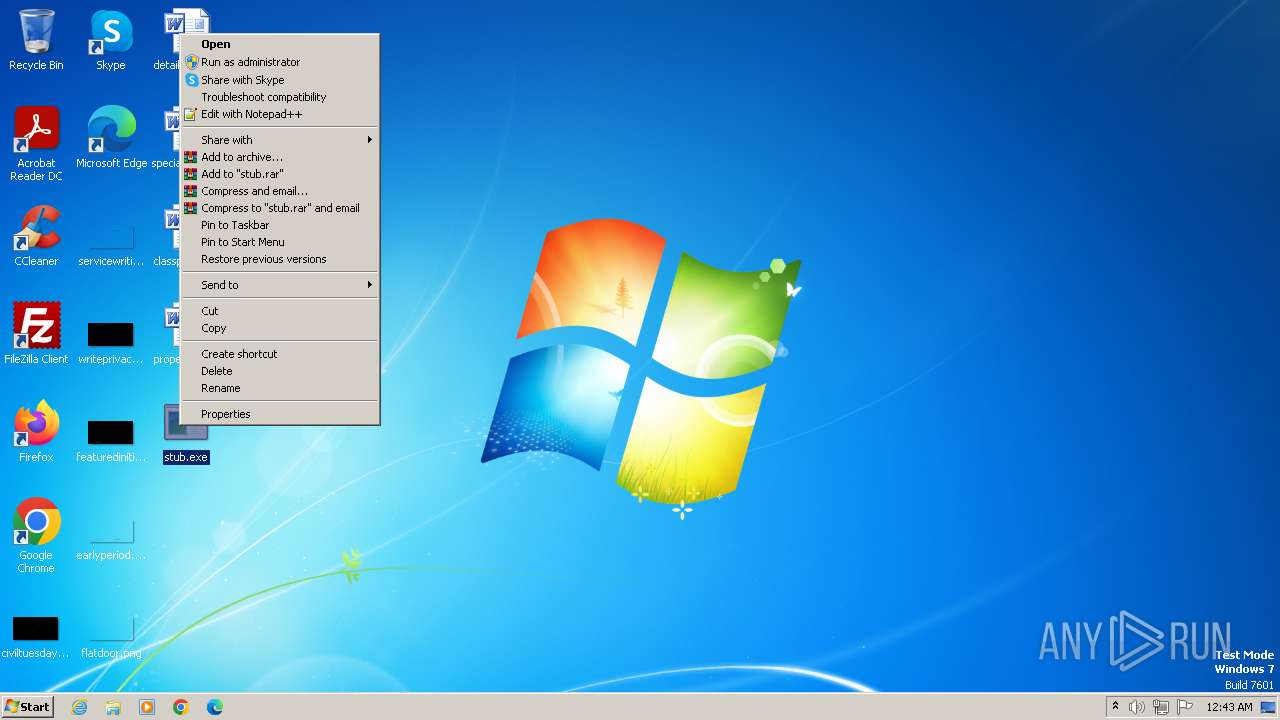
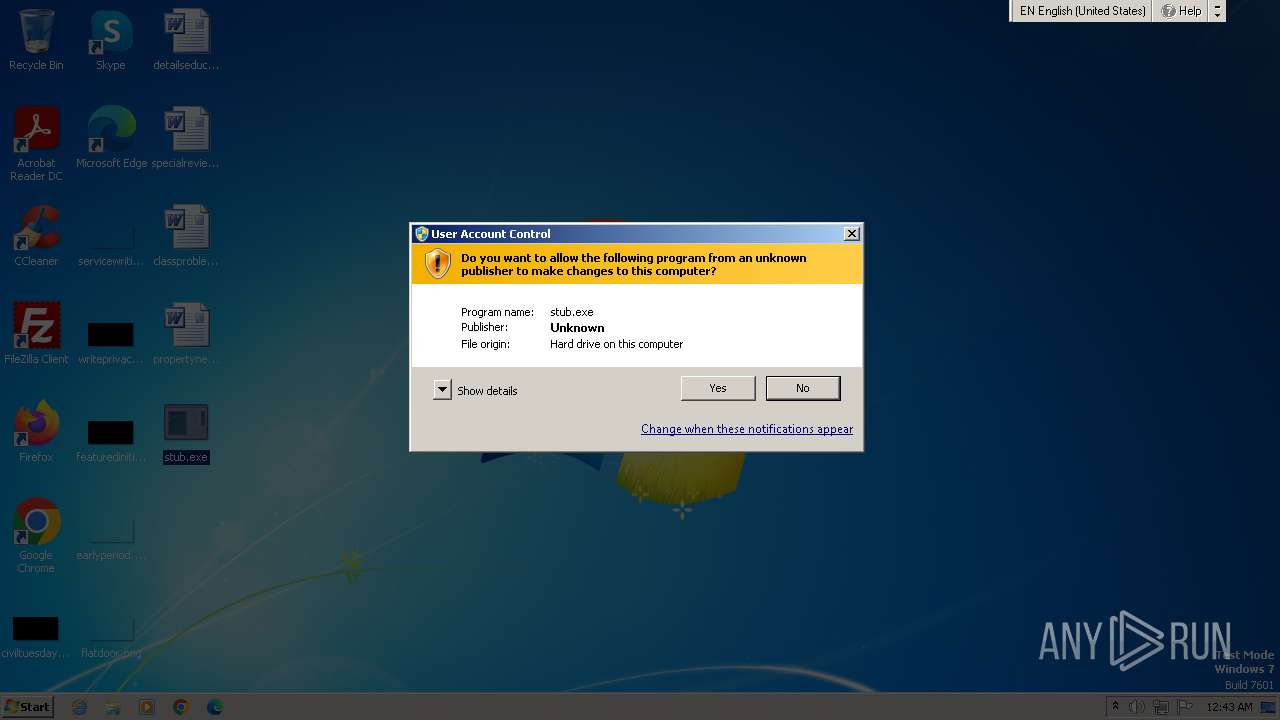
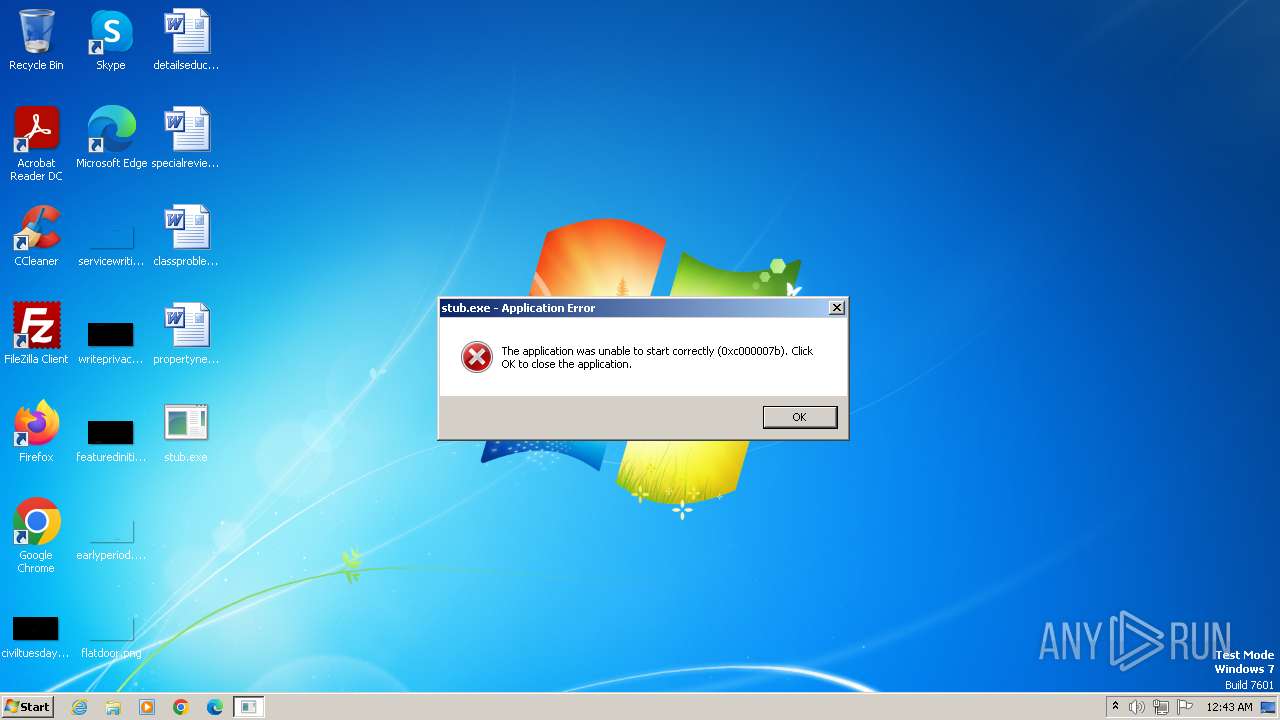
| File name: | stub.exe |
| Full analysis: | https://app.any.run/tasks/f8c10dc1-d916-48dc-84eb-70421572e09f |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2023, 00:42:51 |
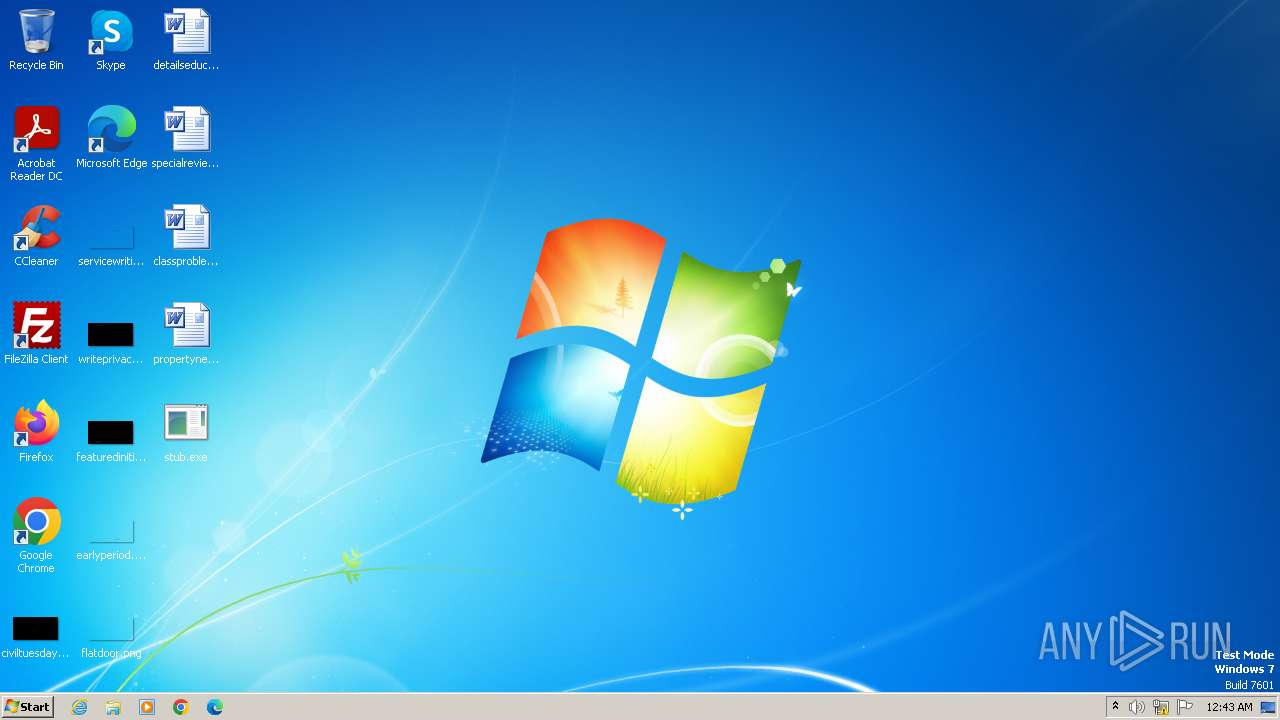
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A298857AD0F136BBACB3497EDA96827D |
| SHA1: | F47E3269A7D36D04C9A10A5B02A77D2E00FB00D2 |
| SHA256: | 10E81816AFB5AA0F02C9AB37286E31005849745CDB2E3F63FEF6FA35E3743A52 |
| SSDEEP: | 6144:99fakdS5+4S2BLx9gOQClzC3KL1qroYbt1c6HEcoUUc6HcT66vlmU4lzC3KL1WtG:95ak05g279gRJMYbkcoUrkcoUU |
MALICIOUS
Drops the executable file immediately after the start
- stub.exe (PID: 2464)
- stub.exe (PID: 1696)
- stub.exe (PID: 3108)
Actions looks like stealing of personal data
- stub.exe (PID: 2464)
SUSPICIOUS
Reads the Internet Settings
- stub.exe (PID: 2464)
- stub.exe (PID: 1696)
- stub.exe (PID: 1380)
- stub.exe (PID: 2696)
- stub.exe (PID: 3916)
The process creates files with name similar to system file names
- stub.exe (PID: 3108)
Process drops legitimate windows executable
- stub.exe (PID: 3108)
Starts itself from another location
- stub.exe (PID: 1380)
- svchost.com (PID: 3632)
- stub.exe (PID: 3916)
- stub.exe (PID: 2696)
Executes as Windows Service
- svchost.exe (PID: 2984)
Starts application with an unusual extension
- stub.exe (PID: 1380)
- stub.exe (PID: 3916)
- stub.exe (PID: 2696)
INFO
Create files in a temporary directory
- stub.exe (PID: 2464)
- stub.exe (PID: 1696)
Checks supported languages
- stub.exe (PID: 2464)
- stub.exe (PID: 2632)
- wmpnscfg.exe (PID: 2928)
- stub.exe (PID: 1696)
- stub.exe (PID: 3108)
- svchost.exe (PID: 3996)
- stub.exe (PID: 1380)
- svchost.exe (PID: 2984)
- svchost.com (PID: 3044)
- stub.exe (PID: 3316)
- svchost.exe (PID: 3312)
- stub.exe (PID: 2696)
- stub.exe (PID: 3916)
- svchost.com (PID: 1004)
- stub.exe (PID: 3052)
- svchost.com (PID: 3632)
Reads the computer name
- stub.exe (PID: 2464)
- wmpnscfg.exe (PID: 2928)
- stub.exe (PID: 1696)
- svchost.exe (PID: 3996)
- stub.exe (PID: 1380)
- svchost.exe (PID: 2984)
- stub.exe (PID: 3916)
- stub.exe (PID: 2696)
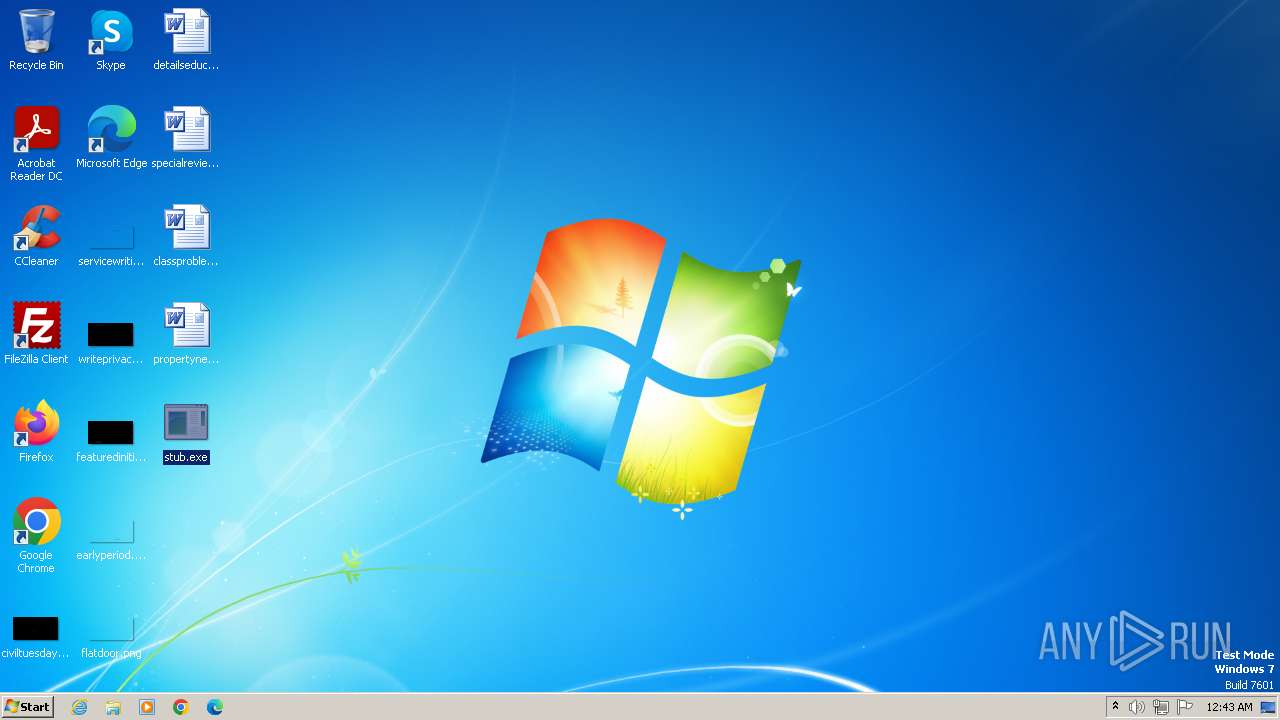
Manual execution by a user
- wmpnscfg.exe (PID: 2928)
- stub.exe (PID: 1696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 6 (75.3) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (11.9) |
| .exe | | | Win32 Executable Delphi generic (4) |
| .scr | | | Windows screen saver (3.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 29696 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x80e4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
55
Monitored processes
16
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1004 | "C:\Windows\svchost.com" "C:\Users\admin\AppData\Local\Temp\3582-490\stub.exe" | C:\Windows\svchost.com | — | stub.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1380 | "C:\Users\admin\AppData\Local\Temp\3582-490\stub.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\stub.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1696 | "C:\Users\admin\Desktop\stub.exe" | C:\Users\admin\Desktop\stub.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2464 | "C:\Users\admin\Desktop\stub.exe" | C:\Users\admin\Desktop\stub.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2632 | "C:\Users\admin\AppData\Local\Temp\3582-490\stub.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\stub.exe | — | stub.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2696 | "C:\Users\admin\AppData\Local\Temp\3582-490\stub.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\stub.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2928 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2984 | C:\Windows\svchost.exe | C:\Windows\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Generic Host Process for Win32 Services Exit code: 0 Version: 5.1.0.0 Modules
| |||||||||||||||
| 3044 | "C:\Windows\svchost.com" "C:\Users\admin\AppData\Local\Temp\3582-490\stub.exe" | C:\Windows\svchost.com | — | stub.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3052 | C:\Users\admin\AppData\Local\Temp\3582-490\stub.exe | C:\Users\admin\AppData\Local\Temp\3582-490\stub.exe | — | svchost.com | |||||||||||
User: admin Company: Microsoft Corporation. Integrity Level: HIGH Description: Windows Update Assistant Exit code: 3221225595 Version: 10.0.17134.1 Modules
| |||||||||||||||
Total events
3 567
Read events
3 527
Write events
40
Delete events
0
Modification events
| (PID) Process: | (2464) stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2464) stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2464) stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2464) stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1696) stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1696) stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1696) stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1696) stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1380) stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1380) stub.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
46
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2464 | stub.exe | C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\setup.exe | executable | |
MD5:566ED4F62FDC96F175AFEDD811FA0370 | SHA256:E17CD94C08FC0E001A49F43A0801CEA4625FB9AEE211B6DFEBEBEC446C21F460 | |||
| 2464 | stub.exe | C:\MSOCache\All Users\{90140000-006E-0407-0000-0000000FF1CE}-C\dwtrig20.exe | executable | |
MD5:CF6C595D3E5E9667667AF096762FD9C4 | SHA256:593E60CC30AE0789448547195AF77F550387F6648D45847EA244DD0DD7ABF03D | |||
| 2464 | stub.exe | C:\MSOCache\All Users\{90140000-006E-040C-0000-0000000FF1CE}-C\dwtrig20.exe | executable | |
MD5:CF6C595D3E5E9667667AF096762FD9C4 | SHA256:593E60CC30AE0789448547195AF77F550387F6648D45847EA244DD0DD7ABF03D | |||
| 2464 | stub.exe | C:\MSOCache\All Users\{90140000-006E-0410-0000-0000000FF1CE}-C\dwtrig20.exe | executable | |
MD5:CF6C595D3E5E9667667AF096762FD9C4 | SHA256:593E60CC30AE0789448547195AF77F550387F6648D45847EA244DD0DD7ABF03D | |||
| 2464 | stub.exe | C:\MSOCache\All Users\{90140000-006E-040C-0000-0000000FF1CE}-C\DW20.EXE | executable | |
MD5:02EE6A3424782531461FB2F10713D3C1 | SHA256:EAD58C483CB20BCD57464F8A4929079539D634F469B213054BF737D227C026DC | |||
| 2464 | stub.exe | C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\ose.exe | executable | |
MD5:58B58875A50A0D8B5E7BE7D6AC685164 | SHA256:2A0AA0763FDEF9C38C5DD4D50703F0C7E27F4903C139804EC75E55F8388139AE | |||
| 2464 | stub.exe | C:\MSOCache\All Users\{90140000-006E-0411-0000-0000000FF1CE}-C\dwtrig20.exe | executable | |
MD5:CF6C595D3E5E9667667AF096762FD9C4 | SHA256:593E60CC30AE0789448547195AF77F550387F6648D45847EA244DD0DD7ABF03D | |||
| 2464 | stub.exe | C:\MSOCache\All Users\{90140000-006E-0407-0000-0000000FF1CE}-C\DW20.EXE | executable | |
MD5:02EE6A3424782531461FB2F10713D3C1 | SHA256:EAD58C483CB20BCD57464F8A4929079539D634F469B213054BF737D227C026DC | |||
| 2464 | stub.exe | C:\MSOCache\All Users\{90140000-006E-0412-0000-0000000FF1CE}-C\DW20.EXE | executable | |
MD5:02EE6A3424782531461FB2F10713D3C1 | SHA256:EAD58C483CB20BCD57464F8A4929079539D634F469B213054BF737D227C026DC | |||
| 2464 | stub.exe | C:\MSOCache\All Users\{90140000-006E-0410-0000-0000000FF1CE}-C\DW20.EXE | executable | |
MD5:02EE6A3424782531461FB2F10713D3C1 | SHA256:EAD58C483CB20BCD57464F8A4929079539D634F469B213054BF737D227C026DC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
868 | svchost.exe | 23.35.228.137:80 | — | AKAMAI-AS | DE | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
868 | svchost.exe | 95.101.148.135:80 | armmf.adobe.com | Akamai International B.V. | NL | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
armmf.adobe.com |
| whitelisted |