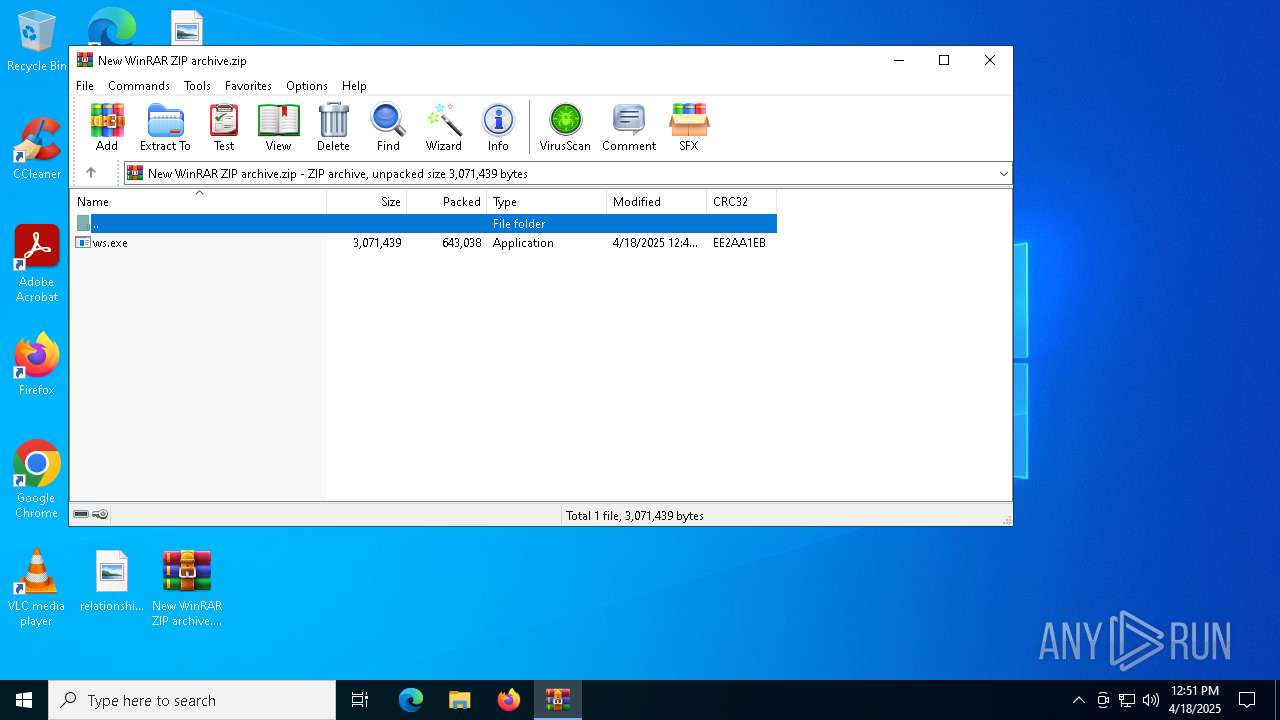
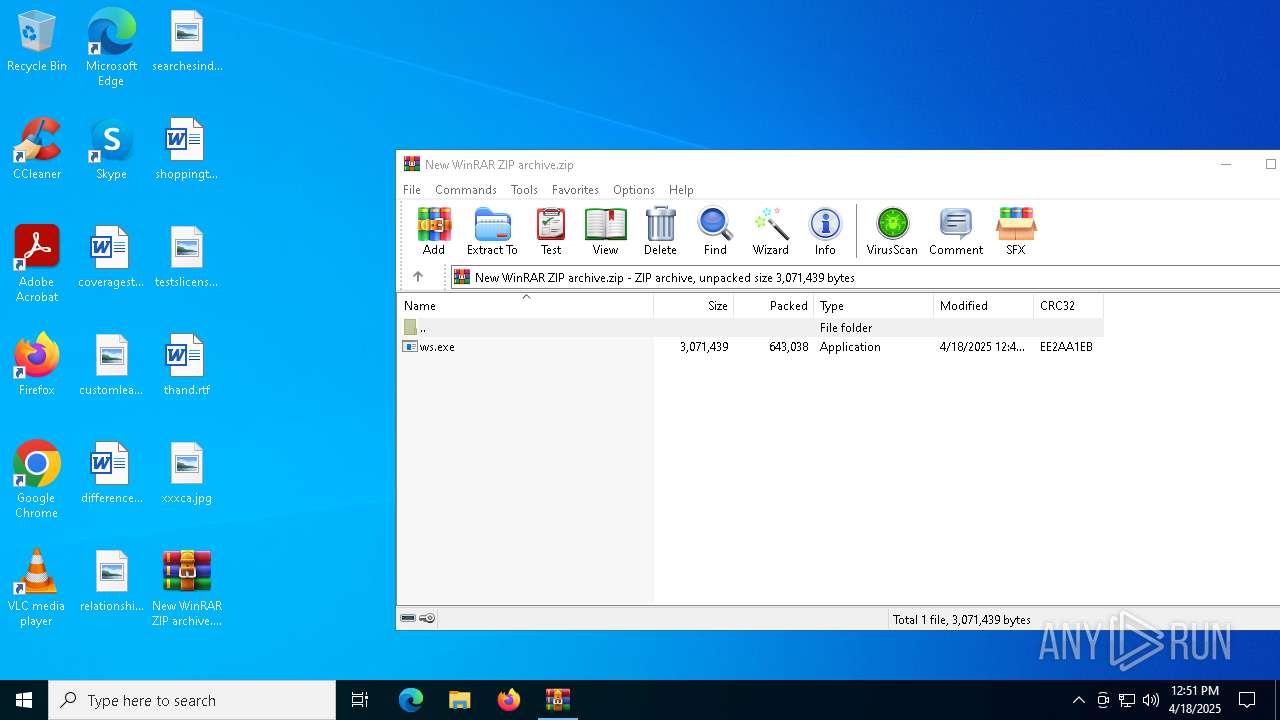
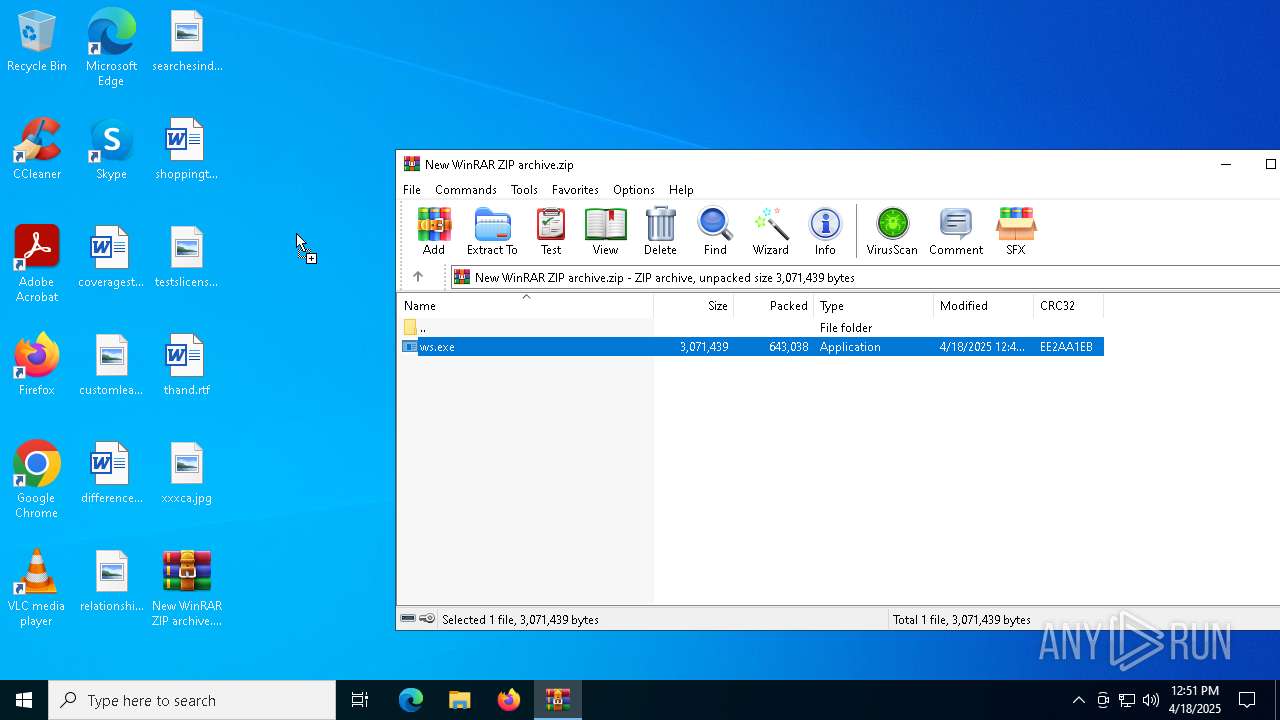
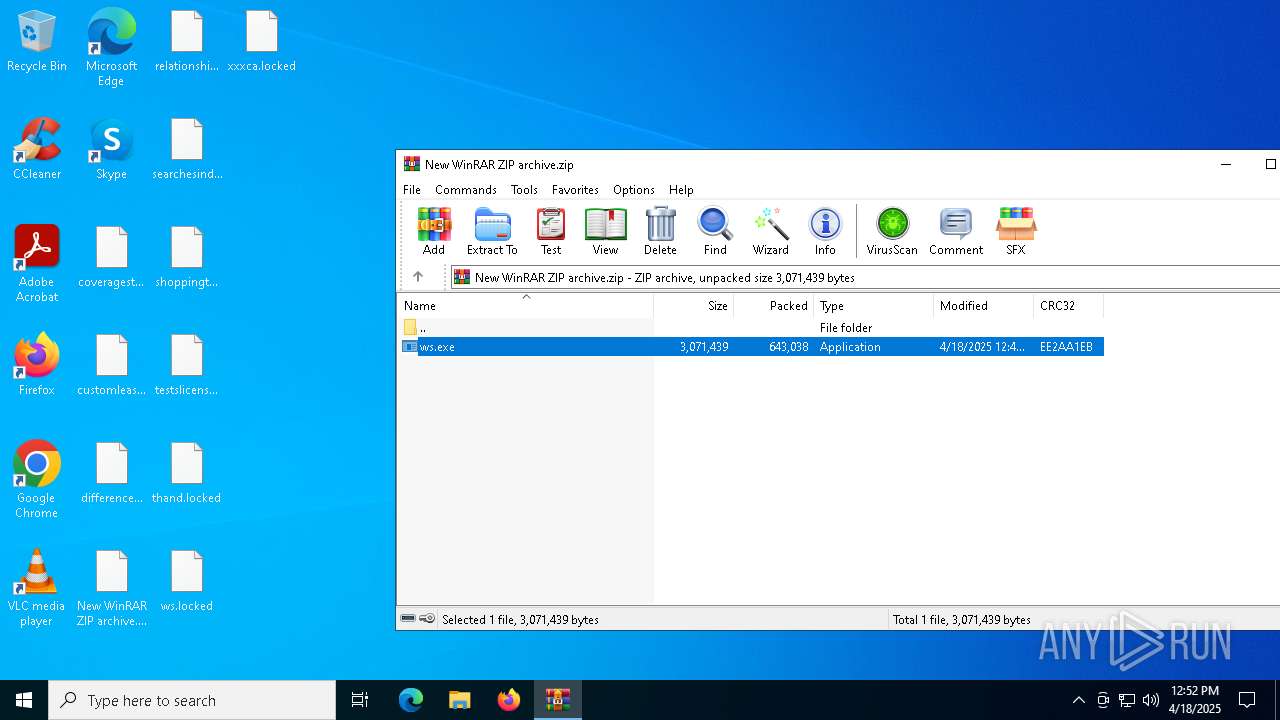
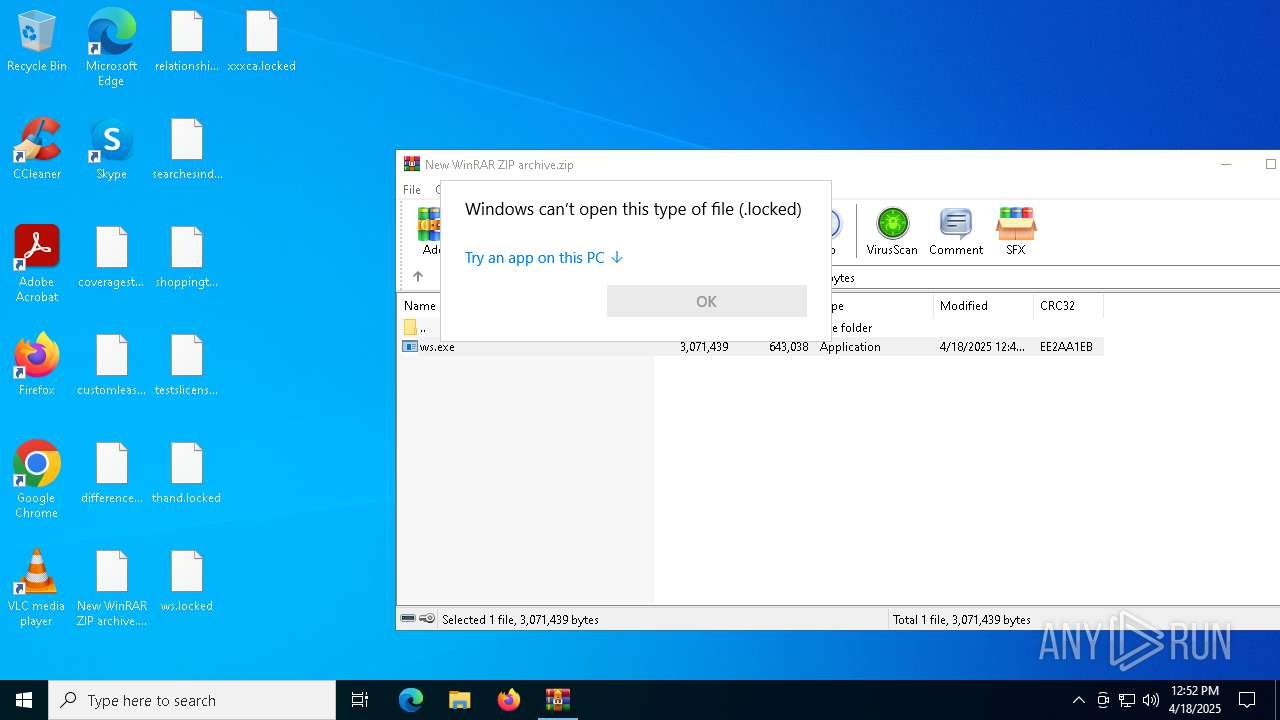
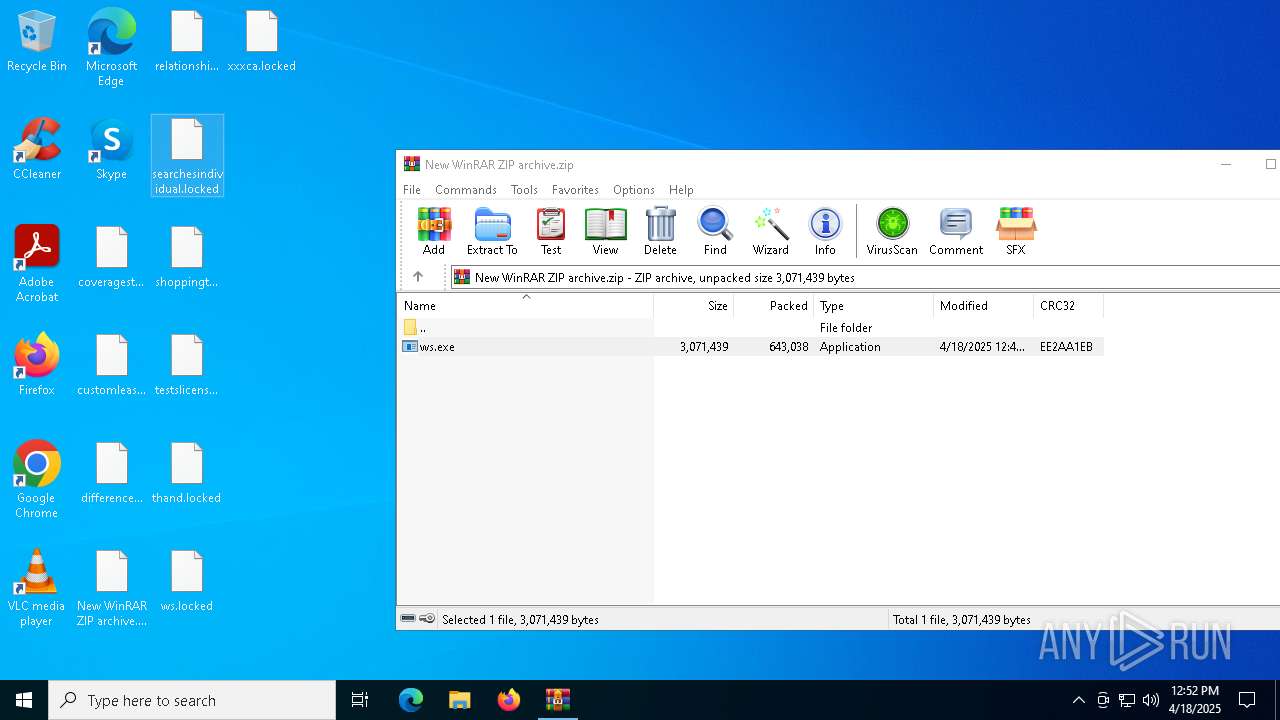
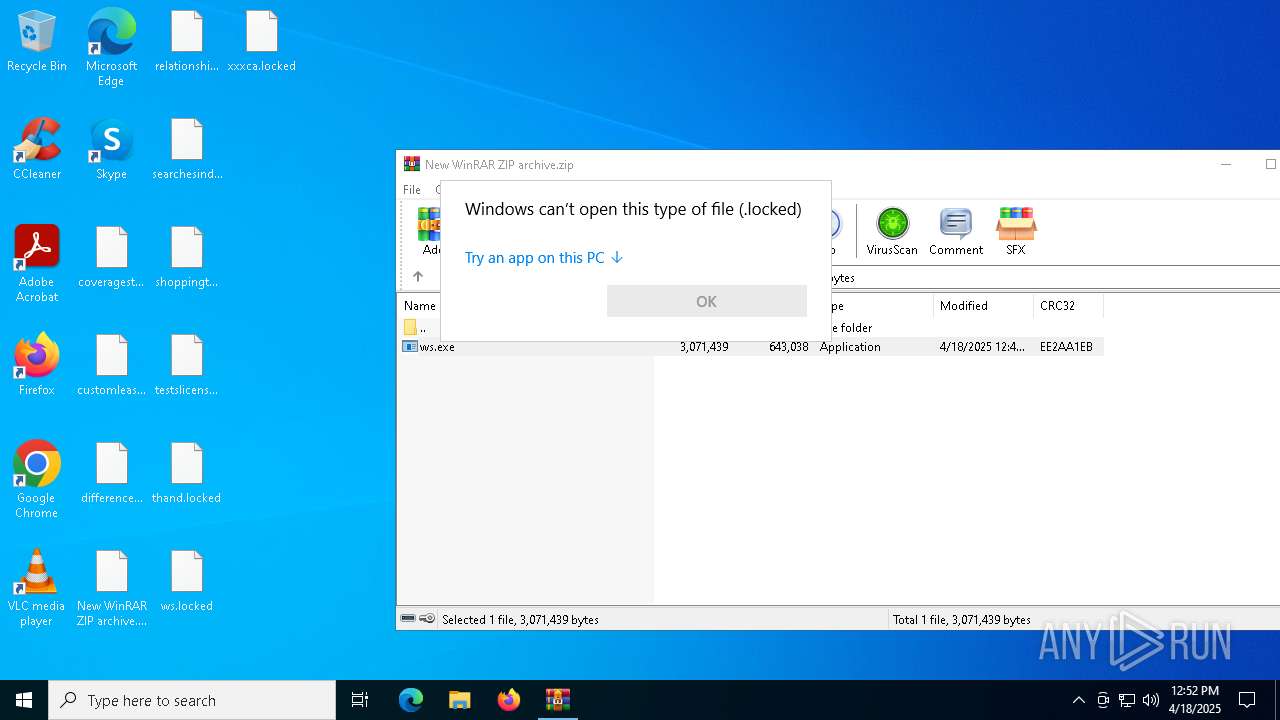
| File name: | New WinRAR ZIP archive.zip |
| Full analysis: | https://app.any.run/tasks/6e430bc4-65c2-4782-b9f3-ecb7b4ebd0e3 |
| Verdict: | Malicious activity |
| Analysis date: | April 18, 2025, 12:51:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | C050C795E8E25DEDEB32897E51AA7BBC |
| SHA1: | 37320EBD389A1B3BED2A172F3A7805B2B11C1391 |
| SHA256: | 118D4F2D3880FAC851E31CF697603377079008A819C36A708D93BBD28177CDED |
| SSDEEP: | 24576:exvF3TQDF7slrD4ESMBH1GS36cYFuSdxQ1B0ArR7f5oAOMKI:exvF3TQDF7slrD4ESMBH1GS36cYFuSdW |
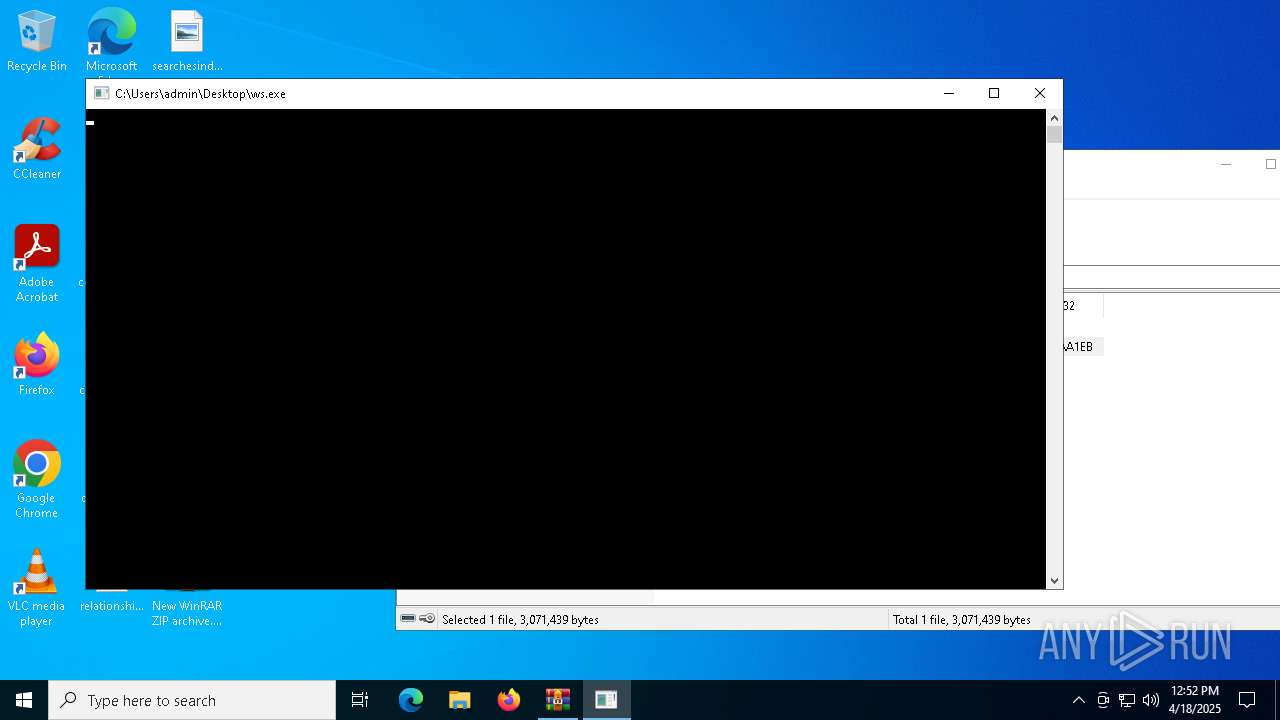
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7012)
Deletes shadow copies
- cmd.exe (PID: 1672)
SUSPICIOUS
Starts CMD.EXE for commands execution
- ws.exe (PID: 5364)
Executable content was dropped or overwritten
- ws.exe (PID: 5364)
INFO
Checks supported languages
- ws.exe (PID: 5364)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7012)
Manual execution by a user
- ws.exe (PID: 5364)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 6872)
- OpenWith.exe (PID: 6132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:18 15:49:08 |
| ZipCRC: | 0xee2aa1eb |
| ZipCompressedSize: | 643038 |
| ZipUncompressedSize: | 3071439 |
| ZipFileName: | ws.exe |
Total processes
138
Monitored processes
11
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | C:\WINDOWS\system32\cmd.exe /c bcdedit /set {current} safeboot minimal | C:\Windows\System32\cmd.exe | — | ws.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1672 | C:\WINDOWS\system32\cmd.exe /c vssadmin delete shadows /all /quiet | C:\Windows\System32\cmd.exe | — | ws.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3332 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ws.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4448 | bcdedit /set {current} safeboot minimal | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot Configuration Data Editor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4896 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5364 | "C:\Users\admin\Desktop\ws.exe" | C:\Users\admin\Desktop\ws.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5720 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6132 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6872 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 683
Read events
2 675
Write events
8
Delete events
0
Modification events
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\New WinRAR ZIP archive.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
12
Text files
9
Unknown types
0
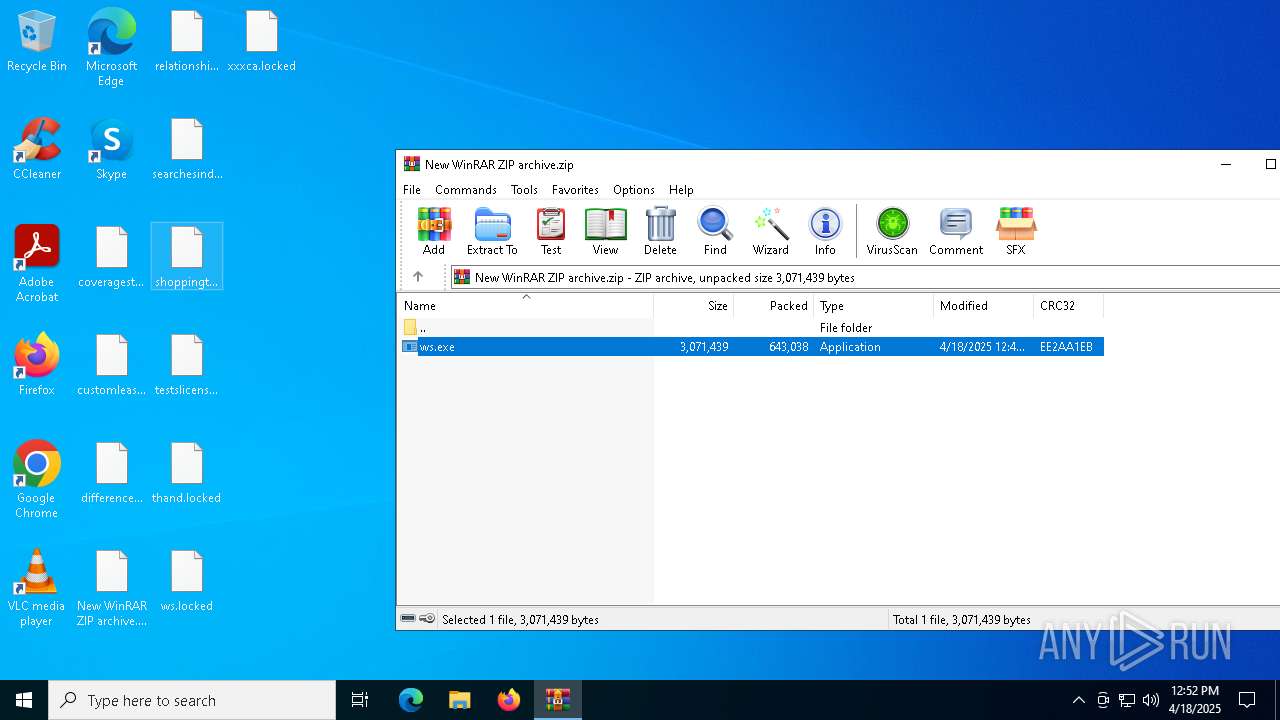
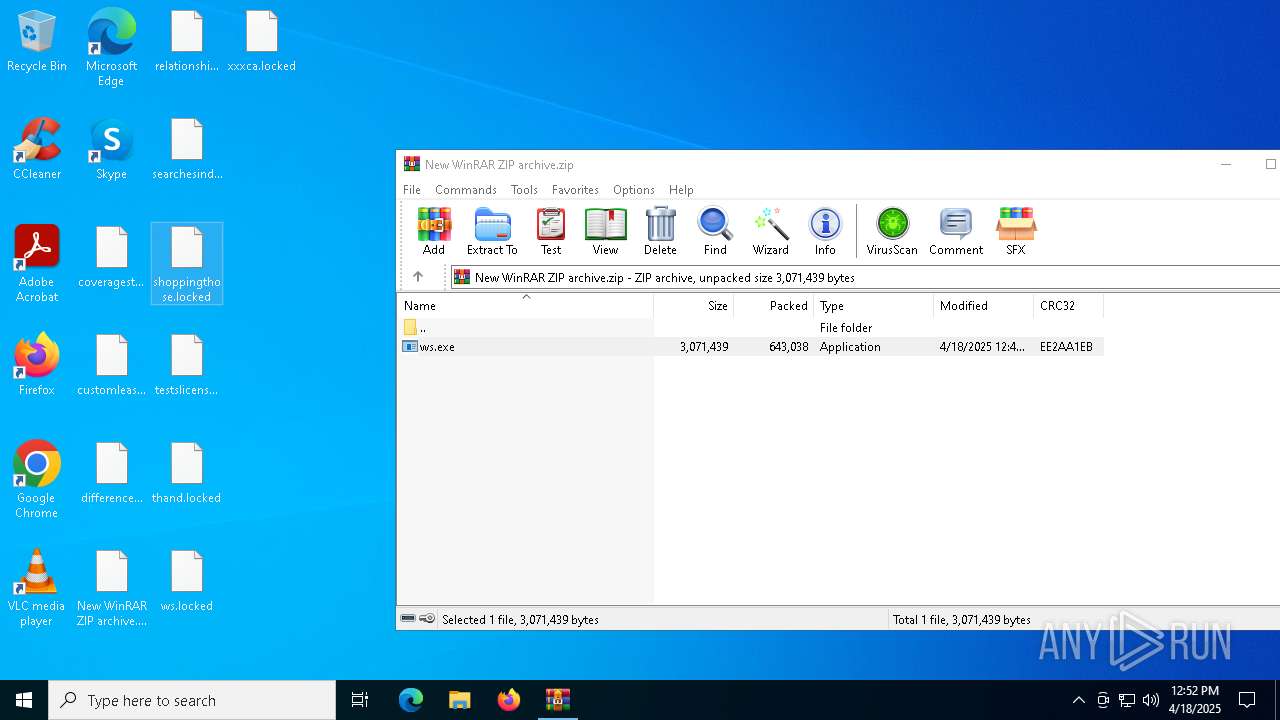
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5364 | ws.exe | C:\Users\admin\Desktop\xxxca.jpg | binary | |
MD5:3B3F2476556CE4492C3E0EBB3BC0F357 | SHA256:E27547BB558488B0846E71F3B9A42242EE3FA7E63A04D2A0383411A4344219DE | |||
| 5364 | ws.exe | C:\Users\admin\Desktop\New WinRAR ZIP archive.zip | binary | |
