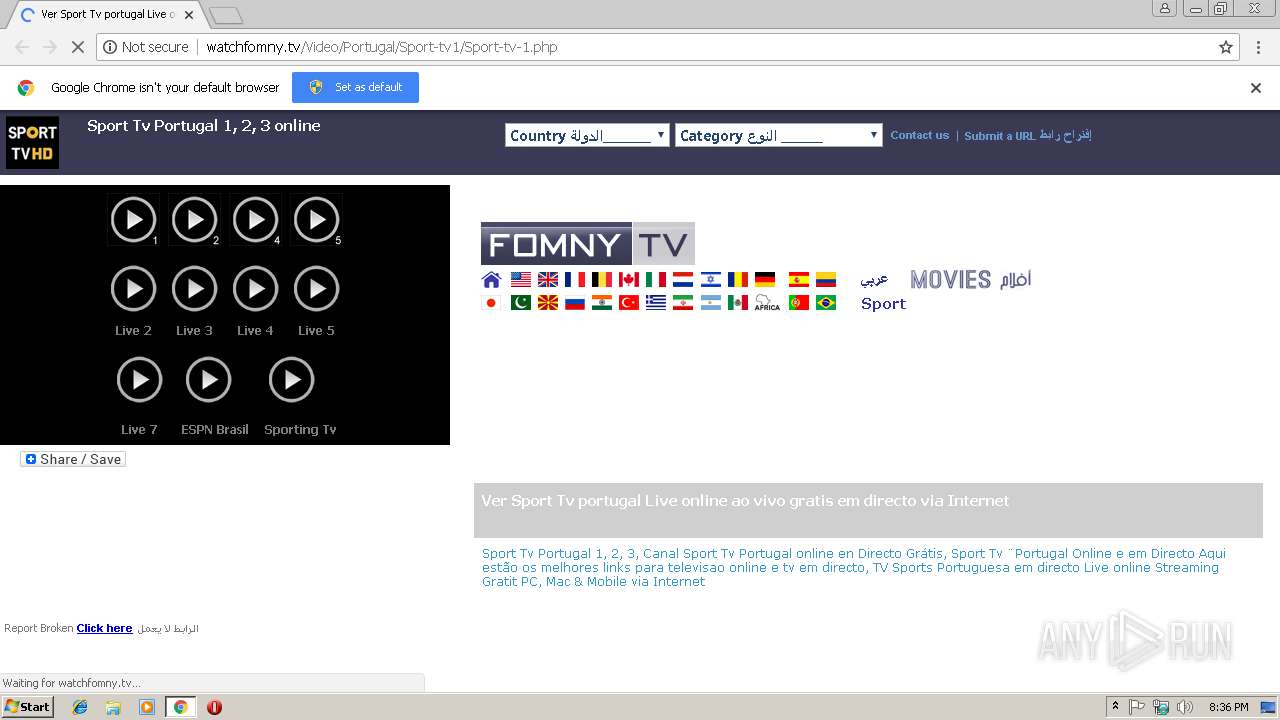
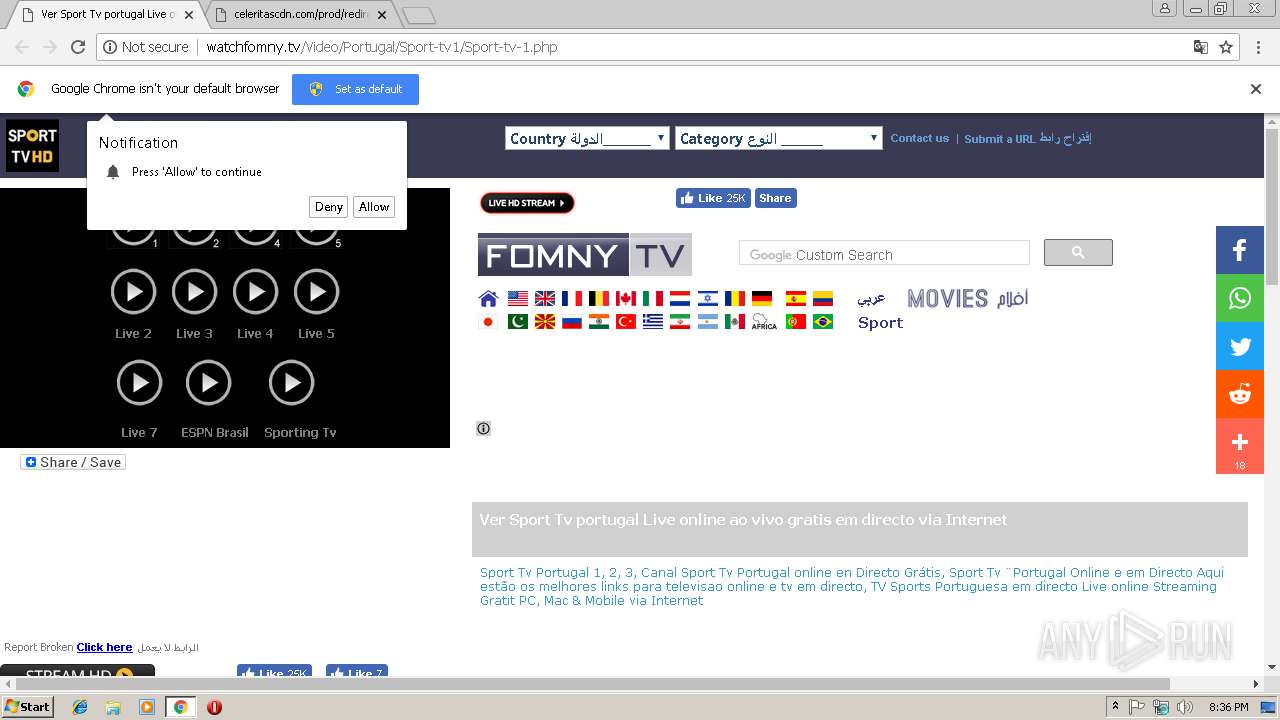
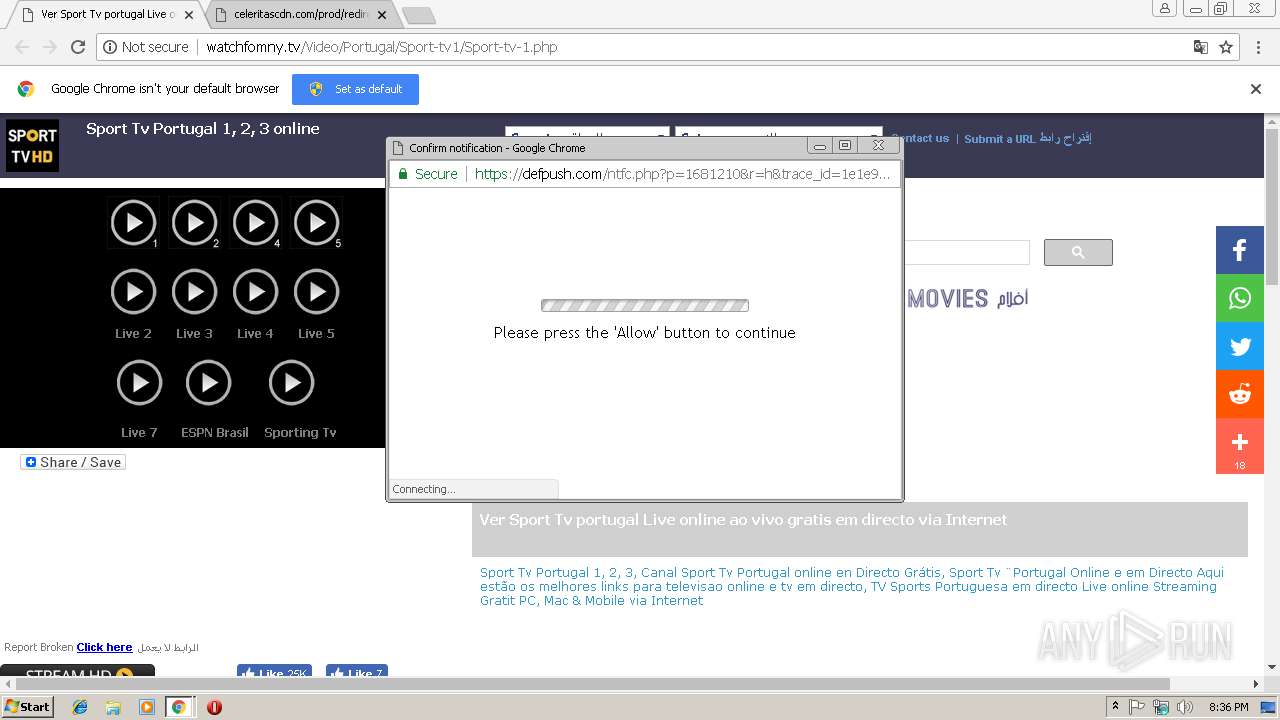
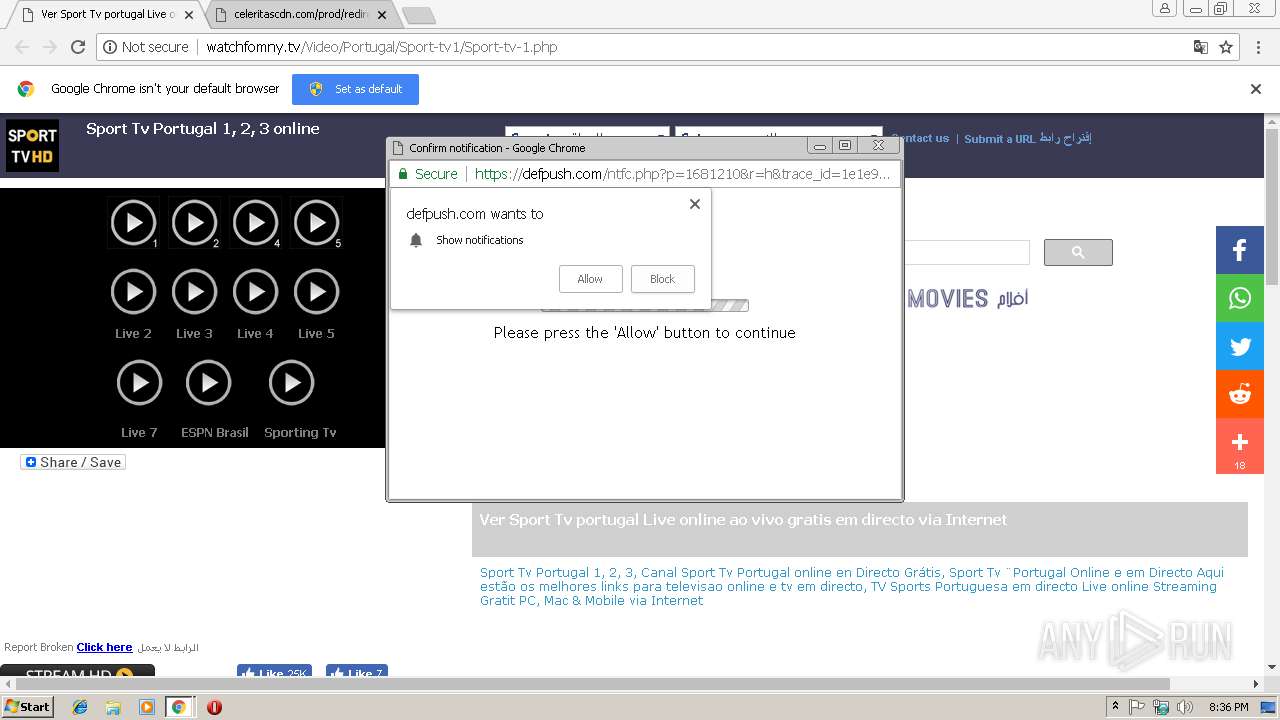
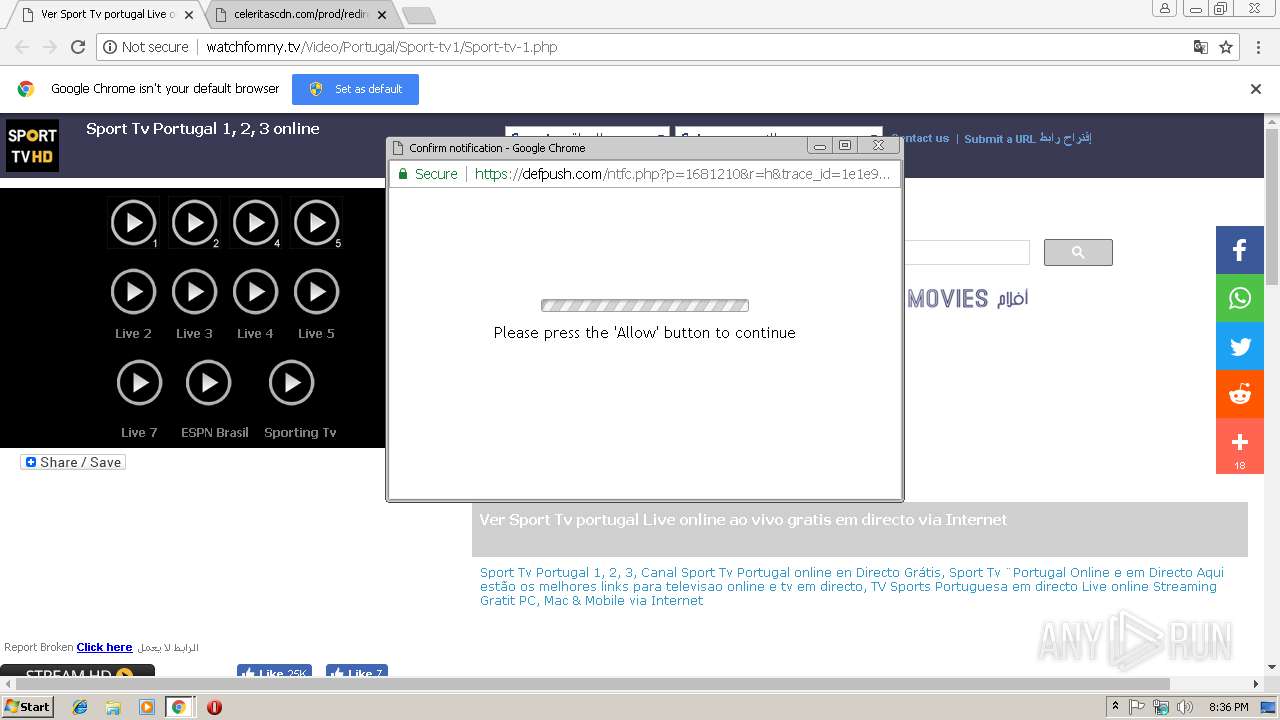
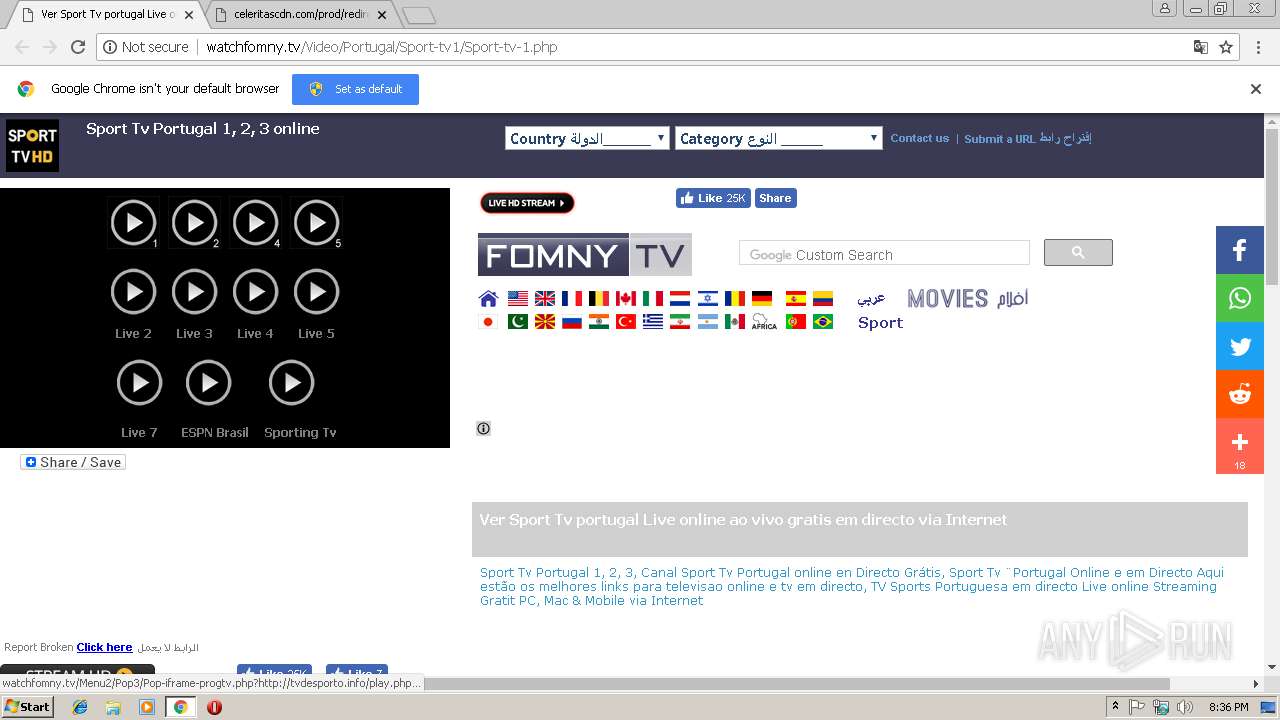
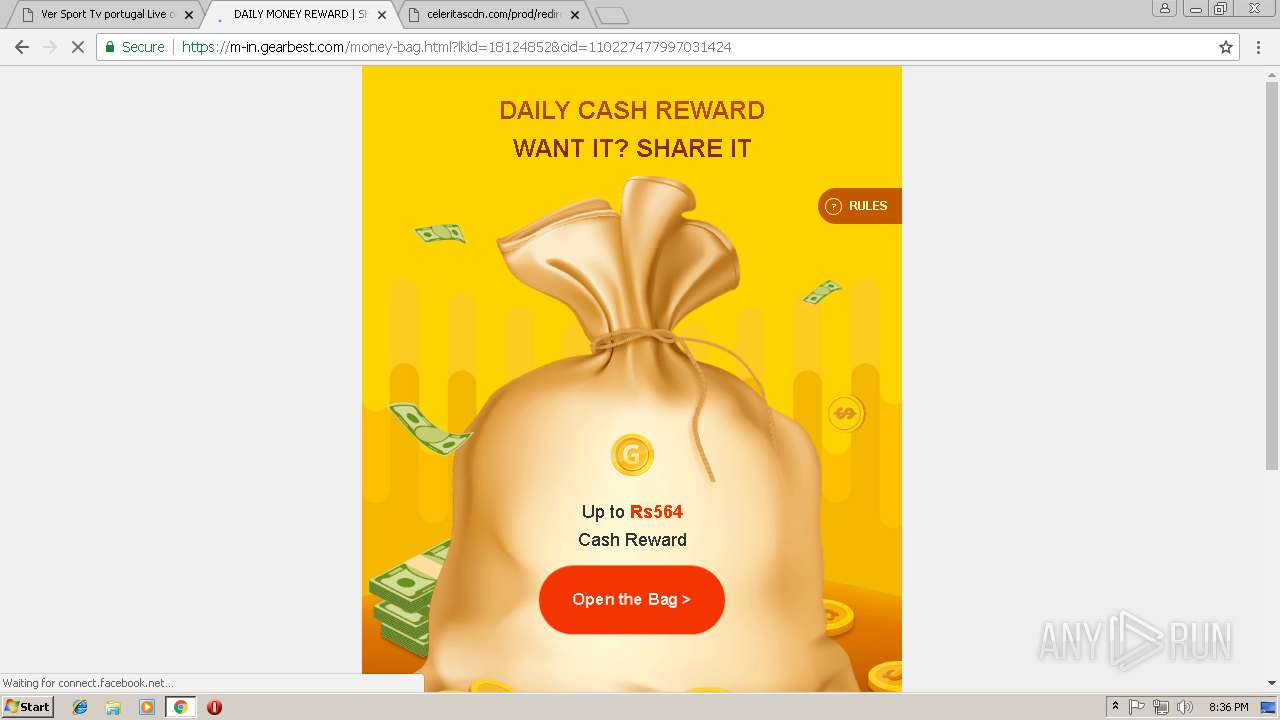
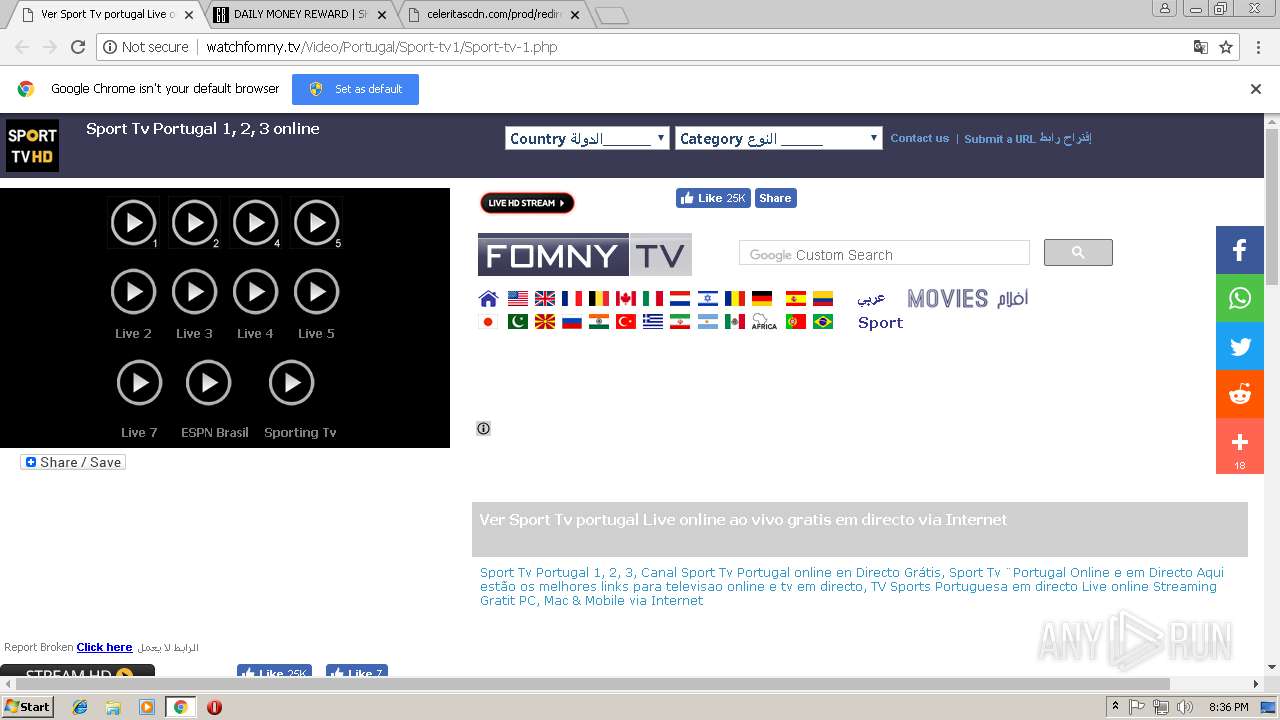
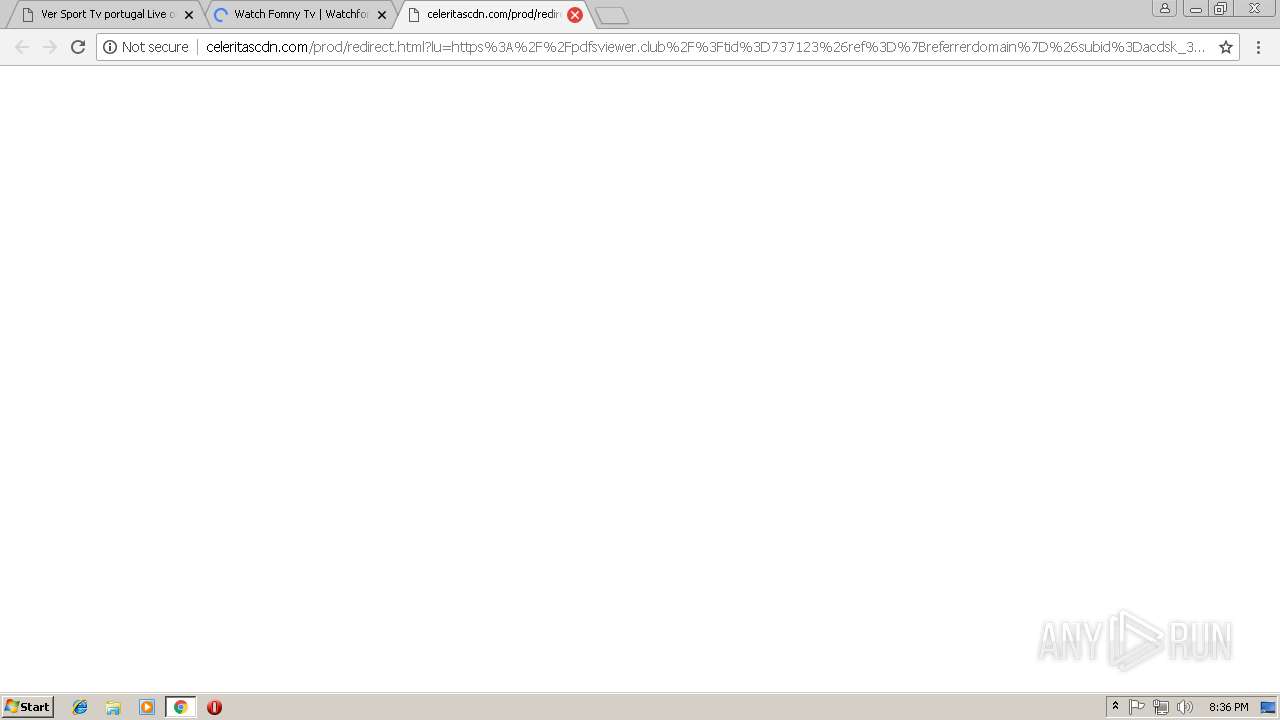
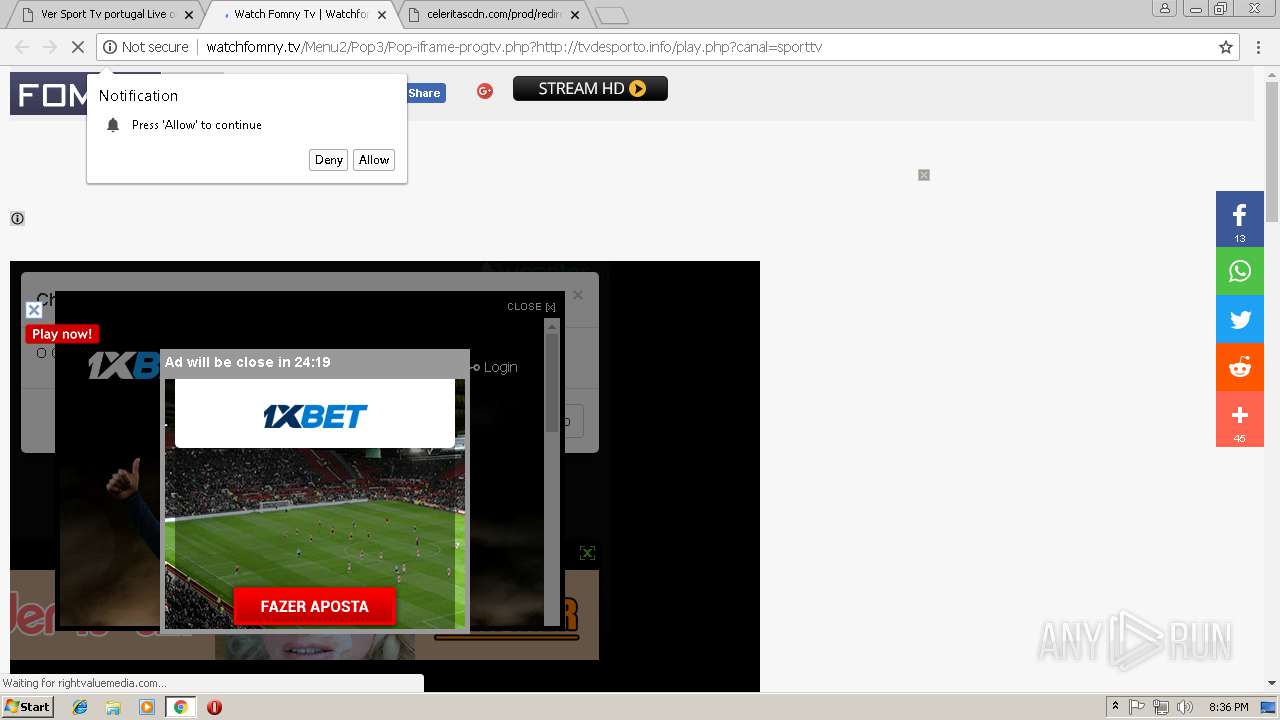
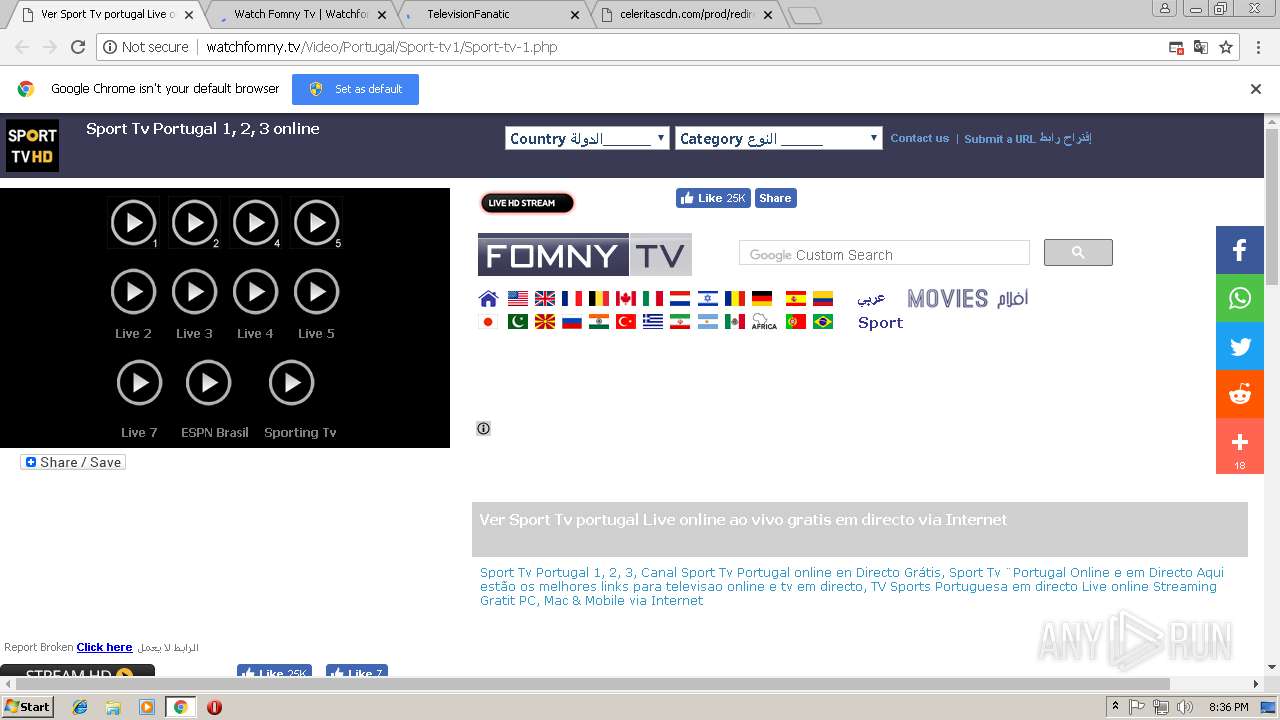
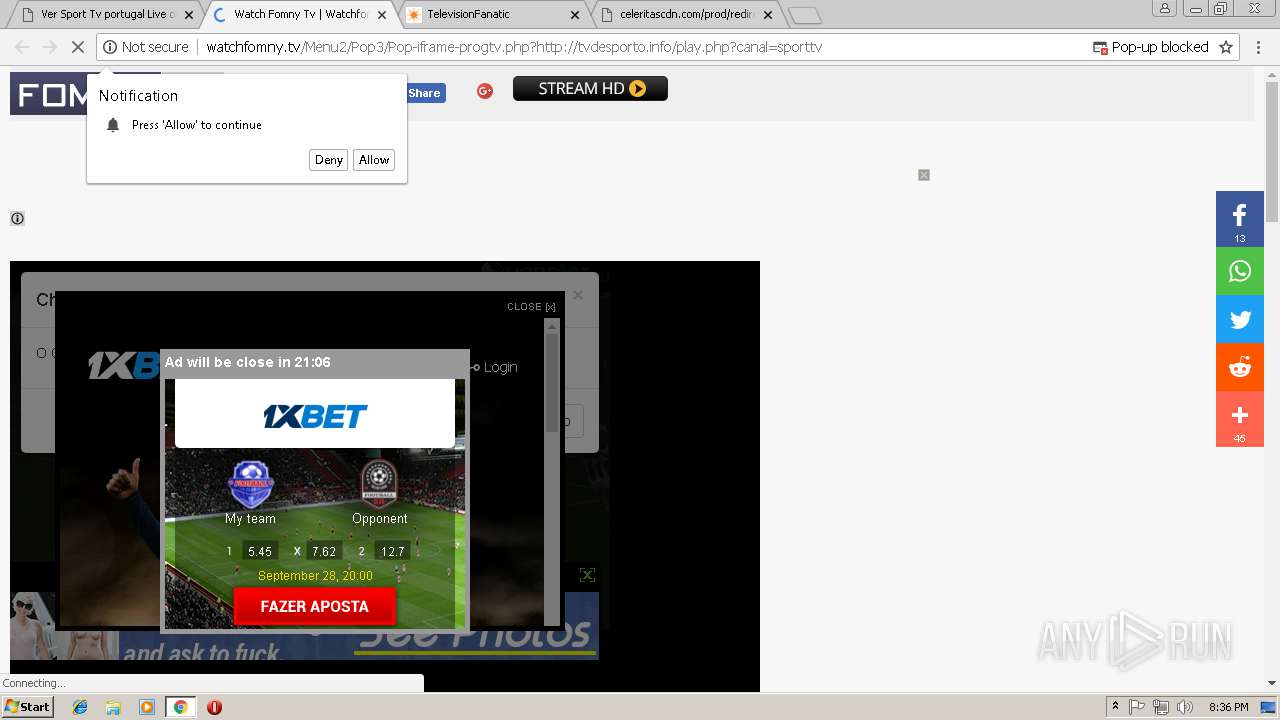
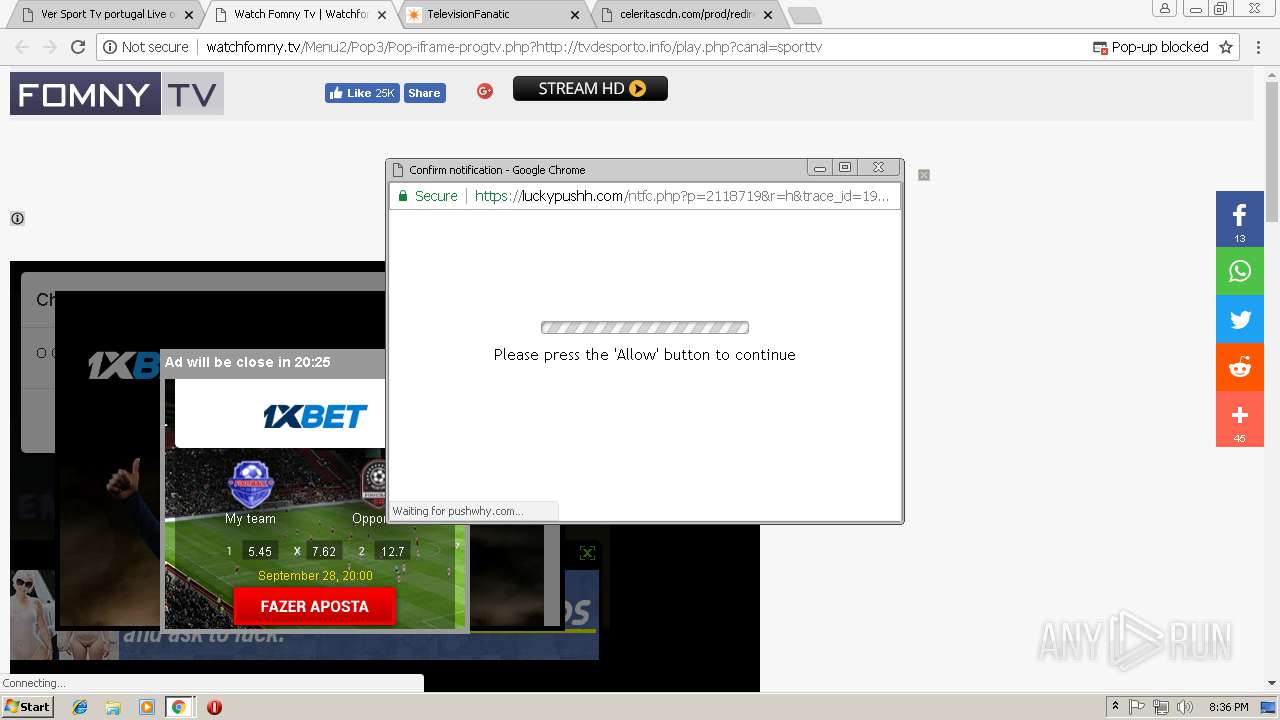
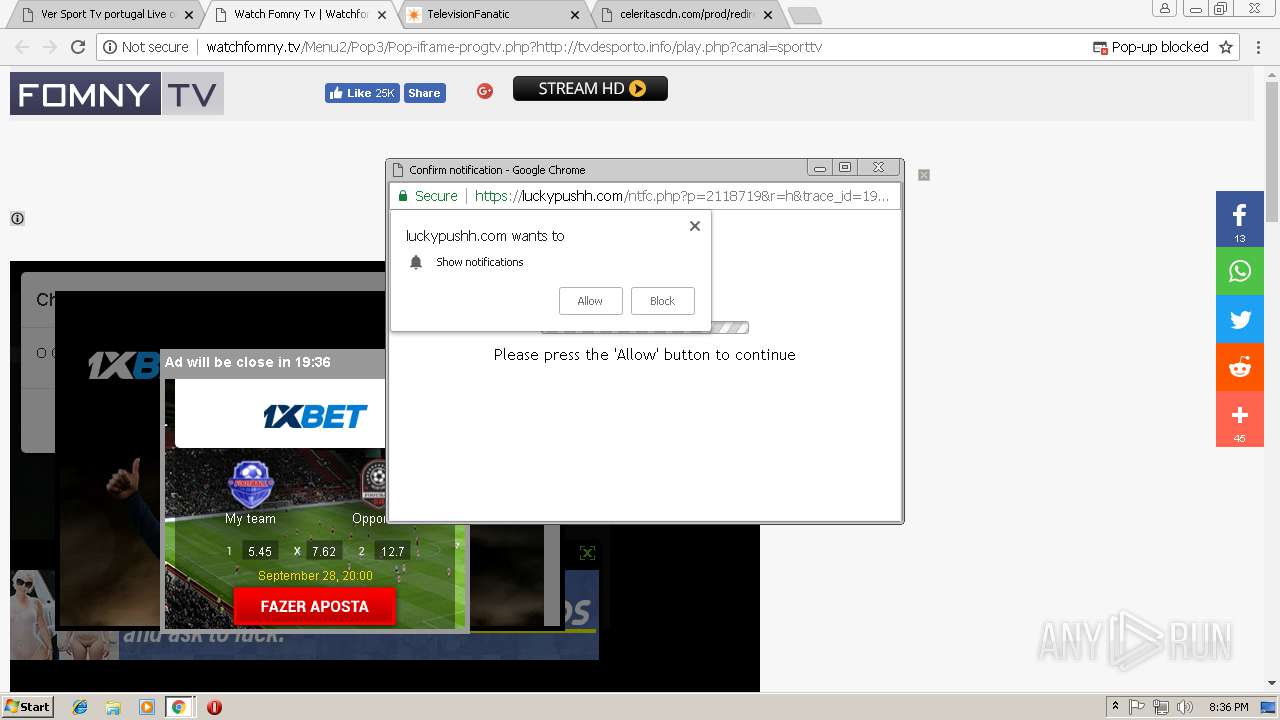
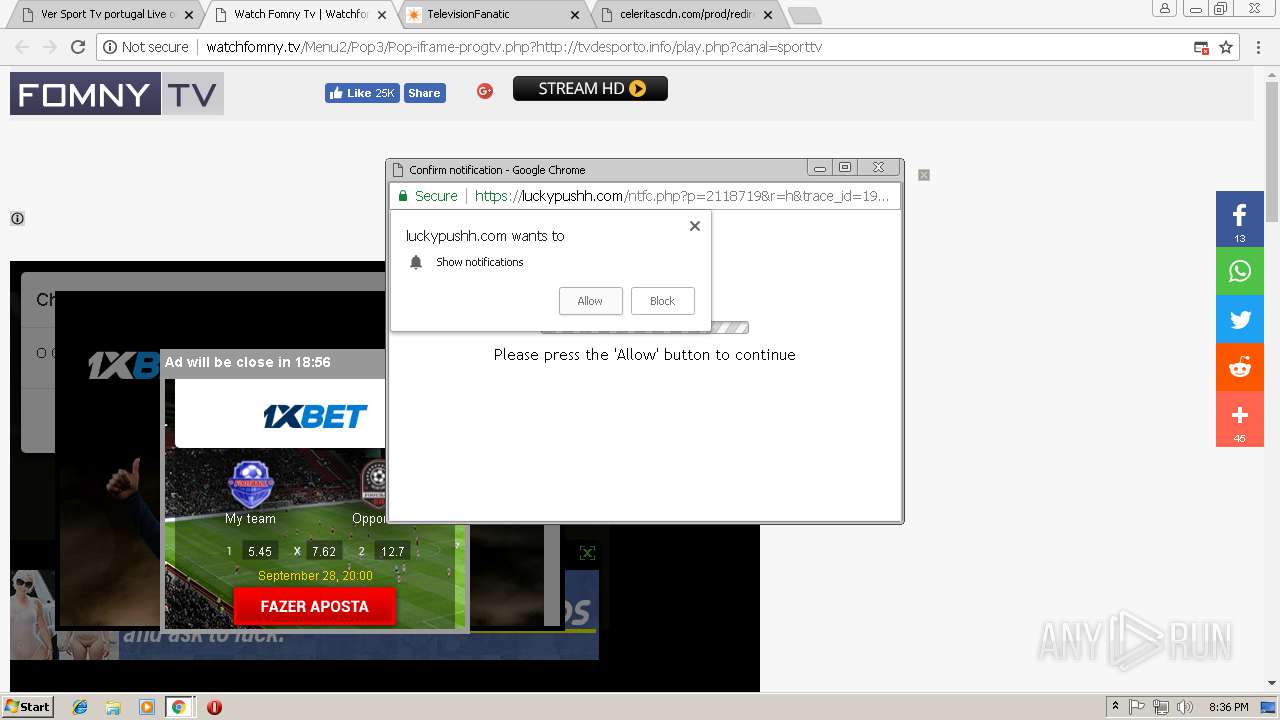
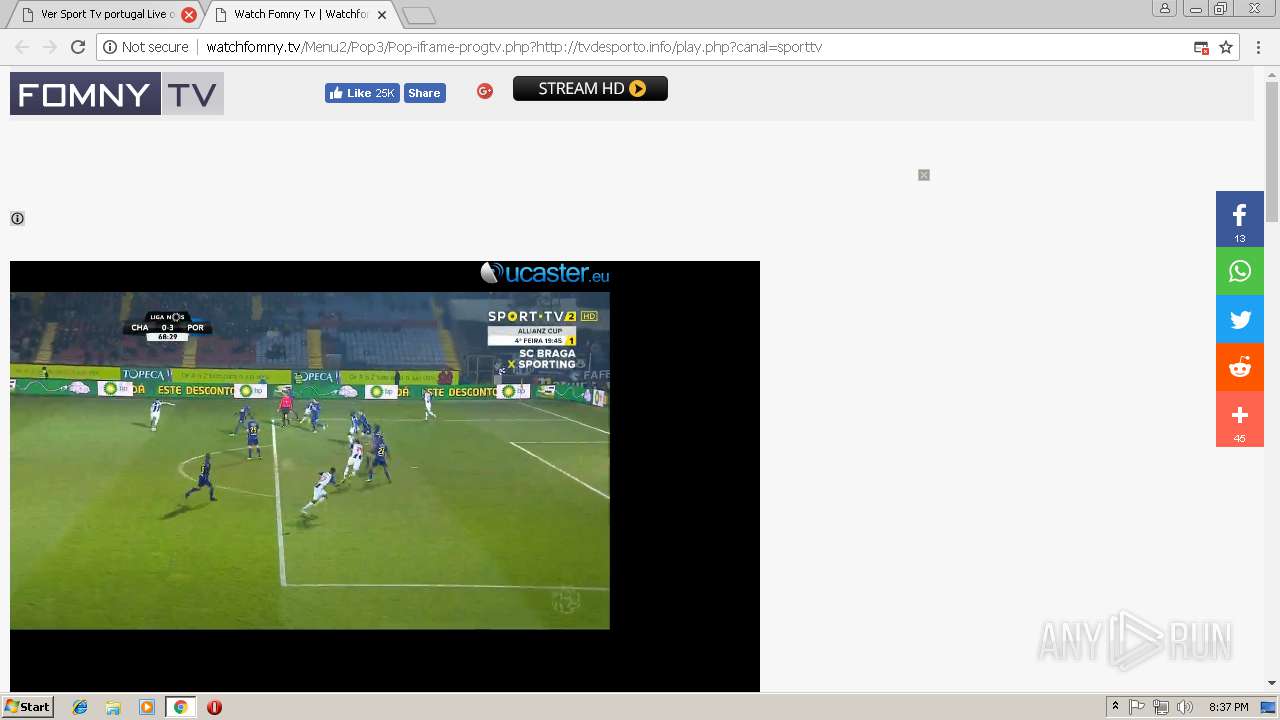
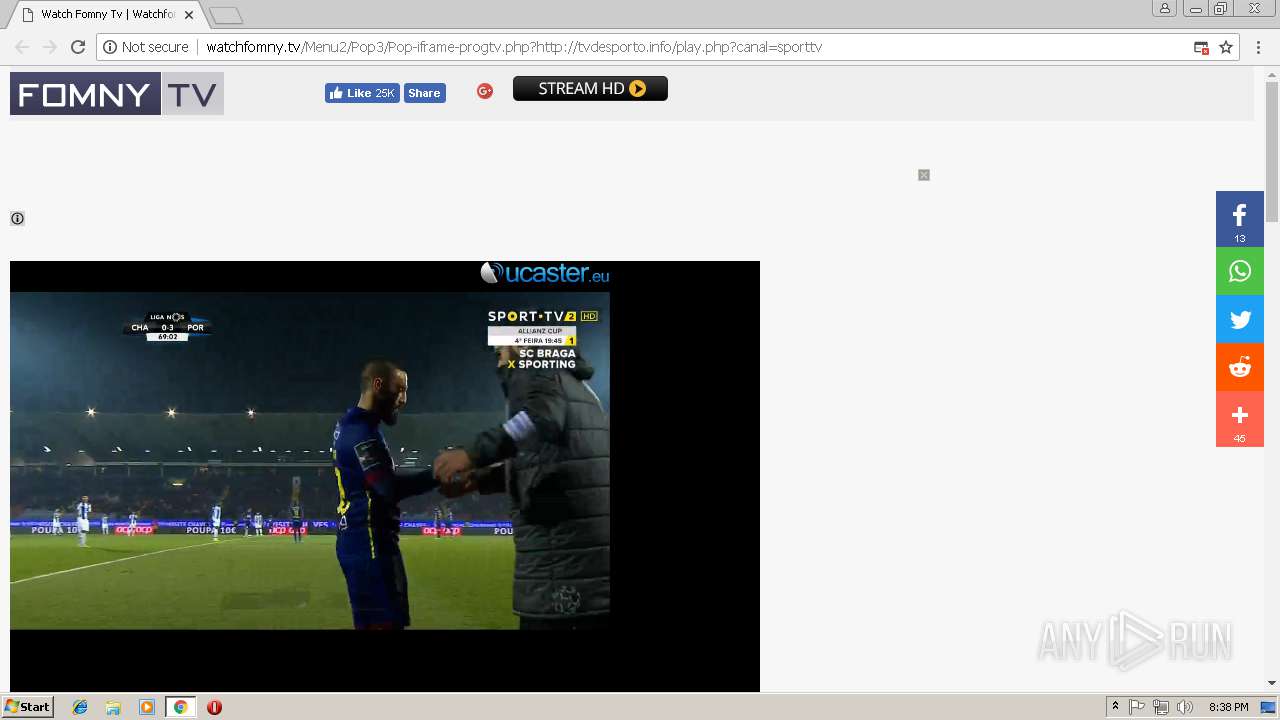
| URL: | http://watchfomny.tv/Video/Portugal/Sport-tv1/Sport-tv-1.php |
| Full analysis: | https://app.any.run/tasks/4ee3ef93-45bb-4767-b394-636b4271d467 |
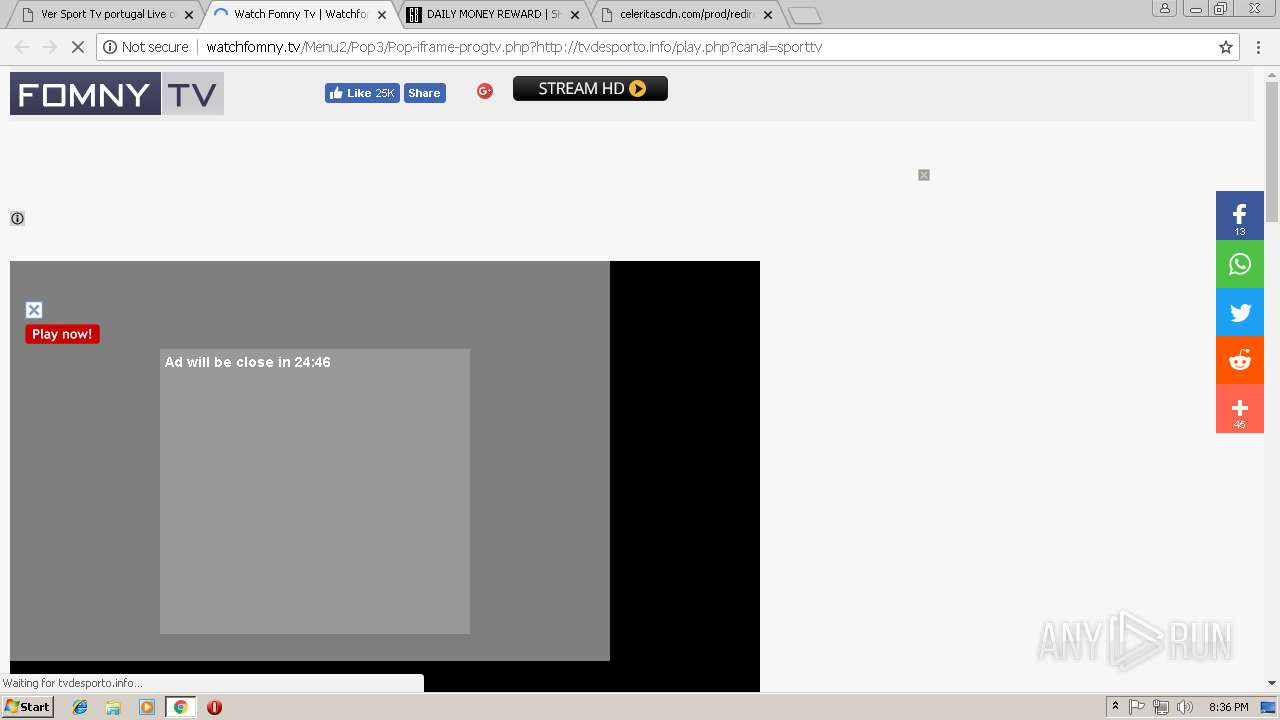
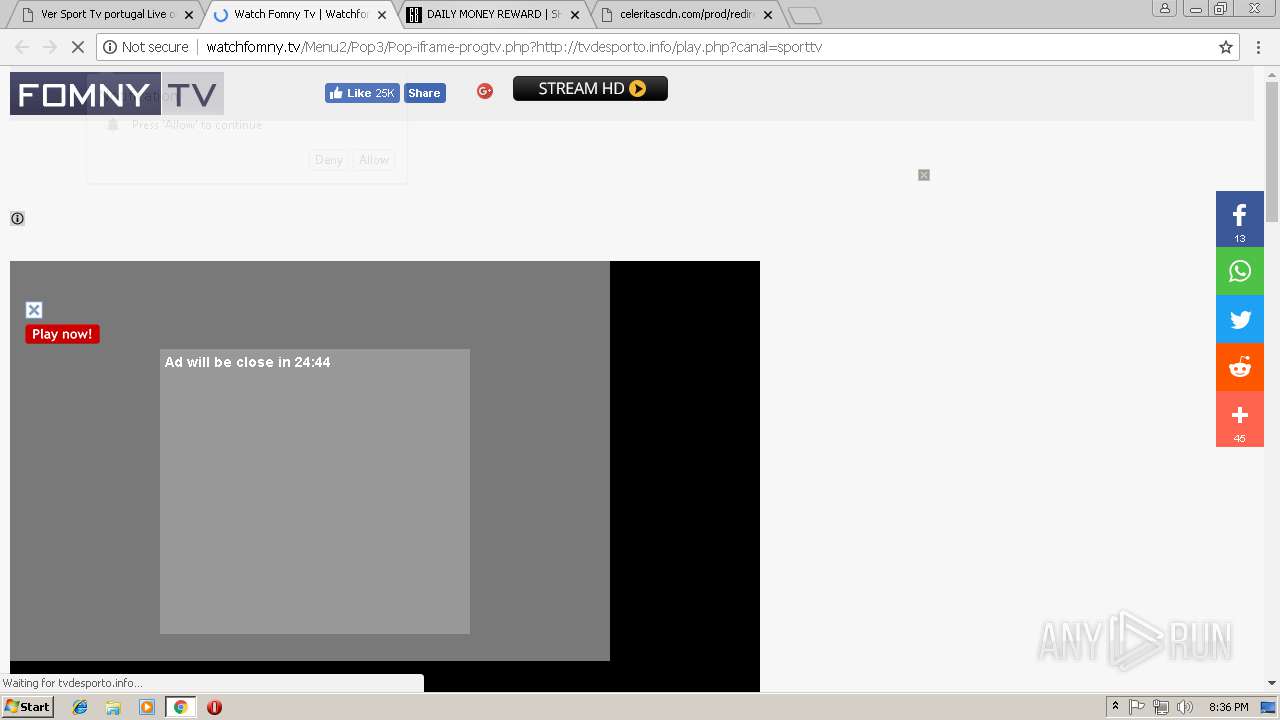
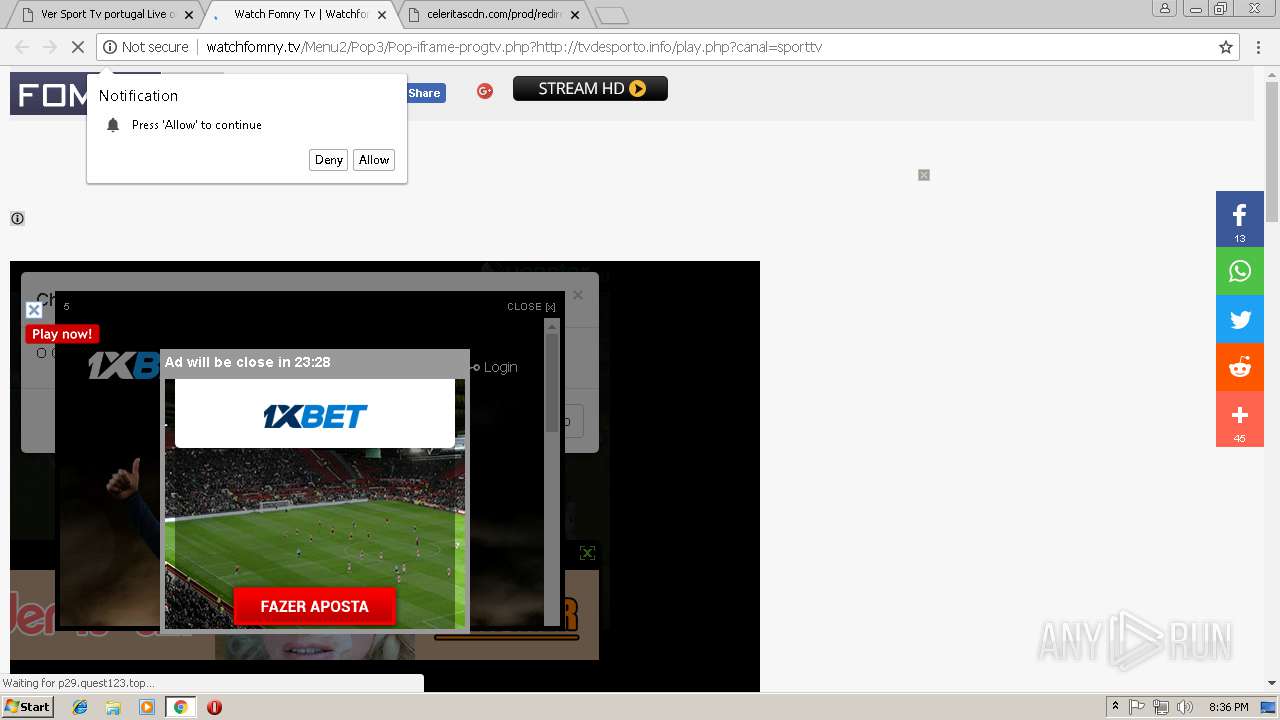
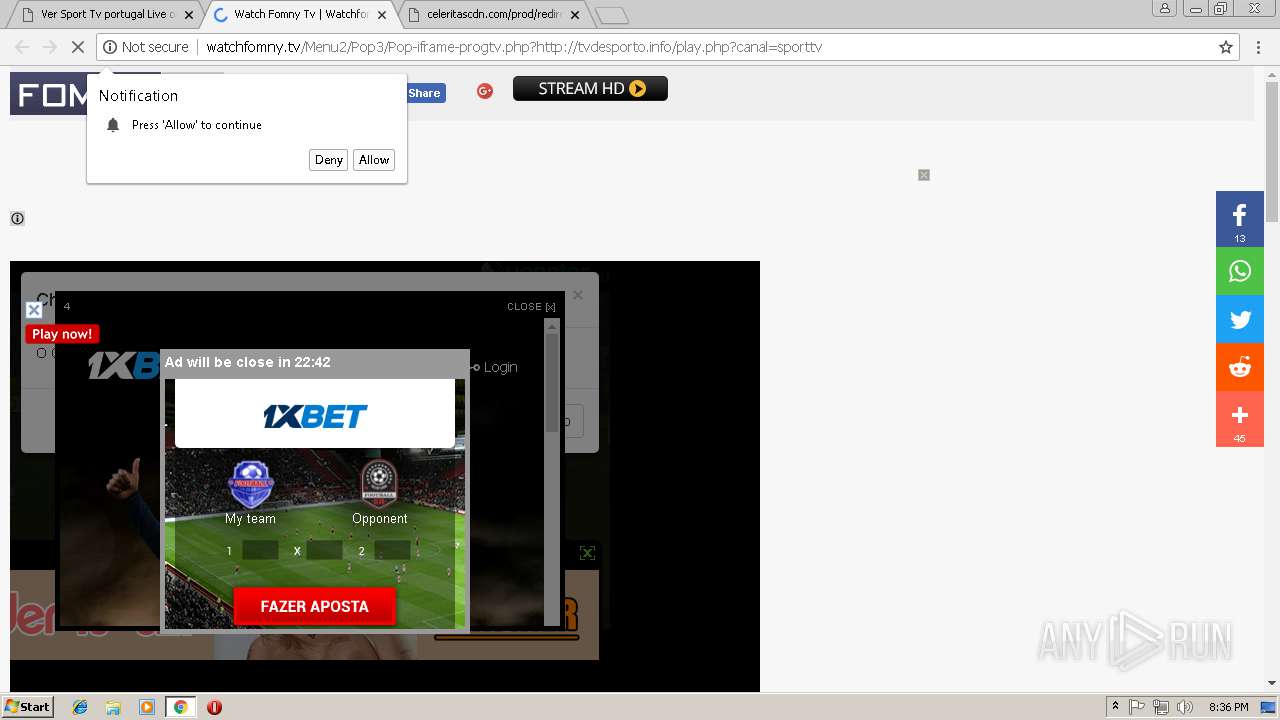
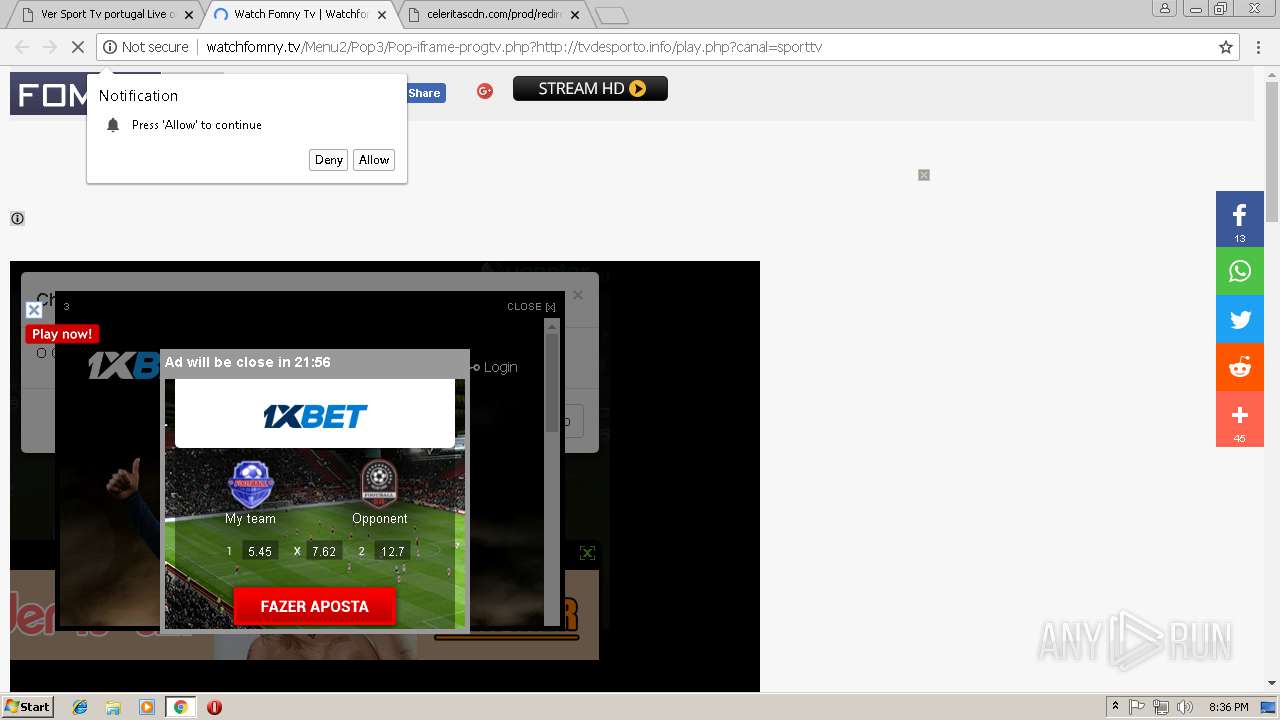
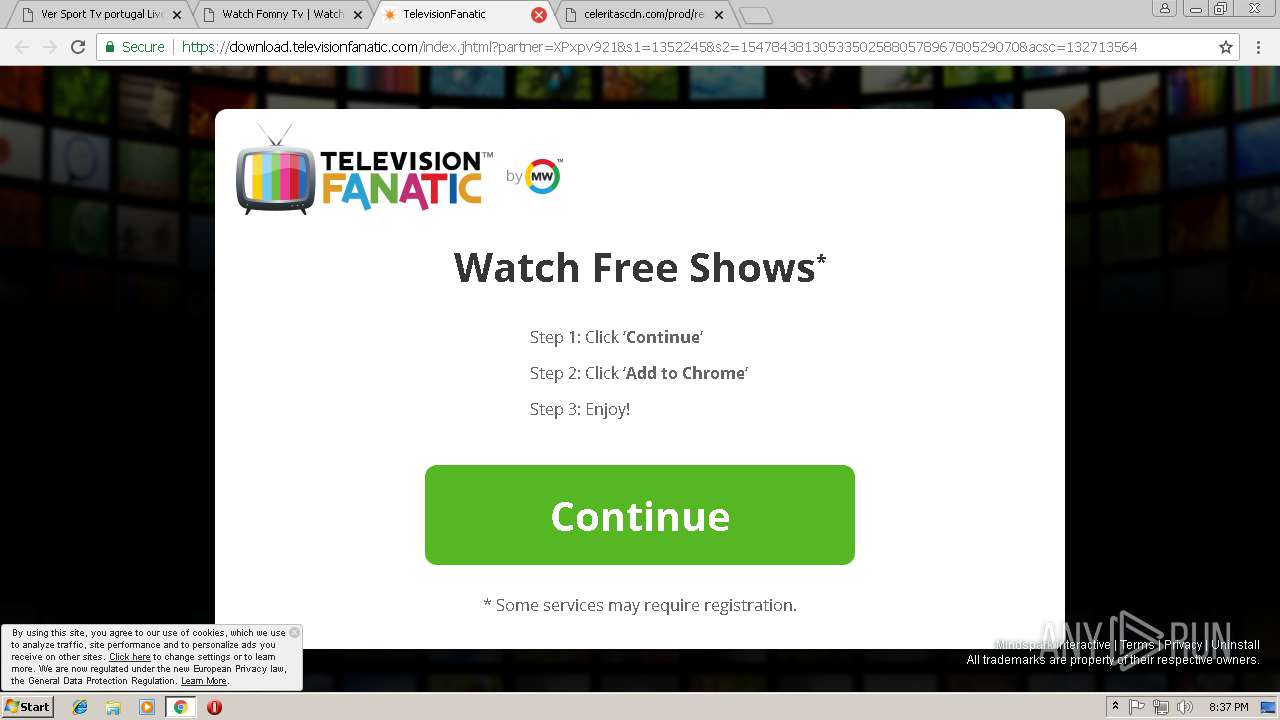
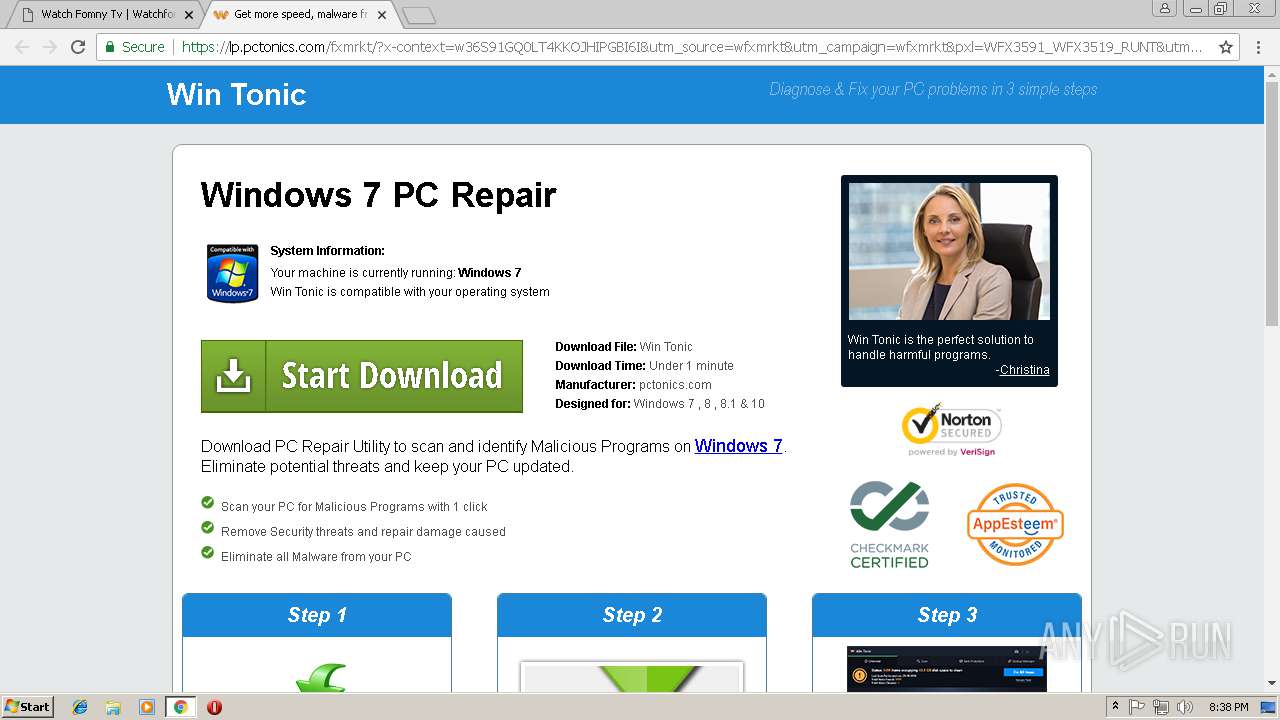
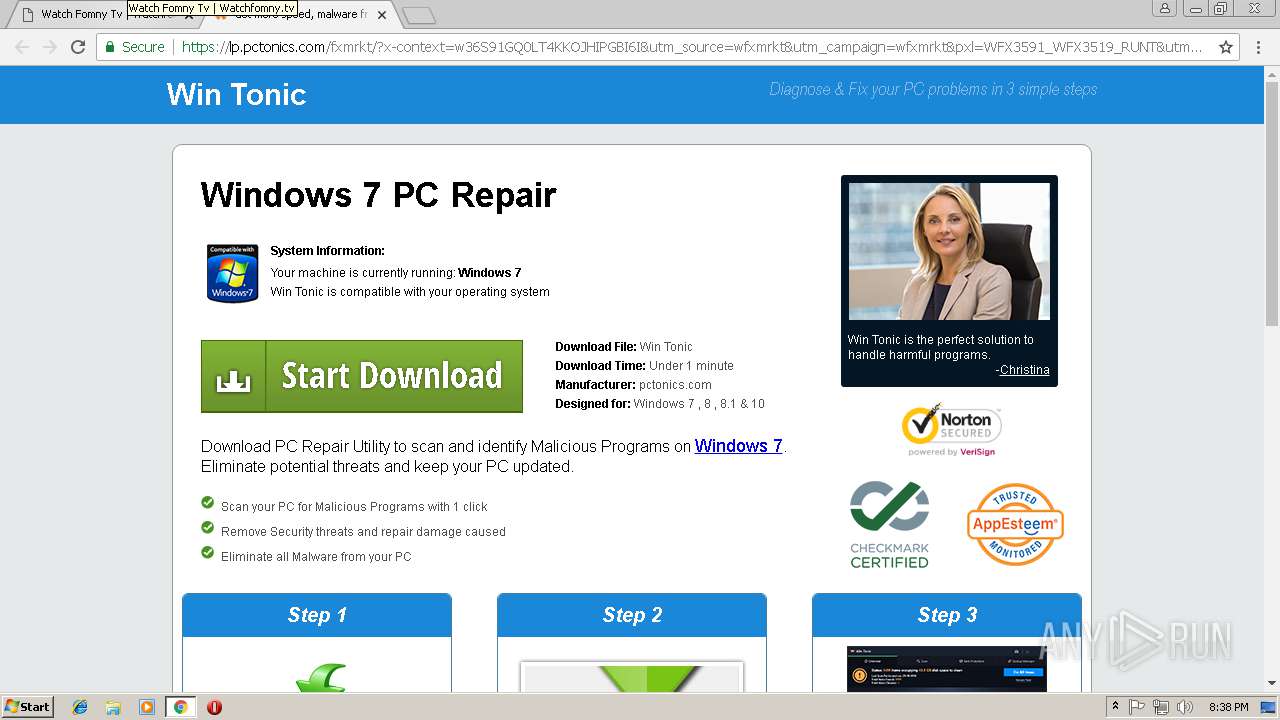
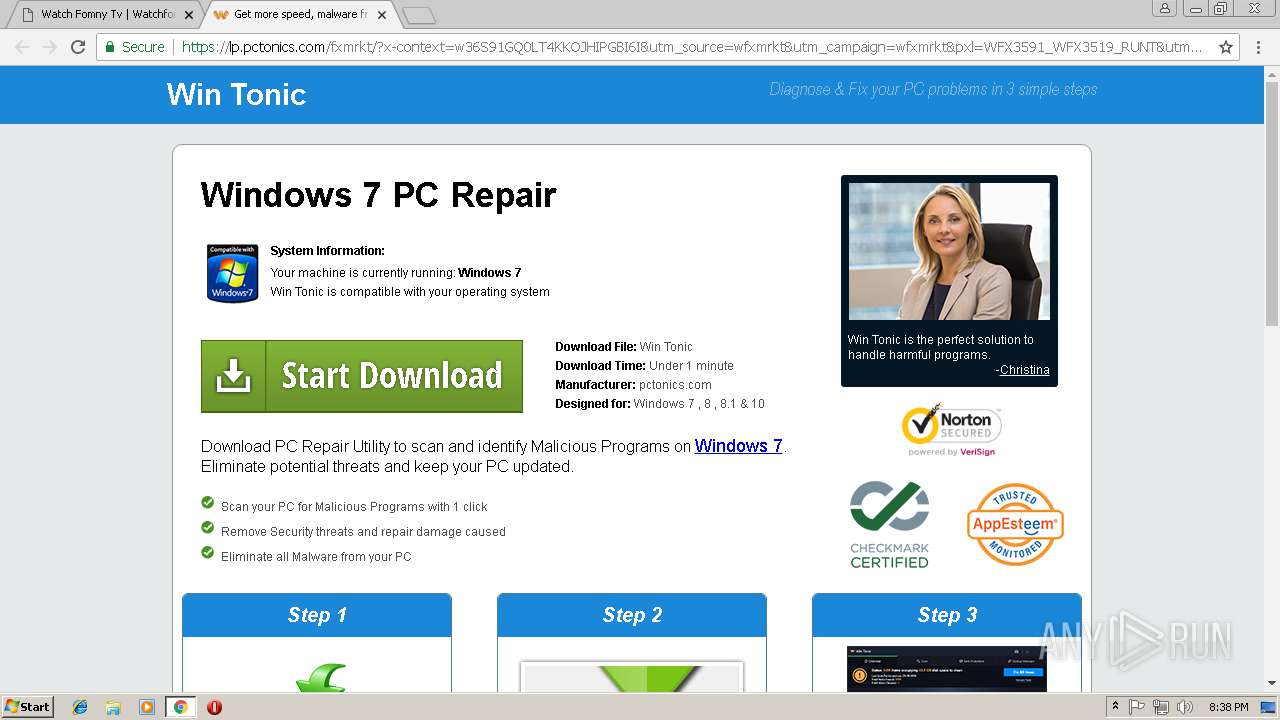
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2019, 20:36:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 19AF05C4196CC6C713970603F2247CCF |
| SHA1: | FD8DB0977D0BCB5AFD9C51FB7527FD7051CFC745 |
| SHA256: | 1150133B60D3981EDC90F378FF77E95A2A6137BEBA0C1FCDDC749651BF23B843 |
| SSDEEP: | 3:N1KJEI6WMttRKKBIRn2gXuR9LV:CKZ3RRBIR2SuRb |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2960)
Dropped object may contain TOR URL's
- chrome.exe (PID: 2960)
Changes settings of System certificates
- chrome.exe (PID: 2960)
Connects to unusual port
- chrome.exe (PID: 2960)
Reads settings of System Certificates
- chrome.exe (PID: 2960)
Creates files in the user directory
- chrome.exe (PID: 2960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=900,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --service-pipe-token=359E3820CD80A1B74F5415712150266D --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=359E3820CD80A1B74F5415712150266D --renderer-client-id=4 --mojo-platform-channel-handle=1848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2964 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://watchfomny.tv/Video/Portugal/Sport-tv1/Sport-tv-1.php | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=900,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=73833B57F2CE9A8D24D78C11992E55F8 --mojo-platform-channel-handle=4068 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=900,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --service-pipe-token=9A45B09FC40F5B70804A3CCA333C02B1 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9A45B09FC40F5B70804A3CCA333C02B1 --renderer-client-id=3 --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=900,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1C90FD6EB0096CCD7A146BADD8DD10DB --mojo-platform-channel-handle=5488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=900,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=C4B645AA56739C7047730307A5653547 --mojo-platform-channel-handle=3056 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f4300b0,0x6f4300c0,0x6f4300cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 4056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=900,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D047695F52D4E5A856185BA6D38AF85B --mojo-platform-channel-handle=972 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
655
Read events
602
Write events
50
Delete events
3
Modification events
| (PID) Process: | (2960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2960) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2960-13192317377228500 |
Value: 259 | |||
| (PID) Process: | (2960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
142
Text files
169
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\83f5afba-a556-4815-9882-34b2f247f92e.tmp | — | |
MD5:— | SHA256:— | |||
| 2960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b7ef2ab9-6fa8-4f72-93ea-002a2886af8b.tmp | — | |
MD5:— | SHA256:— | |||
| 2960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:1AA66EFDB743FB0A8DCC1CD79B0B6542 | SHA256:28D56532CCED7375A2A1C7731E57C1A1C2EC1AC9827F3E5BEEE7F8069A5F87DD | |||
| 2960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:197882774A7ECEC9046BC48F63189B66 | SHA256:27377B0D5F989997C2C3F74ACF163EED44B60631DDAA768F6655D7BE555742B2 | |||
| 2960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF246d22.TMP | text | |
MD5:1AA66EFDB743FB0A8DCC1CD79B0B6542 | SHA256:28D56532CCED7375A2A1C7731E57C1A1C2EC1AC9827F3E5BEEE7F8069A5F87DD | |||
| 2960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF246cf3.TMP | text | |
MD5:92BE6B127E72365885AD4C3FB6534EE2 | SHA256:54302A2573ACC775720E7DB0AD85873276713302B4F72596A8DCC44B01C70E51 | |||
| 2960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF246d22.TMP | text | |
MD5:197882774A7ECEC9046BC48F63189B66 | SHA256:27377B0D5F989997C2C3F74ACF163EED44B60631DDAA768F6655D7BE555742B2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
256
TCP/UDP connections
304
DNS requests
221
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2960 | chrome.exe | GET | 200 | 104.27.191.179:80 | http://watchfomny.tv/Video/Portugal/Sport-tv1/logo.gif | US | image | 1.93 Kb | whitelisted |
2960 | chrome.exe | GET | 200 | 104.27.191.179:80 | http://watchfomny.tv/Video/Portugal/Sport-tv1/Sport-tv-1.php | US | html | 28.2 Kb | whitelisted |
2960 | chrome.exe | GET | 200 | 104.27.191.179:80 | http://watchfomny.tv/images/styles-2.css | US | text | 234 b | whitelisted |
2960 | chrome.exe | GET | 200 | 104.27.191.179:80 | http://watchfomny.tv/popunder/popunder03.js | US | text | 662 b | whitelisted |
2960 | chrome.exe | GET | 200 | 104.27.191.179:80 | http://watchfomny.tv/images/play--5.gif | US | image | 2.98 Kb | whitelisted |
2960 | chrome.exe | GET | 200 | 188.72.202.157:80 | http://luckypushh.com/ntfc.php?p=2118719 | NL | text | 4.18 Kb | whitelisted |
2960 | chrome.exe | GET | 200 | 104.27.191.179:80 | http://watchfomny.tv/images/play-1.gif | US | image | 1.94 Kb | whitelisted |
2960 | chrome.exe | GET | 200 | 104.27.191.179:80 | http://watchfomny.tv/images/play--4.gif | US | image | 2.94 Kb | whitelisted |
2960 | chrome.exe | GET | 200 | 104.27.191.179:80 | http://watchfomny.tv/images/home.gif | US | image | 650 b | whitelisted |
2960 | chrome.exe | GET | 200 | 104.27.191.179:80 | http://watchfomny.tv/images/logo-New.jpg | US | image | 10.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2960 | chrome.exe | 157.240.1.23:80 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
2960 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2960 | chrome.exe | 104.27.191.179:80 | watchfomny.tv | Cloudflare Inc | US | shared |
2960 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2960 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2960 | chrome.exe | 104.20.111.39:80 | static.addtoany.com | Cloudflare Inc | US | shared |
2960 | chrome.exe | 216.58.205.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2960 | chrome.exe | 104.20.50.111:80 | cdn.adtrue.com | Cloudflare Inc | US | shared |
2960 | chrome.exe | 88.85.66.235:443 | pushwhy.com | Webzilla B.V. | NL | unknown |
2960 | chrome.exe | 157.240.1.23:443 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
watchfomny.tv |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
static.addtoany.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
luckypushh.com |
| whitelisted |
defpush.com |
| suspicious |
connect.facebook.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2960 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS WindowBase64.atob Function In Edwards Packed JavaScript - Possible iFrame Injection Detected |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2960 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2960 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |