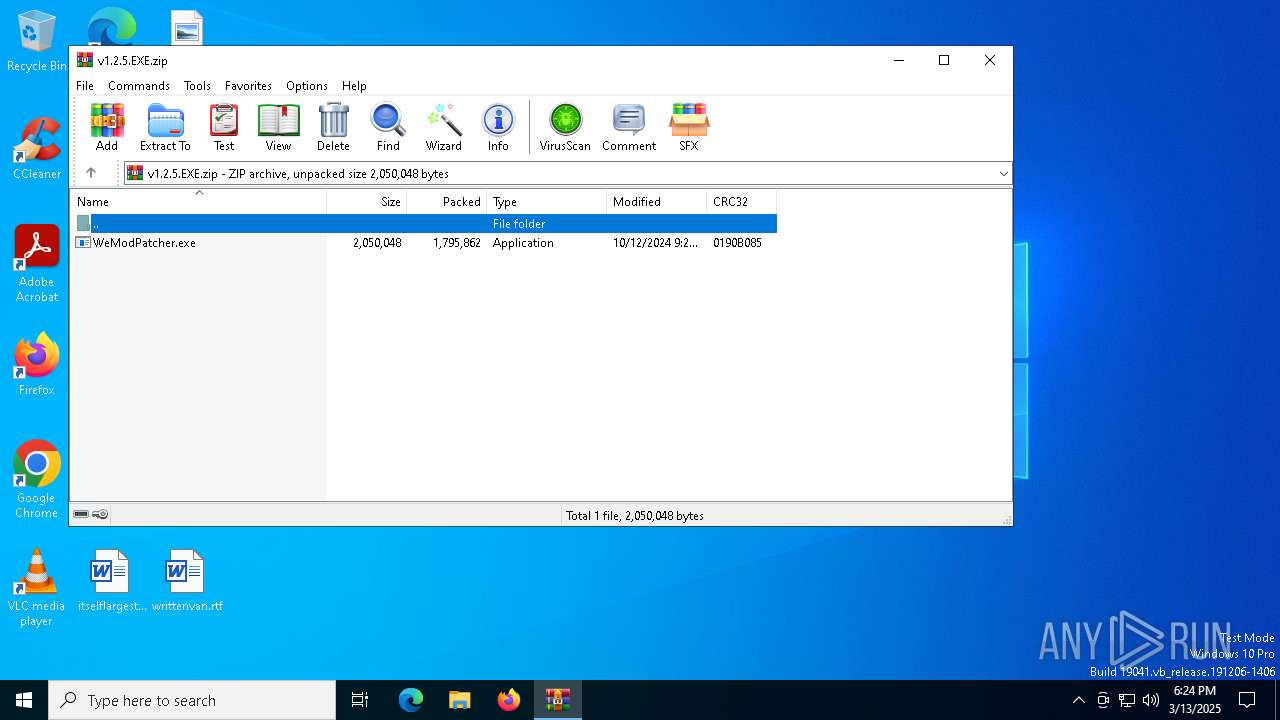
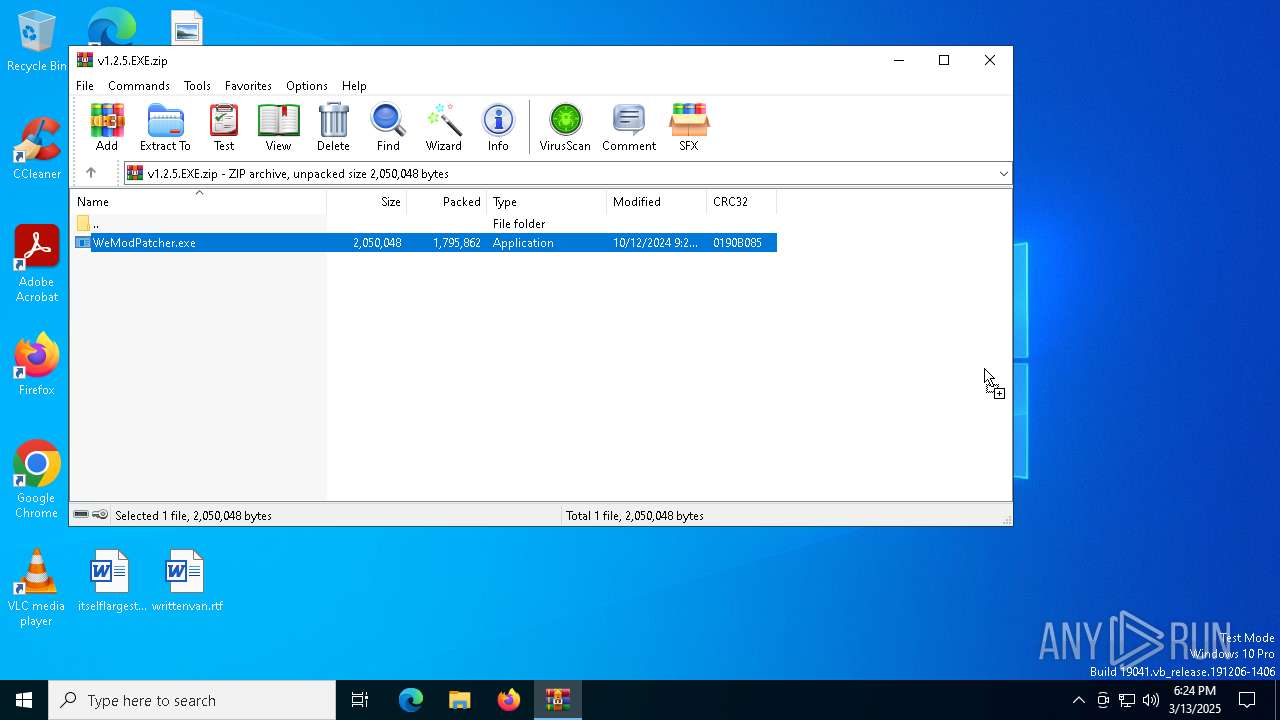
| download: | /brunolee-GIT/W3M0dP4tch32/releases/download/v1.2.5/v1.2.5.EXE.zip |
| Full analysis: | https://app.any.run/tasks/6a8a2cb5-3aff-4721-8aba-d2b0540c3514 |
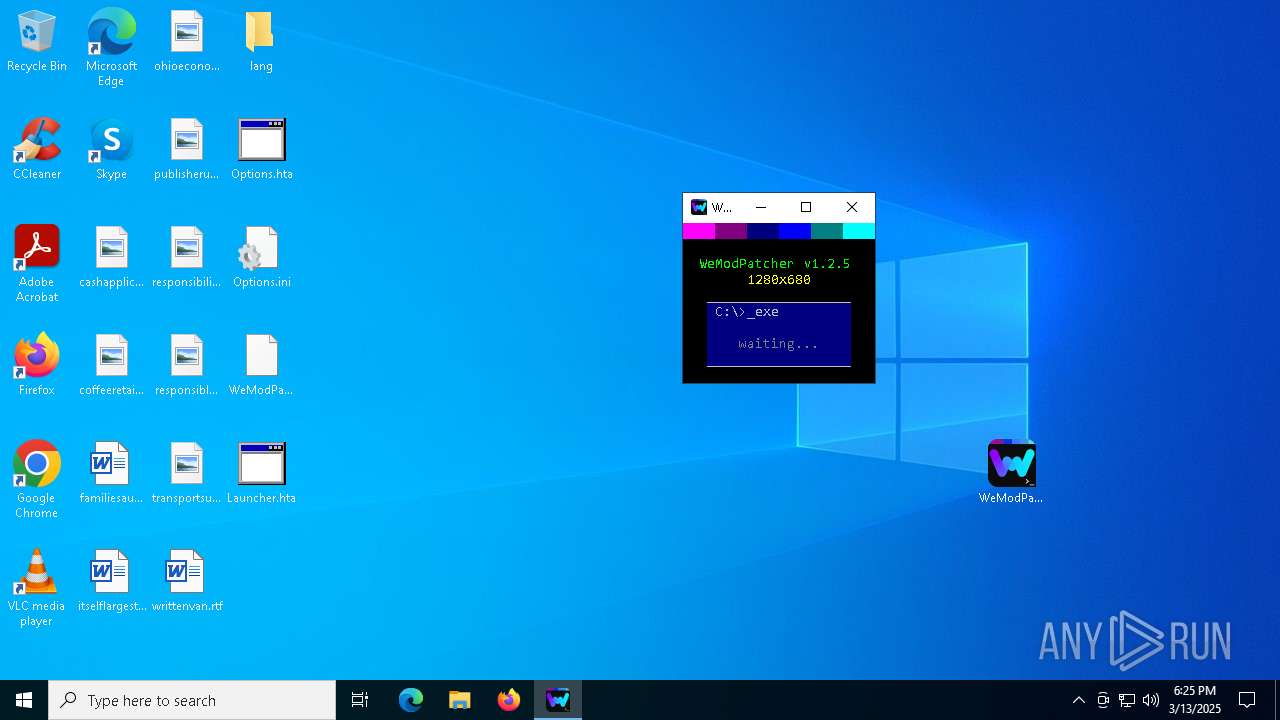
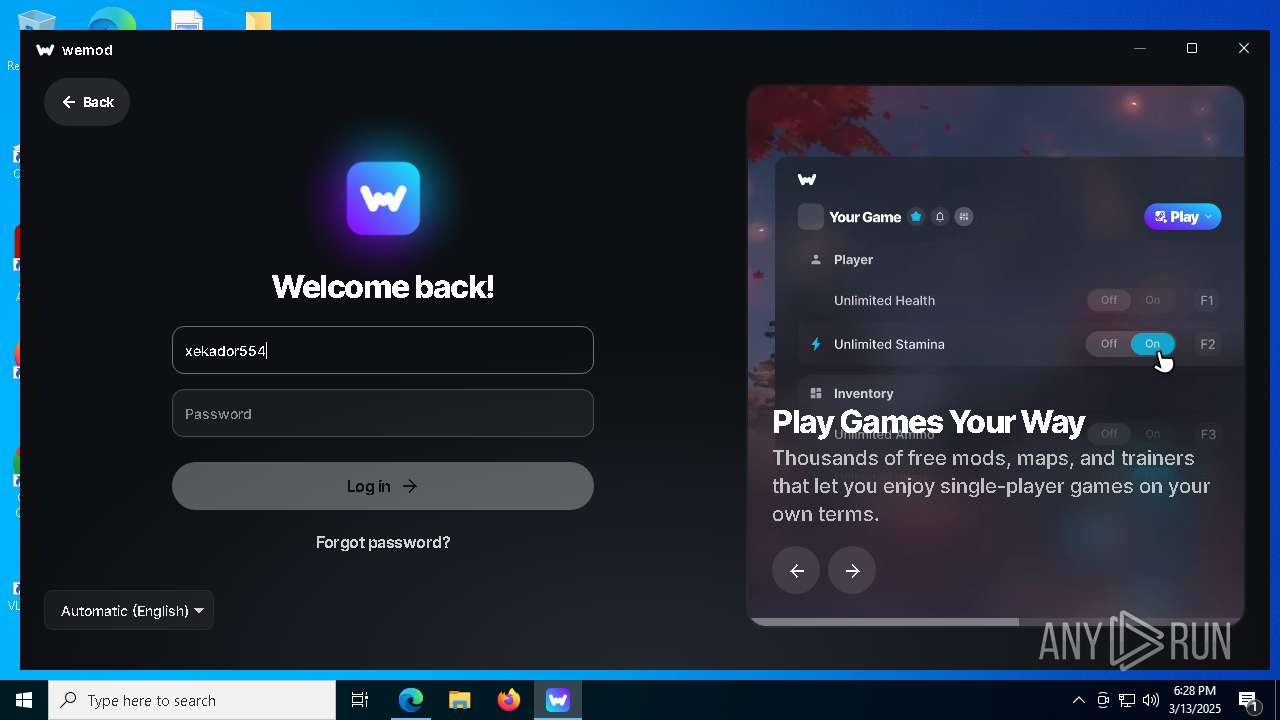
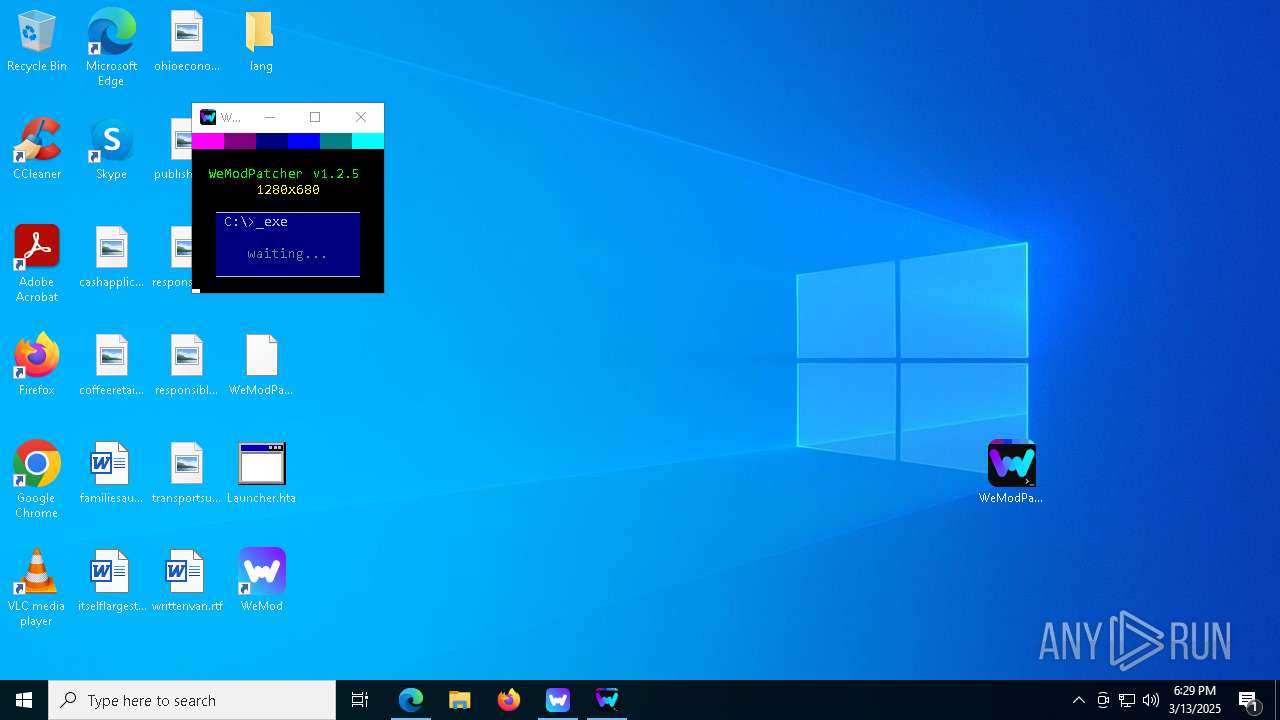
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2025, 18:24:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 3CDEC4330A50CB46375A7C7370BE9AA5 |
| SHA1: | 133E5A51F9724A520DE0F5D9ED6B46EF0F1EE784 |
| SHA256: | 111B7F3EA4018026745DA5DBFAD184020E259BDA127B0E69C9A1271AC46837AE |
| SSDEEP: | 98304:SchXTYT5ftNU2WkyI521Fy9HF4M72IJ0Dg0U9C85CqXkVJGNX3TZpPArvIppo6Lg:0A0y2C |
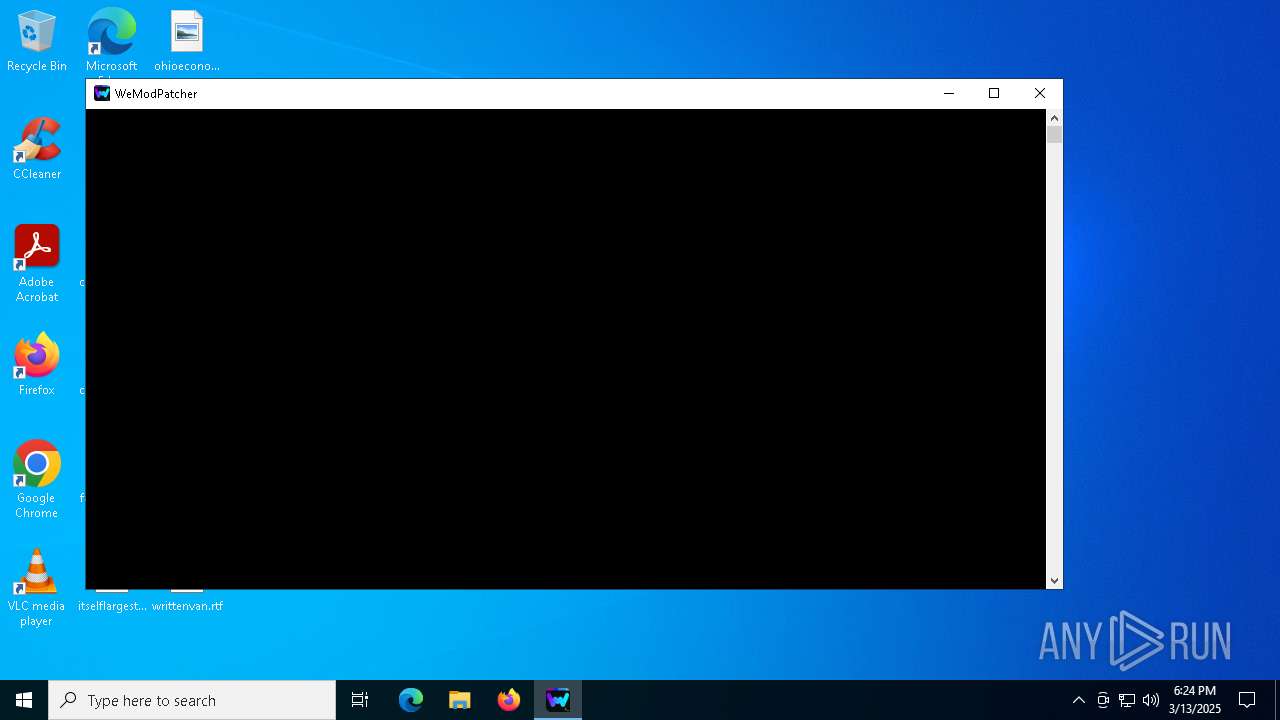
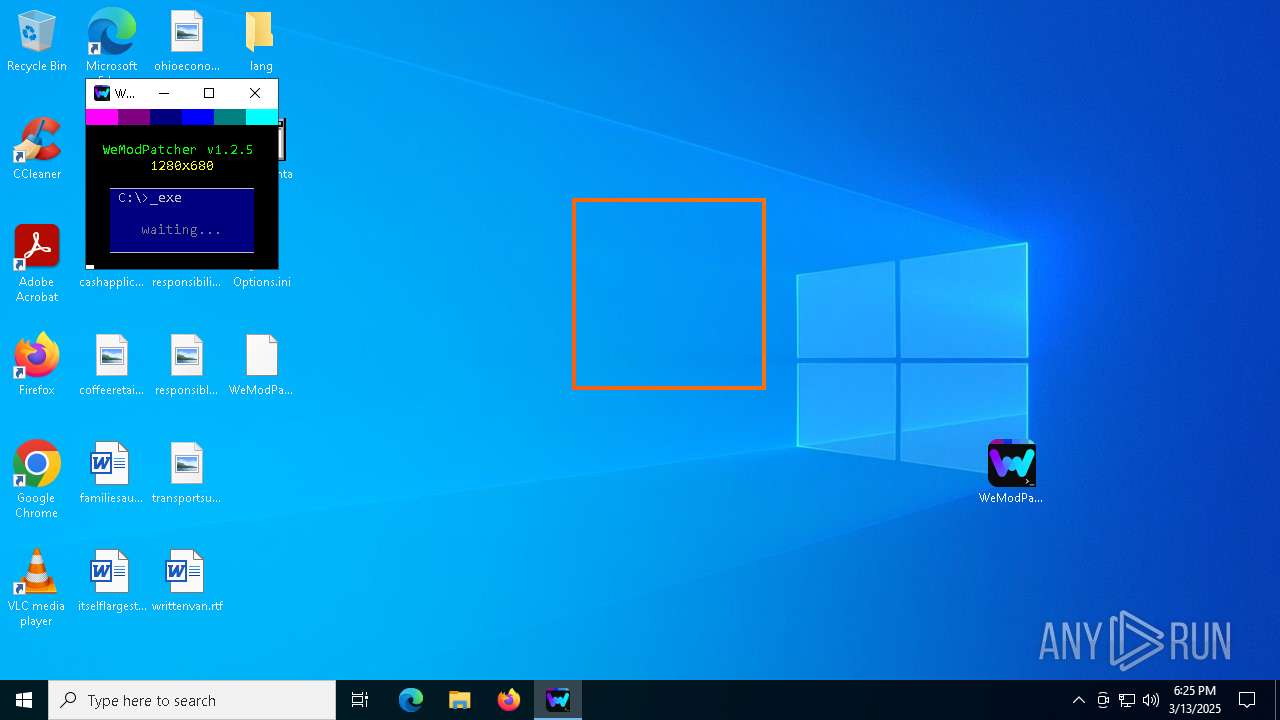
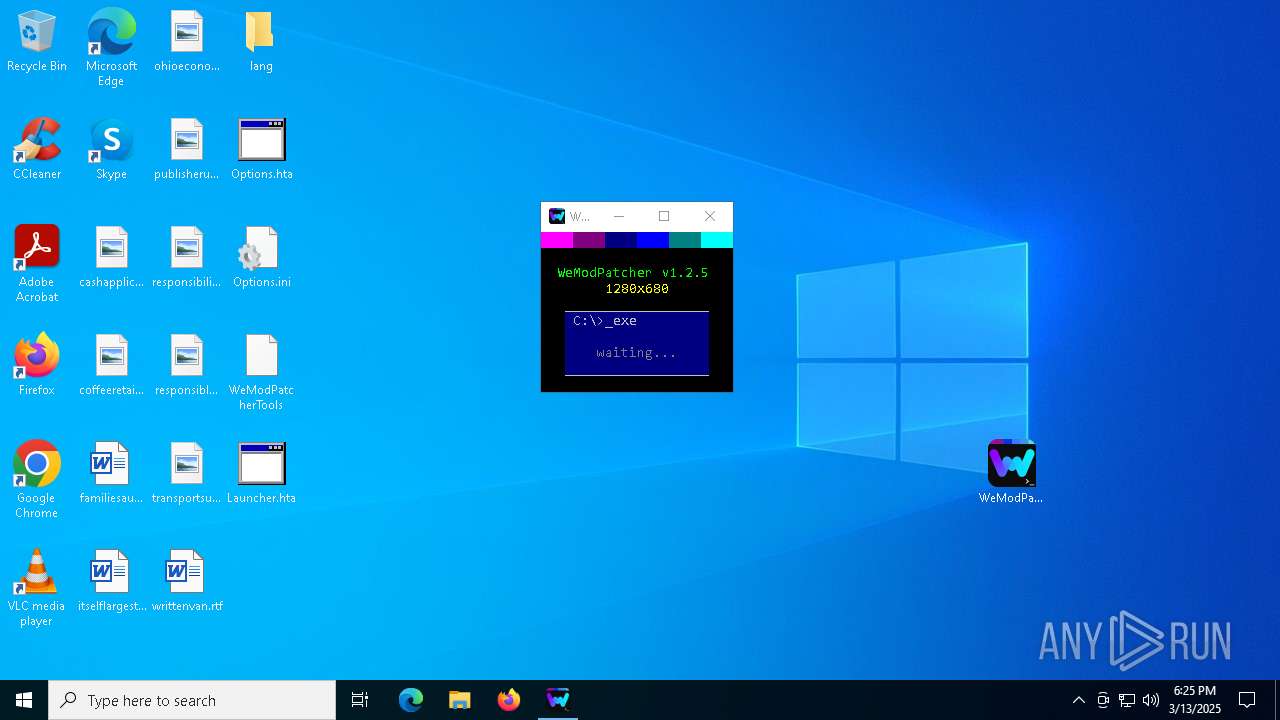
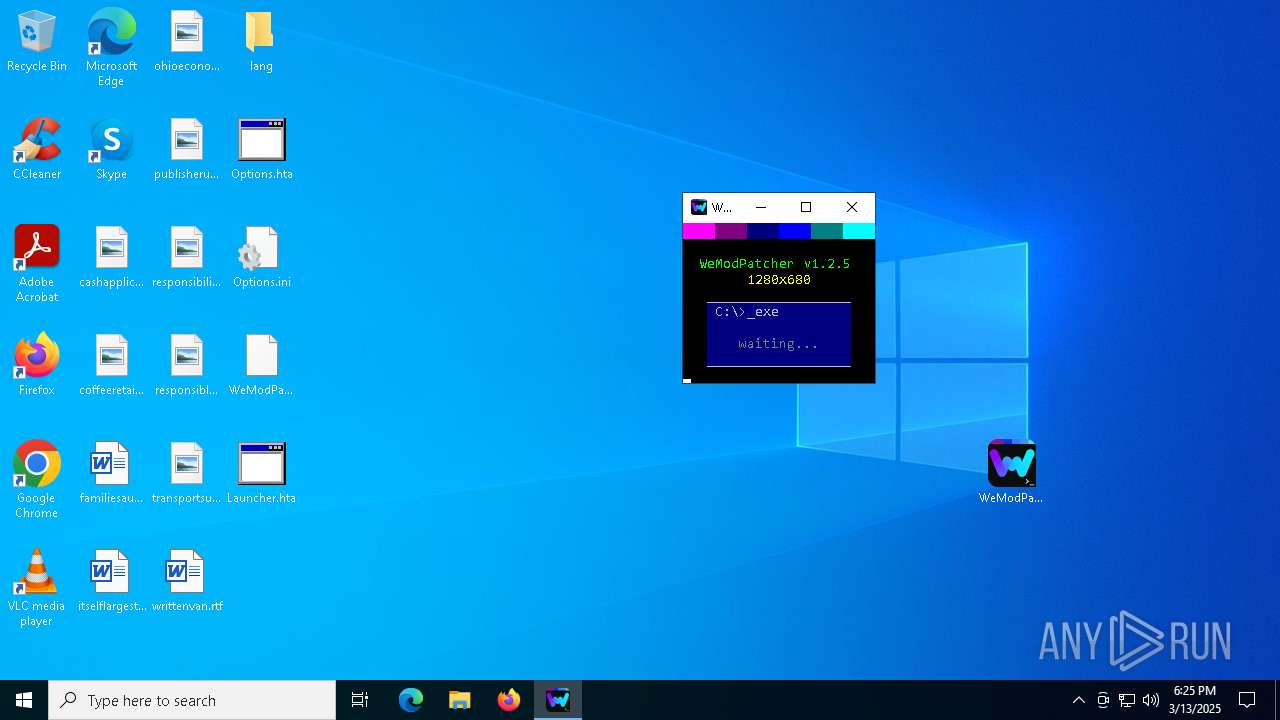
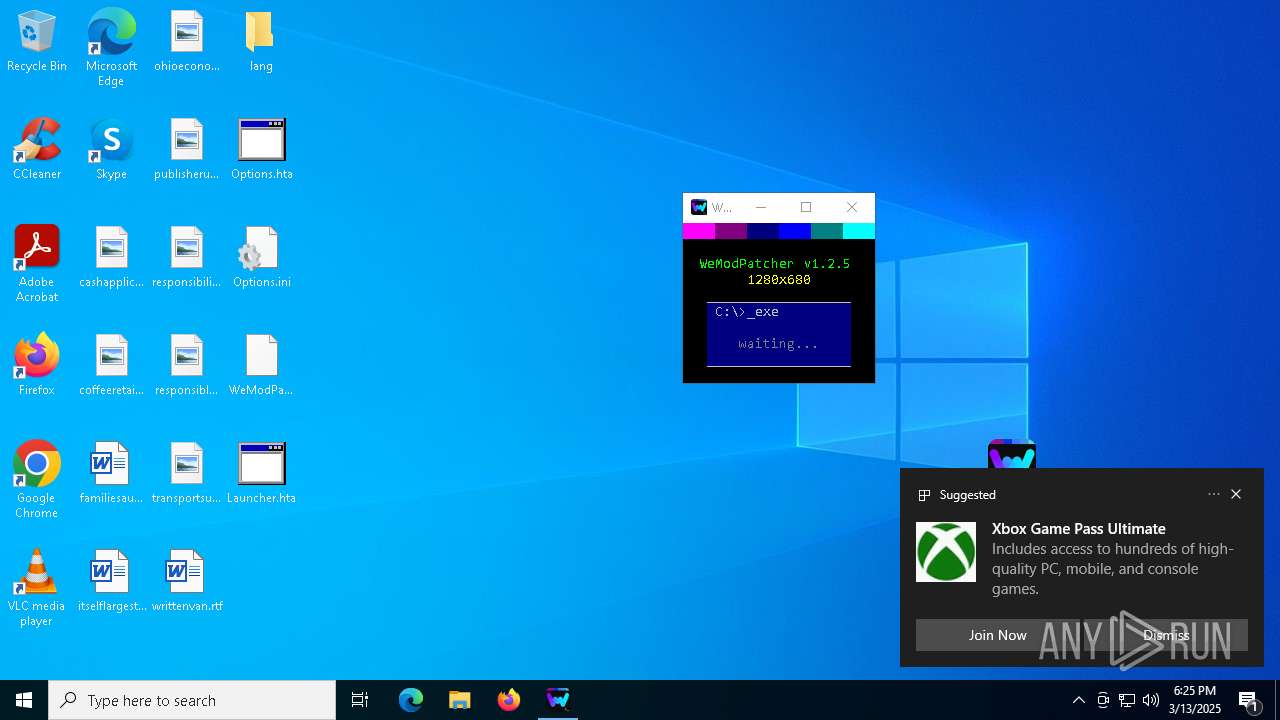
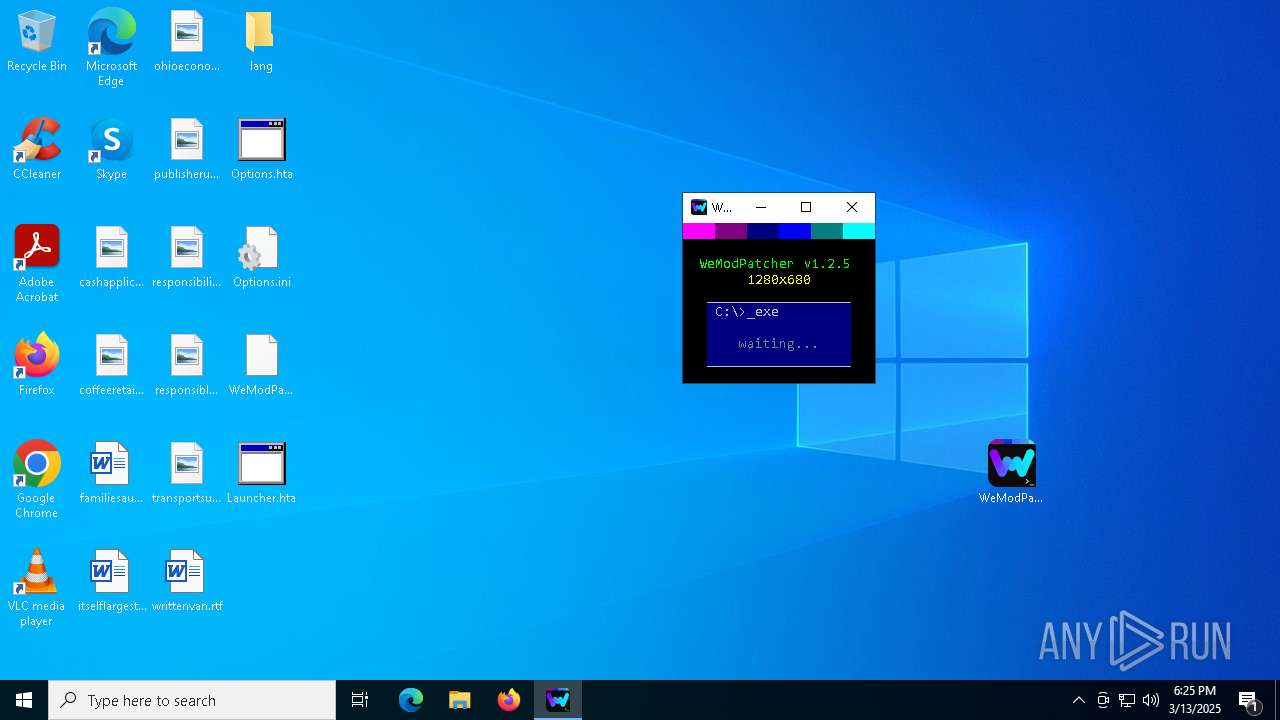
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 4620)
SUSPICIOUS
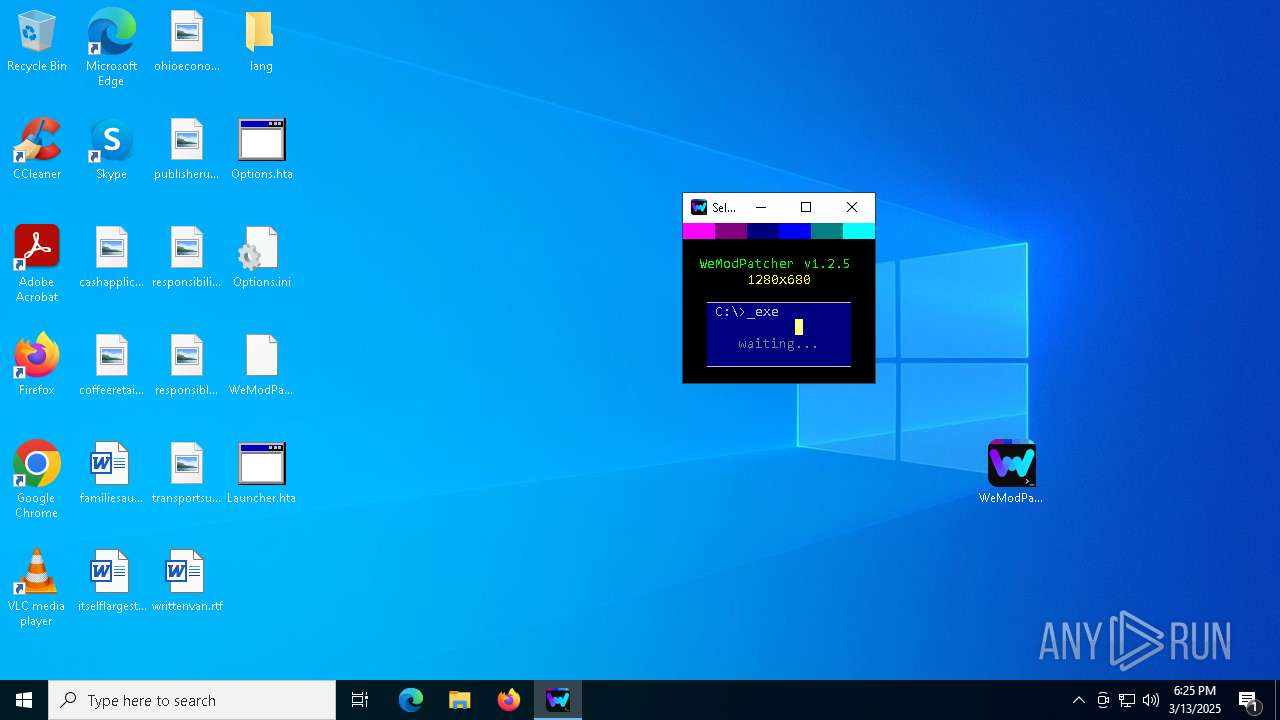
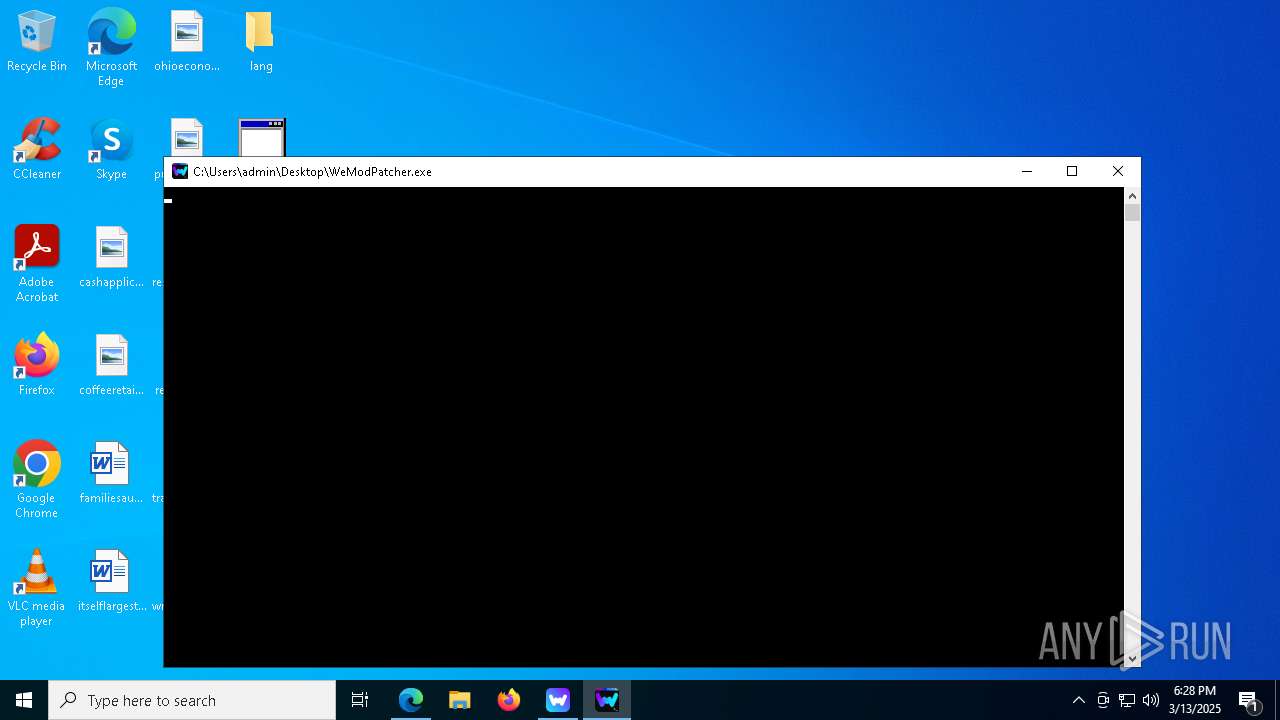
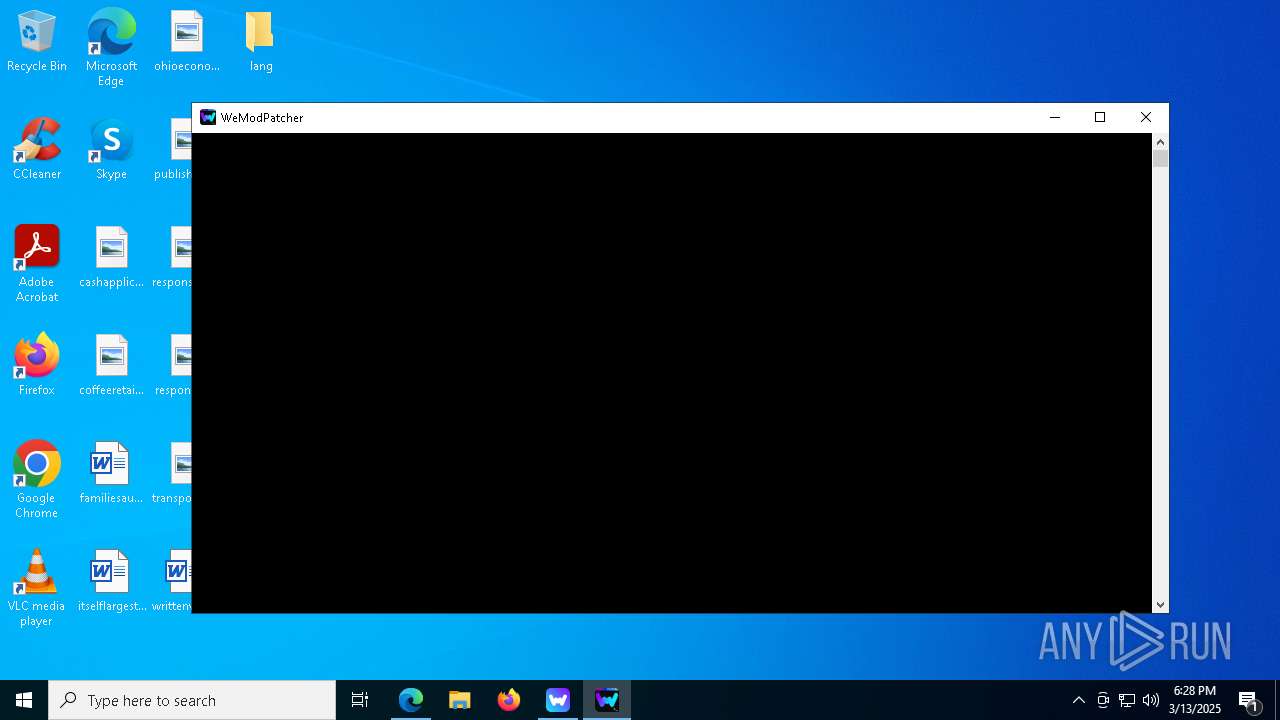
Starts CMD.EXE for commands execution
- WeModPatcher.exe (PID: 7304)
- cmd.exe (PID: 7404)
- WeModPatcher.exe (PID: 664)
- cmd.exe (PID: 8404)
Execution of CURL command
- cmd.exe (PID: 7404)
- cmd.exe (PID: 8404)
Drops 7-zip archiver for unpacking
- WeModPatcher.exe (PID: 7304)
Get information on the list of running processes
- cmd.exe (PID: 7404)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 8404)
- cmd.exe (PID: 8628)
- cmd.exe (PID: 8428)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7892)
- cmd.exe (PID: 7488)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 7272)
- cmd.exe (PID: 5124)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 7772)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 4112)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 5024)
- cmd.exe (PID: 1088)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 7988)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 5500)
- cmd.exe (PID: 8404)
- cmd.exe (PID: 8628)
- cmd.exe (PID: 7488)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 5364)
- cmd.exe (PID: 5436)
- cmd.exe (PID: 3572)
- cmd.exe (PID: 132)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 7260)
- cmd.exe (PID: 9008)
- cmd.exe (PID: 8308)
- cmd.exe (PID: 2564)
- cmd.exe (PID: 6068)
- cmd.exe (PID: 9192)
Executing commands from a ".bat" file
- WeModPatcher.exe (PID: 7304)
- WeModPatcher.exe (PID: 664)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 7404)
- net.exe (PID: 7608)
- cmd.exe (PID: 8404)
- net.exe (PID: 2840)
Application launched itself
- cmd.exe (PID: 7404)
- WeMod.exe (PID: 9016)
- cmd.exe (PID: 8404)
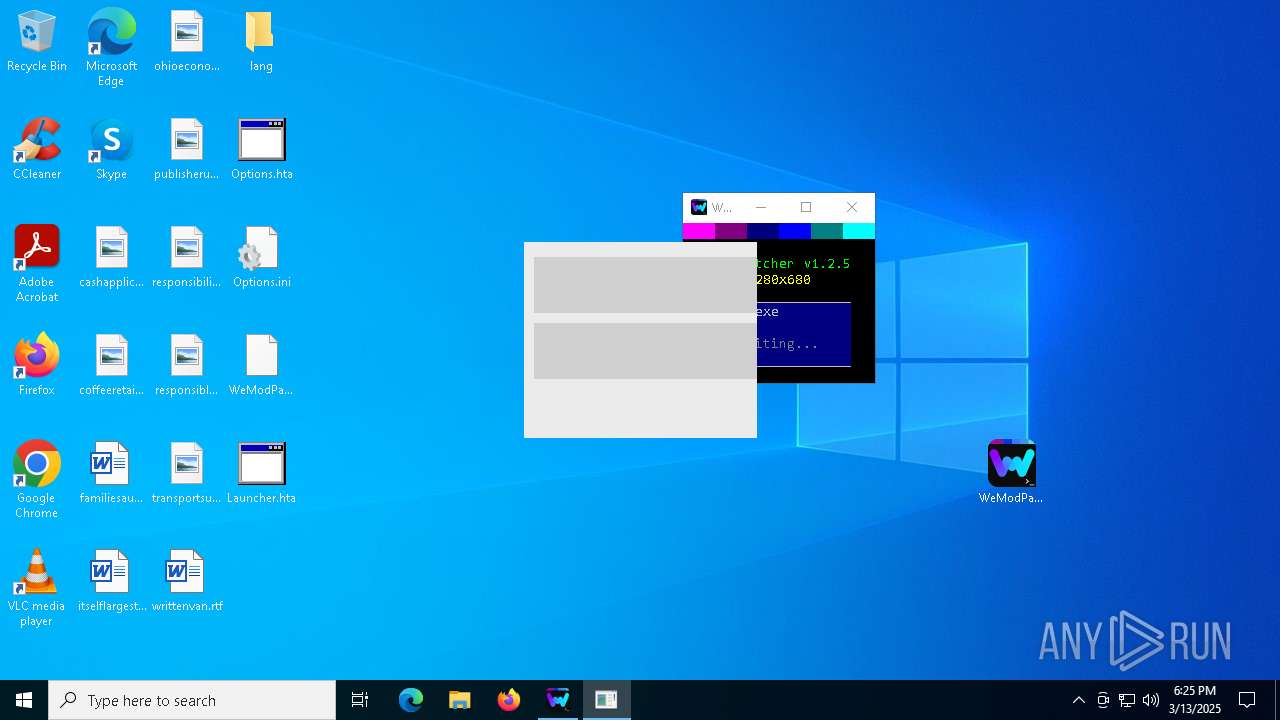
Starts application with an unusual extension
- cmd.exe (PID: 8004)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 8328)
- cmd.exe (PID: 8404)
The process creates files with name similar to system file names
- WerFault.exe (PID: 8012)
- WerFault.exe (PID: 8052)
- WerFault.exe (PID: 7180)
- WerFault.exe (PID: 5228)
- WerFault.exe (PID: 7320)
Executes application which crashes
- mshta.exe (PID: 7960)
- mshta.exe (PID: 8140)
- mshta.exe (PID: 1020)
- mshta.exe (PID: 4400)
- mshta.exe (PID: 7784)
- mshta.exe (PID: 6028)
- mshta.exe (PID: 2088)
- mshta.exe (PID: 7344)
- mshta.exe (PID: 2416)
- mshta.exe (PID: 6712)
- mshta.exe (PID: 5608)
- mshta.exe (PID: 8864)
- mshta.exe (PID: 8568)
- mshta.exe (PID: 1116)
- mshta.exe (PID: 2576)
- mshta.exe (PID: 4672)
- mshta.exe (PID: 8960)
- mshta.exe (PID: 5968)
Creates FileSystem object to access computer's file system (SCRIPT)
- mshta.exe (PID: 7960)
- mshta.exe (PID: 8140)
- mshta.exe (PID: 1020)
- mshta.exe (PID: 4400)
- mshta.exe (PID: 7784)
- mshta.exe (PID: 6028)
- mshta.exe (PID: 7344)
- mshta.exe (PID: 2088)
- mshta.exe (PID: 2416)
- mshta.exe (PID: 6712)
- mshta.exe (PID: 2576)
- mshta.exe (PID: 8864)
- mshta.exe (PID: 5608)
- mshta.exe (PID: 1116)
- mshta.exe (PID: 8568)
- mshta.exe (PID: 8960)
- mshta.exe (PID: 4672)
- mshta.exe (PID: 5968)
Process drops legitimate windows executable
- Update.exe (PID: 8424)
Executable content was dropped or overwritten
- Update.exe (PID: 8424)
INFO
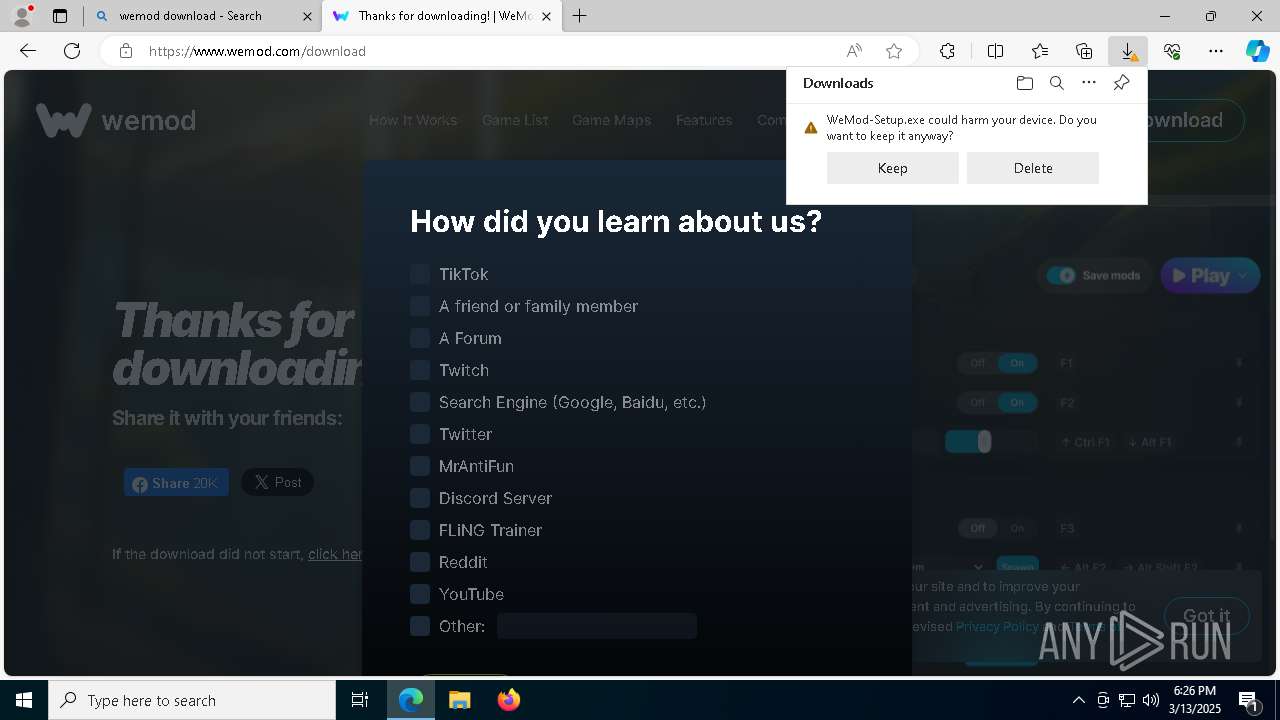
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4620)
- msedge.exe (PID: 5324)
- msedge.exe (PID: 5244)
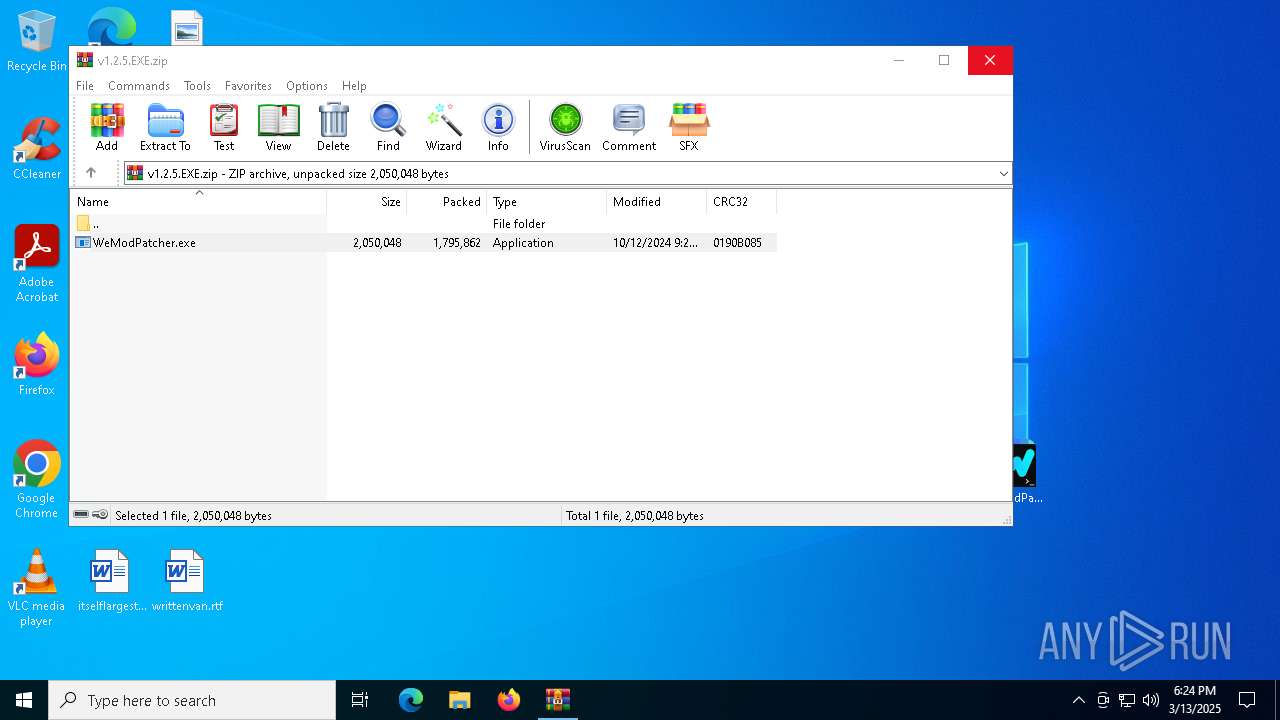
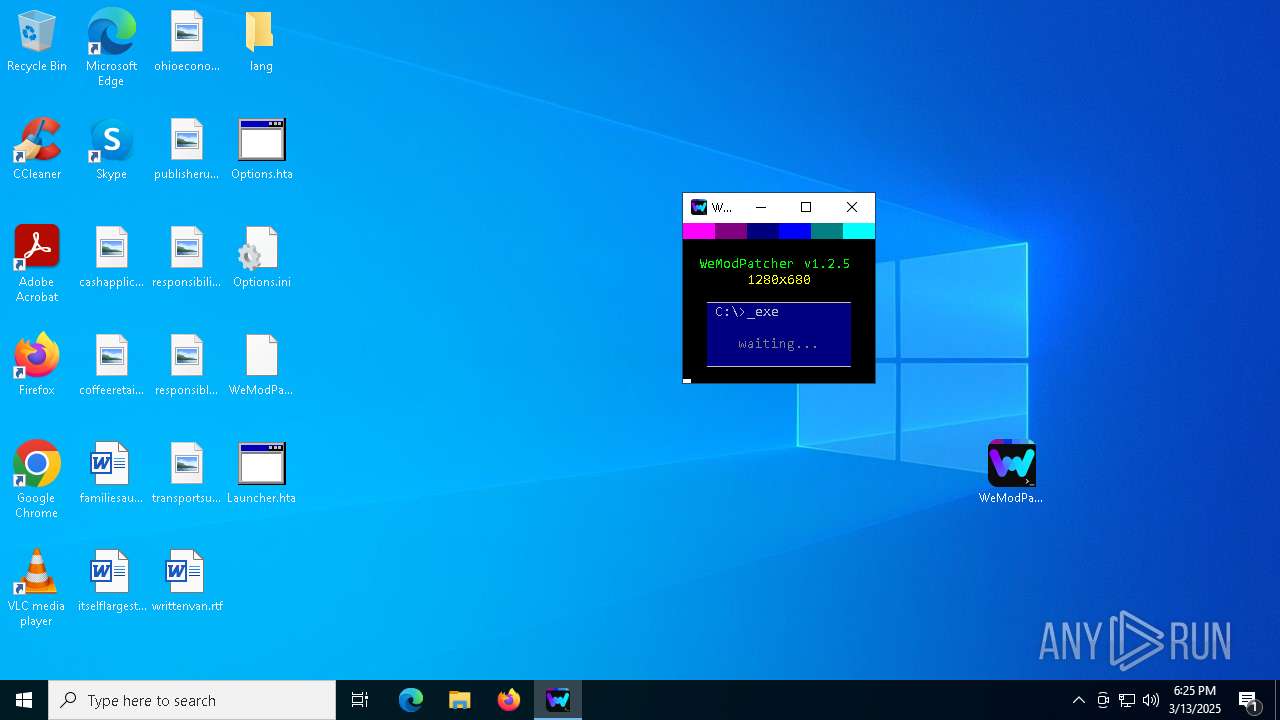
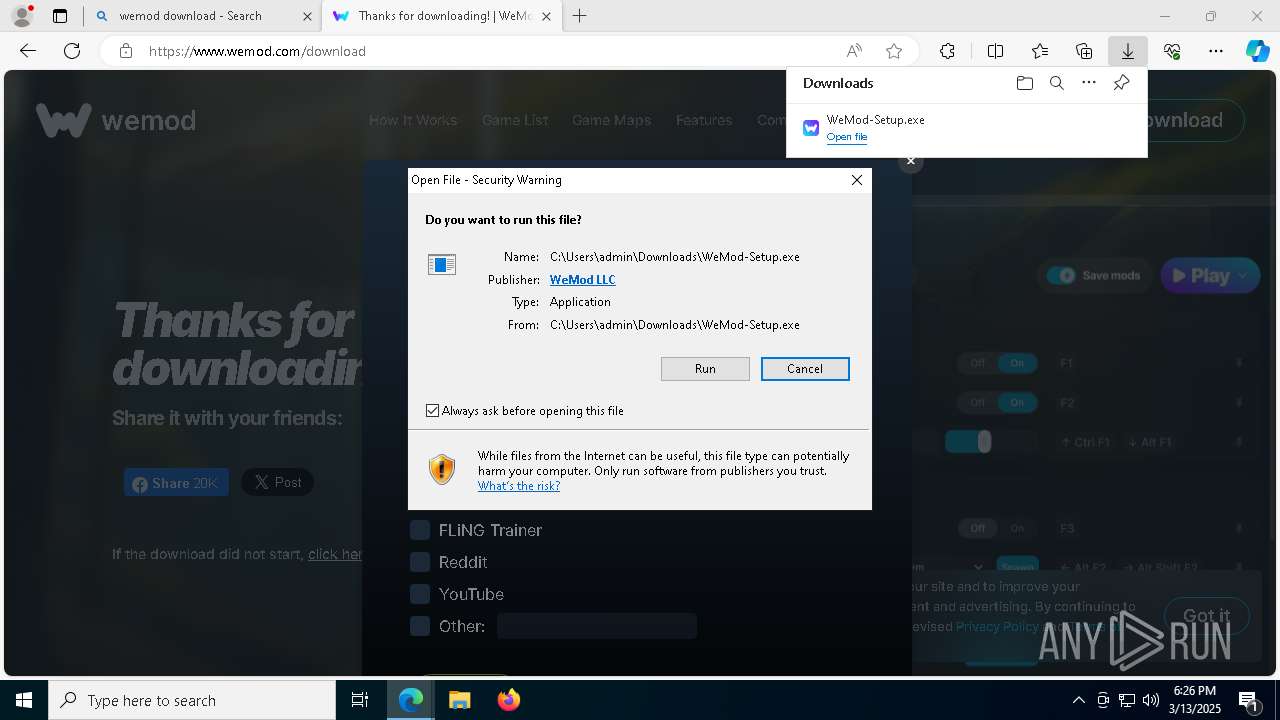
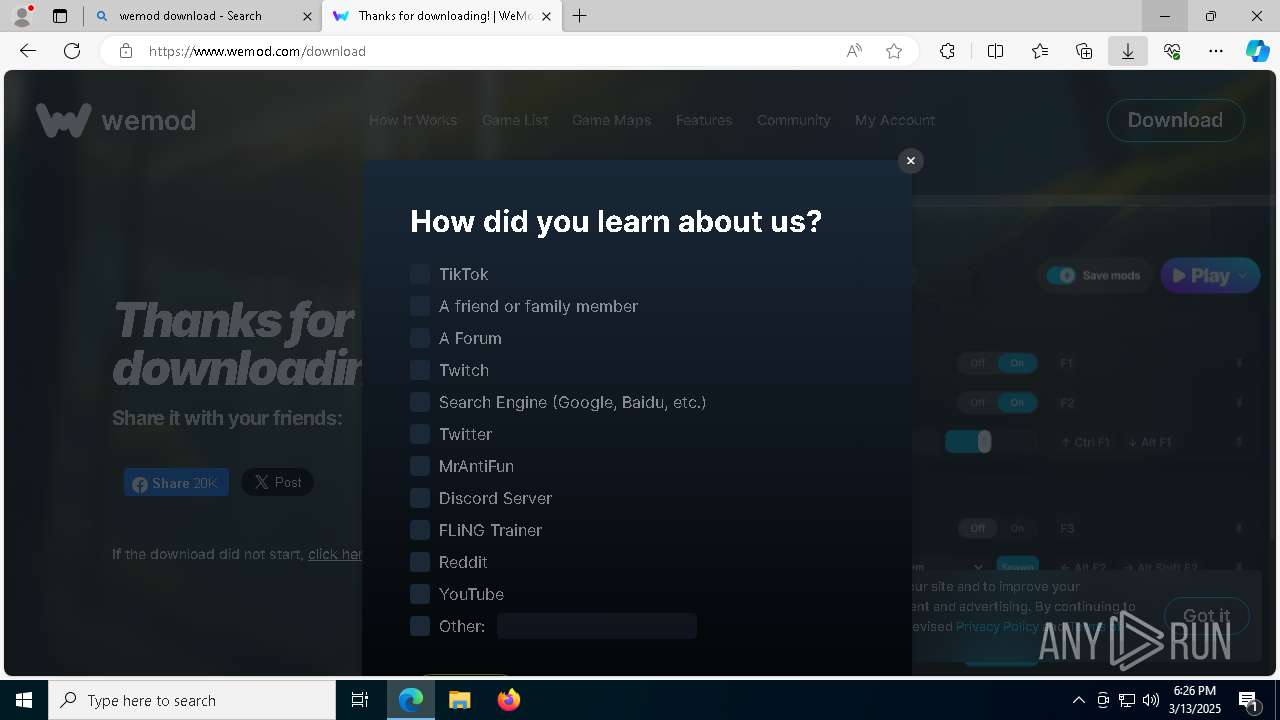
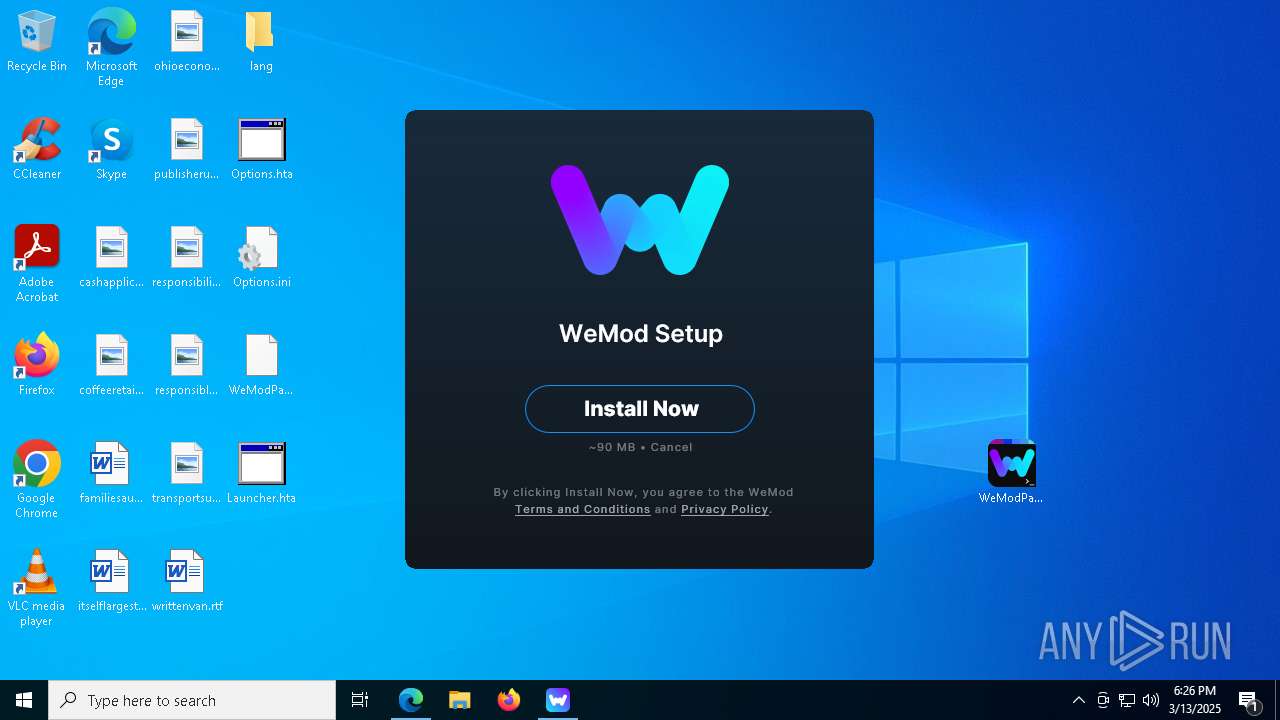
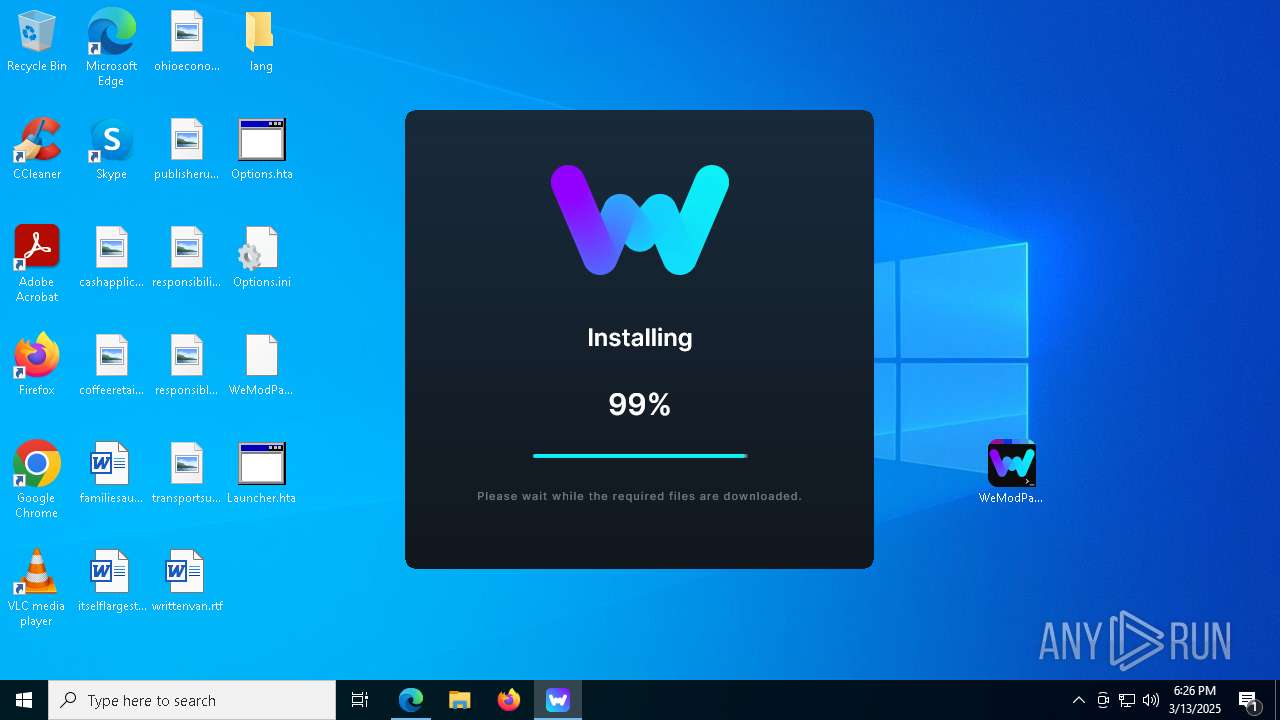
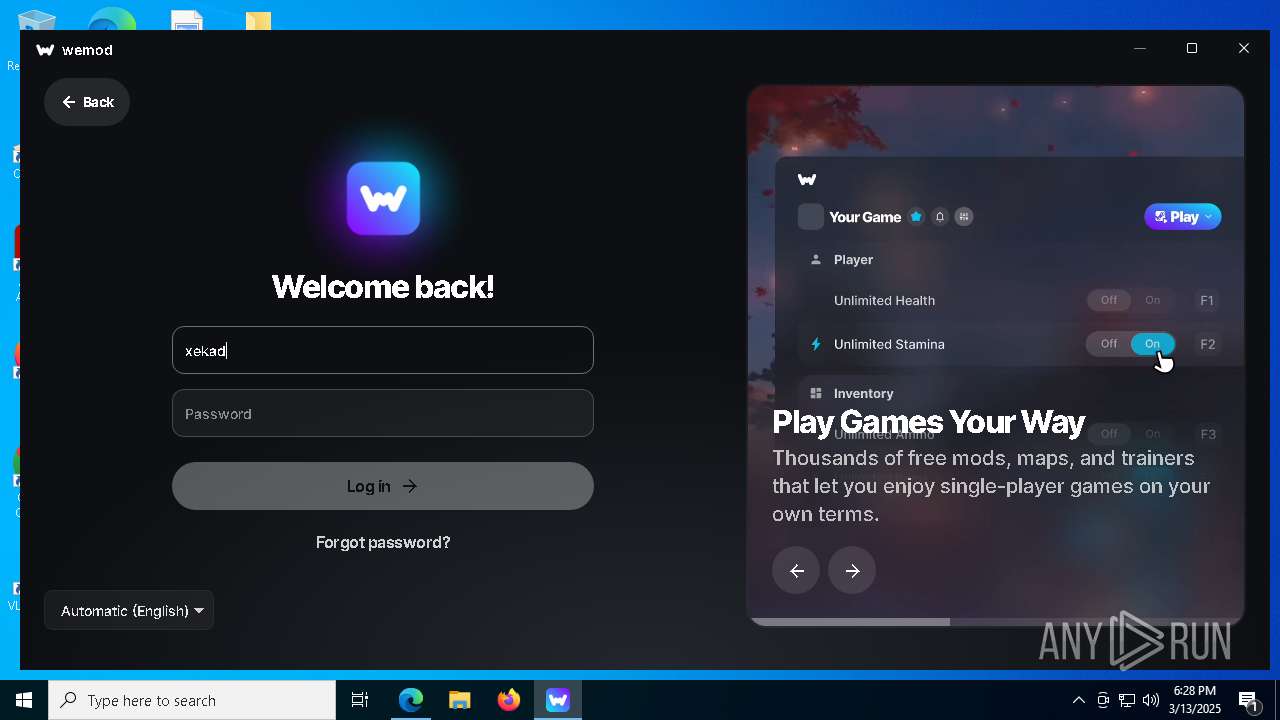
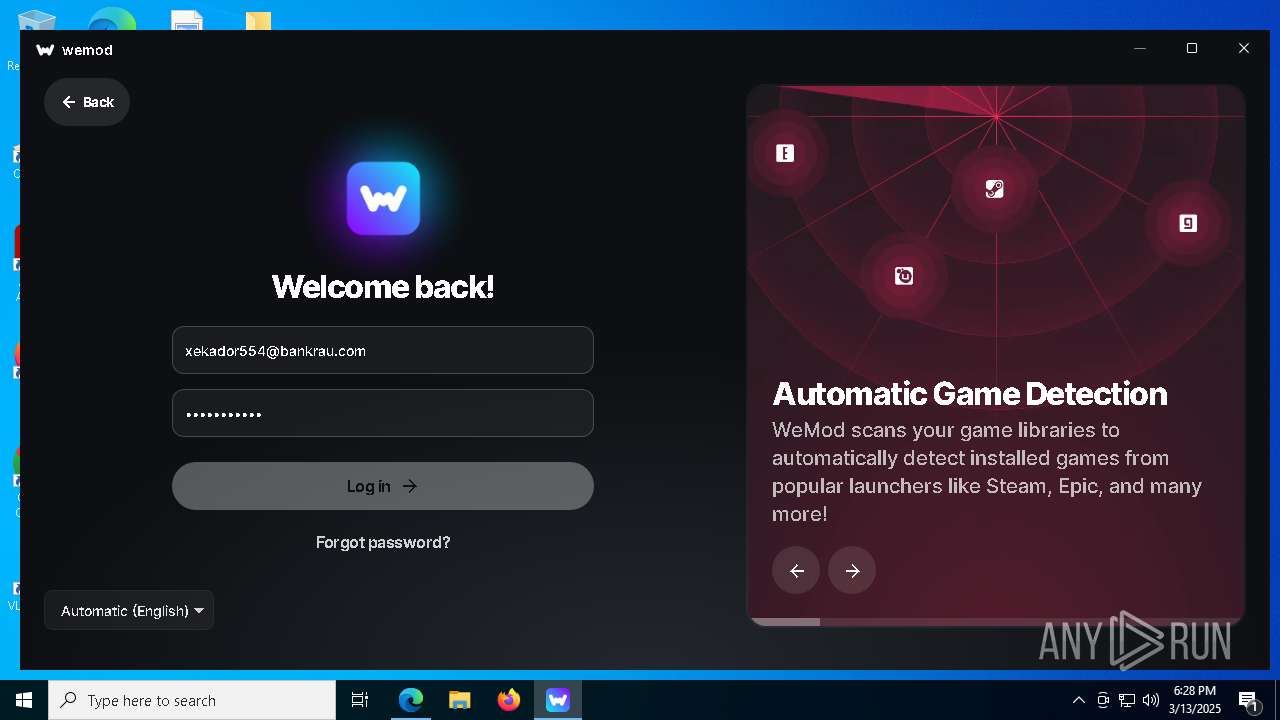
Manual execution by a user
- WeModPatcher.exe (PID: 7304)
- WeModPatcher.exe (PID: 664)
- msedge.exe (PID: 5324)
The sample compiled with english language support
- WeModPatcher.exe (PID: 7304)
- WinRAR.exe (PID: 4620)
- Update.exe (PID: 8424)
- msedge.exe (PID: 5244)
Checks supported languages
- WeModPatcher.exe (PID: 7304)
- curl.exe (PID: 7444)
- chcp.com (PID: 8048)
- mode.com (PID: 8068)
- chcp.com (PID: 8020)
Execution of CURL command
- cmd.exe (PID: 7424)
- cmd.exe (PID: 8124)
Create files in a temporary directory
- WeModPatcher.exe (PID: 7304)
Reads the computer name
- curl.exe (PID: 7444)
Starts MODE.COM to configure console settings
- mode.com (PID: 8068)
- mode.com (PID: 8888)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 1180)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 4724)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 4724)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 4724)
- WerFault.exe (PID: 8012)
- WerFault.exe (PID: 8052)
- WerFault.exe (PID: 7180)
- WerFault.exe (PID: 5228)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7176)
- powershell.exe (PID: 7776)
Changes the display of characters in the console
- cmd.exe (PID: 8004)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 8404)
- cmd.exe (PID: 8328)
Application launched itself
- msedge.exe (PID: 5324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:10:12 22:25:54 |
| ZipCRC: | 0x0190b085 |
| ZipCompressedSize: | 1795862 |
| ZipUncompressedSize: | 2050048 |
| ZipFileName: | WeModPatcher.exe |
Total processes
442
Monitored processes
277
Malicious processes
4
Suspicious processes
21
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "(Get-Culture).Name" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | powershell -Command "[string]([Version]'1.2.5', [Version]'1.2.5' | measure-object -maximum).maximum" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=5356 --field-trial-handle=2308,i,6704794923440764483,4649765507546012963,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7752 --field-trial-handle=2308,i,6704794923440764483,4649765507546012963,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7976 --field-trial-handle=2308,i,6704794923440764483,4649765507546012963,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | "C:\Users\admin\Desktop\WeModPatcher.exe" | C:\Users\admin\Desktop\WeModPatcher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --mojo-platform-channel-handle=6016 --field-trial-handle=2308,i,6704794923440764483,4649765507546012963,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 772 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=9640 --field-trial-handle=2308,i,6704794923440764483,4649765507546012963,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 776 | C:\WINDOWS\system32\cmd.exe /c mshta.exe "C:\Users\admin\Desktop\Launcher.hta" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225477 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 832 | C:\WINDOWS\system32\WerFault.exe -u -p 8960 -s 1852 | C:\Windows\System32\WerFault.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
253 726
Read events
253 585
Write events
121
Delete events
20
Modification events
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\v1.2.5.EXE.zip | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (4620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
82
Suspicious files
1 217
Text files
299
Unknown types
4
Dropped files
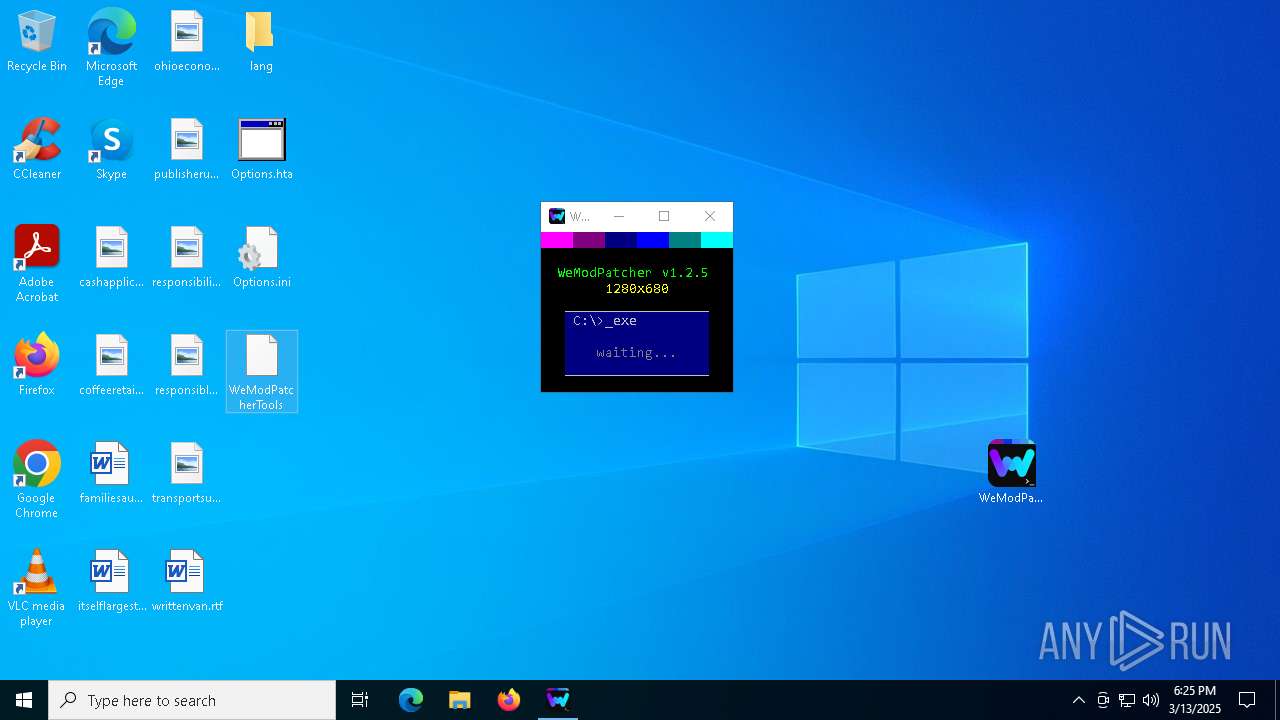
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7304 | WeModPatcher.exe | C:\Users\admin\Desktop\Options.ini | text | |
MD5:83503A2A8B9F78CFFA4ED444885C4959 | SHA256:E217B87EA4F57FA0FBF70BED27EDA1DA7FF3A4D3B7A989BF15B1261E6735387A | |||
| 7304 | WeModPatcher.exe | C:\Users\admin\Desktop\lang\lang_de.ini | text | |
MD5:56F718D833D85B64D368A746CEC7D311 | SHA256:9296A56AE3F33183E5DD78159EEDC14E7C55D58B6FF984D30480927F3491A0A6 | |||
| 7304 | WeModPatcher.exe | C:\Users\admin\Desktop\Options.hta | html | |
MD5:C0826786D1B58B03C4C134865CD0A0A6 | SHA256:E4CDEA4433591103E4C416165B9B7EEBFF79C30B011EEE839064C0621FE0B209 | |||
| 7304 | WeModPatcher.exe | C:\Users\admin\Desktop\lang\lang_en.ini | text | |
MD5:DA7F78CEA561177B4593E43E472B8A61 | SHA256:5CE043FA53863E2FC94E42D72D870DA746D94CA5CDBC1E1F6FBD364681D69F26 | |||
| 4620 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4620.9837\WeModPatcher.exe | executable | |
MD5:2D2B9C759730A8B30107748A3FDF9F09 | SHA256:23EF62989C2210F05BD598C64EC995B96C381EE15FF78ECDD6225FB163C0A388 | |||
| 7304 | WeModPatcher.exe | C:\Users\admin\AppData\Local\Temp\CE7D.tmp\CE7E.tmp\CE7F.bat | binary | |
MD5:A11E36537E59303FD2D217D30C310F21 | SHA256:312EEF935DFB4A14D9997555C1921BE0EAD0AB209FEE2D655148C91C9A60EA0D | |||
| 7304 | WeModPatcher.exe | C:\Users\admin\Desktop\lang\lang_es.ini | text | |
MD5:EFE851D125CBF4EA90D87CF1F469E331 | SHA256:5D75679F3A5CD60EA5700C5F83AF9411D404B1A6077EB994D90597BDFE9855D9 | |||
| 7304 | WeModPatcher.exe | C:\Users\admin\Desktop\lang\lang_pt.ini | text | |
MD5:98D8CB666E73522D7478520D685183CC | SHA256:E56FB42EA5361EDF06D352ADCB3C46CD2A675C59D455B2FAF7D14727ACA1ADE3 | |||
| 4724 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\66b01ad0-9e8b-4bba-8561-07d2f3d41098.down_data | — | |
MD5:— | SHA256:— | |||
| 7304 | WeModPatcher.exe | C:\Users\admin\Desktop\lang\lang_ru.ini | text | |
MD5:0CA2E71373B332E16C4DD703DD55D7D2 | SHA256:B2AD6A04B335B3421A7B180B5AFB3CFCDF965380F4AC46F0652BEE5F8BD982FD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
194
DNS requests
241
Threats
53
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
756 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | binary | 1.42 Kb | whitelisted |
756 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | binary | 2.18 Kb | whitelisted |
3888 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
4724 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 312 b | whitelisted |
4724 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | CL | binary | 419 b | whitelisted |
4724 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | CL | binary | 408 b | whitelisted |
5324 | msedge.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | DE | binary | 727 b | whitelisted |
5324 | msedge.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | DE | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7444 | curl.exe | 185.199.108.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
756 | lsass.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | whitelisted |
3888 | backgroundTaskHost.exe | 20.31.169.57:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
5312 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5312 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5312 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5312 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5312 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5312 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5312 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5312 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
5312 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |