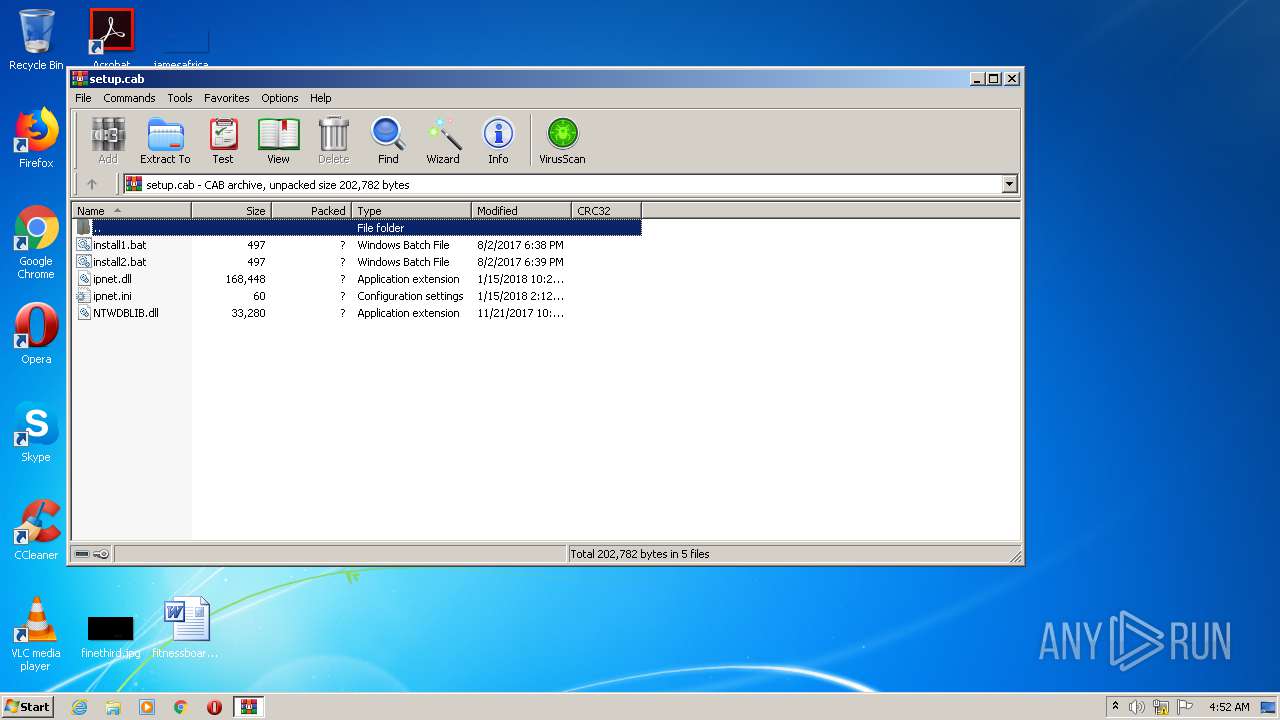
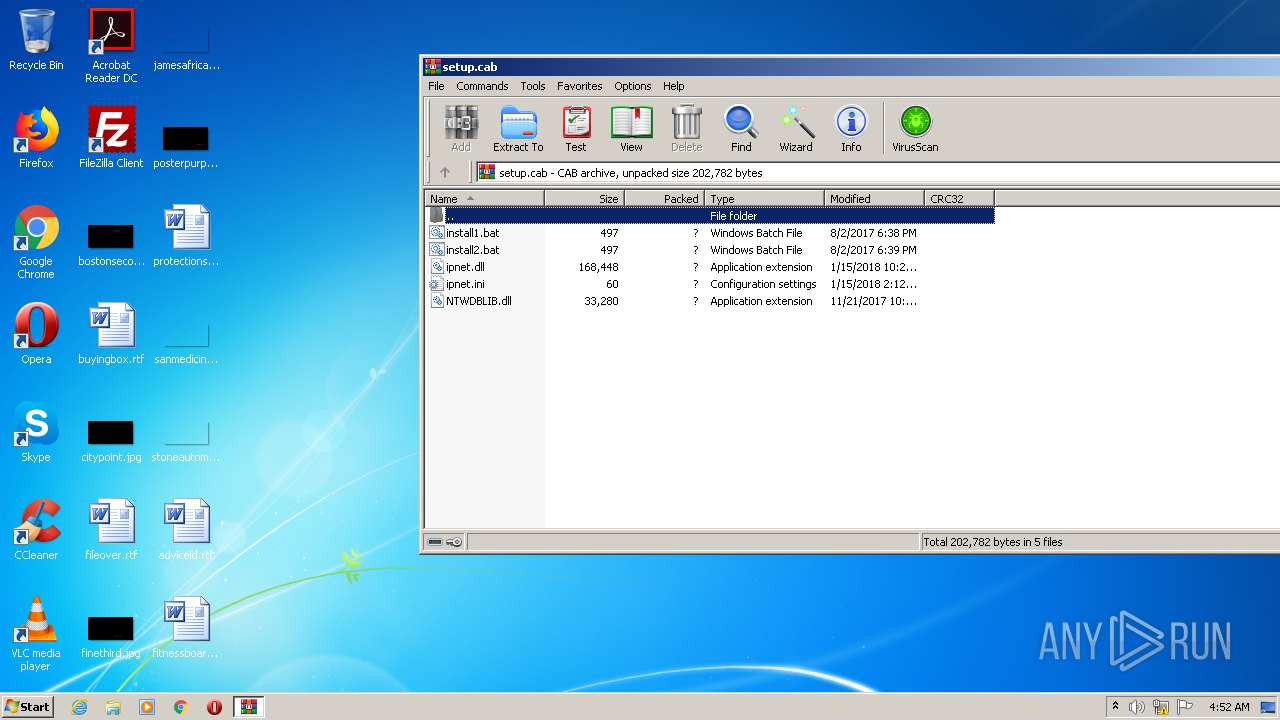
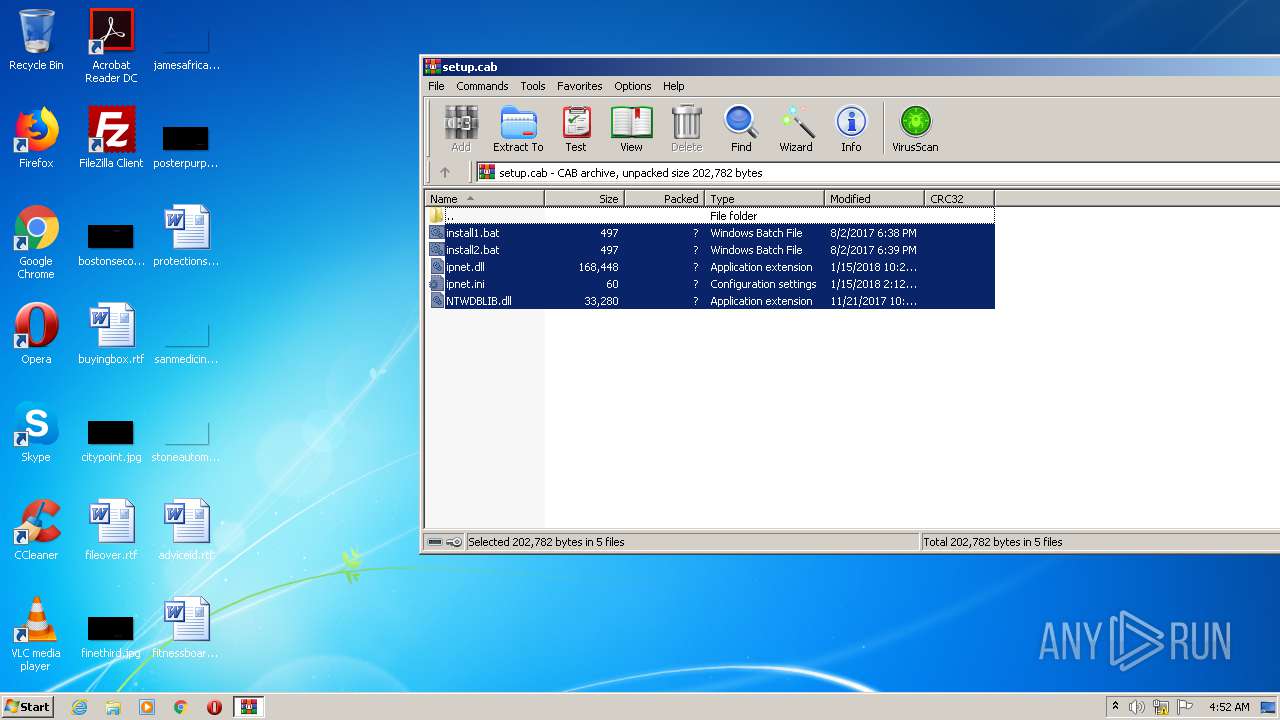
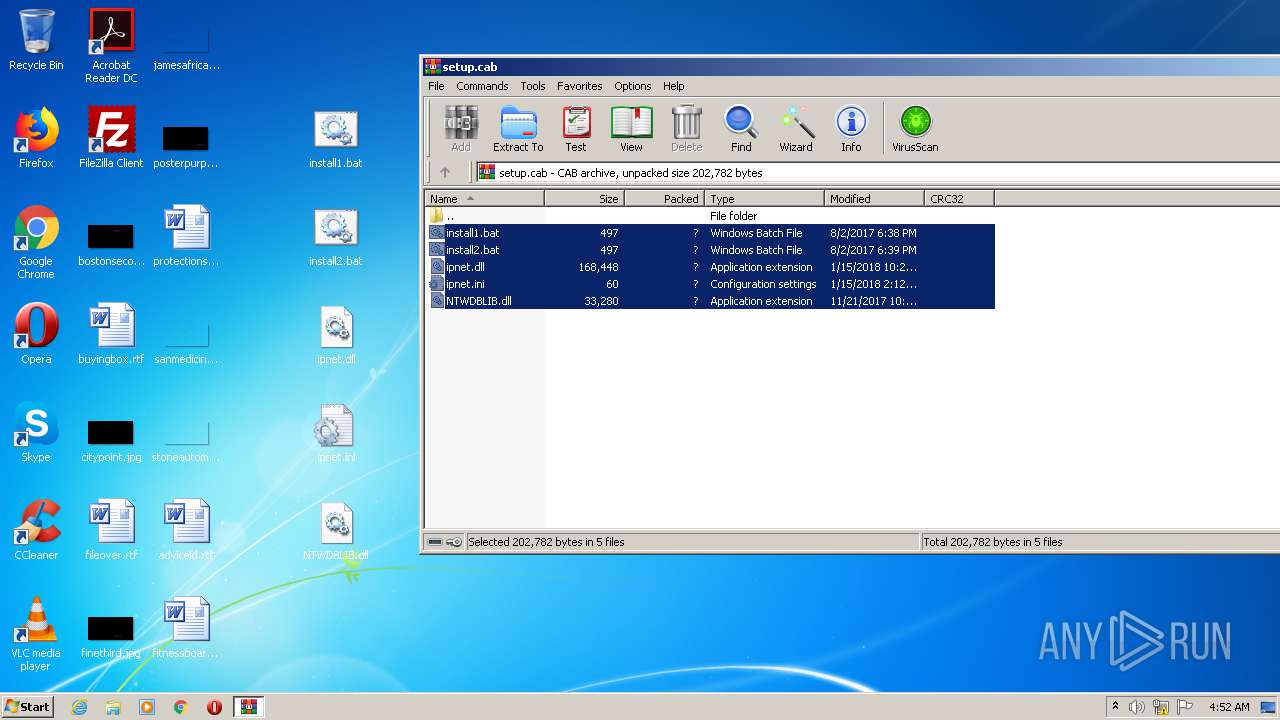
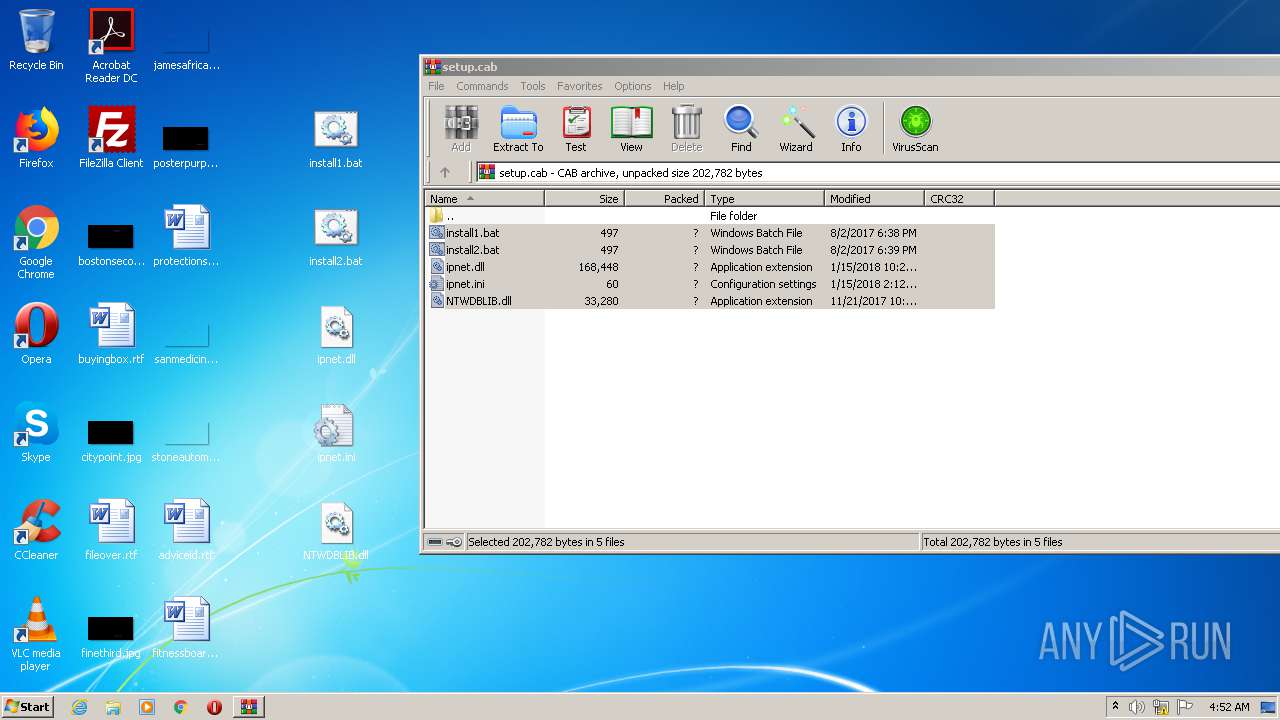
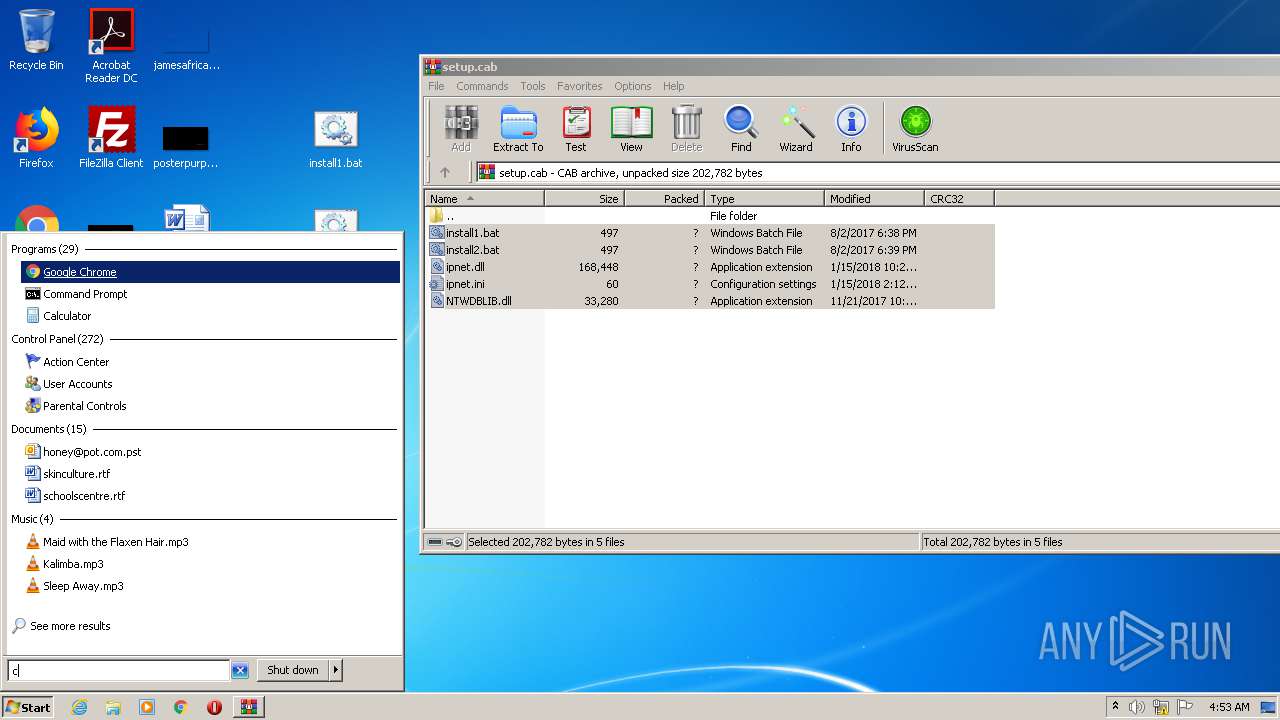
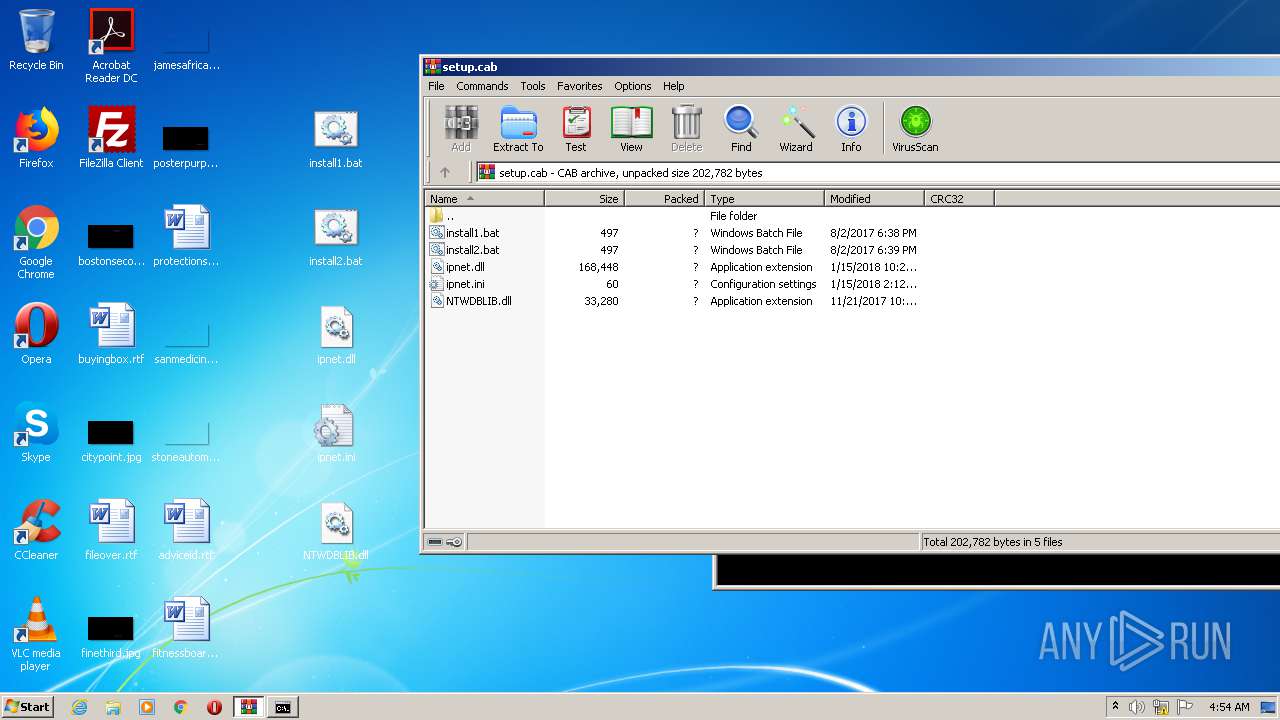
| File name: | setup.cab |
| Full analysis: | https://app.any.run/tasks/ecf0621b-cee5-49f3-9a3c-5ee62c381419 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 03:52:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-cab-compressed |
| File info: | Microsoft Cabinet archive data, 178905 bytes, 5 files |
| MD5: | 8B6962B35209039276B3088830463DF9 |
| SHA1: | DF44D9E288E6899D6D8EE270CB77DB2147D8808E |
| SHA256: | 114C58BEEE239BDFA9166AF50397AEE81505BCA9596F05EE74E239F8E6132E4B |
| SSDEEP: | 3072:0ECTCJk6ab+xCyIMjuoRTvGsu/bVDQHh1DvN/k6H94t6movN+h+JrCI9hxsQZY2z:mCo+xCI9RTvVu6lQaQhar2QZYgb |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2876)
- explorer.exe (PID: 352)
- rundll32.exe (PID: 2864)
Runs app for hidden code execution
- explorer.exe (PID: 352)
SUSPICIOUS
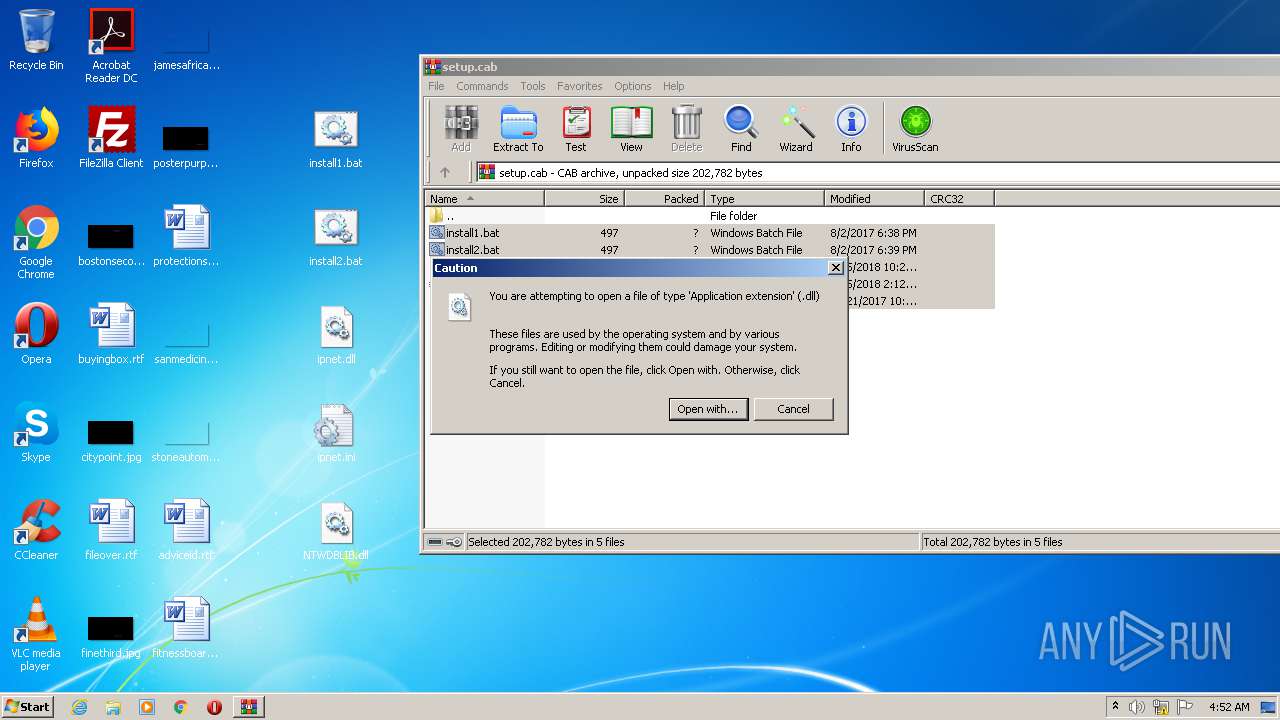
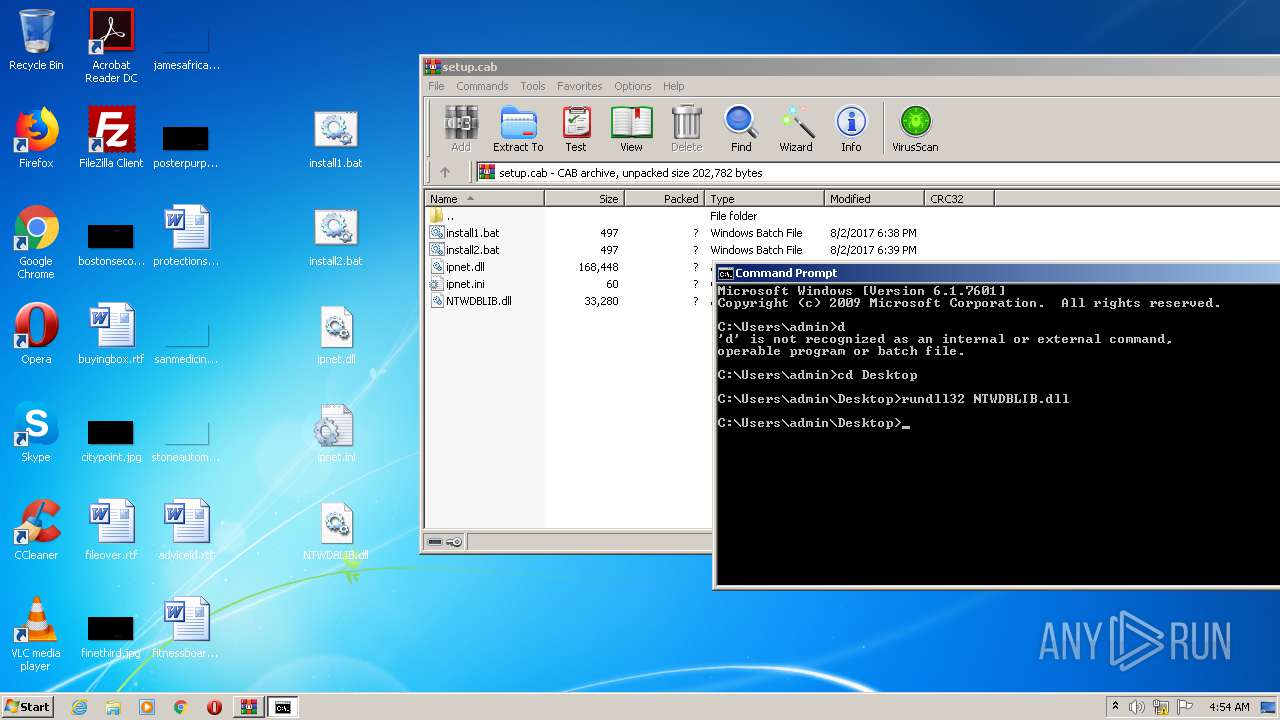
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 352)
- cmd.exe (PID: 1876)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 352)
- rundll32.exe (PID: 2864)
Starts SC.EXE for service management
- cmd.exe (PID: 3276)
- cmd.exe (PID: 2756)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3276)
- cmd.exe (PID: 2756)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2608)
Reads Internet Cache Settings
- rundll32.exe (PID: 2864)
INFO
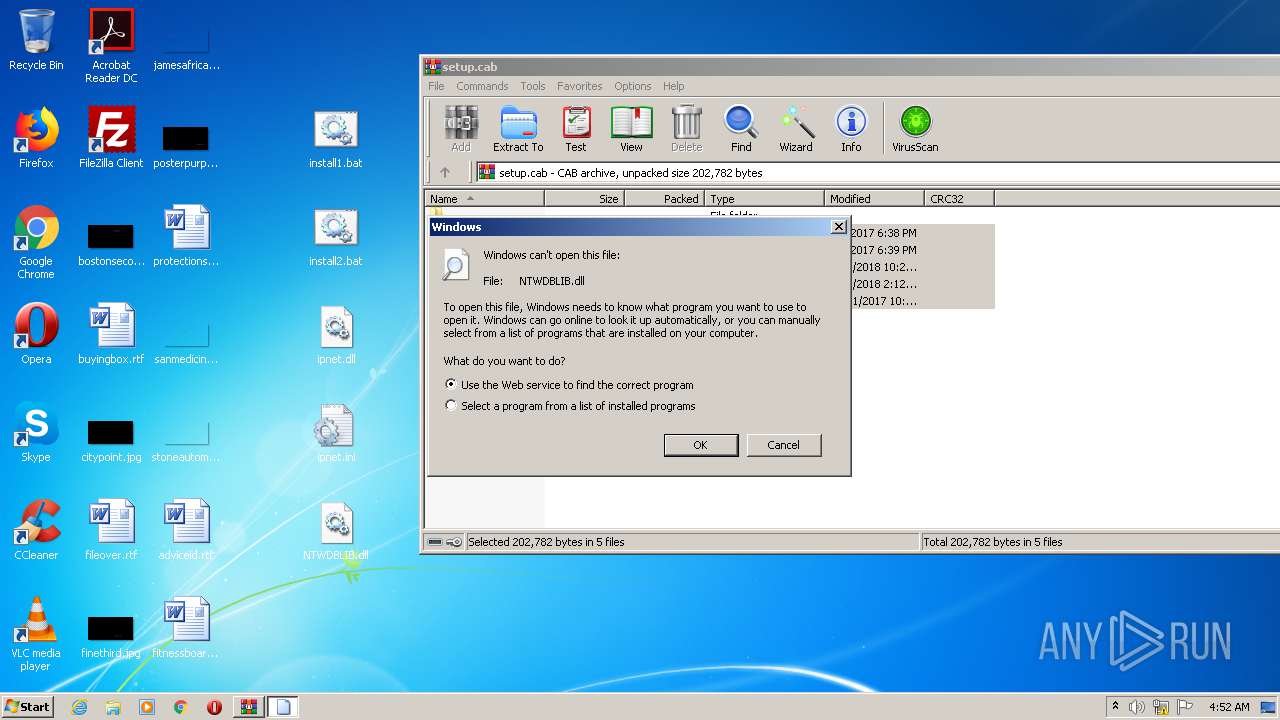
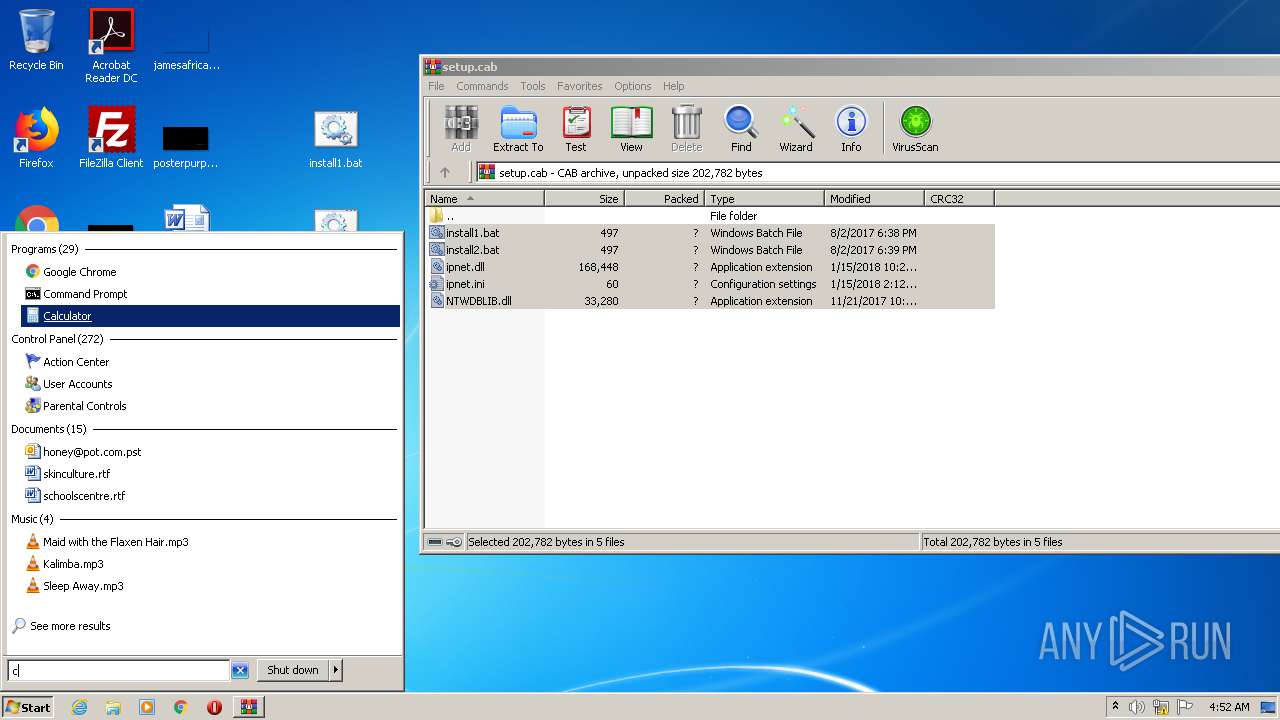
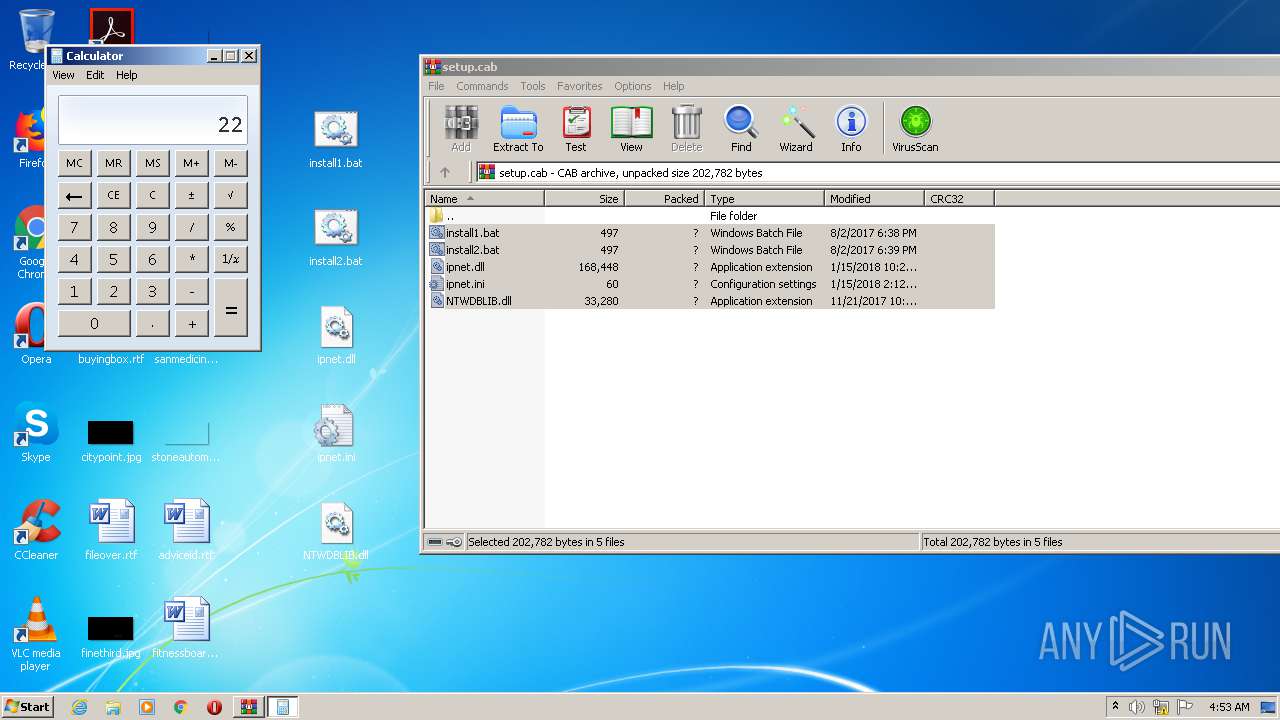
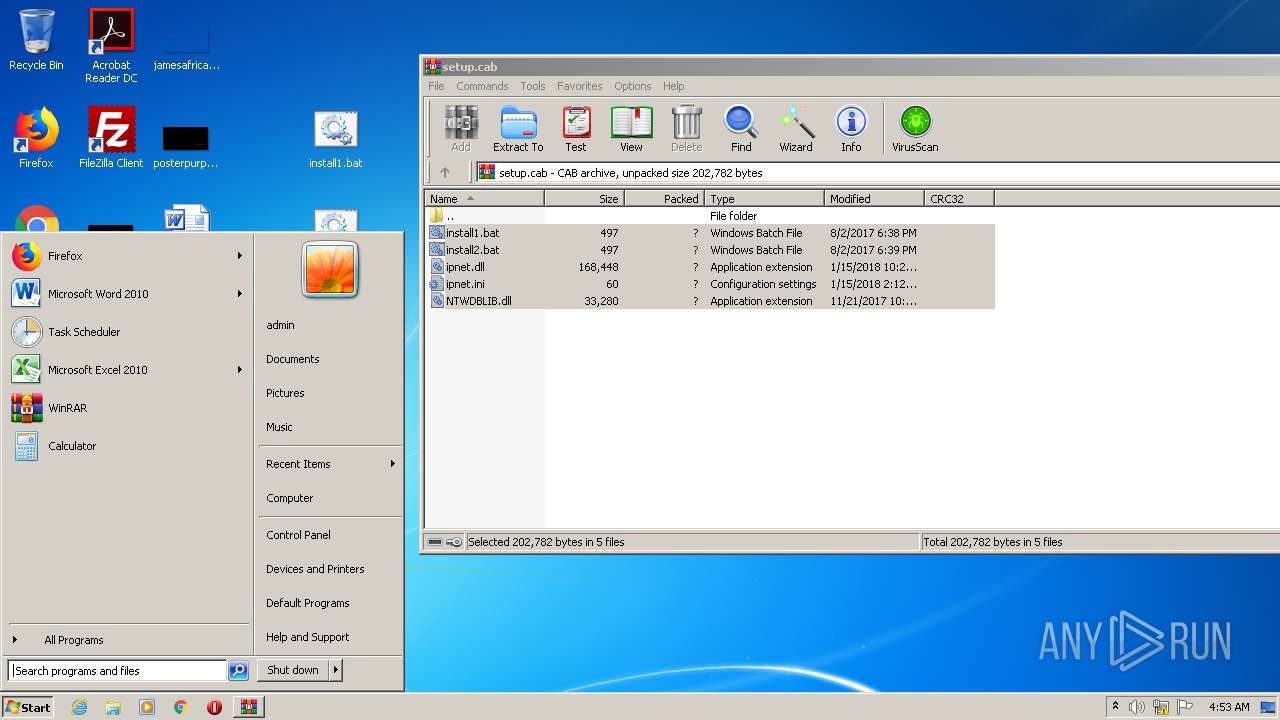
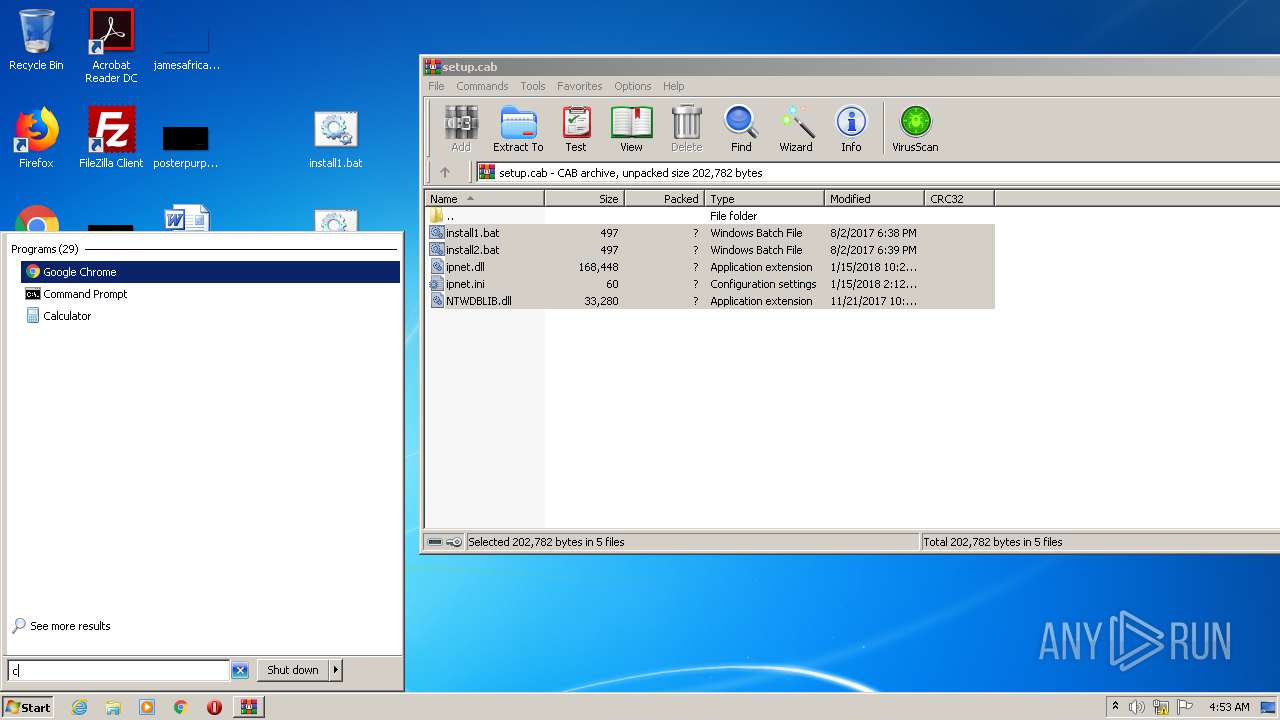
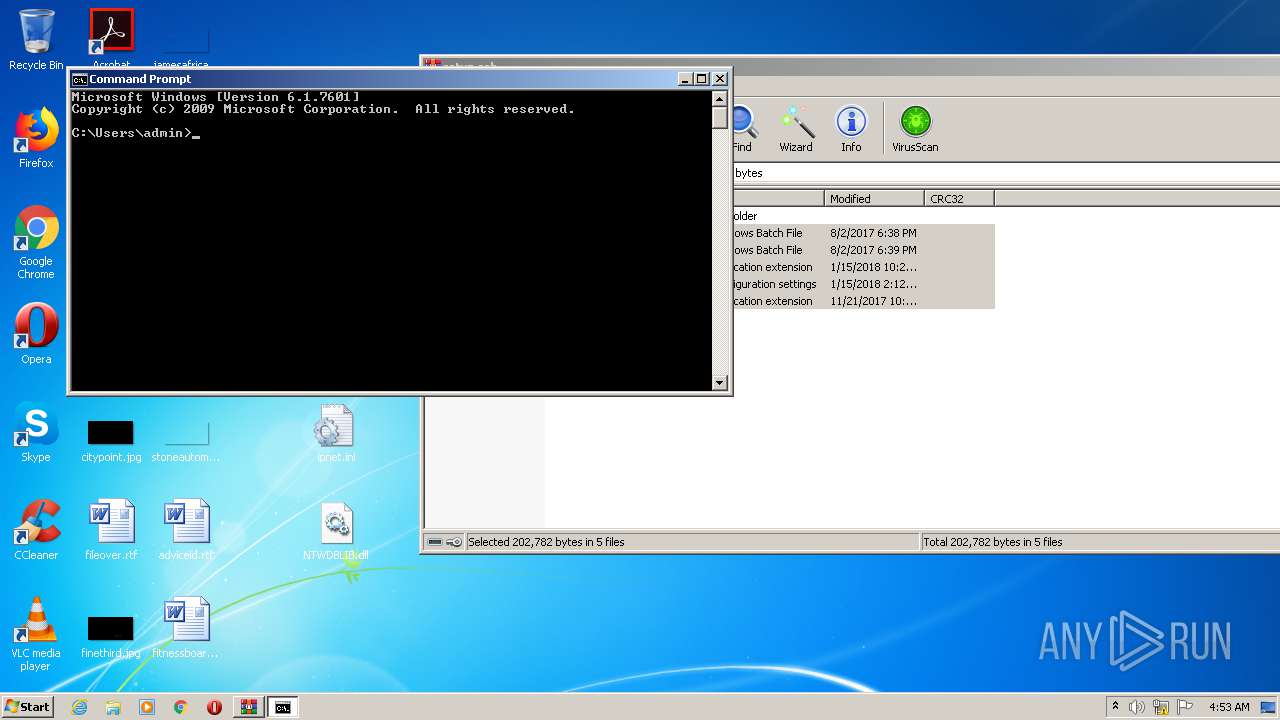
Manual execution by user
- cmd.exe (PID: 1876)
- rundll32.exe (PID: 2572)
- calc.exe (PID: 1236)
- cmd.exe (PID: 3276)
- cmd.exe (PID: 2756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .cab | | | Microsoft Cabinet Archive (100) |
|---|
Total processes
61
Monitored processes
24
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 492 | rundll32 ipnet.dll | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | rundll32 ipnet.dll | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1020 | taskkill /im cliconfg.exe /f /t | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1128 | reg add "HKLM\SYSTEM\CurrentControlSet\Services\COMSysApp\Parameters" /v ServiceDll /t REG_EXPAND_SZ /d "C:\Windows\system32\ipnet.dll" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1236 | "C:\Windows\system32\calc.exe" | C:\Windows\system32\calc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1876 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2056 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SvcHost" /v COMSysApp /t REG_MULTI_SZ /d "COMSysApp" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2180 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\setup.cab" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2244 | sc config COMSysApp type= own start= auto error= normal binpath= "C:\Windows\SysWOW64\svchost.exe -k COMSysApp" | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 174
Read events
1 661
Write events
513
Delete events
0
Modification events
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\setup.cab | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.cab\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
Executable files
2
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2180 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2180.28700\install1.bat | — | |
MD5:— | SHA256:— | |||
| 2180 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2180.28700\install2.bat | — | |
MD5:— | SHA256:— | |||
| 2180 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2180.28700\ipnet.dll | — | |
MD5:— | SHA256:— | |||
| 2180 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2180.28700\ipnet.ini | — | |
MD5:— | SHA256:— | |||
| 2180 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2180.28700\NTWDBLIB.dll | — | |
MD5:— | SHA256:— | |||
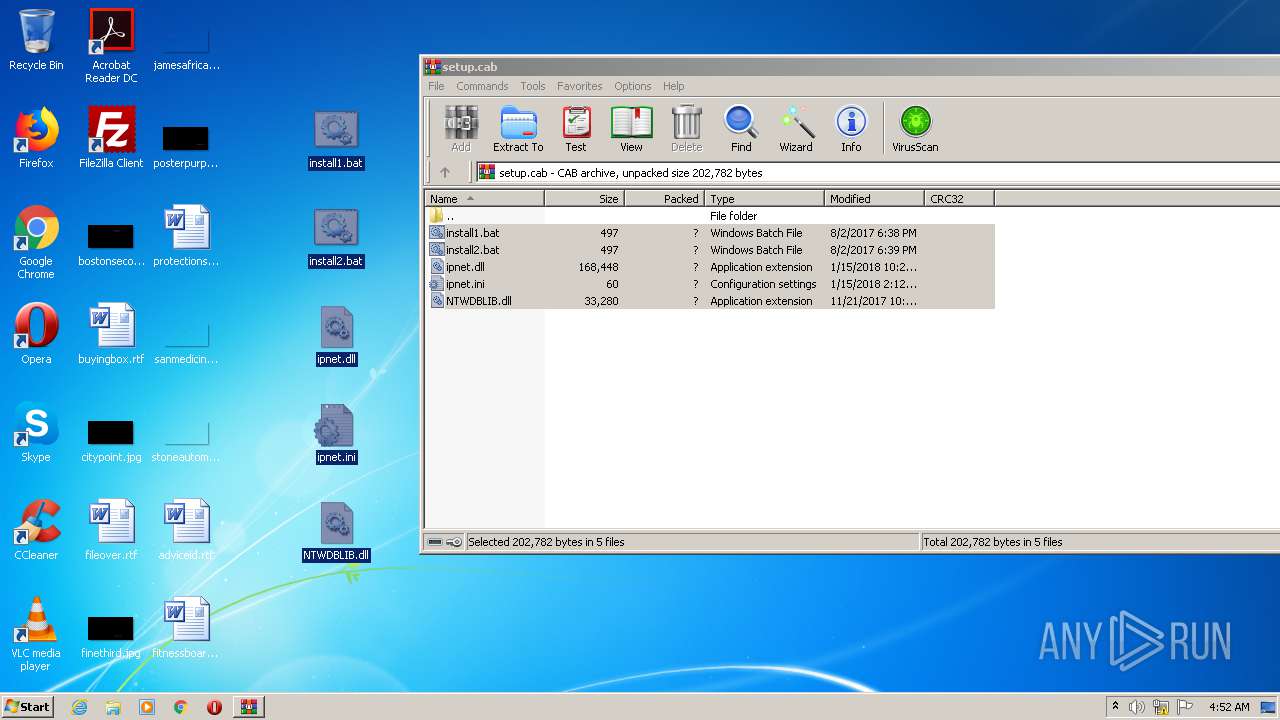
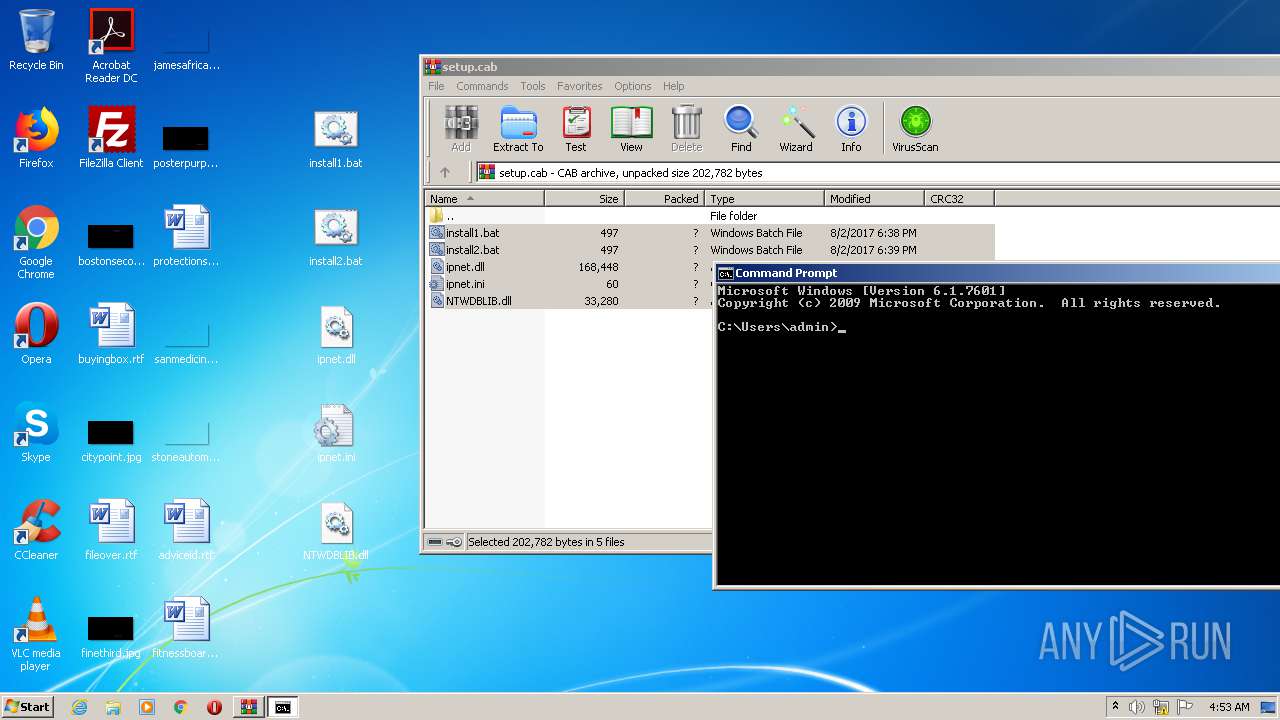
| 352 | explorer.exe | C:\Users\admin\Desktop\install2.bat | text | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\Desktop\ipnet.ini | text | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\Desktop\install1.bat | text | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\Desktop\ipnet.dll | executable | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\Desktop\NTWDBLIB.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
rundll32.exe | [ServiceMain] |
rundll32.exe | C:\Windows\system32\ipnet.ini |
rundll32.exe | C:\Windows\system32\ipnet.ini |
rundll32.exe | [DLL_PROCESS_ATTACH] |
rundll32.exe | [ThreadFunc] |
rundll32.exe | [GetFTPAccountInfo_10001712] |
rundll32.exe | [sub_100024D4] |
rundll32.exe | [sub_10001000] |
rundll32.exe | 111 |
rundll32.exe | USER-PC |