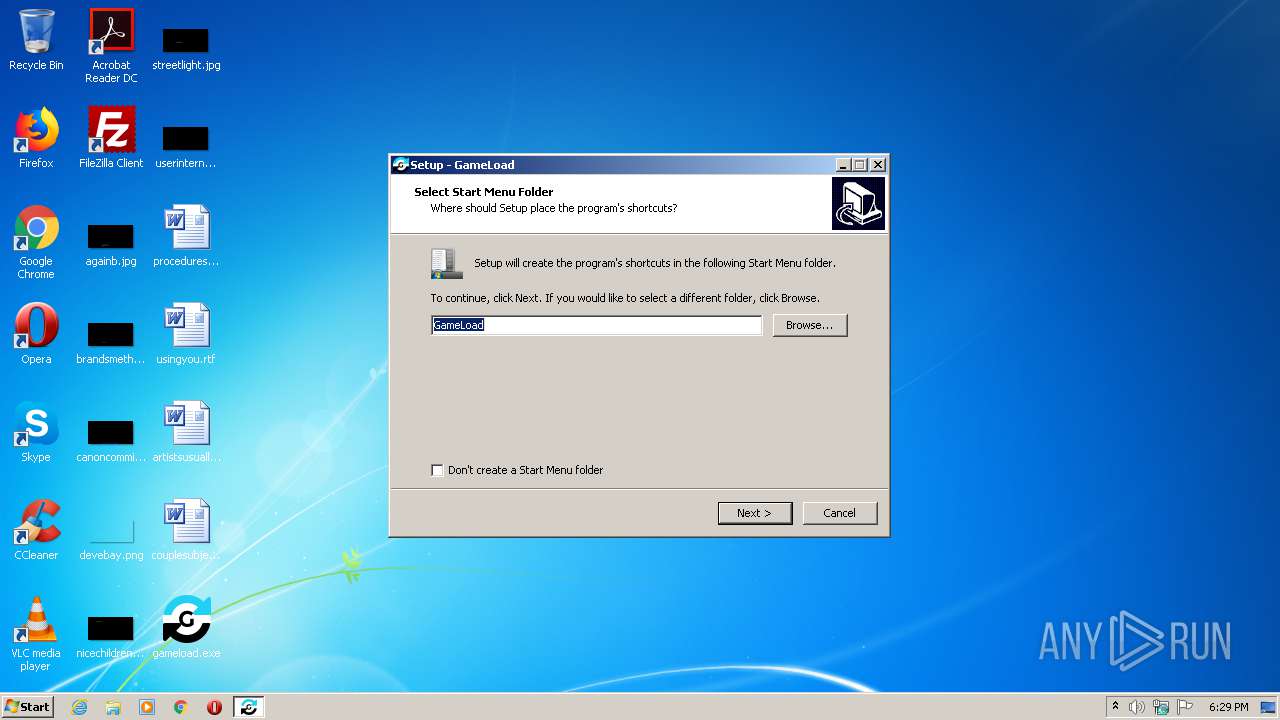
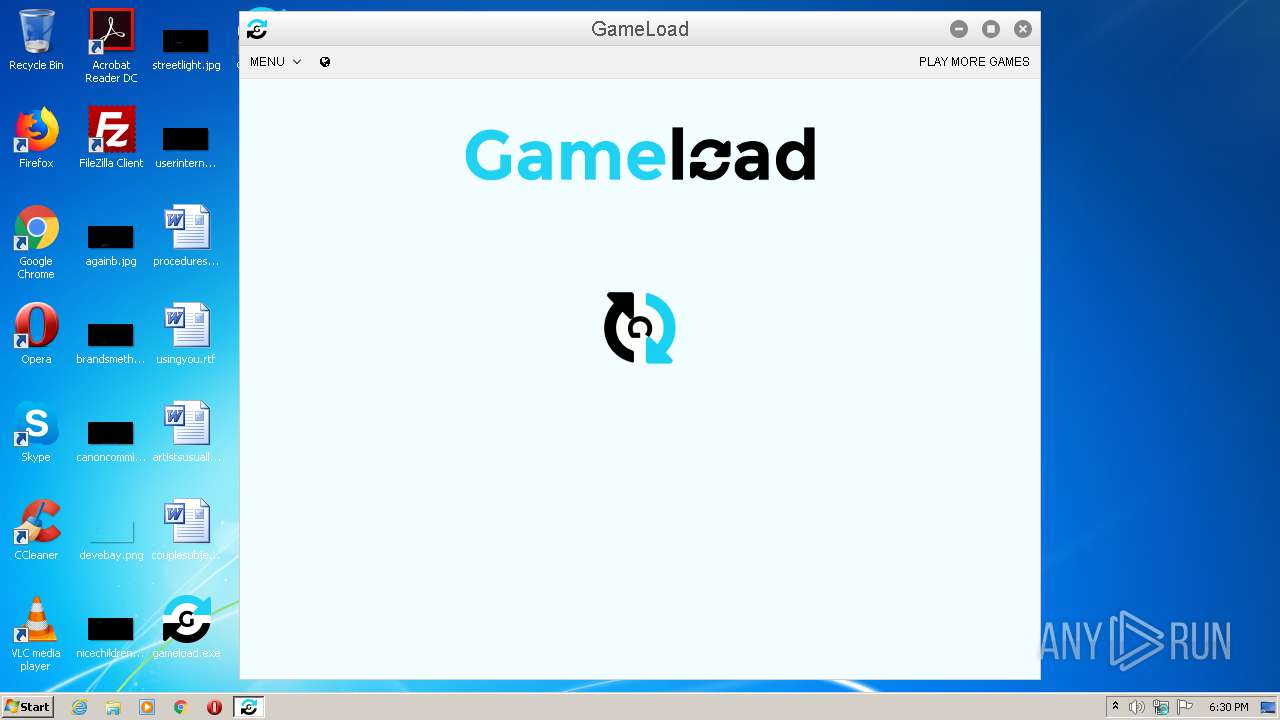
| download: | gameload.exe |
| Full analysis: | https://app.any.run/tasks/f87d6563-a47e-43f0-856a-558cd6e4b70e |
| Verdict: | Malicious activity |
| Analysis date: | July 01, 2020, 17:29:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CBA85F2454AEC9F775671BE8A83201A6 |
| SHA1: | 38B8F9762F789867F54FEF68A54AEA493DFE794D |
| SHA256: | 111F9AF1A6915C9D6DB9FE8606E42E8D1C6EFB973264EF7E1349E021DFA9C5E7 |
| SSDEEP: | 393216:tXW8Hz7rMlxIG30MXe+KB4eDvqBnnjC19MPmMmY1ZXF1TxY36uwxY8IktVoNPDMi:t7IIG3rPKB4eWNZJr3FDYKFLI+oTh |
MALICIOUS
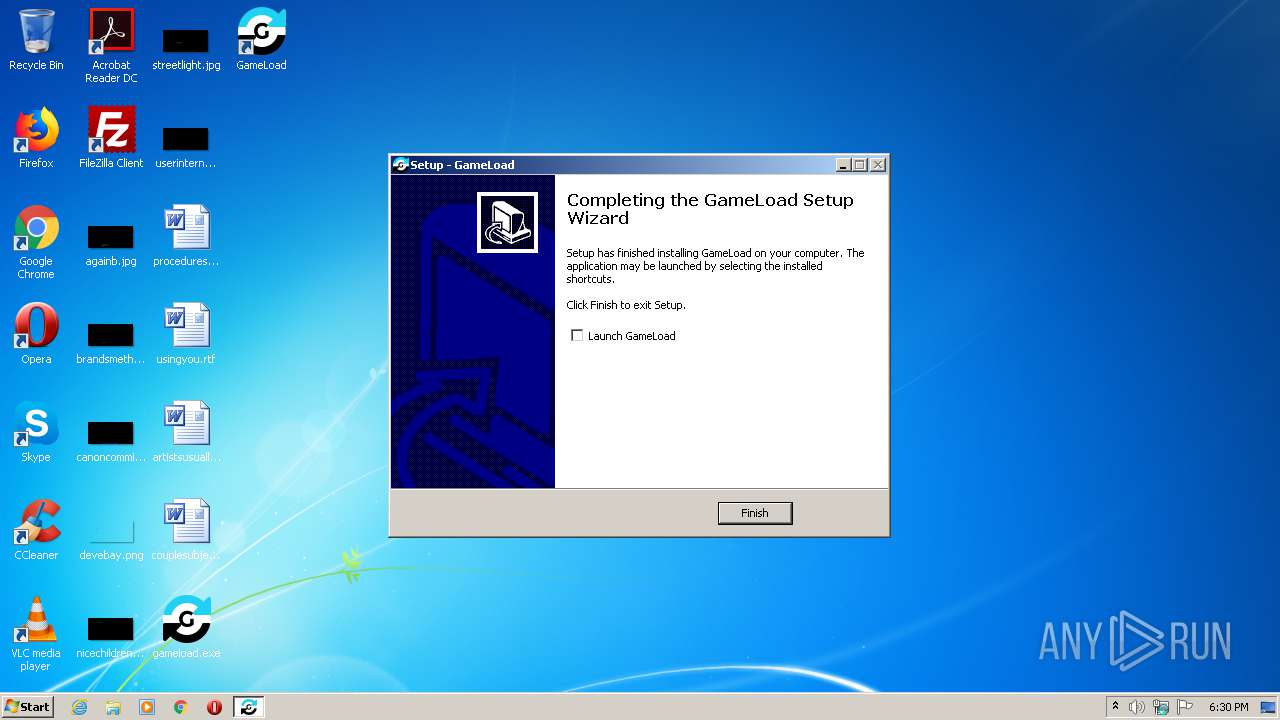
Loads dropped or rewritten executable
- GameLoad.exe (PID: 2124)
- GameLoad.exe (PID: 3196)
- GameLoad.exe (PID: 3872)
- GameLoad.exe (PID: 308)
- GameLoad.exe (PID: 2388)
SUSPICIOUS
Reads the Windows organization settings
- gameload.tmp (PID: 3076)
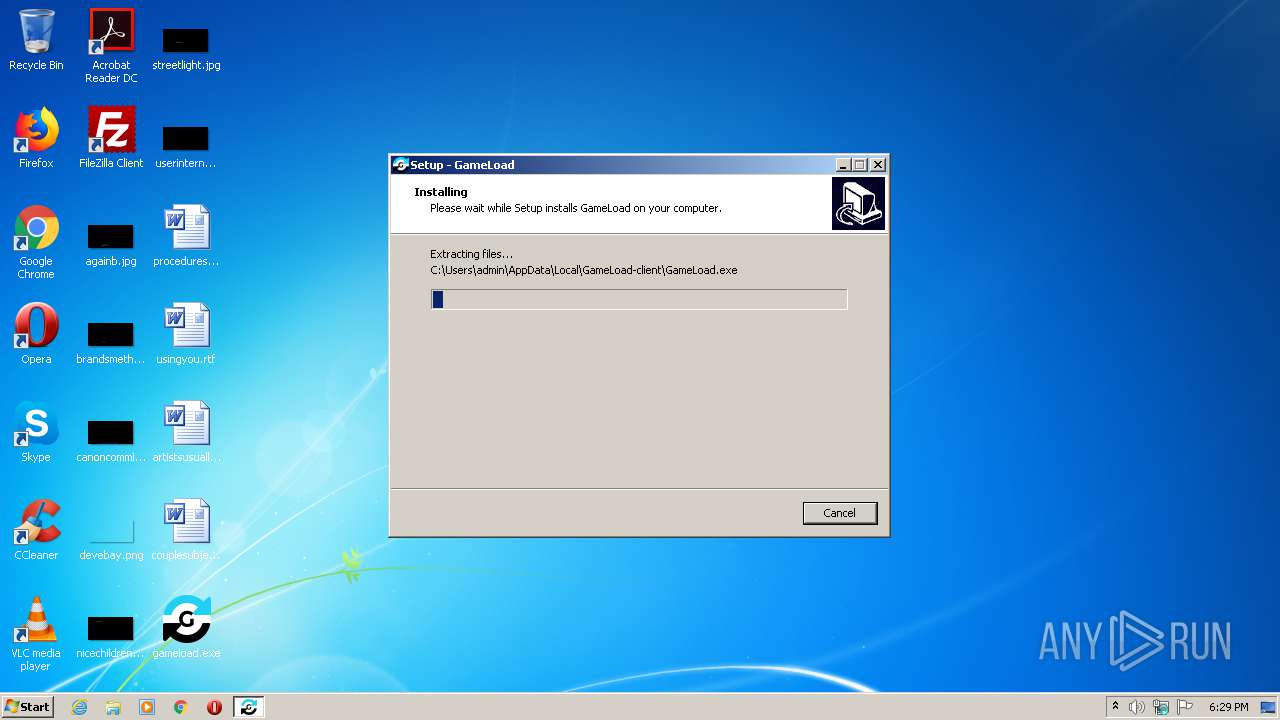
Executable content was dropped or overwritten
- gameload.exe (PID: 4032)
- gameload.exe (PID: 2580)
- gameload.tmp (PID: 3076)
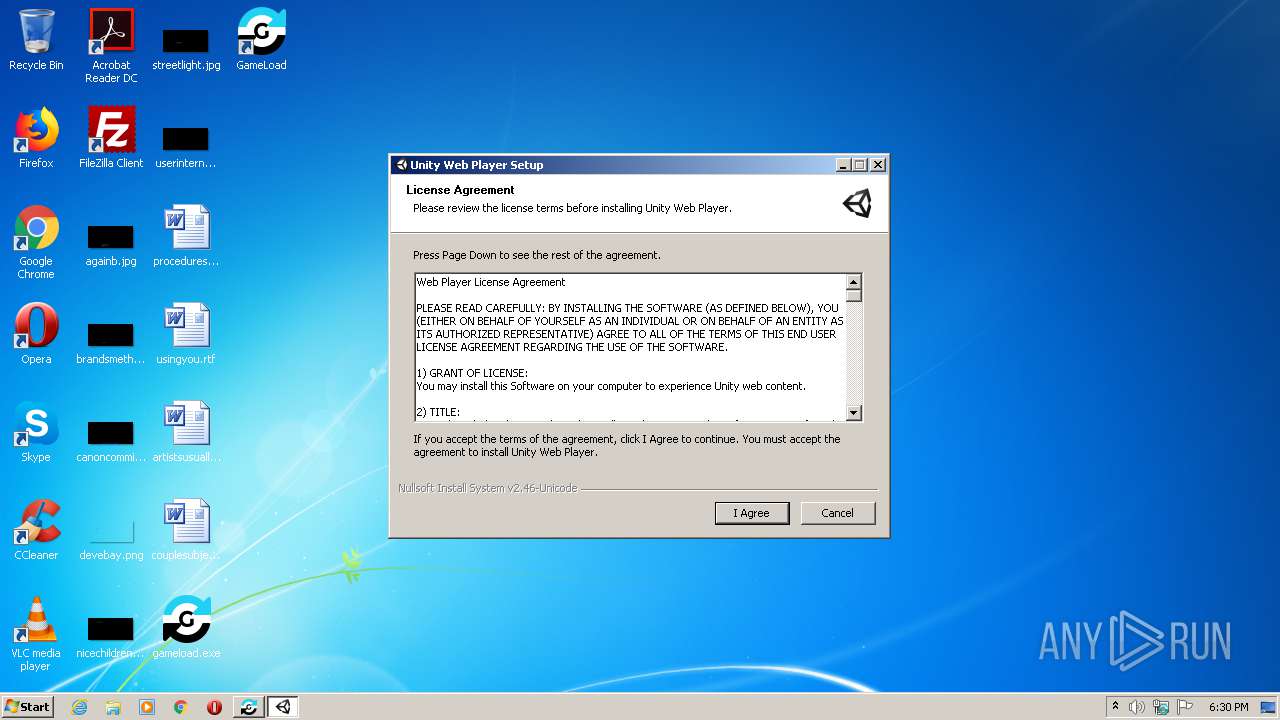
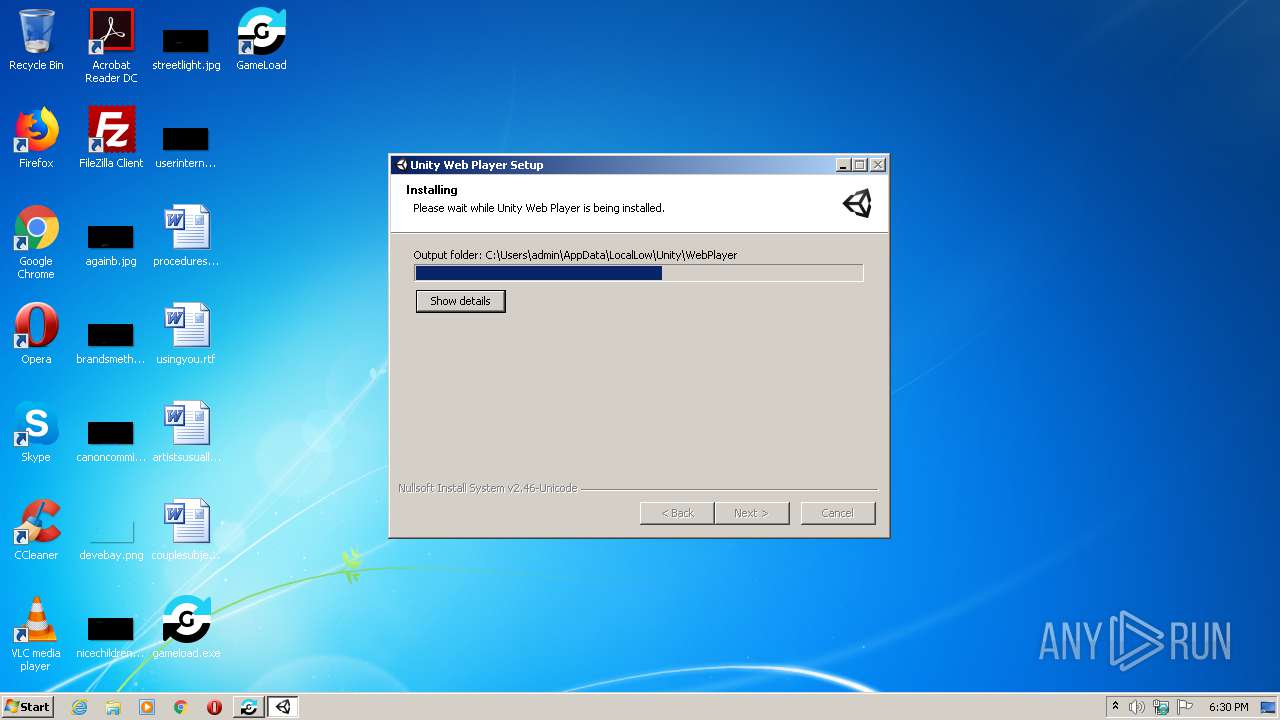
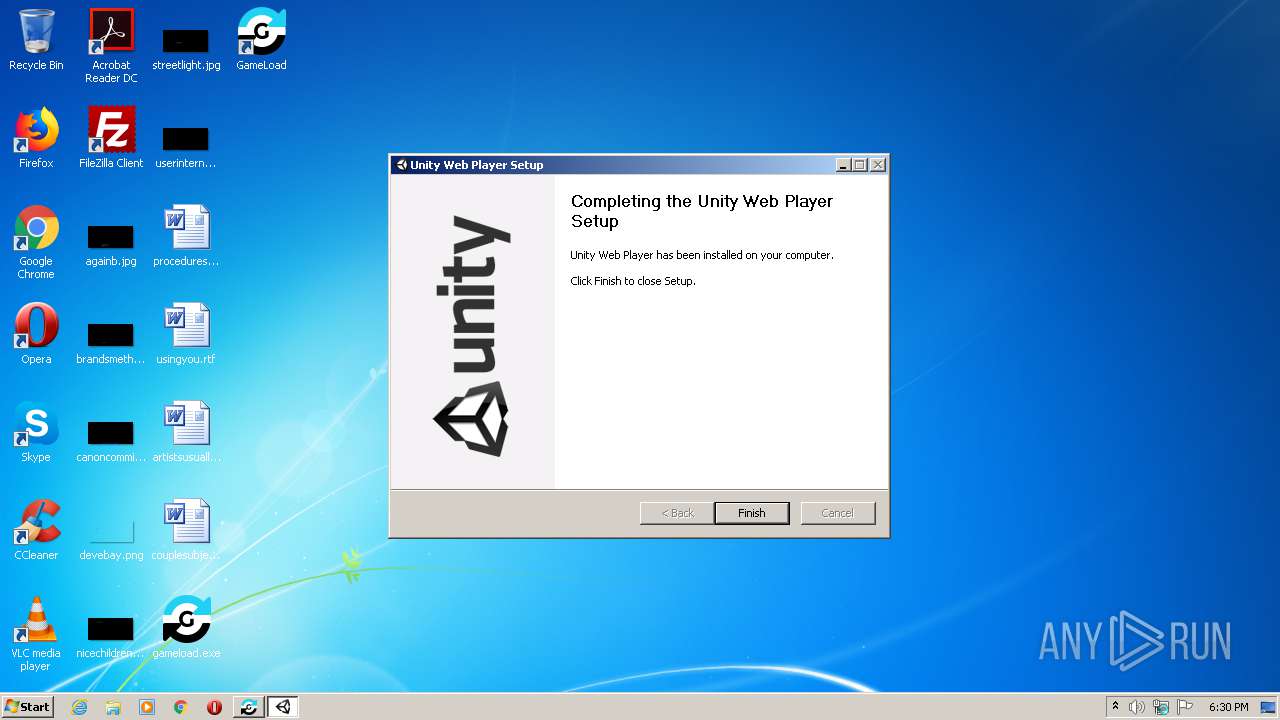
- UnityWebPlayer.exe (PID: 1828)
- GameLoad.exe (PID: 2388)
- GameLoad.exe (PID: 308)
Reads Windows owner or organization settings
- gameload.tmp (PID: 3076)
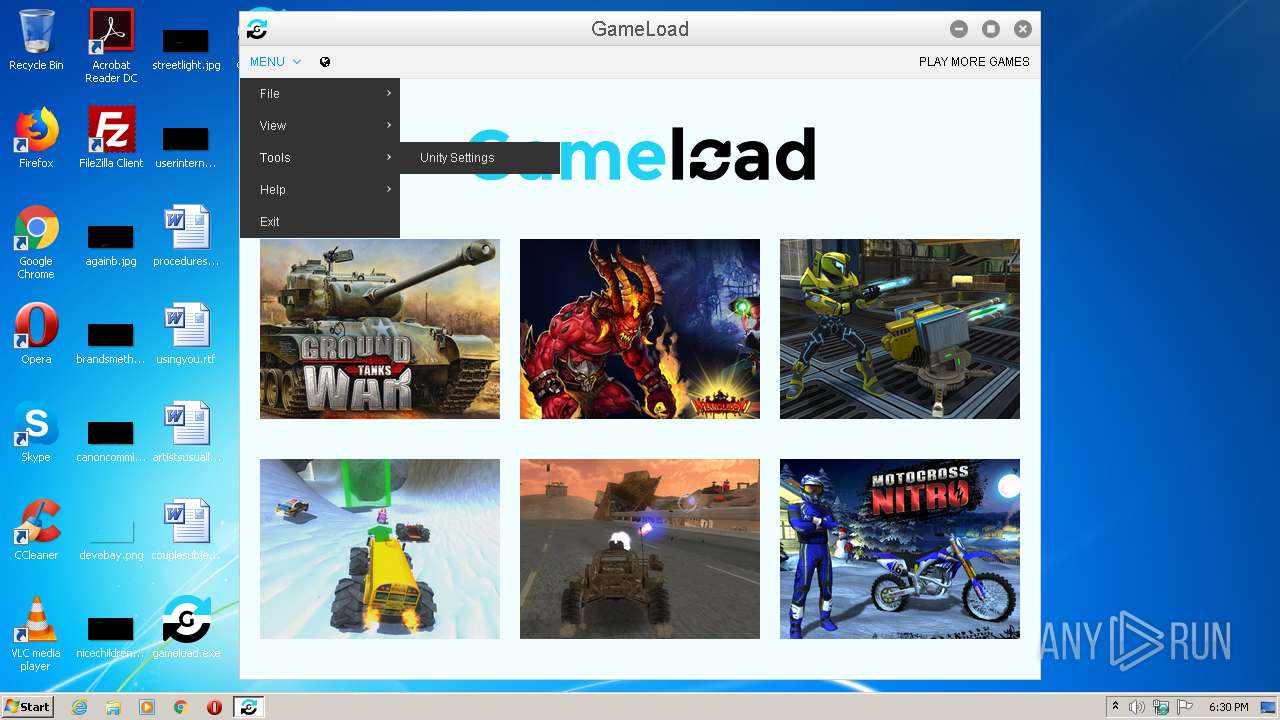
Modifies the open verb of a shell class
- gameload.tmp (PID: 3076)
Application launched itself
- GameLoad.exe (PID: 2388)
INFO
Application was dropped or rewritten from another process
- gameload.tmp (PID: 3076)
- UnityWebPlayer.exe (PID: 1828)
- gameload.tmp (PID: 2296)
Creates files in the program directory
- gameload.tmp (PID: 3076)
Creates a software uninstall entry
- gameload.tmp (PID: 3076)
- UnityWebPlayer.exe (PID: 1828)
Loads dropped or rewritten executable
- UnityWebPlayer.exe (PID: 1828)
Reads the hosts file
- GameLoad.exe (PID: 2388)
Dropped object may contain Bitcoin addresses
- GameLoad.exe (PID: 2388)
- GameLoad.exe (PID: 308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 419328 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
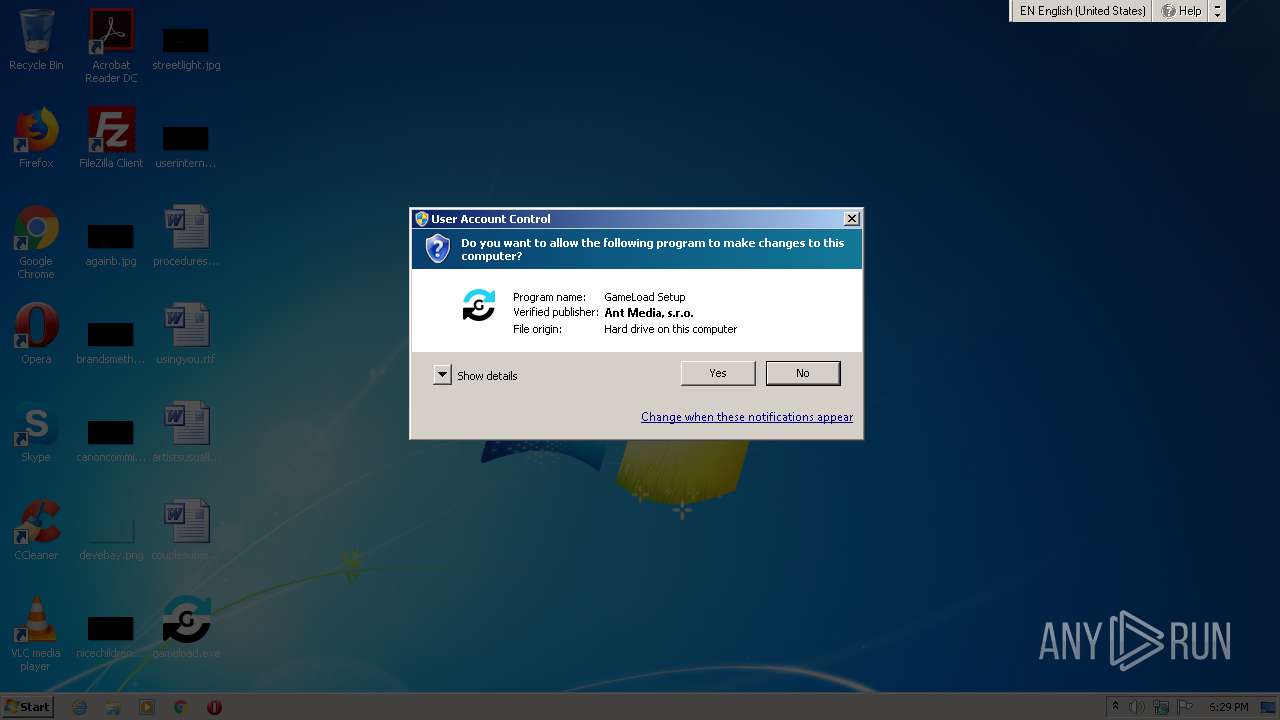
| CompanyName: | Ant Media, s. r. o. |
| FileDescription: | GameLoad Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | GameLoad |
| ProductVersion: | 2.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Ant Media, s. r. o. |
| FileDescription: | GameLoad Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | GameLoad |
| ProductVersion: | 2.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00064408 | 0x00064600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.76917 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.3629 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.96727 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.76267 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.42267 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.22422 | 270376 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
50
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.exe" --type=plugin --plugin-path="C:\Users\admin\AppData\Local\Temp\nw2388_28072\plugins\npUnity3D32.dll" --no-sandbox --lang=en-US --channel="2388.3.1358330771\138780653" /prefetch:-390060480 | C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.exe | GameLoad.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1828 | "C:\Users\admin\AppData\Local\Temp\is-M0VAF.tmp\UnityWebPlayer.exe" | C:\Users\admin\AppData\Local\Temp\is-M0VAF.tmp\UnityWebPlayer.exe | gameload.tmp | ||||||||||||
User: admin Company: Unity Technologies ApS Integrity Level: HIGH Description: Unity Web Player Installer Exit code: 0 Version: 5.2.0.0 Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.exe" --type=gpu-process --channel="2388.0.1159334471\222130326" --no-sandbox --supports-dual-gpus=false --gpu-driver-bug-workarounds=1,18,40 --gpu-vendor-id=0x1234 --gpu-device-id=0x1111 --gpu-driver-vendor=Microsoft --gpu-driver-version=6.1.7600.16385 /prefetch:822062411 | C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.exe | — | GameLoad.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2296 | "C:\Users\admin\AppData\Local\Temp\is-9R3VD.tmp\gameload.tmp" /SL5="$30138,25160827,486912,C:\Users\admin\Desktop\gameload.exe" | C:\Users\admin\AppData\Local\Temp\is-9R3VD.tmp\gameload.tmp | — | gameload.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2388 | "C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.exe" | C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.exe | gameload.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2580 | "C:\Users\admin\Desktop\gameload.exe" /SPAWNWND=$20134 /NOTIFYWND=$30138 | C:\Users\admin\Desktop\gameload.exe | gameload.tmp | ||||||||||||
User: admin Company: Ant Media, s. r. o. Integrity Level: HIGH Description: GameLoad Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3076 | "C:\Users\admin\AppData\Local\Temp\is-J0IHN.tmp\gameload.tmp" /SL5="$20154,25160827,486912,C:\Users\admin\Desktop\gameload.exe" /SPAWNWND=$20134 /NOTIFYWND=$30138 | C:\Users\admin\AppData\Local\Temp\is-J0IHN.tmp\gameload.tmp | gameload.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3196 | "C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.exe" --type=renderer --no-sandbox --enable-deferred-image-decoding --lang=en-US --extension-process --user-agent="Mozilla/5.0 (Windows NT 6.1) Gecko/20100101 Firefox/40.0" --nodejs --working-directory="C:\Users\admin\AppData\Local\Temp\nw2388_28072" --device-scale-factor=1 --font-cache-shared-mem-suffix=2388 --enable-pinch-virtual-viewport --enable-delegated-renderer --num-raster-threads=2 --enable-gpu-rasterization --channel="2388.1.2024540143\1319580203" /prefetch:673131151 | C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.exe | GameLoad.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3872 | "C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.exe" --type=renderer --no-sandbox --enable-deferred-image-decoding --lang=en-US --extension-process --user-agent="Mozilla/5.0 (Windows NT 6.1) Gecko/20100101 Firefox/40.0" --nodejs --working-directory="C:\Users\admin\AppData\Local\Temp\nw2388_28072" --device-scale-factor=1 --font-cache-shared-mem-suffix=2388 --enable-pinch-virtual-viewport --enable-delegated-renderer --num-raster-threads=2 --enable-gpu-rasterization --channel="2388.2.2044434615\412989862" /prefetch:673131151 | C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.exe | — | GameLoad.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4032 | "C:\Users\admin\Desktop\gameload.exe" | C:\Users\admin\Desktop\gameload.exe | explorer.exe | ||||||||||||
User: admin Company: Ant Media, s. r. o. Integrity Level: MEDIUM Description: GameLoad Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
864
Read events
749
Write events
109
Delete events
6
Modification events
| (PID) Process: | (3076) gameload.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 040C00008ADE3938CD4FD601 | |||
| (PID) Process: | (3076) gameload.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: B058966A7E91F65A6E422DD8151BCCBB929657AC5632CBDDDCC8FDA4A062F9EE | |||
| (PID) Process: | (3076) gameload.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3076) gameload.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.exe | |||
| (PID) Process: | (3076) gameload.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: B08C37BD11FC0E7C899751D6E5DA4581DCD8001B978958DDFE994FB7B51700C0 | |||
| (PID) Process: | (3076) gameload.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\GameLoad |
| Operation: | write | Name: | |
Value: URL:GameLoad Protocol | |||
| (PID) Process: | (3076) gameload.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\GameLoad |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (3076) gameload.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\GameLoad\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.exe,0 | |||
| (PID) Process: | (3076) gameload.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\GameLoad\shell\open\command |
| Operation: | write | Name: | |
Value: "C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.exe" "%1" | |||
| (PID) Process: | (3076) gameload.tmp | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\NativeMessagingHosts\com.ant_media.game_load |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.json | |||
Executable files
32
Suspicious files
59
Text files
1 193
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3076 | gameload.tmp | C:\Users\admin\AppData\Local\GameLoad-client\is-Q55R1.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | gameload.tmp | C:\Users\admin\AppData\Local\GameLoad-client\is-RQ7H2.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | gameload.tmp | C:\Users\admin\AppData\Local\GameLoad-client\GameLoad.exe | — | |
MD5:— | SHA256:— | |||
| 3076 | gameload.tmp | C:\Users\admin\AppData\Local\GameLoad-client\is-TETFG.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | gameload.tmp | C:\Users\admin\AppData\Local\GameLoad-client\is-67MP0.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | gameload.tmp | C:\Users\admin\AppData\Local\Temp\is-M0VAF.tmp\is-5JMUL.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | gameload.tmp | C:\Users\admin\AppData\Local\GameLoad-client\is-VU8A7.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | gameload.tmp | C:\Users\admin\AppData\Local\GameLoad-client\nw.pak | — | |
MD5:— | SHA256:— | |||
| 3076 | gameload.tmp | C:\Users\admin\AppData\Local\GameLoad-client\is-AIPGA.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | gameload.tmp | C:\Users\admin\AppData\Local\GameLoad-client\icudtl.dat | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
10
DNS requests
5
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3196 | GameLoad.exe | GET | — | 172.67.186.64:80 | http://172.67.186.64:80/update-files/update/package.json | US | — | — | suspicious |
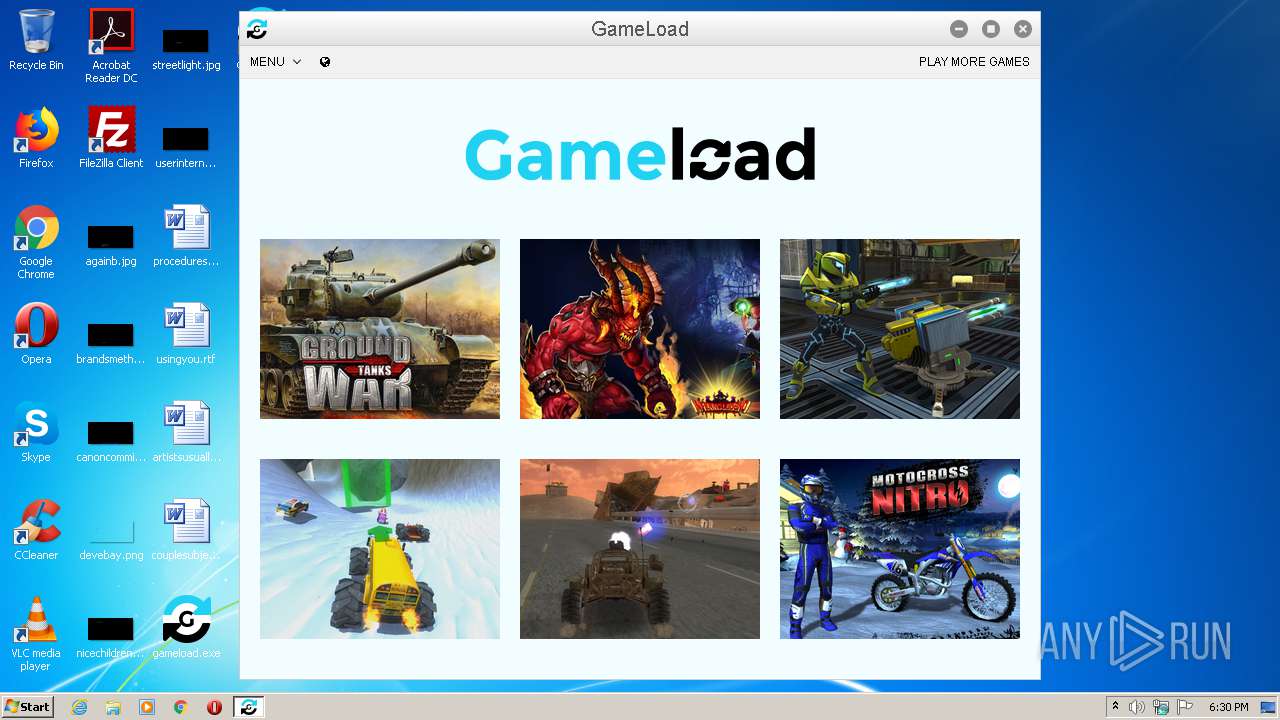
2388 | GameLoad.exe | GET | 200 | 104.27.158.159:80 | http://data.gameload.top/assets/5.jpg | US | image | 39.2 Kb | suspicious |
2388 | GameLoad.exe | GET | 200 | 104.27.158.159:80 | http://data.gameload.top/assets/3.jpg | US | image | 68.9 Kb | suspicious |
2388 | GameLoad.exe | GET | 200 | 104.27.158.159:80 | http://data.gameload.top/assets/2.jpg | US | image | 67.3 Kb | suspicious |
2388 | GameLoad.exe | GET | 200 | 104.27.158.159:80 | http://data.gameload.top/assets/4.jpg | US | image | 42.8 Kb | suspicious |
2388 | GameLoad.exe | GET | 200 | 104.27.158.159:80 | http://data.gameload.top/assets/6.jpg | US | image | 86.6 Kb | suspicious |
2388 | GameLoad.exe | GET | 200 | 23.210.248.71:80 | http://webplayer.unity3d.com//autodownload_webplugin-3.x/Mono3.x.x-win32.zip | NL | compressed | 1.98 Mb | whitelisted |
2388 | GameLoad.exe | GET | 200 | 104.27.158.159:80 | http://data.gameload.top/feed/games.xml?1593624622069 | US | xml | 451 b | suspicious |
2388 | GameLoad.exe | GET | 200 | 104.27.158.159:80 | http://data.gameload.top/assets/1.jpg | US | image | 63.9 Kb | suspicious |
2388 | GameLoad.exe | GET | 200 | 23.210.248.71:80 | http://webplayer.unity3d.com//autodownload_webplugin-3.x/UnityPlayer3.x.x-win32.zip | NL | compressed | 4.95 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2388 | GameLoad.exe | 104.27.158.159:80 | data.gameload.top | Cloudflare Inc | US | suspicious |
2388 | GameLoad.exe | 172.217.16.142:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2388 | GameLoad.exe | 23.210.248.71:80 | autoupdate-revision.unity3d.com | Akamai International B.V. | NL | suspicious |
3196 | GameLoad.exe | 172.67.186.64:80 | data.gameload.top | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
data.gameload.top |
| suspicious |
www.google-analytics.com |
| whitelisted |
autoupdate-revision.unity3d.com |
| suspicious |
webplayer.unity3d.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2388 | GameLoad.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2388 | GameLoad.exe | Unknown Traffic | ET INFO Suspicious User-Agent (1 space) |
2388 | GameLoad.exe | Unknown Traffic | ET INFO Suspicious User-Agent (1 space) |
2388 | GameLoad.exe | Unknown Traffic | ET INFO Suspicious User-Agent (1 space) |
3 ETPRO signatures available at the full report