| download: | /static/update_web/vLocalServerSetup.exe |
| Full analysis: | https://app.any.run/tasks/4a08762f-9db0-4c57-ae63-cb75ff7099f8 |
| Verdict: | Malicious activity |
| Analysis date: | September 21, 2025, 20:35:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 81A391C24829CB4F5F4D6017D6699F81 |
| SHA1: | 33A6FFA8308C085A4677F11BD6E4462BCAA41E85 |
| SHA256: | 1186733072AF16F7E4FC5A71D50BC152535917B9BD8FF1F2C3D6B8924BDC8E30 |
| SSDEEP: | 98304:bE0npSVxrO5PS3vnWs280iX/r4seGnqyZcvZkOEWWrZvTNetnmOQi1ssQ63lcydo:shYc2hXNKNJ2dRFCygrTec09F+4qhCK |
MALICIOUS
Changes the autorun value in the registry
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.tmp (PID: 3872)
Registers / Runs the DLL via REGSVR32.EXE
- vLocalServerSetup.tmp (PID: 5460)
- _iu14D2N.tmp (PID: 5184)
- vLocalServerSetup.tmp (PID: 3872)
- _iu14D2N.tmp (PID: 7132)
Changes settings of System certificates
- certutil.exe (PID: 1236)
SUSPICIOUS
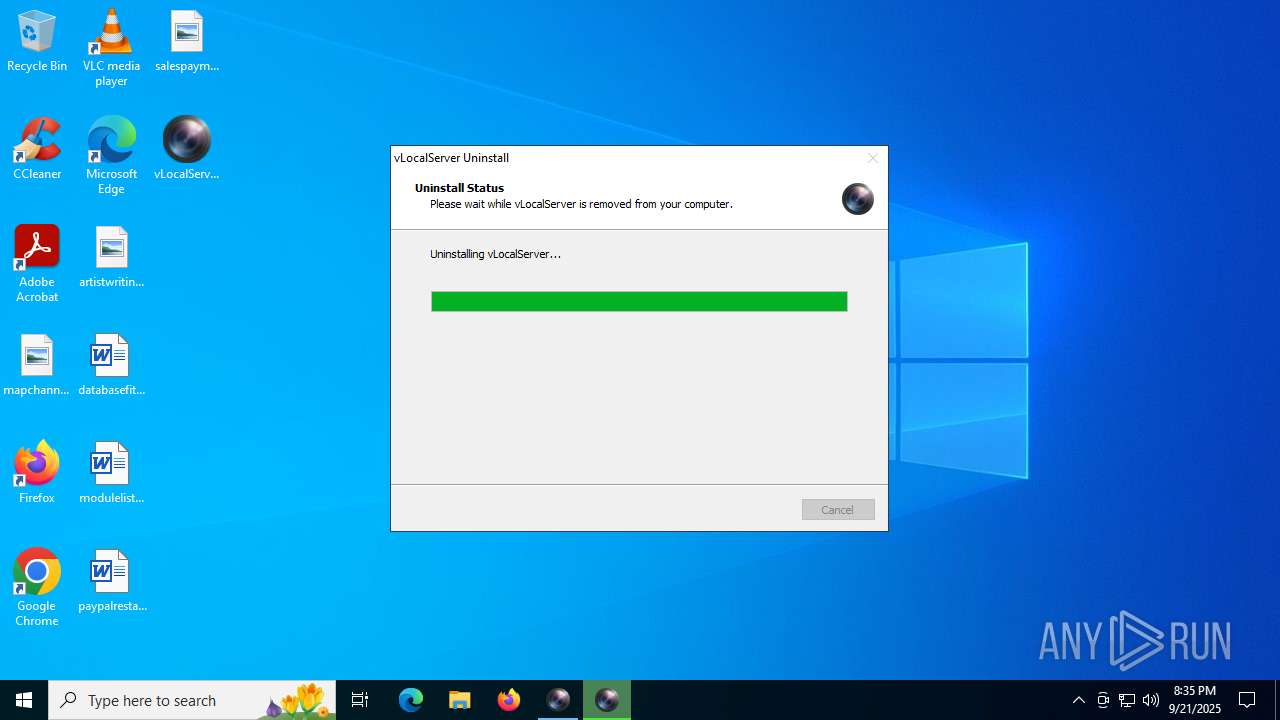
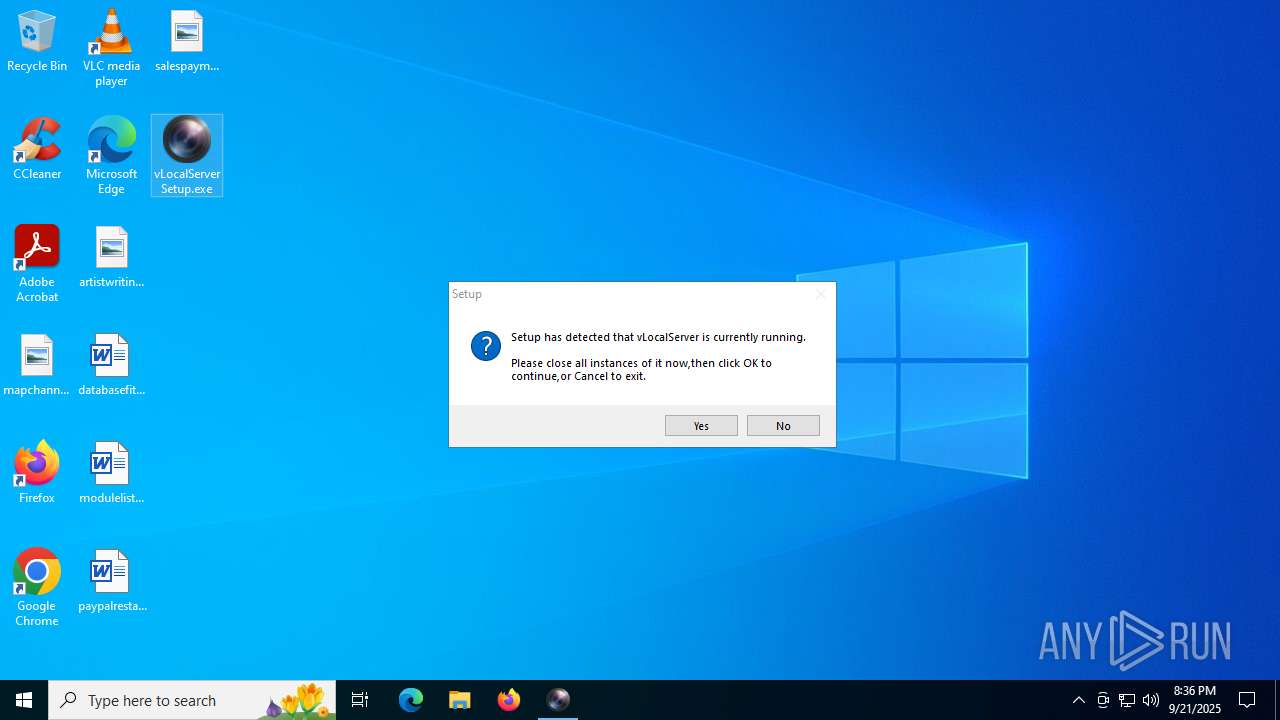
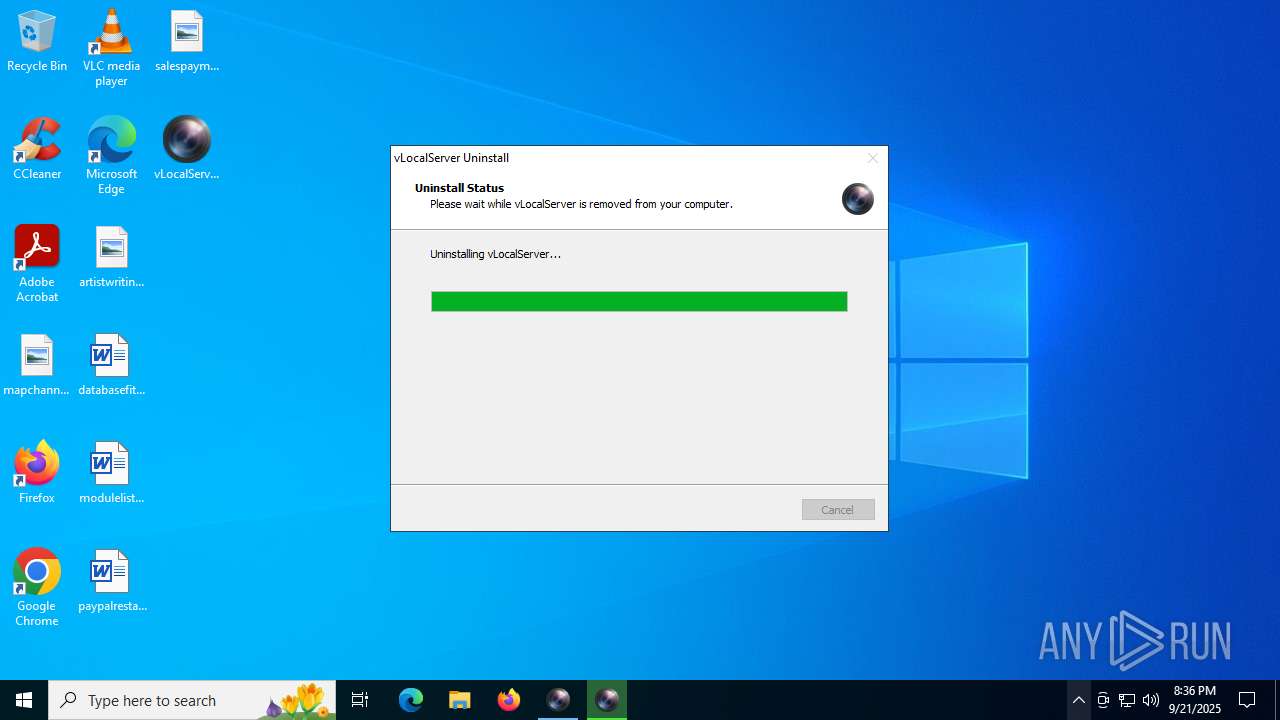
Launching a dropped file
- vLocalServerSetup.exe (PID: 6720)
- vLocalServerSetup.exe (PID: 2216)
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.exe (PID: 2400)
- vLocalServerSetup.exe (PID: 4228)
- vLocalServerSetup.tmp (PID: 3872)
- unins000.exe (PID: 760)
- _iu14D2N.tmp (PID: 5184)
- vLocalServerSetup.exe (PID: 6936)
- vLocalServerSetup.exe (PID: 6876)
- vLocalServerSetup.tmp (PID: 3840)
- vLocalServerSetup.exe (PID: 684)
- vLocalServerSetup.exe (PID: 4224)
- _iu14D2N.tmp (PID: 7132)
- vLocalServerSetup.tmp (PID: 6236)
Executable content was dropped or overwritten
- vLocalServerSetup.exe (PID: 6720)
- vLocalServerSetup.exe (PID: 2216)
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.exe (PID: 2400)
- vLocalServerSetup.exe (PID: 4228)
- vLocalServerSetup.tmp (PID: 3872)
- _iu14D2N.tmp (PID: 5184)
- unins000.exe (PID: 760)
- vLocalServerSetup.exe (PID: 6936)
- vLocalServerSetup.exe (PID: 6876)
- vLocalServerSetup.tmp (PID: 3840)
- vLocalServerSetup.exe (PID: 684)
- vLocalServerSetup.exe (PID: 4224)
- _iu14D2N.tmp (PID: 7132)
- vLocalServerSetup.tmp (PID: 6236)
Reads security settings of Internet Explorer
- vLocalServerSetup.tmp (PID: 2804)
- InstallCert.exe (PID: 2996)
- vLocalServerSetup.tmp (PID: 6164)
- vLocalServerGuard.exe (PID: 1880)
- InstallCert.exe (PID: 5244)
- vLocalServerGuard.exe (PID: 72)
- vLocalServerSetup.tmp (PID: 7000)
- vLocalServerSetup.tmp (PID: 6656)
Reads the Windows owner or organization settings
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.tmp (PID: 3872)
- _iu14D2N.tmp (PID: 5184)
- vLocalServerSetup.tmp (PID: 3840)
- vLocalServerSetup.tmp (PID: 6236)
- _iu14D2N.tmp (PID: 7132)
Process drops legitimate windows executable
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.tmp (PID: 3872)
- _iu14D2N.tmp (PID: 5184)
- vLocalServerSetup.tmp (PID: 3840)
- _iu14D2N.tmp (PID: 7132)
- vLocalServerSetup.tmp (PID: 6236)
The process drops C-runtime libraries
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.tmp (PID: 3872)
Reads the date of Windows installation
- InstallCert.exe (PID: 2996)
- InstallCert.exe (PID: 5244)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3852)
- regsvr32.exe (PID: 1132)
Executing commands from a ".bat" file
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.tmp (PID: 3872)
Adds/modifies Windows certificates
- certutil.exe (PID: 1236)
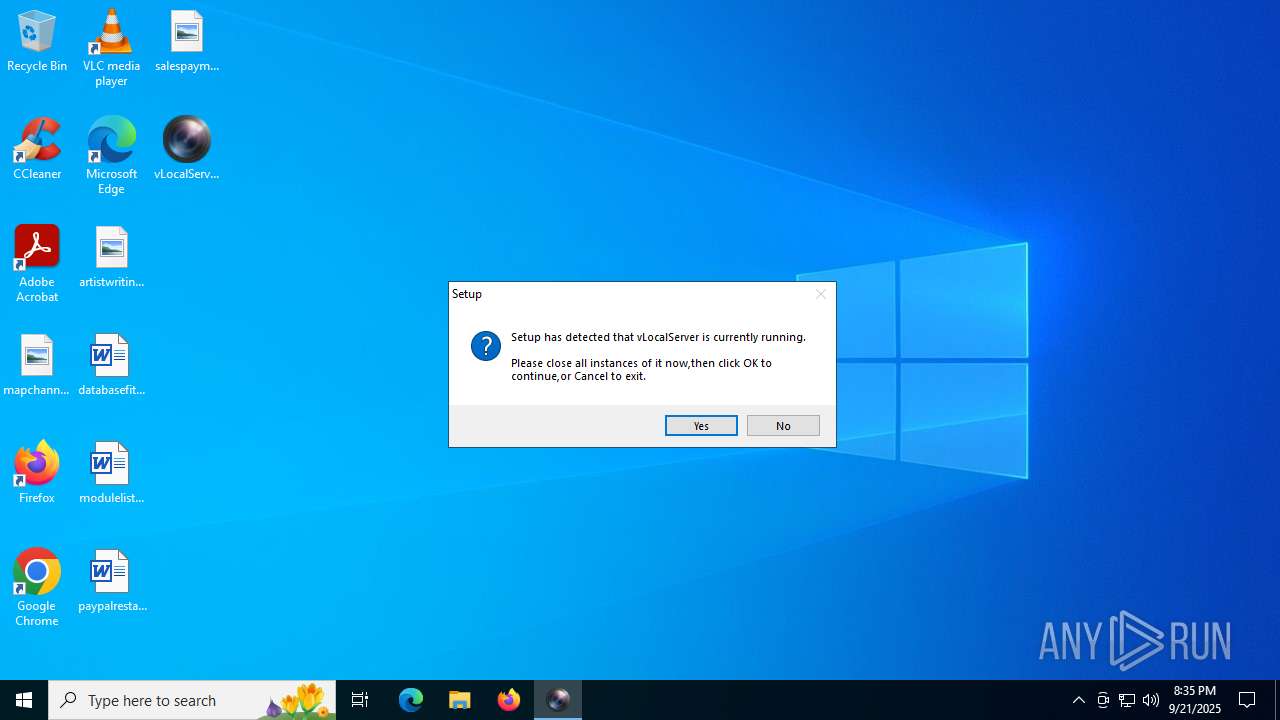
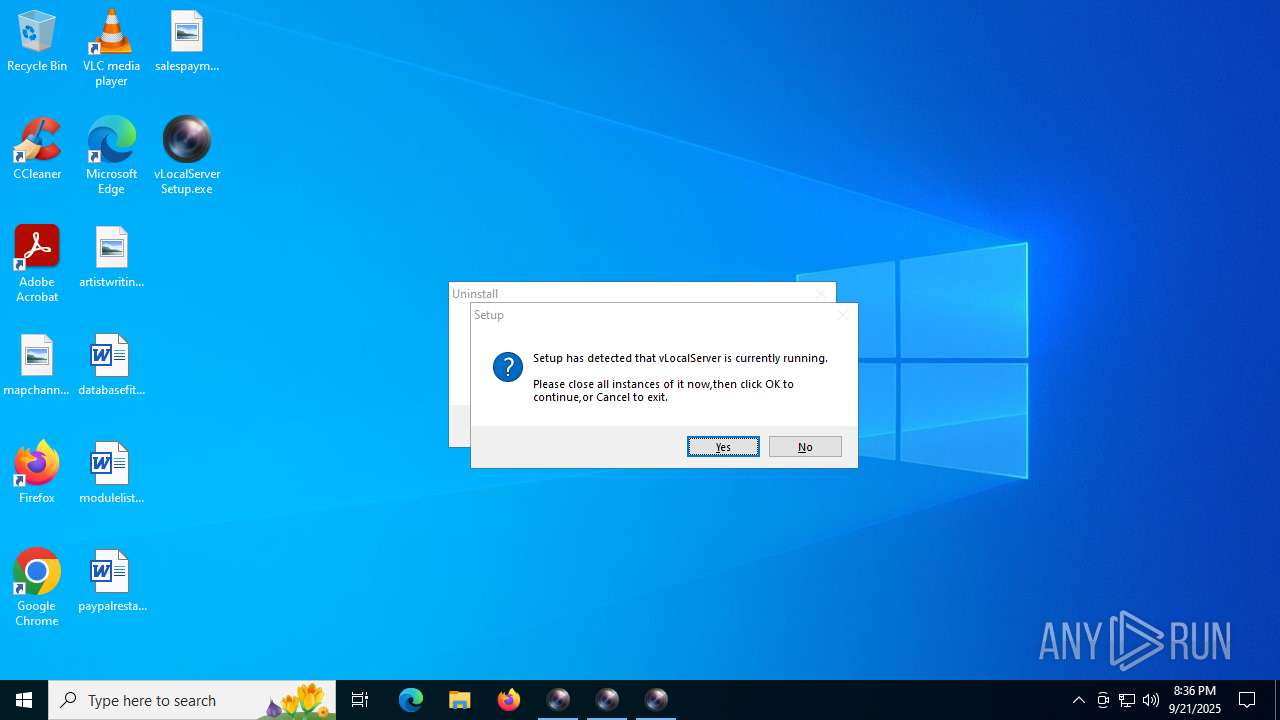
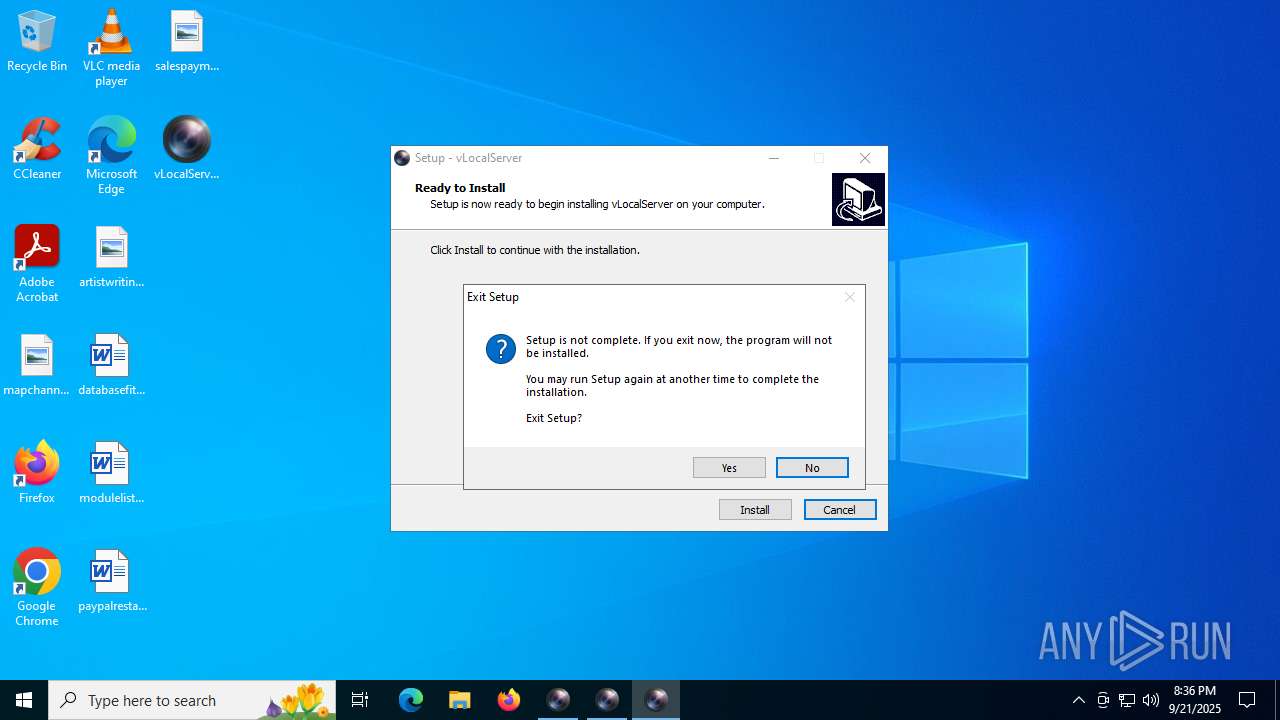
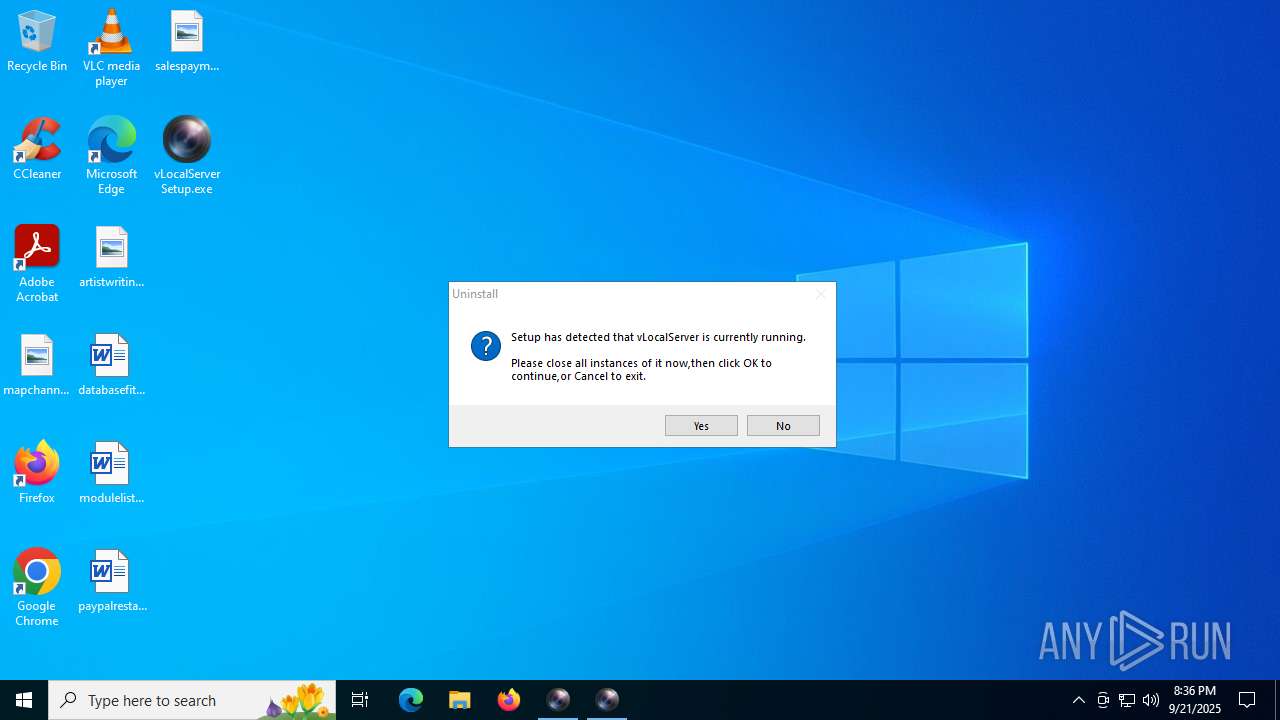
Uses TASKKILL.EXE to kill process
- vLocalServerSetup.tmp (PID: 3872)
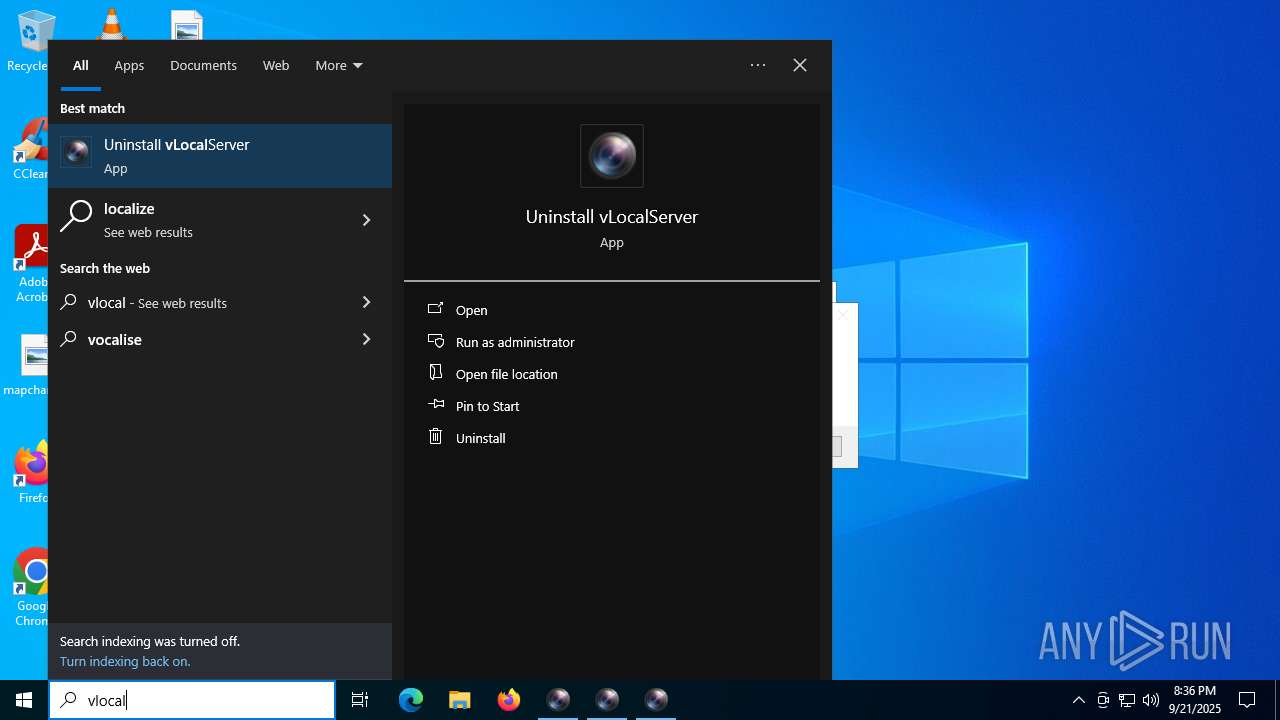
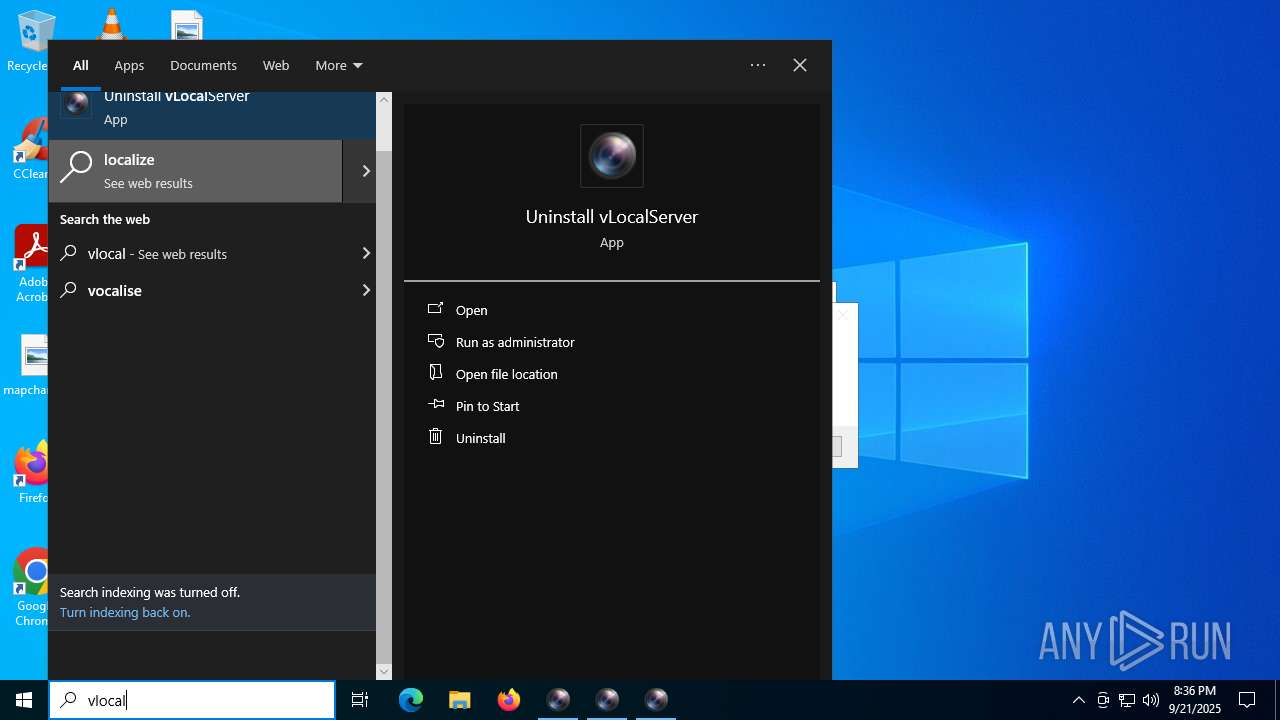
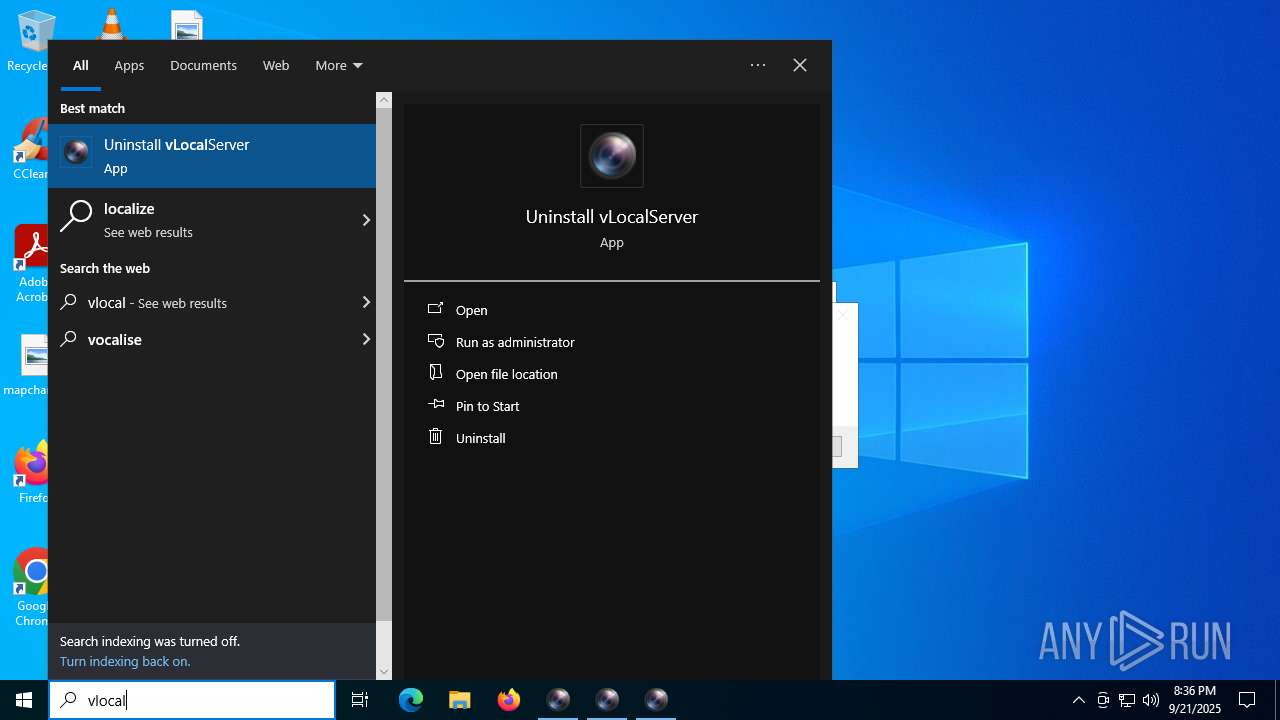
Searches for installed software
- vLocalServerSetup.tmp (PID: 3872)
- vLocalServerSetup.tmp (PID: 3840)
- vLocalServerSetup.tmp (PID: 6236)
Detected use of alternative data streams (AltDS)
- _iu14D2N.tmp (PID: 5184)
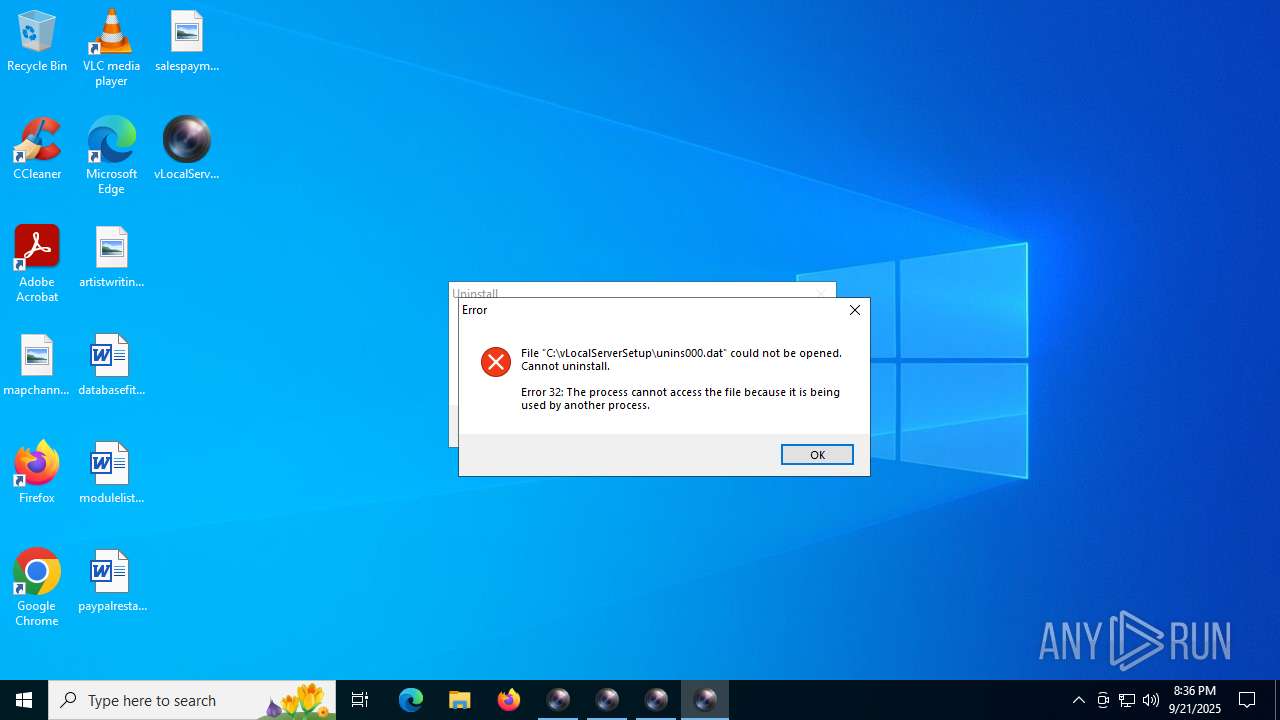
Starts application with an unusual extension
- unins000.exe (PID: 760)
- unins000.exe (PID: 4680)
Starts itself from another location
- unins000.exe (PID: 760)
- unins000.exe (PID: 4680)
INFO
Checks supported languages
- vLocalServerSetup.exe (PID: 6720)
- vLocalServerSetup.tmp (PID: 2804)
- vLocalServerSetup.exe (PID: 2216)
- vLocalServerSetup.tmp (PID: 5460)
- InstallCert.exe (PID: 2996)
- vLocalServerGuard.exe (PID: 1880)
- vLocalServer.exe (PID: 4072)
- vLocalServer.exe (PID: 4708)
- vLocalServerSetup.exe (PID: 2400)
- vLocalServerSetup.tmp (PID: 6164)
- unins000.exe (PID: 760)
- vLocalServerSetup.exe (PID: 4228)
- vLocalServerSetup.tmp (PID: 3872)
- _iu14D2N.tmp (PID: 5184)
- InstallCert.exe (PID: 5244)
- vLocalServer.exe (PID: 3876)
- vLocalServerGuard.exe (PID: 72)
- vLocalServer.exe (PID: 892)
- vLocalServerSetup.exe (PID: 6936)
- vLocalServerSetup.tmp (PID: 7000)
- vLocalServerSetup.exe (PID: 6876)
- vLocalServerSetup.tmp (PID: 3840)
- vLocalServerSetup.exe (PID: 684)
- vLocalServerSetup.tmp (PID: 6656)
- unins000.exe (PID: 4680)
- vLocalServerSetup.exe (PID: 4224)
- _iu14D2N.tmp (PID: 7132)
- vLocalServerSetup.tmp (PID: 6236)
- unins000.exe (PID: 5172)
Process checks computer location settings
- vLocalServerSetup.tmp (PID: 2804)
- InstallCert.exe (PID: 2996)
- vLocalServerGuard.exe (PID: 1880)
- vLocalServerSetup.tmp (PID: 6164)
- _iu14D2N.tmp (PID: 5184)
- InstallCert.exe (PID: 5244)
- vLocalServerGuard.exe (PID: 72)
- vLocalServerSetup.tmp (PID: 7000)
- vLocalServerSetup.tmp (PID: 6656)
- _iu14D2N.tmp (PID: 7132)
Create files in a temporary directory
- vLocalServerSetup.exe (PID: 6720)
- vLocalServerSetup.exe (PID: 2216)
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.exe (PID: 2400)
- vLocalServerSetup.tmp (PID: 3872)
- unins000.exe (PID: 760)
- vLocalServerSetup.exe (PID: 4228)
- _iu14D2N.tmp (PID: 5184)
- vLocalServerSetup.exe (PID: 6936)
- vLocalServerSetup.exe (PID: 6876)
- vLocalServerSetup.tmp (PID: 3840)
- vLocalServerSetup.exe (PID: 684)
- unins000.exe (PID: 4680)
- vLocalServerSetup.exe (PID: 4224)
- vLocalServerSetup.tmp (PID: 6236)
- _iu14D2N.tmp (PID: 7132)
Reads the computer name
- vLocalServerSetup.tmp (PID: 2804)
- vLocalServerSetup.tmp (PID: 5460)
- InstallCert.exe (PID: 2996)
- vLocalServerGuard.exe (PID: 1880)
- vLocalServer.exe (PID: 4072)
- vLocalServerSetup.tmp (PID: 6164)
- vLocalServerSetup.tmp (PID: 3872)
- unins000.exe (PID: 760)
- _iu14D2N.tmp (PID: 5184)
- InstallCert.exe (PID: 5244)
- vLocalServerGuard.exe (PID: 72)
- vLocalServer.exe (PID: 3876)
- vLocalServerSetup.tmp (PID: 3840)
- vLocalServerSetup.tmp (PID: 7000)
- vLocalServerSetup.tmp (PID: 6656)
- unins000.exe (PID: 4680)
- _iu14D2N.tmp (PID: 7132)
- vLocalServerSetup.tmp (PID: 6236)
- unins000.exe (PID: 5172)
The sample compiled with english language support
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.tmp (PID: 3872)
- _iu14D2N.tmp (PID: 5184)
- vLocalServerSetup.tmp (PID: 3840)
- _iu14D2N.tmp (PID: 7132)
- vLocalServerSetup.tmp (PID: 6236)
The sample compiled with russian language support
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.tmp (PID: 3872)
- vLocalServerSetup.tmp (PID: 3840)
- vLocalServerSetup.tmp (PID: 6236)
The sample compiled with chinese language support
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.tmp (PID: 3872)
The sample compiled with Italian language support
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.tmp (PID: 3872)
- vLocalServerSetup.tmp (PID: 3840)
- vLocalServerSetup.tmp (PID: 6236)
Detects InnoSetup installer (YARA)
- vLocalServerSetup.exe (PID: 6720)
- vLocalServerSetup.tmp (PID: 2804)
Launching a file from a Registry key
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.tmp (PID: 3872)
Creates a software uninstall entry
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.tmp (PID: 3872)
Creates files or folders in the user directory
- vLocalServerSetup.tmp (PID: 5460)
- vLocalServerSetup.tmp (PID: 3872)
Compiled with Borland Delphi (YARA)
- vLocalServerSetup.tmp (PID: 2804)
Reads the machine GUID from the registry
- vLocalServer.exe (PID: 4072)
- vLocalServer.exe (PID: 3876)
Checks proxy server information
- vLocalServer.exe (PID: 4072)
- vLocalServer.exe (PID: 3876)
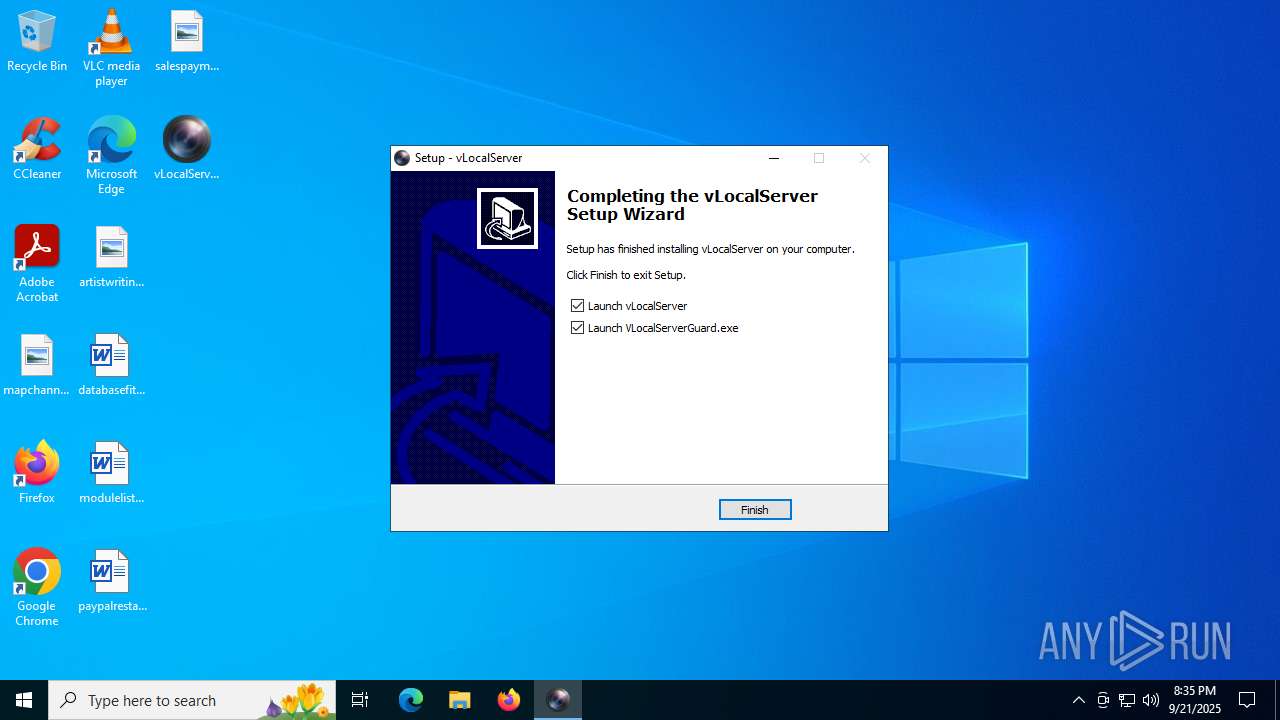
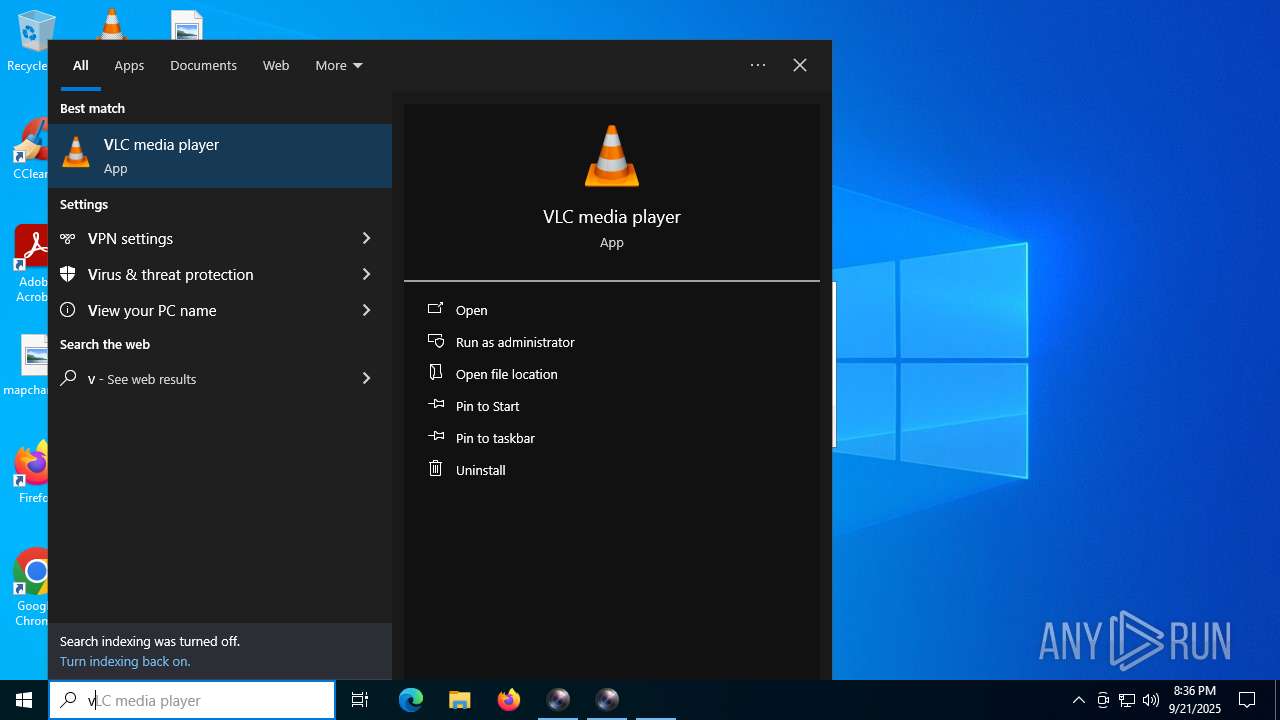
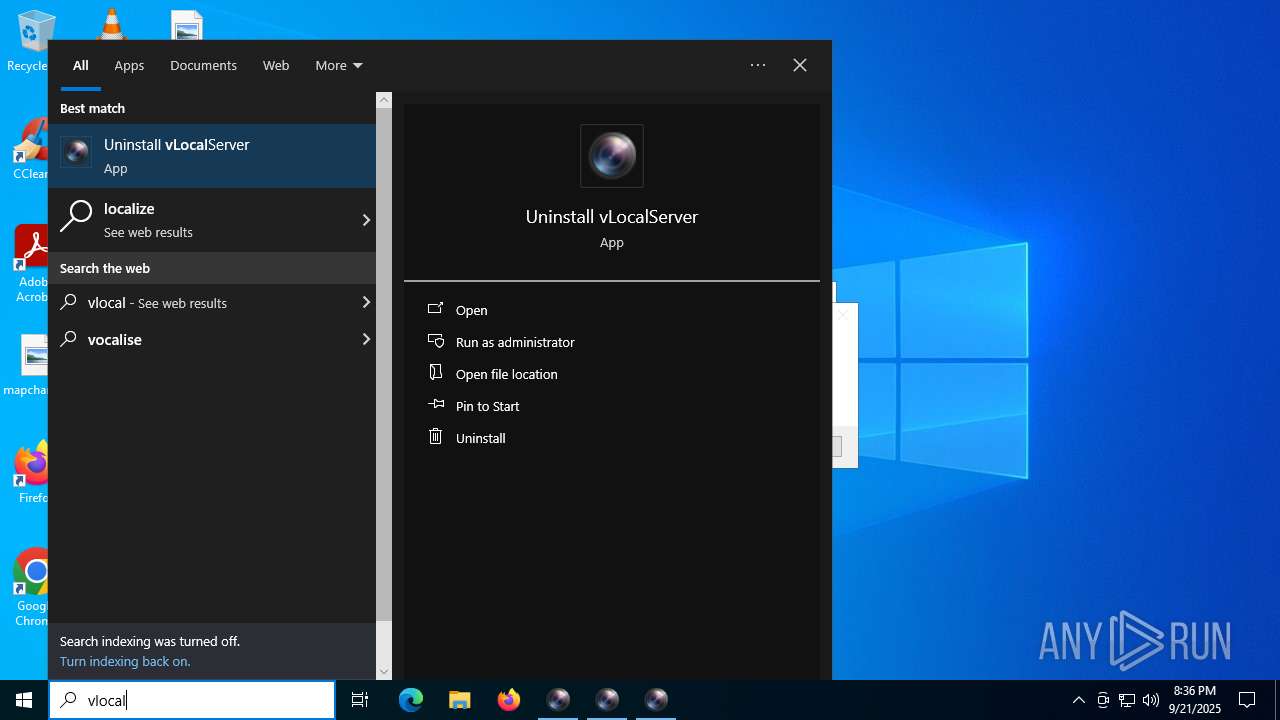
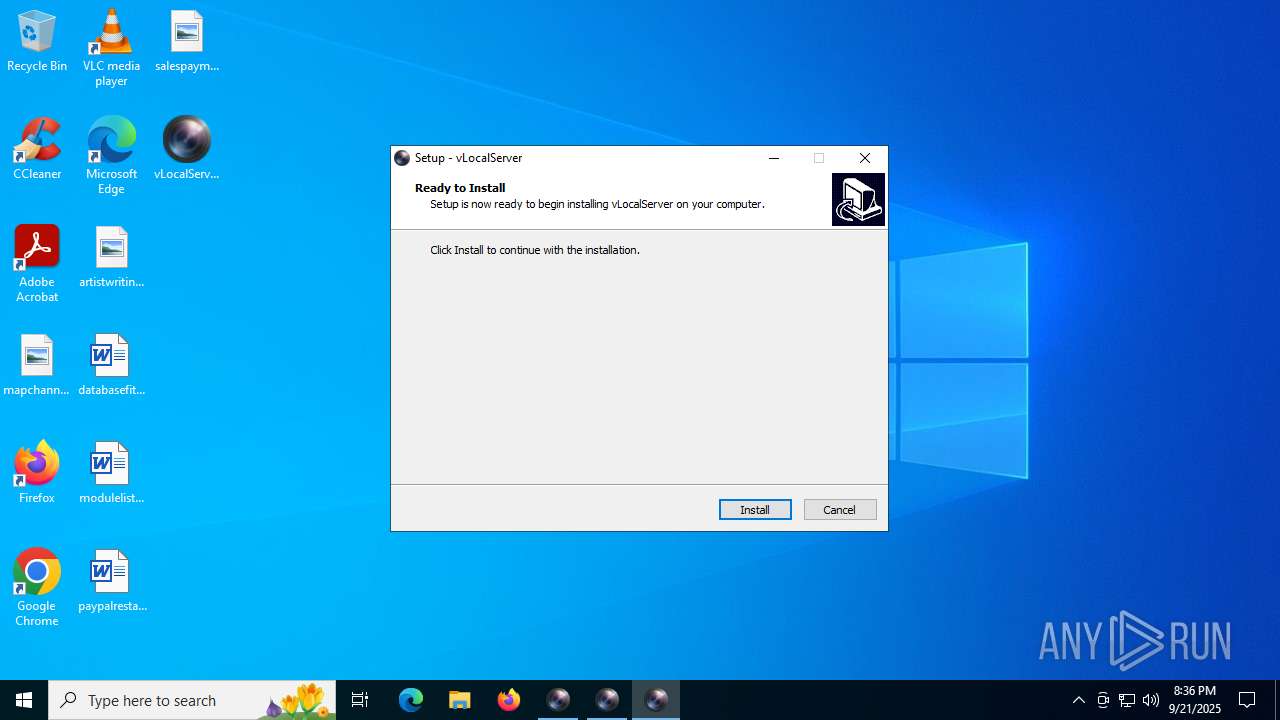
Manual execution by a user
- vLocalServerSetup.exe (PID: 2400)
- vLocalServerSetup.exe (PID: 6936)
- vLocalServerSetup.exe (PID: 684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40448 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f8 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | vLocalServer Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | vLocalServer |
| ProductVersion: | 1.0.23.79 |
Total processes
194
Monitored processes
54
Malicious processes
4
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 72 | "C:\vLocalServerSetup\vLocalServerGuard.exe" | C:\vLocalServerSetup\vLocalServerGuard.exe | vLocalServerSetup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 684 | "C:\Users\admin\Desktop\vLocalServerSetup.exe" | C:\Users\admin\Desktop\vLocalServerSetup.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: vLocalServer Setup Exit code: 2 Version: Modules
| |||||||||||||||
| 760 | "C:\vLocalServerSetup\unins000.exe" /silent | C:\vLocalServerSetup\unins000.exe | vLocalServerSetup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 892 | "C:\vLocalServerSetup\vLocalServer.exe" | C:\vLocalServerSetup\vLocalServer.exe | vLocalServerGuard.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225547 Modules
| |||||||||||||||
| 1132 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\vLocalServerSetup\VPlugin\VPlugin.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | vLocalServerSetup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1236 | "C:\Windows\System32\certutil.exe" -addstore -f Root C:\vLocalServerSetup\rootca.crt | C:\Windows\System32\certutil.exe | — | InstallCert.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | "regsvr32" /u /SILENT "C:\vLocalServerSetup"\VPlugin\VPlugin.dll | C:\Windows\SysWOW64\regsvr32.exe | — | _iu14D2N.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1380 | "regsvr32" /u /SILENT "C:\vLocalServerSetup"\VPlugin\VPlugin.dll | C:\Windows\SysWOW64\regsvr32.exe | — | _iu14D2N.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1828 | "taskkill" /PID 4072 /F | C:\Windows\SysWOW64\taskkill.exe | — | vLocalServerSetup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1880 | "C:\vLocalServerSetup\vLocalServerGuard.exe" | C:\vLocalServerSetup\vLocalServerGuard.exe | vLocalServerSetup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
6 859
Read events
6 748
Write events
52
Delete events
59
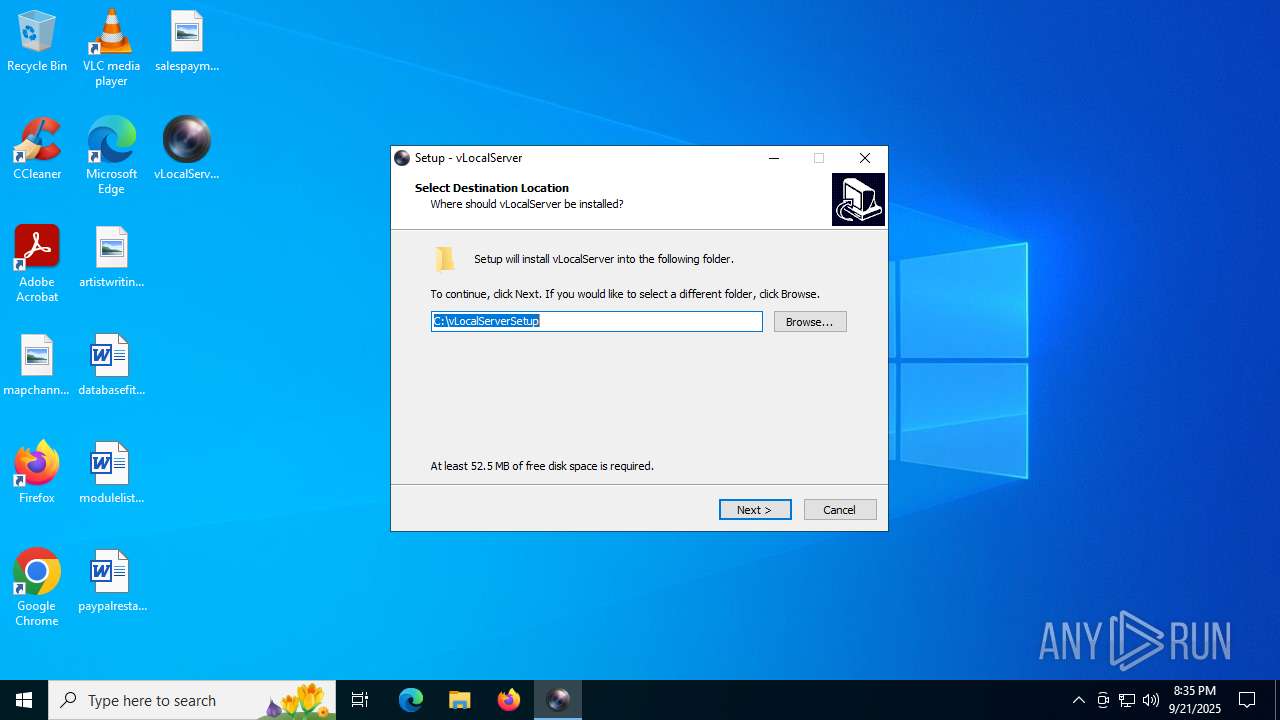
Modification events
| (PID) Process: | (5460) vLocalServerSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | vLocalServer |
Value: C:\vLocalServerSetup\vLocalServer.exe | |||
| (PID) Process: | (5460) vLocalServerSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | vLocalServerGuard |
Value: C:\vLocalServerSetup\VLocalServerGuard.exe | |||
| (PID) Process: | (5460) vLocalServerSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{AF447598-6779-4DB5-8555-B5855F84001B}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.8 (a) | |||
| (PID) Process: | (5460) vLocalServerSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{AF447598-6779-4DB5-8555-B5855F84001B}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\vLocalServerSetup | |||
| (PID) Process: | (5460) vLocalServerSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{AF447598-6779-4DB5-8555-B5855F84001B}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\vLocalServerSetup\ | |||
| (PID) Process: | (5460) vLocalServerSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{AF447598-6779-4DB5-8555-B5855F84001B}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (5460) vLocalServerSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{AF447598-6779-4DB5-8555-B5855F84001B}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (5460) vLocalServerSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{AF447598-6779-4DB5-8555-B5855F84001B}_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: english | |||
| (PID) Process: | (5460) vLocalServerSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{AF447598-6779-4DB5-8555-B5855F84001B}_is1 |
| Operation: | write | Name: | DisplayName |
Value: vLocalServer version 1.0.23.79 | |||
| (PID) Process: | (5460) vLocalServerSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{AF447598-6779-4DB5-8555-B5855F84001B}_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\vLocalServerSetup\unins000.exe" | |||
Executable files
278
Suspicious files
12
Text files
142
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2216 | vLocalServerSetup.exe | C:\Users\admin\AppData\Local\Temp\is-DS8AC.tmp\vLocalServerSetup.tmp | executable | |
MD5:CBDEC94F37FE967565C113EF0633DBC2 | SHA256:582F961579F05C0AF80988D9D98713A84B7FFCEF48CBB7FFD386CC7C47C2BF9A | |||
| 5460 | vLocalServerSetup.tmp | C:\vLocalServerSetup\unins000.exe | executable | |
MD5:5F4844DB9ED055152A4B9AE021FECBE9 | SHA256:71E7C624917BAC90EF0E19BD53EF4218507D75DA2454FE8D503D72AF9E394424 | |||
| 6720 | vLocalServerSetup.exe | C:\Users\admin\AppData\Local\Temp\is-EE2QB.tmp\vLocalServerSetup.tmp | executable | |
MD5:CBDEC94F37FE967565C113EF0633DBC2 | SHA256:582F961579F05C0AF80988D9D98713A84B7FFCEF48CBB7FFD386CC7C47C2BF9A | |||
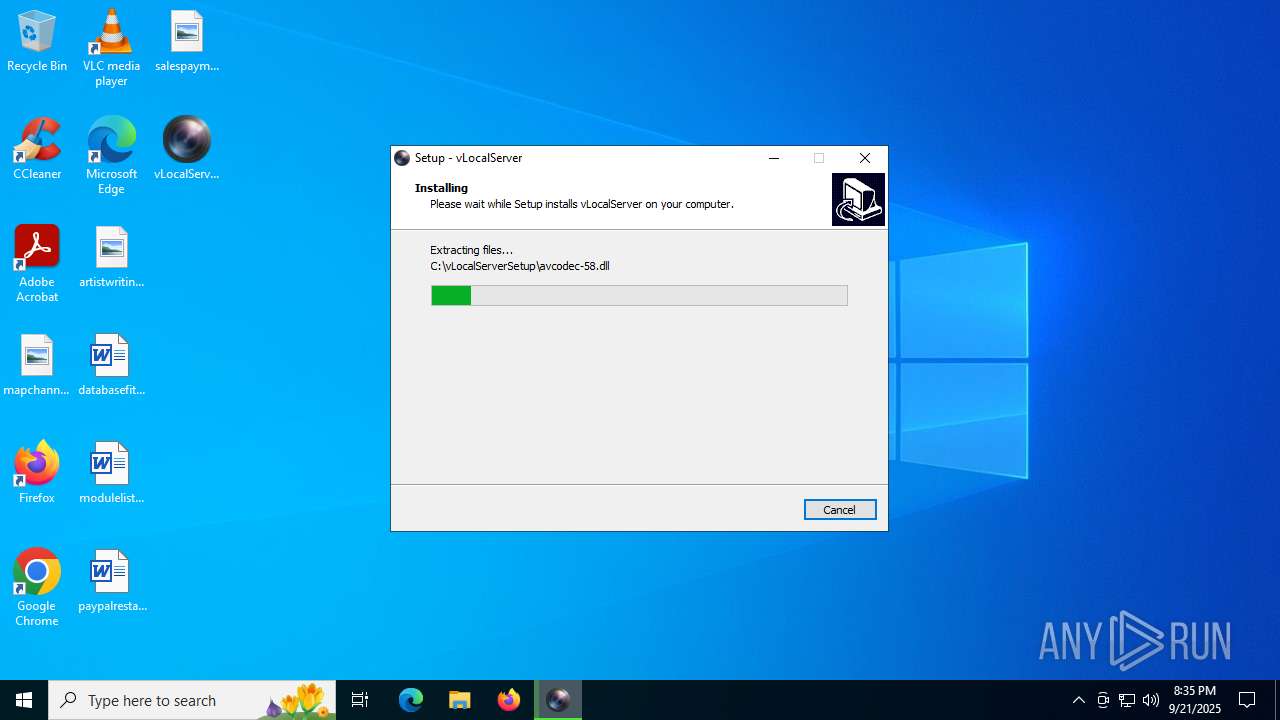
| 5460 | vLocalServerSetup.tmp | C:\vLocalServerSetup\avcodec-58.dll | executable | |
MD5:48EF2A5DF80580F298BC0368464D185C | SHA256:3287BEB59F157F2EE6F2BAB8143E0810753E1B5D9BD402D4E314C8EF13F0BA12 | |||
| 5460 | vLocalServerSetup.tmp | C:\Users\admin\AppData\Local\Temp\is-QESDH.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 5460 | vLocalServerSetup.tmp | C:\Users\admin\AppData\Local\Temp\is-QESDH.tmp\ISTask.dll | executable | |
MD5:86A1311D51C00B278CB7F27796EA442E | SHA256:E916BDF232744E00CBD8D608168A019C9F41A68A7E8390AA48CFB525276C483D | |||
| 5460 | vLocalServerSetup.tmp | C:\vLocalServerSetup\is-HGNVQ.tmp | executable | |
MD5:48EF2A5DF80580F298BC0368464D185C | SHA256:3287BEB59F157F2EE6F2BAB8143E0810753E1B5D9BD402D4E314C8EF13F0BA12 | |||
| 5460 | vLocalServerSetup.tmp | C:\vLocalServerSetup\is-M51AO.tmp | binary | |
MD5:5ABE28938437BDE310CCFC4595CD8D91 | SHA256:5F07EB286B034F84E064715E698BE99E1BA0A504BBBCE36A3B57CBE7BD58EAC1 | |||
| 5460 | vLocalServerSetup.tmp | C:\Users\admin\AppData\Local\Temp\is-QESDH.tmp\psvince.dll | executable | |
MD5:C413EE1A8BE7906F98D681E831026692 | SHA256:7250D7A3E3DA906147FA01FE6AC0BAC6B1B16E1B27A1D4D8D4EB00422C2D9A4D | |||
| 5460 | vLocalServerSetup.tmp | C:\vLocalServerSetup\is-HCCGC.tmp | executable | |
