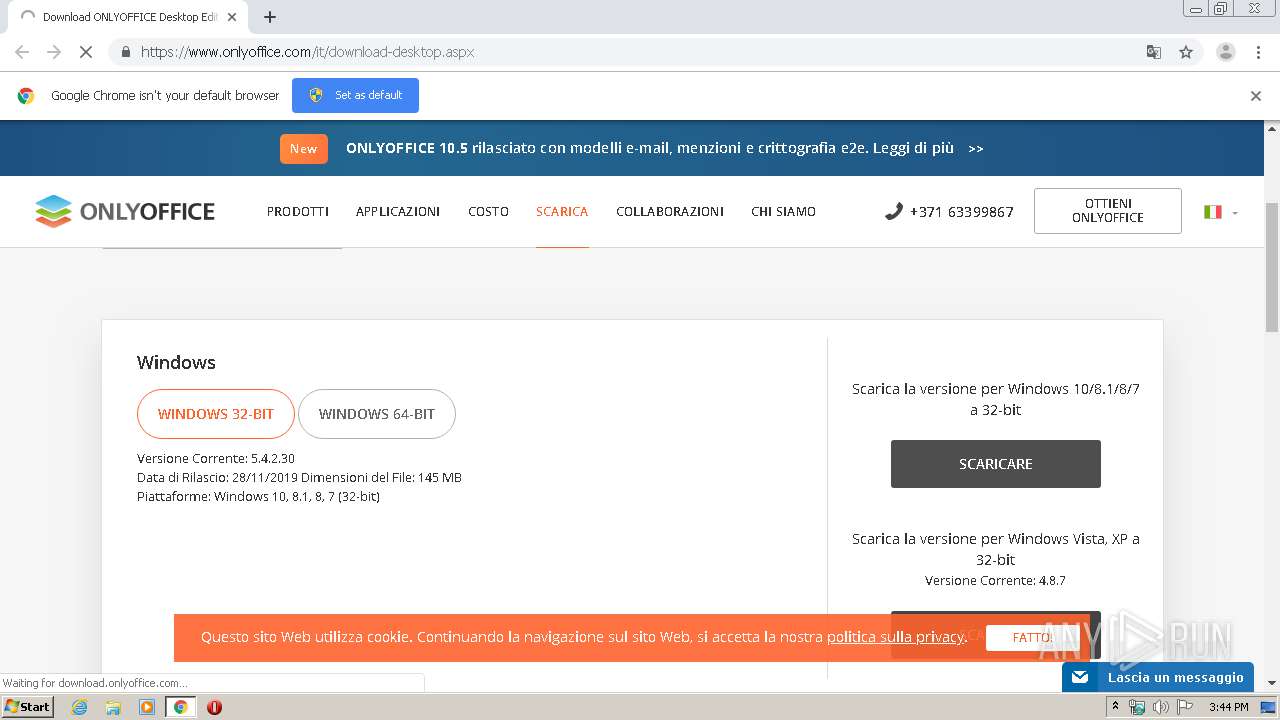
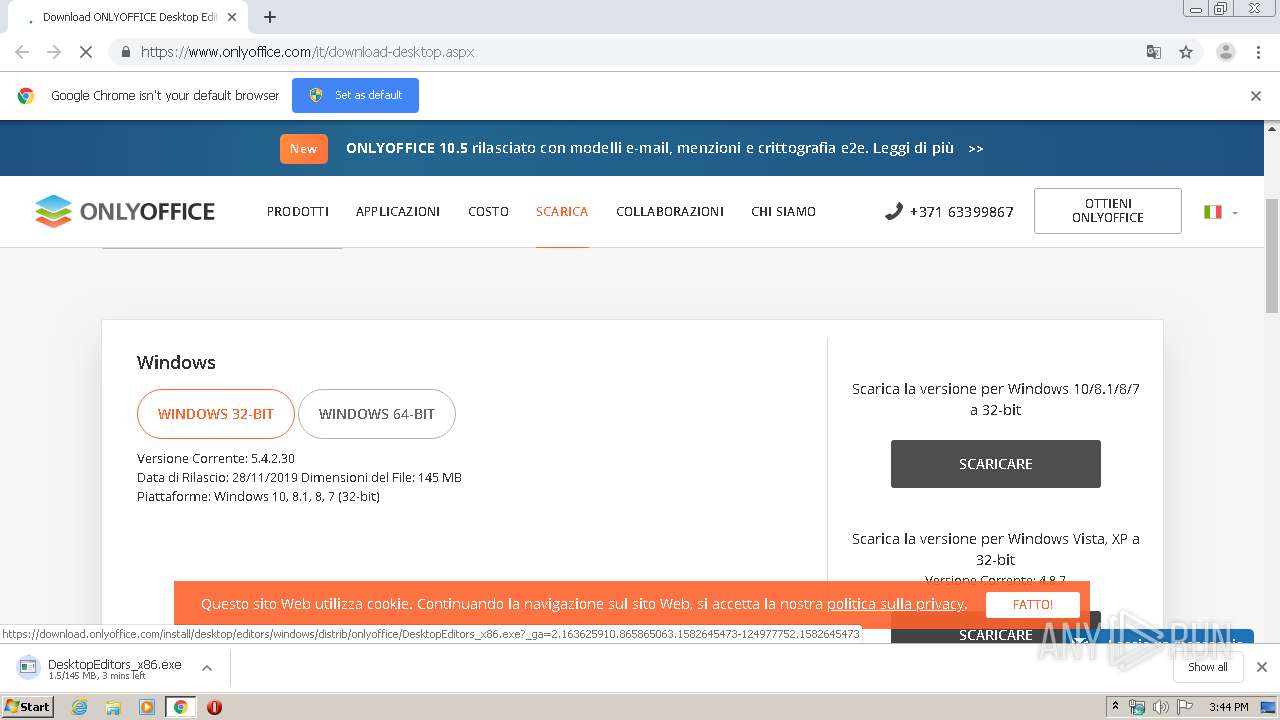
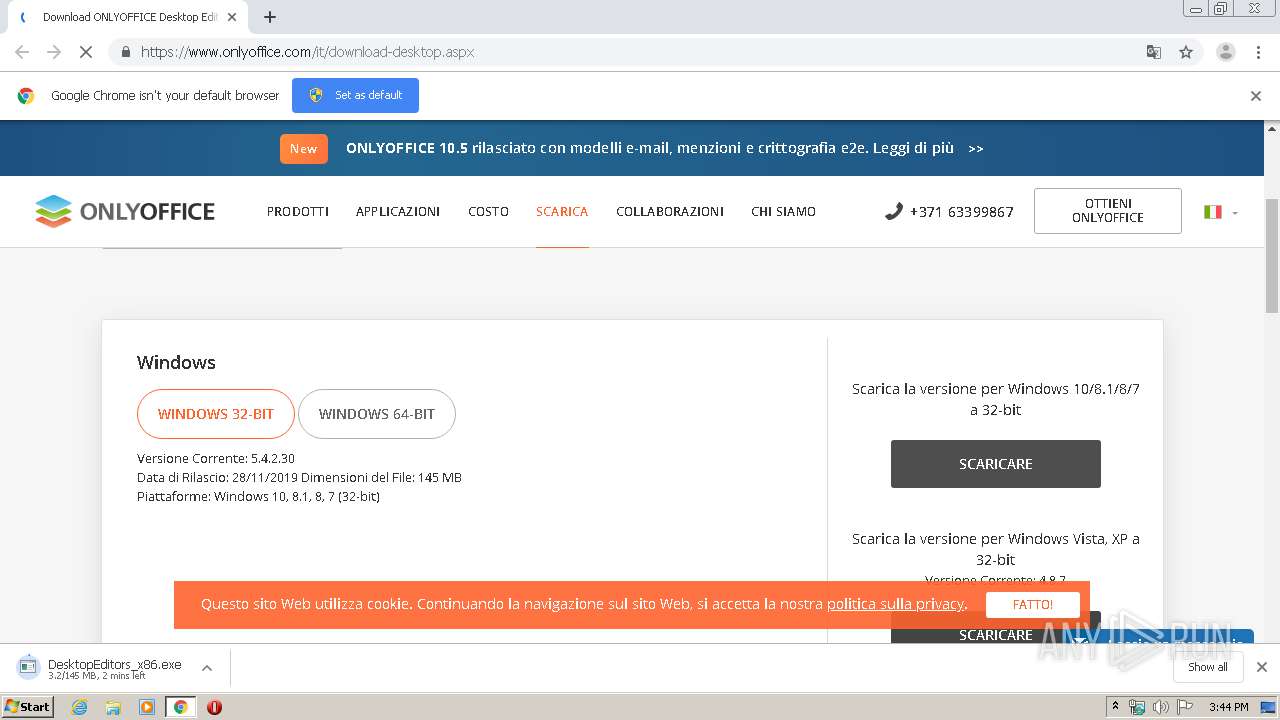
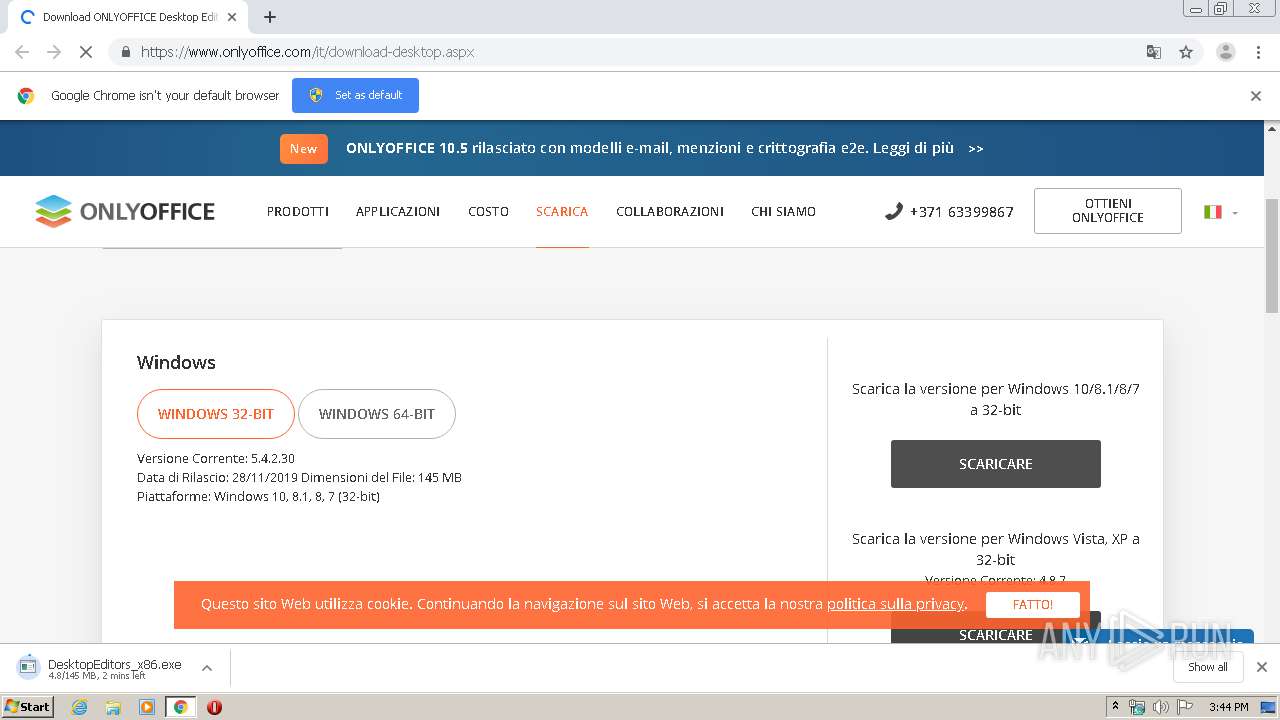
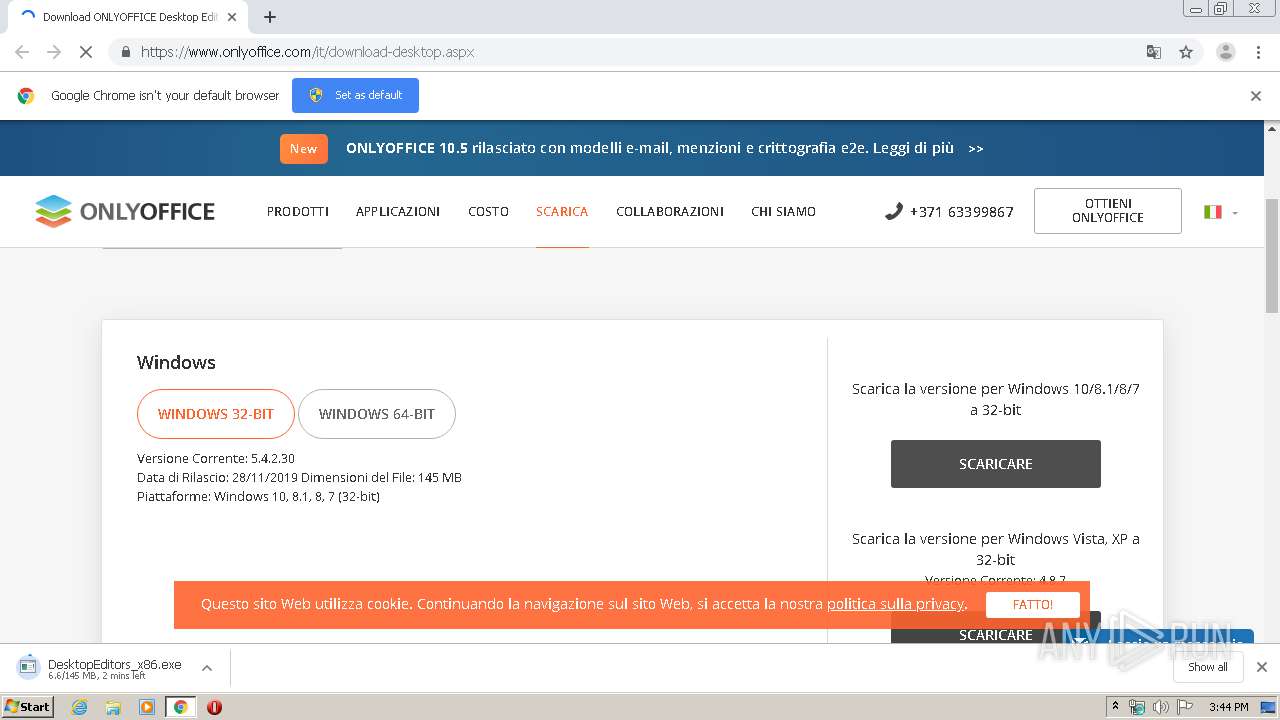
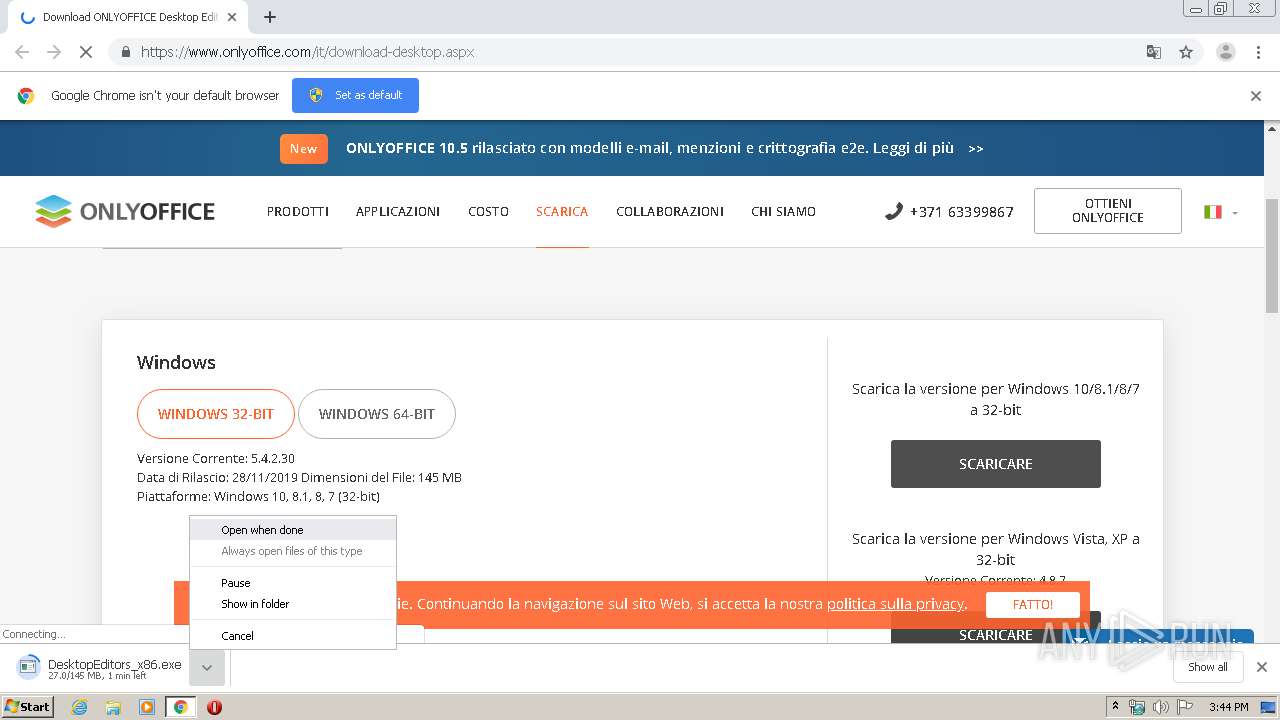
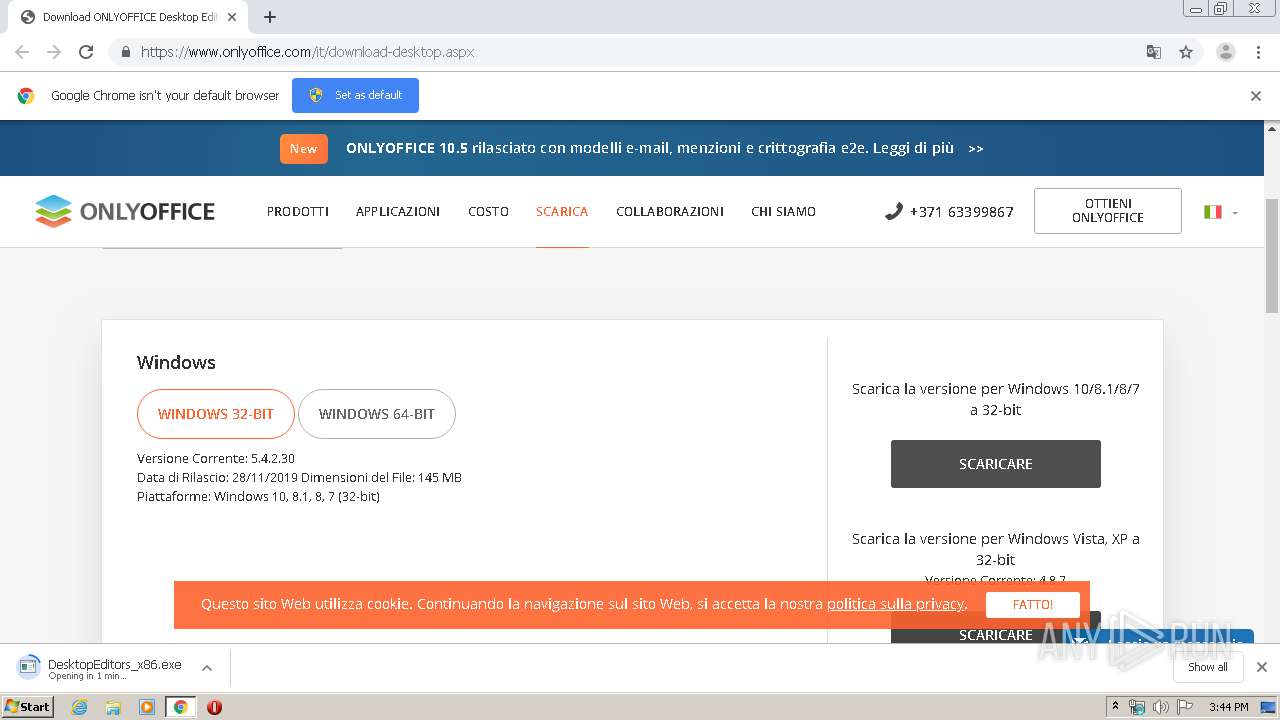
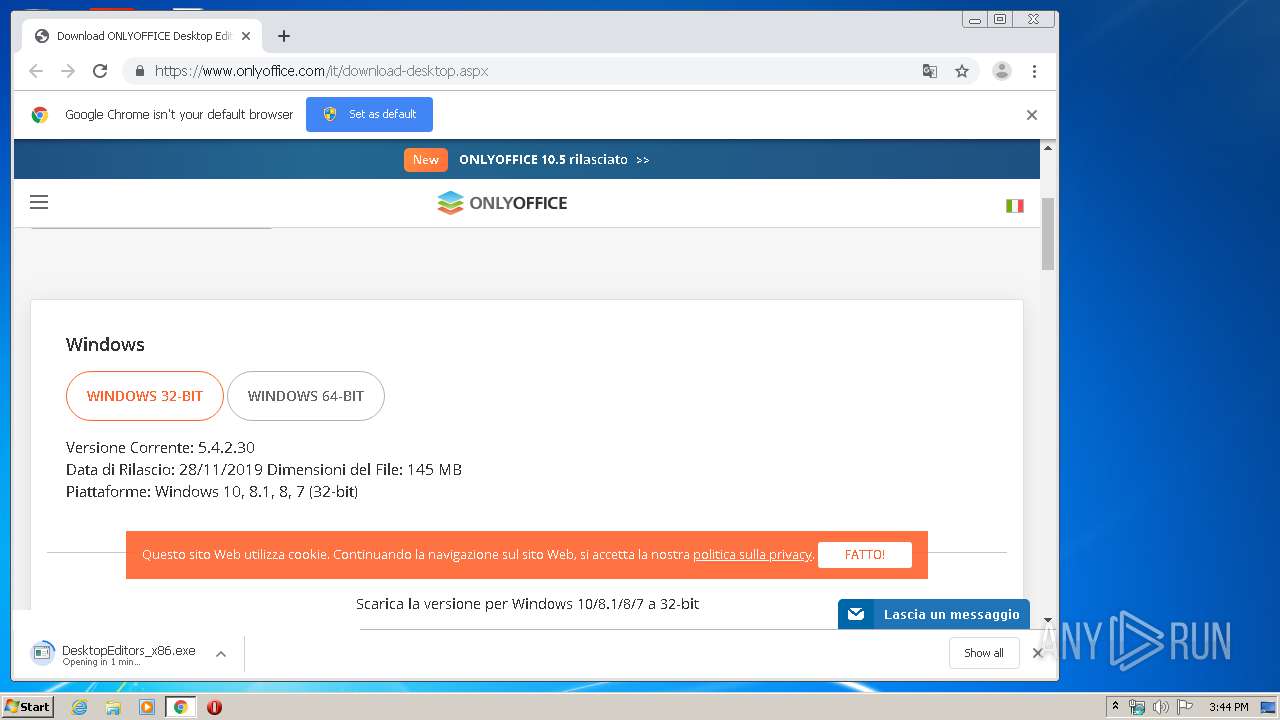
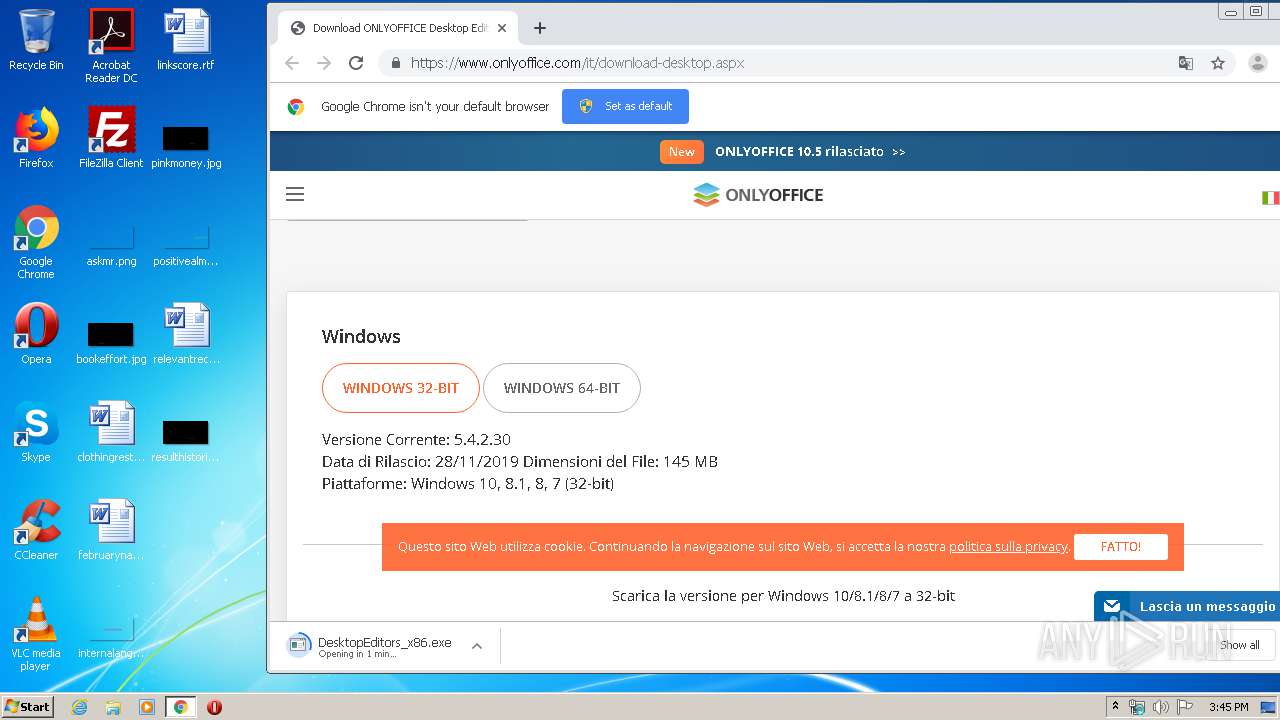
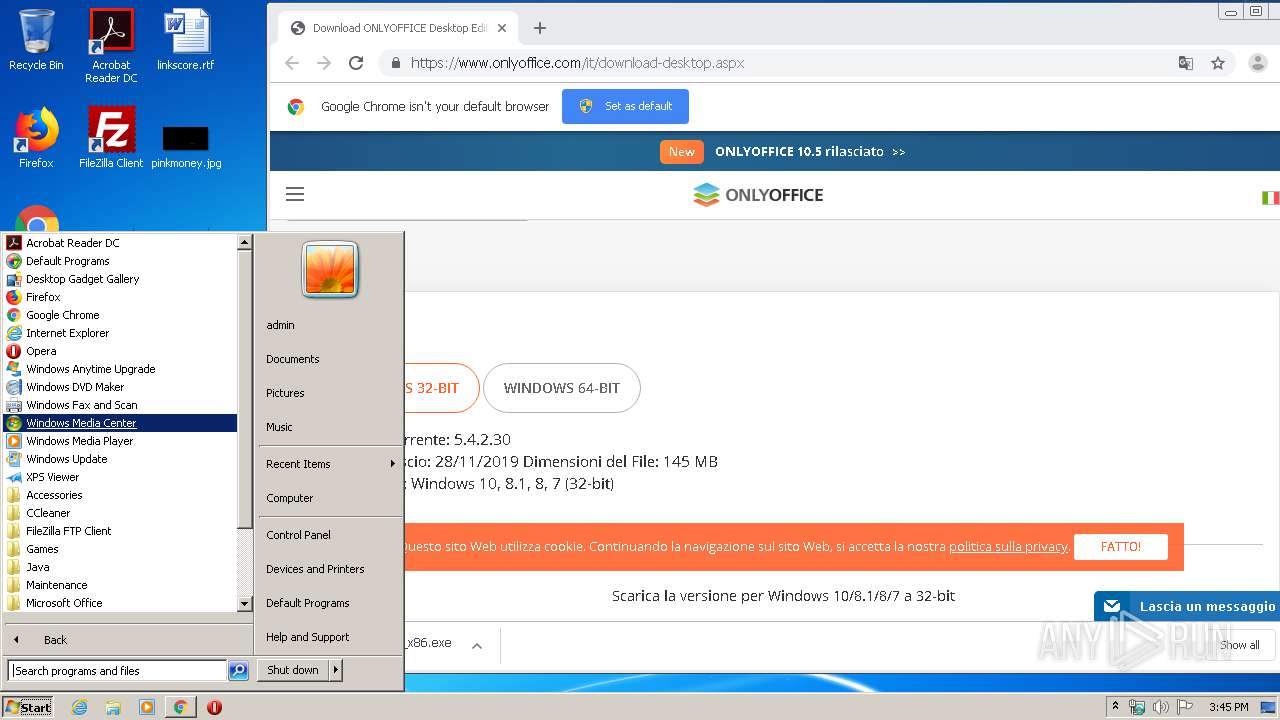
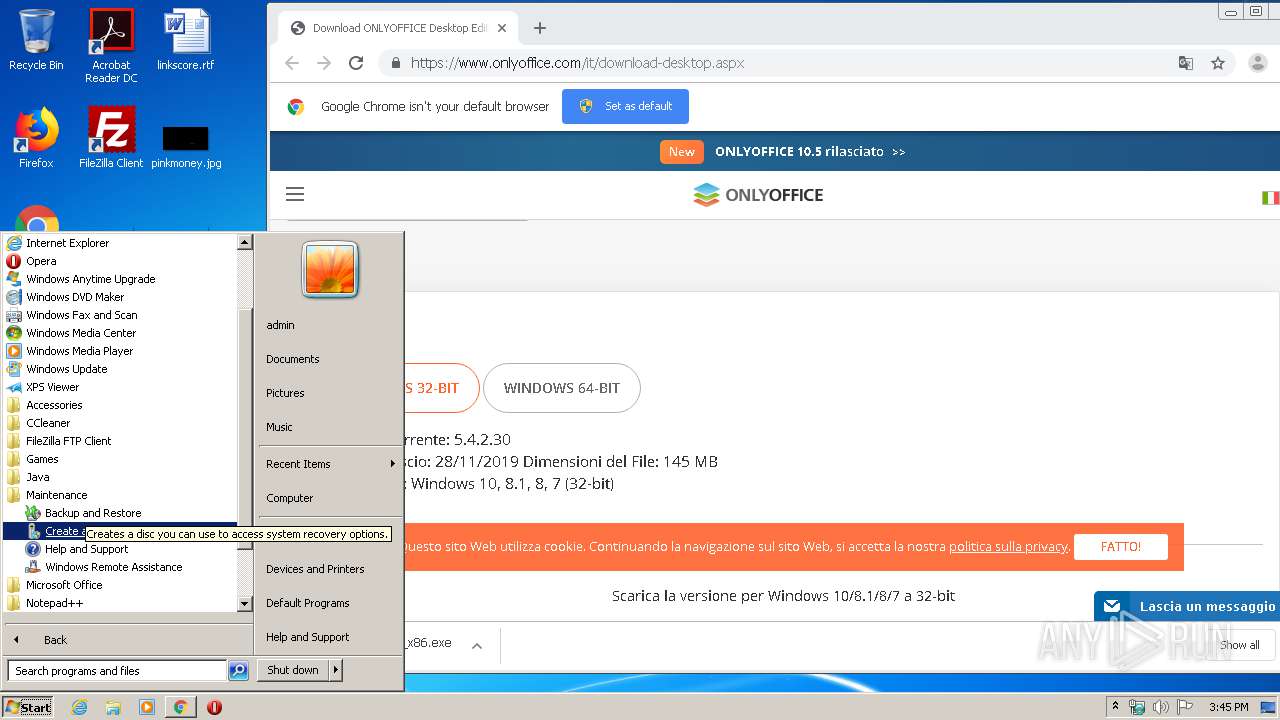
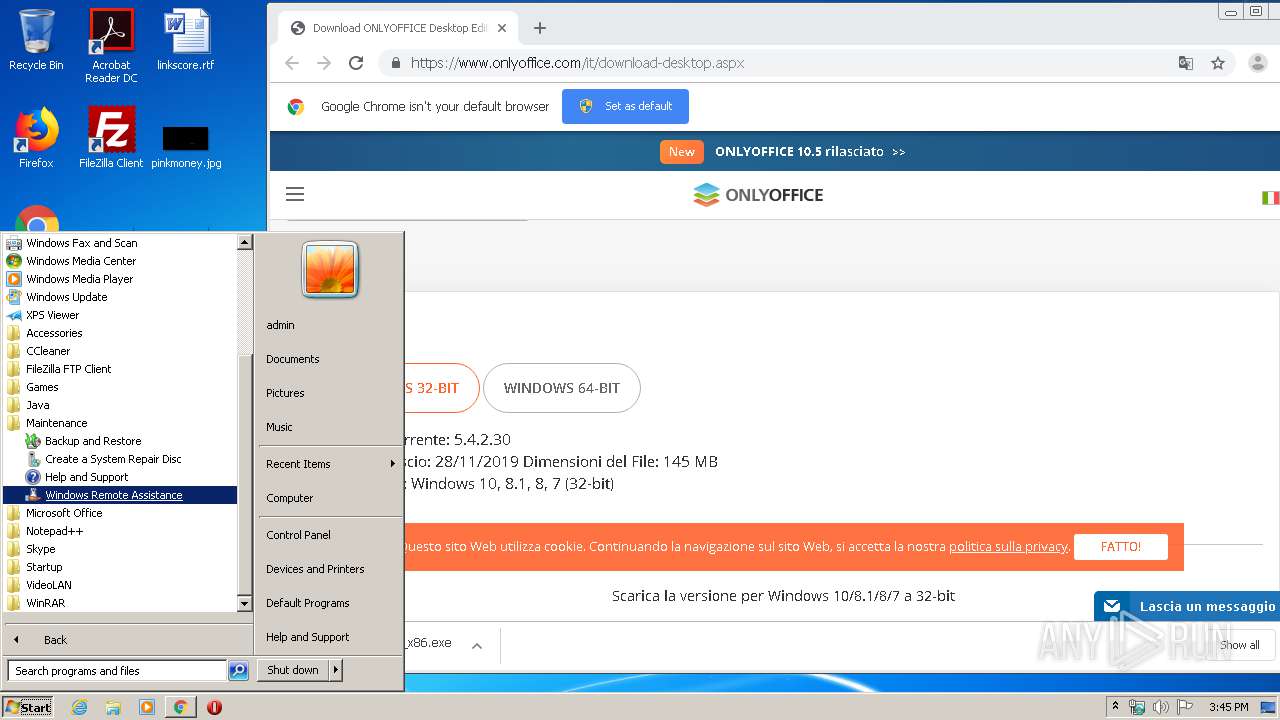
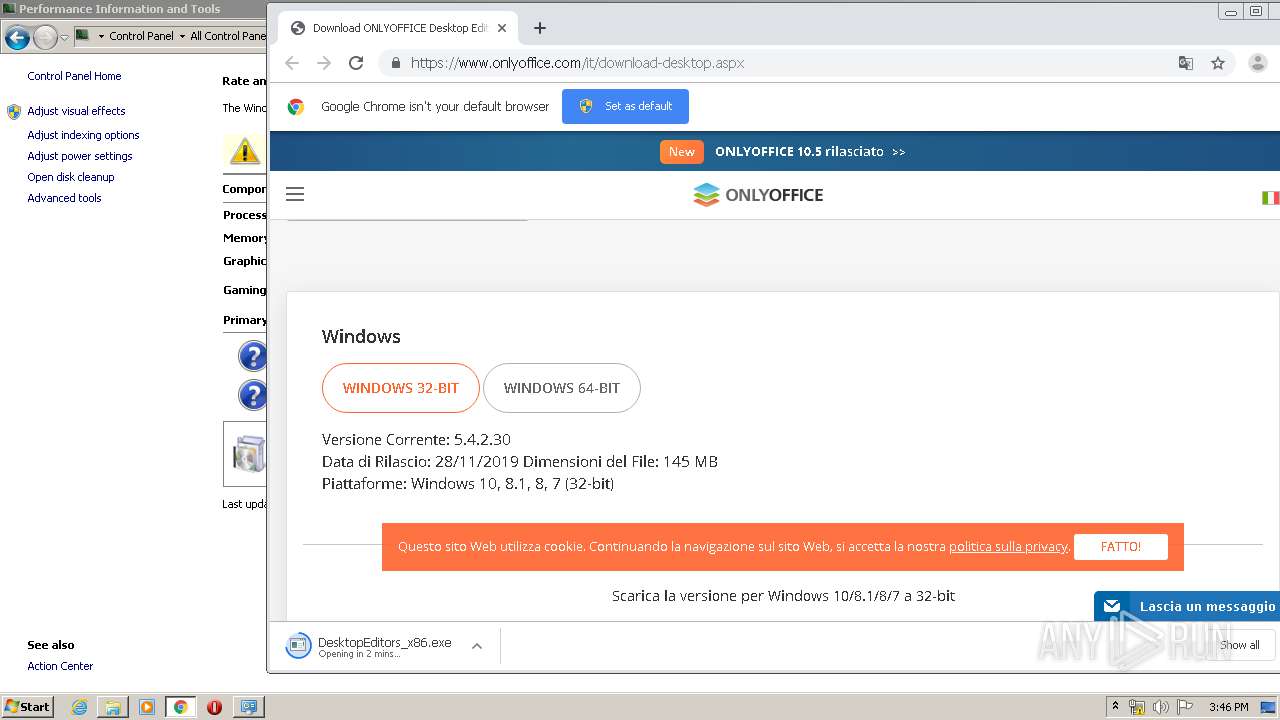
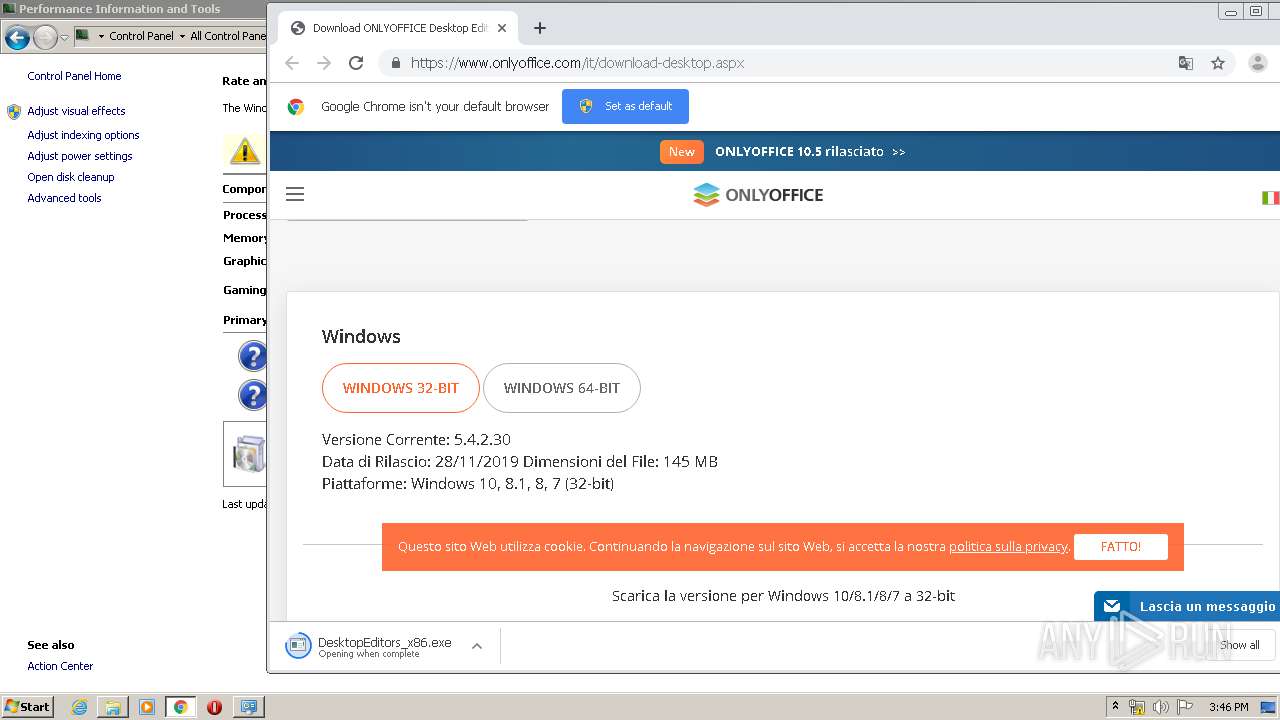
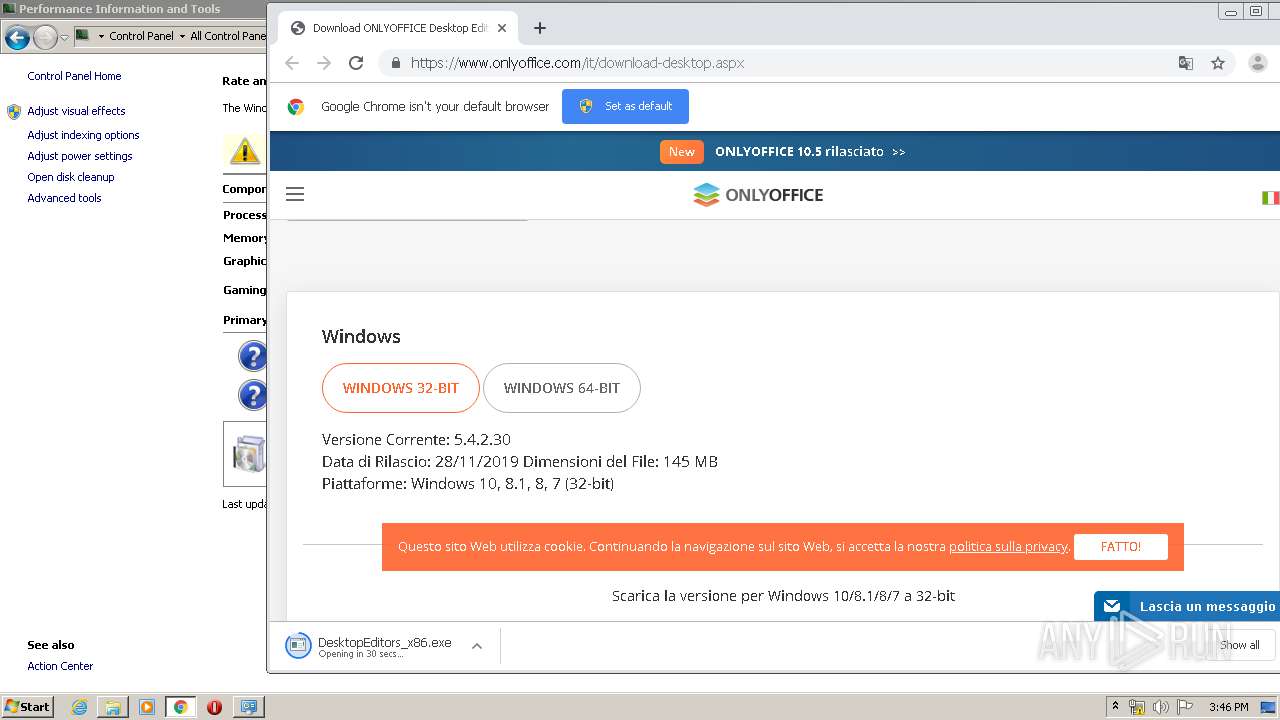
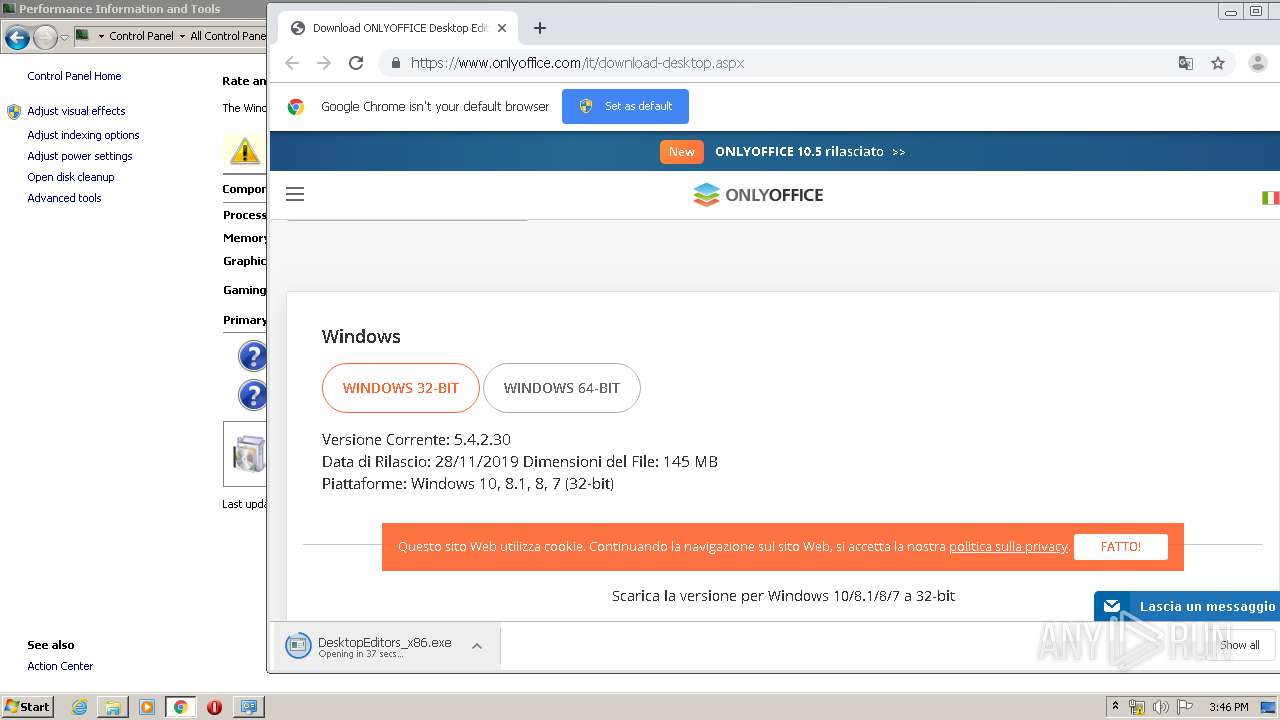
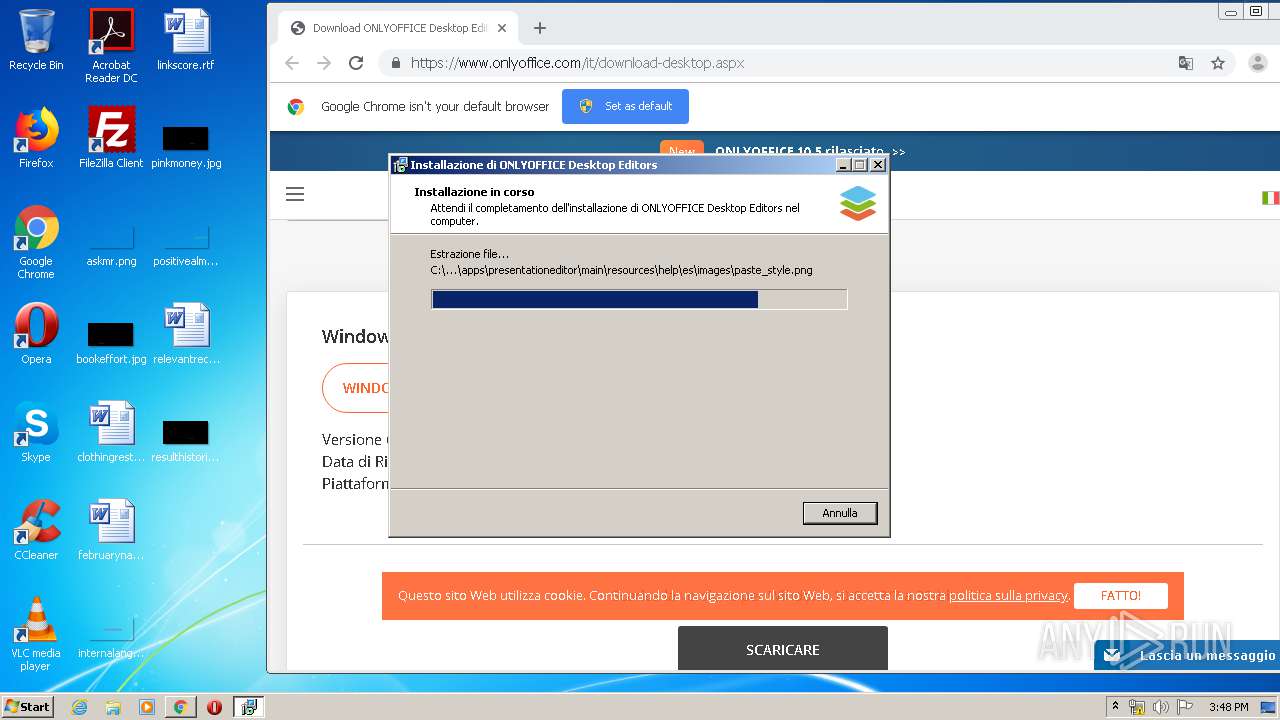
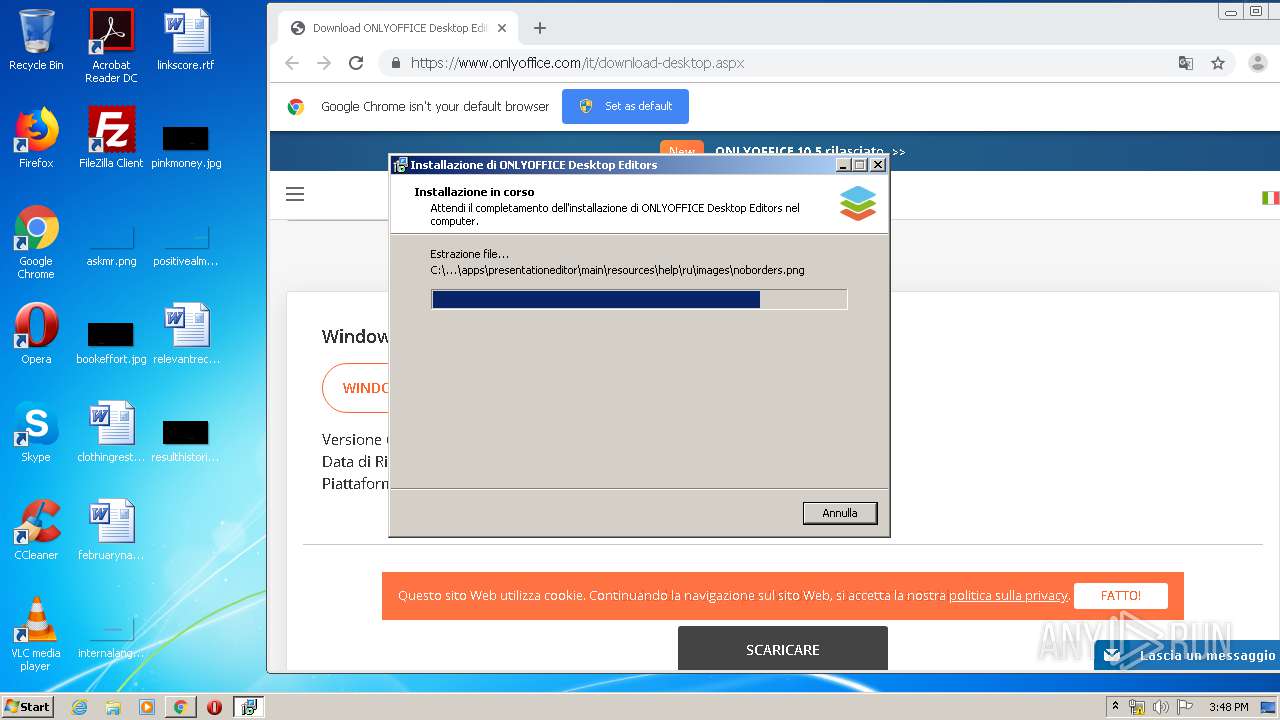
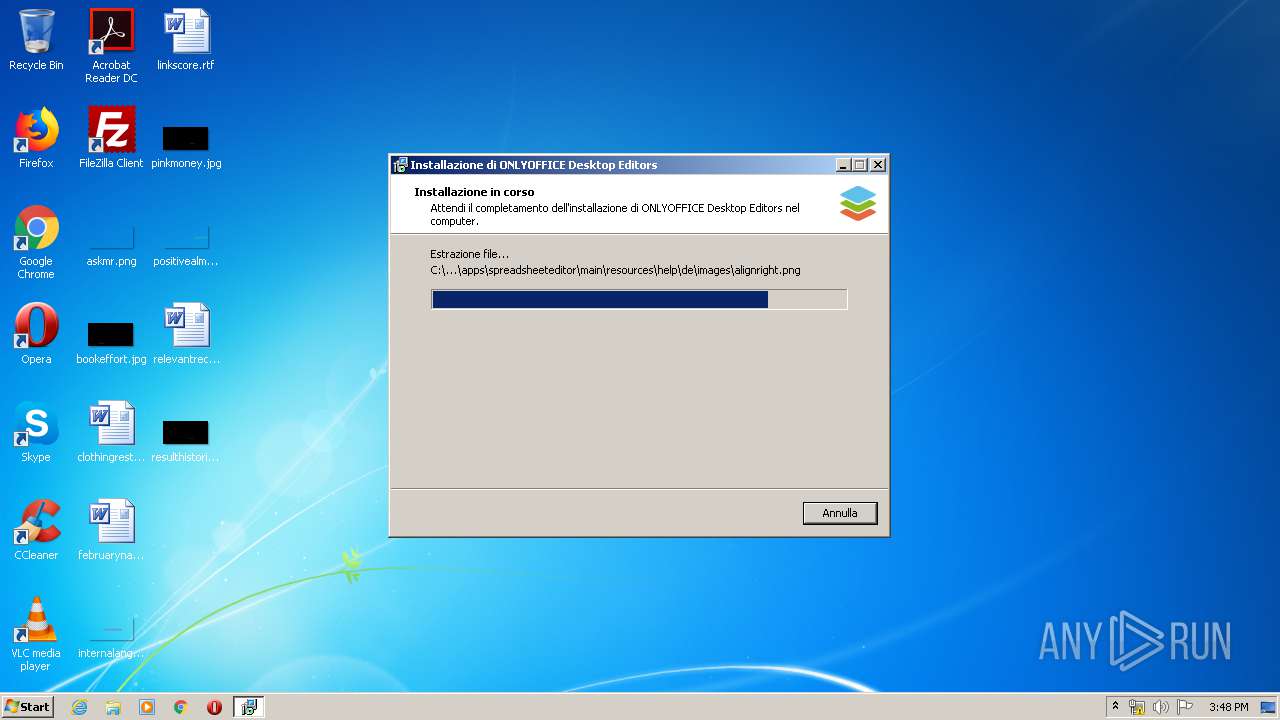
| URL: | https://www.onlyoffice.com/it/download-desktop.aspx |
| Full analysis: | https://app.any.run/tasks/83a437f5-a758-4ee5-a75b-fd916ab407f3 |
| Verdict: | Malicious activity |
| Analysis date: | February 25, 2020, 15:44:14 |
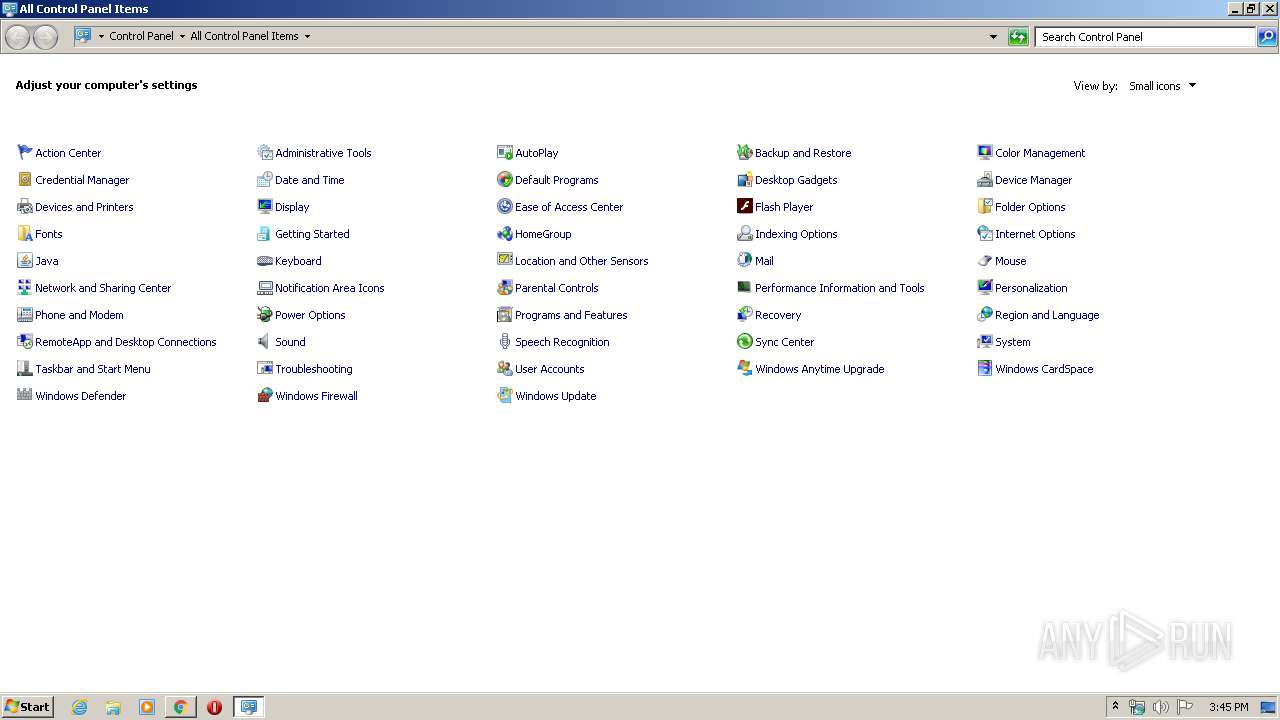
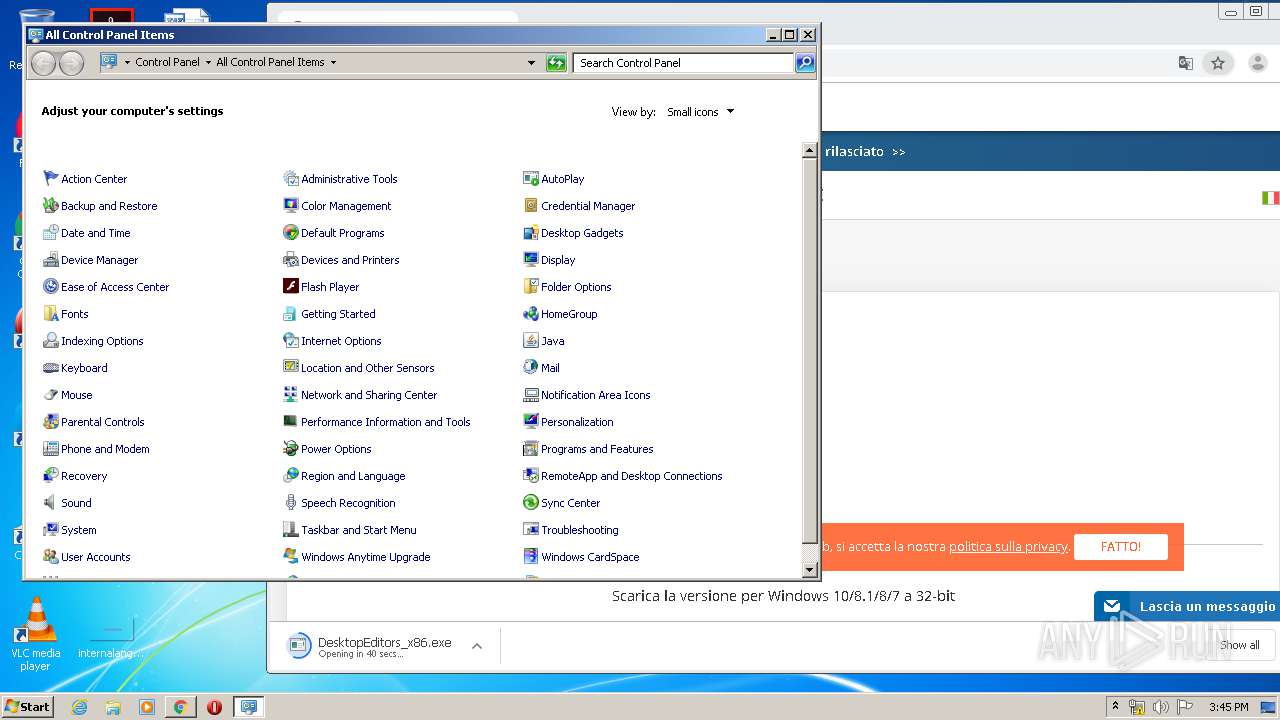
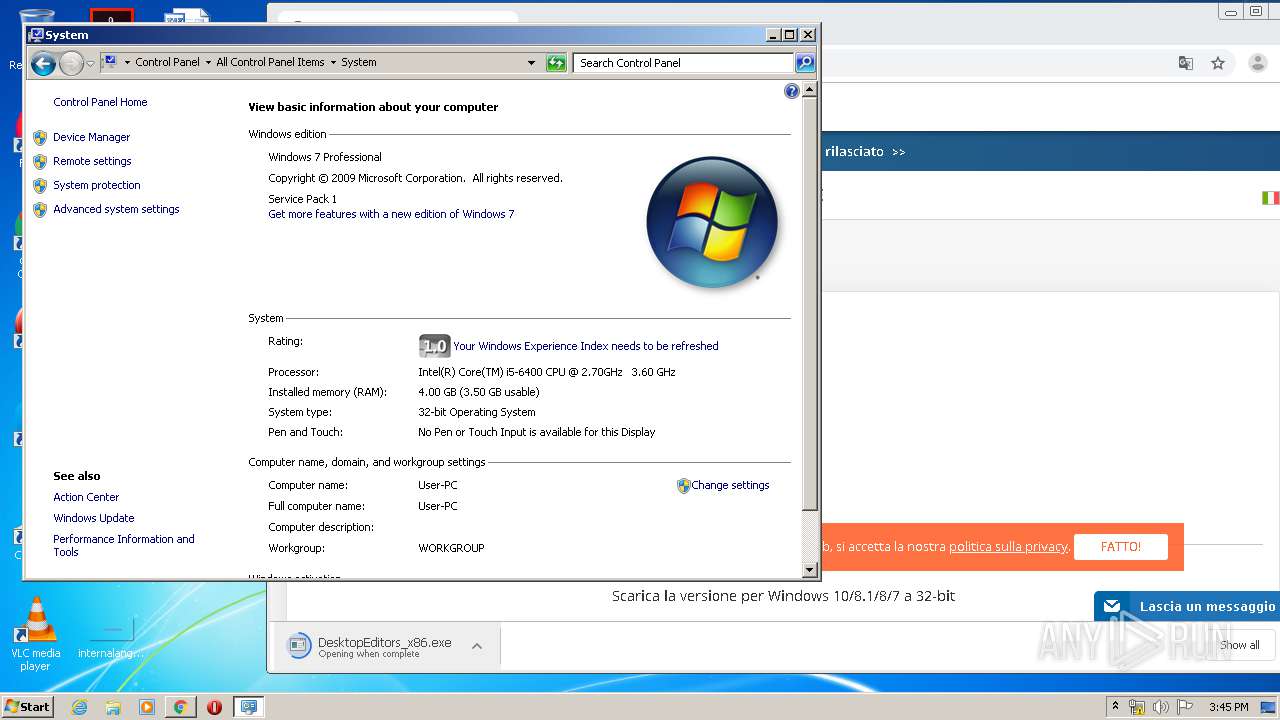
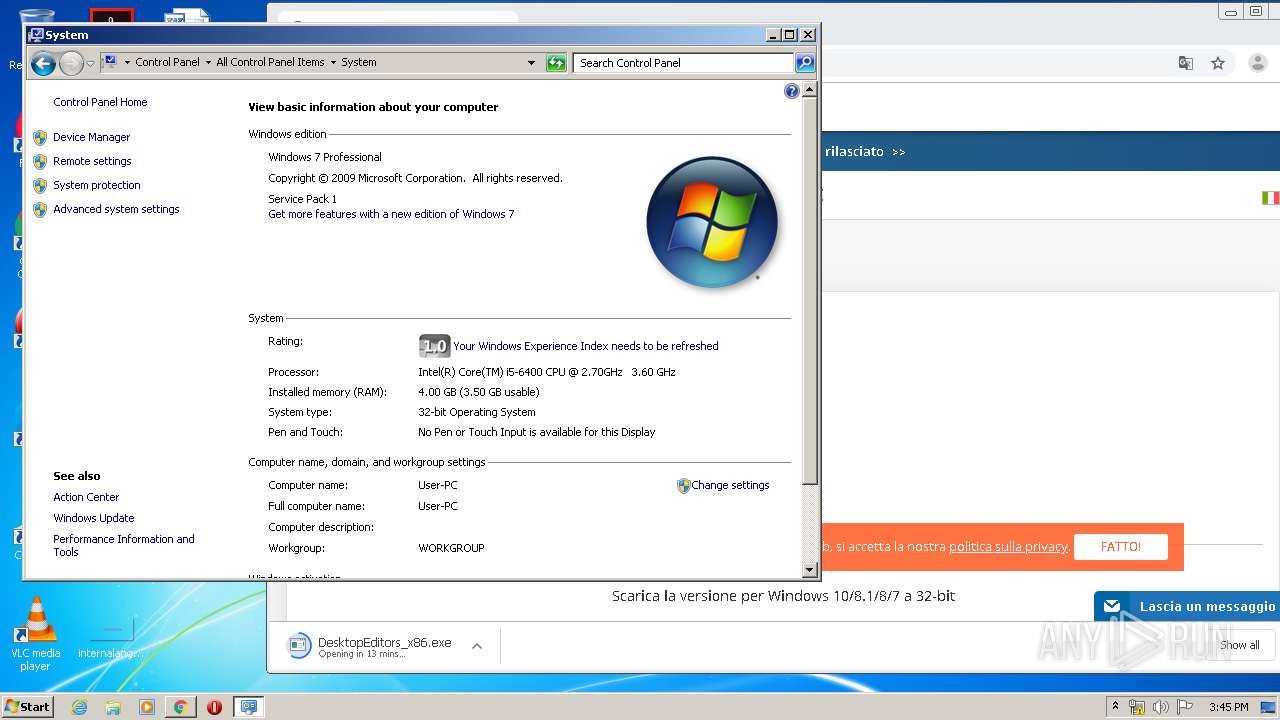
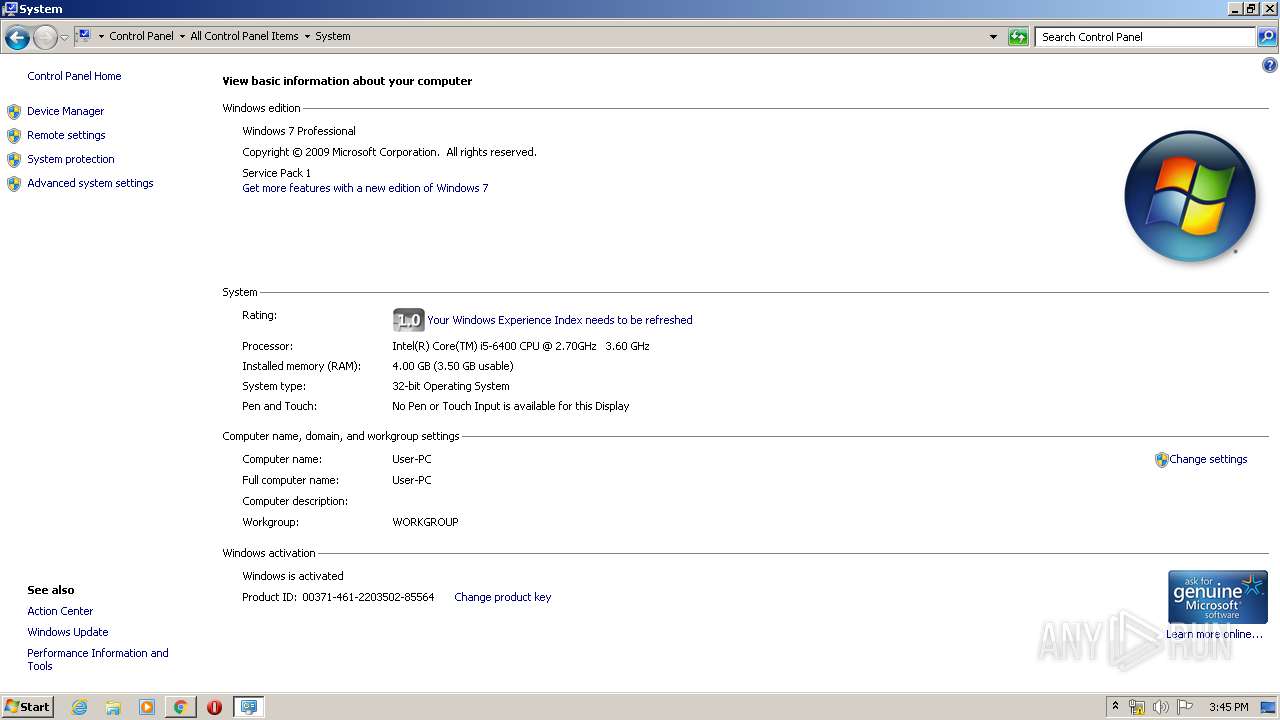
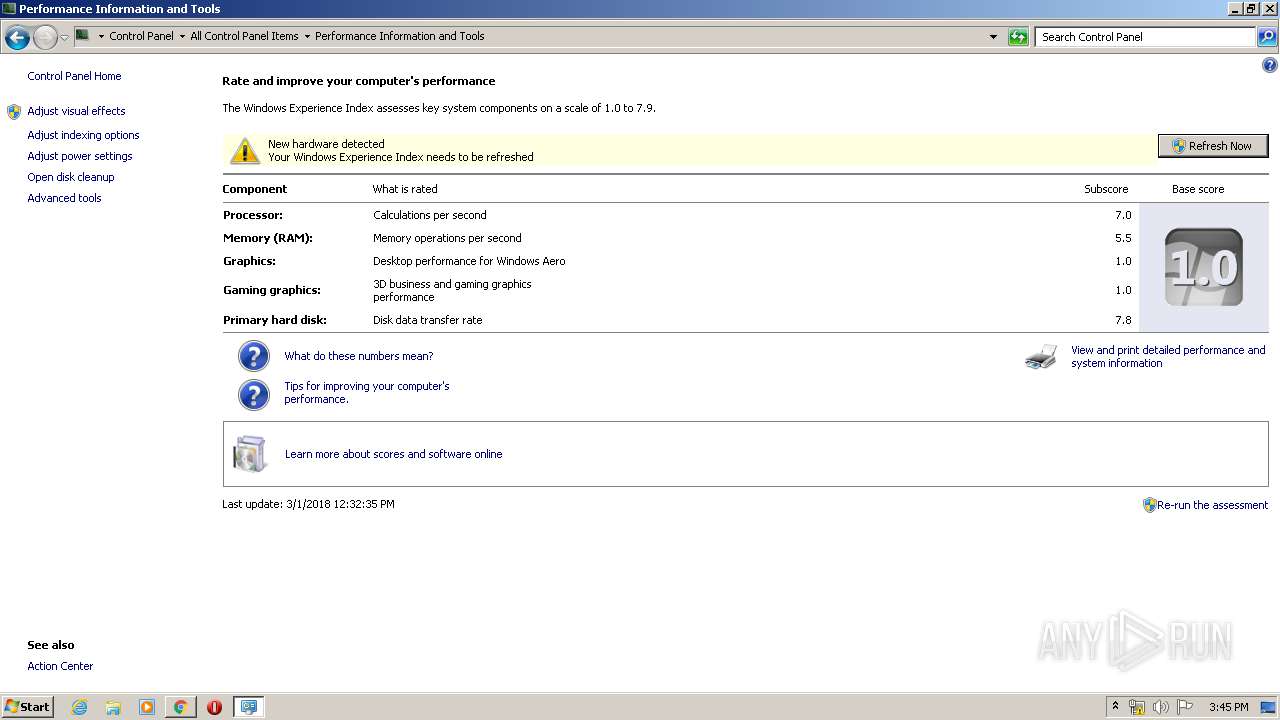
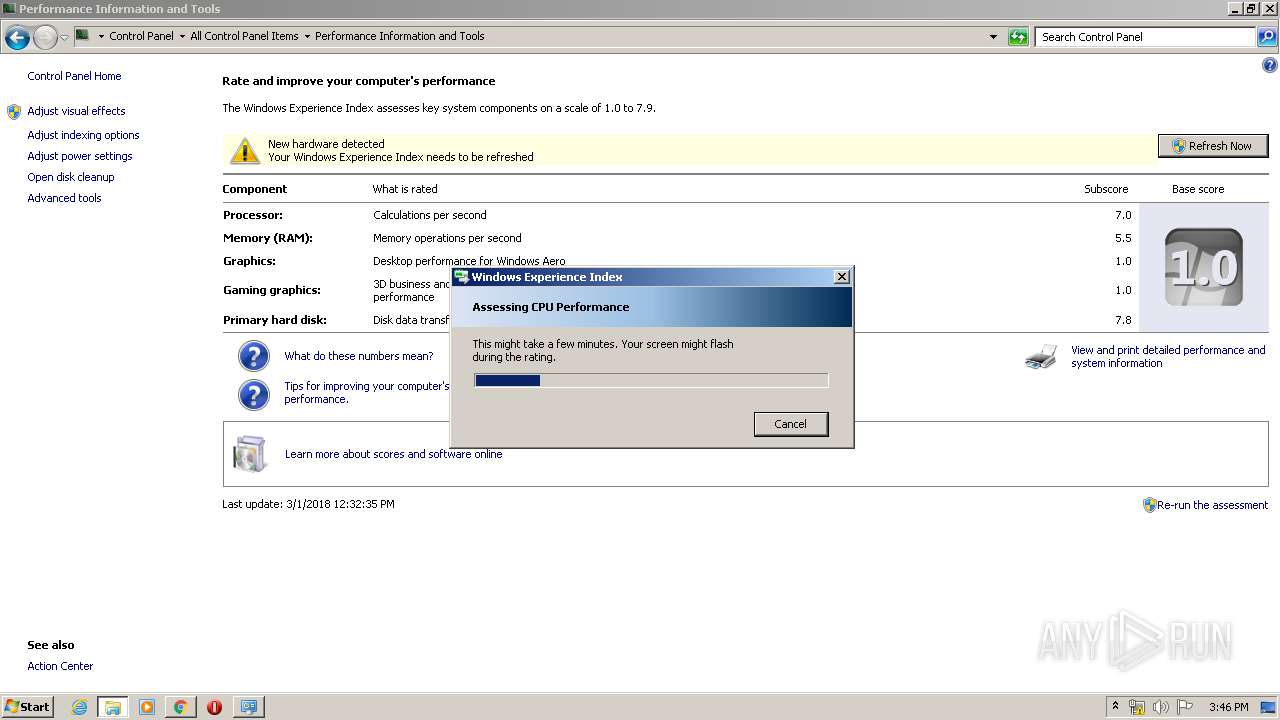
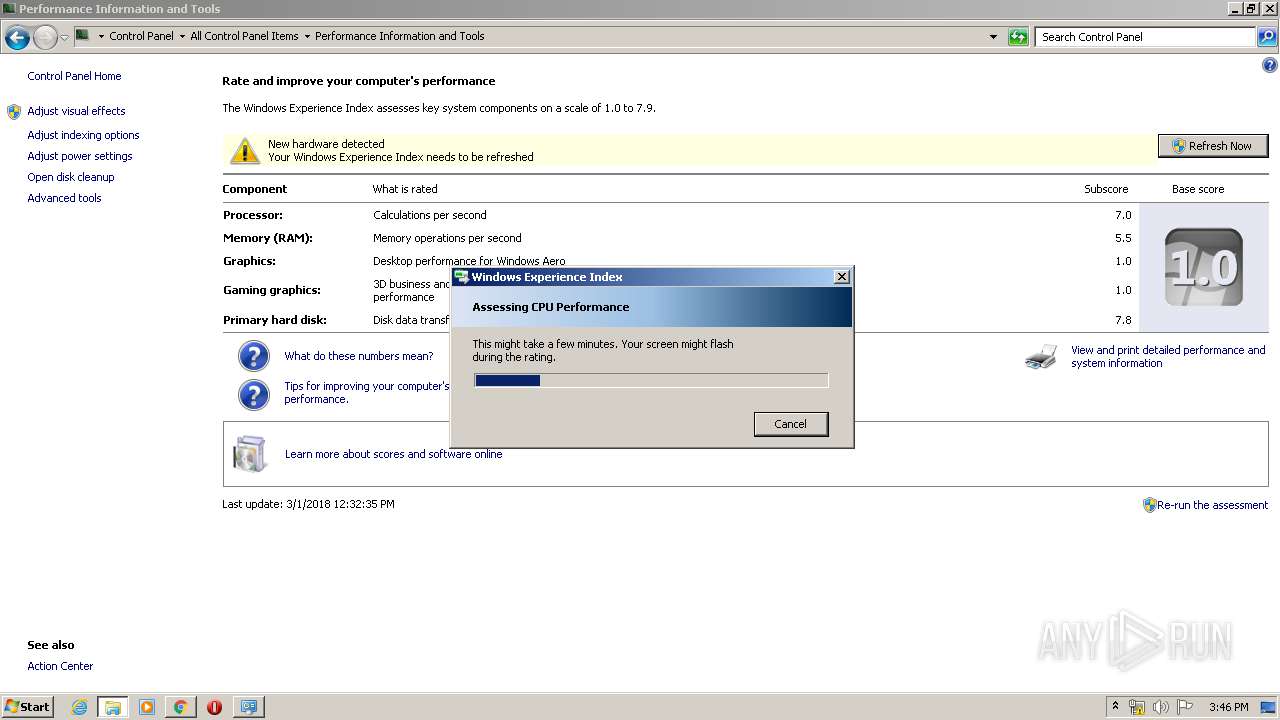
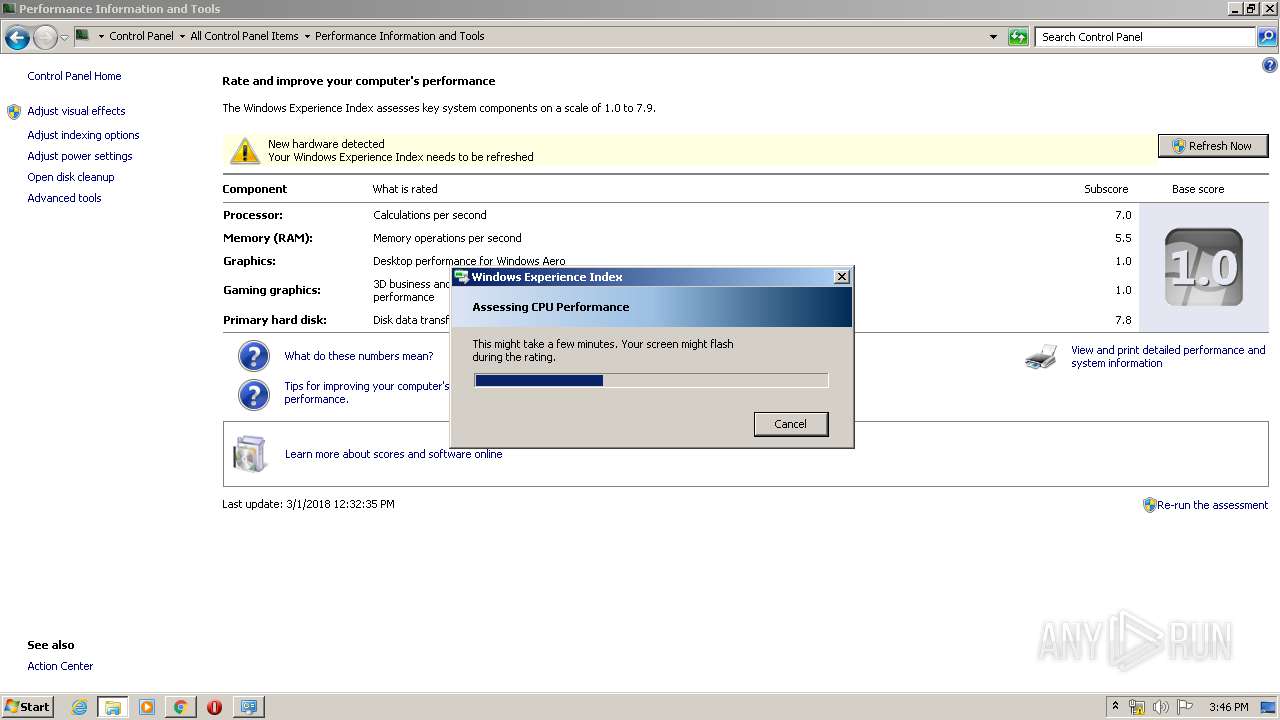
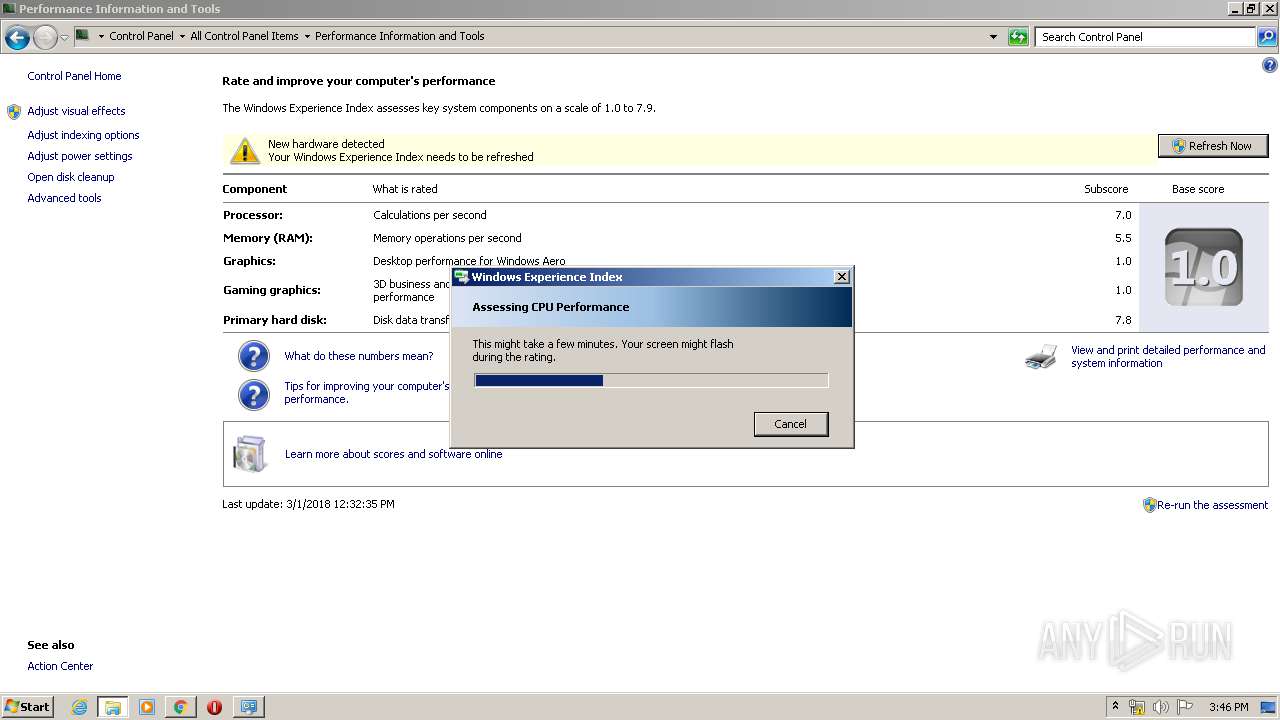
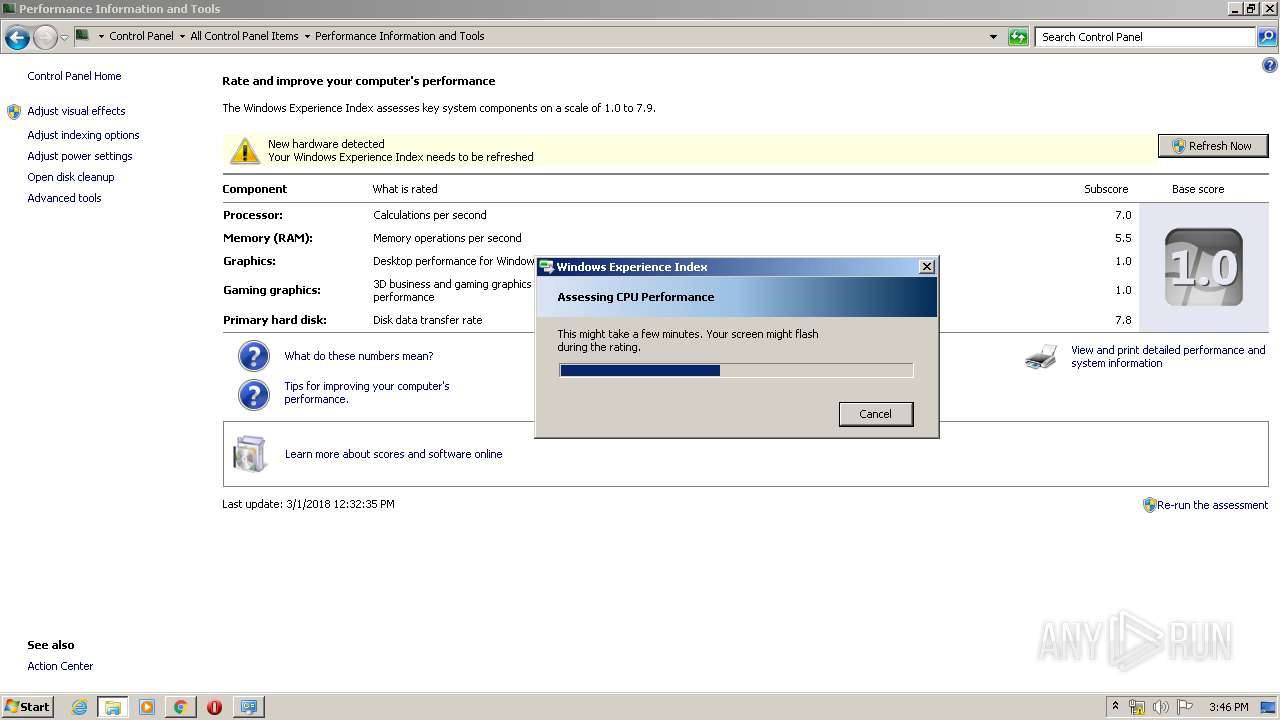
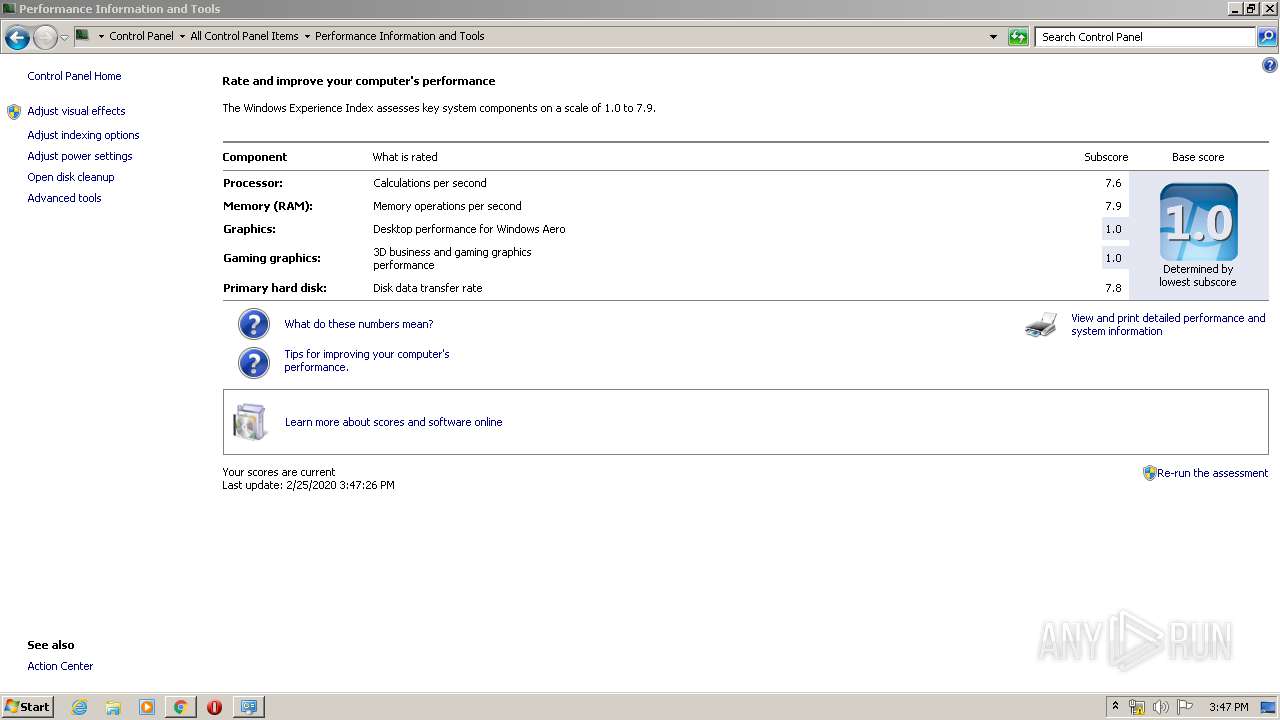
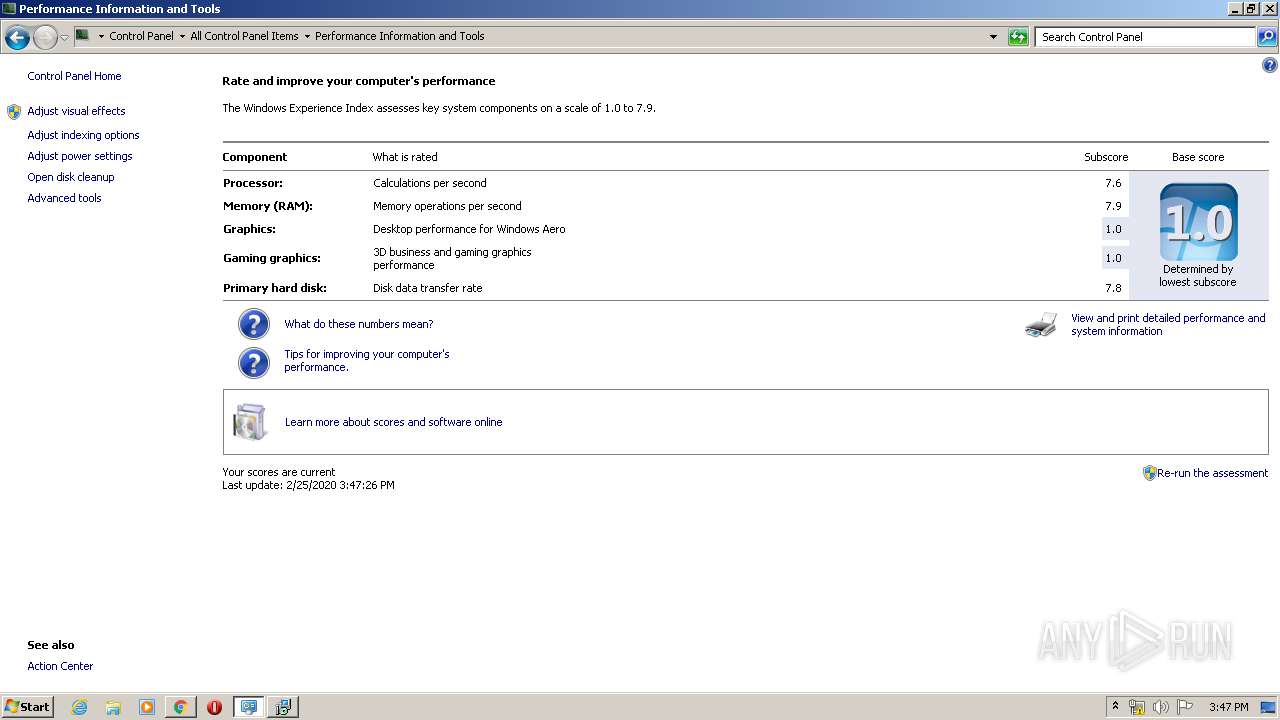
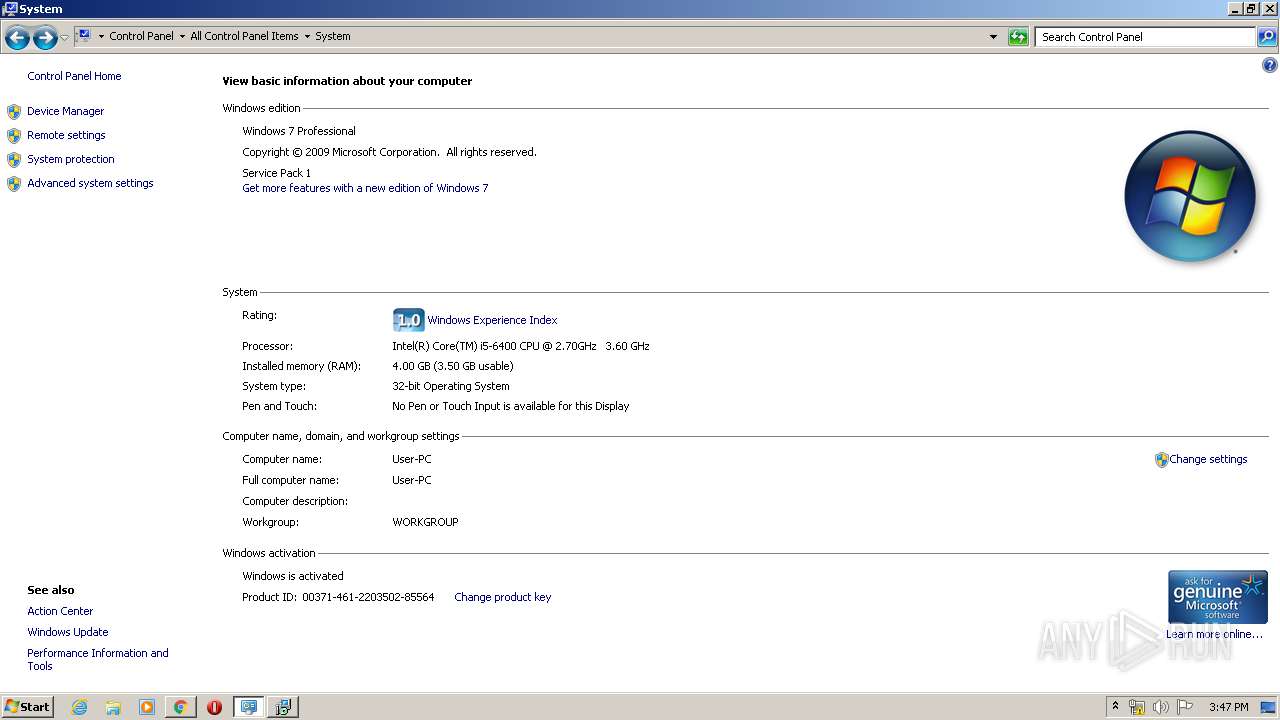
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F4CB9A267489FA0B90291FFBF8DC84F8 |
| SHA1: | A4194E9D63A0276A2855CC4080D241F289711BD5 |
| SHA256: | 10FB3C60B0BE9DD872ED0801703538E588FF4174FE076059812FCFA67F930EE2 |
| SSDEEP: | 3:N8DSLOQX+wkBAWOROL/3:2OL5+whOLf |
MALICIOUS
Changes the autorun value in the registry
- winsat.exe (PID: 2584)
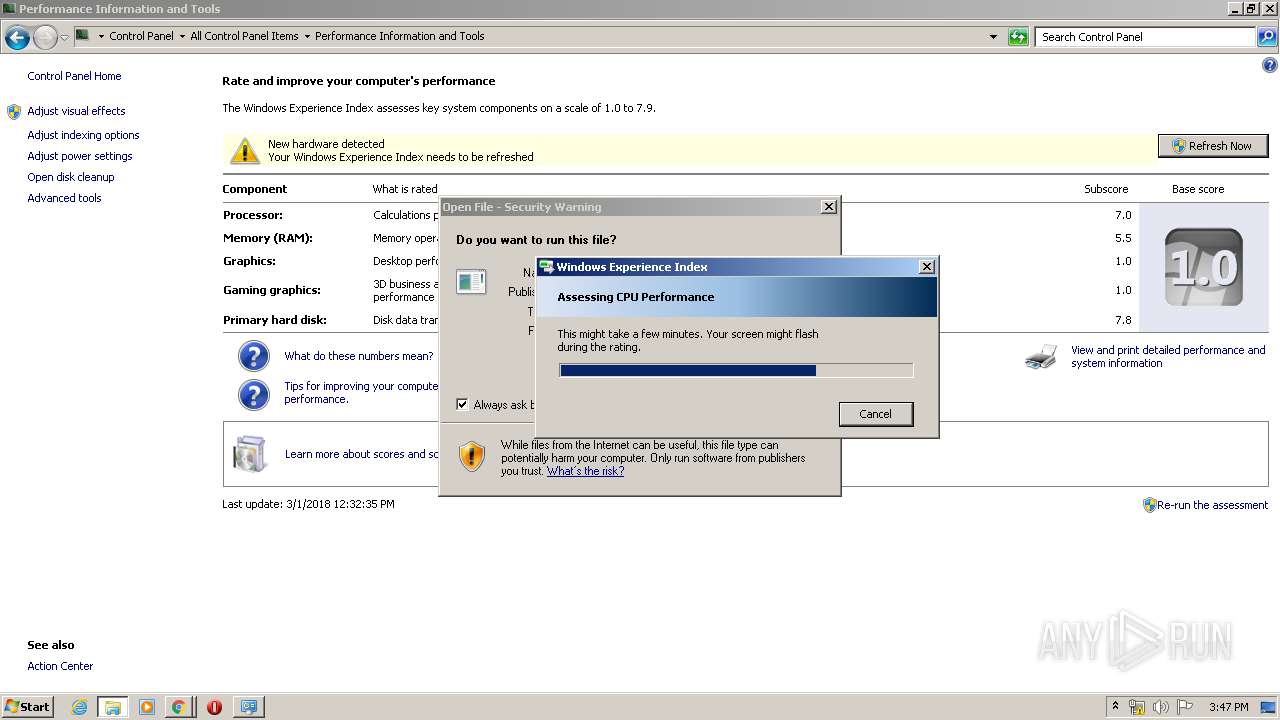
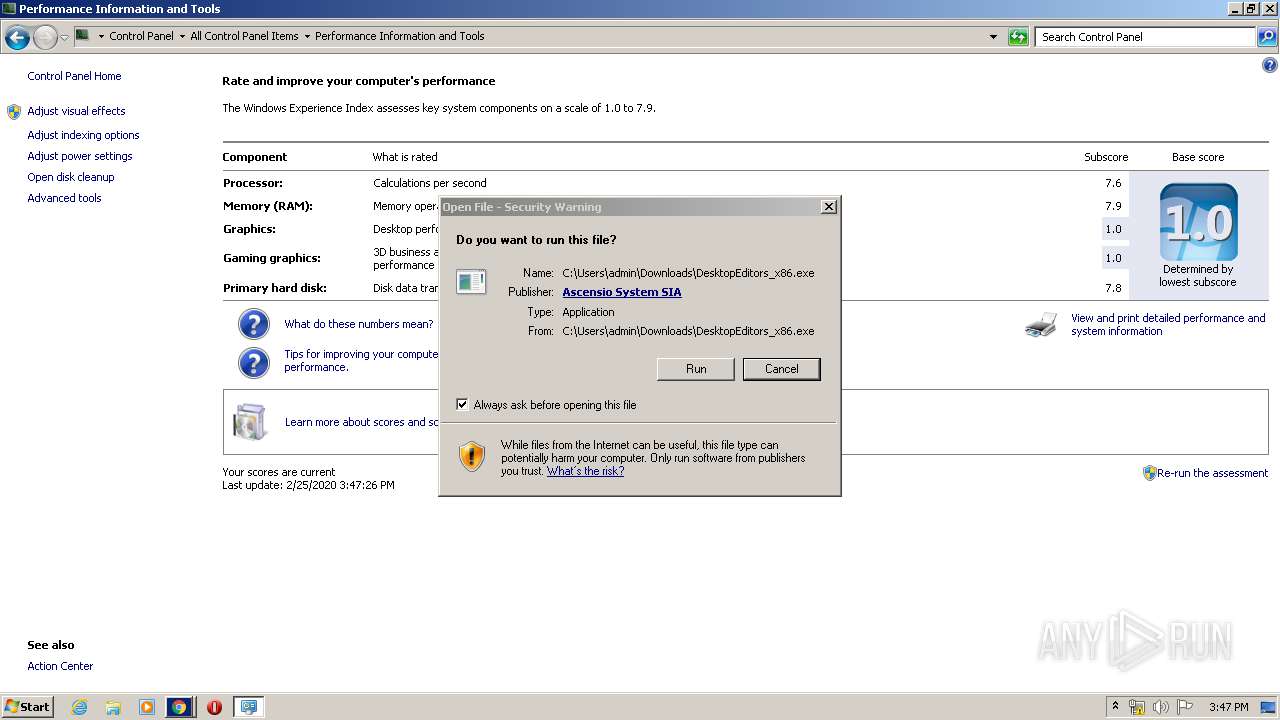
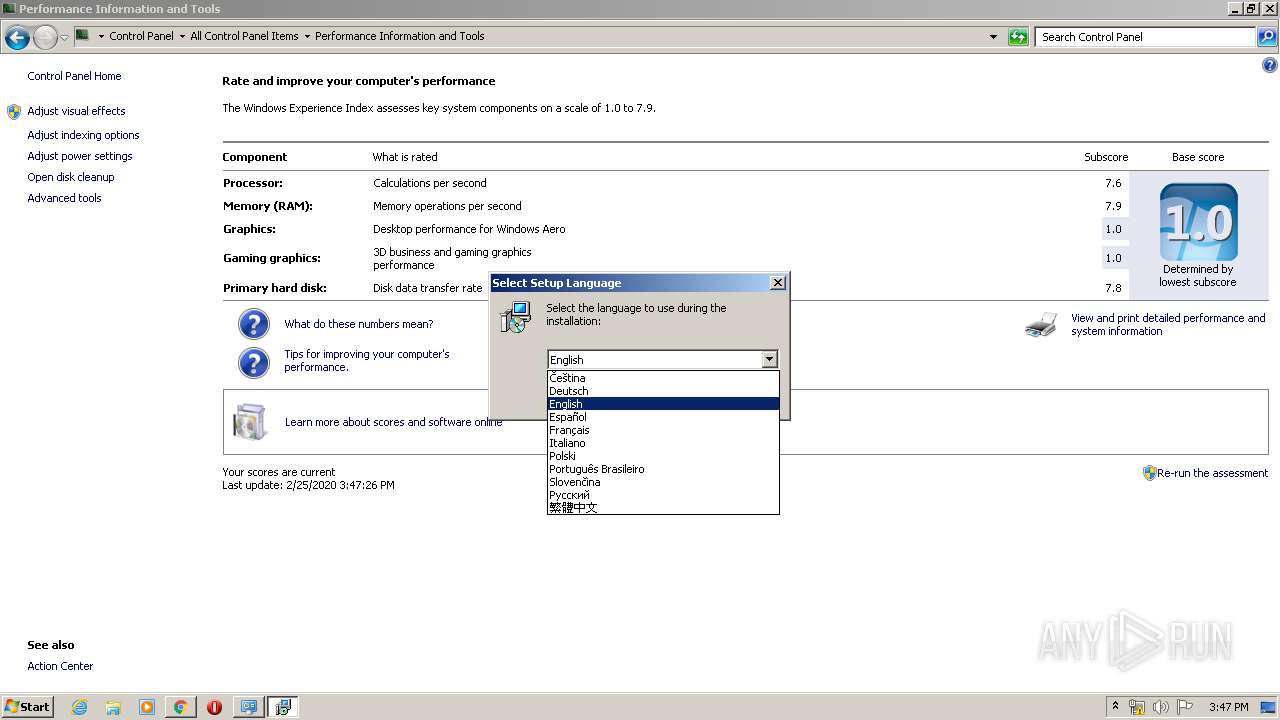
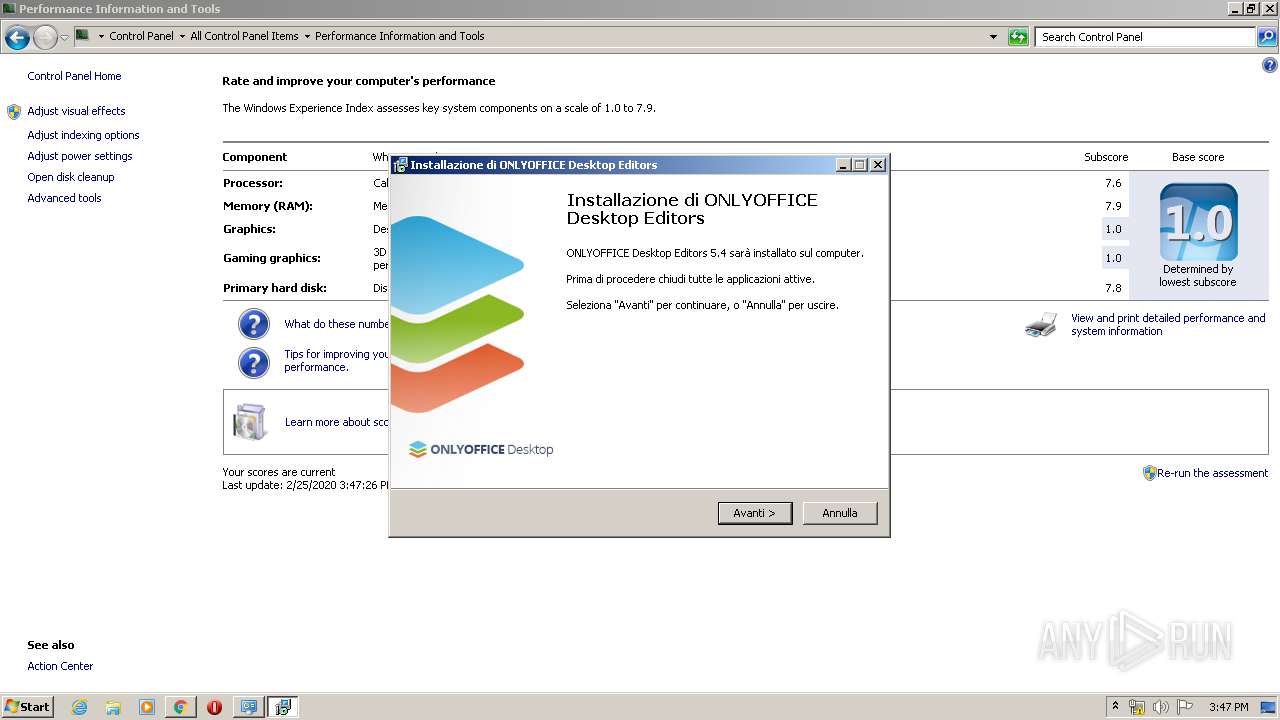
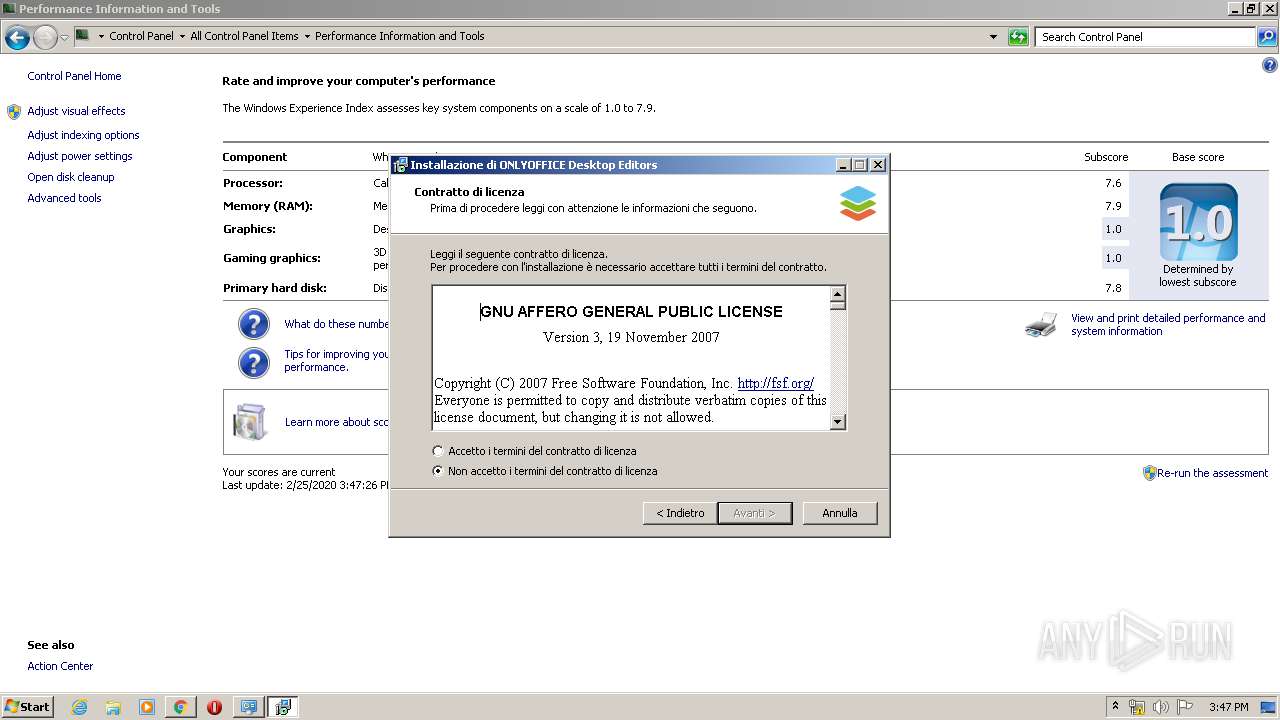
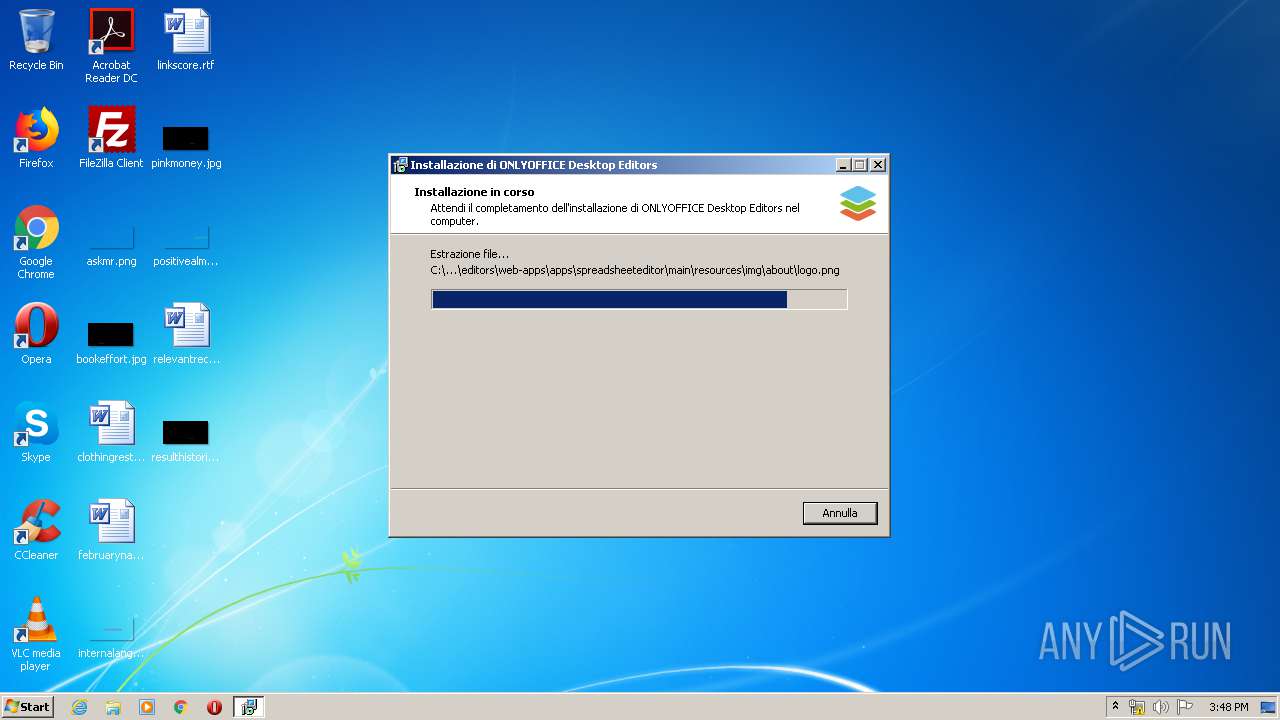
Application was dropped or rewritten from another process
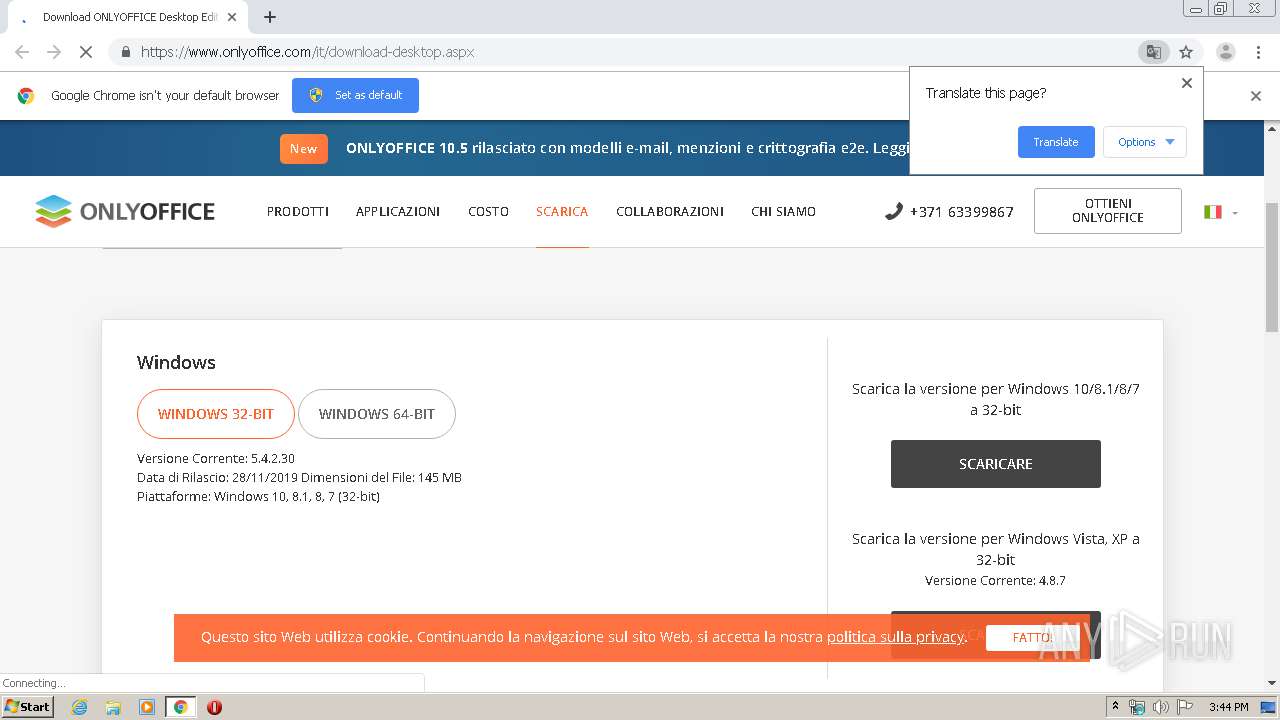
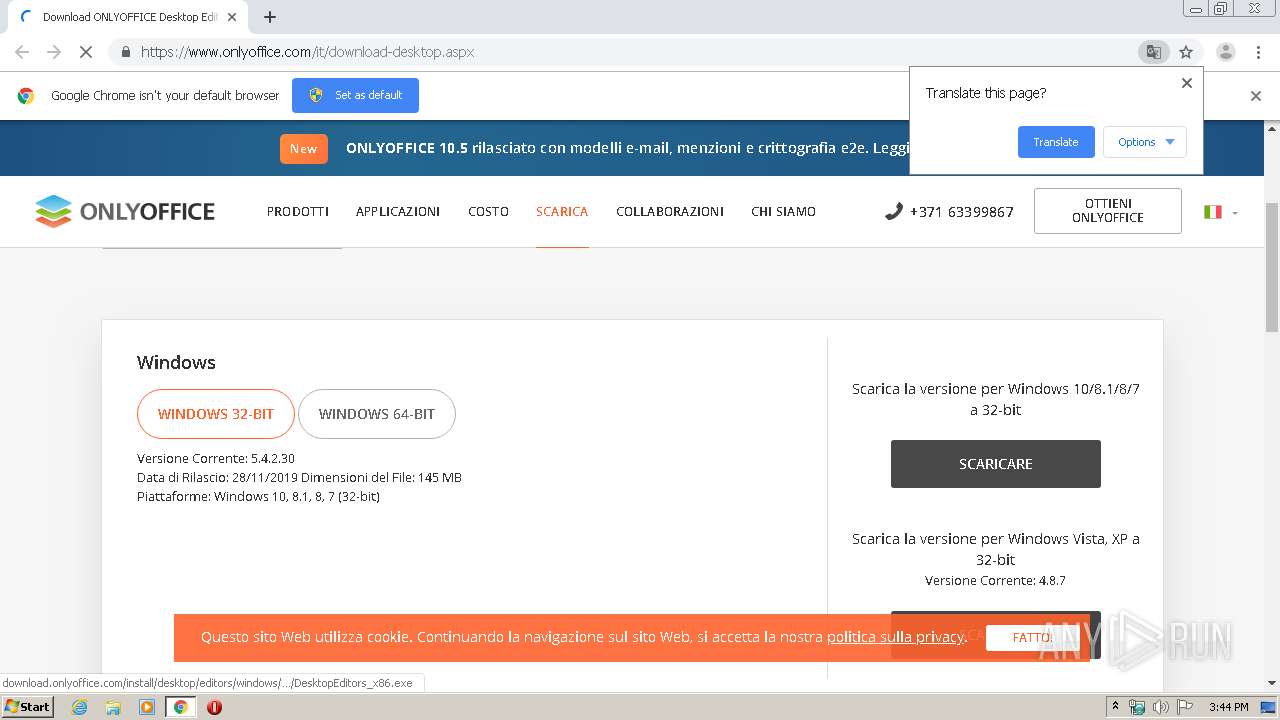
- DesktopEditors_x86.exe (PID: 3108)
- DesktopEditors_x86.exe (PID: 2608)
- DesktopEditors.exe (PID: 3820)
- editors.exe (PID: 2540)
- editors.exe (PID: 2404)
- editors.exe (PID: 2244)
- x2t.exe (PID: 3212)
- editors.exe (PID: 740)
- editors.exe (PID: 2868)
- editors.exe (PID: 2660)
- editors.exe (PID: 2432)
Loads dropped or rewritten executable
- DesktopEditors.exe (PID: 3820)
- editors.exe (PID: 2540)
- editors.exe (PID: 2404)
- x2t.exe (PID: 3212)
- editors.exe (PID: 2432)
- editors.exe (PID: 2868)
- editors.exe (PID: 740)
- editors.exe (PID: 2244)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 304)
- DesktopEditors_x86.exe (PID: 2608)
- DesktopEditors_x86.exe (PID: 3108)
- DesktopEditors_x86.tmp (PID: 3692)
Modifies files in Chrome extension folder
- chrome.exe (PID: 304)
Creates files in the Windows directory
- winsat.exe (PID: 2584)
Low-level read access rights to disk partition
- winsat.exe (PID: 2584)
Reads Windows owner or organization settings
- DesktopEditors_x86.tmp (PID: 3692)
Reads the Windows organization settings
- DesktopEditors_x86.tmp (PID: 3692)
Modifies the open verb of a shell class
- DesktopEditors_x86.tmp (PID: 3692)
Application launched itself
- editors.exe (PID: 2540)
Reads Internet Cache Settings
- editors.exe (PID: 2540)
INFO
Reads the hosts file
- chrome.exe (PID: 304)
- chrome.exe (PID: 3728)
- editors.exe (PID: 2540)
Application launched itself
- chrome.exe (PID: 304)
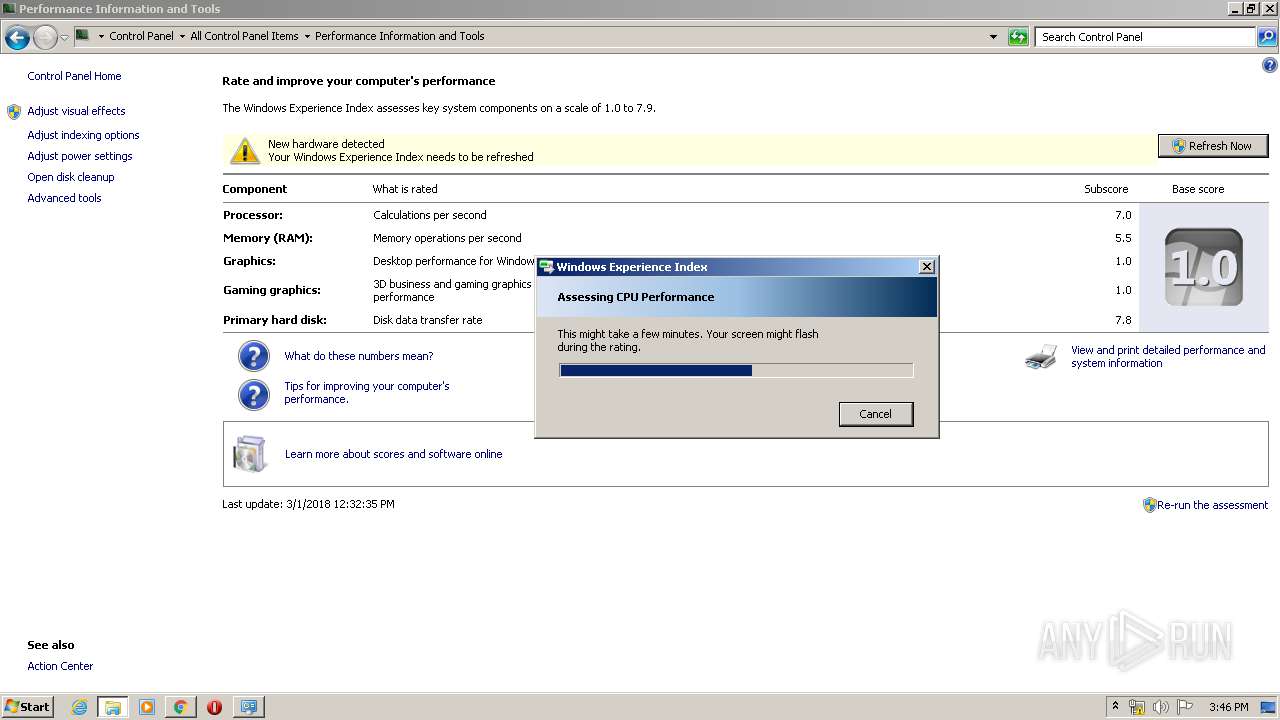
Manual execution by user
- winsat.exe (PID: 2584)
- winsat.exe (PID: 2104)
Reads settings of System Certificates
- chrome.exe (PID: 3728)
- chrome.exe (PID: 304)
- editors.exe (PID: 2540)
Application was dropped or rewritten from another process
- DesktopEditors_x86.tmp (PID: 2616)
- DesktopEditors_x86.tmp (PID: 3692)
Reads Internet Cache Settings
- chrome.exe (PID: 304)
Loads dropped or rewritten executable
- DesktopEditors_x86.tmp (PID: 3692)
Dropped object may contain Bitcoin addresses
- DesktopEditors_x86.tmp (PID: 3692)
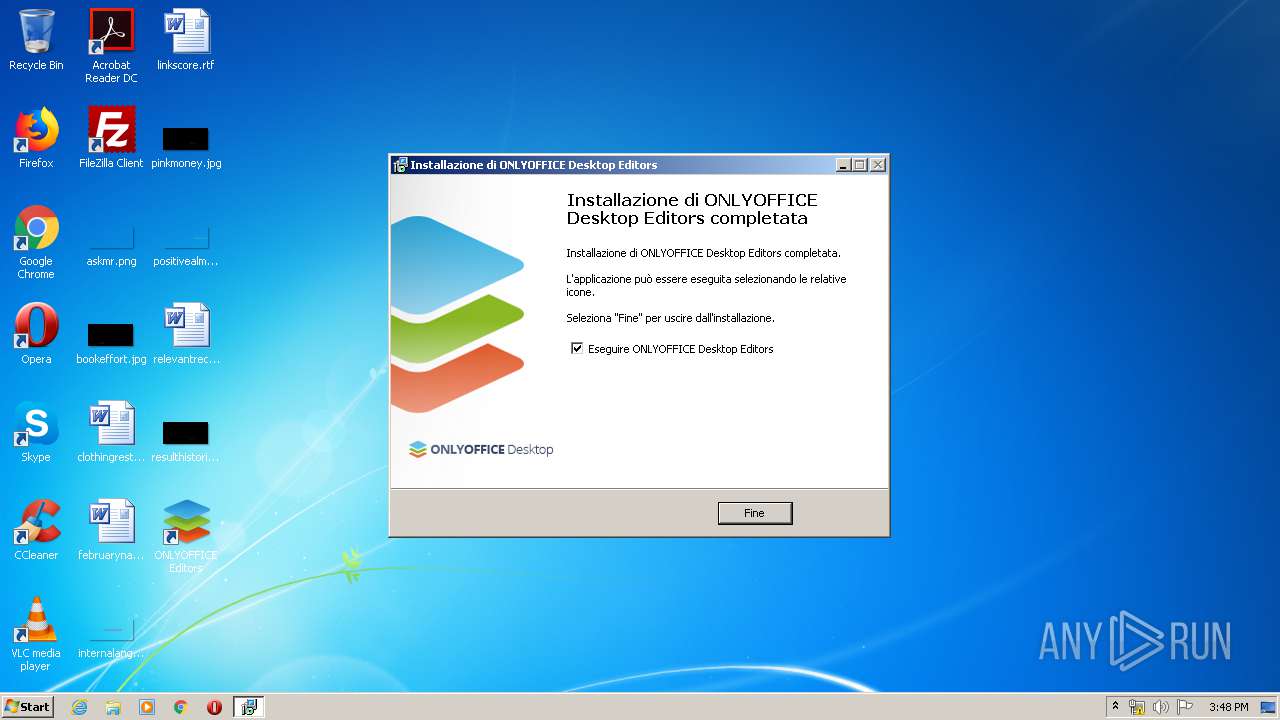
Creates a software uninstall entry
- DesktopEditors_x86.tmp (PID: 3692)
Creates files in the program directory
- DesktopEditors_x86.tmp (PID: 3692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
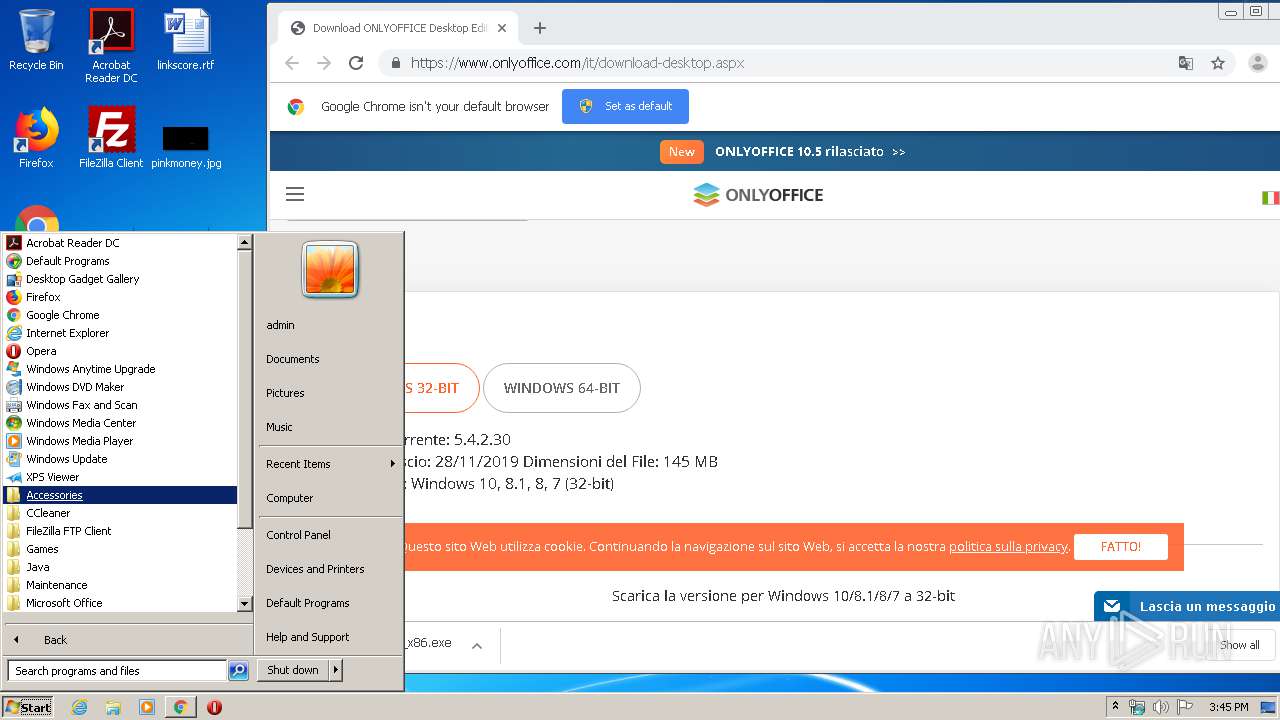
Total processes
98
Monitored processes
41
Malicious processes
14
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://www.onlyoffice.com/it/download-desktop.aspx" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=907271588682583780 --mojo-platform-channel-handle=2280 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1325947323275310015 --mojo-platform-channel-handle=4108 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 740 | "C:\Program Files\ONLYOFFICE\DesktopEditors\editors.exe" --type=gpu-process --no-sandbox --lang=en-US --log-file=C:/Users/admin/AppData/Local/ONLYOFFICE/DesktopEditors/data/cache/log.log --log-severity=disable --disable-direct-composition --use-gl=swiftshader-webgl --supports-dual-gpus=false --gpu-driver-bug-workarounds=9,12,13,22,23,24,27,49,84 --disable-gl-extensions="GL_KHR_blend_equation_advanced GL_KHR_blend_equation_advanced_coherent" --disable-accelerated-video-decode --gpu-vendor-id=0x1234 --gpu-device-id=0x1111 --gpu-driver-vendor="Google Inc." --gpu-driver-version=3.3.0.2 --gpu-driver-date=2017/04/07 --lang=en-US --log-file=C:/Users/admin/AppData/Local/ONLYOFFICE/DesktopEditors/data/cache/log.log --log-severity=disable --service-request-channel-token=93909B70D2034A3368B8C27661AB6C10 --mojo-platform-channel-handle=2872 /prefetch:2 | C:\Program Files\ONLYOFFICE\DesktopEditors\editors.exe | editors.exe | ||||||||||||
User: admin Company: Ascensio System SIA Integrity Level: MEDIUM Description: ONLYOFFICE Desktop Editors Exit code: 3221226356 Version: 5.4.2.30 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8546147189581177235 --mojo-platform-channel-handle=3424 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14871919487870142545 --mojo-platform-channel-handle=3924 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16996387677484310301 --mojo-platform-channel-handle=3964 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3378257711193470507 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4188272847977923909 --mojo-platform-channel-handle=3428 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Windows\system32\winsat.exe" formal -cancelevent 253b35a9-c1d4-4cd1-9d09-7461db95a1f8 | C:\Windows\system32\winsat.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows System Assessment Tool Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 834
Read events
1 547
Write events
275
Delete events
12
Modification events
| (PID) Process: | (2108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 304-13227119069771375 |
Value: 259 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (304) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
58
Suspicious files
173
Text files
11 057
Unknown types
45
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E5540DE-130.pma | — | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d945441e-3b85-4b03-91f2-211a72d648d8.tmp | — | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66bf1.TMP | text | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa66c2f.TMP | text | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66d87.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
60
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2540 | editors.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
3728 | chrome.exe | GET | 200 | 74.125.104.87:80 | http://r1---sn-4g5ednle.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=92.118.13.11&mm=28&mn=sn-4g5ednle&ms=nvh&mt=1582645394&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3728 | chrome.exe | GET | 200 | 173.194.188.73:80 | http://r4---sn-4g5ednsl.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=92.118.13.11&mm=28&mn=sn-4g5ednsl&ms=nvh&mt=1582645394&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2540 | editors.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
2540 | editors.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQC%2B2ZhCn6Nr%2FQ%3D%3D | US | der | 1.74 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3728 | chrome.exe | 54.186.188.62:443 | www.onlyoffice.com | Amazon.com, Inc. | US | unknown |
3728 | chrome.exe | 216.58.207.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3728 | chrome.exe | 216.58.207.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3728 | chrome.exe | 172.217.22.72:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3728 | chrome.exe | 104.16.83.55:443 | v2.zopim.com | Cloudflare Inc | US | shared |
3728 | chrome.exe | 216.58.206.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3728 | chrome.exe | 143.204.202.56:443 | static-www.onlyoffice.com | — | US | malicious |
3728 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3728 | chrome.exe | 172.217.21.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3728 | chrome.exe | 172.217.18.2:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.onlyoffice.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
static-www.onlyoffice.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
v2.zopim.com |
| whitelisted |
static.zdassets.com |
| whitelisted |
Threats
Process | Message |
|---|---|
editors.exe | WinSparkle: *** USING INSECURE URL: releasŊ |
editors.exe | WinSparkle: ----------------------------
|
editors.exe | WinSparkle: ----------------------------
|
editors.exe | WinSparkle: ----------------------------
|
editors.exe | WinSparkle: *** USING INSECURE URL: update file from http://download.onlyoffice.com/install/desktop/editors/windows/onlyoffice/updates/editors_update_x86.exe ***
|
editors.exe | WinSparkle: *** USING INSECURE URL: release notes from http://download.onlyoffice.com/install/desktop/editors/windows/onlyoffice/changes/changes.html ***
|