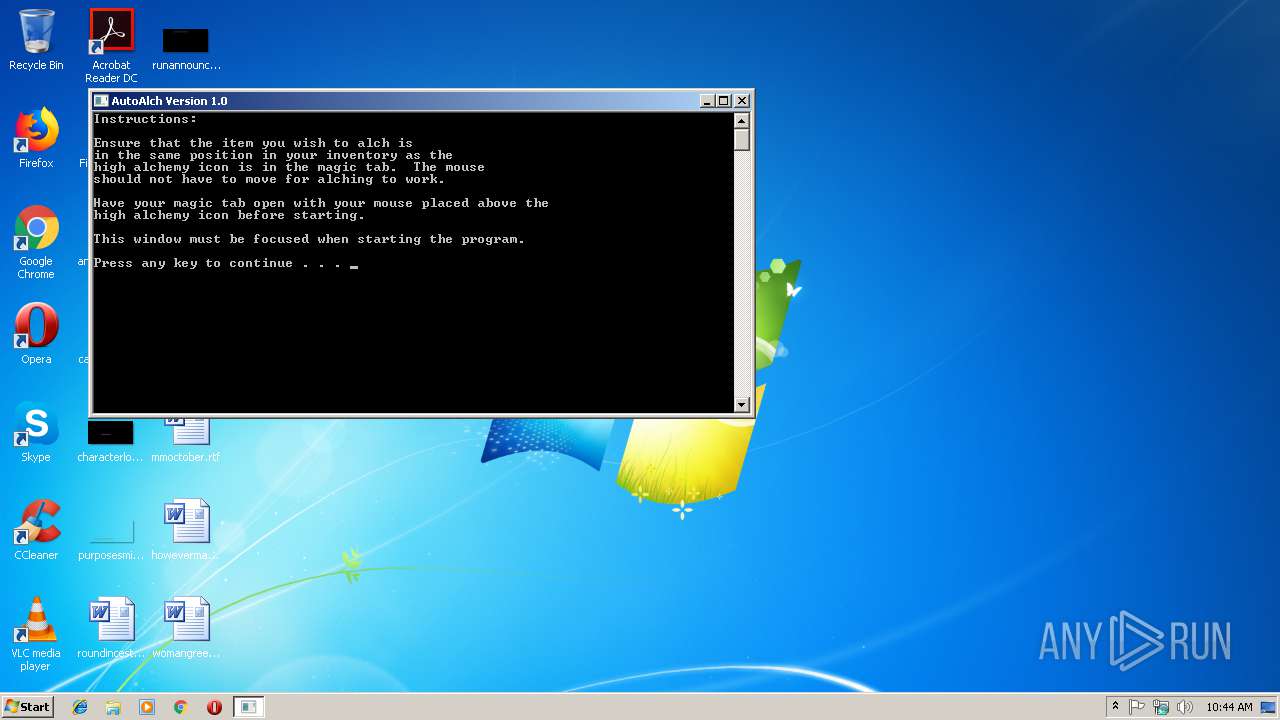
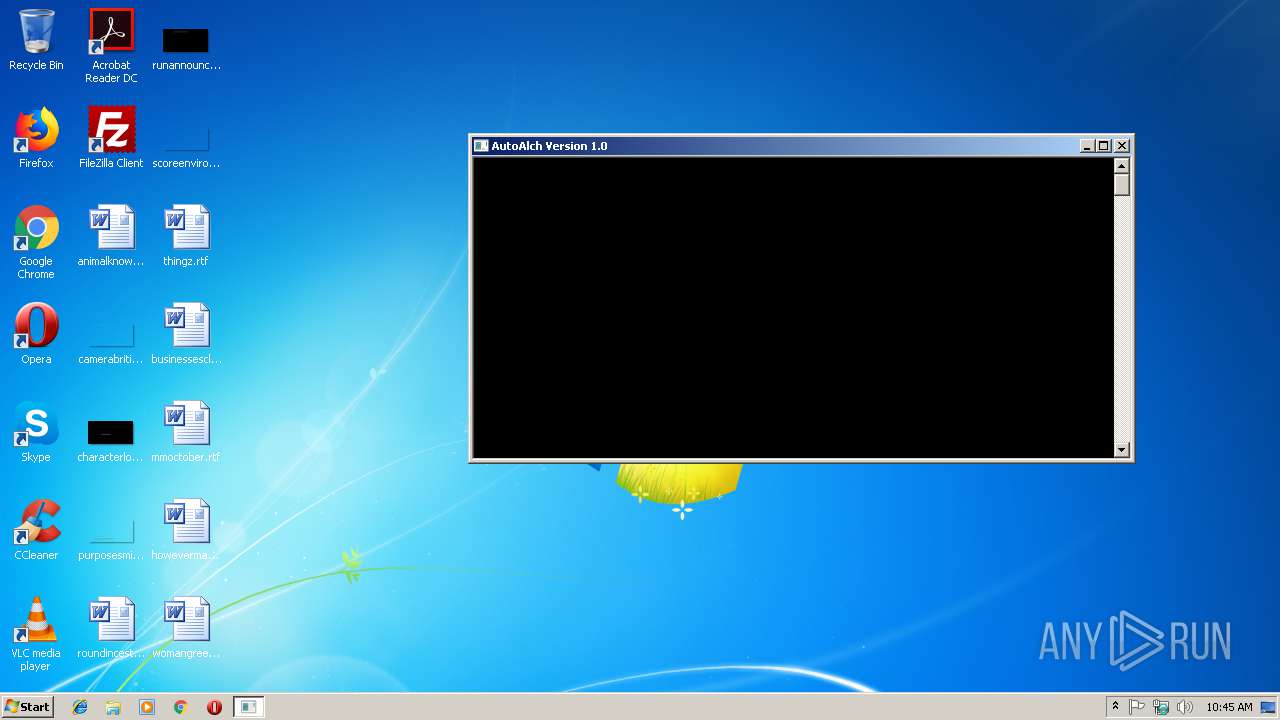
| File name: | AutoAlch_1_0.exe |
| Full analysis: | https://app.any.run/tasks/b926ca34-e80e-4f63-8d21-56d28772f37e |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2019, 10:44:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 05B577DAFC1A0DA4DDEC2388C6F805FD |
| SHA1: | 8D758DEE1DD29453C562D3321E6F3C2074EF01E1 |
| SHA256: | 1109FF7DFCD672962ECAE9BAC75B9219CBBE8666604CD806A8B15CBD4FB5DB09 |
| SSDEEP: | 12288:w9gkektKLIUjnzJHo5CMbdSqG1r5VhnkPTspTC2HMfcEiP/3IWVJ/WxgcZmX:wukektKLIU401r5Hn7P/h |
MALICIOUS
No malicious indicators.SUSPICIOUS
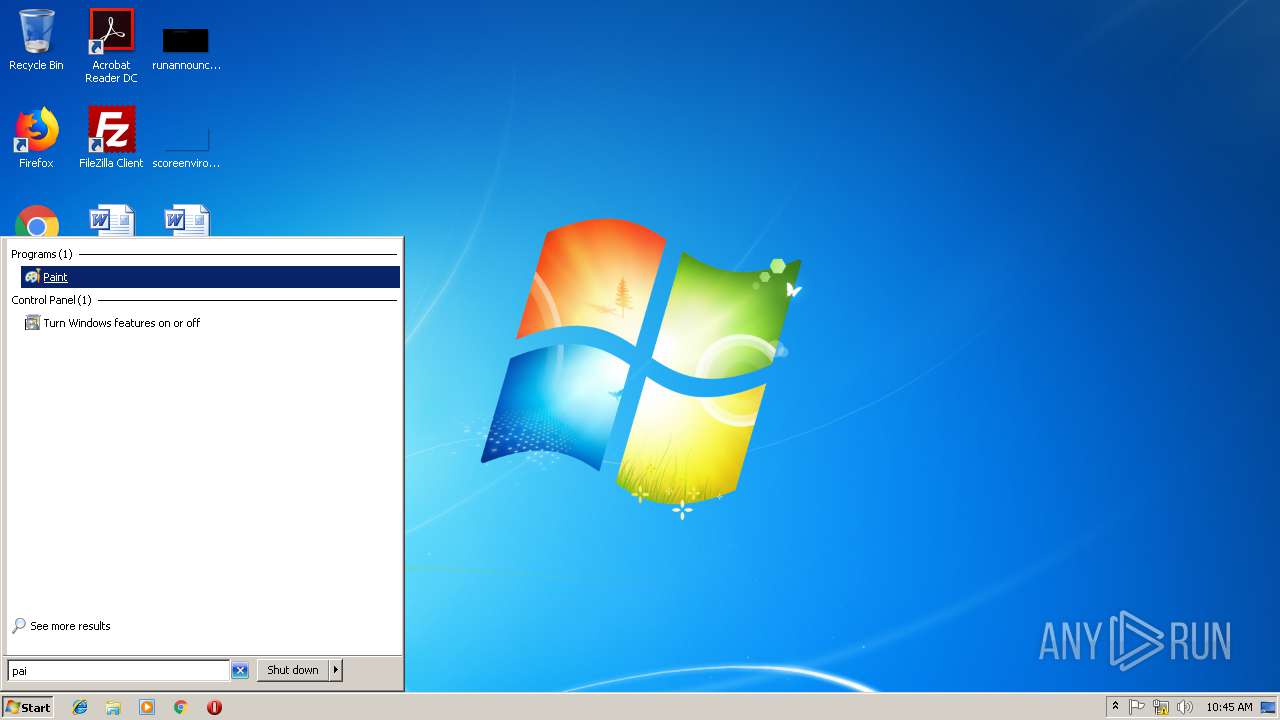
Reads Internet Cache Settings
- mspaint.exe (PID: 2940)
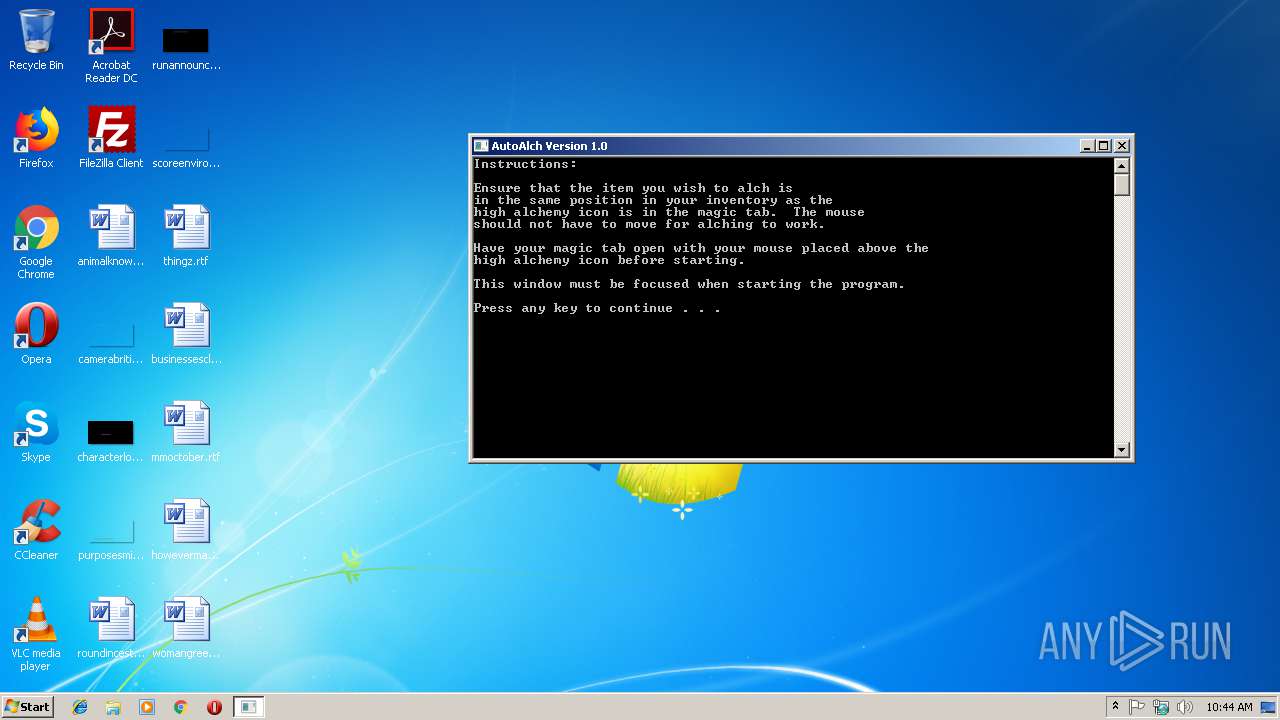
Starts CMD.EXE for commands execution
- AutoAlch_1_0.exe (PID: 3100)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:24 01:43:16+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.56 |
| CodeSize: | 253952 |
| InitializedDataSize: | 267776 |
| UninitializedDataSize: | 19456 |
| EntryPoint: | 0x1220 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 24-Feb-2018 00:43:16 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Feb-2018 00:43:16 |
| Pointer to Symbol Table: | 0x00041A00 |
| Number of symbols: | 5239 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003DFE0 | 0x0003E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.09273 |
.data | 0x0003F000 | 0x00000190 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.21956 |
.rdata | 0x00040000 | 0x000028E0 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14468 |
.bss | 0x00043000 | 0x00004BE0 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00048000 | 0x00000894 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.34736 |
Imports
KERNEL32.dll |
USER32.dll |
msvcrt.dll |
Total processes
54
Monitored processes
19
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1416 | C:\Windows\system32\cmd.exe /c CLS | C:\Windows\system32\cmd.exe | — | AutoAlch_1_0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2288 | C:\Windows\system32\cmd.exe /c CLS | C:\Windows\system32\cmd.exe | — | AutoAlch_1_0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2436 | C:\Windows\system32\cmd.exe /c CLS | C:\Windows\system32\cmd.exe | — | AutoAlch_1_0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2504 | C:\Windows\system32\cmd.exe /c CLS | C:\Windows\system32\cmd.exe | — | AutoAlch_1_0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2748 | C:\Windows\system32\cmd.exe /c CLS | C:\Windows\system32\cmd.exe | — | AutoAlch_1_0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2764 | C:\Windows\system32\cmd.exe /c CLS | C:\Windows\system32\cmd.exe | — | AutoAlch_1_0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2772 | C:\Windows\system32\cmd.exe /c CLS | C:\Windows\system32\cmd.exe | — | AutoAlch_1_0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
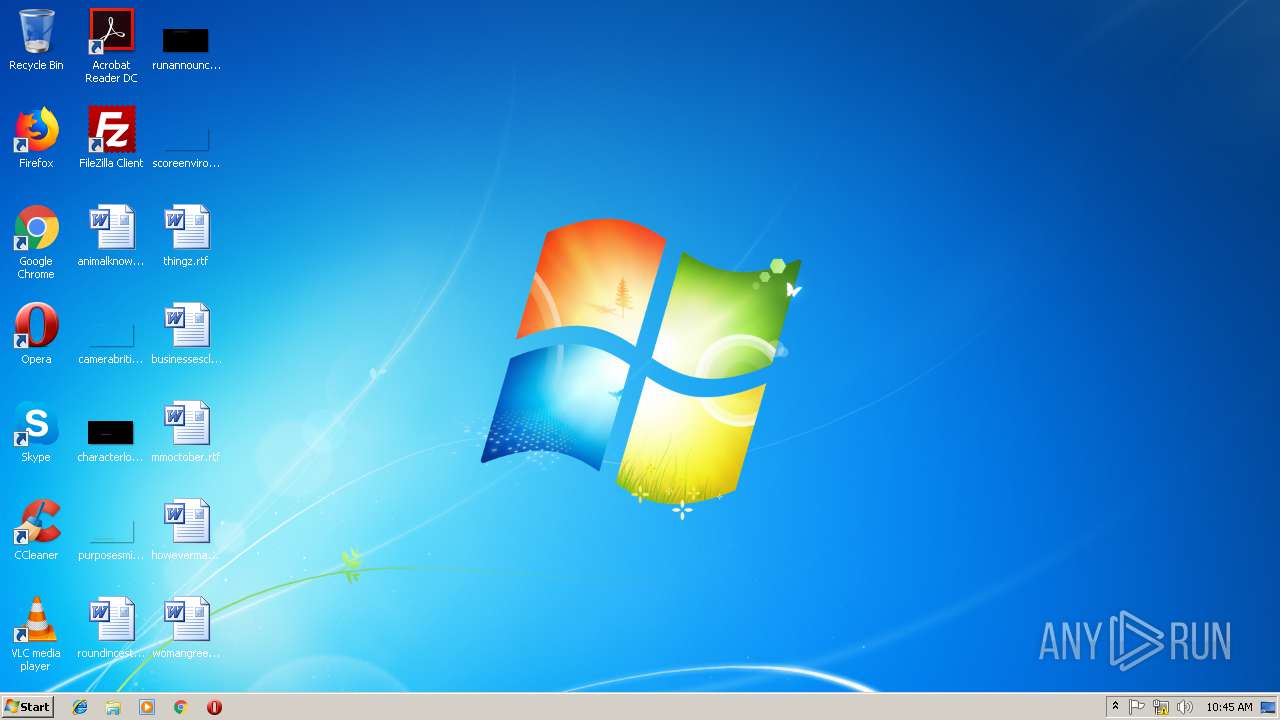
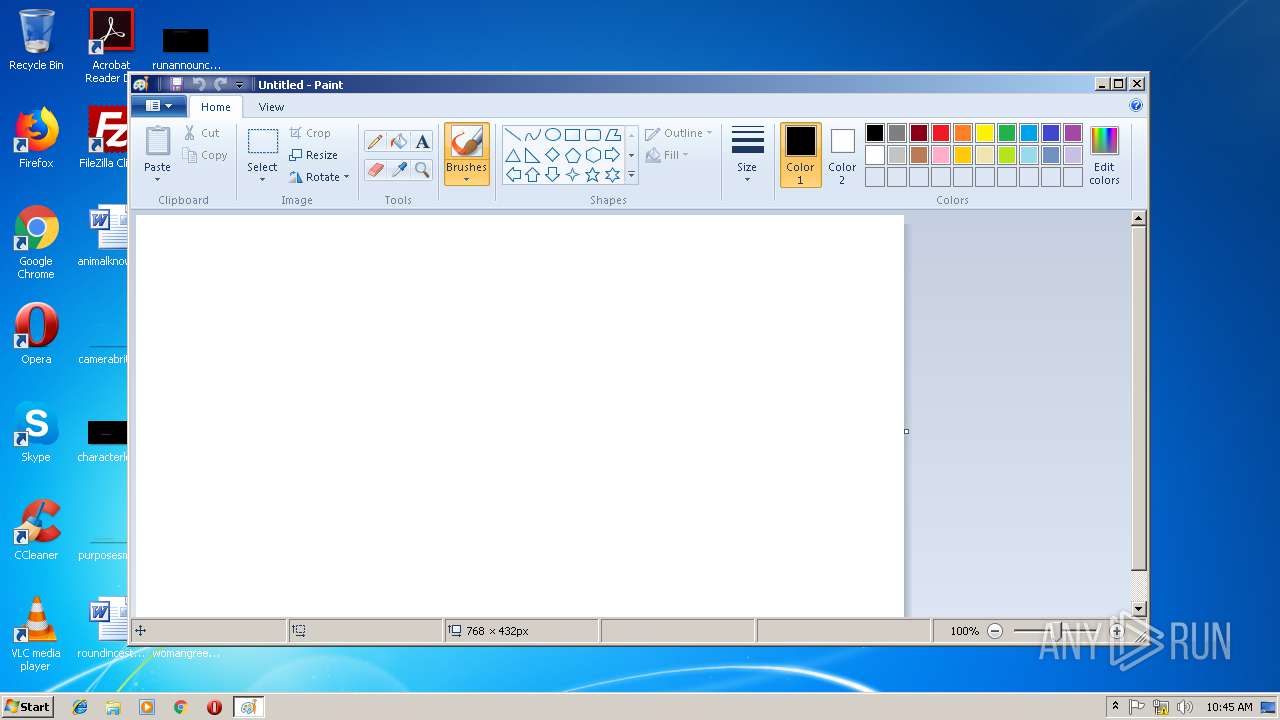
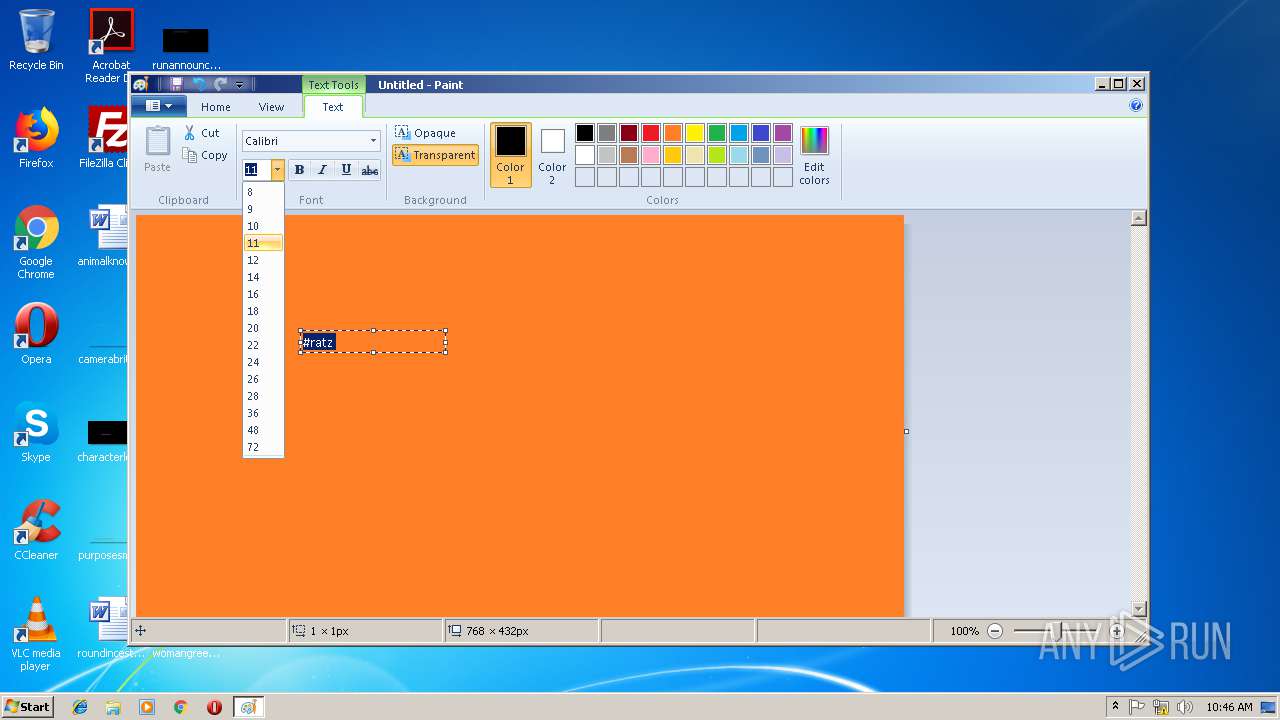
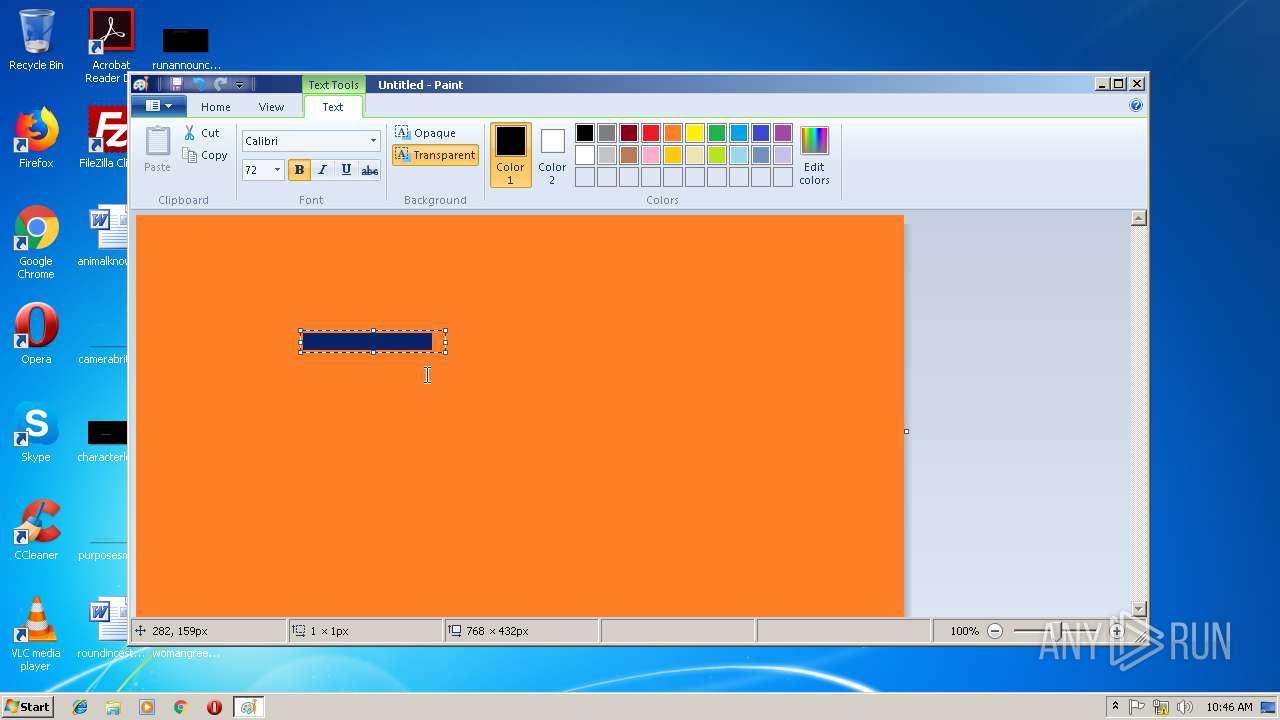
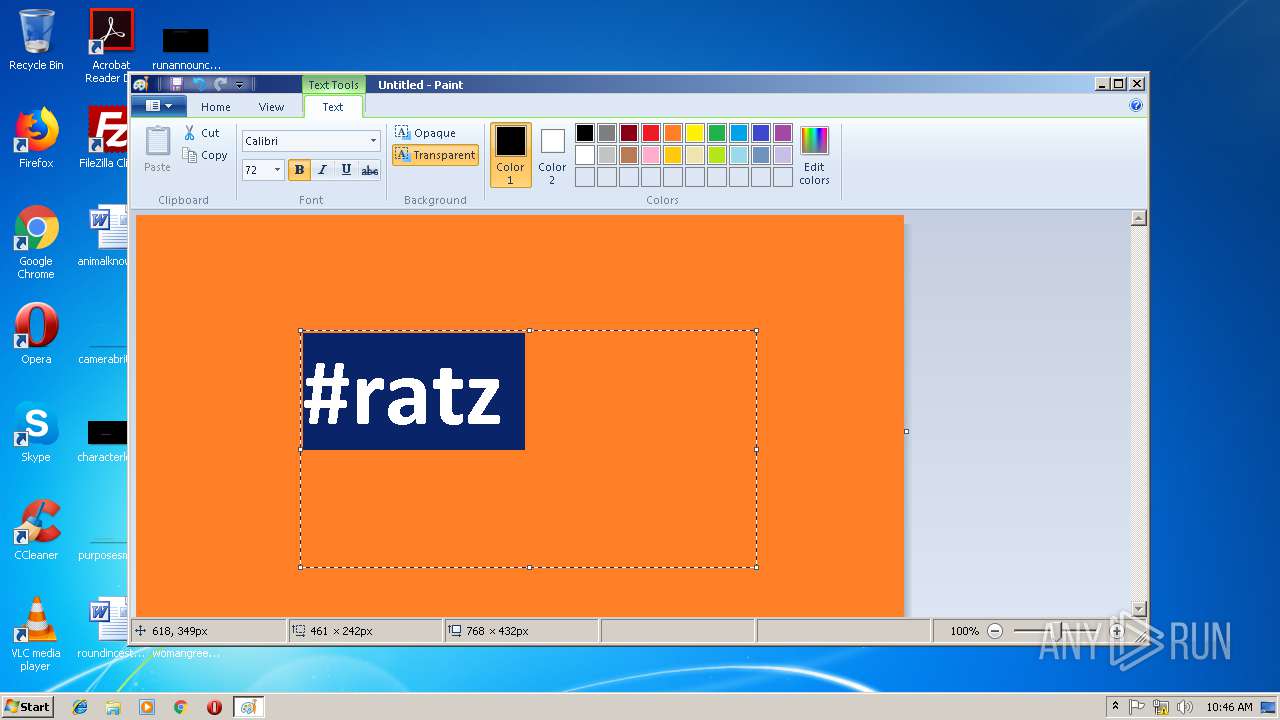
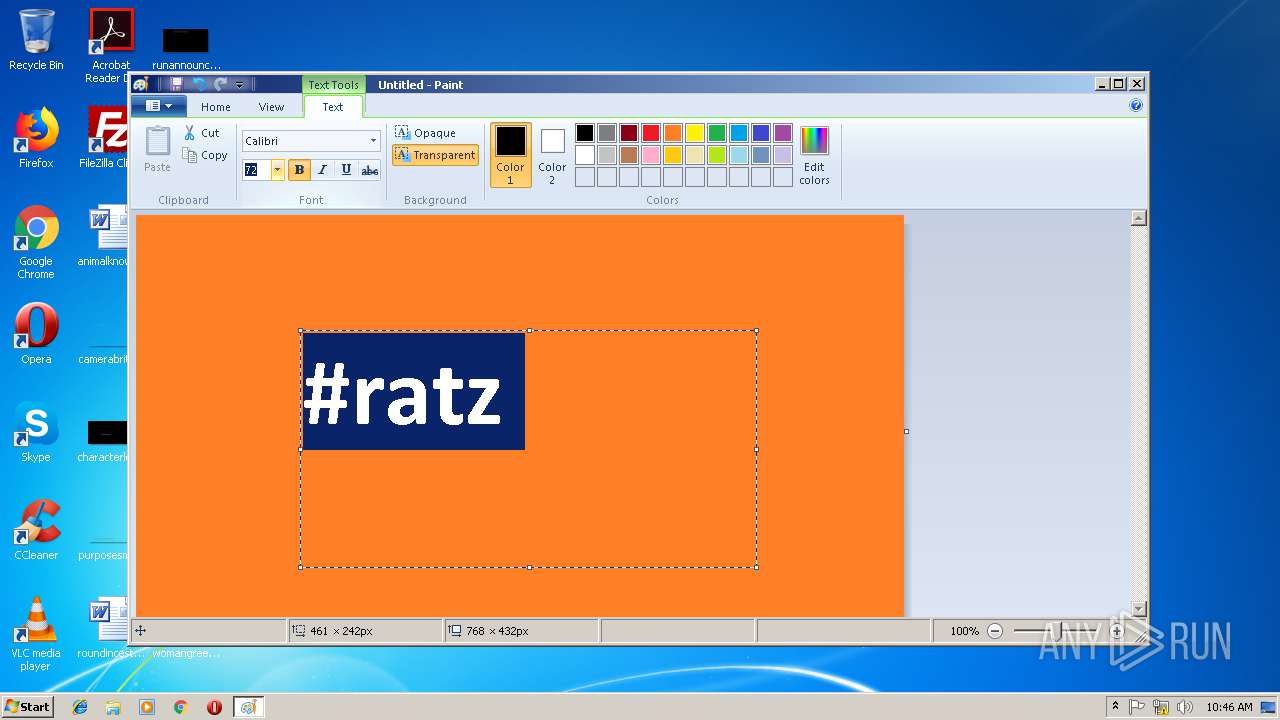
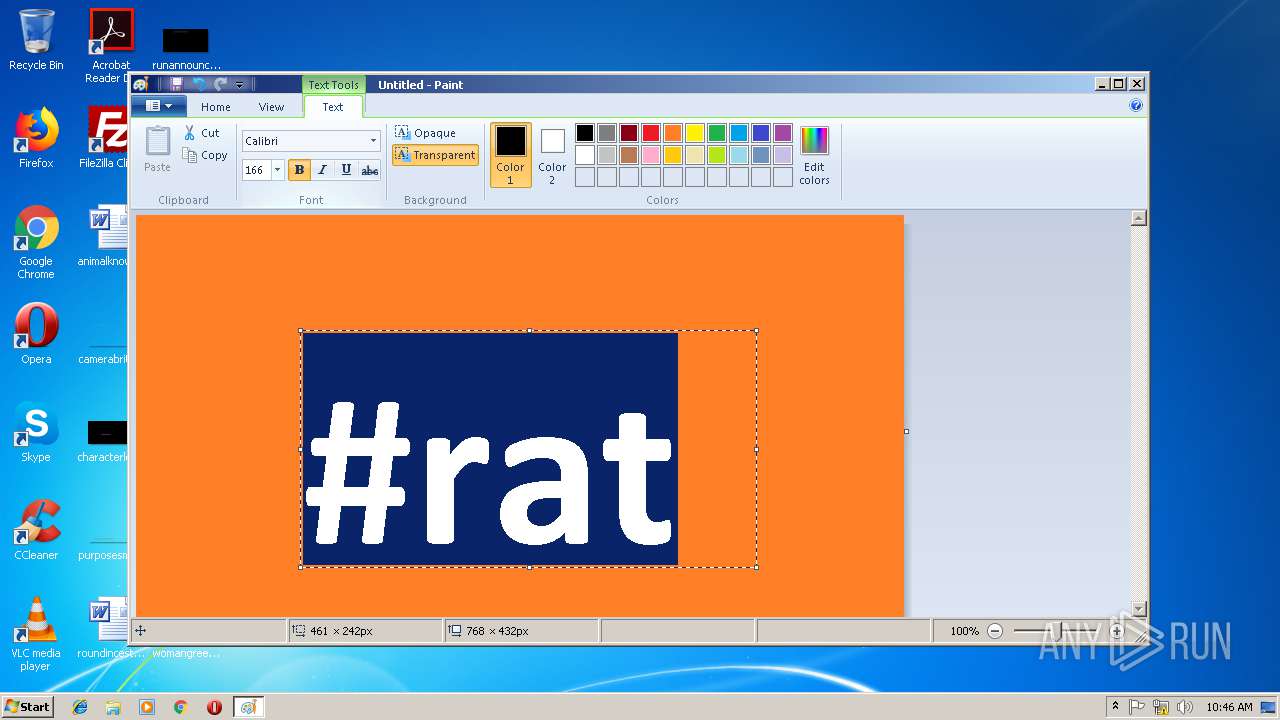
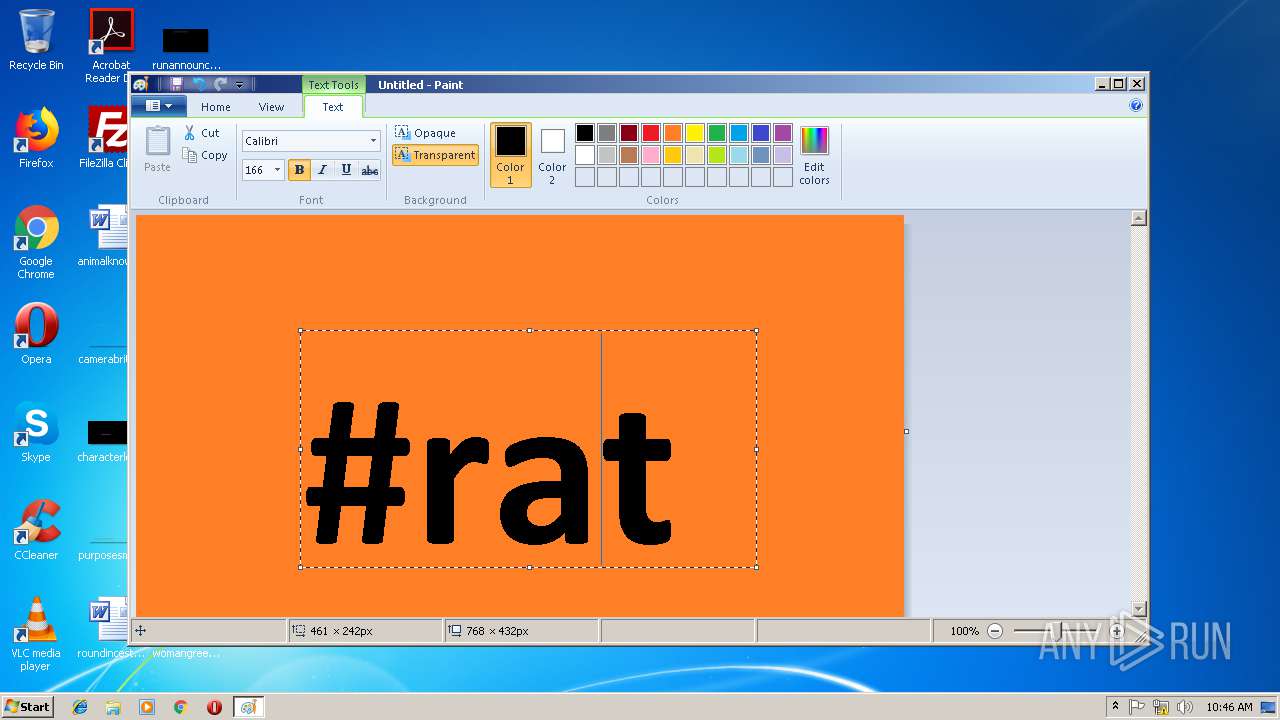
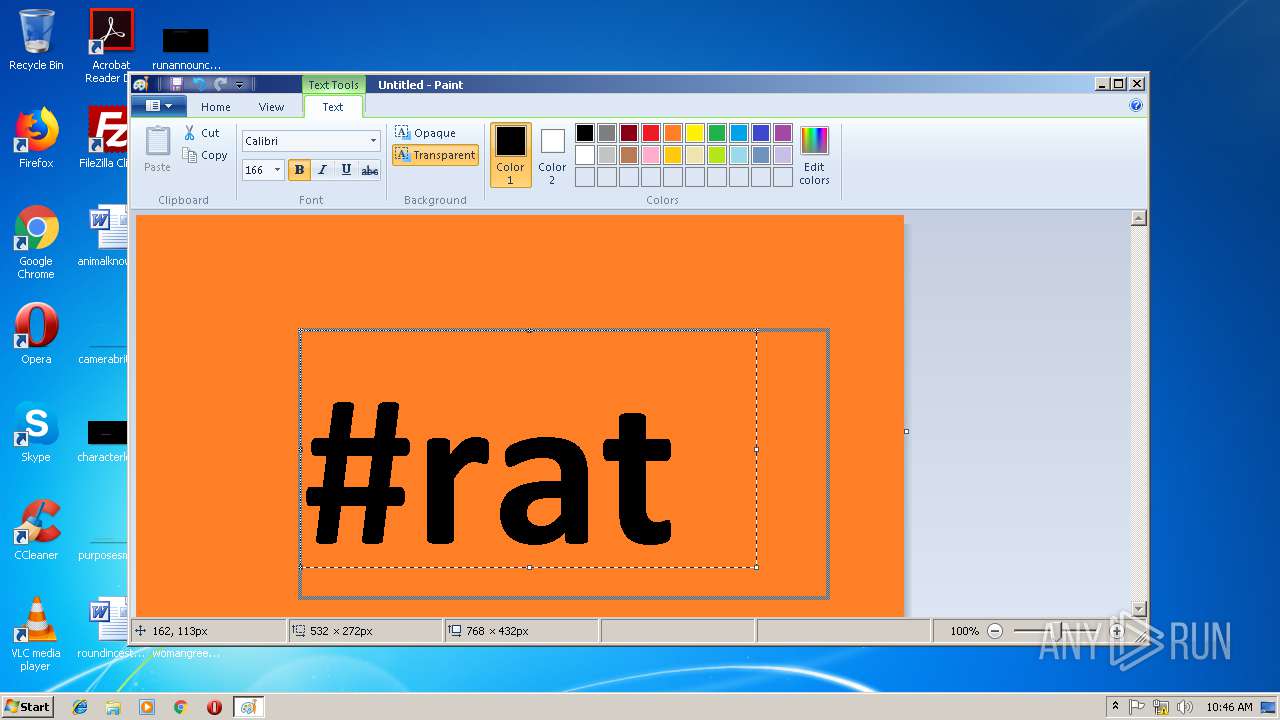
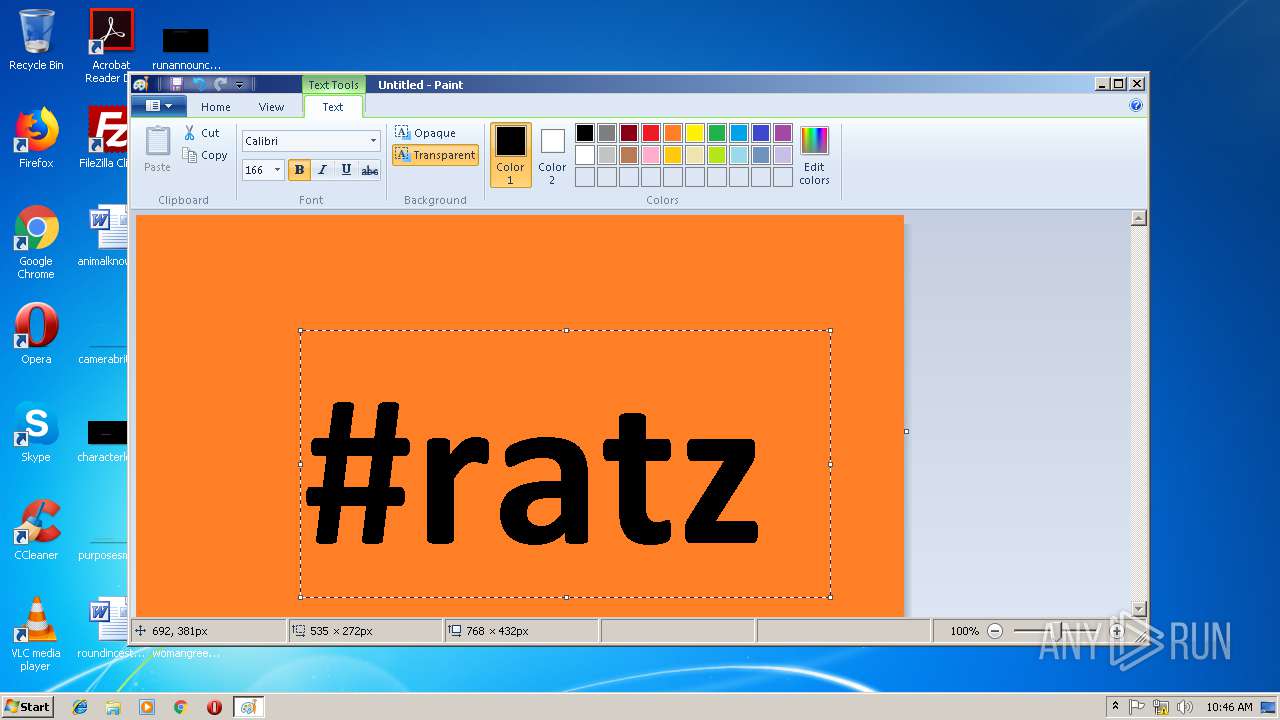
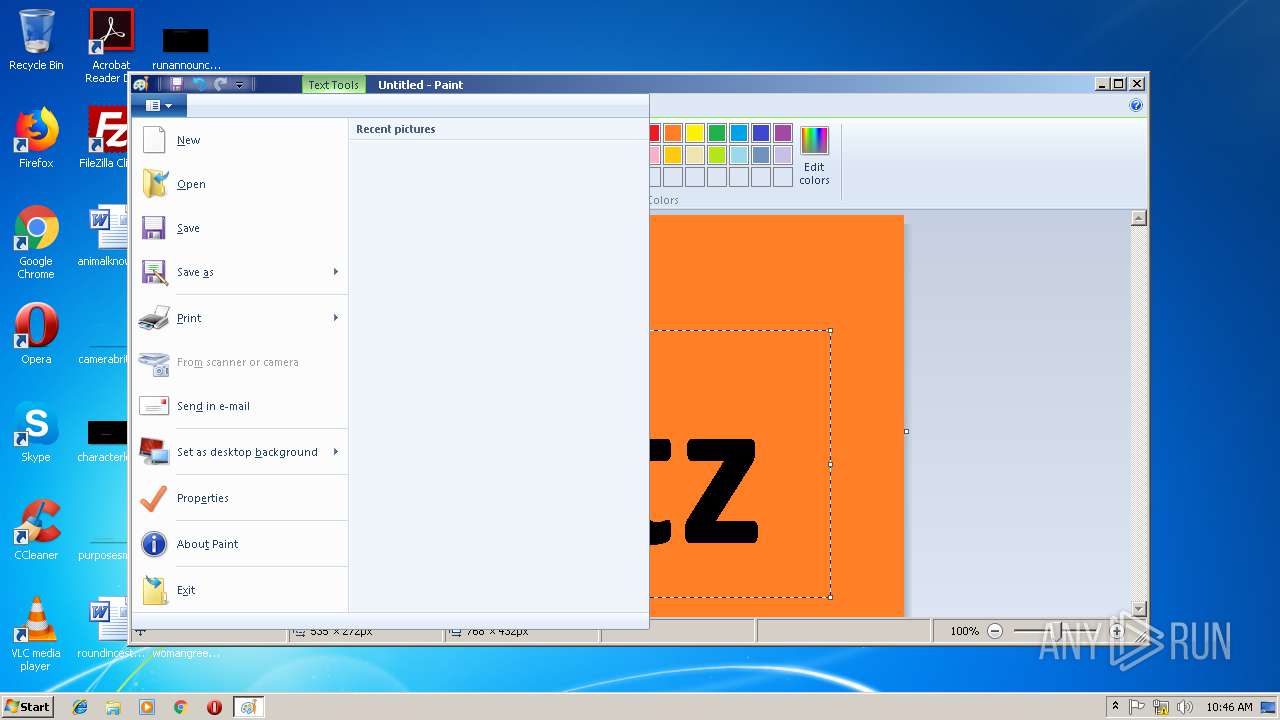
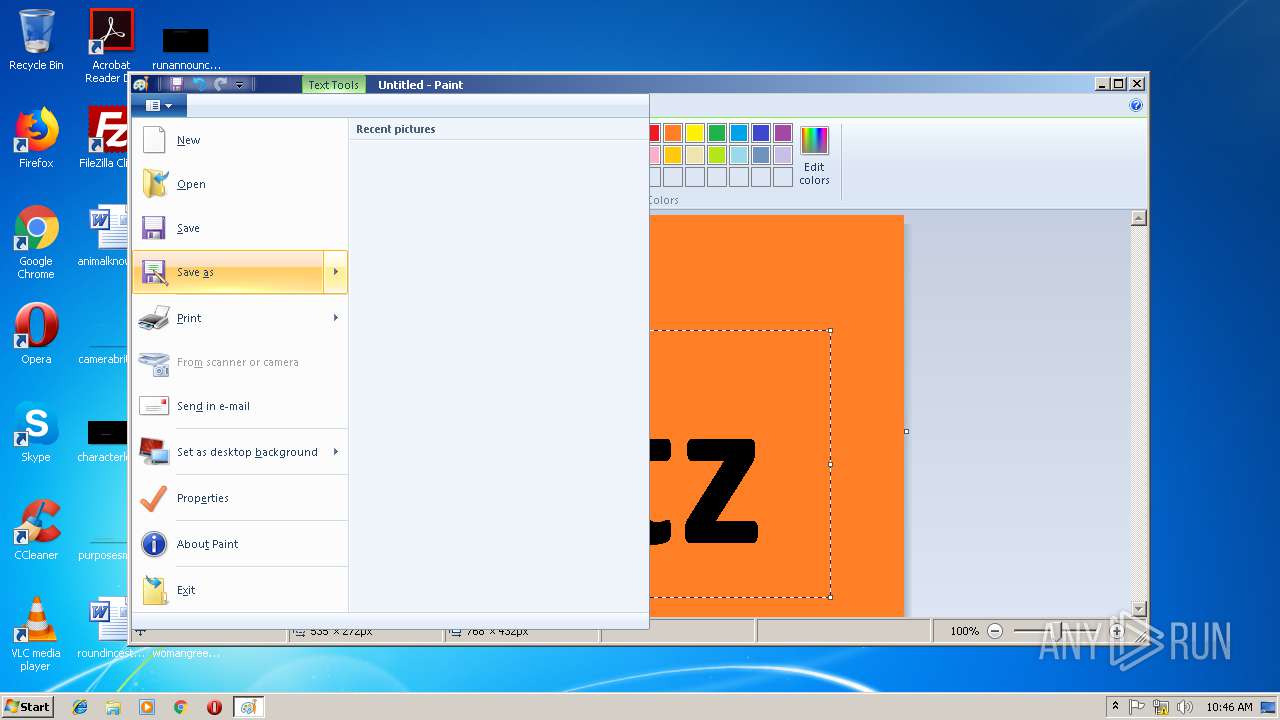
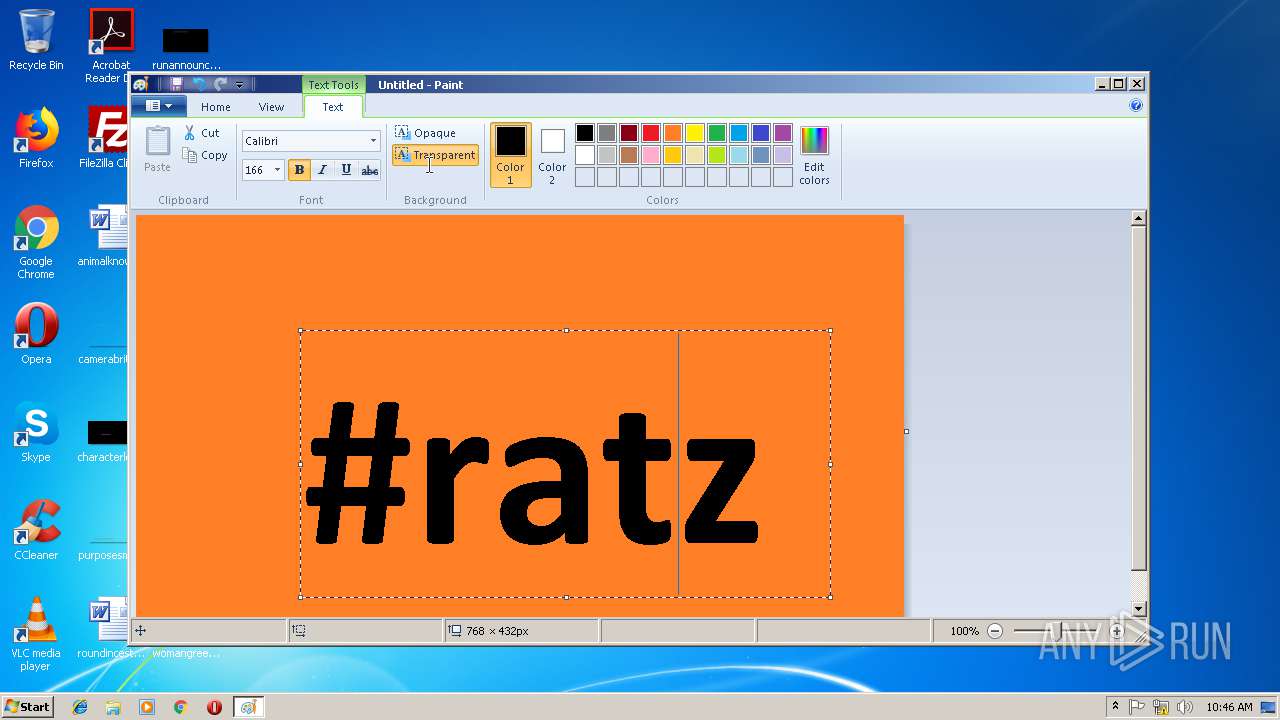
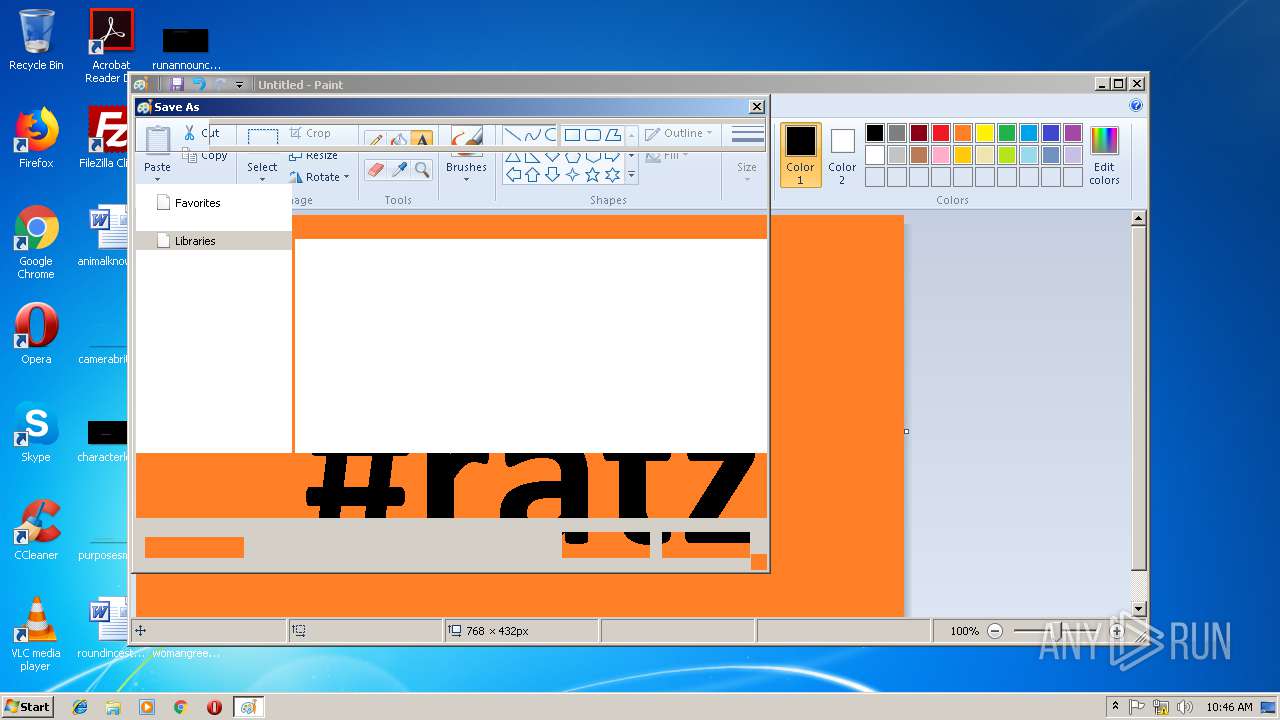
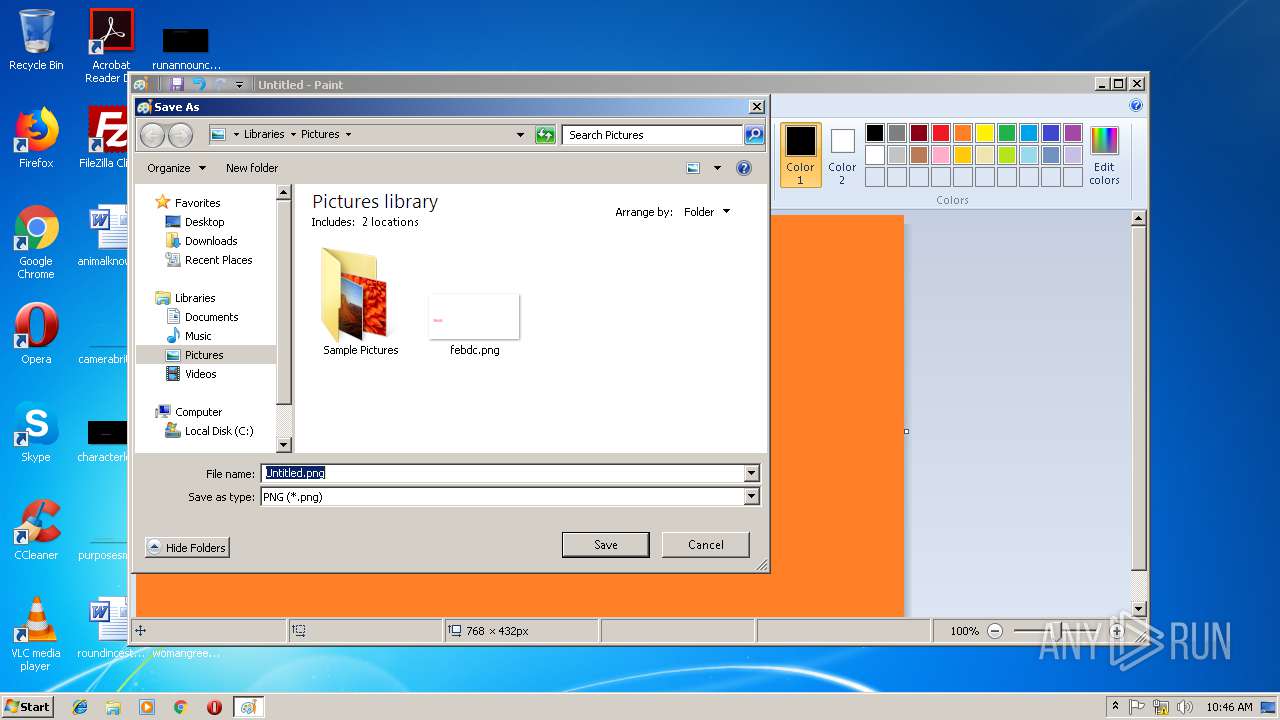
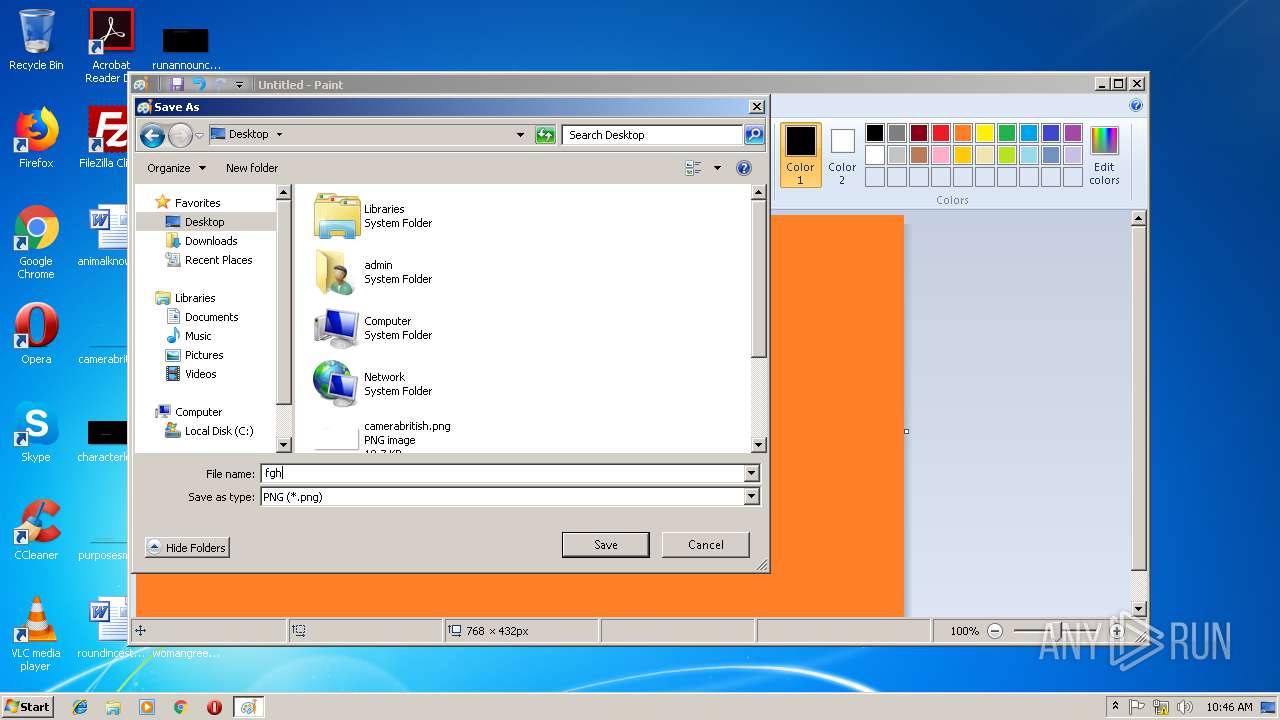
| 2940 | "C:\Windows\system32\mspaint.exe" | C:\Windows\system32\mspaint.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3100 | "C:\Users\admin\AppData\Local\Temp\AutoAlch_1_0.exe" | C:\Users\admin\AppData\Local\Temp\AutoAlch_1_0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 3164 | C:\Windows\system32\cmd.exe /c CLS | C:\Windows\system32\cmd.exe | — | AutoAlch_1_0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
771
Read events
657
Write events
111
Delete events
3
Modification events
| (PID) Process: | (2940) mspaint.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Font Management\Auto Activation Languages |
| Operation: | write | Name: | en-Latn-US |
Value: 1033 | |||
| (PID) Process: | (2940) mspaint.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Font Management |
| Operation: | write | Name: | Inactive Fonts |
Value: Large Fonts | |||
| (PID) Process: | (2940) mspaint.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Font Management |
| Operation: | write | Name: | Active Languages |
Value: 09040000 | |||
| (PID) Process: | (2940) mspaint.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00570069006E0064006F00770073005C00730079007300740065006D00330032005C006D0073007000610069006E0074002E00650078006500000043003A005C00550073006500720073005C00610064006D0069006E005C00500069006300740075007200650073000000 | |||
| (PID) Process: | (2940) mspaint.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (2940) mspaint.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2940) mspaint.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000000000000010000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2940) mspaint.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\2 |
| Operation: | write | Name: | 1 |
Value: 9E0000001A00EEBBFE23000010009FAE90A93BA0804E94BC9912D750410400002A0000000000EFBE000000200000000000000000000000000000000000000000000000000100000020002A0000000000EFBEEBAA2B0B4200CA4DAA4D3EE8648D03E58207BA827A5B6945B5D7EC83085F08CC20002A0000000000EFBE000000200000000000000000000000000000000000000000000000000100000020000000 | |||
| (PID) Process: | (2940) mspaint.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\2 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
| (PID) Process: | (2940) mspaint.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
Executable files
0
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | mspaint.exe | C:\Users\admin\AppData\Local\Temp\fghjfghj.png | — | |
MD5:— | SHA256:— | |||
| 2940 | mspaint.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\thumbcache_idx.db | binary | |
MD5:— | SHA256:— | |||
| 2940 | mspaint.exe | C:\Users\admin\Desktop\fghjfghj.png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report