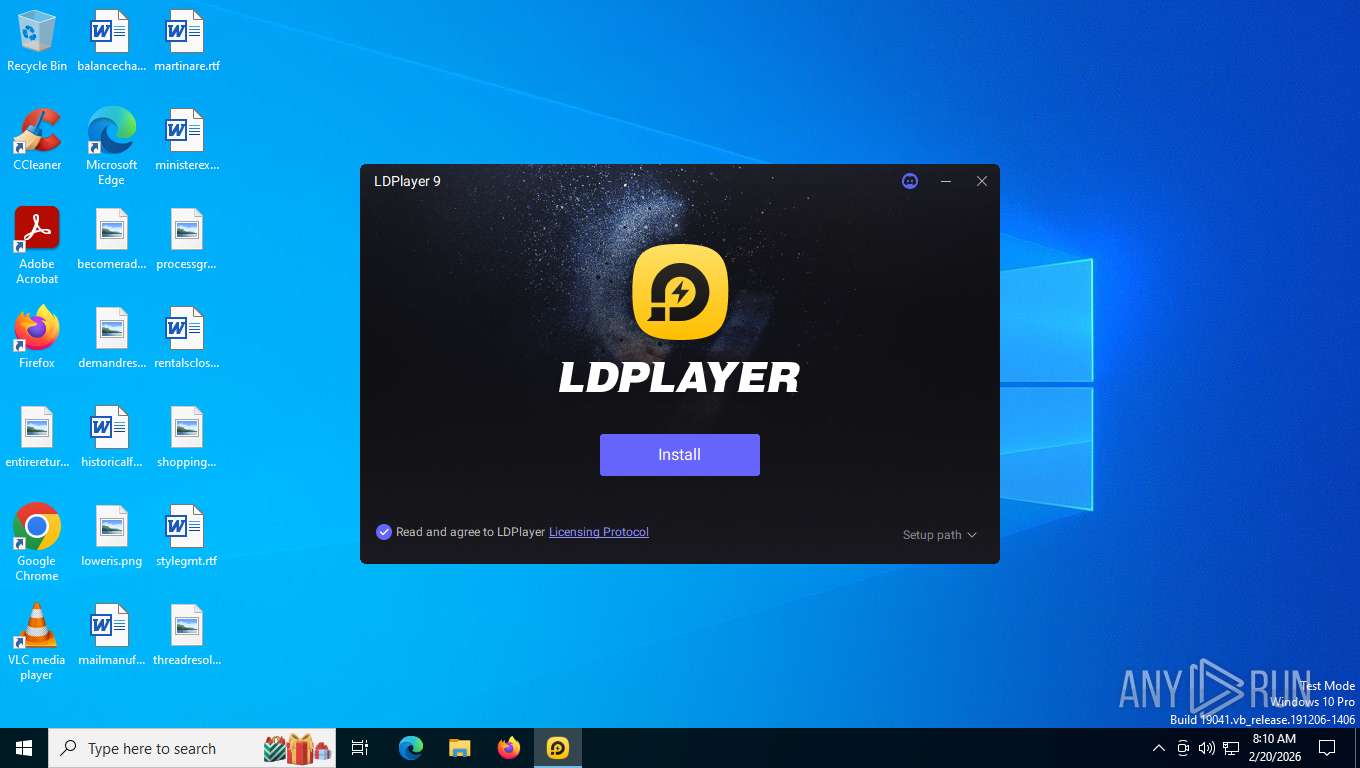
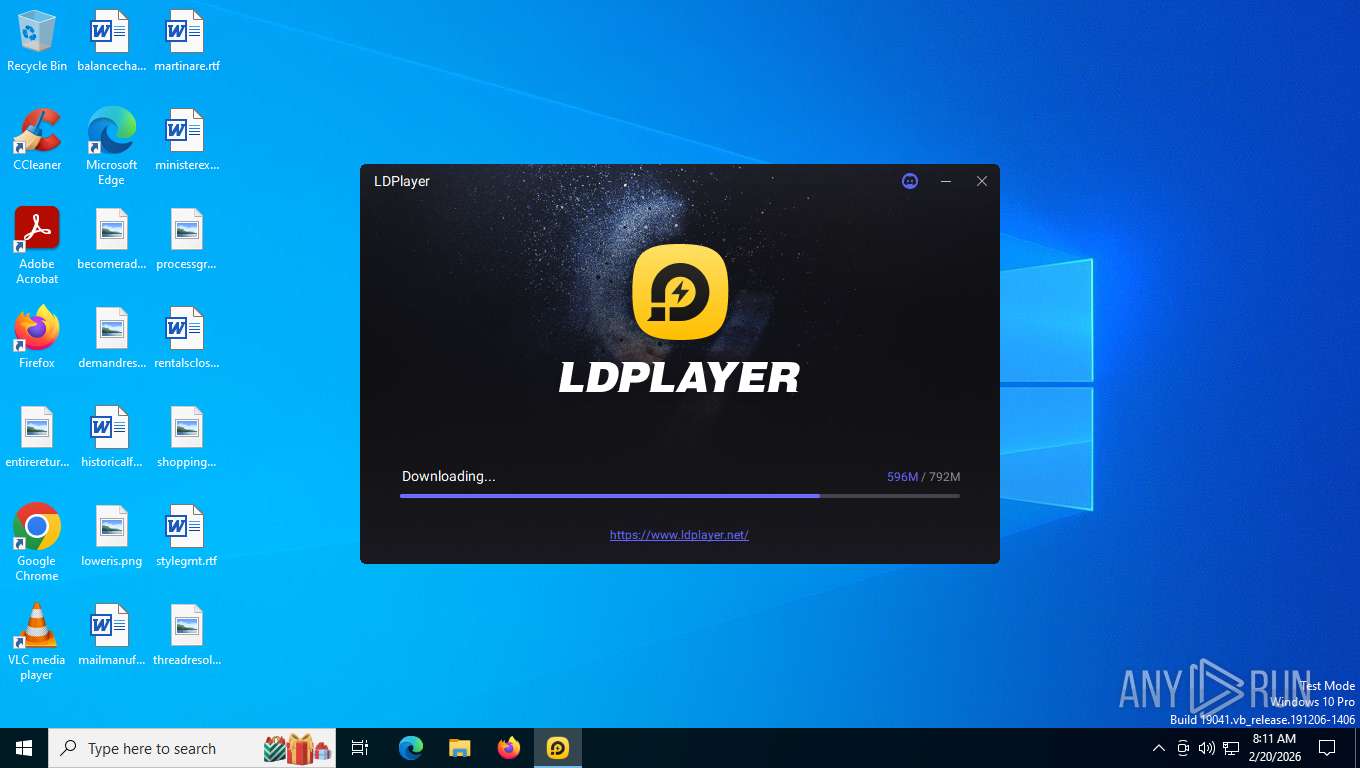
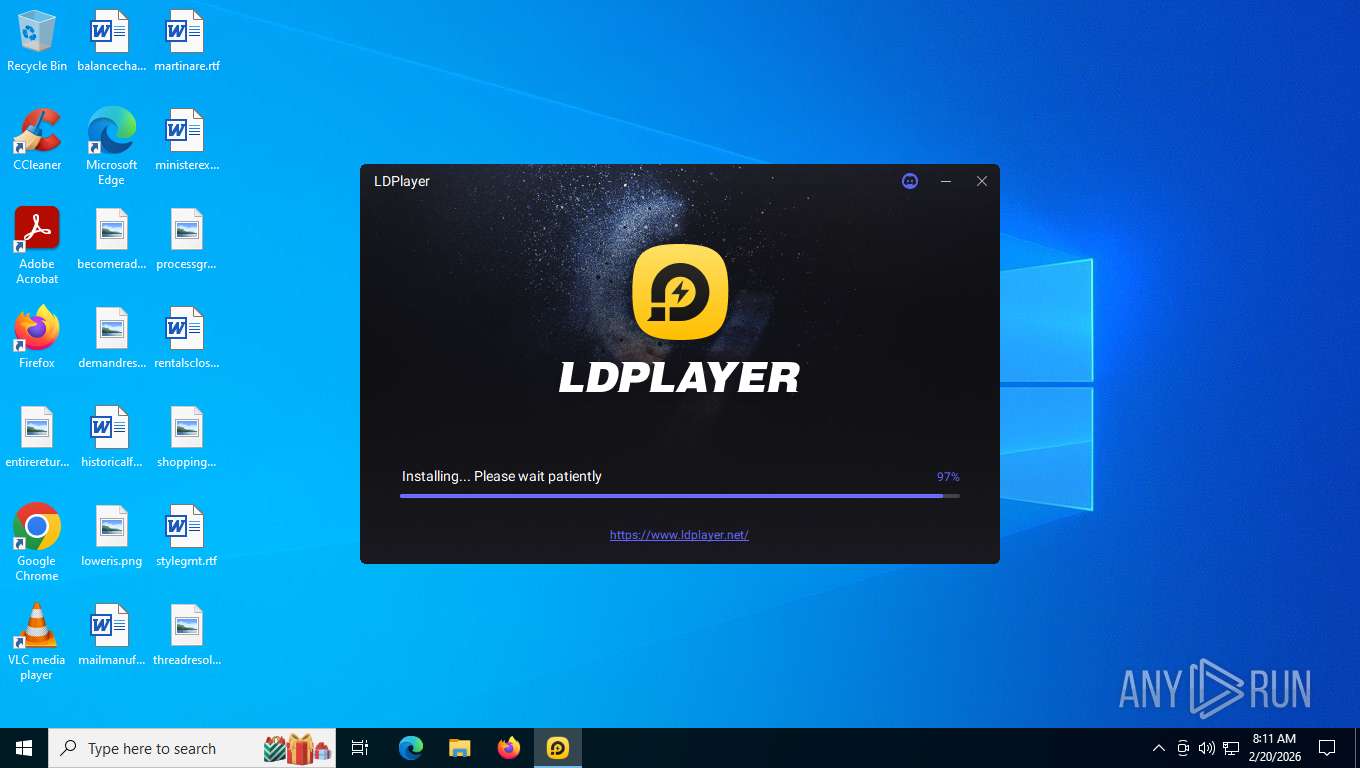
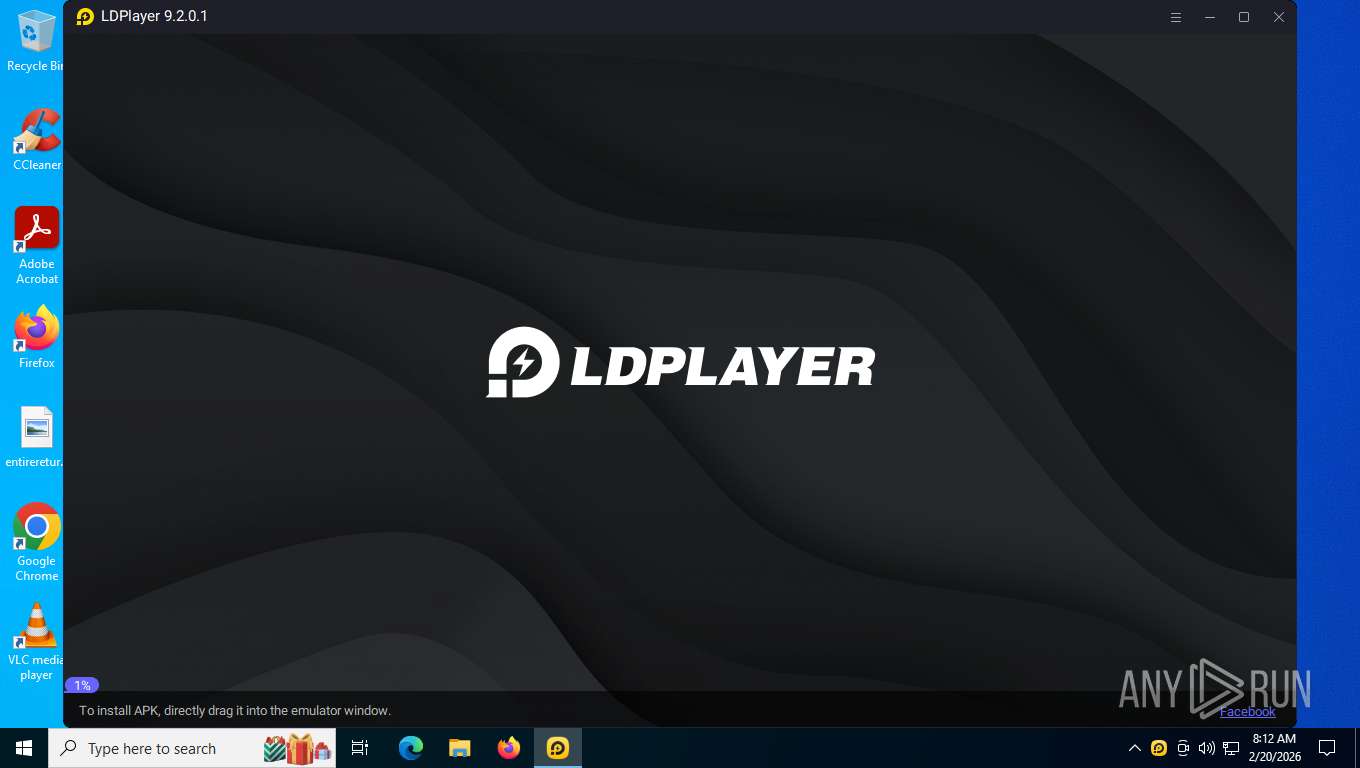
| download: | /download/LDPlayer9.exe |
| Full analysis: | https://app.any.run/tasks/5ae611c7-79b3-42d1-b998-44ae2dbe581d |
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2026, 13:10:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | E1D2D9CCEF105D0D0B4BBFA13A1ABB13 |
| SHA1: | 717F2DCA5DD007D091F1DCE6C6D786CB03C68579 |
| SHA256: | 10FCACEC94908199B1C3A9C8912381C623419C7E7F4310D407AC4BD2F00286EA |
| SSDEEP: | 98304:tAHAQ89zGP++kjkVAGR+cXxKp0IXthS+i6te+AMLAgDsUBtK8fWi1OjtbJhN8eWD:Z0f |
MALICIOUS
Starts NET.EXE for service management
- dnrepairer.exe (PID: 8544)
- net.exe (PID: 8308)
GENERIC has been found (auto)
- LDPlayer_0900020001.exe (PID: 3304)
Registers / Runs the DLL via REGSVR32.EXE
- dnrepairer.exe (PID: 8544)
SUSPICIOUS
The process creates files with name similar to system file names
- LDPlayer_0900020001.exe (PID: 3304)
Uses ICACLS.EXE to modify access control lists
- dnrepairer.exe (PID: 8544)
- LDPlayer_0900020001.exe (PID: 3304)
Starts POWERSHELL.EXE for commands execution
- dnrepairer.exe (PID: 8544)
Drops a system driver (possible attempt to evade defenses)
- dnrepairer.exe (PID: 8544)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3636)
- regsvr32.exe (PID: 1320)
Creates a new Windows service
- sc.exe (PID: 1512)
Windows service management via SC.EXE
- sc.exe (PID: 7340)
- sc.exe (PID: 7956)
- sc.exe (PID: 4364)
Takes ownership (TAKEOWN.EXE)
- dnrepairer.exe (PID: 8544)
- LDPlayer_0900020001.exe (PID: 3304)
Uses powercfg.exe to modify the power settings
- LDPlayer_0900020001.exe (PID: 3304)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 2140)
Starts CMD.EXE for commands execution
- dnplayer.exe (PID: 7620)
The process checks if it is being run in the virtual environment
- conhost.exe (PID: 7156)
- conhost.exe (PID: 1684)
- conhost.exe (PID: 1844)
Executes application which crashes
- Ld9BoxHeadless.exe (PID: 4152)
There is functionality for communication over UDP network (YARA)
- dnplayer.exe (PID: 7620)
- Ld9BoxSVC.exe (PID: 6916)
There is functionality for VM detection VirtualBox (YARA)
- dnplayer.exe (PID: 7620)
- Ld9BoxSVC.exe (PID: 6916)
There is functionality for VM detection antiVM strings (YARA)
- dnplayer.exe (PID: 7620)
INFO
Checks supported languages
- LDPlayer9.exe (PID: 5752)
- LDPlayer_0900020001.exe (PID: 3304)
- dnrepairer.exe (PID: 8544)
- Ld9BoxSVC.exe (PID: 7864)
- driverconfig.exe (PID: 7100)
- dnplayer.exe (PID: 7620)
- Ld9BoxSVC.exe (PID: 6916)
- vbox-img.exe (PID: 8668)
- vbox-img.exe (PID: 7608)
- vbox-img.exe (PID: 5524)
- Ld9BoxHeadless.exe (PID: 4152)
Creates files or folders in the user directory
- LDPlayer9.exe (PID: 5752)
- LDPlayer_0900020001.exe (PID: 3304)
- dnrepairer.exe (PID: 8544)
- dnplayer.exe (PID: 7620)
- WerFault.exe (PID: 6884)
Checks proxy server information
- LDPlayer9.exe (PID: 5752)
- LDPlayer_0900020001.exe (PID: 3304)
- dnplayer.exe (PID: 7620)
- slui.exe (PID: 2424)
- WerFault.exe (PID: 6884)
Reads the computer name
- LDPlayer9.exe (PID: 5752)
- LDPlayer_0900020001.exe (PID: 3304)
- Ld9BoxSVC.exe (PID: 7864)
- dnplayer.exe (PID: 7620)
- Ld9BoxSVC.exe (PID: 6916)
- Ld9BoxHeadless.exe (PID: 4152)
Reads the machine GUID from the registry
- LDPlayer_0900020001.exe (PID: 3304)
- LDPlayer9.exe (PID: 5752)
- dnrepairer.exe (PID: 8544)
- dnplayer.exe (PID: 7620)
Reads security settings of Internet Explorer
- LDPlayer_0900020001.exe (PID: 3304)
- LDPlayer9.exe (PID: 5752)
- dnplayer.exe (PID: 7620)
Creates files in the program directory
- dnrepairer.exe (PID: 8544)
Drops script file
- dnrepairer.exe (PID: 8544)
- powershell.exe (PID: 8396)
- powershell.exe (PID: 412)
- powershell.exe (PID: 5304)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5304)
- powershell.exe (PID: 412)
- powershell.exe (PID: 8396)
There is functionality for taking screenshot (YARA)
- dnrepairer.exe (PID: 8544)
- dnplayer.exe (PID: 7620)
Creates a software uninstall entry
- LDPlayer_0900020001.exe (PID: 3304)
Create files in a temporary directory
- Ld9BoxHeadless.exe (PID: 4152)
Reads Environment values
- Ld9BoxHeadless.exe (PID: 4152)
Reads CPU info
- dnplayer.exe (PID: 7620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2026:02:06 03:31:40+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 2147328 |
| InitializedDataSize: | 1380352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1762bd |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (0009) |
| CharacterSet: | Unicode |
| CompanyName: | JUST OKAY LIMITED |
| FileDescription: | JUST OKAY LIMITED |
| FileVersion: | 1.0.0.6 |
| InternalName: | JUST OKAY LIMITED |
| LegalCopyright: | Copyright (C) 2024 |
| OriginalFileName: | JUST OKAY LIMITED |
| ProductName: | JUST OKAY LIMITED |
| ProductVersion: | 1.0.0.6 |
Total processes
228
Monitored processes
70
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 144 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 412 | "powershell.exe" New-NetFirewallRule -DisplayName "Ld9BoxNat" -Direction Inbound -Program 'C:\Program Files\ldplayer9box\VBoxNetNAT.exe' -RemoteAddress LocalSubnet -Action Allow | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 552 | "takeown" /f "C:\LDPlayer\LDPlayer9\vms" /r /d y | C:\Windows\SysWOW64\takeown.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | "regsvr32" "C:\Program Files\ldplayer9box\VBoxC.dll" /s | C:\Windows\System32\regsvr32.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1320 | "regsvr32" "C:\Program Files\ldplayer9box\x86\VBoxProxyStub-x86.dll" /s | C:\Windows\SysWOW64\regsvr32.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | "C:\WINDOWS\system32\sc" create Ld9BoxSup binPath= "C:\Program Files\ldplayer9box\Ld9BoxSup.sys" type= kernel start= auto | C:\Windows\SysWOW64\sc.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | vbox-img.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1844 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | vbox-img.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1856 | "icacls" "C:\LDPlayer\LDPlayer9\vms" /grant everyone:F /t | C:\Windows\SysWOW64\icacls.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
44 890
Read events
44 422
Write events
444
Delete events
24
Modification events
| (PID) Process: | (5752) LDPlayer9.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\lden |
| Operation: | write | Name: | pcmac |
Value: 86b7989e20bc11c77505a712814c8321 | |||
| (PID) Process: | (3304) LDPlayer_0900020001.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\ld\dnplayer_en |
| Operation: | write | Name: | pcid |
Value: 86b7989e20bc11c77505a712814c8321 | |||
| (PID) Process: | (5588) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\OID\EncodingType 1\CryptDllEncodeObject\1.3.6.1.4.1.311.2.1.15 |
| Operation: | write | Name: | Dll |
Value: WINTRUST.DLL | |||
| (PID) Process: | (5588) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\OID\EncodingType 1\CryptDllEncodeObject\1.3.6.1.4.1.311.2.1.15 |
| Operation: | write | Name: | FuncName |
Value: WVTAsn1SpcPeImageDataEncode | |||
| (PID) Process: | (5588) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\OID\EncodingType 1\CryptDllEncodeObject\#2004 |
| Operation: | write | Name: | Dll |
Value: WINTRUST.DLL | |||
| (PID) Process: | (5588) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\OID\EncodingType 1\CryptDllEncodeObject\#2004 |
| Operation: | write | Name: | FuncName |
Value: WVTAsn1SpcPeImageDataEncode | |||
| (PID) Process: | (5588) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\OID\EncodingType 1\CryptDllEncodeObject\1.3.6.1.4.1.311.2.1.25 |
| Operation: | write | Name: | Dll |
Value: WINTRUST.DLL | |||
| (PID) Process: | (5588) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\OID\EncodingType 1\CryptDllEncodeObject\1.3.6.1.4.1.311.2.1.25 |
| Operation: | write | Name: | FuncName |
Value: WVTAsn1SpcLinkEncode | |||
| (PID) Process: | (5588) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\OID\EncodingType 1\CryptDllEncodeObject\#2008 |
| Operation: | write | Name: | Dll |
Value: WINTRUST.DLL | |||
| (PID) Process: | (5588) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\OID\EncodingType 1\CryptDllEncodeObject\#2008 |
| Operation: | write | Name: | FuncName |
Value: WVTAsn1SpcLinkEncode | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
670
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5752 | LDPlayer9.exe | C:\LDPlayer\LDPlayer9\LDPlayer_0900020001.exe.part1 | — | |
MD5:— | SHA256:— | |||
| 5752 | LDPlayer9.exe | C:\LDPlayer\LDPlayer9\LDPlayer_0900020001.exe.part0 | — | |
MD5:— | SHA256:— | |||
| 5752 | LDPlayer9.exe | C:\LDPlayer\LDPlayer9\LDPlayer_0900020001.exe | — | |
MD5:— | SHA256:— | |||
| 3304 | LDPlayer_0900020001.exe | C:\Users\admin\AppData\Roaming\XuanZhi\fonts\NotoSans-Regular.otf | — | |
MD5:— | SHA256:— | |||
| 3304 | LDPlayer_0900020001.exe | C:\LDPlayer\LDPlayer9\data-3G.vmdk | — | |
MD5:— | SHA256:— | |||
| 3304 | LDPlayer_0900020001.exe | C:\LDPlayer\LDPlayer9\data.vmdk | — | |
MD5:— | SHA256:— | |||
| 3304 | LDPlayer_0900020001.exe | C:\LDPlayer\LDPlayer9\dnresource.rcc | — | |
MD5:— | SHA256:— | |||
| 5752 | LDPlayer9.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_B7ED31D77D311A56FDCB56A0083B3E0B | binary | |
MD5:50495C523DD259127D57983EDE0D4AD7 | SHA256:F0FF8A832FC72E0B7D99FBEE2E801950FE181D14B73CF478FFAEB06CBCD74805 | |||
| 5752 | LDPlayer9.exe | C:\LDPlayer\LDPlayer9\th_count_0900020001.ini | binary | |
MD5:04E392F8ABB284A9A73F966A497E469E | SHA256:1A10E1F299B3CF82F901B8ECB14D82B5C9CE0EF49464FF8EFABA2D603DBEC6D3 | |||
| 3304 | LDPlayer_0900020001.exe | C:\LDPlayer\LDPlayer9\fonts\NanumGothicLight.otf | binary | |
MD5:E2E37D20B47D7EE294B91572F69E323A | SHA256:153161AB882DB768C70A753AF5E8129852B9C9CAE5511A23653BEB6414D834A2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
69
DNS requests
42
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5752 | LDPlayer9.exe | GET | — | 23.213.161.23:443 | https://static.ldrescdn.com/download/package/LDPlayer_9.2.0.1.exe | NL | — | — | unknown |
5752 | LDPlayer9.exe | GET | — | 2.16.168.102:443 | https://res.ldrescdn.com/download/package/LDPlayer_9.2.0.1.exe | NL | — | — | unknown |
5752 | LDPlayer9.exe | GET | — | 2.16.168.102:443 | https://res.ldrescdn.com/download/package/LDPlayer_9.2.0.1.exe | NL | — | — | unknown |
5752 | LDPlayer9.exe | GET | — | 2.16.168.102:443 | https://res.ldrescdn.com/download/package/LDPlayer_9.2.0.1.exe | NL | — | — | unknown |
5752 | LDPlayer9.exe | GET | 200 | 2.16.168.100:443 | https://files.ldrescdn.com/player_files/en/leidian | NL | binary | 1.92 Kb | unknown |
5752 | LDPlayer9.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAsA6S1NbXMfyjBZx8seGIY%3D | US | binary | 313 b | whitelisted |
5752 | LDPlayer9.exe | POST | 200 | 8.222.131.165:443 | https://sg-datahub.changzhi.top/collection/mnq?appId=1 | CN | binary | 47 b | unknown |
5752 | LDPlayer9.exe | GET | 200 | 47.254.135.96:443 | https://apien.ldmnq.com/check/machine/channel?m=86b7989e20bc11c77505a712814c8321 | CN | binary | 58 b | unknown |
5752 | LDPlayer9.exe | GET | 200 | 2.16.168.102:443 | https://res.ldrescdn.com/player_files/en/lddownloader.data | NL | binary | 4.60 Kb | unknown |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | US | binary | 314 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6320 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8740 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 92.123.104.5:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5752 | LDPlayer9.exe | 2.16.168.100:443 | files.ldrescdn.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
files.ldrescdn.com |
| whitelisted |
sg-datahub.changzhi.top |
| unknown |
apien.ldmnq.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
5752 | LDPlayer9.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
5752 | LDPlayer9.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2292 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
5752 | LDPlayer9.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
6884 | WerFault.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
dnplayer.exe | audio wait from recv
|
Ld9BoxHeadless.exe | ldutils myhook enter |
Ld9BoxHeadless.exe | ldutils backgroundPreread enter |
Ld9BoxHeadless.exe | ldutils backgroundPreread leave |