| File name: | _65004.exe |
| Full analysis: | https://app.any.run/tasks/f4f34236-59dc-48f3-8980-00c4b6a53b63 |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2018, 17:05:24 |
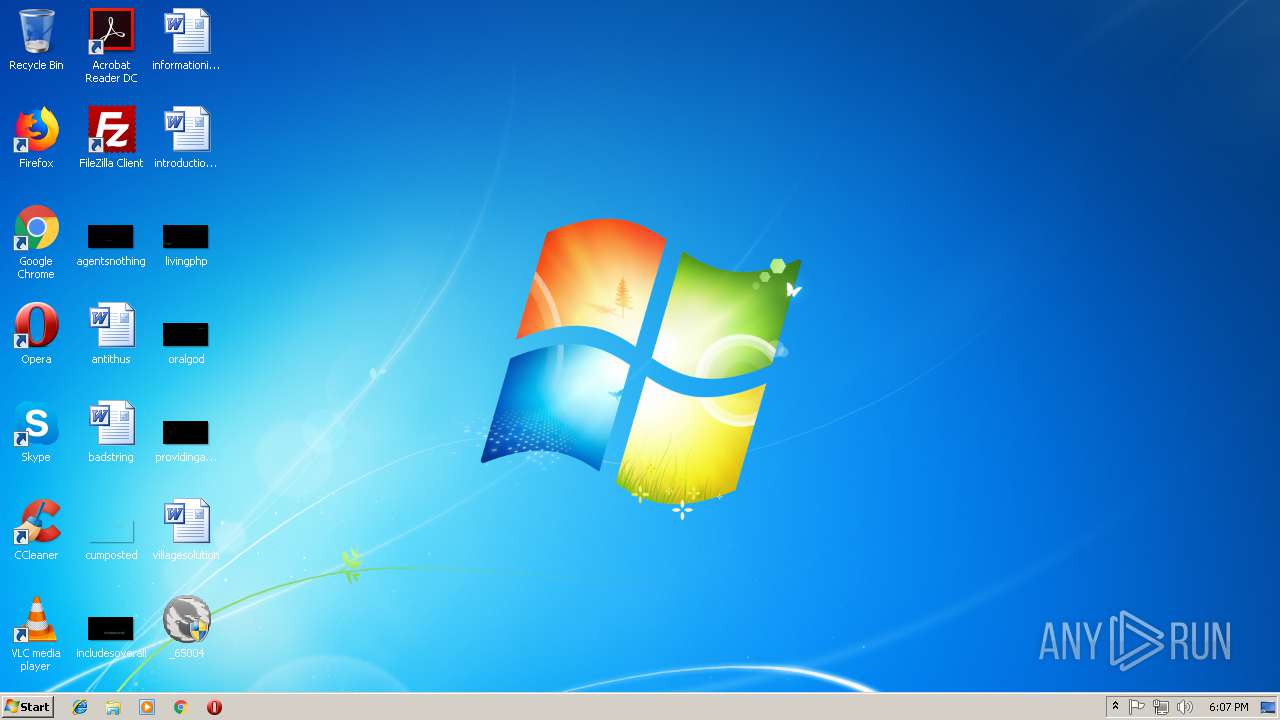
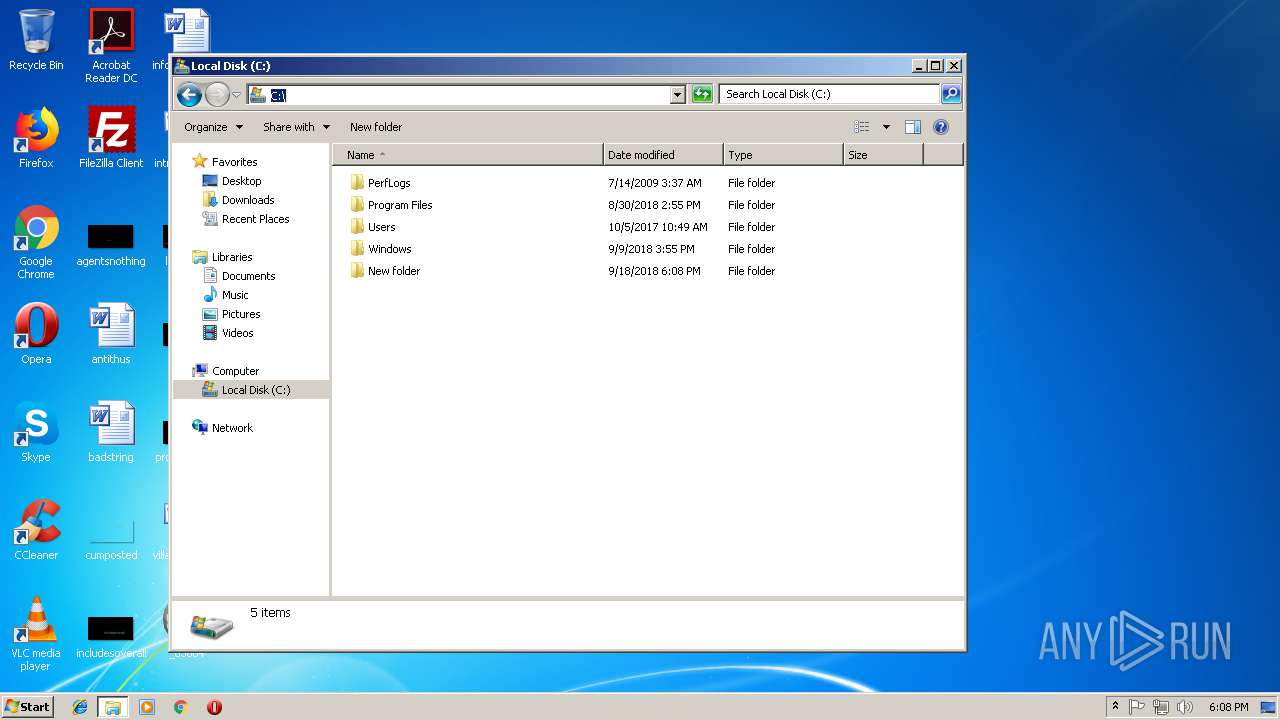
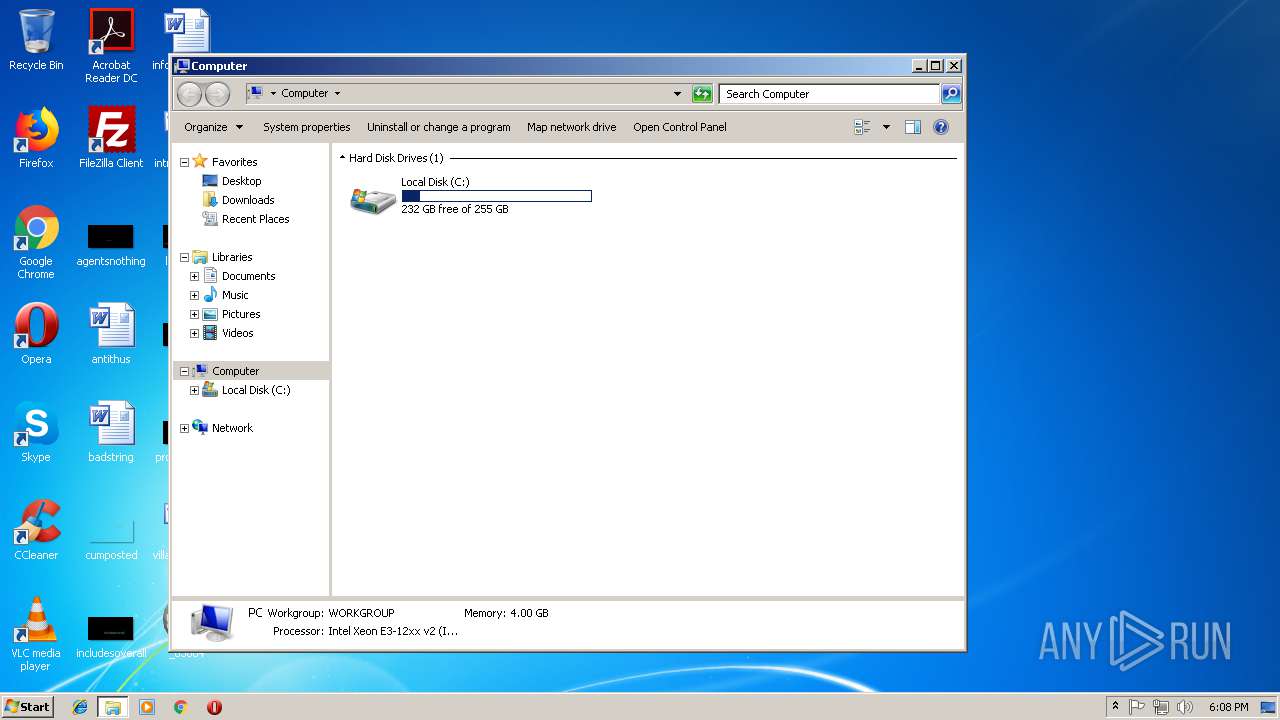
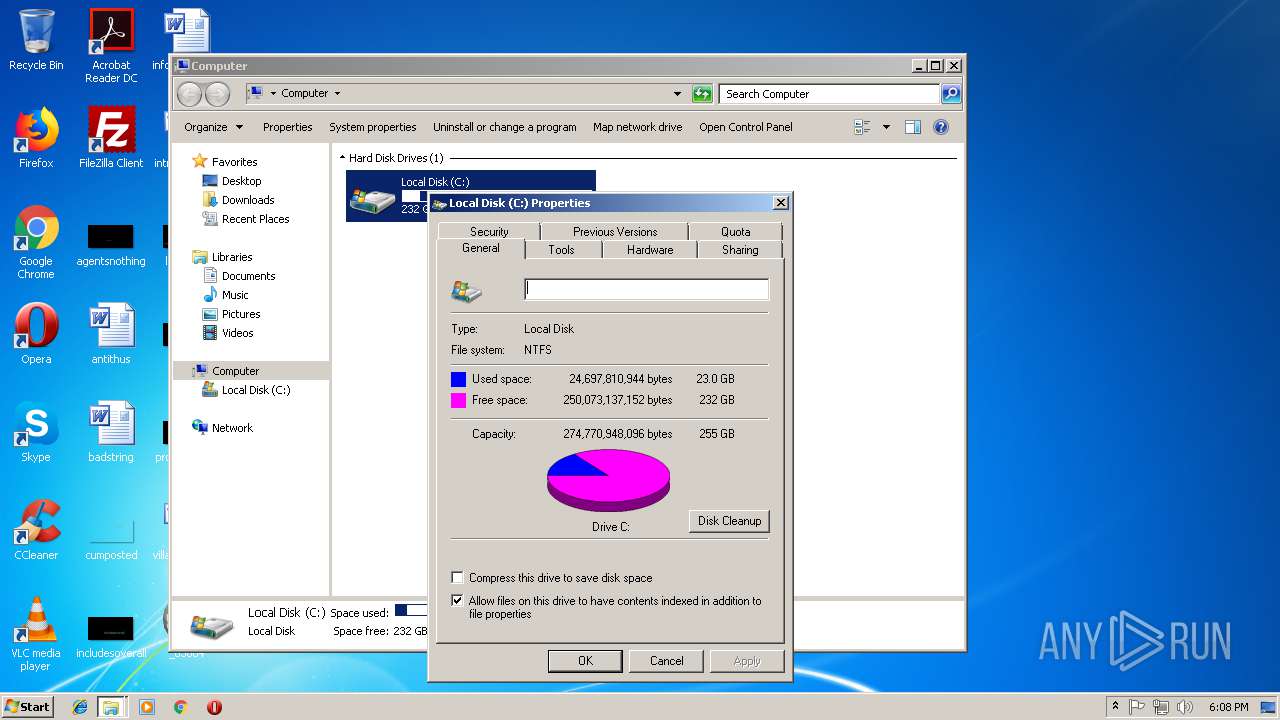
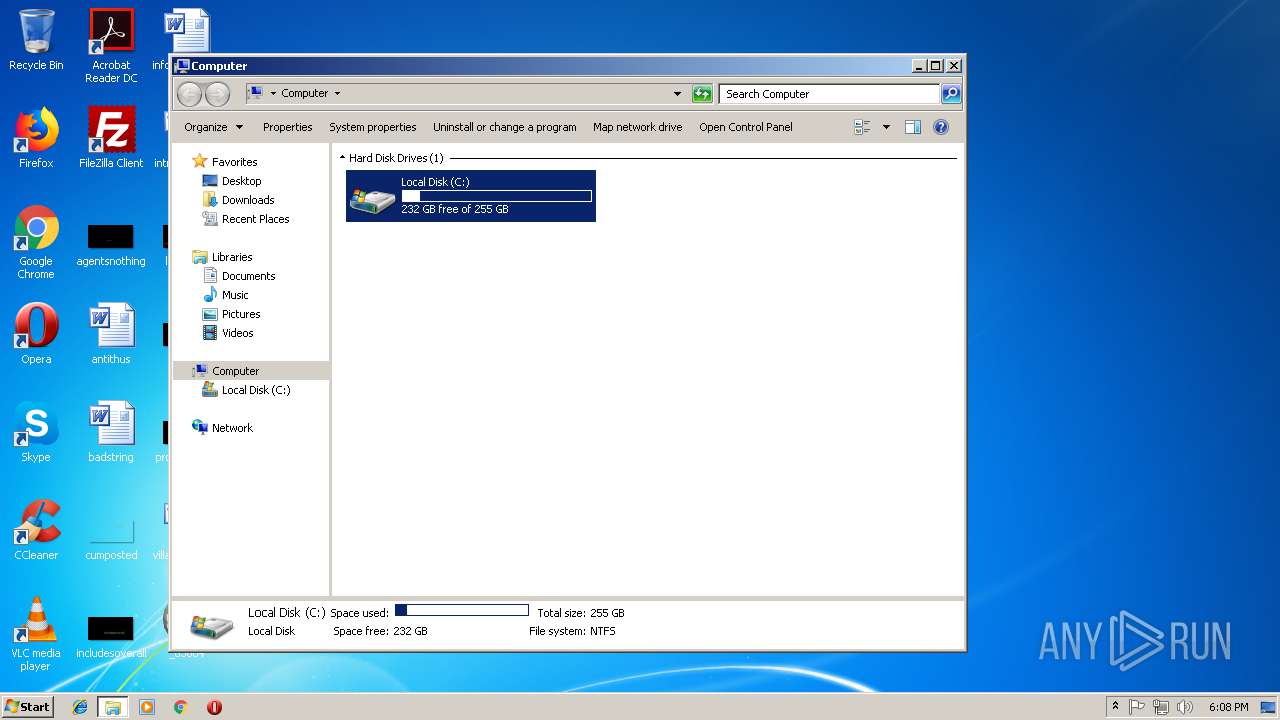
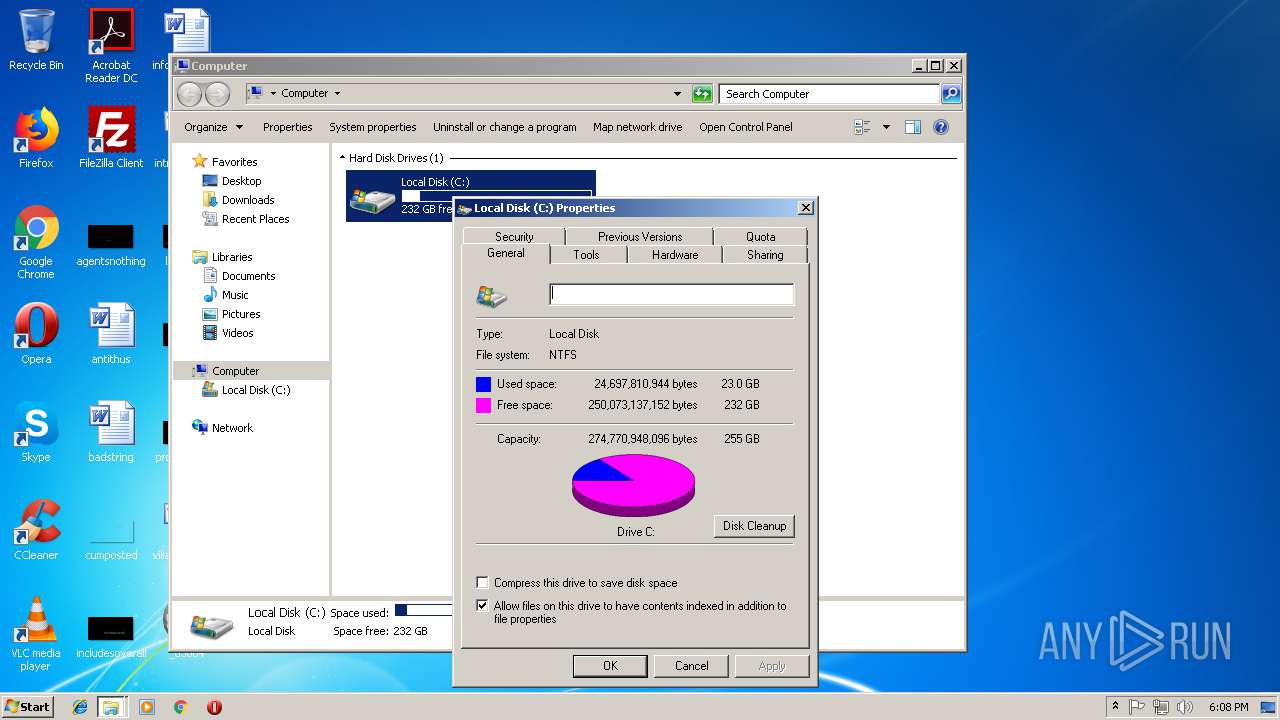
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2B000B74AFFEF0A07FCFE02988979D5A |
| SHA1: | 15FB08EC582C3D32C3CC36C7A39FC90BDA196D29 |
| SHA256: | 111D19003ED754307D4A57BC736599C0AA76422BC3CED4FBFDCD9B42ACD712D1 |
| SSDEEP: | 196608:Dc8fZqI4hJk8TeMOHGd3t3xumN0OcmaZSjj0/BRQiK3K8LT:48BwJdeXHM3g4+S9N3jL |
MALICIOUS
Application was dropped or rewritten from another process
- sll.exe (PID: 3880)
- start.exe (PID: 3860)
- nvsc.exe (PID: 1388)
- checkFirewall.exe (PID: 128)
- TaskSetter.exe (PID: 928)
- checkFirewall.exe (PID: 2580)
- TaskSetter.exe (PID: 236)
- TaskSetter.exe (PID: 3172)
- TaskSetter.exe (PID: 2820)
- fmtm.exe (PID: 2812)
- start.exe (PID: 384)
- keystart.exe (PID: 3676)
- nvscex.exe (PID: 3608)
- TaskSetter.exe (PID: 2360)
- TaskSetter.exe (PID: 456)
- TaskSetter.exe (PID: 4064)
- TaskSetter.exe (PID: 256)
Runs app for hidden code execution
- _65004.exe (PID: 3896)
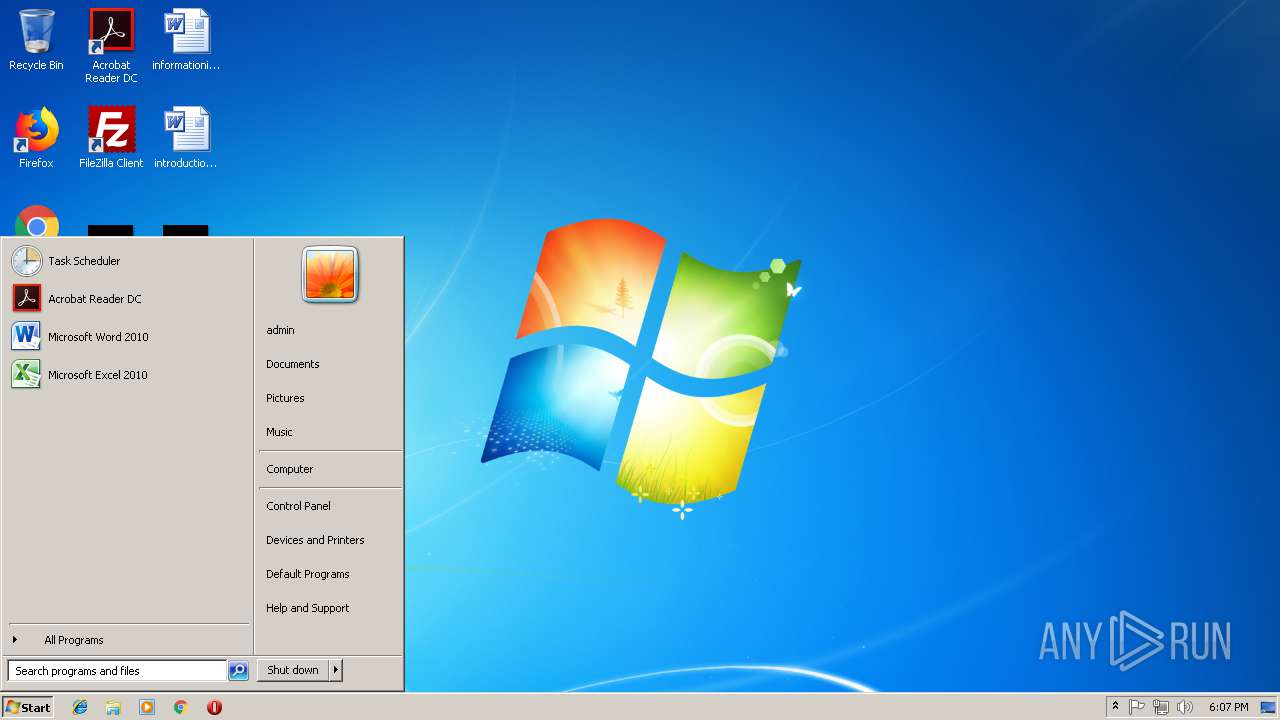
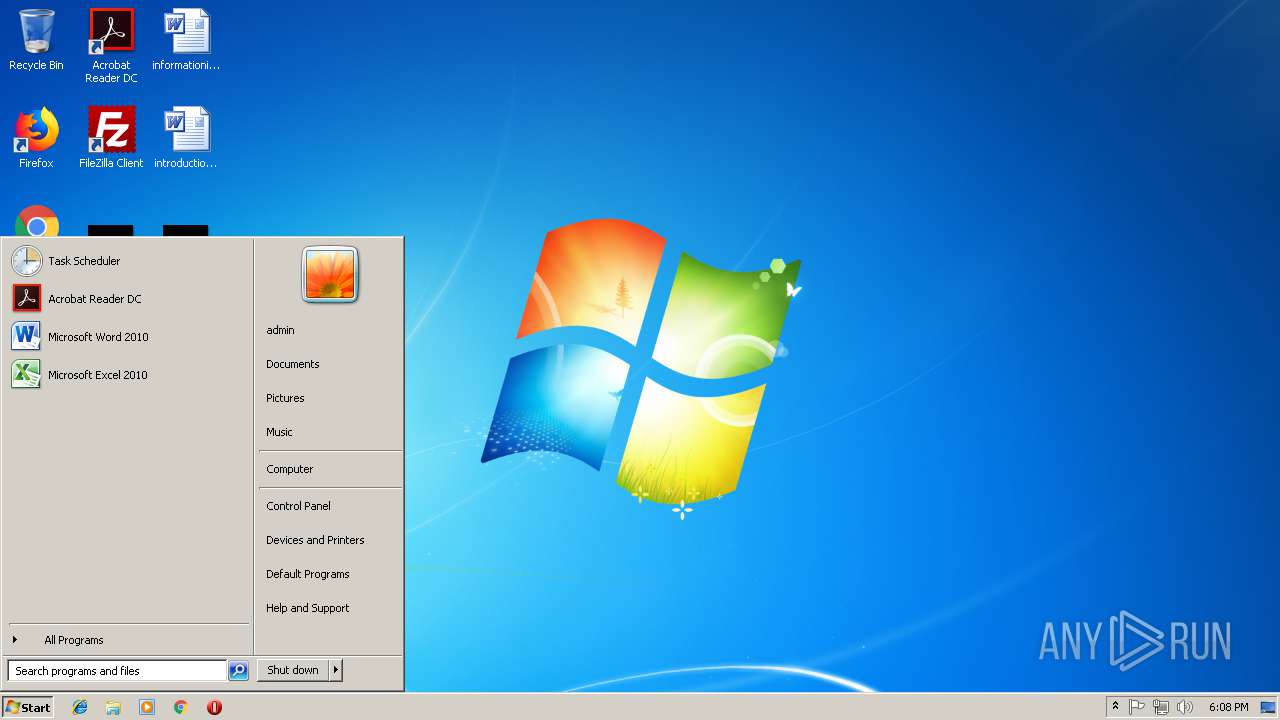
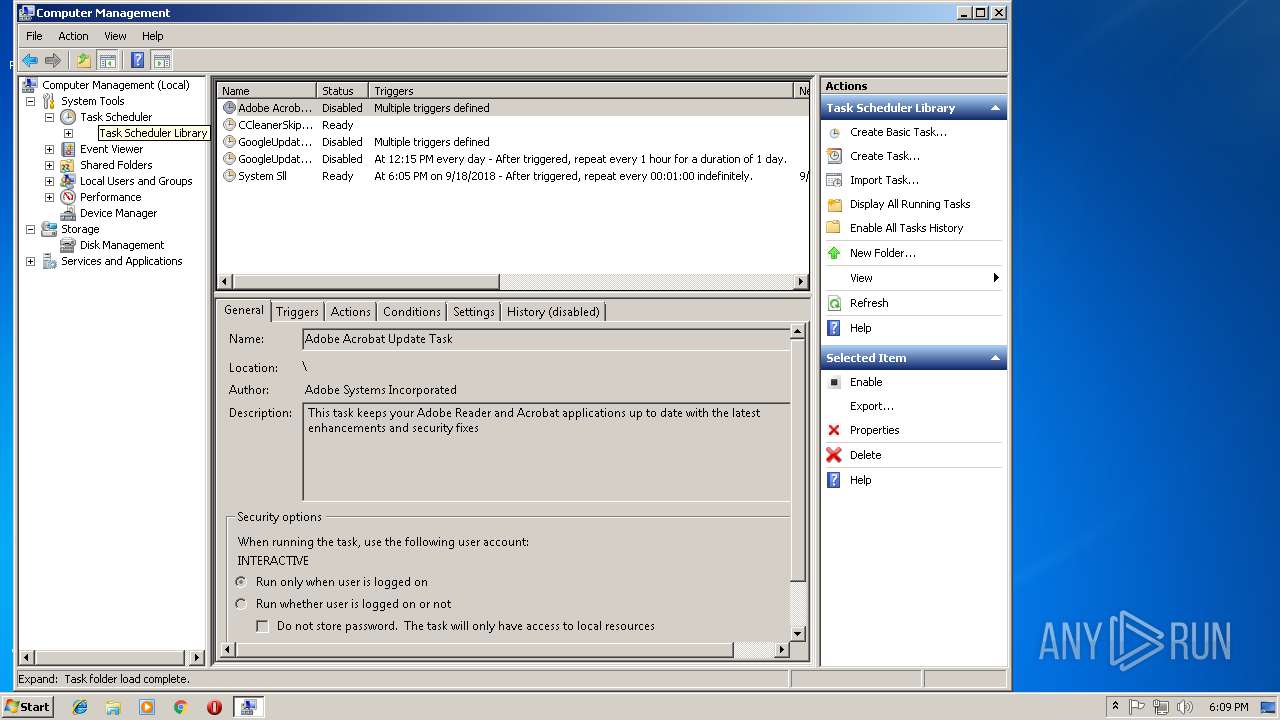
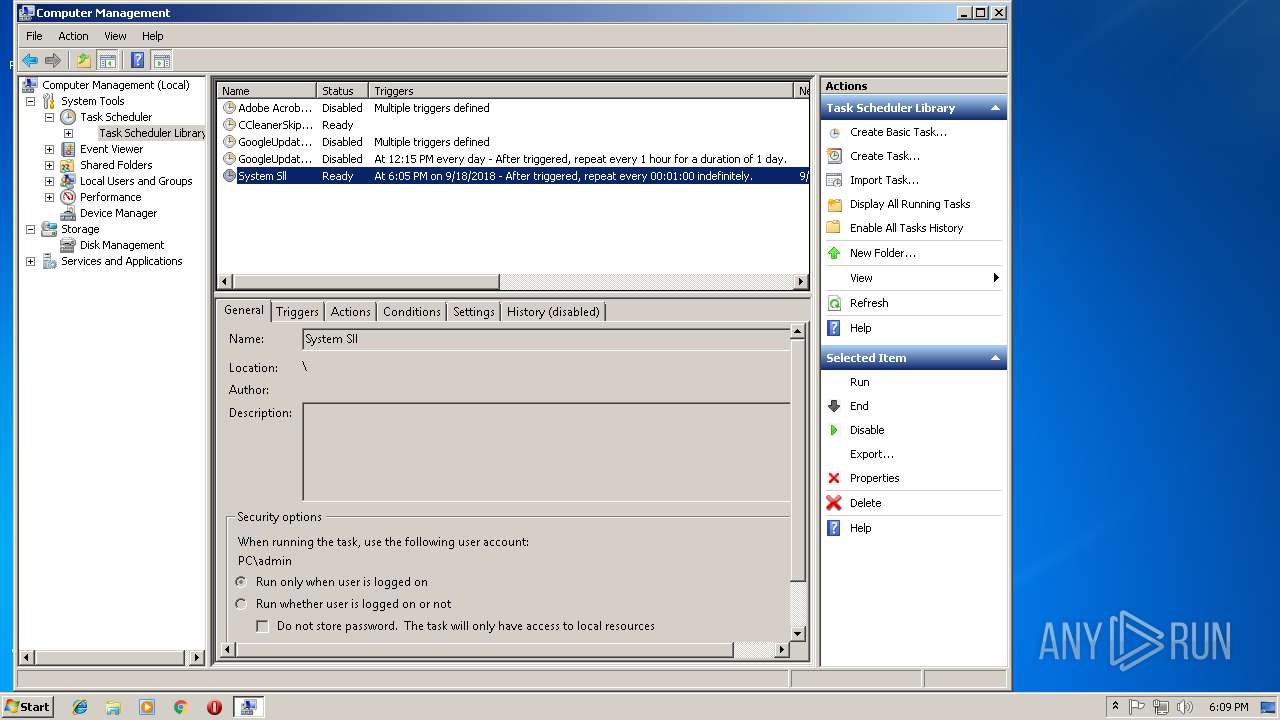
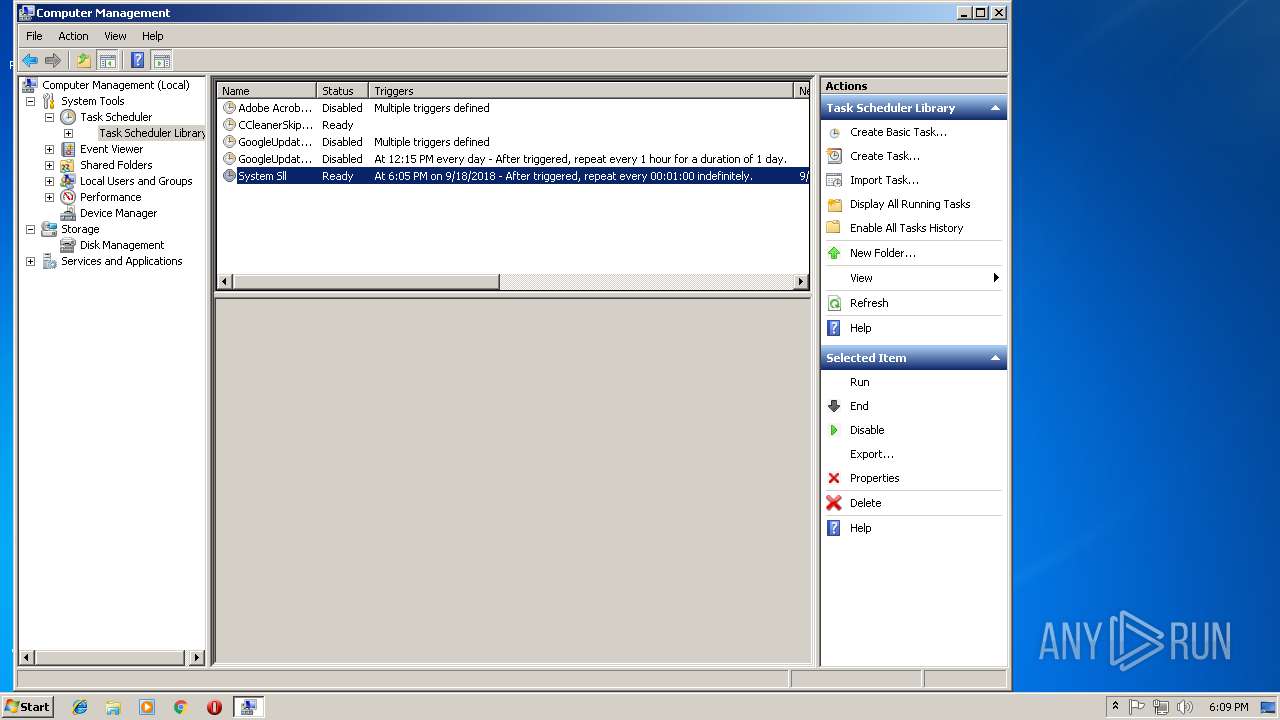
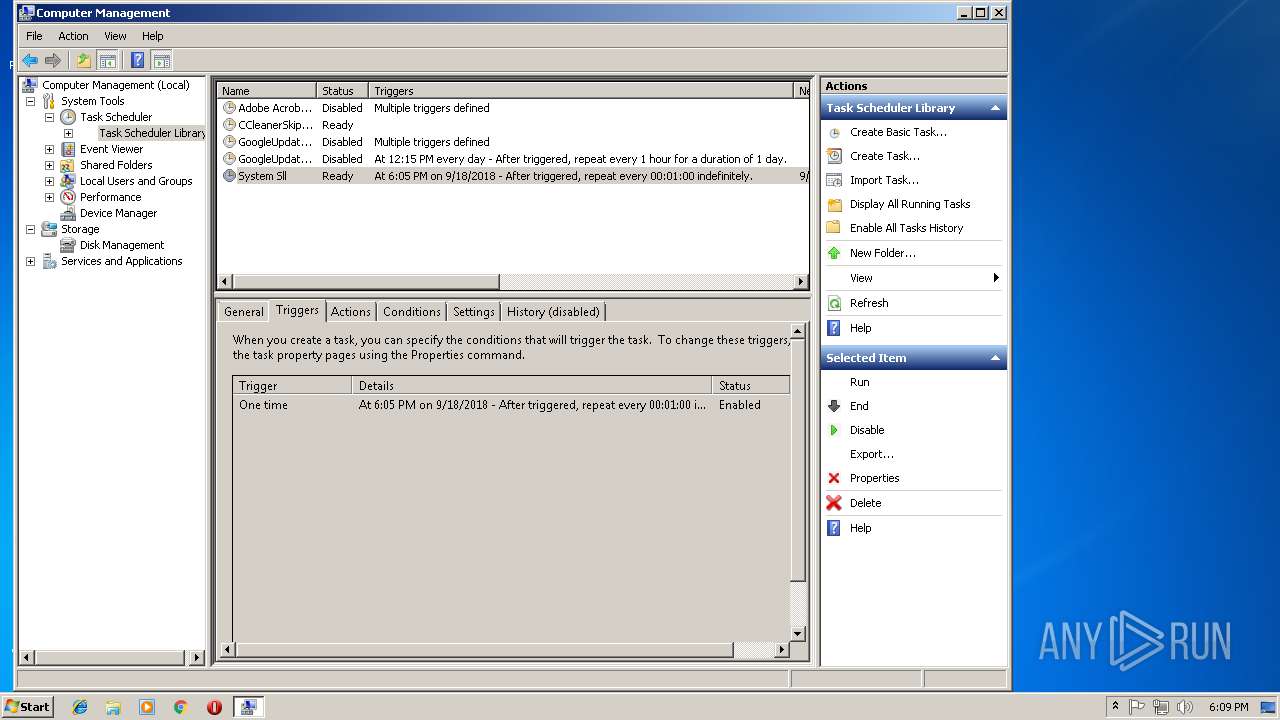
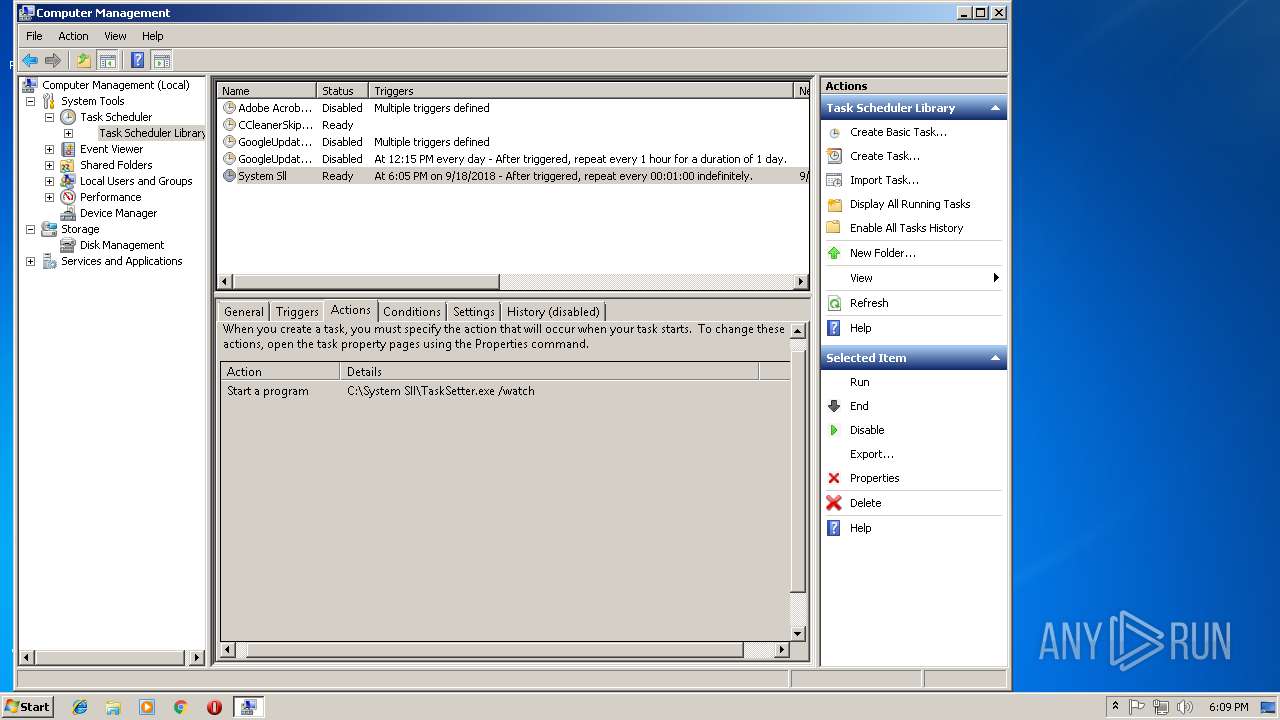
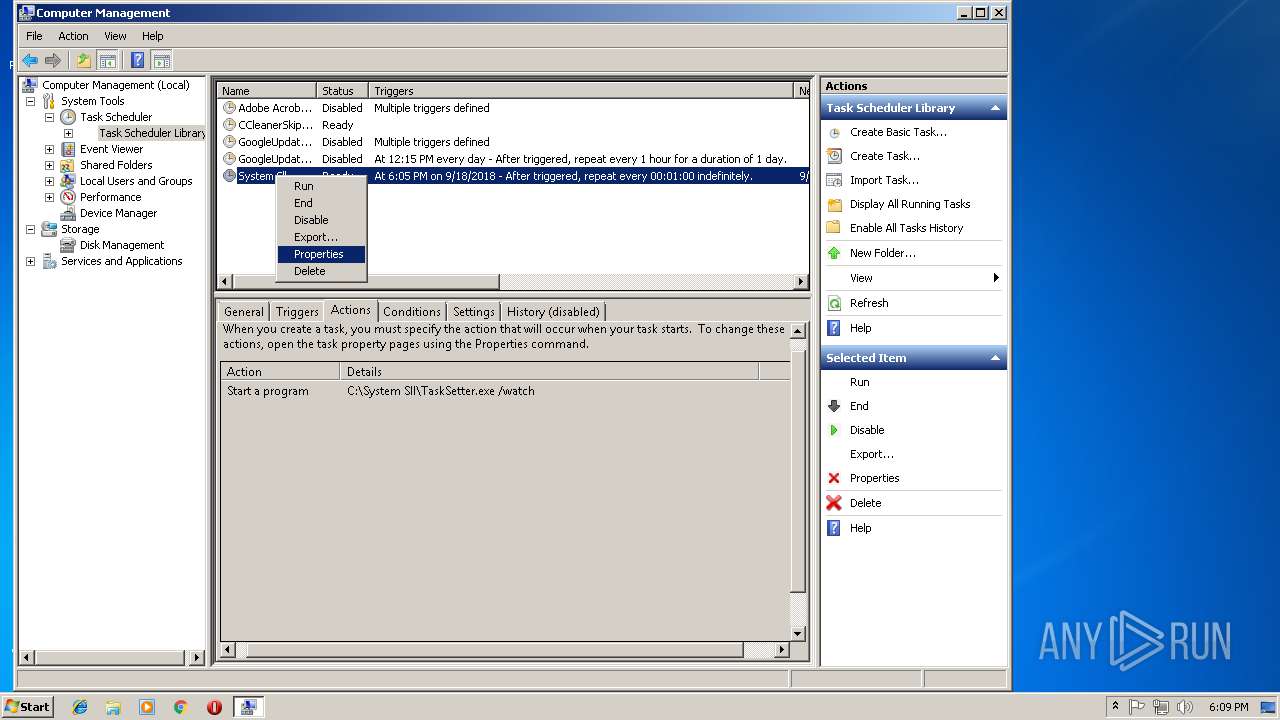
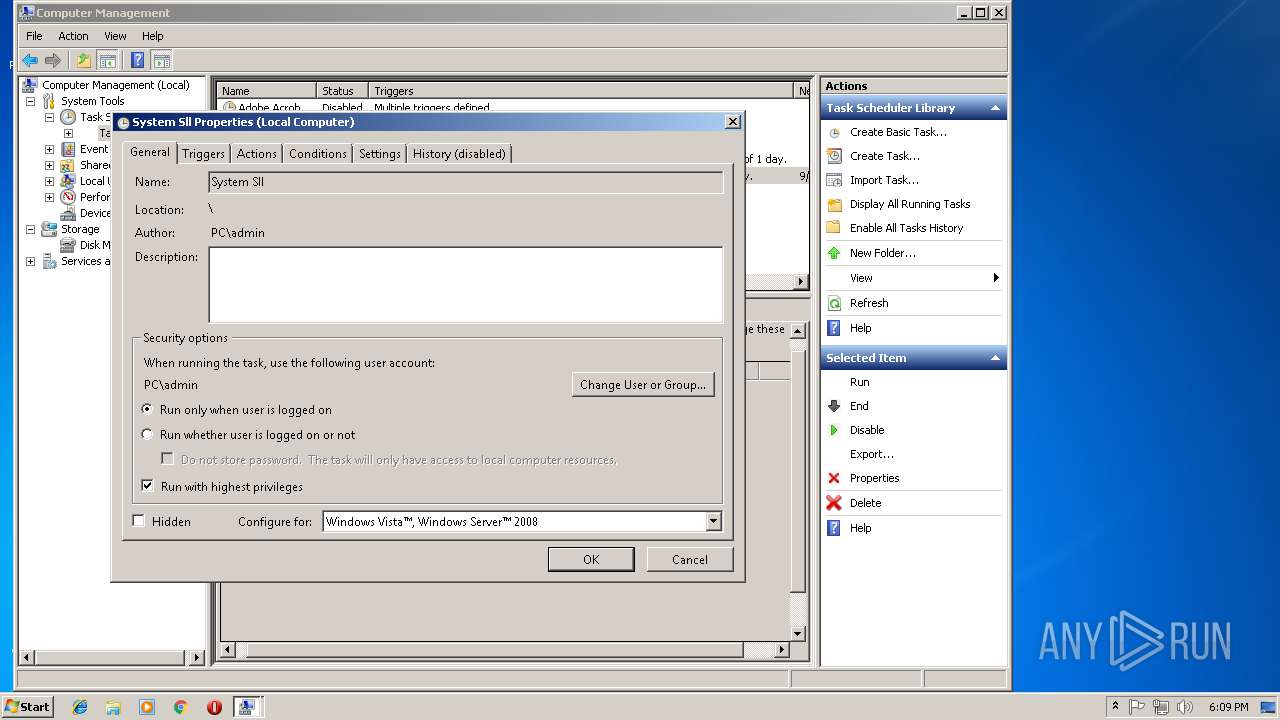
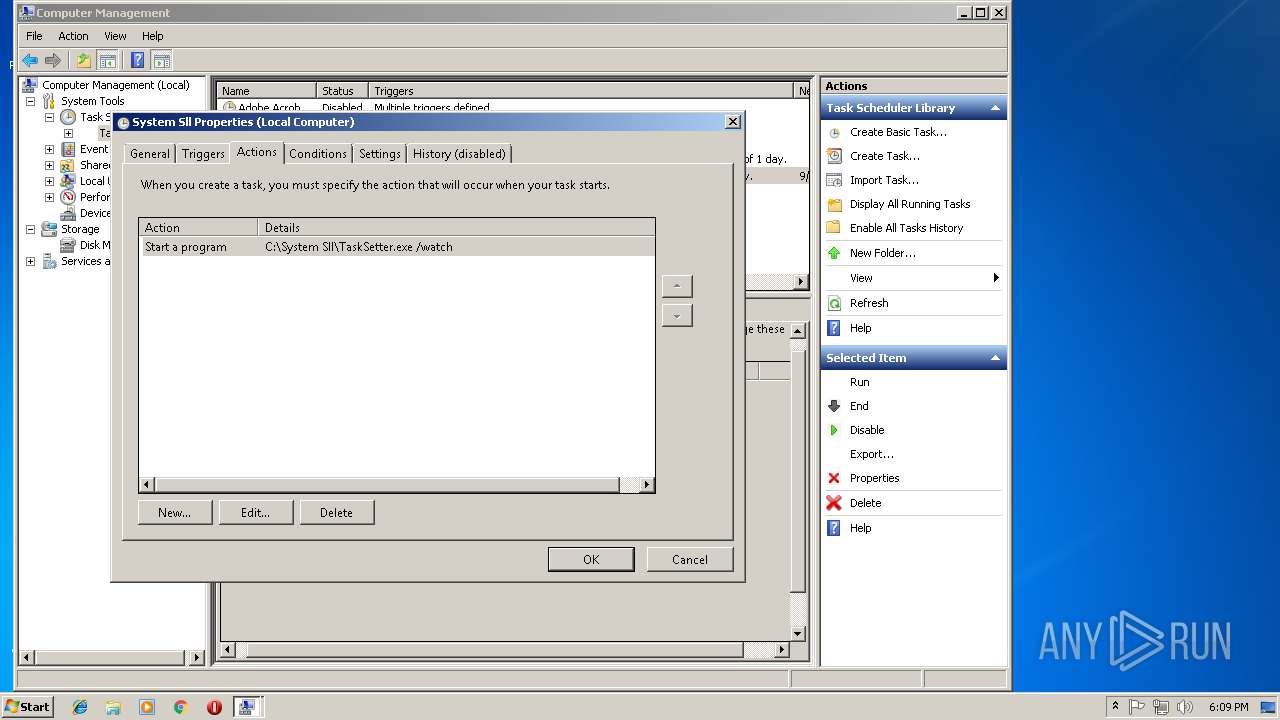
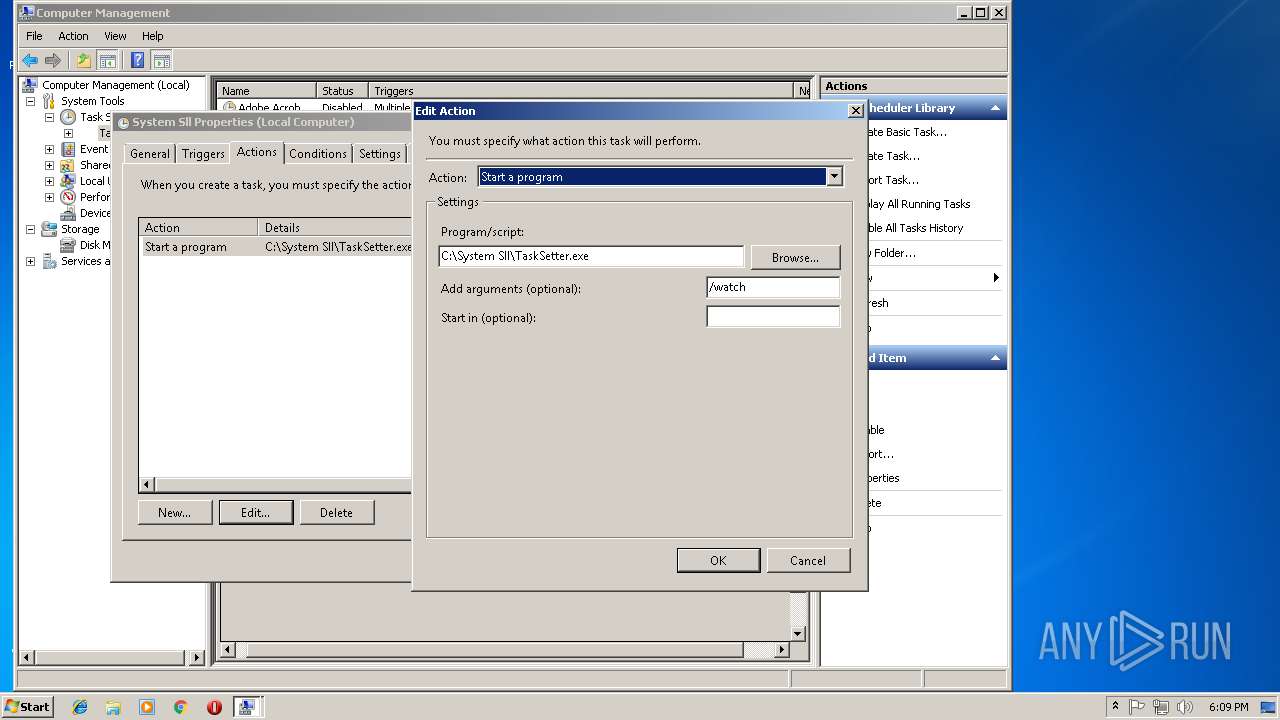
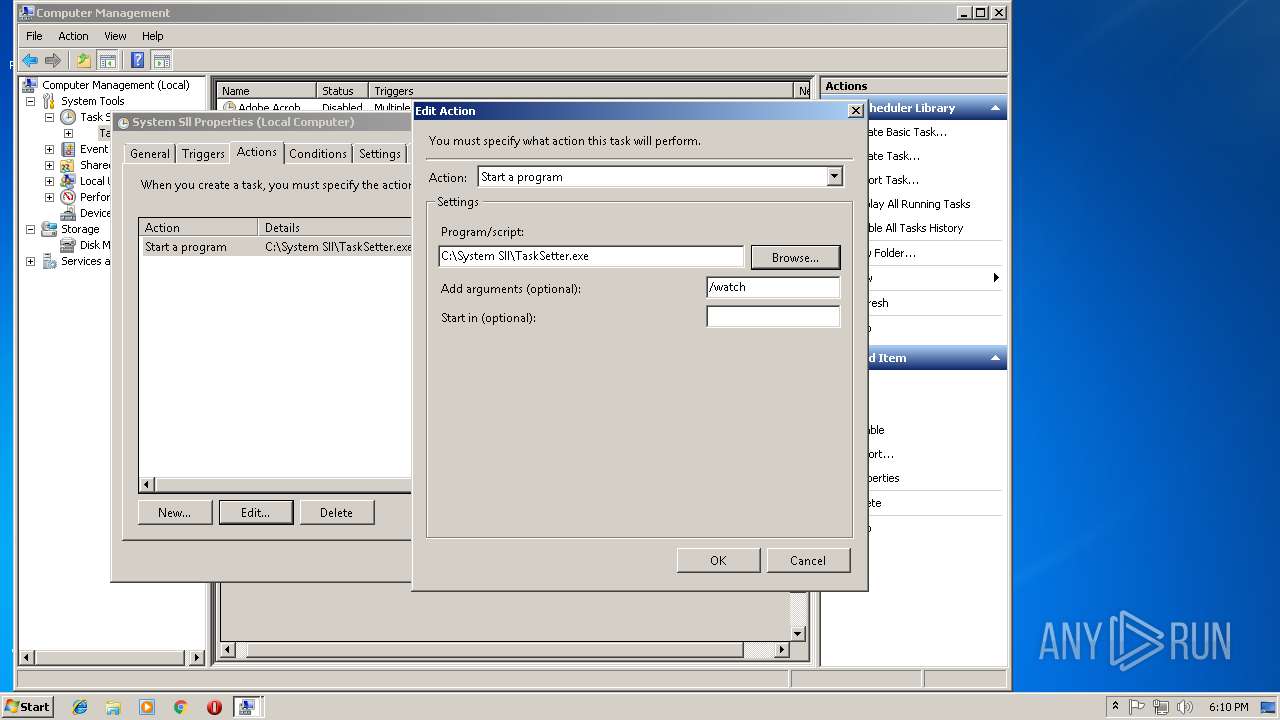
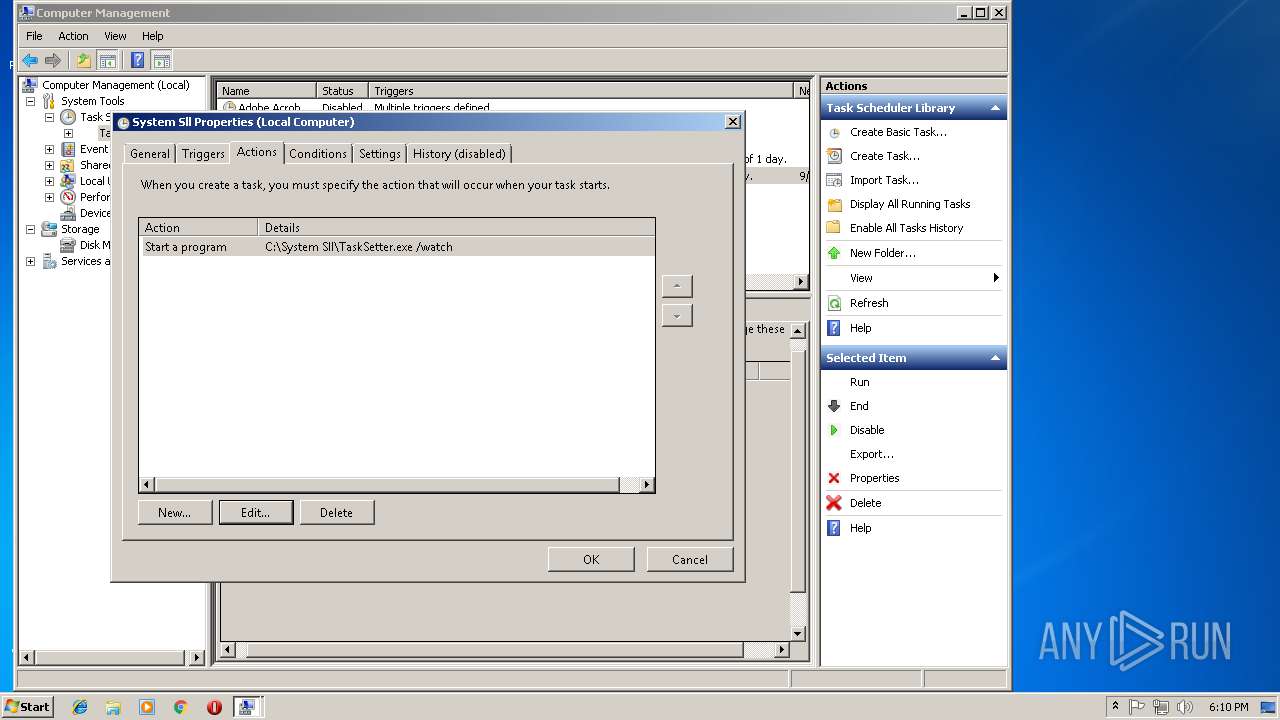
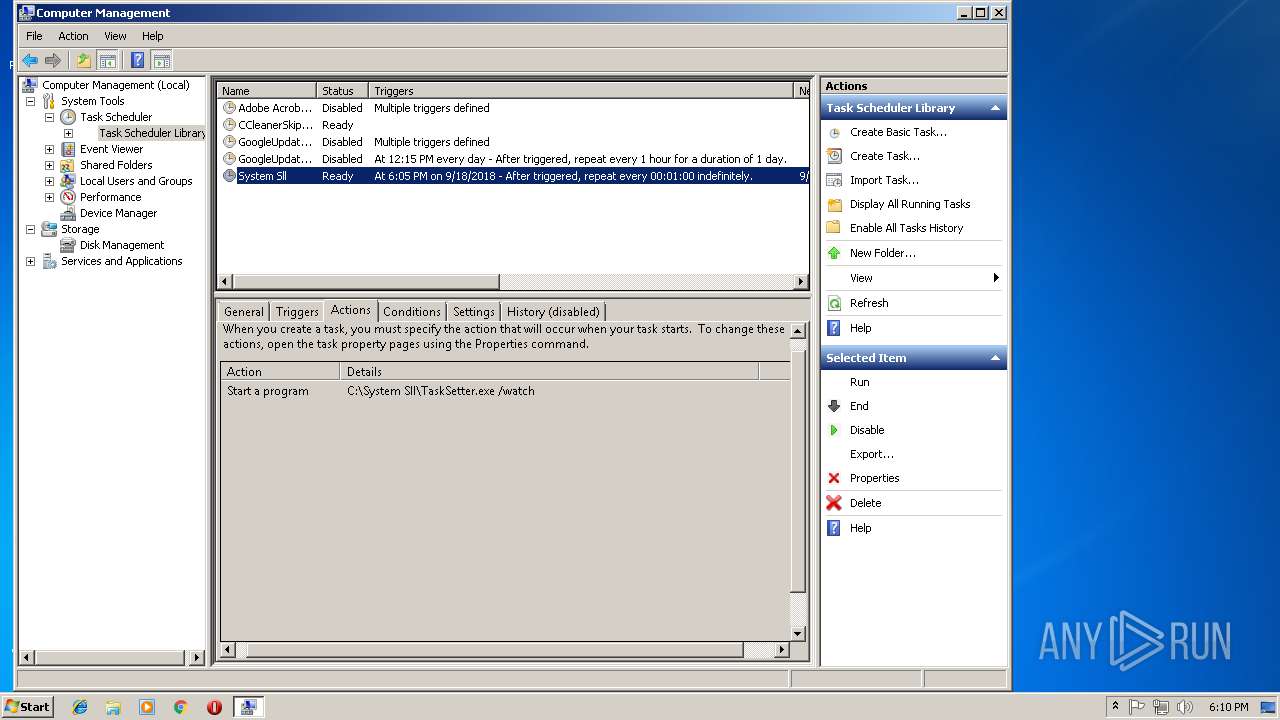
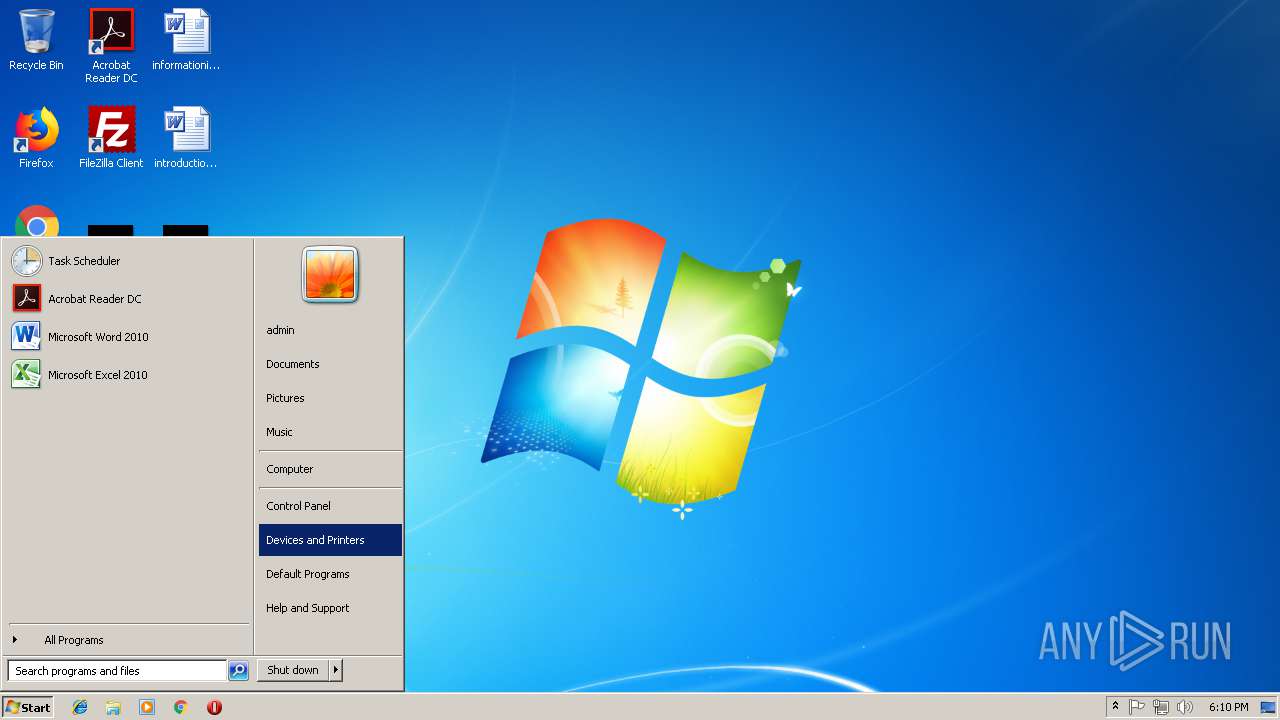
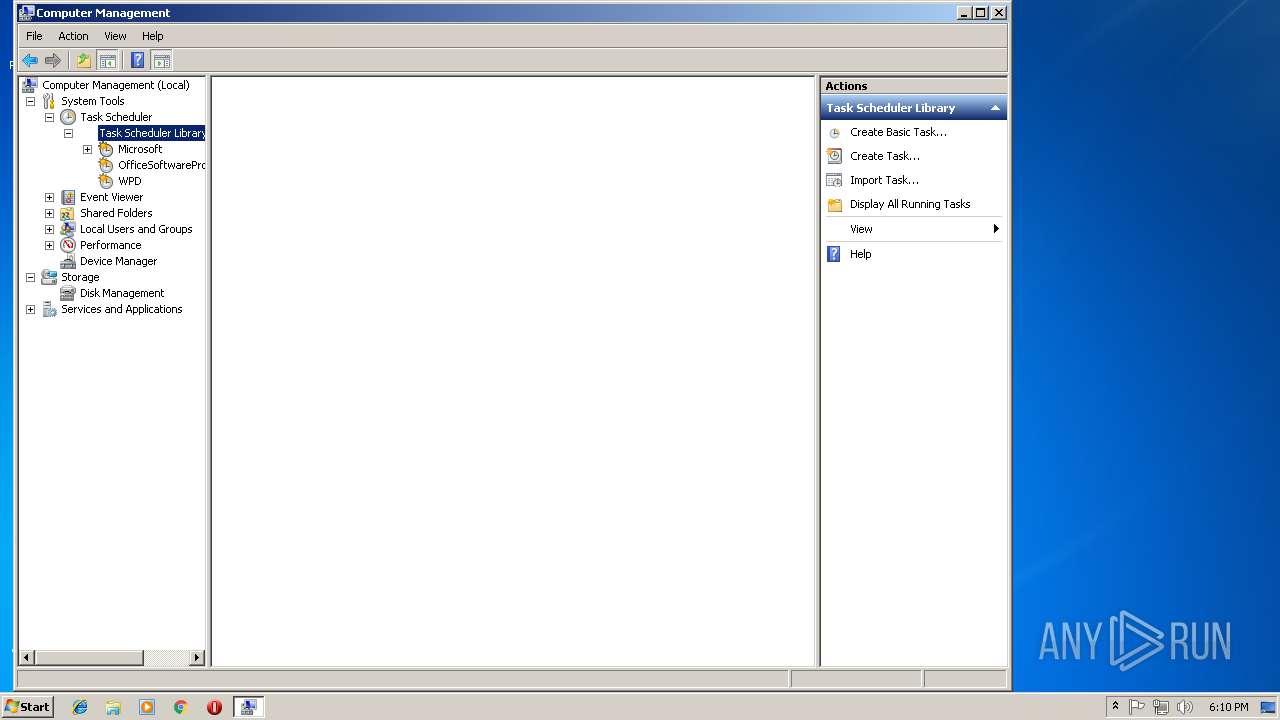
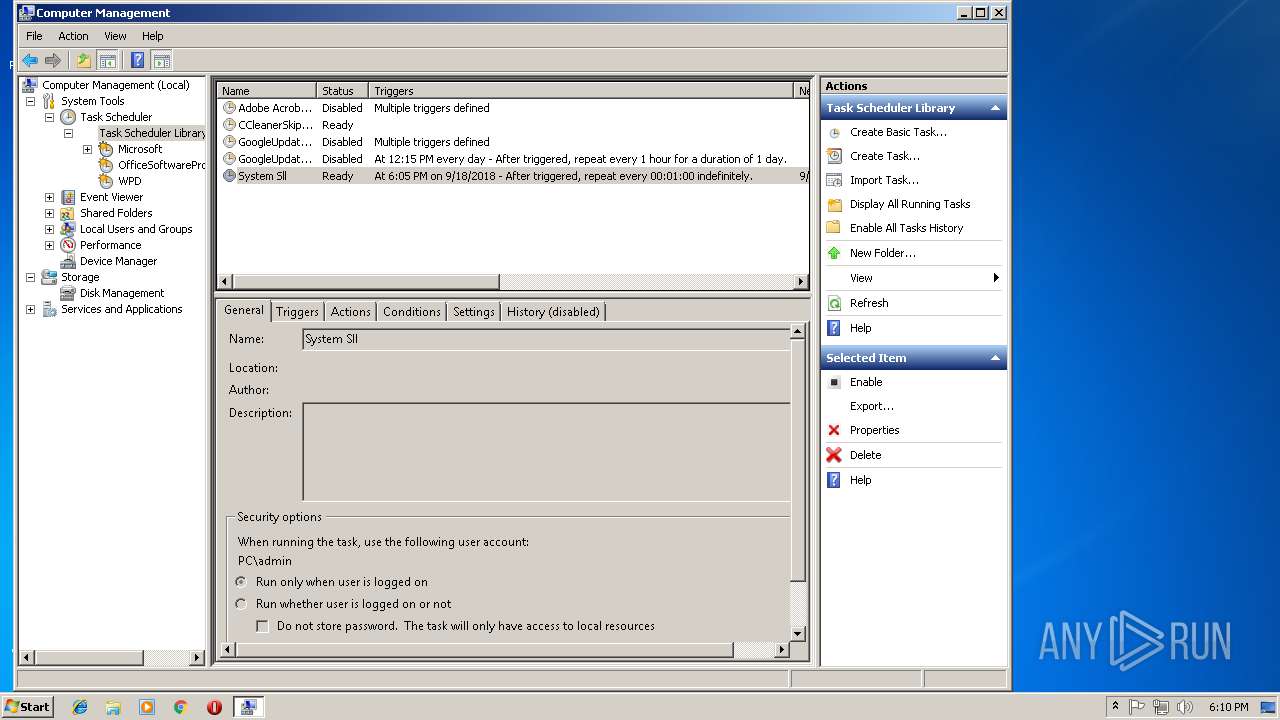
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3296)
Loads the Task Scheduler COM API
- TaskSetter.exe (PID: 236)
- schtasks.exe (PID: 1148)
- mmc.exe (PID: 2672)
- mmc.exe (PID: 2240)
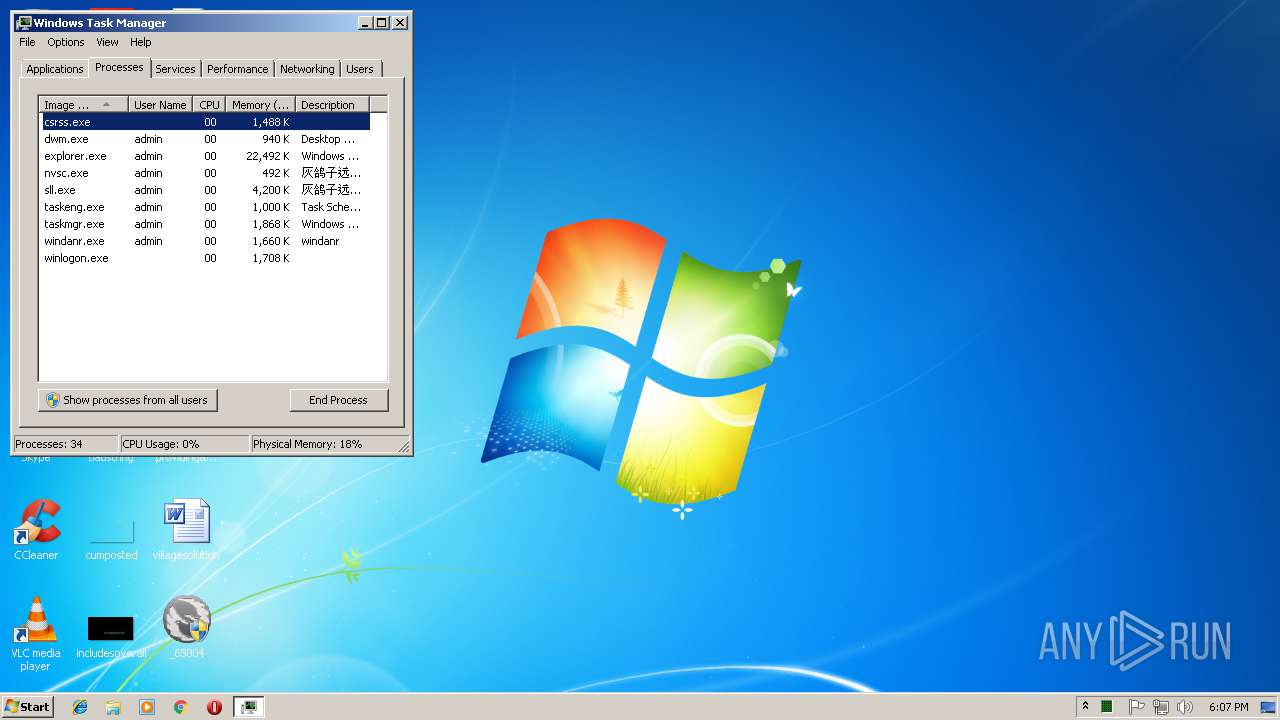
Loads dropped or rewritten executable
- sll.exe (PID: 3880)
- nvsc.exe (PID: 1388)
- explorer.exe (PID: 1604)
- dwm.exe (PID: 1556)
- taskmgr.exe (PID: 3424)
- DllHost.exe (PID: 2628)
- DllHost.exe (PID: 2800)
- mmc.exe (PID: 2672)
- mmc.exe (PID: 2240)
SUSPICIOUS
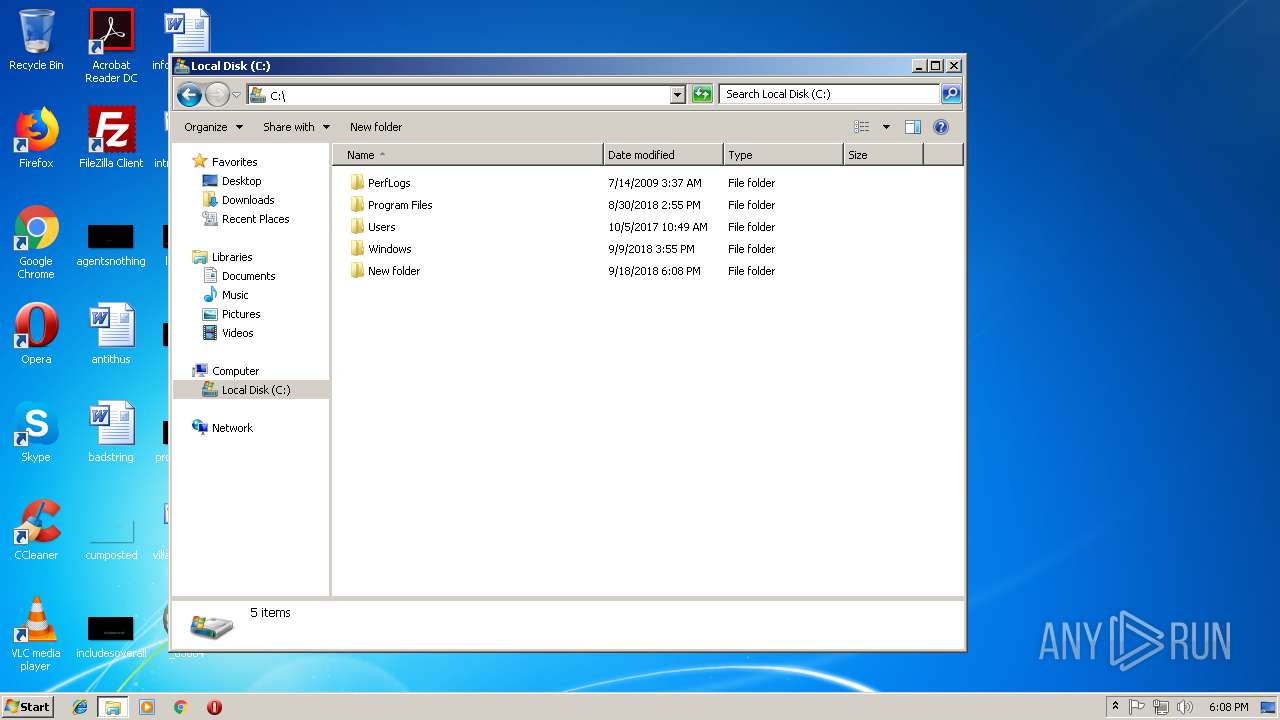
Executable content was dropped or overwritten
- _65004.exe (PID: 3896)
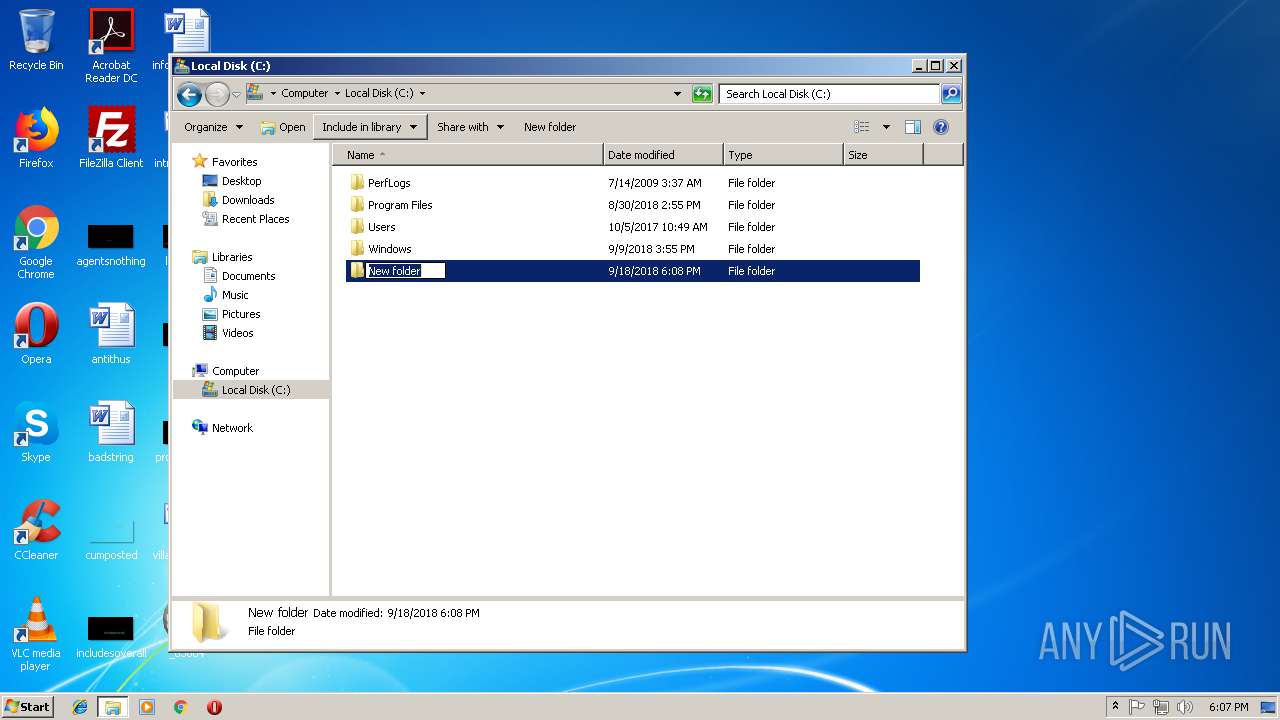
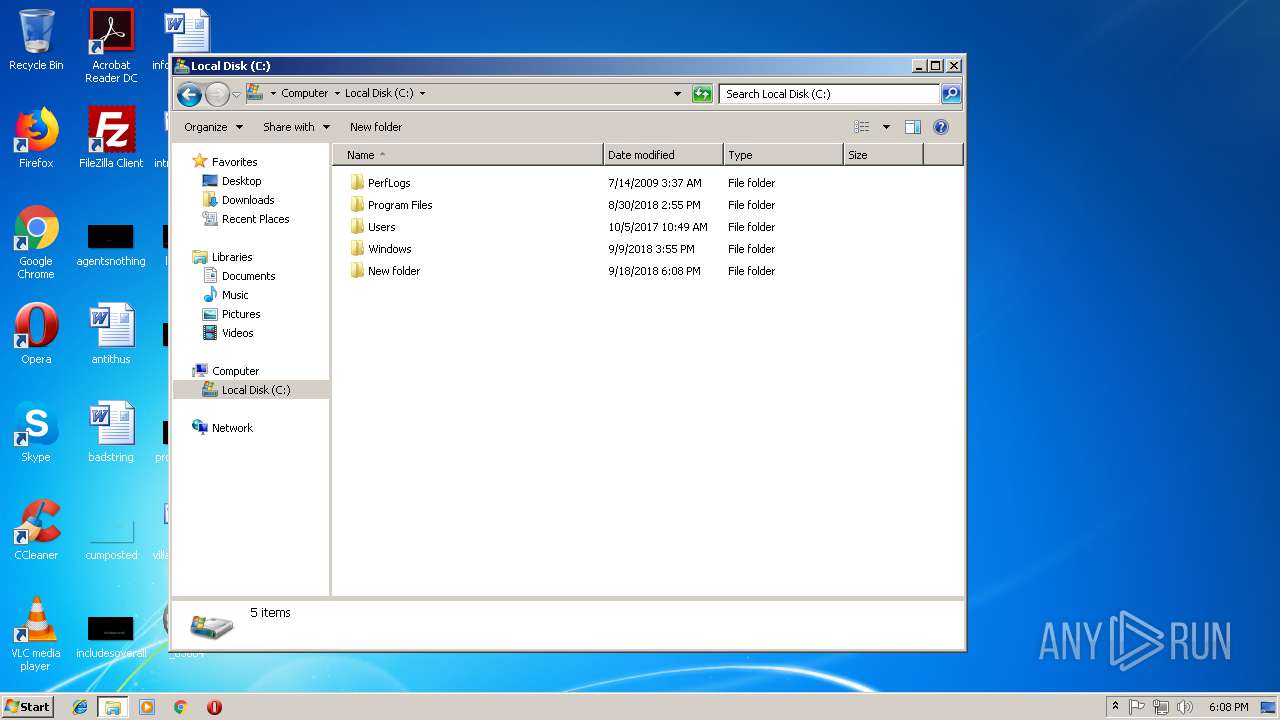
Creates files in the Windows directory
- _65004.exe (PID: 3896)
Starts CMD.EXE for commands execution
- _65004.exe (PID: 3896)
- TaskSetter.exe (PID: 236)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 324)
Connects to unusual port
- sll.exe (PID: 3880)
Reads CPU info
- sll.exe (PID: 3880)
Searches for installed software
- sll.exe (PID: 3880)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (30.9) |
| .scr | | | Windows screen saver (14.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.3) |
| .exe | | | Win32 Executable (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:07:24 11:06:05+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 10924032 |
| InitializedDataSize: | 22528 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa6ceee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.4.0.1 |
| ProductVersionNumber: | 5.4.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | 灰鸽子远程管理系统员工端 |
| CompanyName: | 灰鸽子远程管理系统员工端 潍坊灰鸽子安防工程有限公司 网址:www.hgzvip.net QQ 834999498 |
| FileDescription: | 灰鸽子远程管理系统员工端 |
| FileVersion: | 5.4.0.1 |
| InternalName: | es1.exe |
| LegalCopyright: | Copyright © 潍坊灰鸽子安防工程有限公司 2016 |
| OriginalFileName: | es1.exe |
| ProductName: | 灰鸽子远程管理系统员工端 |
| ProductVersion: | 5.4.0.1 |
| AssemblyVersion: | 5.4.0.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Jul-2017 09:06:05 |
| Comments: | 灰鸽子远程管理系统员工端 |
| CompanyName: | 灰鸽子远程管理系统员工端 潍坊灰鸽子安防工程有限公司 网址:www.hgzvip.net QQ 834999498 |
| FileDescription: | 灰鸽子远程管理系统员工端 |
| FileVersion: | 5.4.0.1 |
| InternalName: | es1.exe |
| LegalCopyright: | Copyright © 潍坊灰鸽子安防工程有限公司 2016 |
| OriginalFilename: | es1.exe |
| ProductName: | 灰鸽子远程管理系统员工端 |
| ProductVersion: | 5.4.0.1 |
| Assembly Version: | 5.4.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 24-Jul-2017 09:06:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00A6AEF4 | 0x00A6B000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.42755 |
.sdata | 0x00A6E000 | 0x00000162 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.02184 |
.rsrc | 0x00A70000 | 0x000052B4 | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.02796 |
.reloc | 0x00A76000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.88378 | 2994 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.75035 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.0815 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
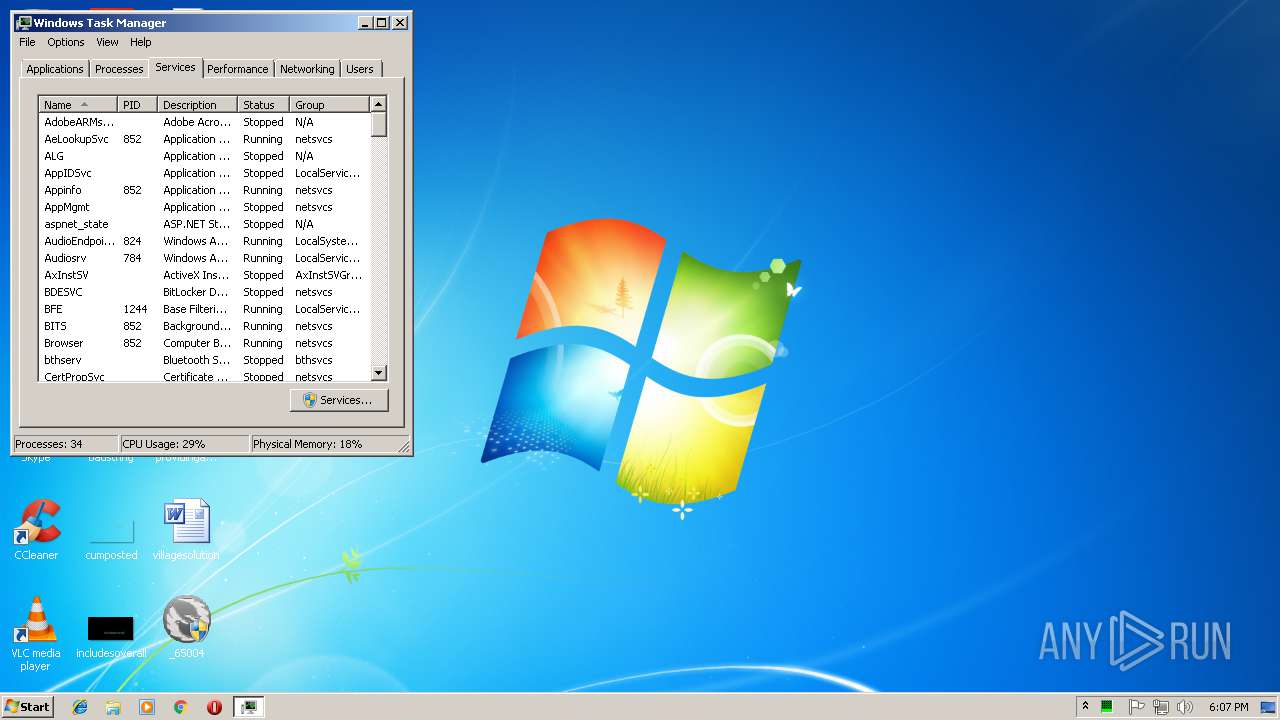
Total processes
79
Monitored processes
34
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\System Sll\checkFirewall.exe" C:\System Sll/Updater/updater.exe | C:\System Sll\checkFirewall.exe | — | sll.exe | |||||||||||
User: admin Company: Weifang Gray Dove Security Engineering Co.,Ltd. Integrity Level: HIGH Description: windows防火墙联网检测 Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 236 | "C:\System Sll\TaskSetter.exe" /install | C:\System Sll\TaskSetter.exe | — | _65004.exe | |||||||||||
User: admin Company: 潍坊灰鸽子安防工程有限公司 Integrity Level: HIGH Description: 灰鸽子远程管理系统 Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 256 | "C:\System Sll\TaskSetter.exe" /watch | C:\System Sll\TaskSetter.exe | — | taskeng.exe | |||||||||||
User: admin Company: 潍坊灰鸽子安防工程有限公司 Integrity Level: HIGH Description: 灰鸽子远程管理系统 Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 324 | "cmd.exe" | C:\Windows\system32\cmd.exe | — | _65004.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 384 | "C:\System Sll\fmtm\start.exe" stop | C:\System Sll\fmtm\start.exe | — | sll.exe | |||||||||||
User: admin Company: 潍坊灰鸽子安防工程有限公司 Integrity Level: HIGH Description: 灰鸽子远程管理系统 Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 456 | "C:\System Sll\TaskSetter.exe" /watch | C:\System Sll\TaskSetter.exe | — | taskeng.exe | |||||||||||
User: admin Company: 潍坊灰鸽子安防工程有限公司 Integrity Level: HIGH Description: 灰鸽子远程管理系统 Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 584 | "C:\Windows\system32\CompMgmtLauncher.exe" | C:\Windows\system32\CompMgmtLauncher.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Computer Management Snapin Launcher Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 928 | "C:\System Sll\TaskSetter.exe" /watch | C:\System Sll\TaskSetter.exe | — | taskeng.exe | |||||||||||
User: admin Company: 潍坊灰鸽子安防工程有限公司 Integrity Level: HIGH Description: 灰鸽子远程管理系统 Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 1000 | "C:\Windows\system32\CompMgmtLauncher.exe" | C:\Windows\system32\CompMgmtLauncher.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Computer Management Snapin Launcher Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1148 | Schtasks /run /tn "System Sll" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 055
Read events
3 282
Write events
771
Delete events
2
Modification events
| (PID) Process: | (3896) _65004.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3360) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Lsa\FipsAlgorithmPolicy\Enabled |
| Operation: | write | Name: | Administrator |
Value: 0 | |||
| (PID) Process: | (3896) _65004.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3896) _65004.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (236) TaskSetter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (236) TaskSetter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3880) sll.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3880) sll.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3880) sll.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sll_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3880) sll.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sll_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
60
Suspicious files
20
Text files
12
Unknown types
52
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3896 | _65004.exe | C:\Users\admin\AppData\Local\Temp\CabEF2.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | _65004.exe | C:\Users\admin\AppData\Local\Temp\TarEF3.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | _65004.exe | C:\Users\admin\AppData\Local\Temp\CabF04.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | _65004.exe | C:\Users\admin\AppData\Local\Temp\TarF05.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | _65004.exe | C:\Users\admin\AppData\Local\Temp\Cab103F.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | _65004.exe | C:\Users\admin\AppData\Local\Temp\Tar1040.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | _65004.exe | C:\Users\admin\AppData\Local\Temp\Cab10EC.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | _65004.exe | C:\Users\admin\AppData\Local\Temp\Tar10ED.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | _65004.exe | C:\Users\admin\AppData\Local\Temp\Cab115C.tmp | — | |
MD5:— | SHA256:— | |||
| 3896 | _65004.exe | C:\Users\admin\AppData\Local\Temp\Tar115D.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
13
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3896 | _65004.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
3896 | _65004.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
3896 | _65004.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
3896 | _65004.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
3896 | _65004.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
3896 | _65004.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
3896 | _65004.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
3896 | _65004.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
3896 | _65004.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
3880 | sll.exe | GET | 200 | 115.231.171.135:80 | http://api.ip138.com/query/?datatype=jsonp&token=cb7b47fb53f57902917d914c81030b28 | CN | text | 77 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3880 | sll.exe | 123.59.116.117:4530 | ceshi.hgzvip.net | China Unicom Beijing Province Network | CN | malicious |
3880 | sll.exe | 123.59.116.117:4531 | ceshi.hgzvip.net | China Unicom Beijing Province Network | CN | malicious |
3880 | sll.exe | 123.59.116.117:4532 | ceshi.hgzvip.net | China Unicom Beijing Province Network | CN | malicious |
3880 | sll.exe | 115.231.171.135:80 | api.ip138.com | No.31,Jin-rong Street | CN | unknown |
3880 | sll.exe | 123.59.209.193:9900 | safe.hgzvip.net | China Unicom Beijing Province Network | CN | malicious |
3880 | sll.exe | 123.59.209.193:9901 | safe.hgzvip.net | China Unicom Beijing Province Network | CN | malicious |
3896 | _65004.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
ceshi.hgzvip.net |
| malicious |
safe.hgzvip.net |
| malicious |
api.ip138.com |
| suspicious |
Threats
Process | Message |
|---|---|
mmc.exe | ViewerConfigPath = 'C:\ProgramData\Microsoft\Event Viewer': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerViewsFolderPath = 'C:\ProgramData\Microsoft\Event Viewer\Views': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerAdminViewsPath = 'C:\ProgramData\Microsoft\Event Viewer\Views\ApplicationViewsRootNode': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerExternalLogsPath = 'C:\ProgramData\Microsoft\Event Viewer\ExternalLogs': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerExtension
|
mmc.exe | ViewerViewsFolderPath = 'C:\ProgramData\Microsoft\Event Viewer\Views': Microsoft.Windows.ManagementUI.CombinedControls.EvĜ |
mmc.exe | ViewerViewsFolderPath = 'C:\ProgramData\Microsoft\Event Viewer\Views': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerExternalLogsPath = 'C:\ProgramData\Microsoft\Event Viewer\ExternalLogs': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerExternalLogsPath = 'C:\ProgramData\Microsoft\Event Viewer\ExternalLogs': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerExtension
|