MD5:2E6C71C58FDE02F84186B2C2F8B04B14 | SHA256:35BDE72A167C2353AAD625382882CD122B71F7A84B7D1DD9F4D89D4840608101 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
55
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2064 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3052 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3052 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3052 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
3052 | SIHClient.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
3052 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
3052 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
3052 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6240 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.32.238.107:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4072 | vLocalServer.exe | 54.36.172.198:8300 | api.qvcloud.net | — | — | unknown |
4072 | vLocalServer.exe | 185.137.234.93:8300 | api.qvcloud.net | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
api.qvcloud.net |
| unknown |
kenik.qvcloud.net |
| unknown |
mqttsr5.qvcloud.net |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
vLocalServerGuard.exe | C:\vLocalServerSetup\vLocalServer.exe |
vLocalServer.exe | [20:35:40.988] IHTTPSocketSSL::HTTPSInitialize(44)--------------->OK.
|
vLocalServer.exe | [20:35:40.988] [NETCOM] PipeEventWatcher::DoInit() GetPortId == 1e,GetSocketFd == 964
|
vLocalServer.exe | [20:35:40.988] [NETCOM] PipeEventWatcher::DoInit() GetPortId == 1f,GetSocketFd == 1044
|
vLocalServer.exe | [20:35:40.988] [NETCOM] PipeEventWatcher::DoInit() GetPortId == 20,GetSocketFd == 1088
|
vLocalServer.exe | [20:35:40.988] [NETCOM] PipeEventWatcher::DoInit() GetPortId == 21,GetSocketFd == 1132
|
vLocalServer.exe | [20:35:40.988] [NETCOM] PipeEventWatcher::DoInit() GetPortId == 22,GetSocketFd == 1176
|
vLocalServer.exe | [20:35:40.988] [NETCOM] PipeEventWatcher::DoInit() GetPortId == 23,GetSocketFd == 1244
|
vLocalServer.exe | [20:35:41.004] [APPCLIENT] MqttConnect::OnResource re_time_ == 0
|
vLocalServer.exe | [20:35:41.004] [APPCLIENT] AppClientService::Init ============> ok .
|