| File name: | 02469657_3 |
| Full analysis: | https://app.any.run/tasks/0647c3a0-a978-4228-8cf1-ee482c2953a1 |
| Verdict: | Malicious activity |
| Analysis date: | April 08, 2021, 23:52:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1E4D916BE5D3E531F3D32405D4183425 |
| SHA1: | DD040D37717CF9066EC512FD1E31F4BF4E0E0792 |
| SHA256: | 115A90E61AC5BA58A14CF26D71D4C4F4AA59281587AFFF2F86DAFEB8FDF996F1 |
| SSDEEP: | 196608:tCSnuVYkuK3dj1HpyqJ2bDKHkcBqtKWi75/Mwiyk01YulN+ukqcTCPqg:cSuVduuWaSMNTewh1YuBBcmPT |
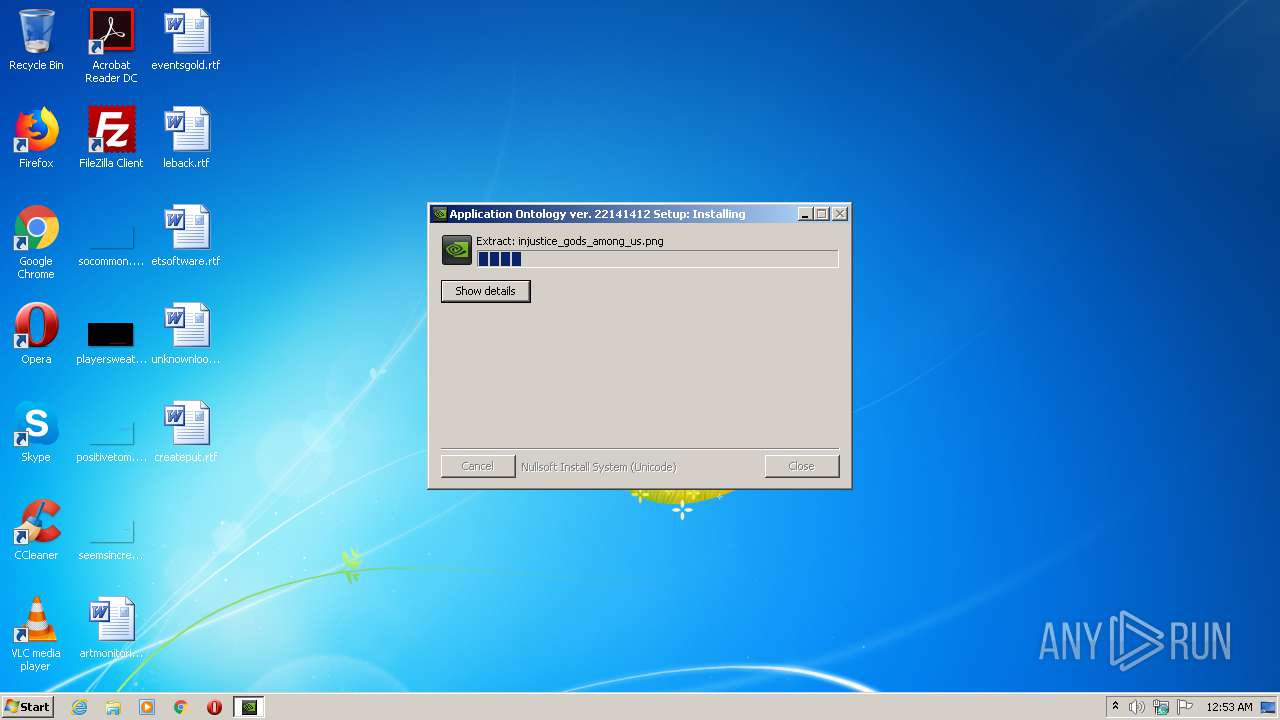
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops a file that was compiled in debug mode
- 02469657_3.exe (PID: 3712)
Executable content was dropped or overwritten
- 02469657_3.exe (PID: 3712)
Creates files in the program directory
- 02469657_3.exe (PID: 3712)
INFO
Dropped object may contain Bitcoin addresses
- 02469657_3.exe (PID: 3712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5 |
| ImageVersion: | 6 |
| OSVersion: | 5 |
| EntryPoint: | 0x38af |
| UninitializedDataSize: | 16896 |
| InitializedDataSize: | 489984 |
| CodeSize: | 29696 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| TimeStamp: | 2012:02:24 20:20:04+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:20:04 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:20:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000728C | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49971 |
.rdata | 0x00009000 | 0x00002B6E | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.49793 |
.data | 0x0000C000 | 0x00072B9C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.80494 |
.ndata | 0x0007F000 | 0x00089000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00108000 | 0x000015A8 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.46221 |
.reloc | 0x0010A000 | 0x00000FD6 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.0715 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21266 | 726 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
37
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3712 | "C:\Users\admin\AppData\Local\Temp\02469657_3.exe" | C:\Users\admin\AppData\Local\Temp\02469657_3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
342
Read events
342
Write events
0
Delete events
0
Modification events
Executable files
4
Suspicious files
0
Text files
961
Unknown types
1 027
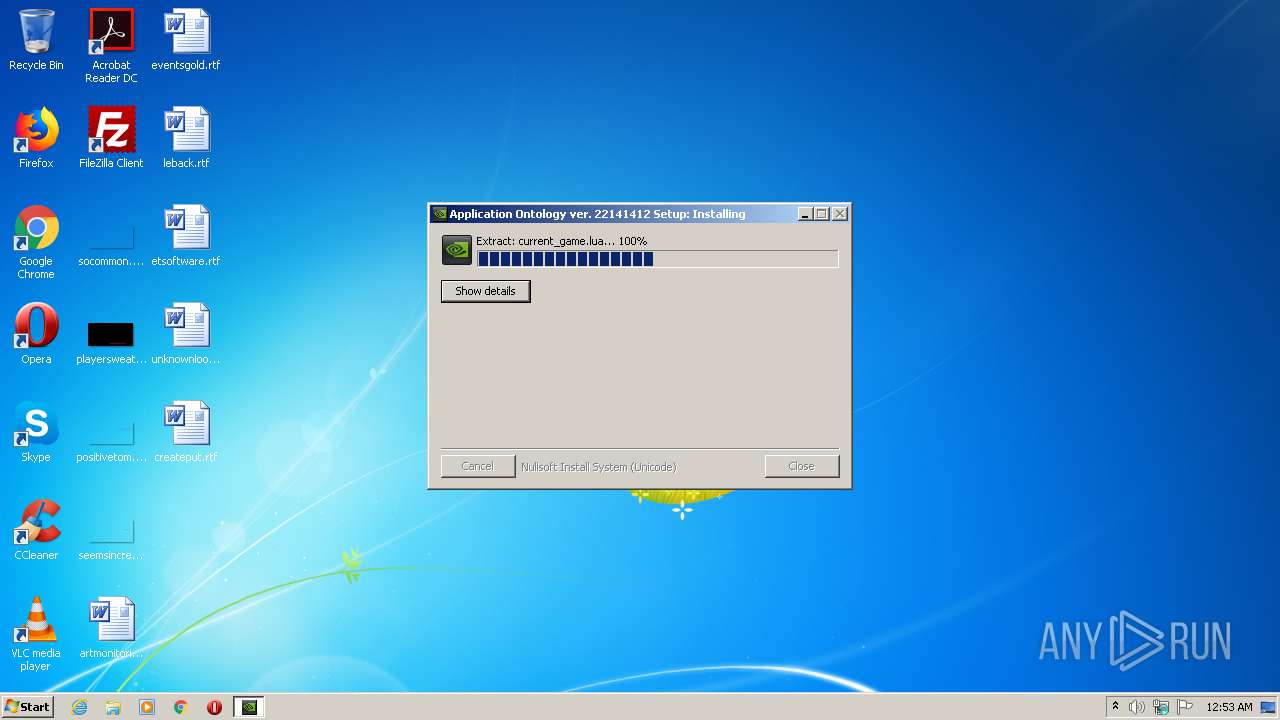
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3712 | 02469657_3.exe | C:\ProgramData\NVIDIA\Updatus\ApplicationOntology\data\fingerprint.db | xml | |
MD5:9CBA42A352D0480273DADB39B7563415 | SHA256:2D3BF231402C4B8D1F06CD948F9B865AE09D4D4605F1E0F336092978DE940A83 | |||
| 3712 | 02469657_3.exe | C:\ProgramData\NVIDIA\Updatus\ApplicationOntology\data\icons\7fan_all_heroes.png | image | |
MD5:5C759778DE1274C7E486E565E9EAC551 | SHA256:91F0DCB45F9B6FC5F94B0FCD2D5753E9F93343E7E2C7421B7443922800284D35 | |||
| 3712 | 02469657_3.exe | C:\ProgramData\NVIDIA\Updatus\ApplicationOntology\data\icons\ace_combat_assault_horizon.png | image | |
MD5:65F4DD3955CAA2A2CFC1B231042D53CE | SHA256:CB992E991CE8B897AA85925C70E5D5CDDABD9856B495D8F176669C9517ABB594 | |||
| 3712 | 02469657_3.exe | C:\ProgramData\NVIDIA\Updatus\ApplicationOntology\data\icons\age_of_wushu.png | image | |
MD5:135CCA06CD74CE67C2AF80169BC4D9F4 | SHA256:D111DC8E8C50D9D8887146EE862858DB258DEF3E94B93F40BF155082D1B8B1C8 | |||
| 3712 | 02469657_3.exe | C:\ProgramData\NVIDIA\Updatus\ApplicationOntology\data\icons\7_days_to_die.png | image | |
MD5:814CA8C187F731FAD8D4FFE431DB8428 | SHA256:E57C25F2947D2B2668C192B77889754031993822A7B957E5157326A3983FE0DA | |||
| 3712 | 02469657_3.exe | C:\ProgramData\NVIDIA\Updatus\ApplicationOntology\data\icons\arma_iii.png | image | |
MD5:B8A742AC796479B9465AED3A69DF148B | SHA256:178EC5E3011F0426B26E4336A9AD6DBFBE00FC68FFC18EE0D46B1B61BC351A16 | |||
| 3712 | 02469657_3.exe | C:\ProgramData\NVIDIA\Updatus\ApplicationOntology\data\icons\aion.png | image | |
MD5:3F1CEC429F46FF0327535B8324F6EB49 | SHA256:7C3DDAE99D46F31A2866AD2A34F90DA47A3E30E96A0C8E5C27F3FEFB19166F58 | |||
| 3712 | 02469657_3.exe | C:\ProgramData\NVIDIA\Updatus\ApplicationOntology\data\icons\albino_lullaby.png | image | |
MD5:D146F2541E9465CE465DBF32619E298A | SHA256:4A9E4CA212106D1F87981895844D007C0F5FE685BF8F0F846BA44F58C71B4D21 | |||
| 3712 | 02469657_3.exe | C:\ProgramData\NVIDIA\Updatus\ApplicationOntology\data\icons\300_ying_xiong.png | image | |
MD5:3A0B8E4D58A6051CC438B8E308B2BA4B | SHA256:F82C787B661A1E4D3551F61FC4685299743750A3B1B6E6363141DC5AC22E45C3 | |||
| 3712 | 02469657_3.exe | C:\ProgramData\NVIDIA\Updatus\ApplicationOntology\data\icons\aliens_colonial_marines.png | image | |
MD5:298B36FFA16D0206FF2681D9C6EFCD56 | SHA256:AAD70D54A843C7B9F4474DB5FE866AA0C3BC23388E14407C247B08FC05C78B96 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report