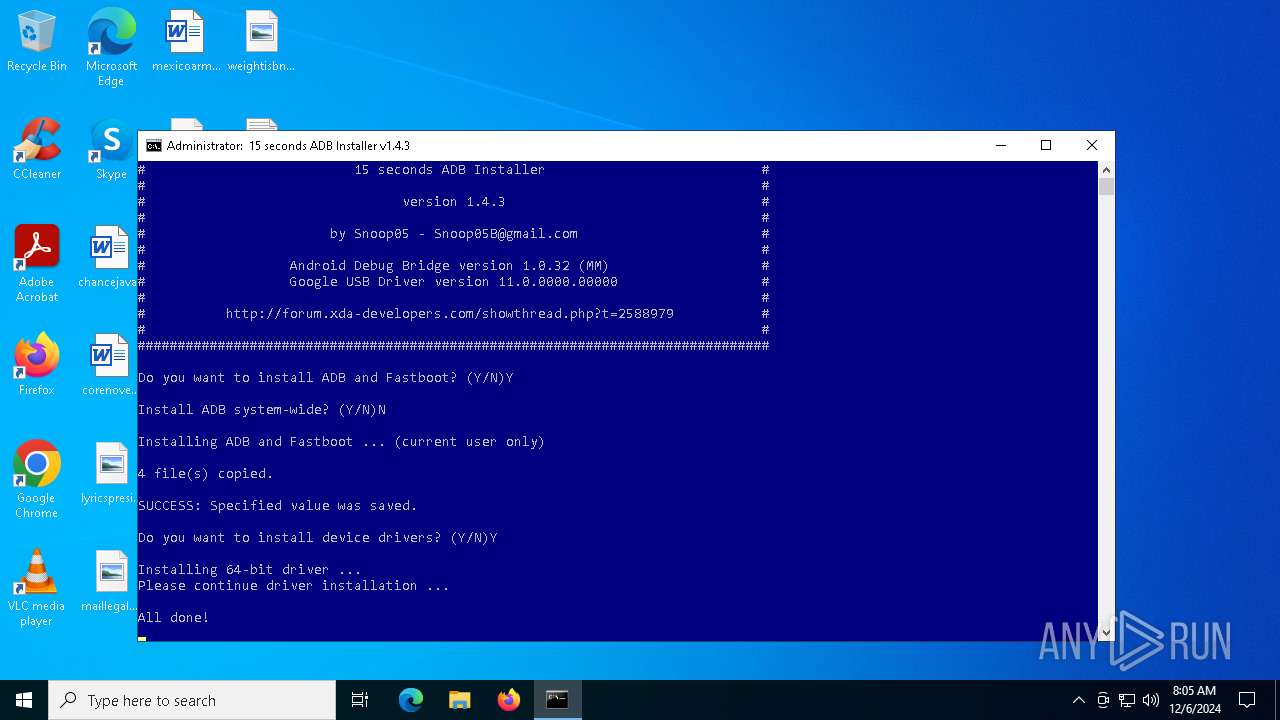
| File name: | adb-setup-1.4.3.exe |
| Full analysis: | https://app.any.run/tasks/590dc9b1-c4c1-4dd7-b80f-5f62e7d83f59 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2024, 08:05:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 4C2574964F1A0F42CA2DD604989842FE |
| SHA1: | 6A3C7C0F389F0443C48EBB5E1E0F68A1CD1871AC |
| SHA256: | 11934B2E5B4FC6ACA7649CB5861D07A4A42BB1EA18A18C8C8C2EF228738BDFDD |
| SSDEEP: | 98304:2k5uJWeV6RPwgH/ICdP25trbW3X+7zgUakvqVe0sIMw/OxtSceP/y7MXmnnKtC9T:q8UXNB+yk7gcf7igccyeTK2Hpzbrm |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- adb-setup-1.4.3.exe (PID: 6396)
- adb-setup-1.4.3.exe (PID: 6636)
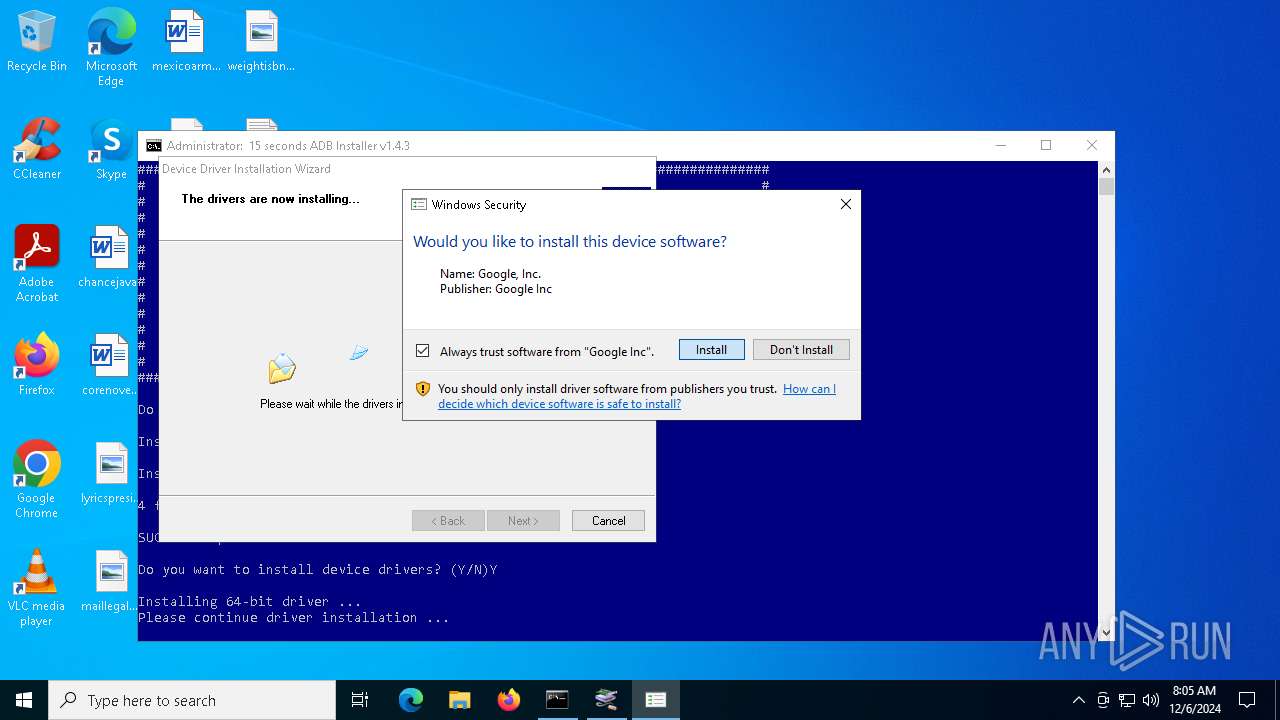
Application launched itself
- adb-setup-1.4.3.exe (PID: 6396)
- adb-setup-1.4.3.exe (PID: 6576)
- cmd.exe (PID: 6676)
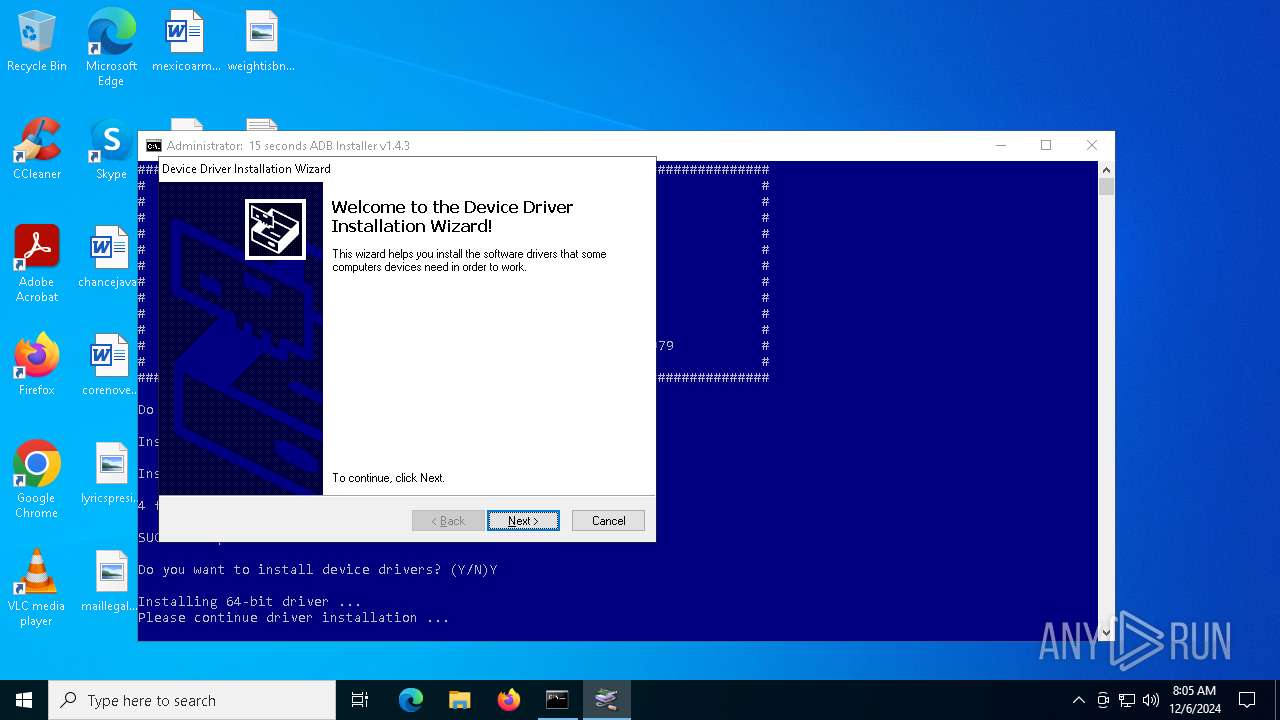
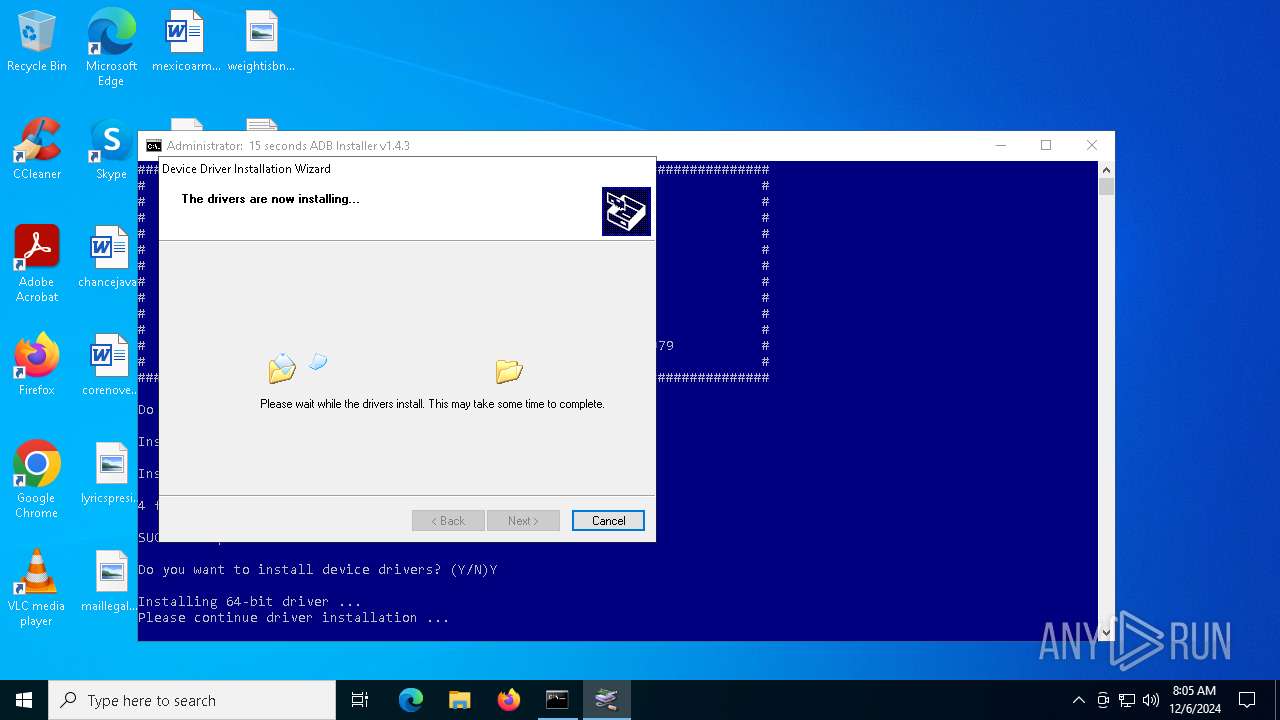
Executable content was dropped or overwritten
- adb-setup-1.4.3.exe (PID: 6576)
- xcopy.exe (PID: 7068)
- xcopy.exe (PID: 7092)
- xcopy.exe (PID: 7116)
- xcopy.exe (PID: 7144)
- DPInst_x64.exe (PID: 1944)
- drvinst.exe (PID: 3736)
Process drops legitimate windows executable
- adb-setup-1.4.3.exe (PID: 6576)
- DPInst_x64.exe (PID: 1944)
- drvinst.exe (PID: 3736)
Starts CMD.EXE for commands execution
- adb-setup-1.4.3.exe (PID: 6636)
- cmd.exe (PID: 6676)
Executing commands from a ".bat" file
- adb-setup-1.4.3.exe (PID: 6636)
Process copies executable file
- cmd.exe (PID: 6676)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 6676)
The executable file from the user directory is run by the CMD process
- DPInst_x64.exe (PID: 1944)
Starts a Microsoft application from unusual location
- DPInst_x64.exe (PID: 1944)
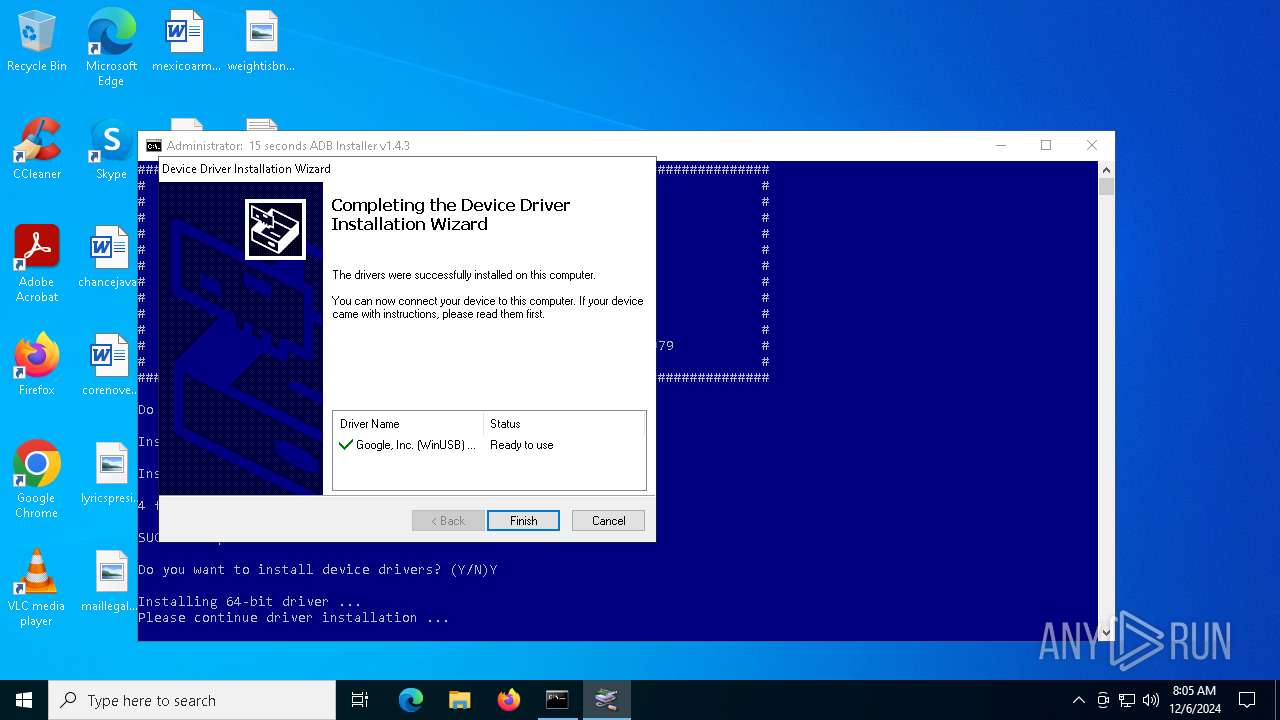
Creates files in the driver directory
- drvinst.exe (PID: 3736)
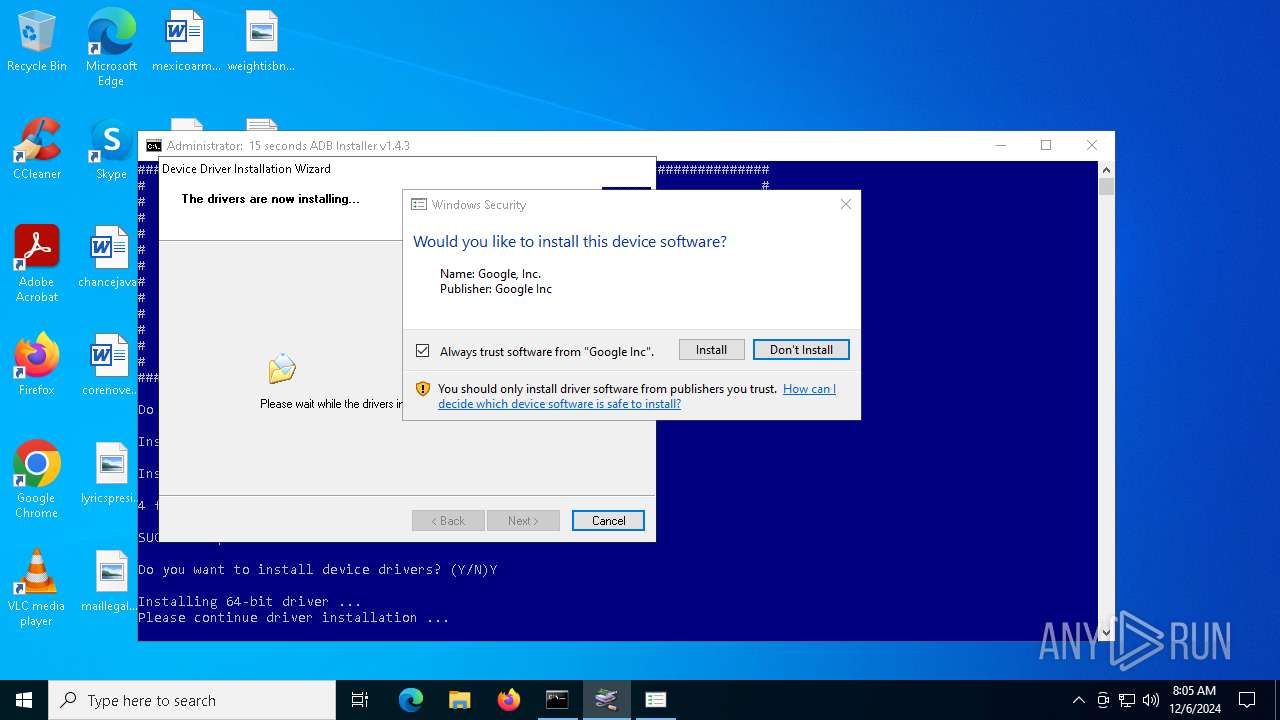
Checks Windows Trust Settings
- drvinst.exe (PID: 3736)
Creates a software uninstall entry
- DPInst_x64.exe (PID: 1944)
INFO
Reads the computer name
- adb-setup-1.4.3.exe (PID: 6396)
- adb-setup-1.4.3.exe (PID: 6636)
- DPInst_x64.exe (PID: 1944)
- drvinst.exe (PID: 3736)
Checks supported languages
- adb-setup-1.4.3.exe (PID: 6396)
- adb-setup-1.4.3.exe (PID: 6576)
- adb-setup-1.4.3.exe (PID: 6636)
- drvinst.exe (PID: 3736)
- DPInst_x64.exe (PID: 1944)
Process checks computer location settings
- adb-setup-1.4.3.exe (PID: 6396)
- adb-setup-1.4.3.exe (PID: 6636)
Create files in a temporary directory
- adb-setup-1.4.3.exe (PID: 6576)
- DPInst_x64.exe (PID: 1944)
Checks operating system version
- cmd.exe (PID: 6676)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 3208)
Reads the software policy settings
- rundll32.exe (PID: 3208)
- DPInst_x64.exe (PID: 1944)
- drvinst.exe (PID: 3736)
Creates files in the program directory
- DPInst_x64.exe (PID: 1944)
Reads the machine GUID from the registry
- DPInst_x64.exe (PID: 1944)
- drvinst.exe (PID: 3736)
Adds/modifies Windows certificates
- drvinst.exe (PID: 3736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:31 00:38:38+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 89600 |
| InitializedDataSize: | 324096 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1638f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.3.0 |
| ProductVersionNumber: | 1.4.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Snoop05 |
| FileDescription: | 15 seconds ADB Installer |
| FileVersion: | 1.4.3 |
| InternalName: | adb-installer |
| LegalCopyright: | - |
| OriginalFileName: | adb-installer-1.4.3.exe |
| PrivateBuild: | December 30, 2012 |
| ProductName: | 15 seconds ADB Installer |
| ProductVersion: | 1.4.3 |
Total processes
143
Monitored processes
18
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1944 | driver\DPInst_x64 /f | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\DPInst_x64.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 256 Version: 2.1 Modules
| |||||||||||||||
| 2072 | SETX PATH "C:\Program Files (x86)\Common Files\Oracle\Java\javapath;C:\WINDOWS\system32;C:\WINDOWS;C:\WINDOWS\System32\Wbem;C:\WINDOWS\System32\WindowsPowerShell\v1.0\;C:\WINDOWS\System32\OpenSSH\;C:\Program Files\PowerShell\7\;C:\Users\admin\AppData\Local\Microsoft\WindowsApps;C:\Users\admin\adb" | C:\Windows\SysWOW64\setx.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setx - Sets environment variables Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2612 | PING localhost -n 1 | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3208 | rundll32.exe C:\WINDOWS\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{2430c999-92e9-4640-bf51-91a270c6da49} Global\{2843f351-319a-6c4e-a09a-7ef237aa99e3} C:\WINDOWS\System32\DriverStore\Temp\{d3b29aec-62bf-7e4a-b3b9-cbf0c71c2bab}\android_winusb.inf C:\WINDOWS\System32\DriverStore\Temp\{d3b29aec-62bf-7e4a-b3b9-cbf0c71c2bab}\androidwinusba64.cat | C:\Windows\System32\rundll32.exe | — | drvinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3736 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{1a56c95a-c559-ca49-907d-42a583a1f958}\android_winusb.inf" "9" "4a40c2c7f" "0000000000000180" "WinSta0\Default" "00000000000001DC" "208" "c:\users\admin\appdata\local\temp\7zipsfx.000\driver" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4320 | PING localhost -n 2 | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4500 | C:\WINDOWS\system32\cmd.exe /S /D /c" VER " | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6280 | FIND "C:\Users\admin\adb" PATH.TMP | C:\Windows\SysWOW64\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6300 | FIND "5.1" | C:\Windows\SysWOW64\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6396 | "C:\Users\admin\AppData\Local\Temp\adb-setup-1.4.3.exe" | C:\Users\admin\AppData\Local\Temp\adb-setup-1.4.3.exe | — | explorer.exe | |||||||||||
User: admin Company: Snoop05 Integrity Level: MEDIUM Description: 15 seconds ADB Installer Exit code: 0 Version: 1.4.3 Modules
| |||||||||||||||
Total events
11 072
Read events
11 063
Write events
8
Delete events
1
Modification events
| (PID) Process: | (2072) setx.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | PATH |
Value: C:\Program Files (x86)\Common Files\Oracle\Java\javapath;C:\WINDOWS\system32;C:\WINDOWS;C:\WINDOWS\System32\Wbem;C:\WINDOWS\System32\WindowsPowerShell\v1.0\;C:\WINDOWS\System32\OpenSSH\;C:\Program Files\PowerShell\7\;C:\Users\admin\AppData\Local\Microsoft\WindowsApps;C:\Users\admin\adb | |||
| (PID) Process: | (1944) DPInst_x64.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (3736) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates |
| Operation: | delete value | Name: | FCAC7E666CC54341CA213BECF2EB463F2B62ADB0 |
Value: | |||
| (PID) Process: | (3736) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates\FCAC7E666CC54341CA213BECF2EB463F2B62ADB0 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000FCAC7E666CC54341CA213BECF2EB463F2B62ADB0040000000100000010000000C576F4A854906489E58DDE48E108AAF419000000010000001000000064C86CE87B2959F545802172EFC08C5E0F0000000100000014000000670418BBA696DA1A0C4FFE2848906DFB9756BC5220000000010000008B050000308205873082046FA00302010202102912C70C9A2B8A3EF6F6074662D68B8D300D06092A864886F70D01010505003081B4310B300906035504061302555331173015060355040A130E566572695369676E2C20496E632E311F301D060355040B1316566572695369676E205472757374204E6574776F726B313B3039060355040B13325465726D73206F66207573652061742068747470733A2F2F7777772E766572697369676E2E636F6D2F727061202863293130312E302C06035504031325566572695369676E20436C617373203320436F6465205369676E696E672032303130204341301E170D3134303132393030303030305A170D3136303132393233353935395A3081CA310B3009060355040613025553311330110603550408130A43616C69666F726E6961311630140603550407130D4D6F756E7461696E205669657731133011060355040A140A476F6F676C6520496E633131302F060355040B13284469676974616C20494420436C6173732033202D204A617661204F626A656374205369676E696E673131302F060355040B14284469676974616C20494420436C6173732033202D204A617661204F626A656374205369676E696E67311330110603550403140A476F6F676C6520496E6330820122300D06092A864886F70D01010105000382010F003082010A0282010100BE19705B27A5D05B05974BB1EF49E88FF1E83E1B7581DB62A385DA751BE2B0FD8611D2C86535ED786A357CA7254DCD2A8216C1F3A89BA53B5F307791D9F8105305E400D88B6D1B96A0BCA2B3493A0F96F7E63859E651DDB5F3087844DCCF2B61AA1BEB3A5C83F6CE91AE09F5FE4115941B13DE7E4C99BB955798A5DD6A827AC837A73F75D8B794DDBDF4F8FC16E4C82E82883A1553EECF2E32F86EA0E4647F693C6A7589D7BE54F4C8713D920E1007FCBDFC7851EB187C62227FBE8EC6988B47C8836A30780B0B5107921B1D405FF7E0CCAD35FB17FAAC418E6FB96A870A0B4165E38288C3914B68C04D764433C4834D5CB545F1781F90A83C4E65BA6B78DEFF0203010001A382017B3082017730090603551D1304023000300E0603551D0F0101FF04040302078030400603551D1F043930373035A033A031862F687474703A2F2F637363332D323031302D63726C2E766572697369676E2E636F6D2F435343332D323031302E63726C30440603551D20043D303B3039060B6086480186F84501071703302A302806082B06010505070201161C68747470733A2F2F7777772E766572697369676E2E636F6D2F72706130130603551D25040C300A06082B06010505070303307106082B0601050507010104653063302406082B060105050730018618687474703A2F2F6F6373702E766572697369676E2E636F6D303B06082B06010505073002862F687474703A2F2F637363332D323031302D6169612E766572697369676E2E636F6D2F435343332D323031302E636572301F0603551D23041830168014CF99A9EA7B26F44BC98E8FD7F00526EFE3D2A79D301106096086480186F84201010404030204103016060A2B06010401823702011B040830060101000101FF300D06092A864886F70D01010505000382010100D8E992BE922493B580EFF7C98F783E3C8D90EDAC5DD68EAE031DDCE137F8F9E2E405CF5D74DDBC4DAC33D93939623904C72B8615A5E0C9F886C11B8A7BC3FFFCD70B6CC490B190C329189390B93601F8CBA11F01FAE8D7C4DFB3495435DCD400F3955DB1DE7A461E611BFCD764E1E0087F728A00913ABA20B610FA4C7FAAE57EC7A30AAF768087667BCD5A001564257D0C0D2F13EB6414820C8A16D124103E33ADB71F42125D1D41092FBAD45AAE61ED57E753CCCB4B721DDEABDDA5ACB0C408FCD0DAFD2F3AA012661911470C213995FCBB0212754AB79F3BF74AB2D11137223595D9B2FD942BC4075511AE850269BF56290EE17CC1C8D1D06D280F202C359E | |||
| (PID) Process: | (1944) DPInst_x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\092555911492C6959D2596D612F52DCA71881CA2 |
| Operation: | write | Name: | UninstallString |
Value: C:\PROGRA~1\DIFX\D29FE547208FE130\DPInst_x64.exe /u C:\WINDOWS\System32\DriverStore\FileRepository\android_winusb.inf_amd64_bd75d06c56998078\android_winusb.inf | |||
| (PID) Process: | (1944) DPInst_x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\092555911492C6959D2596D612F52DCA71881CA2 |
| Operation: | write | Name: | DisplayName |
Value: Windows Driver Package - Google, Inc. (WinUSB) AndroidUsbDeviceClass (08/28/2014 11.0.0000.00000) | |||
| (PID) Process: | (1944) DPInst_x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\092555911492C6959D2596D612F52DCA71881CA2 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\PROGRA~1\DIFX\D29FE547208FE130\DPInst_x64.exe,0 | |||
| (PID) Process: | (1944) DPInst_x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\092555911492C6959D2596D612F52DCA71881CA2 |
| Operation: | write | Name: | DisplayVersion |
Value: 08/28/2014 11.0.0000.00000 | |||
| (PID) Process: | (1944) DPInst_x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\092555911492C6959D2596D612F52DCA71881CA2 |
| Operation: | write | Name: | Publisher |
Value: Google, Inc. | |||
Executable files
27
Suspicious files
11
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6576 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\adb\adb.exe | executable | |
MD5:775416971E2A69064B8ACD575D3DFF4D | SHA256:1A7919487FF69796754219239D5D5B5472D019AF988757B5C4092253E7A78F2B | |||
| 6576 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\androidwinusba64.cat | binary | |
MD5:B83F9FA084F11007C7E6C668E6FA9E54 | SHA256:8F3F15BAEAF50AE7388562BE0303F5AC7EE3CB255448A24E3D33E1F094E0680E | |||
| 6576 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\amd64\NOTICE.txt | text | |
MD5:EA7F2158B930BAF2C0FE799566489716 | SHA256:A19B767B9DDDA7306C78232E4A223D0BA966471B74DCE3C0C995307CAB5BF7B7 | |||
| 6576 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\install.bat | text | |
MD5:6F6EDB4834BD4AFE36503A447BFFECCF | SHA256:151A3EA2B30720D1462109CA4563E42EC6A6709C502941AA533476858A6F3657 | |||
| 6576 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\androidwinusb86.cat | cat | |
MD5:76CFE751E17119F352C29F9FCE83D24F | SHA256:15A39B14E5FA4EC4BBE16632DBB19C7E0159649702BF98F9F77B2ABD7EBCC4DE | |||
| 6576 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\i386\WUDFUpdate_01009.dll | executable | |
MD5:E1BBE9E3568CF54598E9A8D23697B67E | SHA256:A902BB3BFF785FAAEB6432BE76F798627A80B2CC45441E16440E46E6D7340F2C | |||
| 6576 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\xp\SETX.exe | executable | |
MD5:5C04E0E82A5CF2288512BA35DE3223C3 | SHA256:0AB71E83950C682A0EAB6B35E9BACE97EDFDB25E909988B0D5D0A6EA5C3E4D40 | |||
| 6576 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\android_winusb.inf | binary | |
MD5:BEA78A10D31B64E81D007B4CE0ECD0EE | SHA256:7984D14AF8EBCE8255448AA728A5436916FCCB36D1814516301F04A7DEA2A666 | |||
| 6576 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\DPInst_x64.exe | executable | |
MD5:4192A5B905374E423EC1E545599AA86E | SHA256:567F40A09F1D9E72396296AD194FA7CF48B72361D6E259D6B99DA774C2CD8981 | |||
| 6576 | adb-setup-1.4.3.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\driver\DPInst_x86.exe | executable | |
MD5:9568538CEF3A955A88811250C7B9F053 | SHA256:CB7F00F91AE5F7D88277AC2EE5CFB5D3A9F8E9E629C3DE317ABF226A8B6B76B6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
32
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6176 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5888 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5888 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.18:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.164.18:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.20.142.3:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |