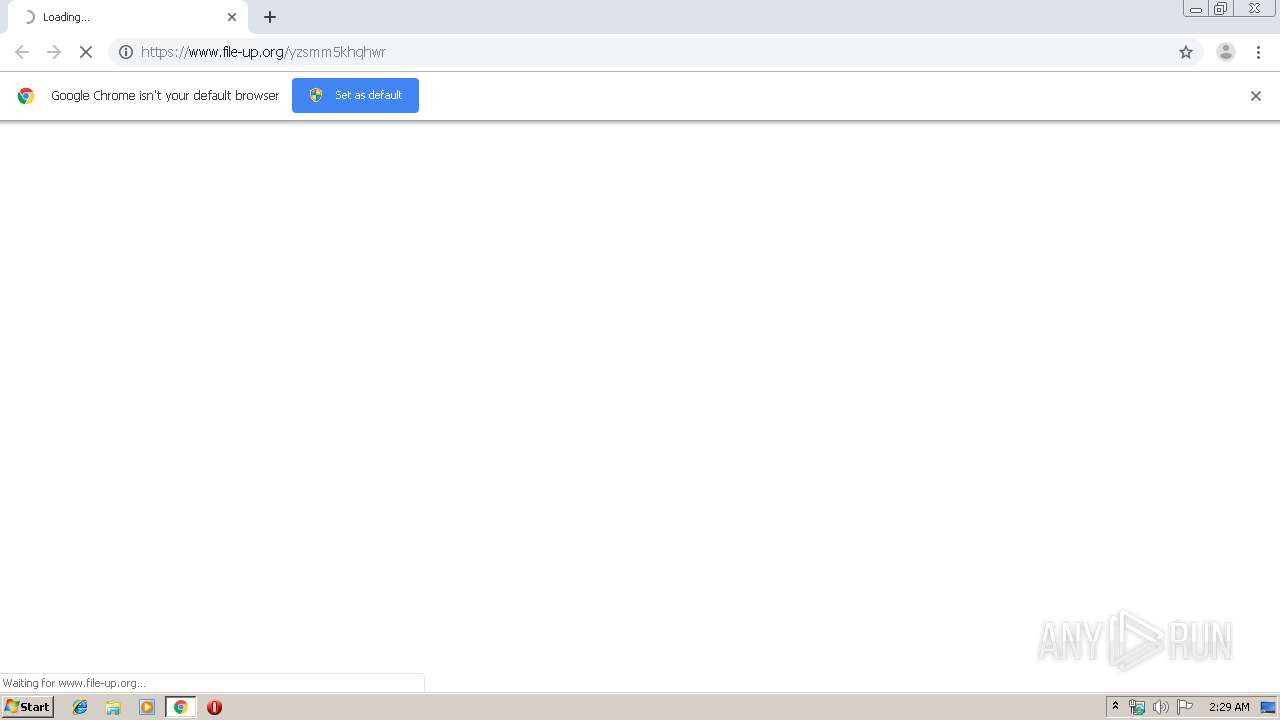
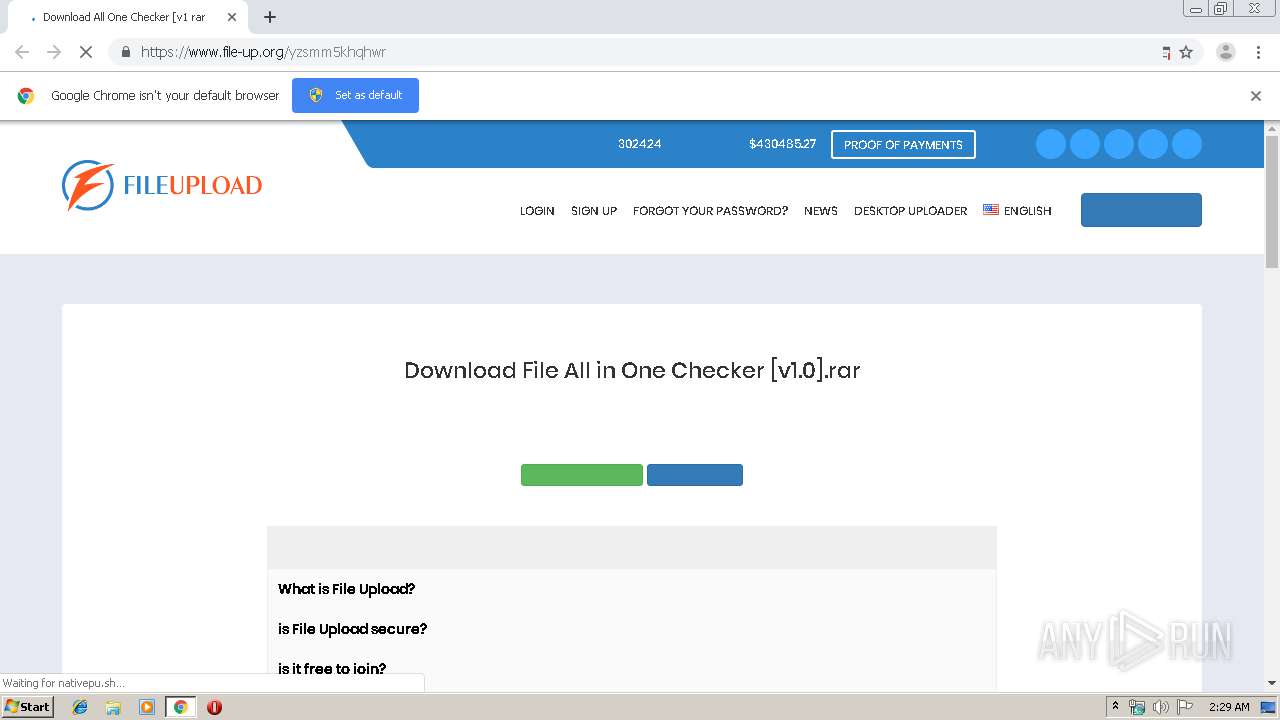
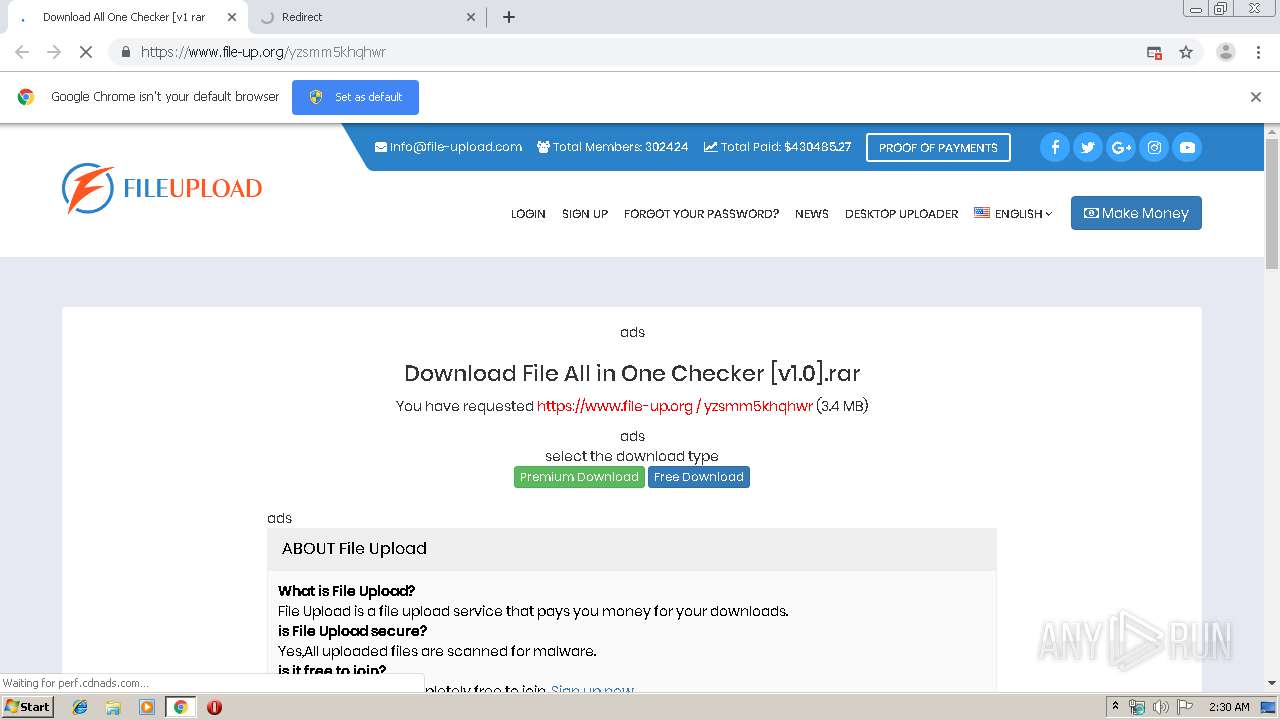
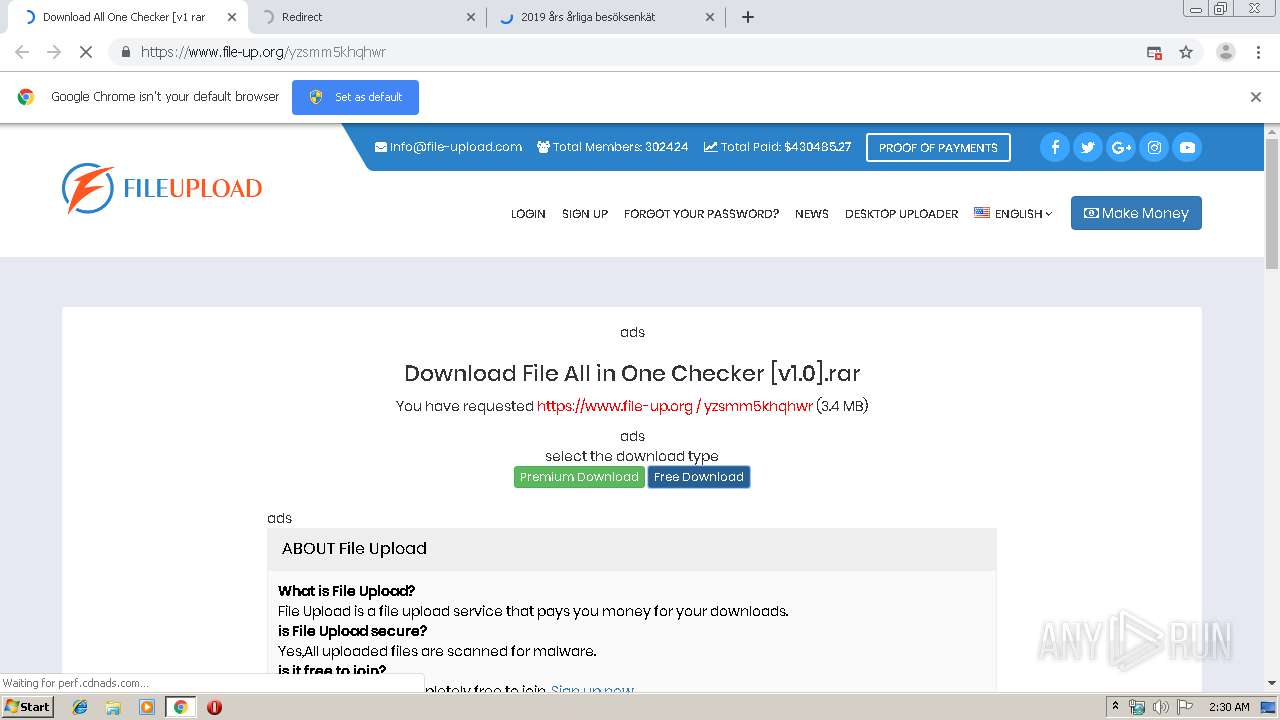
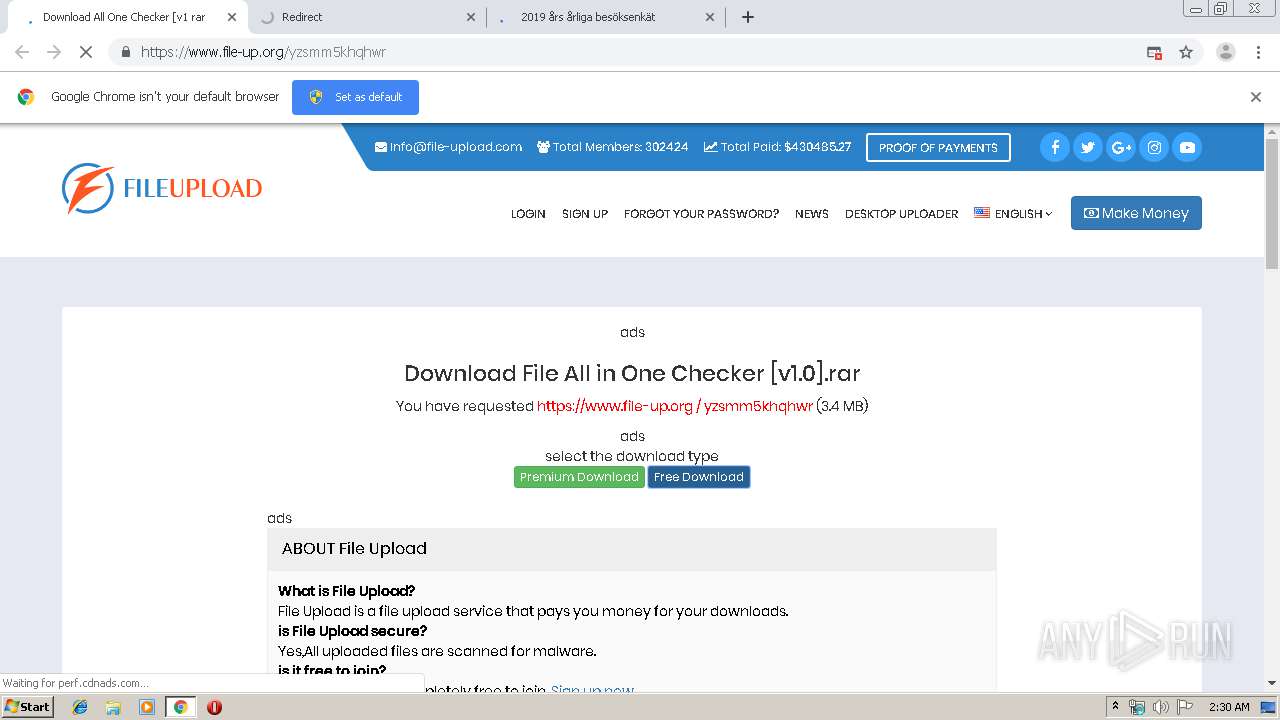
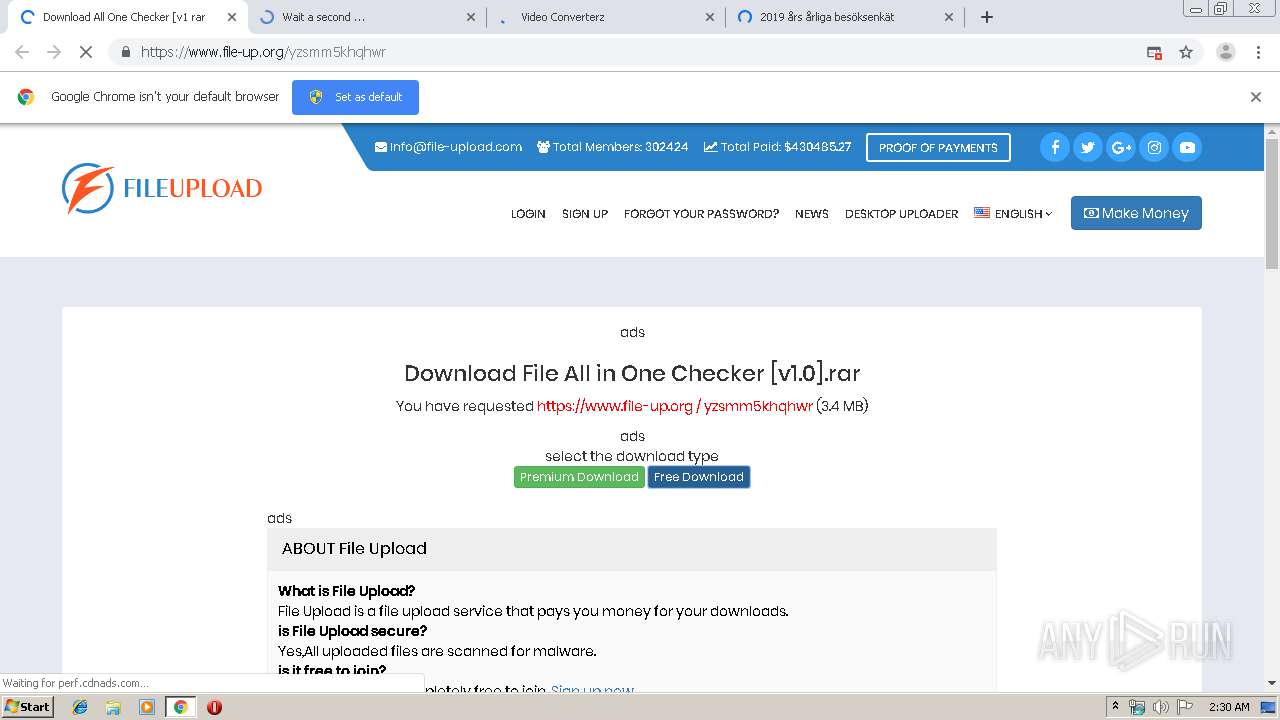
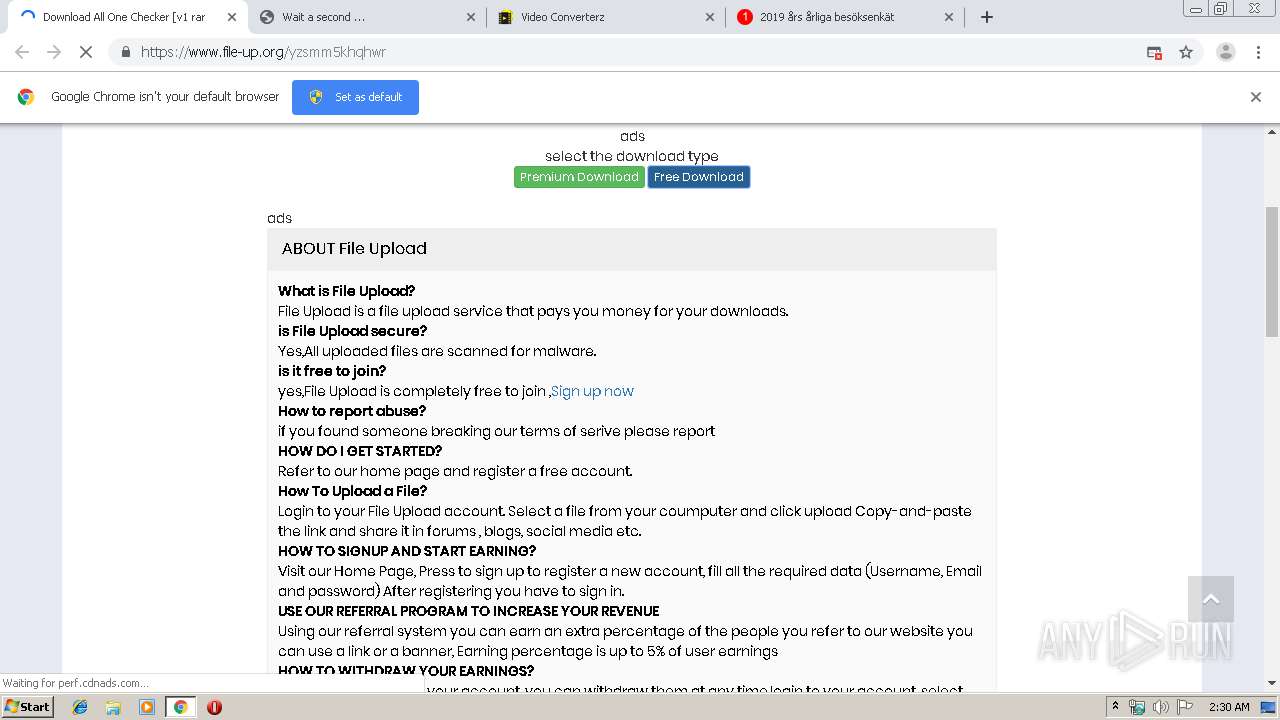
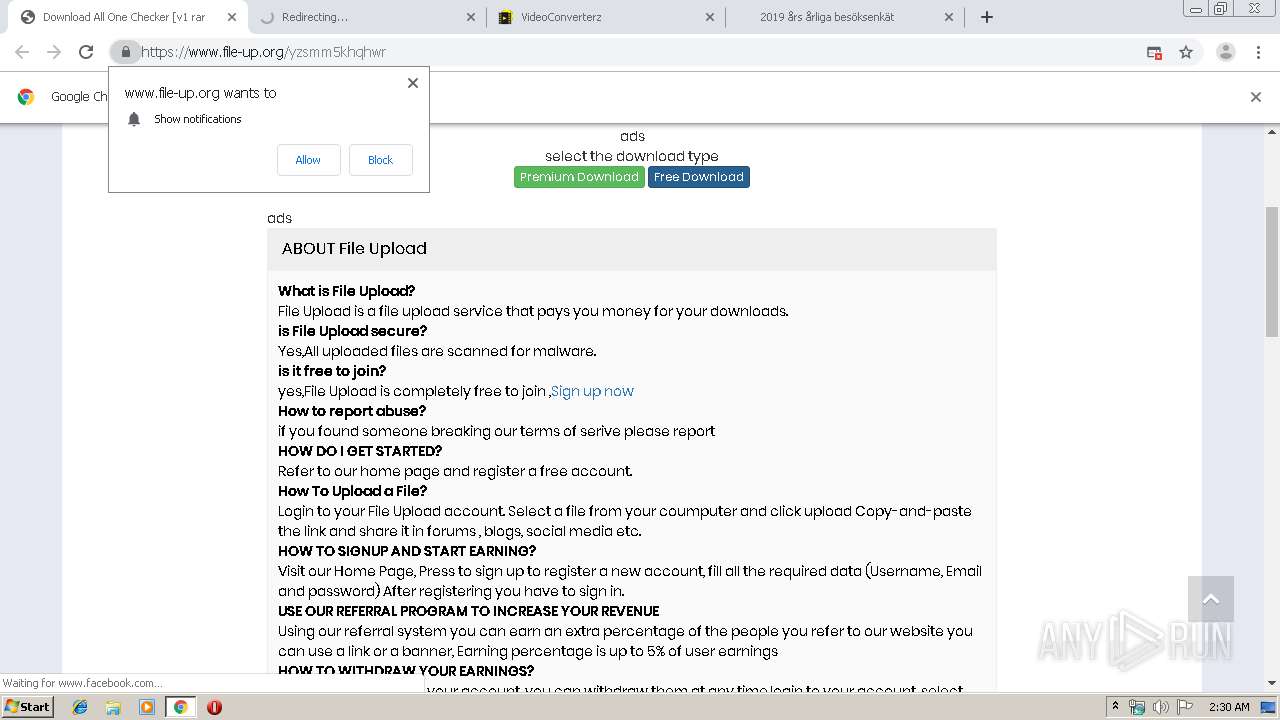
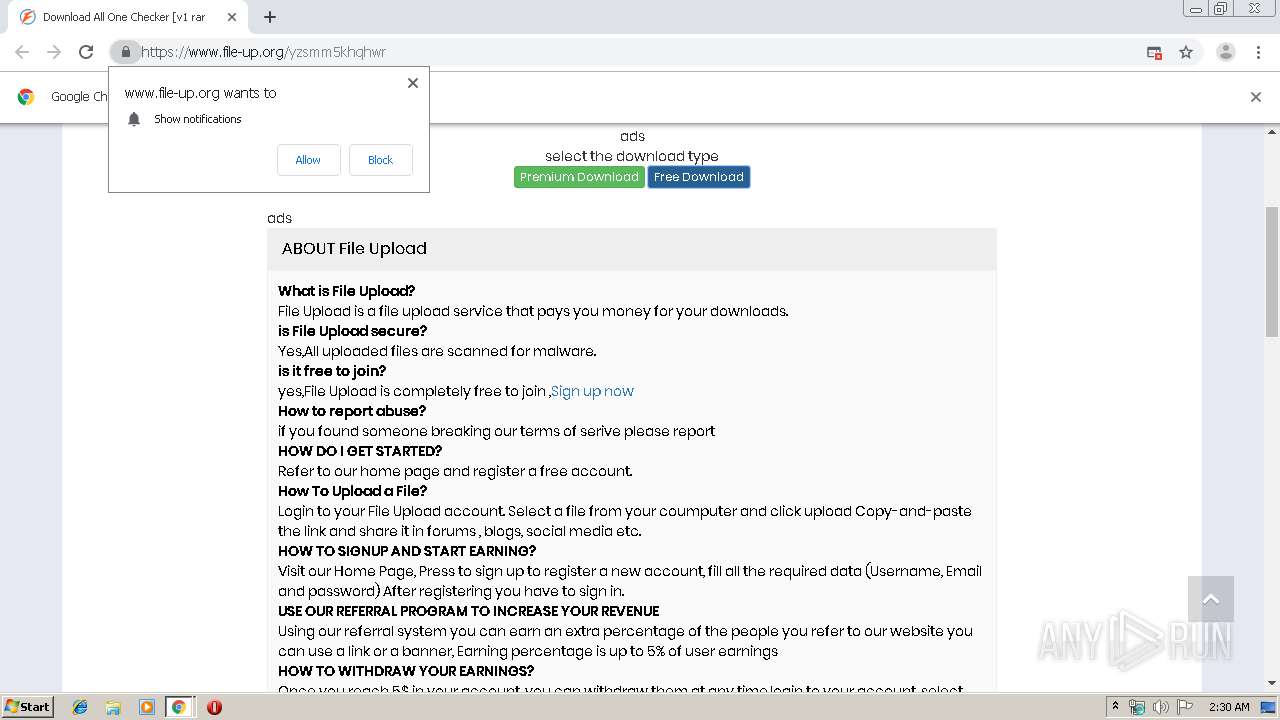
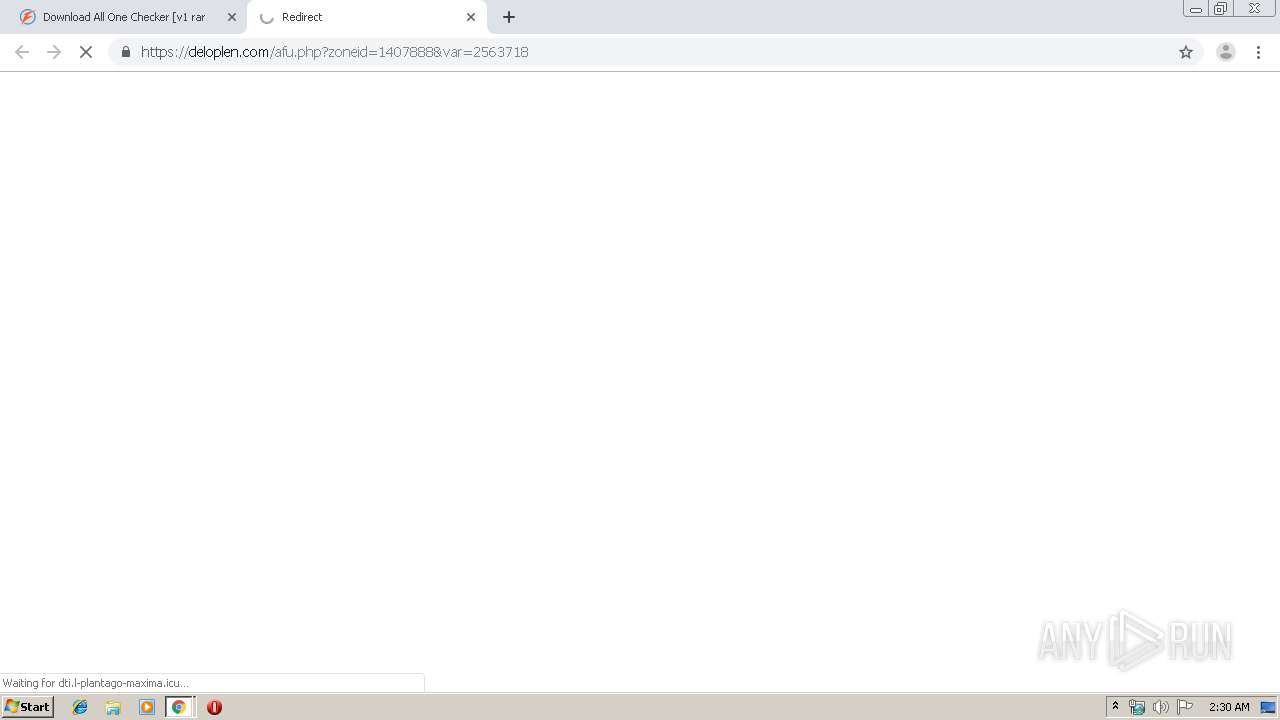
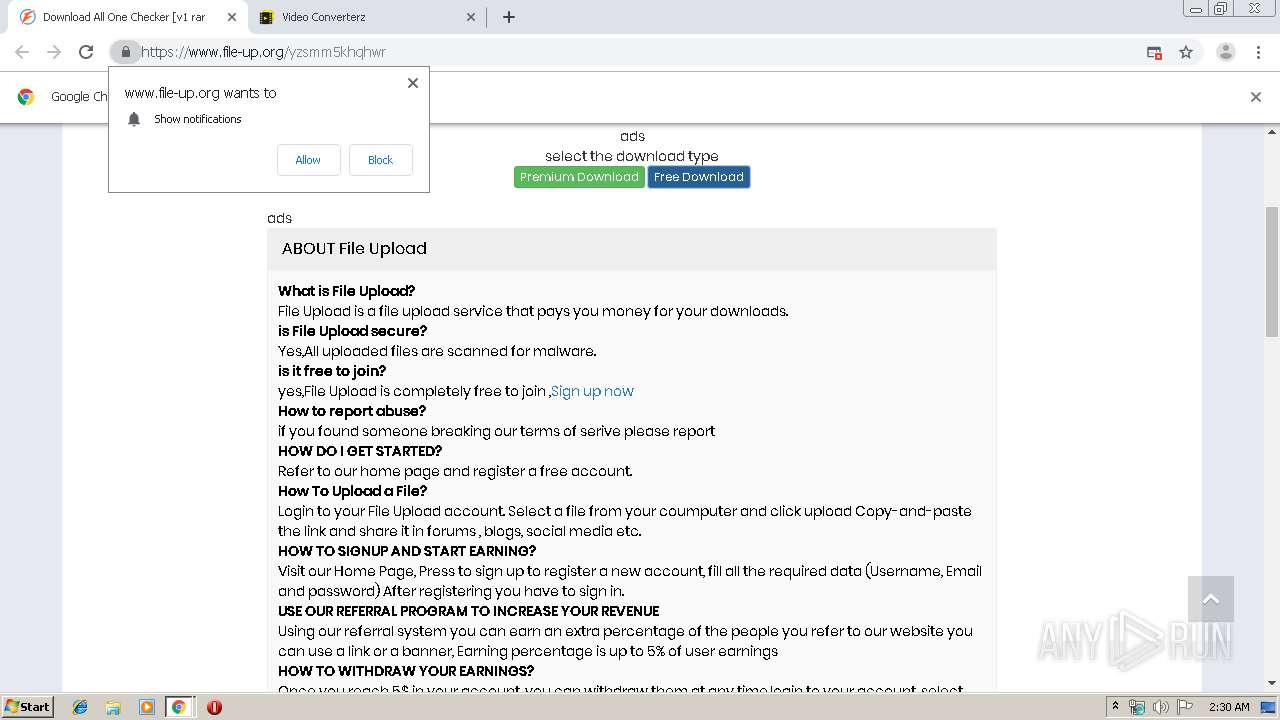
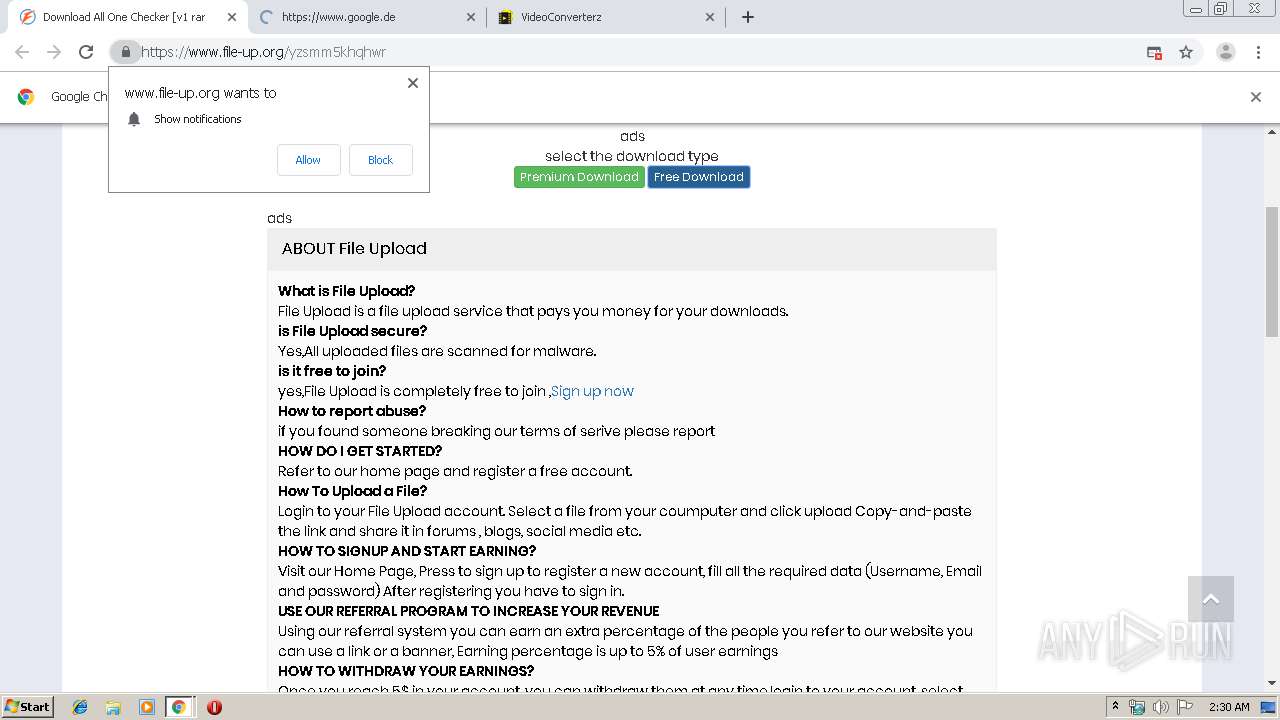
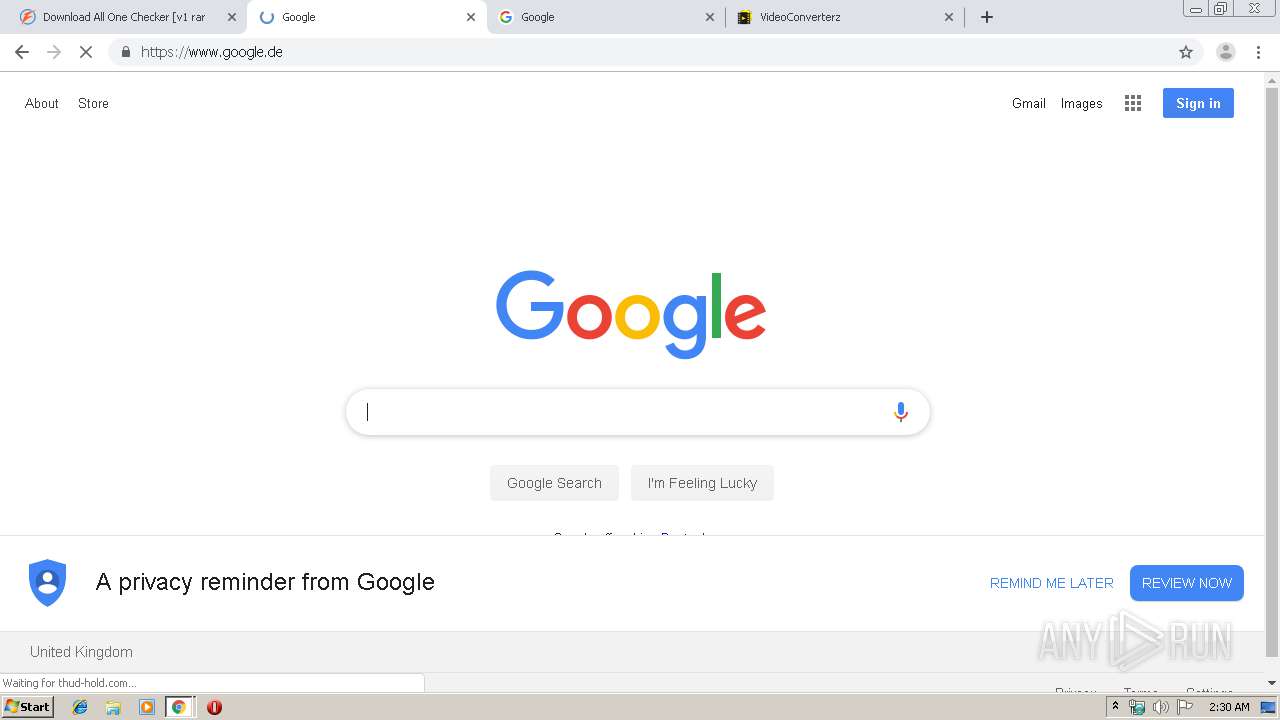
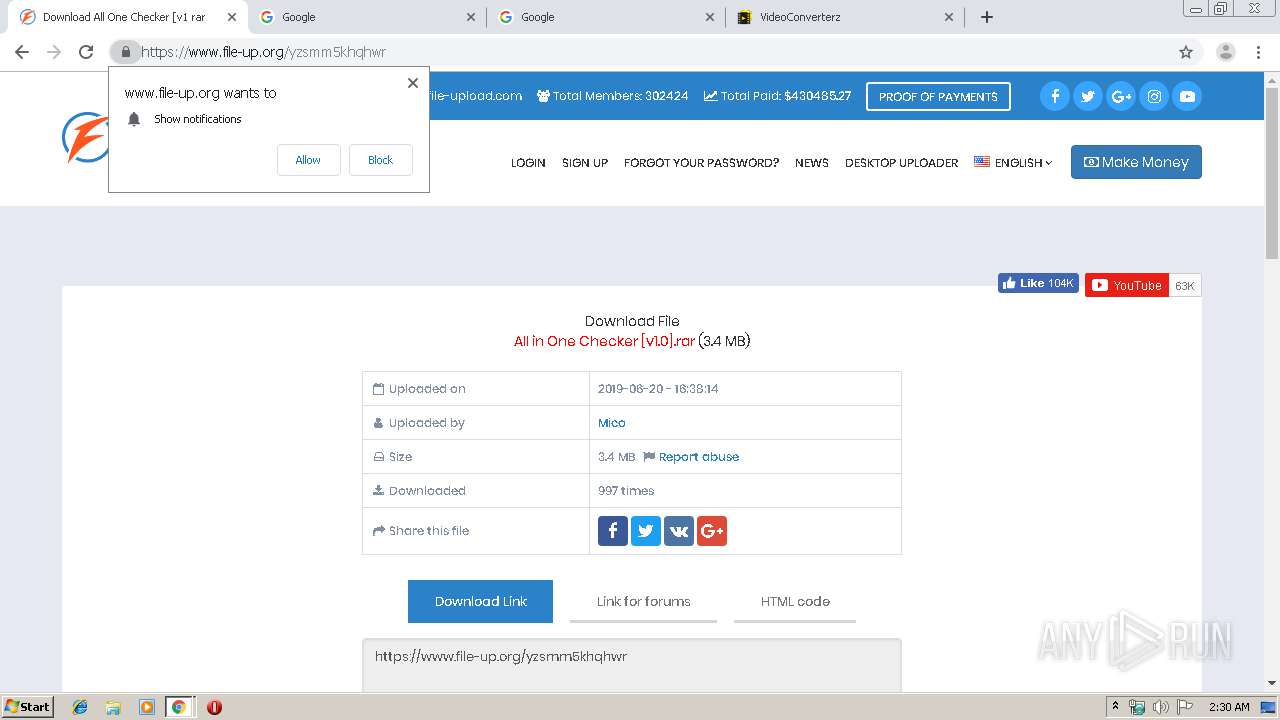
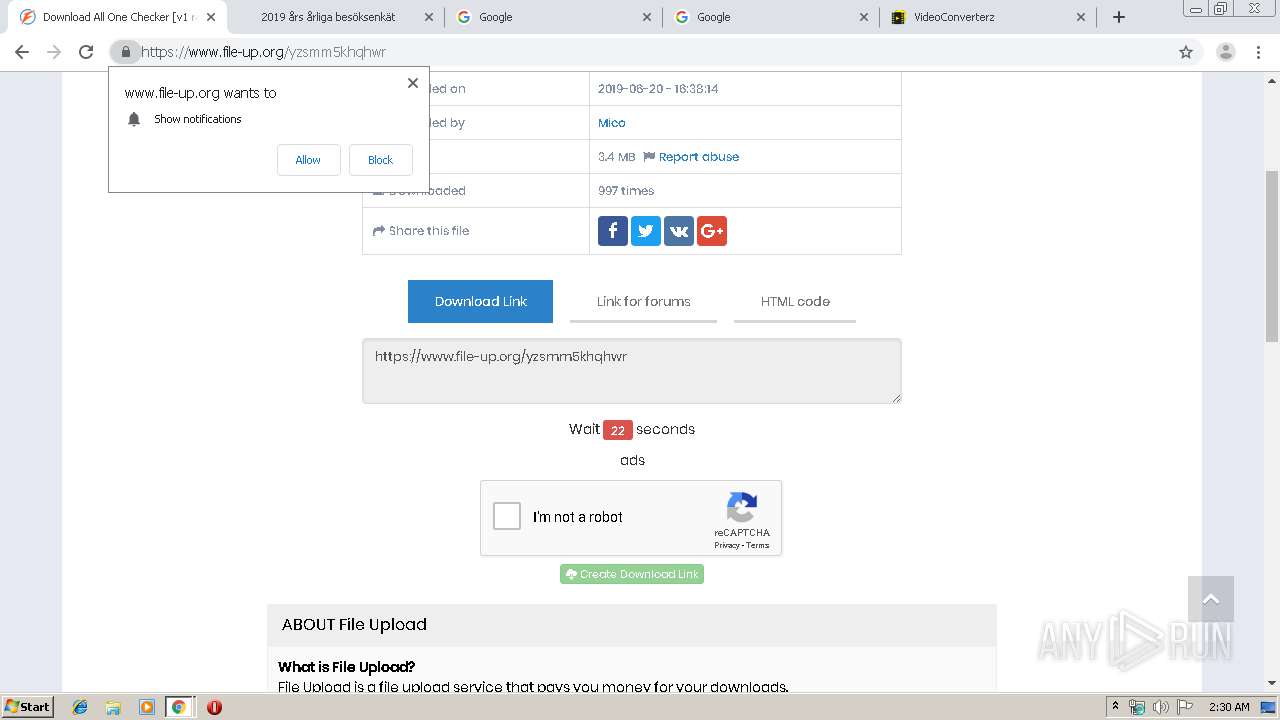
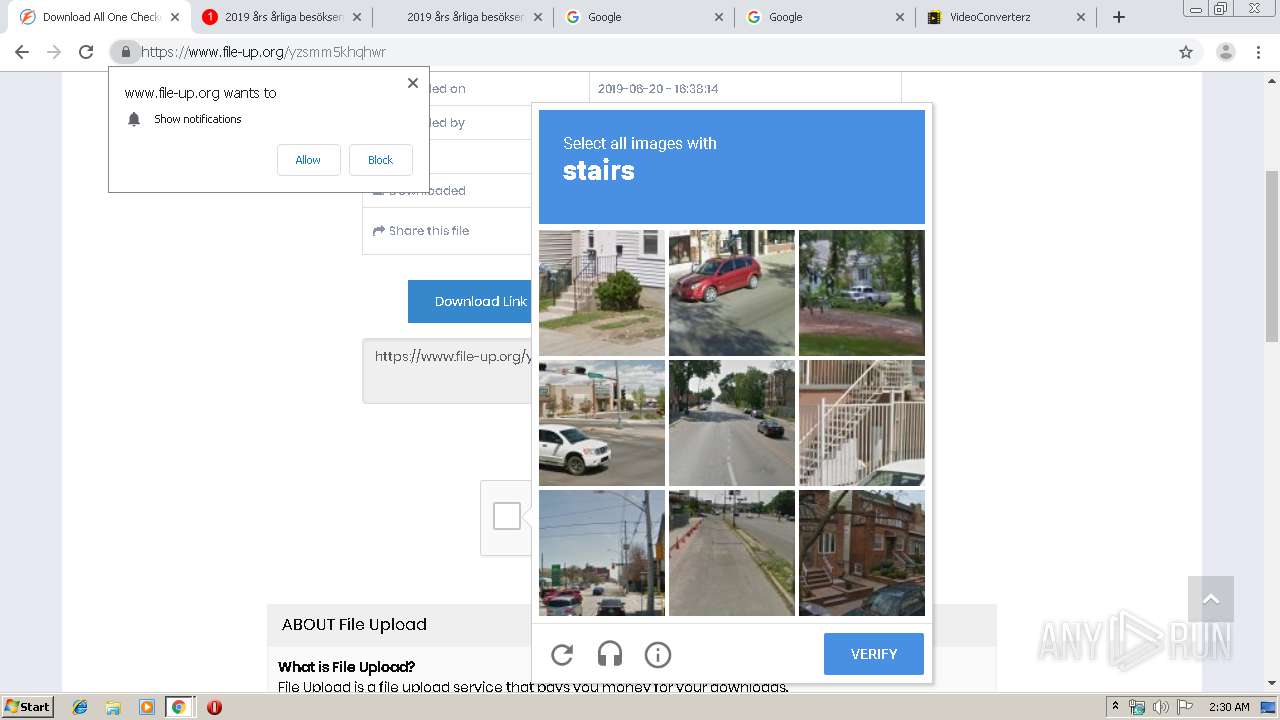
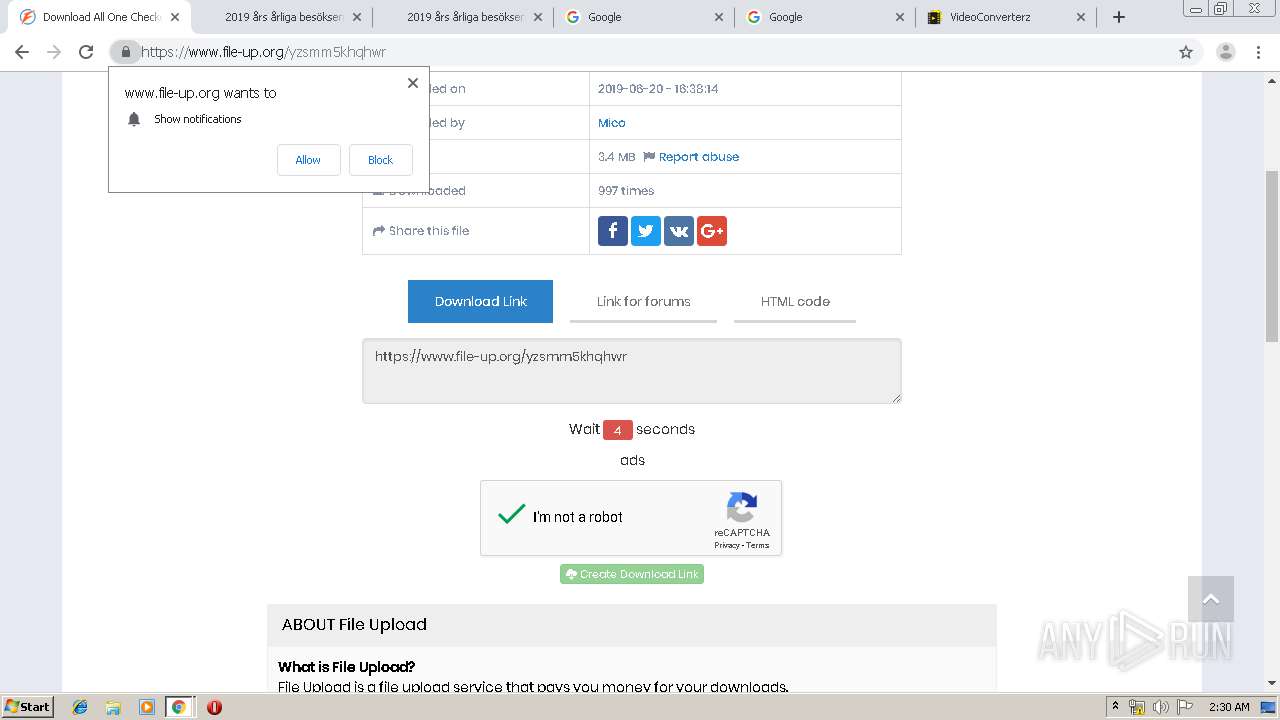
| URL: | https://www.file-up.org/yzsmm5khqhwr |
| Full analysis: | https://app.any.run/tasks/02dca852-de1a-439c-b001-5cca3fff1d5f |
| Verdict: | Malicious activity |
| Analysis date: | August 18, 2019, 01:29:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2AE9703E02967A560BF795C7C8E57A97 |
| SHA1: | CFC241C55110793D904414B34C4BBFFA90C270B5 |
| SHA256: | 116ECBB3C8B4906C01447013F92BE5D24B2E9EB2759C18736157EC674C475141 |
| SSDEEP: | 3:N8DSLQnFCkn:2OLQnFTn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3564)
INFO
Application launched itself
- chrome.exe (PID: 3564)
Dropped object may contain TOR URL's
- chrome.exe (PID: 3564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
84
Monitored processes
50
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15769221253400577932 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3164287282710611181 --renderer-client-id=43 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6029950419783397475 --mojo-platform-channel-handle=1516 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8298835695216394735 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4764 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fe6a9d0,0x6fe6a9e0,0x6fe6a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6345111580249415586 --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5736 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13118207877700522842 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16568259987828645101 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16049814544489322923 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,9971679469583064978,4665624506560870971,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17728379589186107264 --mojo-platform-channel-handle=5344 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
650
Read events
535
Write events
110
Delete events
5
Modification events
| (PID) Process: | (3564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3564-13210565394952875 |
Value: 259 | |||
| (PID) Process: | (3564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3564) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
139
Text files
210
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\55b0cb45-eca1-4305-a928-ee568982a832.tmp | — | |
MD5:— | SHA256:— | |||
| 3564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF169c44.TMP | text | |
MD5:— | SHA256:— | |||
| 3564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169c06.TMP | text | |
MD5:— | SHA256:— | |||
| 3564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
60
TCP/UDP connections
117
DNS requests
69
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2060 | chrome.exe | GET | 200 | 2.16.106.233:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.6 Kb | whitelisted |
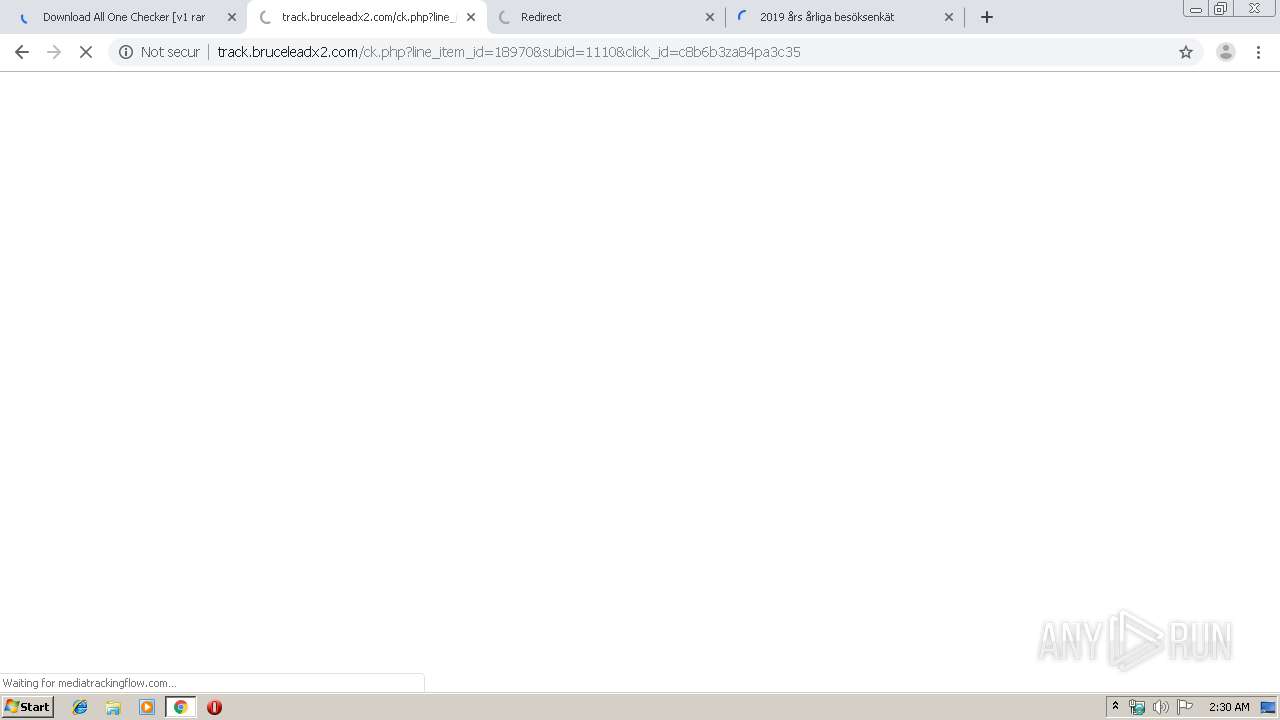
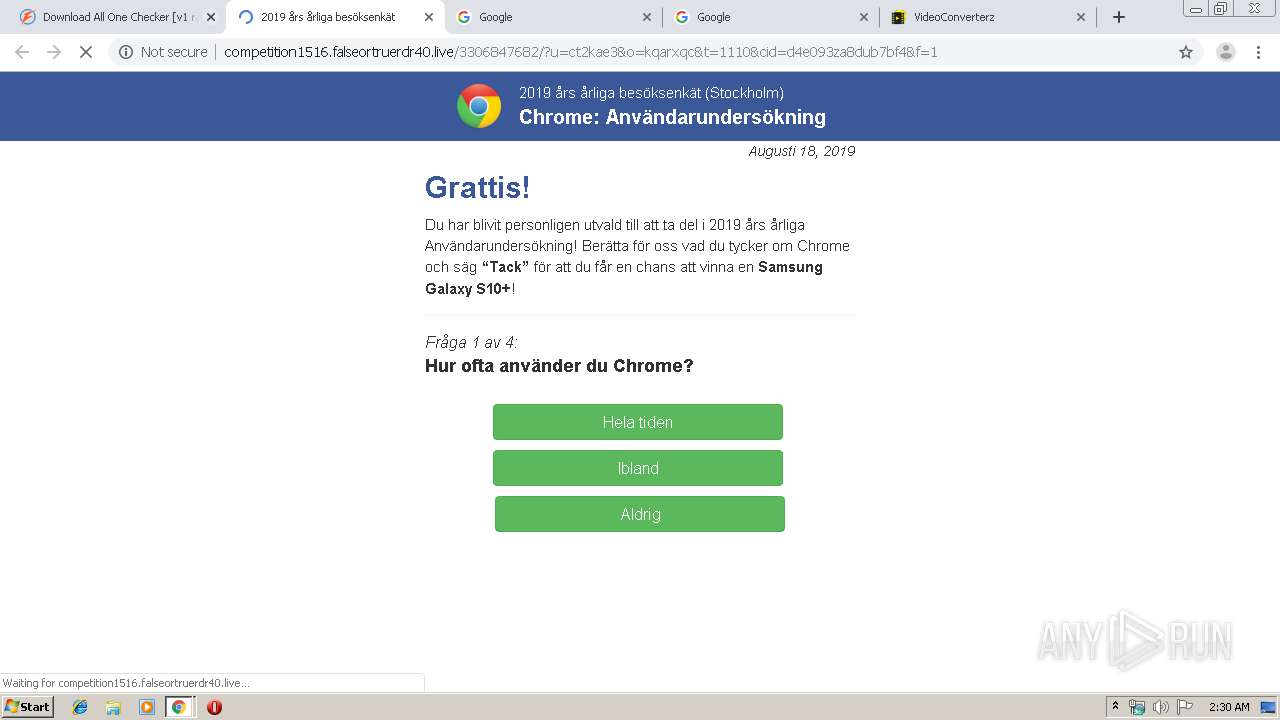
2060 | chrome.exe | GET | 200 | 79.110.23.105:80 | http://competition1516.falseortruerdr40.live/media/mainstream/se/wap/mobsurvey/main.css | RO | text | 10.0 Kb | suspicious |
2060 | chrome.exe | GET | 200 | 79.110.23.105:80 | http://competition1516.falseortruerdr40.live/media/mainstream/se/wap/mobsurvey/font-awesome.css | RO | text | 17.2 Kb | suspicious |
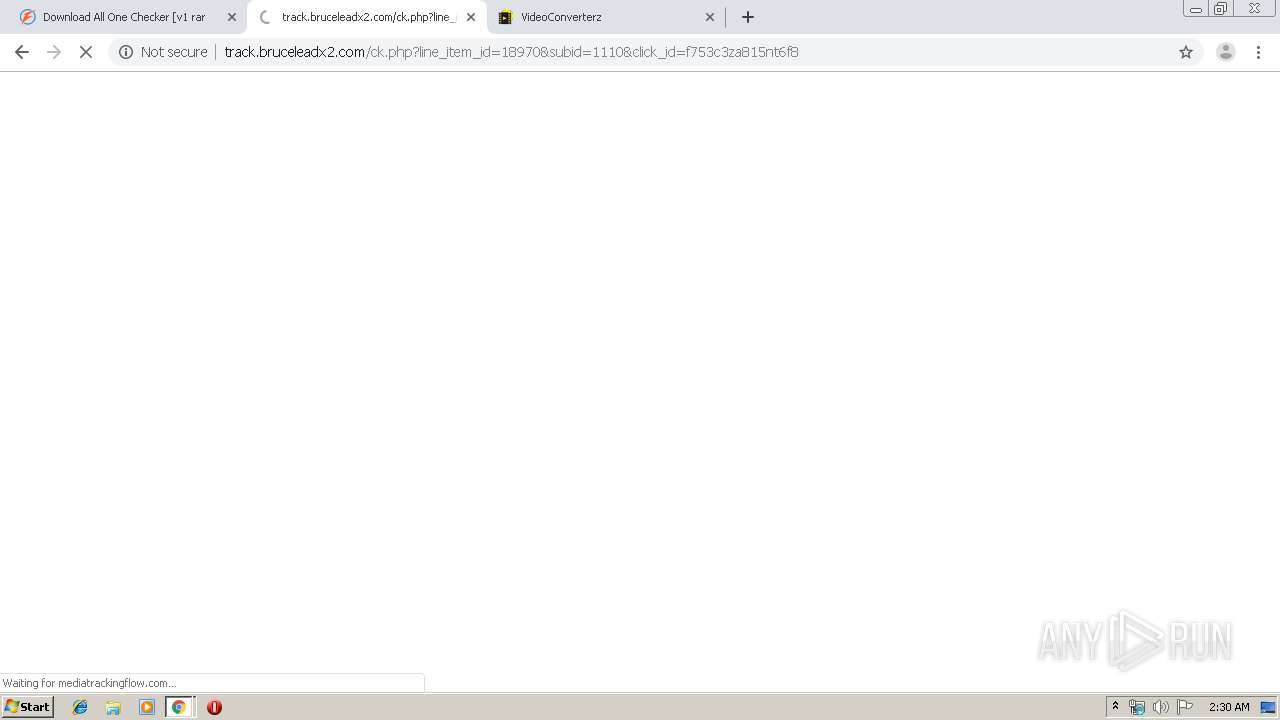
2060 | chrome.exe | GET | 200 | 79.110.23.105:80 | http://competition1516.falseortruerdr40.live/2853637370/?u=ct2kae3&o=kqarxqc&t=1110&cid=609d13za8ktikf01&f=1 | RO | html | 16.7 Kb | suspicious |
2060 | chrome.exe | GET | 200 | 79.110.23.105:80 | http://competition1516.falseortruerdr40.live/media/mainstream/us/wap/mobsurvey/comment.js | RO | text | 2.77 Kb | suspicious |
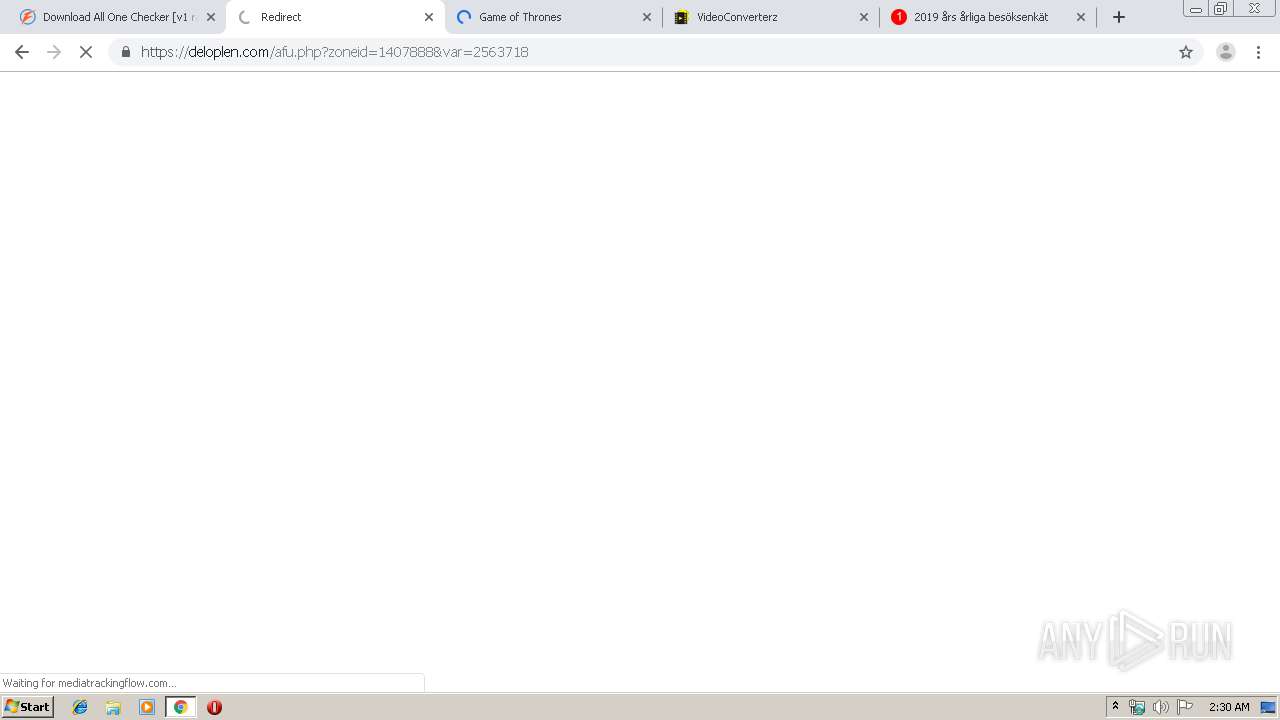
2060 | chrome.exe | GET | 302 | 212.32.252.66:80 | http://dti.l-plantago-maxima.icu/click?pid=256&offer_id=1061&sub1=bf2693za8wh1772b | NL | html | 145 b | suspicious |
2060 | chrome.exe | GET | 200 | 79.110.23.105:80 | http://competition1516.falseortruerdr40.live/media/mainstream/se/wap/mobsurvey/modernizr-2.6.2-respond-1.1.0.min.js | RO | html | 17.8 Kb | suspicious |
2060 | chrome.exe | GET | 200 | 79.110.23.105:80 | http://competition1516.falseortruerdr40.live/media/mainstream/se/wap/mobsurvey/sv-en.js | RO | text | 5.03 Kb | suspicious |
2060 | chrome.exe | GET | 200 | 79.110.23.105:80 | http://competition1516.falseortruerdr40.live/media/mainstream/us/wap/mobsurvey/logo2.js | RO | text | 6.96 Kb | suspicious |
2060 | chrome.exe | GET | 200 | 79.110.23.105:80 | http://competition1516.falseortruerdr40.live/media/mainstream/se/wap/mobsurvey/jquery-ui.min.js | RO | text | 222 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2060 | chrome.exe | 104.24.101.209:443 | www.file-up.org | Cloudflare Inc | US | shared |
2060 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
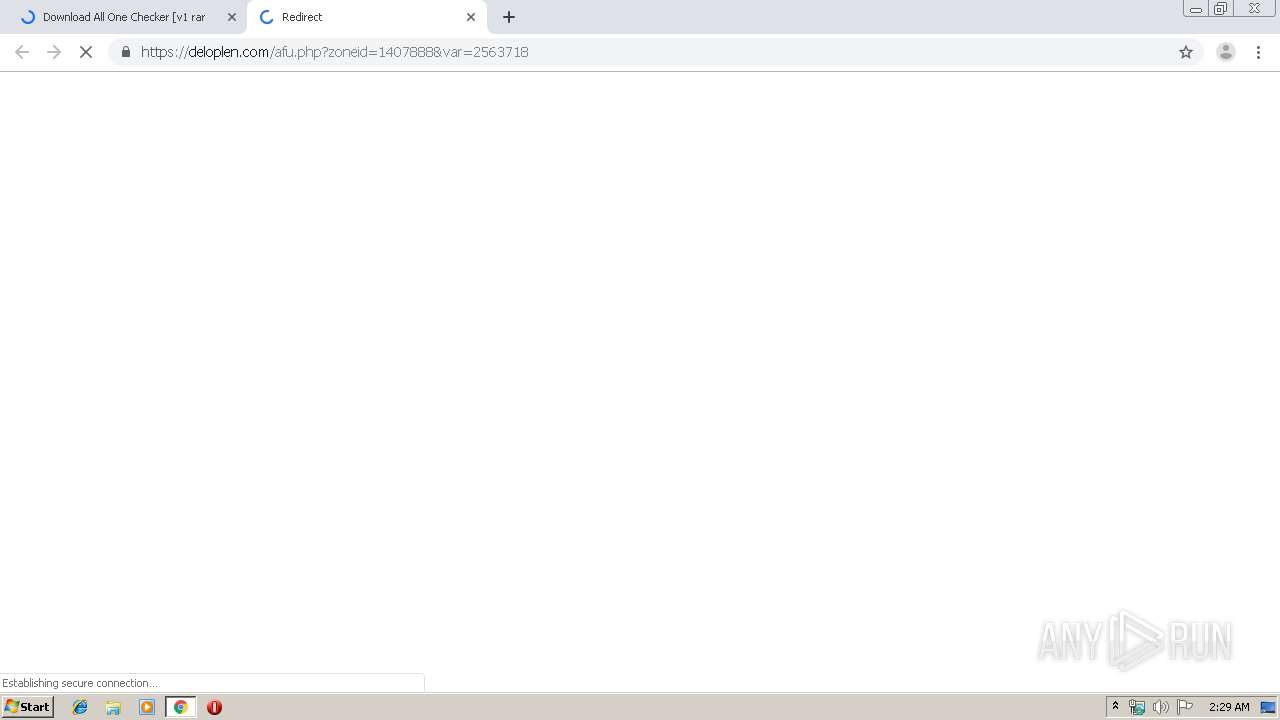
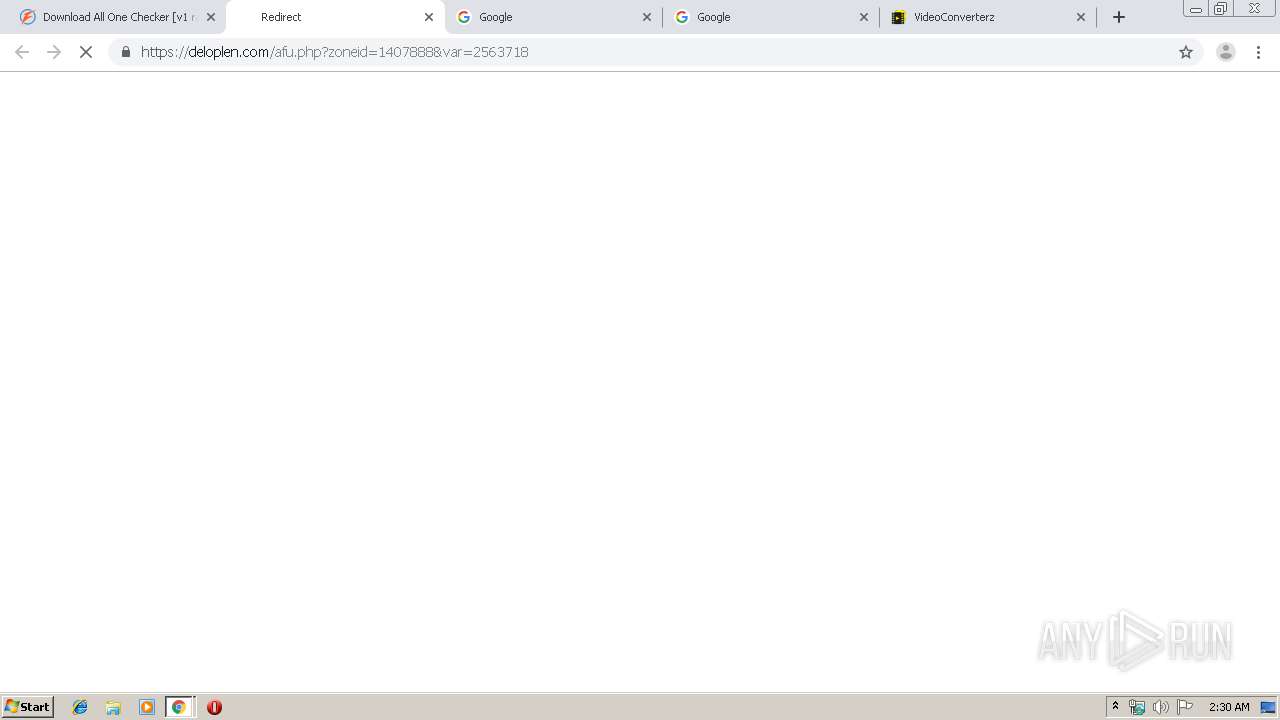
2060 | chrome.exe | 88.85.66.196:443 | deloplen.com | Webzilla B.V. | NL | suspicious |
— | — | 151.139.242.29:443 | images.dmca.com | netDNA | US | unknown |
2060 | chrome.exe | 13.249.11.34:443 | certify-js.alexametrics.com | — | US | unknown |
2060 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2060 | chrome.exe | 172.217.18.168:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
2060 | chrome.exe | 13.249.12.74:80 | x.ss2.us | — | US | unknown |
2060 | chrome.exe | 207.154.254.152:443 | trackingflow.pro | Digital Ocean, Inc. | DE | suspicious |
2060 | chrome.exe | 2.16.106.233:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.file-up.org |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
deloplen.com |
| whitelisted |
nativepu.sh |
| suspicious |
images.dmca.com |
| whitelisted |
certify-js.alexametrics.com |
| shared |
ssl.google-analytics.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
x.ss2.us |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
1 ETPRO signatures available at the full report