MD5:72519ED5AA3CFA51EF6FB5CE205542E7 | SHA256:BE5890F844A928983A5B347D728CDA0344BFCF6F602EE6BA9F13BF6CDB3B60AB | |||
| 5364 | ws.exe | C:\Users\admin\Desktop\relationshipcertain.locked | binary | |
MD5:75359DEAA21385B082BE26262F19FA5A | SHA256:94DB1482EC2A95DDB75480B830689F2EE9AA523A9F25951C8AD0878402D591C5 | |||
| 5364 | ws.exe | C:\Users\admin\Desktop\relationshipcertain.jpg | binary | |
MD5:75359DEAA21385B082BE26262F19FA5A | SHA256:94DB1482EC2A95DDB75480B830689F2EE9AA523A9F25951C8AD0878402D591C5 | |||
| 5364 | ws.exe | C:\Users\admin\Desktop\thand.rtf | text | |
MD5:BE34BA23F589CA7B3439E7FE86441AE2 | SHA256:E8B86B414C4FF2323660FE6012D551BE250CCAC49F04FDF8DADE3B3E23978F95 | |||
| 5364 | ws.exe | C:\Users\admin\Desktop\shoppingthose.locked | text | |
MD5:BC2C68440C1ACCF0EC5F5ACDA7C6B496 | SHA256:47F2903FE2E884982177B0B2DFB317500510768E6AD12F5C5A478EC69ACED041 | |||
| 5364 | ws.exe | C:\Users\admin\Desktop\differencecover.locked | text | |
MD5:0665D6A4436545A5FC7892FDAAC52EE7 | SHA256:0F86E7FF5FF83557B0199A9CFFA9D52CC8F5B6C16681B62D8D17A37D1B0845FF | |||
| 5364 | ws.exe | C:\Users\admin\Desktop\New WinRAR ZIP archive.locked | binary | |
MD5:72519ED5AA3CFA51EF6FB5CE205542E7 | SHA256:BE5890F844A928983A5B347D728CDA0344BFCF6F602EE6BA9F13BF6CDB3B60AB | |||
| 5364 | ws.exe | C:\Users\admin\Desktop\searchesindividual.locked | binary | |
MD5:D15A3222CE1D6CA2550E1747ED214E6F | SHA256:4B1DE4BE3BD467B1FB98F9D87444BE6F3035156E2DBE4F71D9D99B61CB31632F | |||
| 5364 | ws.exe | C:\Users\admin\Desktop\coveragestatement.locked | text | |
MD5:ACBE718A6F6452C2F732265F9AD0585A | SHA256:10F8890A3D7BFE93764372069E0E09EC4B9FA5BAE0BBC88CB9861298C3AA801F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
17
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4228 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4228 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4228 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
4228 | SIHClient.exe | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |