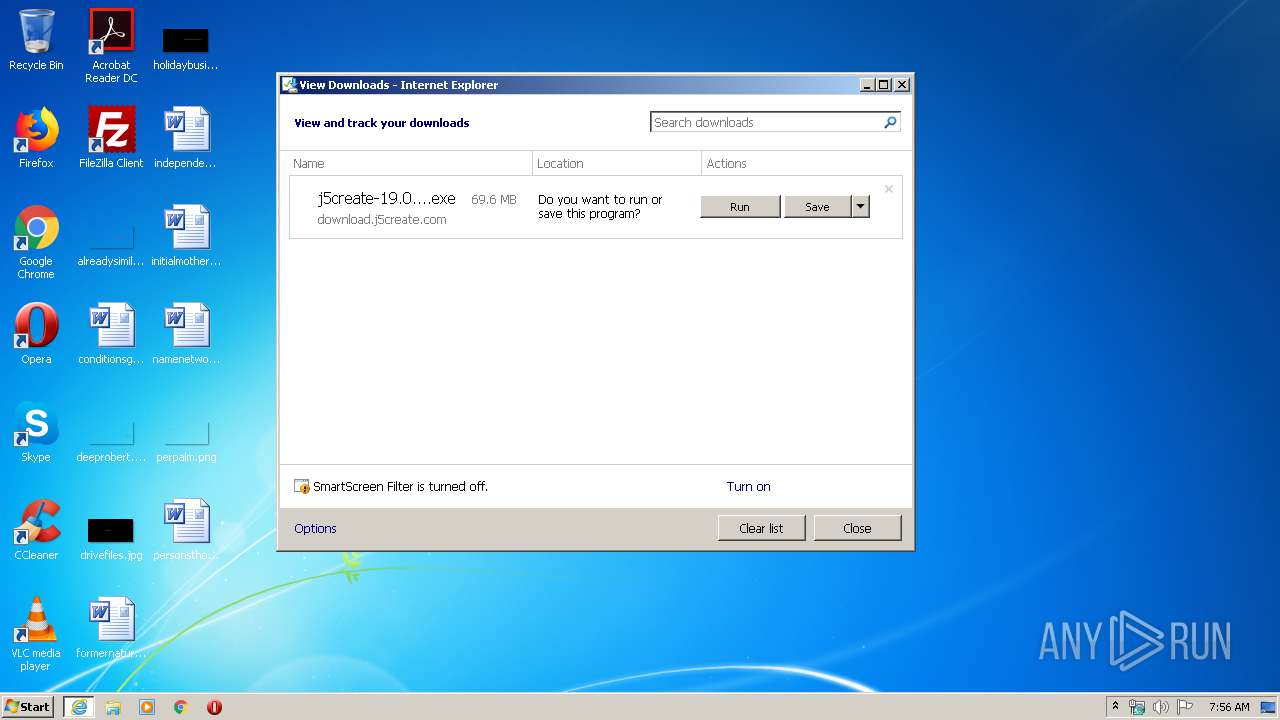
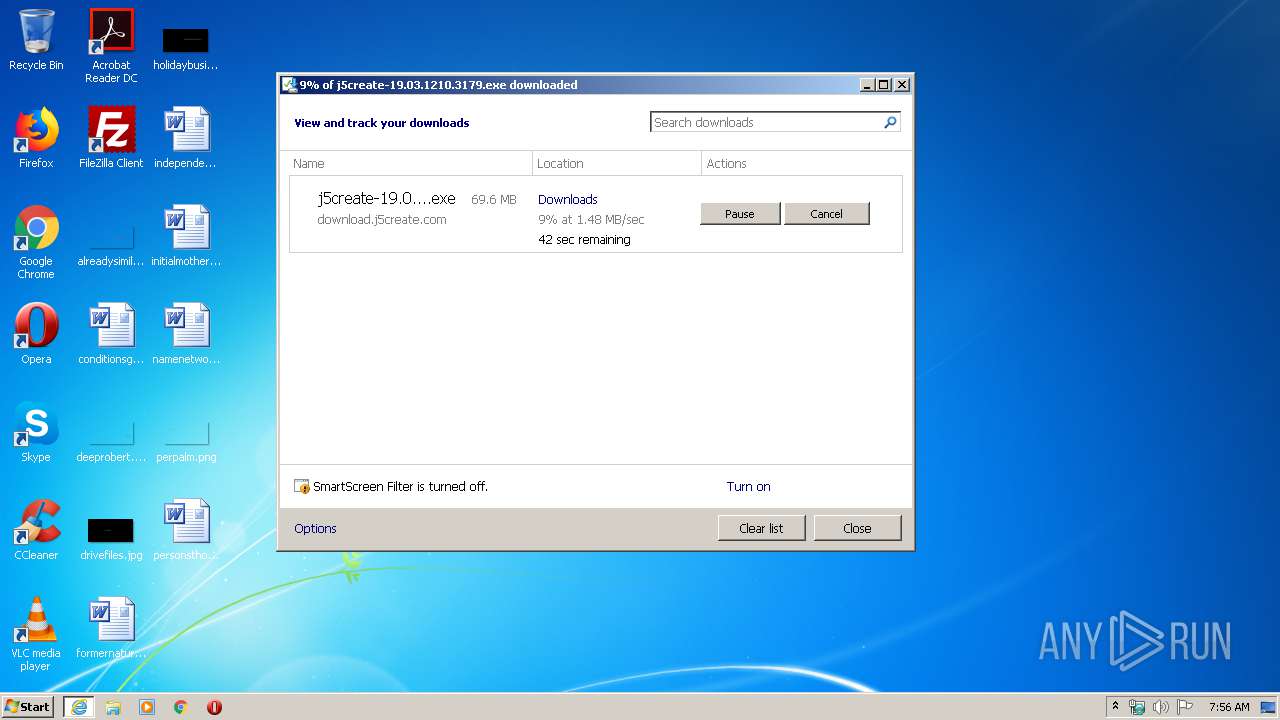
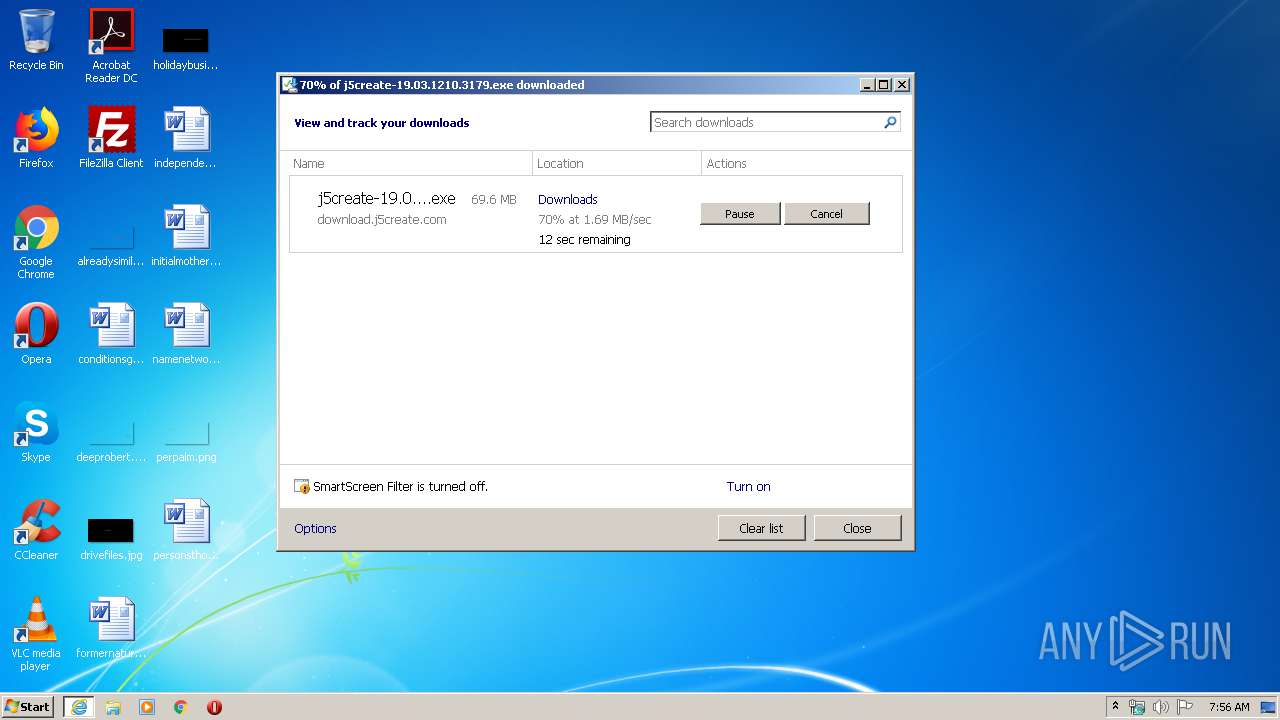
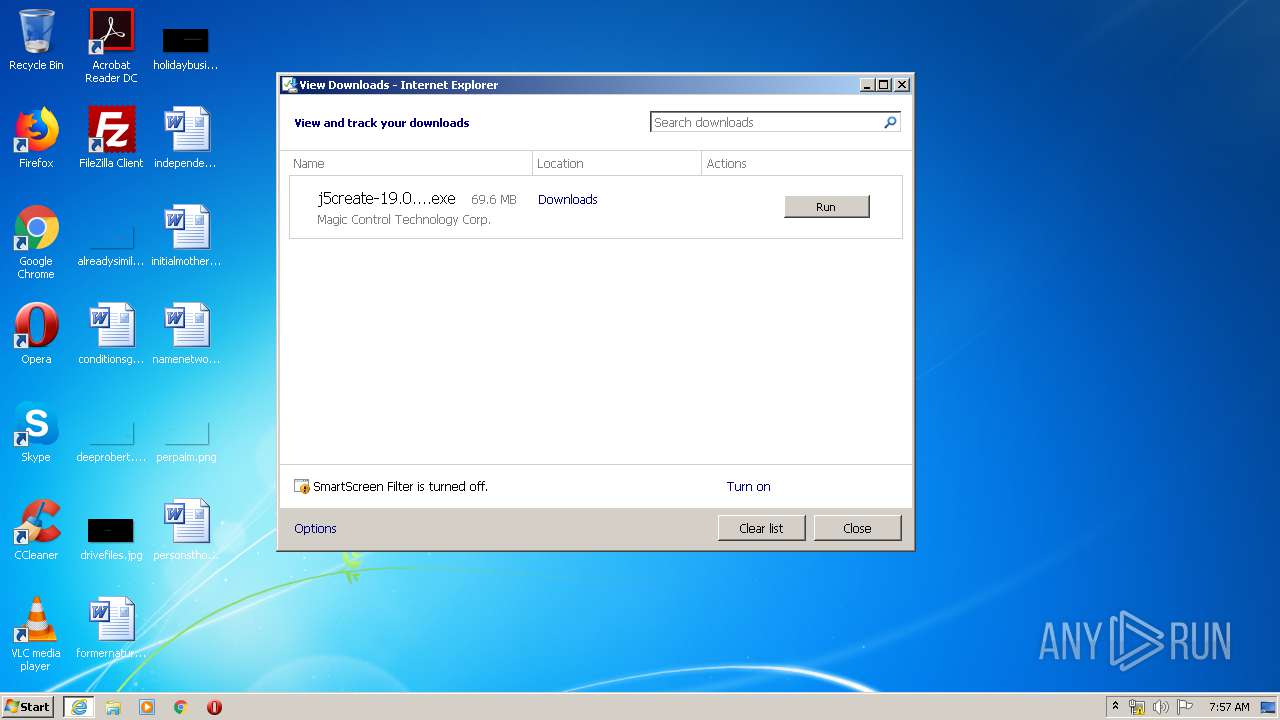
| URL: | http://download.j5create.com/driver/USB_Display_Adapters_Windows_Driver/j5create-19.03.1210.3179.exe |
| Full analysis: | https://app.any.run/tasks/0ebce725-81e8-4b17-9953-6195a4184ad2 |
| Verdict: | Malicious activity |
| Analysis date: | February 28, 2020, 07:55:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CAA049B529F321D8247FCD5DC1DE948A |
| SHA1: | EE4D6065B3F84D7A45F0726904EE140757AD4883 |
| SHA256: | 11010CA79DA49D752969D25FC740C40E7B82FA080624DD65AB7AA9FB13BC7B2D |
| SSDEEP: | 3:N1KaKElbXhmzXenGR6n6P4NPTXgppnV3SrCn:Ca5bXhmc066P4NPbgppnVirC |
MALICIOUS
Loads dropped or rewritten executable
- j5create-19.03.1210.3179.exe (PID: 3708)
- TUCCD.exe (PID: 1948)
Application was dropped or rewritten from another process
- GManager.exe (PID: 3036)
- GManager.exe (PID: 3384)
- GManager.exe (PID: 1932)
- CertMgr.exe (PID: 2988)
- mlpatch.exe (PID: 3824)
- devcon32.exe (PID: 1676)
- TUCCD.exe (PID: 1948)
- MlPatch.exe (PID: 620)
- mlpatch.exe (PID: 3188)
Changes settings of System certificates
- CertMgr.exe (PID: 2988)
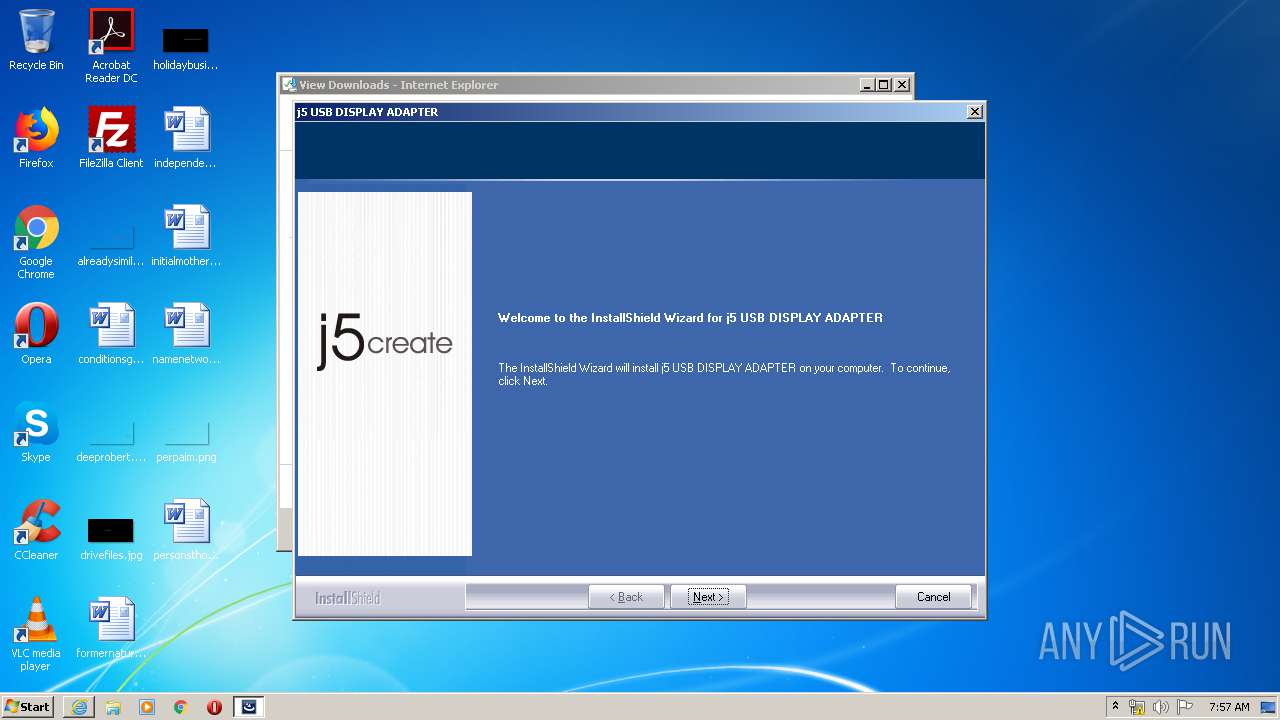
Changes the autorun value in the registry
- j5create-19.03.1210.3179.exe (PID: 3708)
SUSPICIOUS
Reads Environment values
- j5create-19.03.1210.3179.exe (PID: 3708)
Reads the Windows organization settings
- j5create-19.03.1210.3179.exe (PID: 3708)
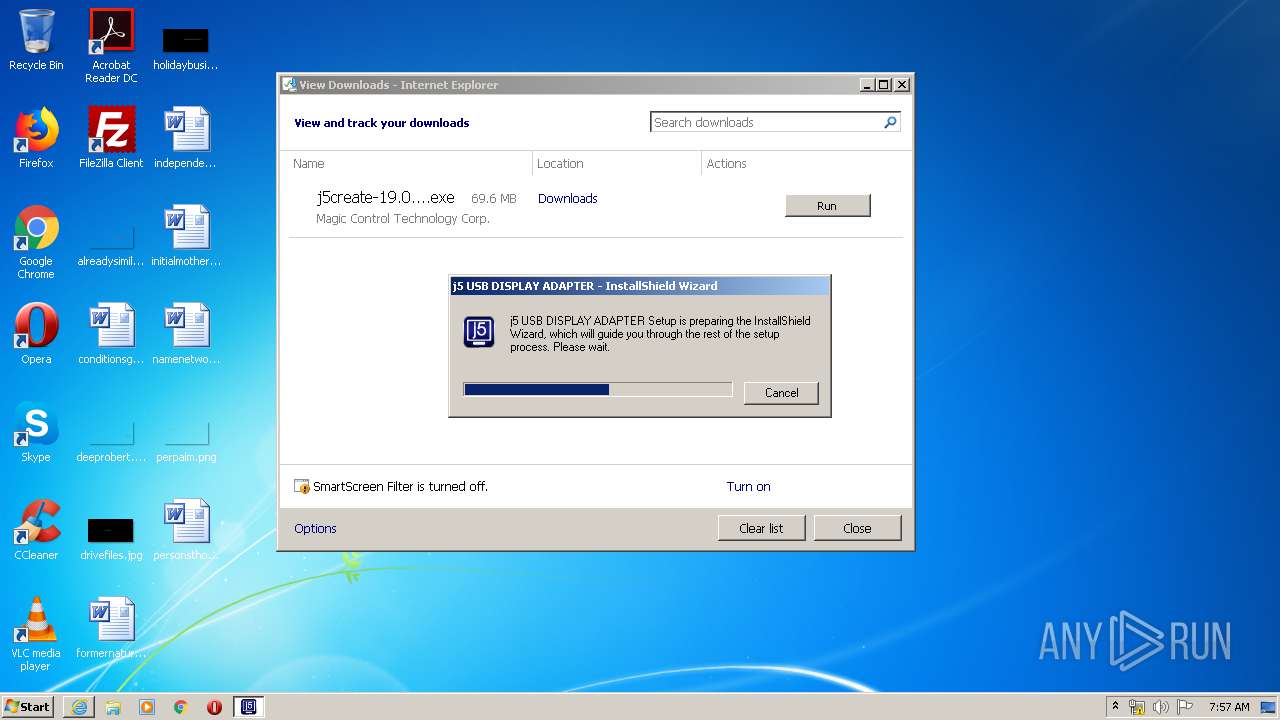
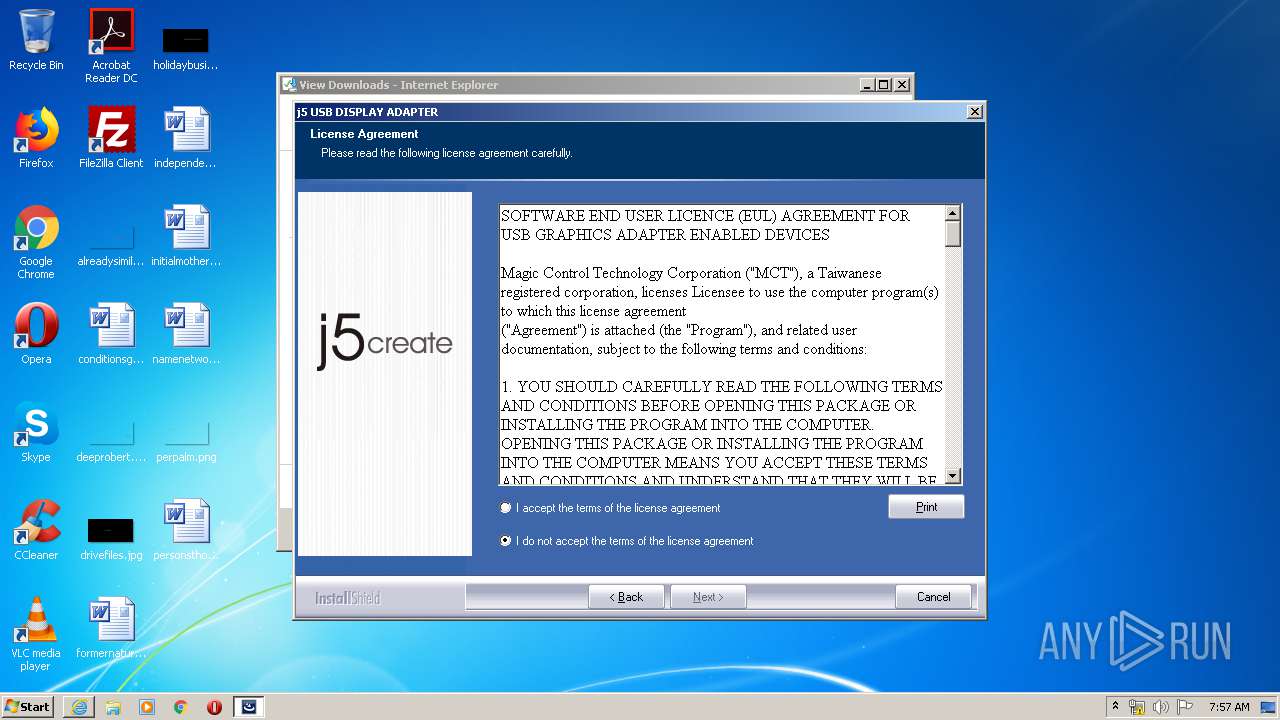
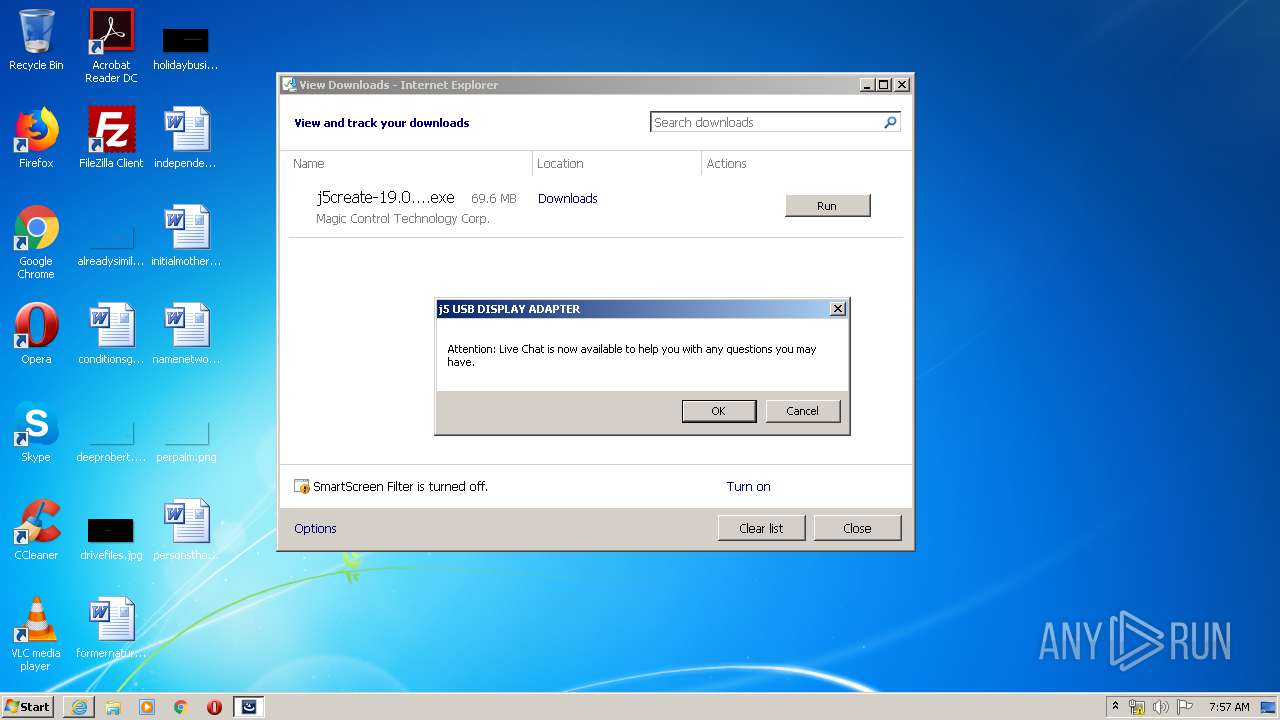
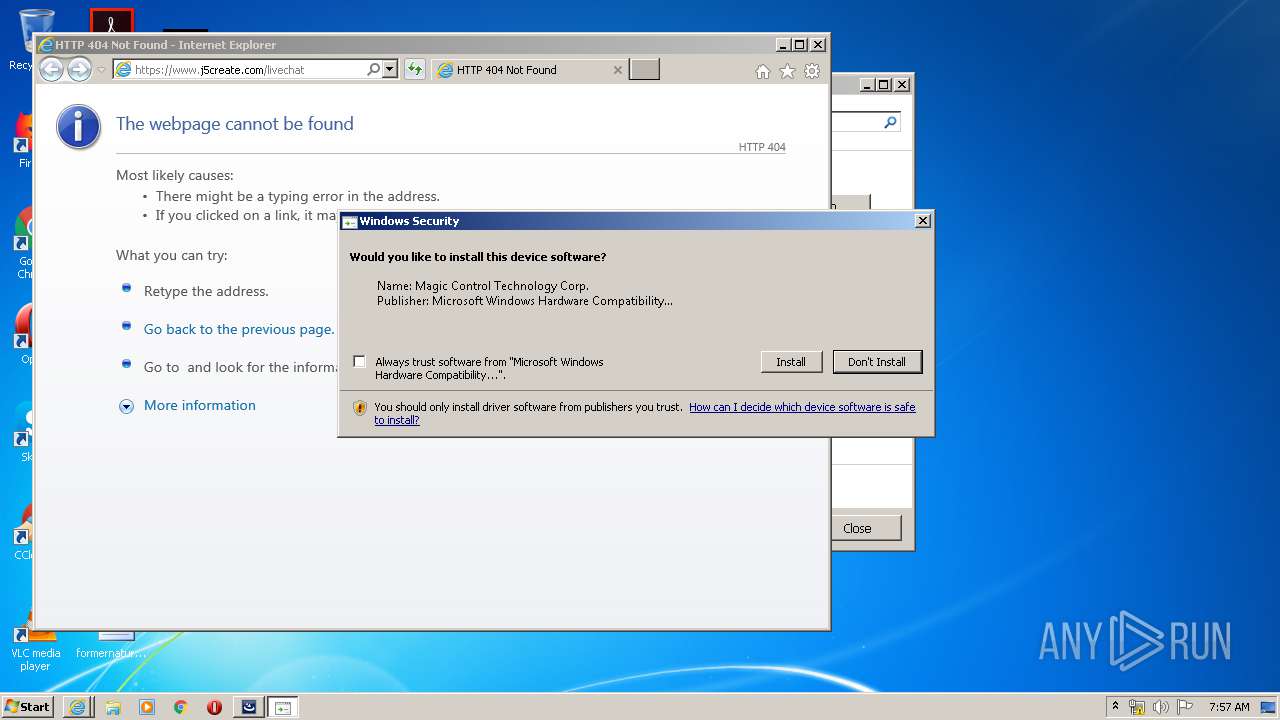
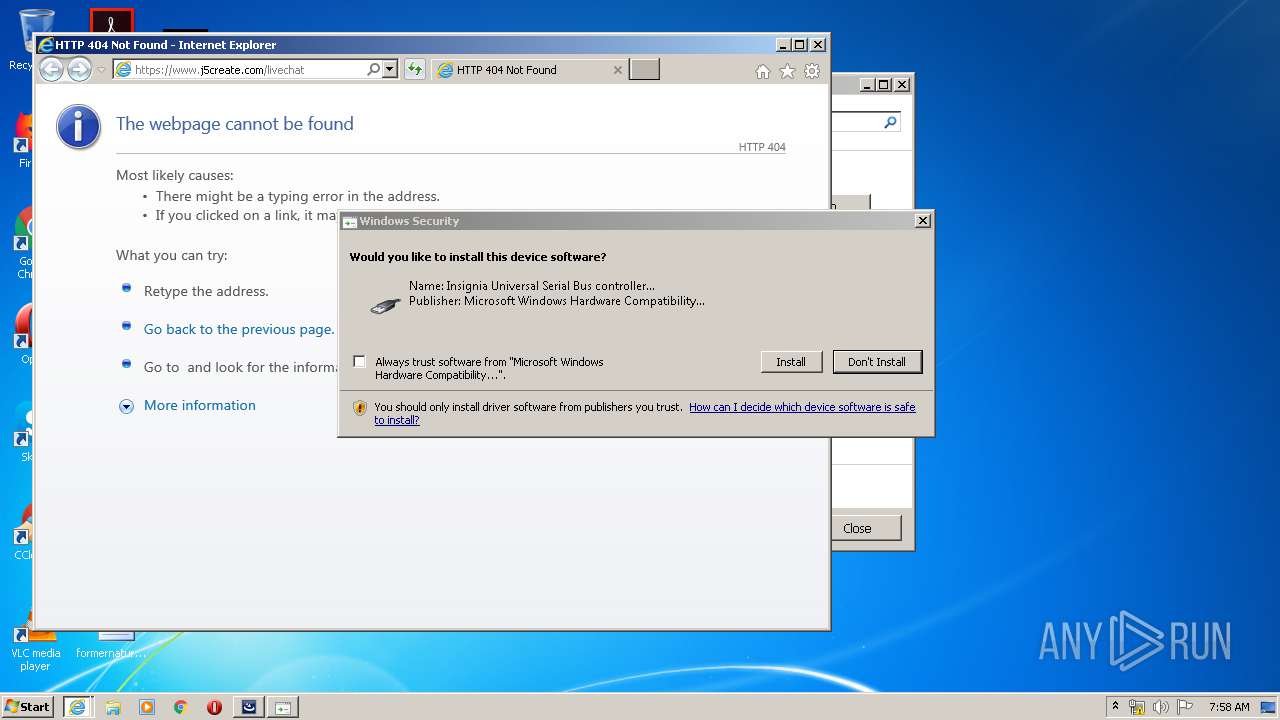
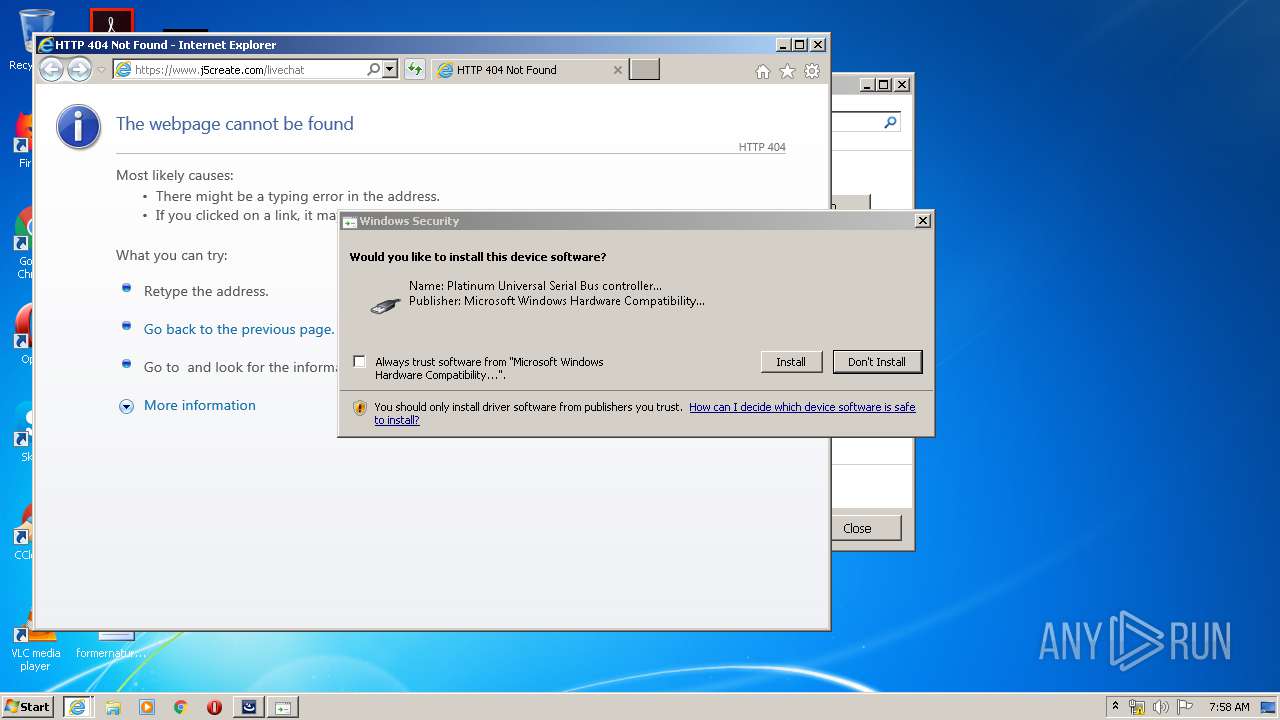
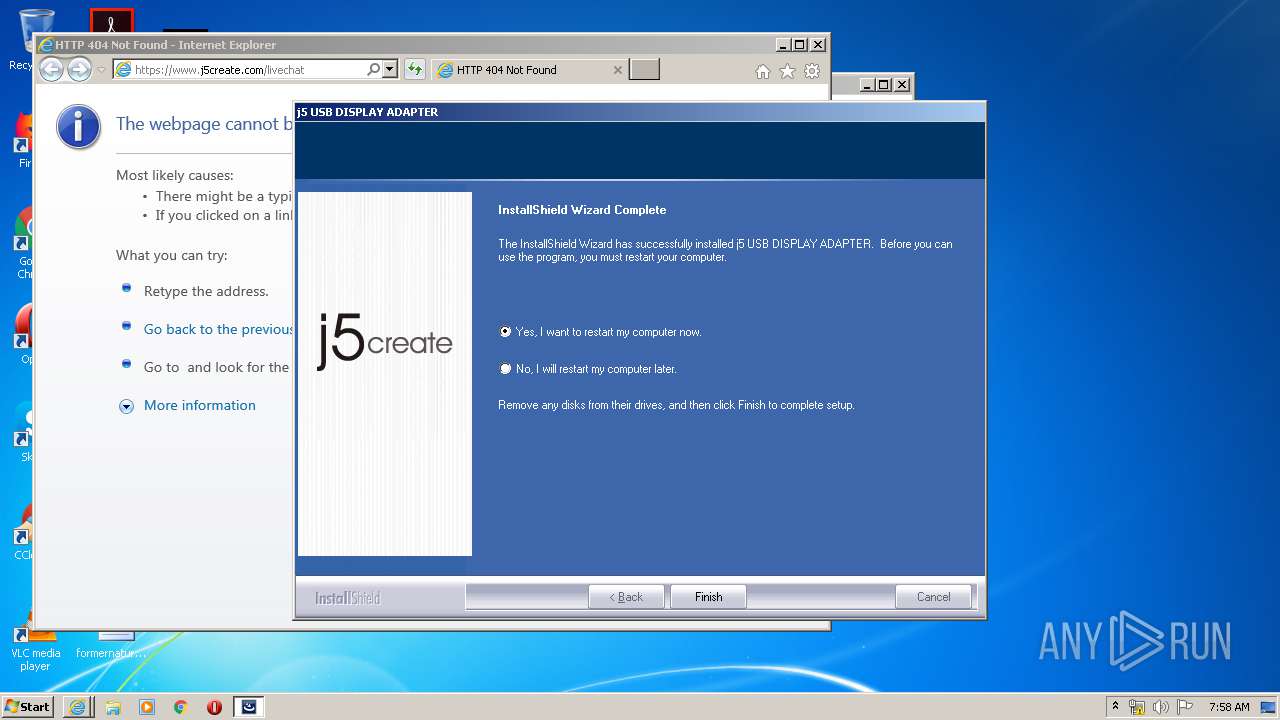
Starts Internet Explorer
- j5create-19.03.1210.3179.exe (PID: 3708)
Reads Windows owner or organization settings
- j5create-19.03.1210.3179.exe (PID: 3708)
Creates or modifies windows services
- j5create-19.03.1210.3179.exe (PID: 3708)
Executed as Windows Service
- vssvc.exe (PID: 2576)
- GManager.exe (PID: 1932)
- MlPatch.exe (PID: 620)
Uses TASKKILL.EXE to kill process
- j5create-19.03.1210.3179.exe (PID: 3708)
Starts CMD.EXE for commands execution
- j5create-19.03.1210.3179.exe (PID: 3708)
Creates files in the Windows directory
- j5create-19.03.1210.3179.exe (PID: 3708)
- GManager.exe (PID: 3036)
- DrvInst.exe (PID: 2352)
- DrvInst.exe (PID: 2344)
- DrvInst.exe (PID: 2800)
- DrvInst.exe (PID: 1024)
Removes files from Windows directory
- j5create-19.03.1210.3179.exe (PID: 3708)
- DrvInst.exe (PID: 2352)
- DrvInst.exe (PID: 2344)
- DrvInst.exe (PID: 2800)
- DrvInst.exe (PID: 1024)
Creates files in the driver directory
- j5create-19.03.1210.3179.exe (PID: 3708)
- DrvInst.exe (PID: 2352)
- DrvInst.exe (PID: 2800)
- DrvInst.exe (PID: 2344)
- DrvInst.exe (PID: 1024)
Creates a software uninstall entry
- j5create-19.03.1210.3179.exe (PID: 3708)
Starts SC.EXE for service management
- j5create-19.03.1210.3179.exe (PID: 3708)
Creates files in the program directory
- j5create-19.03.1210.3179.exe (PID: 3708)
Executed via COM
- DrvInst.exe (PID: 2352)
- DrvInst.exe (PID: 2800)
- DrvInst.exe (PID: 2344)
- DrvInst.exe (PID: 1024)
Executable content was dropped or overwritten
- DrvInst.exe (PID: 2352)
- j5create-19.03.1210.3179.exe (PID: 3708)
- DrvInst.exe (PID: 2344)
- DrvInst.exe (PID: 2800)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 2352)
- DrvInst.exe (PID: 2344)
- DrvInst.exe (PID: 2800)
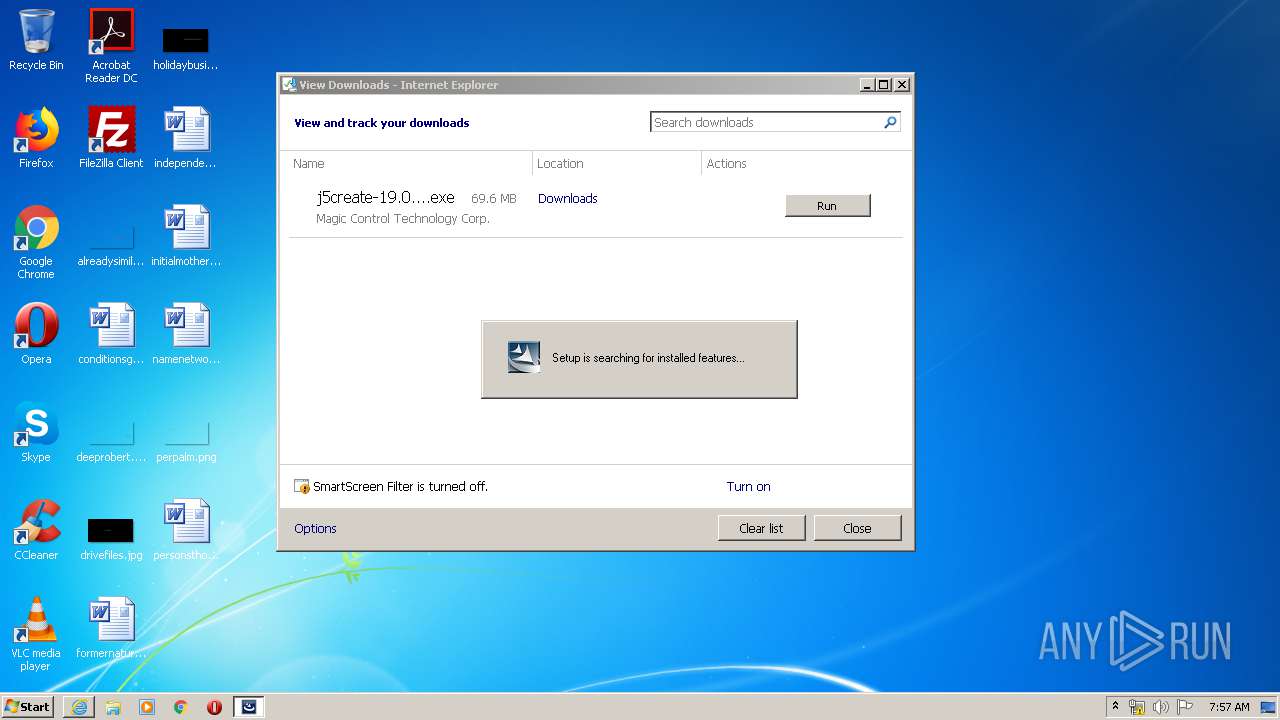
Searches for installed software
- j5create-19.03.1210.3179.exe (PID: 3708)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3892)
- iexplore.exe (PID: 3252)
- IEXPLORE.EXE (PID: 2448)
- IEXPLORE.EXE (PID: 3388)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3892)
Creates files in the user directory
- iexplore.exe (PID: 3892)
Changes internet zones settings
- iexplore.exe (PID: 3892)
- IEXPLORE.EXE (PID: 3388)
Application launched itself
- IEXPLORE.EXE (PID: 3388)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2576)
Adds / modifies Windows certificates
- IEXPLORE.EXE (PID: 2448)
- DrvInst.exe (PID: 2352)
- iexplore.exe (PID: 3892)
Reads settings of System Certificates
- IEXPLORE.EXE (PID: 2448)
- iexplore.exe (PID: 3892)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 2448)
Changes settings of System certificates
- IEXPLORE.EXE (PID: 2448)
- DrvInst.exe (PID: 2352)
- iexplore.exe (PID: 3892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
31
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{7429d63b-c1ae-0212-8831-db0c4a7a001d} Global\{551017b5-dcbf-53b8-5cb3-65068def0e55} C:\Windows\System32\DriverStore\Temp\{57e3930b-47d1-11a2-e38f-ec57c1e15d51}\IsnaUsbVga.inf C:\Windows\System32\DriverStore\Temp\{57e3930b-47d1-11a2-e38f-ec57c1e15d51}\IsnaUsbVga.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 564 | C:\Windows\System32\cmd.exe /c rd /s /q "C:\Program Files\MCT Corp\MagicLink\Driver" | C:\Windows\System32\cmd.exe | — | j5create-19.03.1210.3179.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 620 | C:\Windows\system32\MlPatch.exe | C:\Windows\system32\MlPatch.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1024 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{5033a010-04c2-0b56-8704-773b3a0bb669}\T5Audio.INF" "0" "6981ccc7f" "00000060" "WinSta0\Default" "00000558" "208" "C:\PROGRA~1\MCTCOR~1\UVTP100\Driver\3rd\AudioFilter\Win7" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1676 | "C:\Program Files\MCT Corp\UVTP100\Driver\devcon32.exe" rescan | C:\Program Files\MCT Corp\UVTP100\Driver\devcon32.exe | — | j5create-19.03.1210.3179.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.2.9200.16384 (win8_rtm.120725-1247) Modules
| |||||||||||||||
| 1932 | C:\Windows\system32\GManager.exe | C:\Windows\system32\GManager.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: General MCT Display Service Exit code: 0 Version: 1.5.17.725 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\MCT Corp\UVTP100\Driver\TUCCDUTIL\TUCCD.exe" | C:\Program Files\MCT Corp\UVTP100\Driver\TUCCDUTIL\TUCCD.exe | j5create-19.03.1210.3179.exe | ||||||||||||
User: admin Company: Magic Control Technology Corporation Integrity Level: HIGH Exit code: 0 Version: 1.0.17.918 Modules
| |||||||||||||||
| 2272 | "C:\Users\admin\Downloads\j5create-19.03.1210.3179.exe" | C:\Users\admin\Downloads\j5create-19.03.1210.3179.exe | — | iexplore.exe | |||||||||||
User: admin Company: Flexera Software LLC Integrity Level: MEDIUM Description: InstallScript Setup Launcher Unicode Exit code: 3221226540 Version: 20.0.496 Modules
| |||||||||||||||
| 2344 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{3daeb256-b220-0aba-ce23-9c1f20b2ba0a}\IsnaUsbVga.inf" "0" "677babae7" "00000554" "WinSta0\Default" "000003FC" "208" "C:\PROGRA~1\MCTCOR~1\UVTP100\Driver" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2352 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{0beb16f1-b2bc-1675-0455-9d0140aa2e0b}\MctUsbVga.inf" "0" "625e5206b" "00000558" "WinSta0\Default" "00000554" "208" "C:\PROGRA~1\MCTCOR~1\UVTP100\Driver" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 488
Read events
2 188
Write events
5 005
Delete events
2 295
Modification events
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2602569096 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30797324 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
202
Suspicious files
95
Text files
188
Unknown types
56
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\j5create-19.03.1210.3179[1].exe | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\Downloads\j5create-19.03.1210.3179.exe.7fkn8kj.partial | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF945467D7ABB80B28.TMP | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\Downloads\j5create-19.03.1210.3179.exe.7fkn8kj.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\Downloads\j5create-19.03.1210.3179.exe | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab32CB.tmp | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar32CC.tmp | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab330C.tmp | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar330D.tmp | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab338B.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3252 | iexplore.exe | GET | — | 192.232.251.98:80 | http://download.j5create.com/driver/USB_Display_Adapters_Windows_Driver/j5create-19.03.1210.3179.exe | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3252 | iexplore.exe | 192.232.251.98:80 | download.j5create.com | Unified Layer | US | malicious |
3892 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.j5create.com |
| malicious |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3252 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
GManager.exe | [GManager] MCT::Service Install
|
GManager.exe | [GManager] MCT::Service Install
|
GManager.exe | [GManager] MCT::Service Run
|
GManager.exe | [GManager] enumerateDevice start
|
GManager.exe | [GManager] GetEjectInfo RegOpenKeyEx success
|
GManager.exe | [GManager] loadCommon start
|
GManager.exe | [GManager] GetEjectInfo Read after ret = 0
|
GManager.exe | [GManager] DELAY_LOAD = 10000
|
GManager.exe | [GManager] loadCommon end
|
GManager.exe | [GManager] DELAY_ENABLE = 0
|