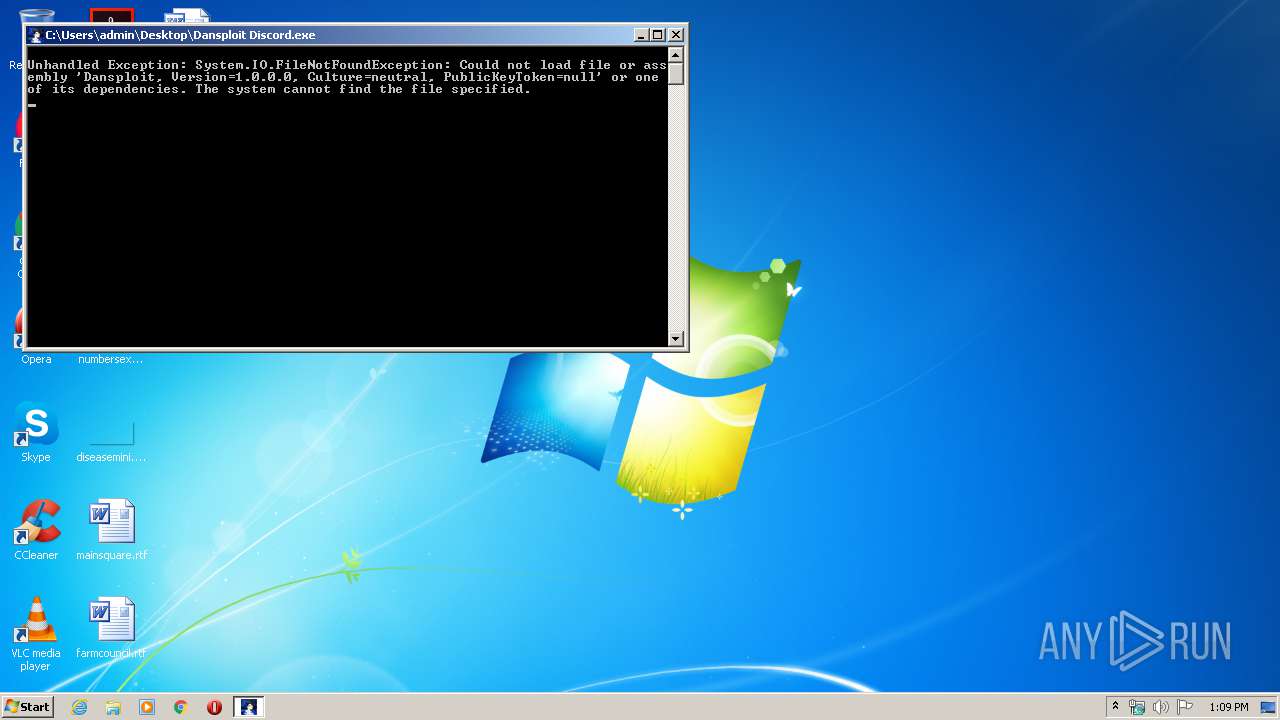
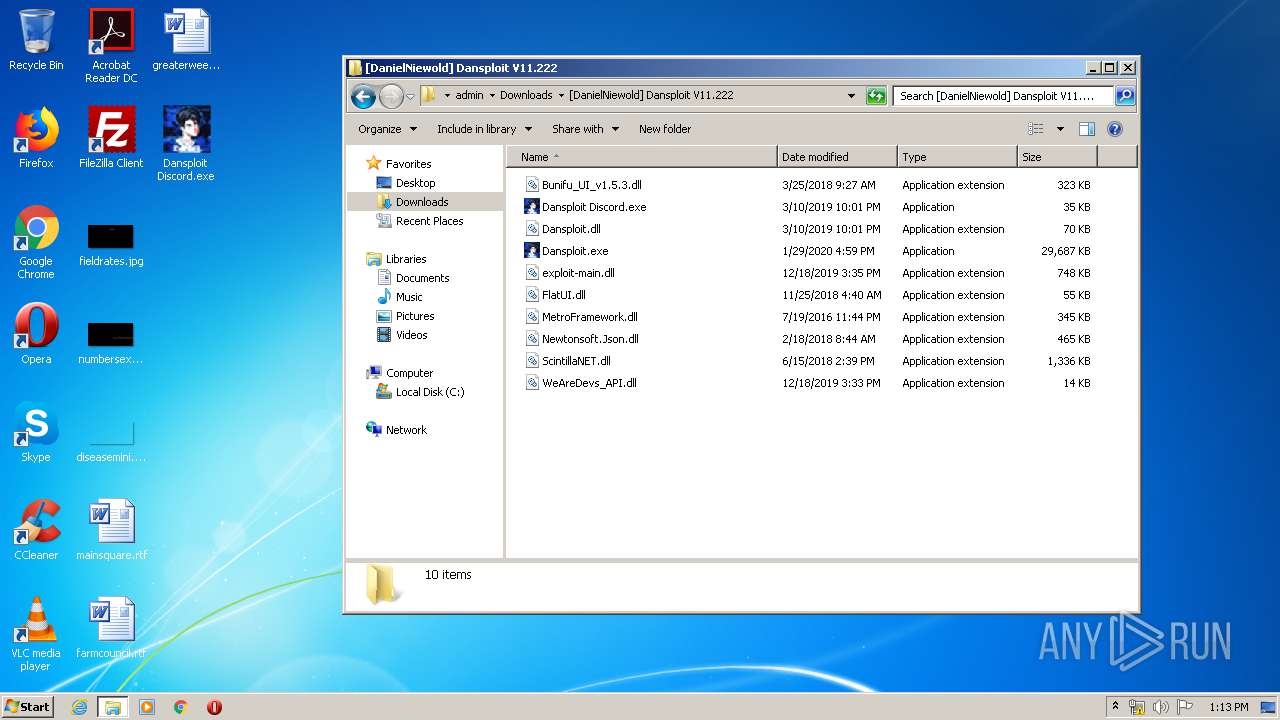
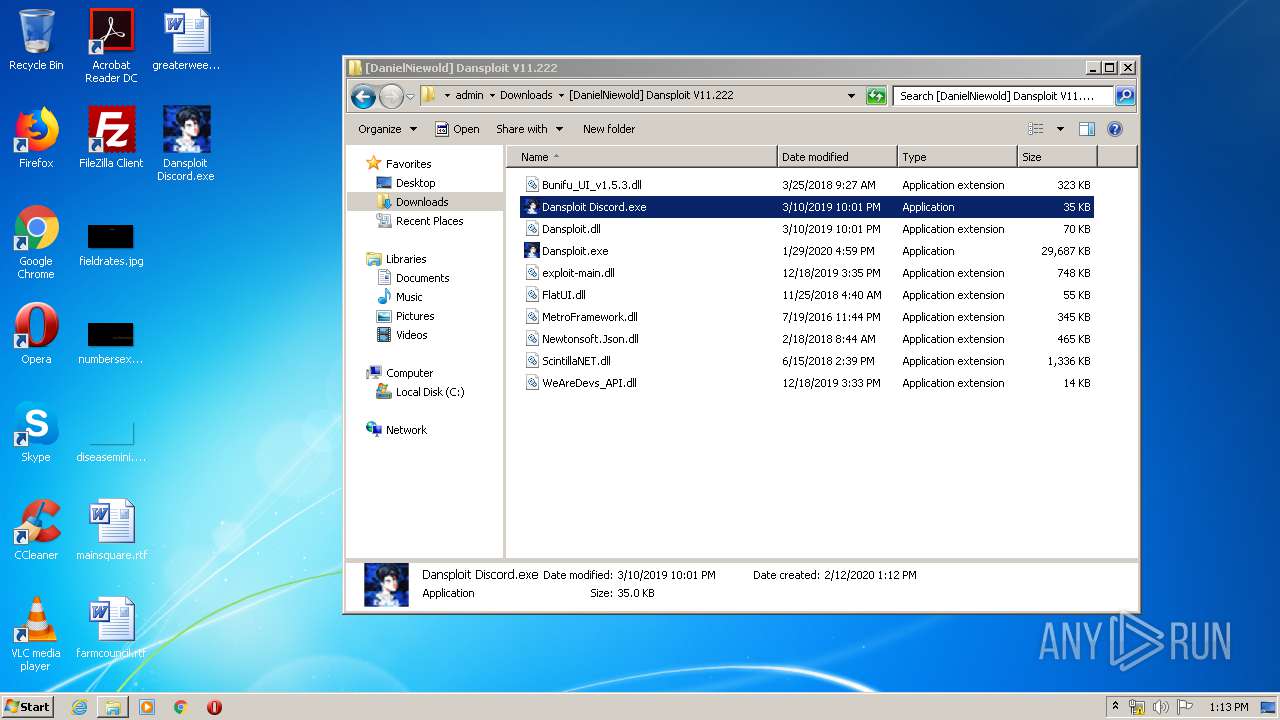
| File name: | Dansploit Discord.exe |
| Full analysis: | https://app.any.run/tasks/71303586-1920-4299-a10f-f9d15311254e |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2020, 13:09:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | A500AB916F3158FCCEB39F5DA0738A38 |
| SHA1: | 94C762BC924FC9B8B1A48EA74FE9BD1316037469 |
| SHA256: | 10E6826D6A48683BF1EB7255ED70BBA698E5074B84BEC6F0AB094830AB1128BD |
| SSDEEP: | 768:cQwqi91MmppM/w0rBfLnexTy6I2W2r0SV3niYKcpml:pwLd36BTeE6x0SV3dKSml |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3080)
- Dansploit.exe (PID: 2780)
- Dansploit Discord.exe (PID: 2388)
Application was dropped or rewritten from another process
- Dansploit.exe (PID: 2780)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3536)
Modifies the open verb of a shell class
- Dansploit Discord.exe (PID: 2388)
INFO
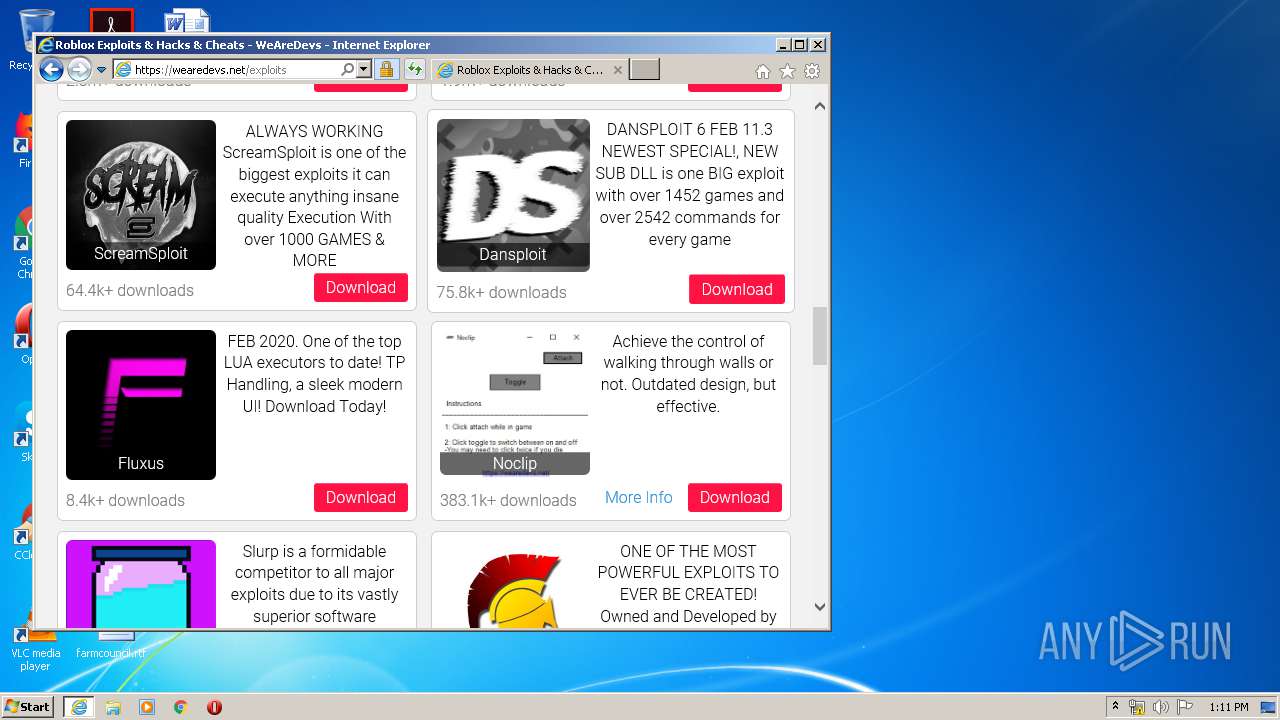
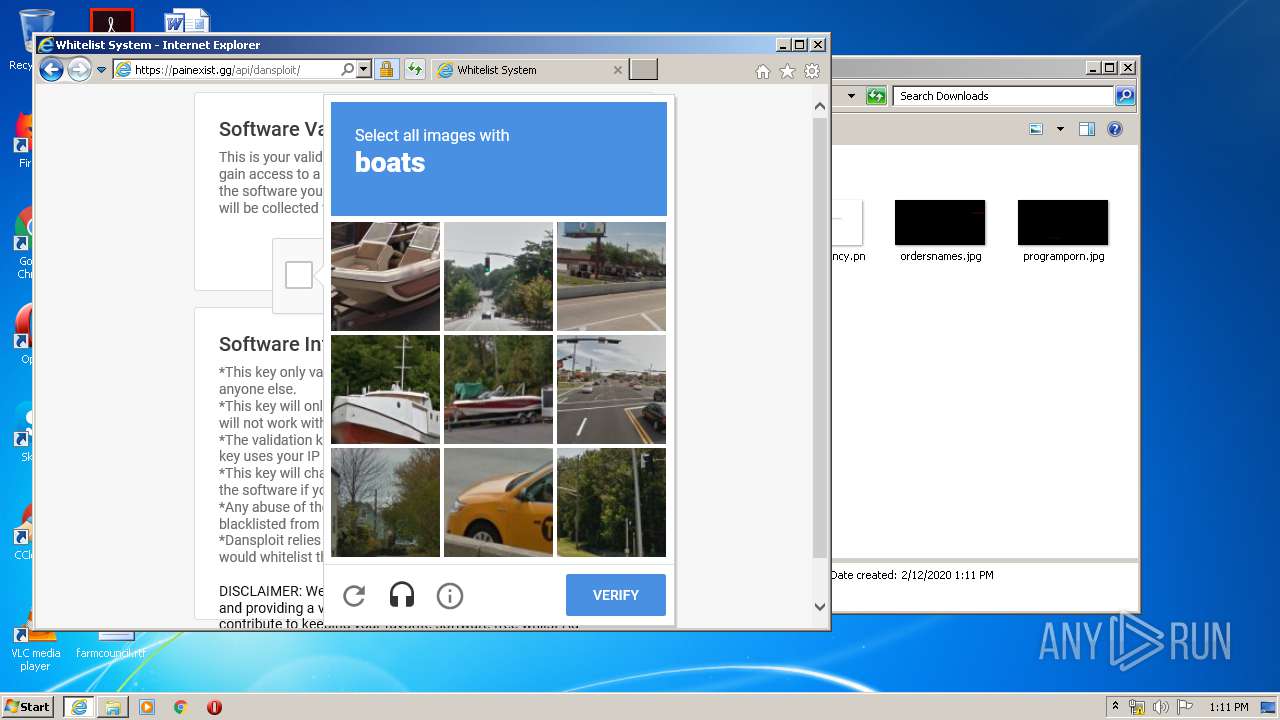
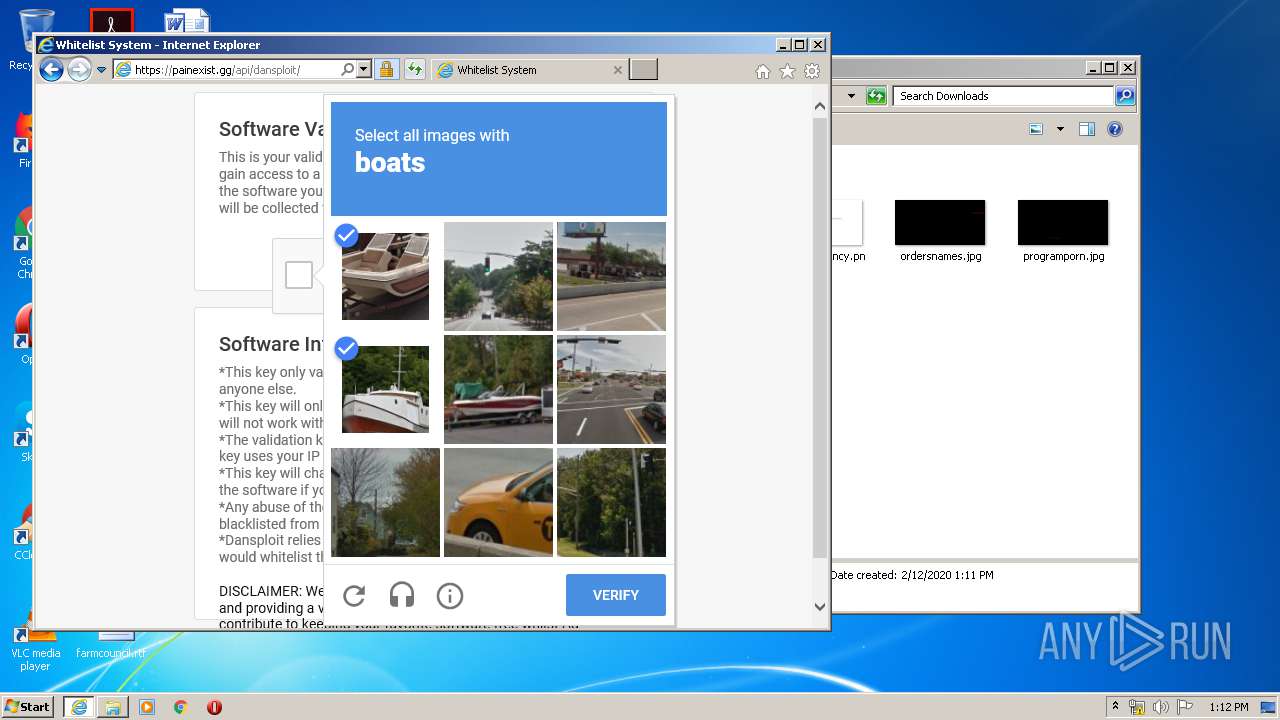
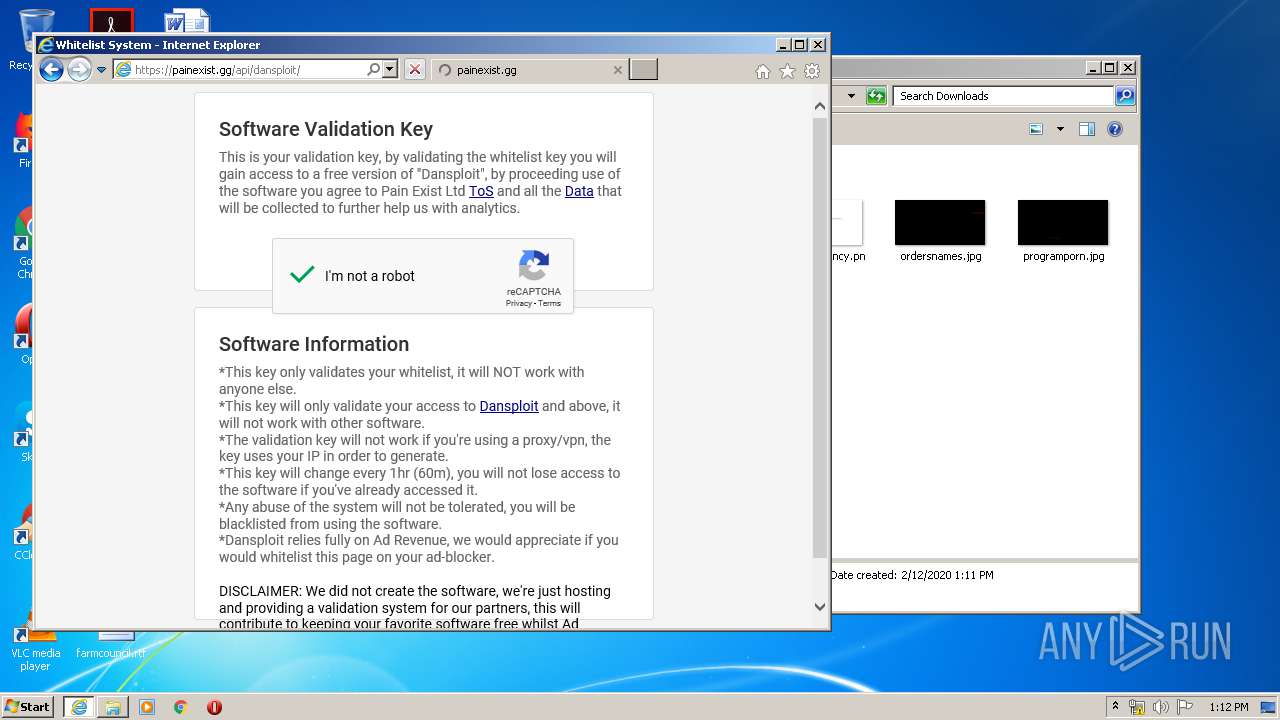
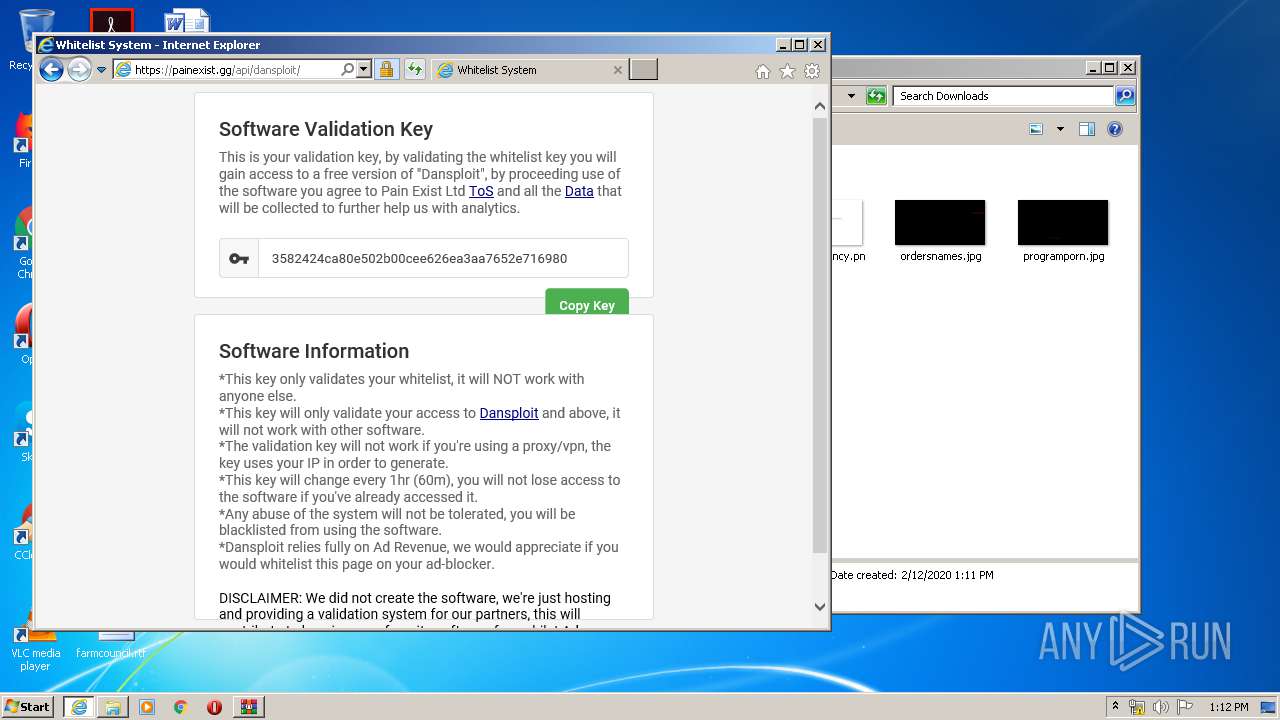
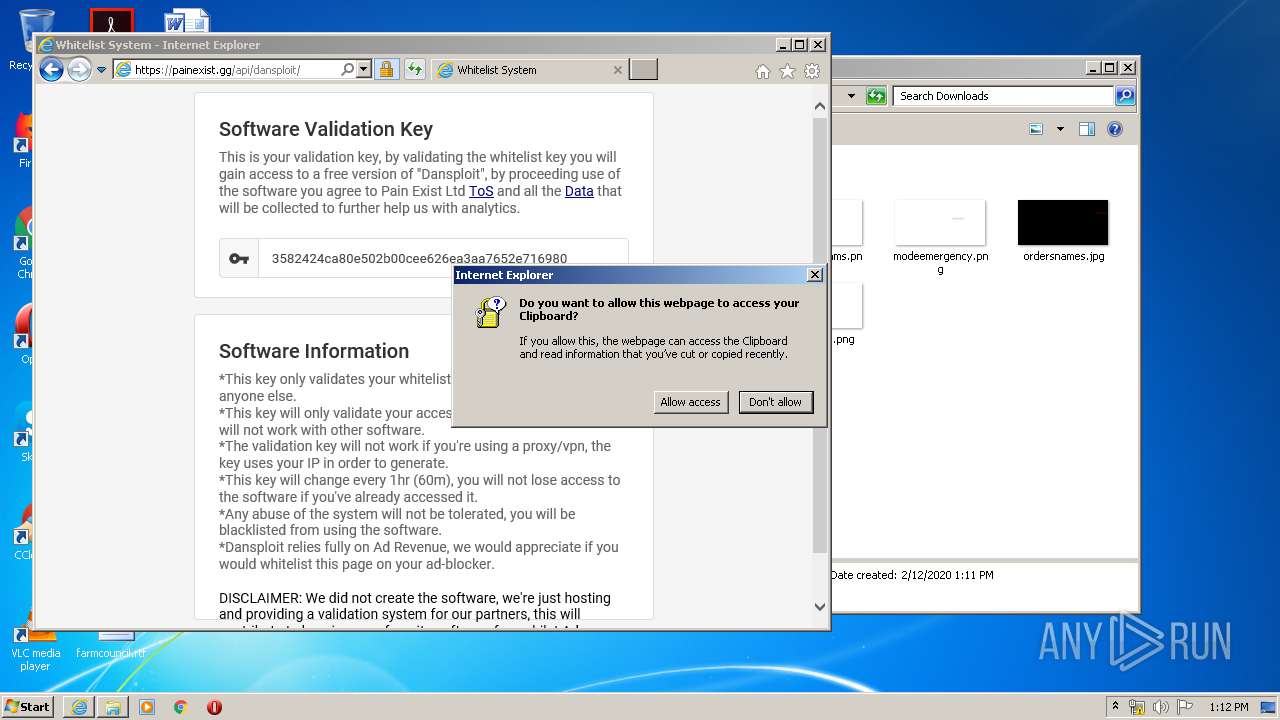
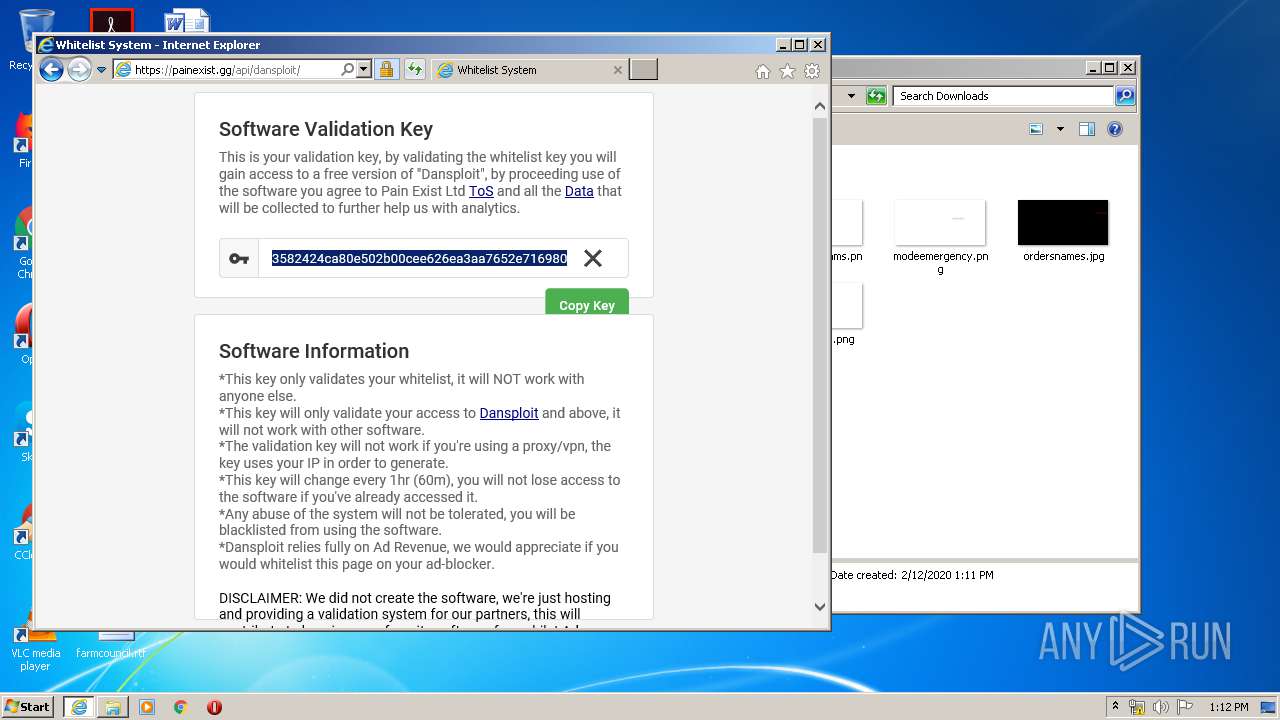
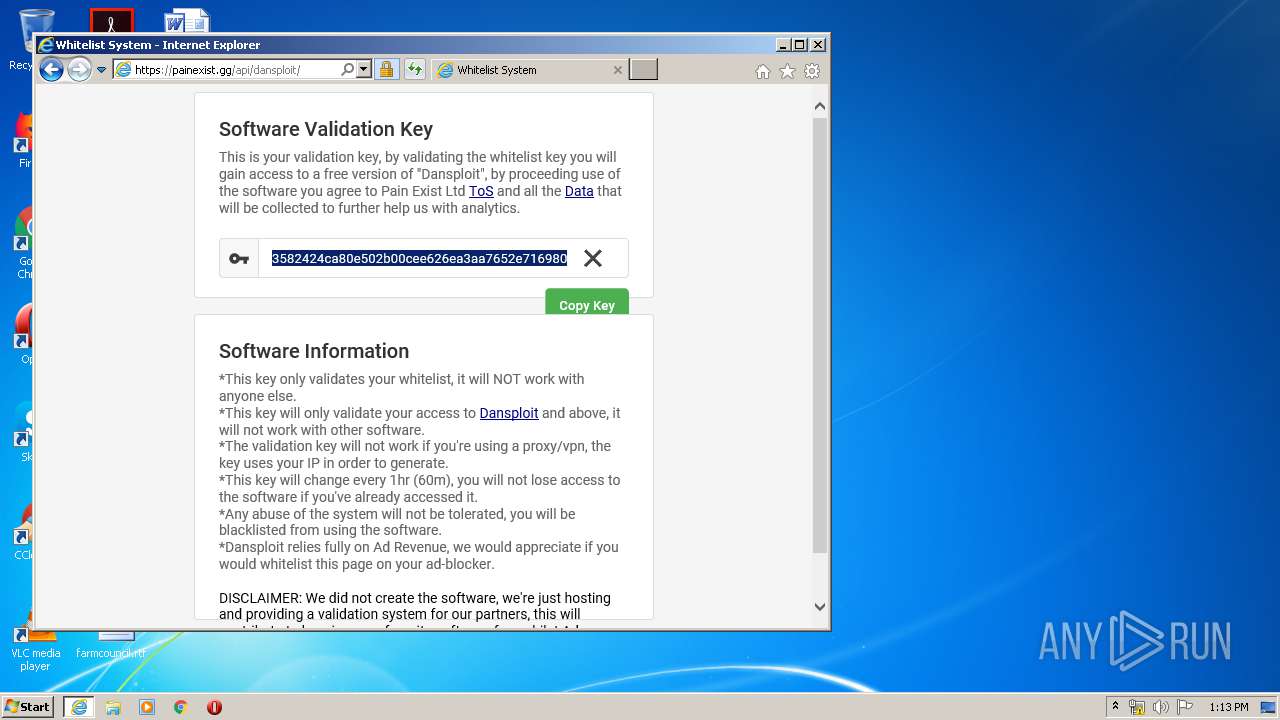
Reads Internet Cache Settings
- iexplore.exe (PID: 2736)
- iexplore.exe (PID: 2084)
- iexplore.exe (PID: 3072)
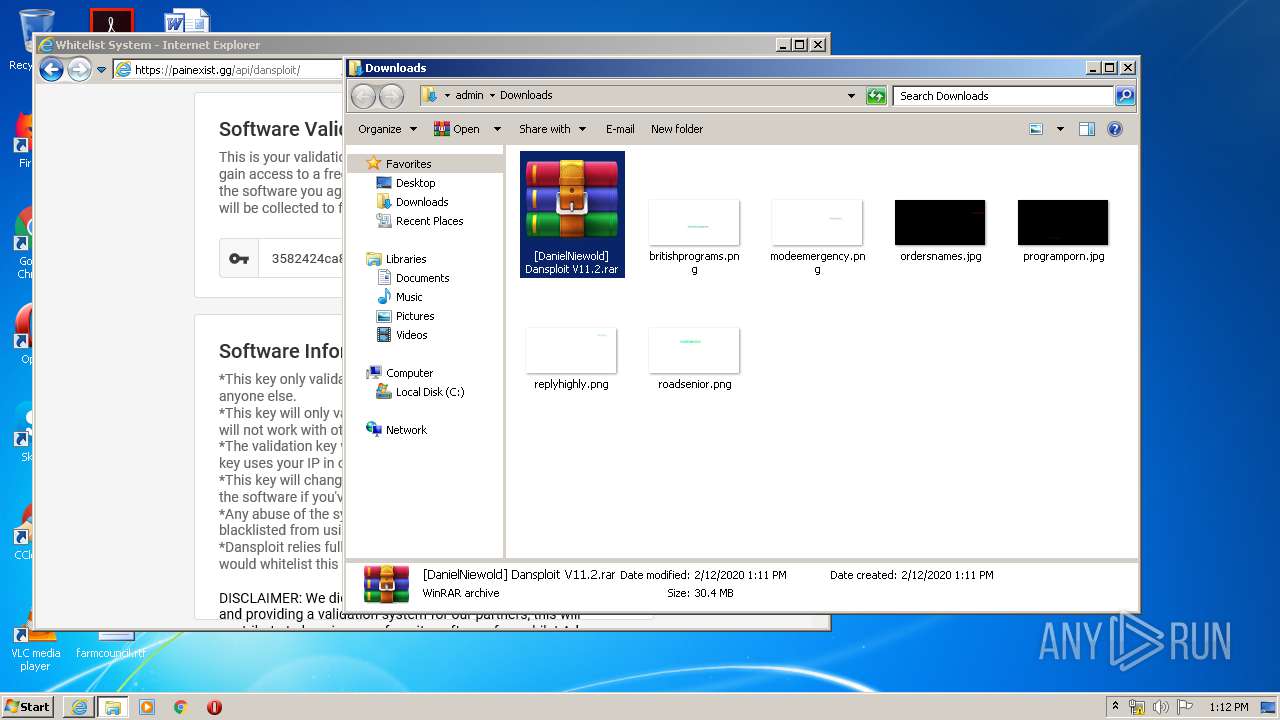
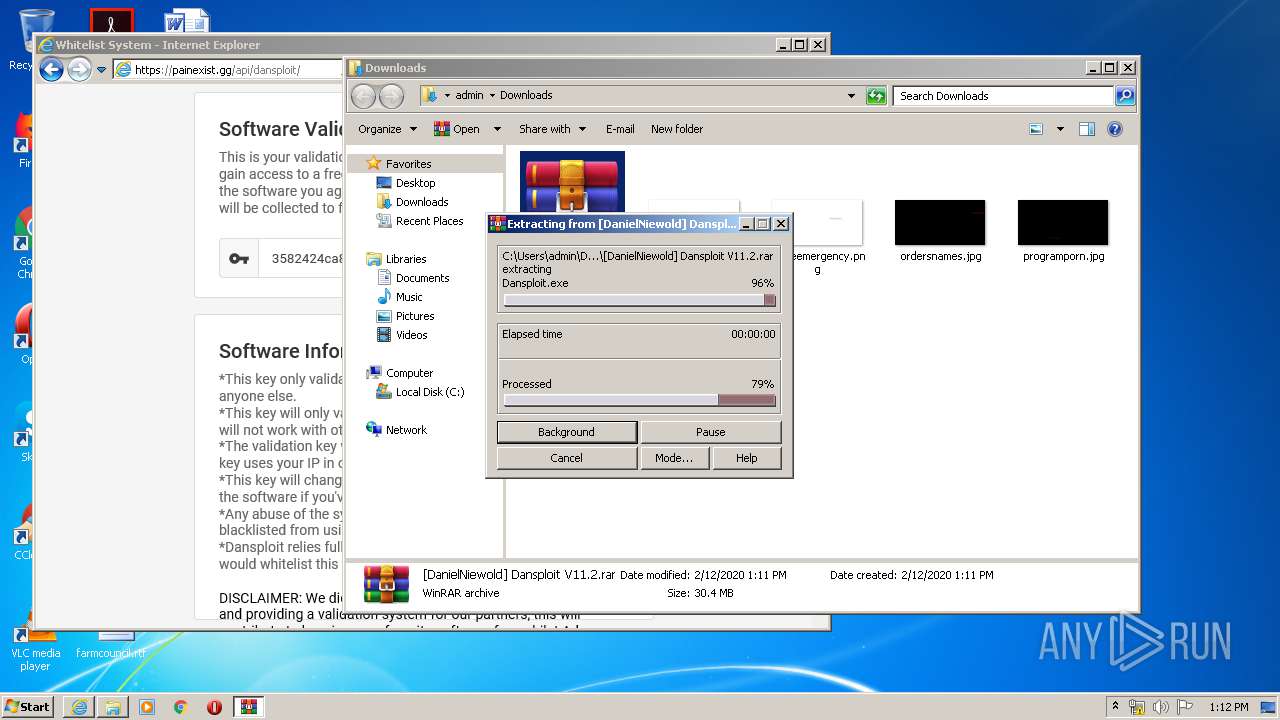
Manual execution by user
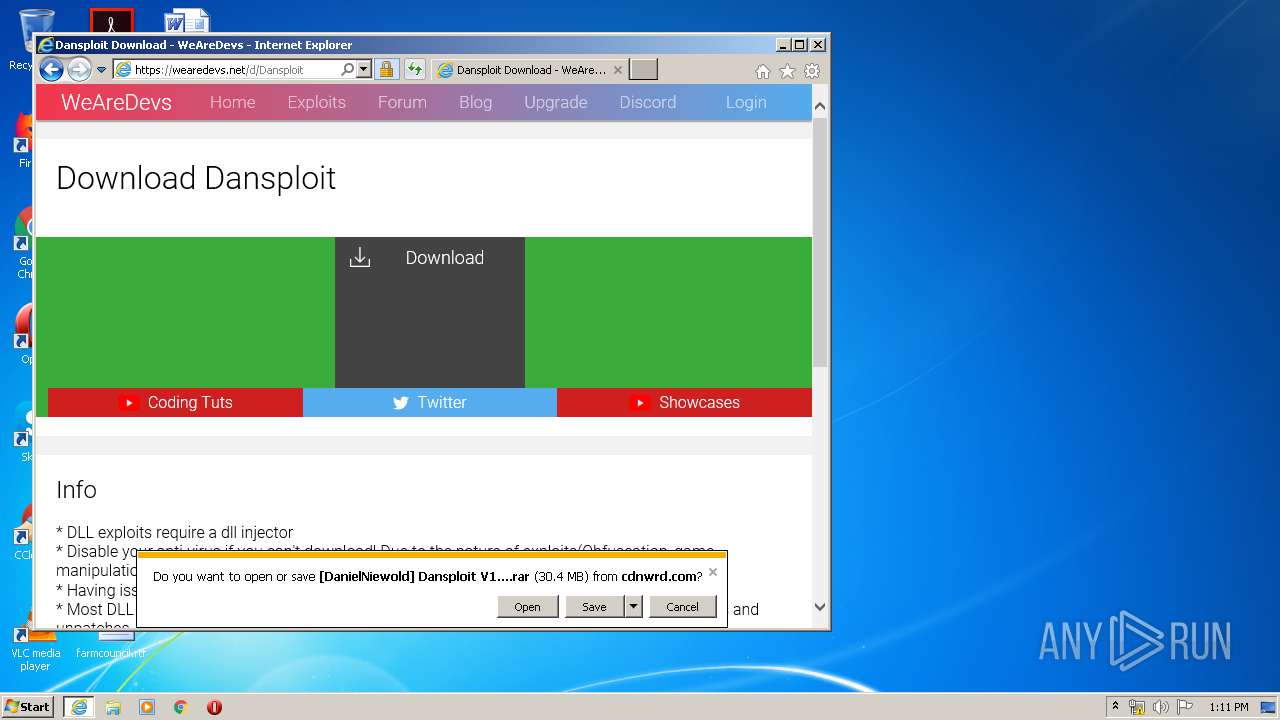
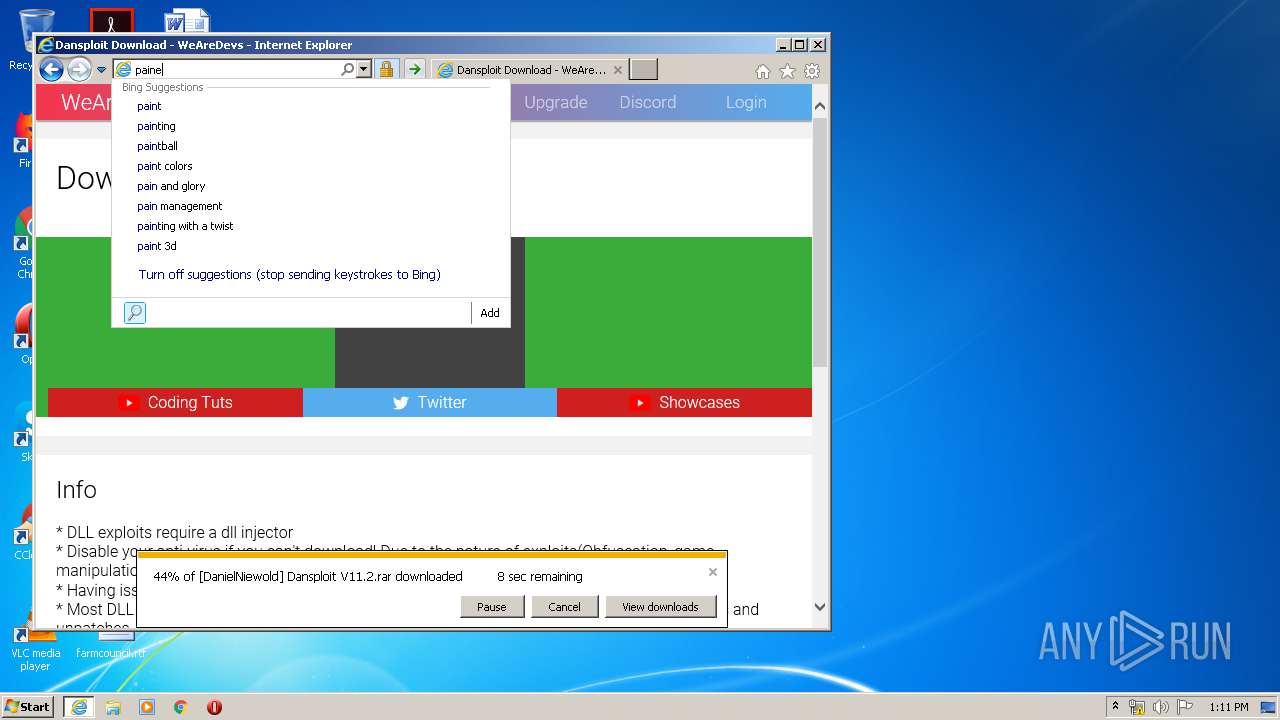
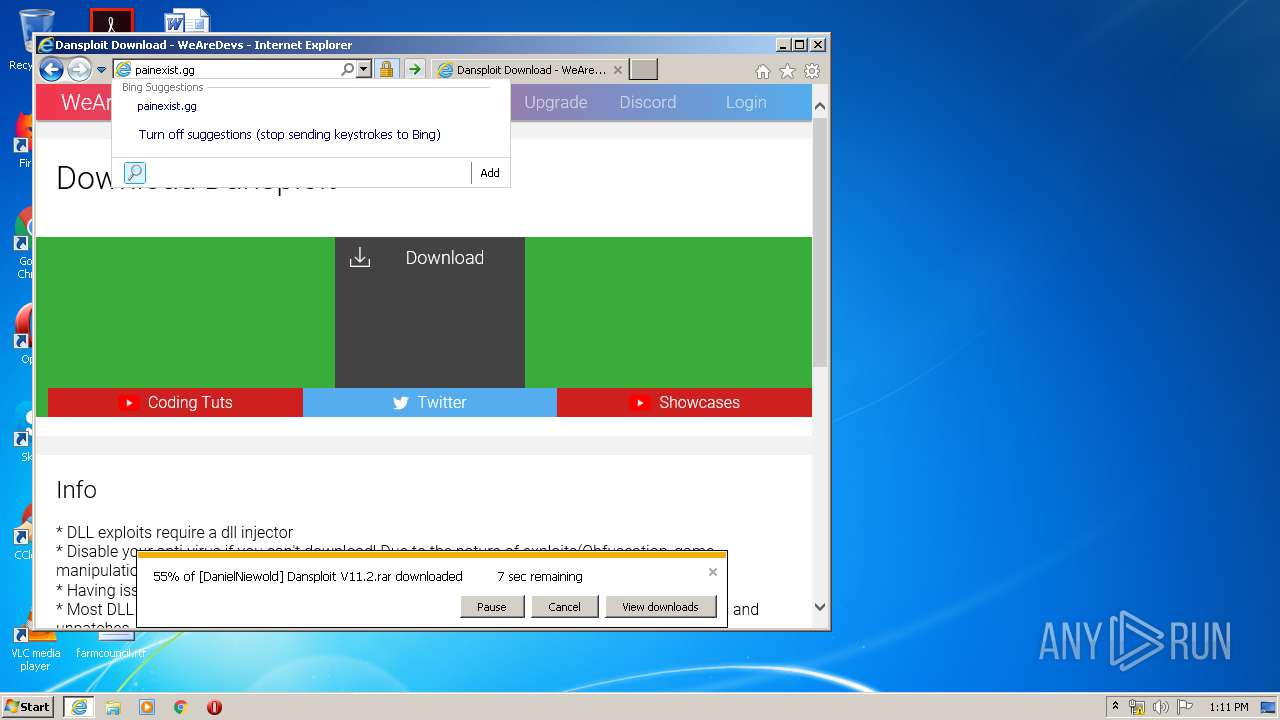
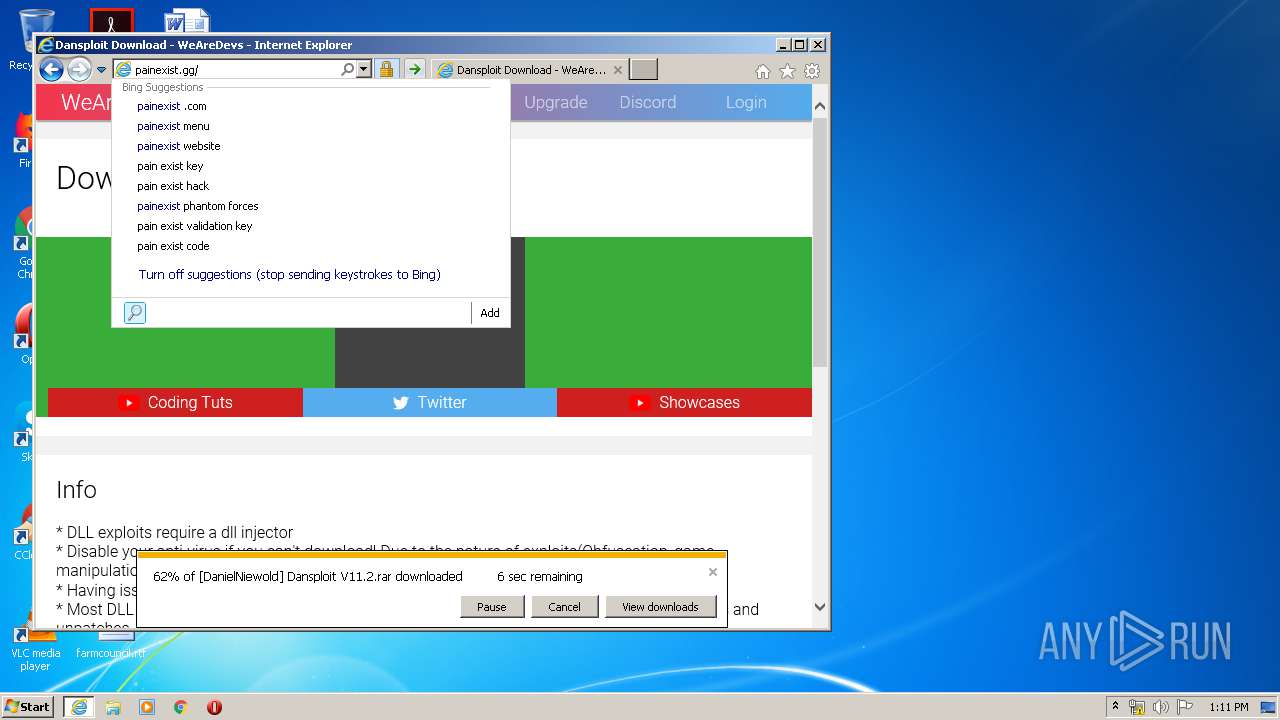
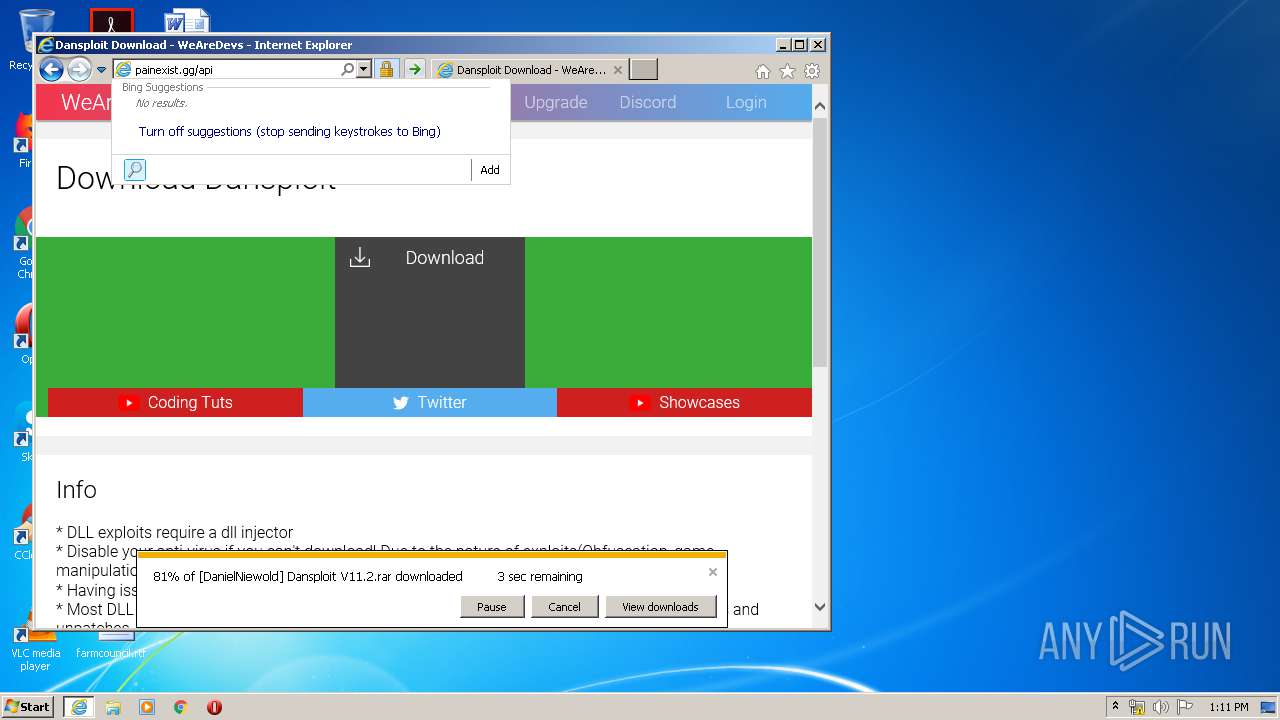
- iexplore.exe (PID: 2736)
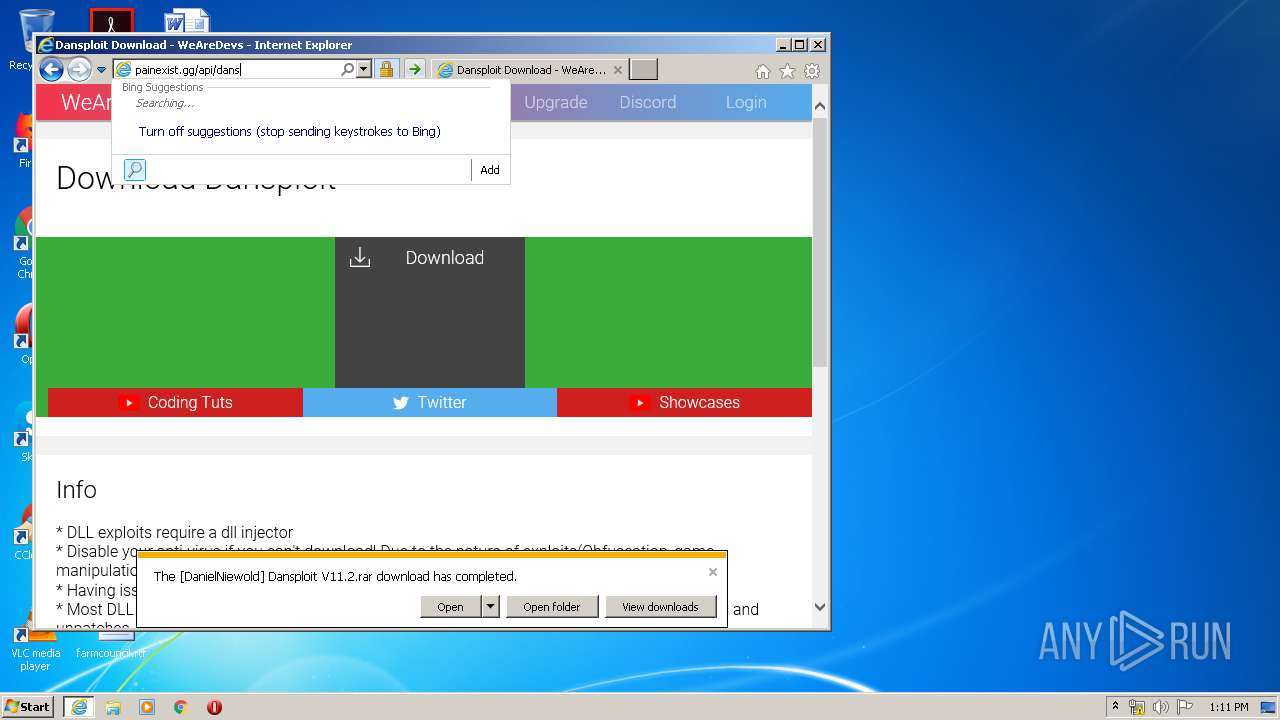
- WinRAR.exe (PID: 3536)
- explorer.exe (PID: 3664)
- Dansploit.exe (PID: 2780)
- Dansploit Discord.exe (PID: 2388)
Changes internet zones settings
- iexplore.exe (PID: 2736)
Reads settings of System Certificates
- iexplore.exe (PID: 2084)
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 2736)
Application launched itself
- iexplore.exe (PID: 2736)
Reads internet explorer settings
- iexplore.exe (PID: 2084)
- iexplore.exe (PID: 3072)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2736)
Creates files in the user directory
- iexplore.exe (PID: 2736)
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 2084)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3536)
Changes settings of System certificates
- iexplore.exe (PID: 2736)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:10 23:01:17+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 8704 |
| InitializedDataSize: | 26624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x40ce |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
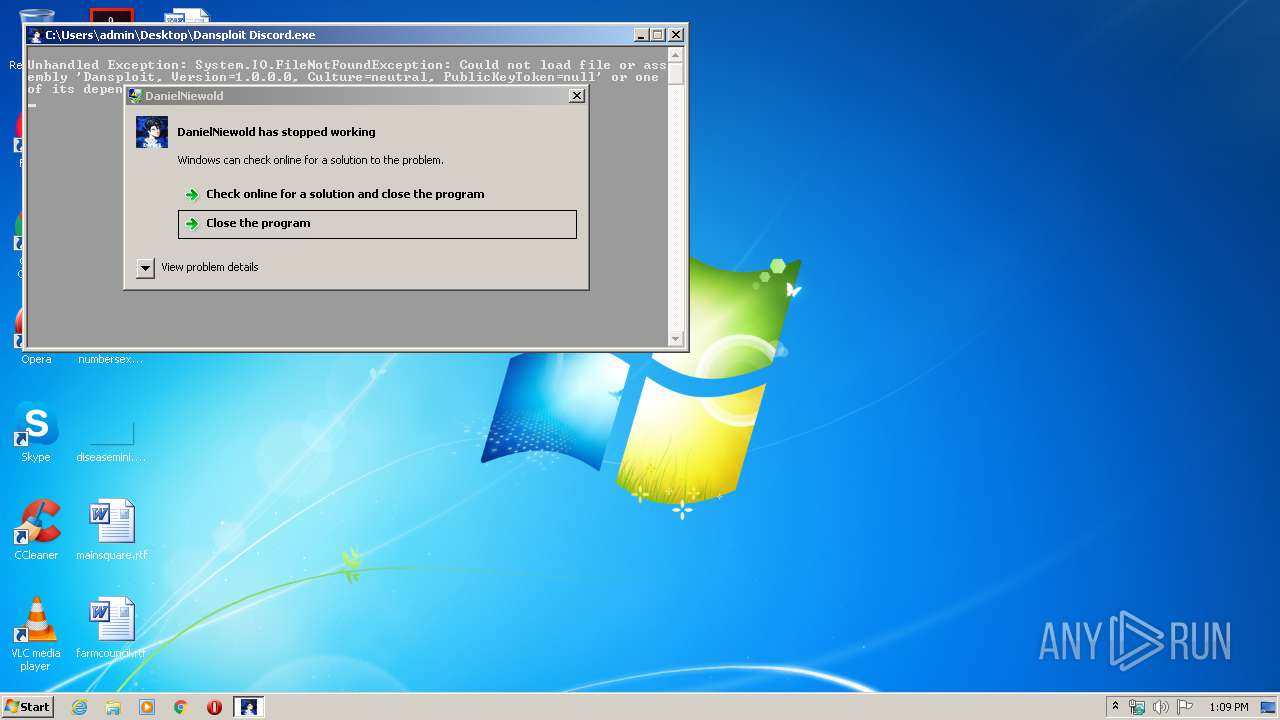
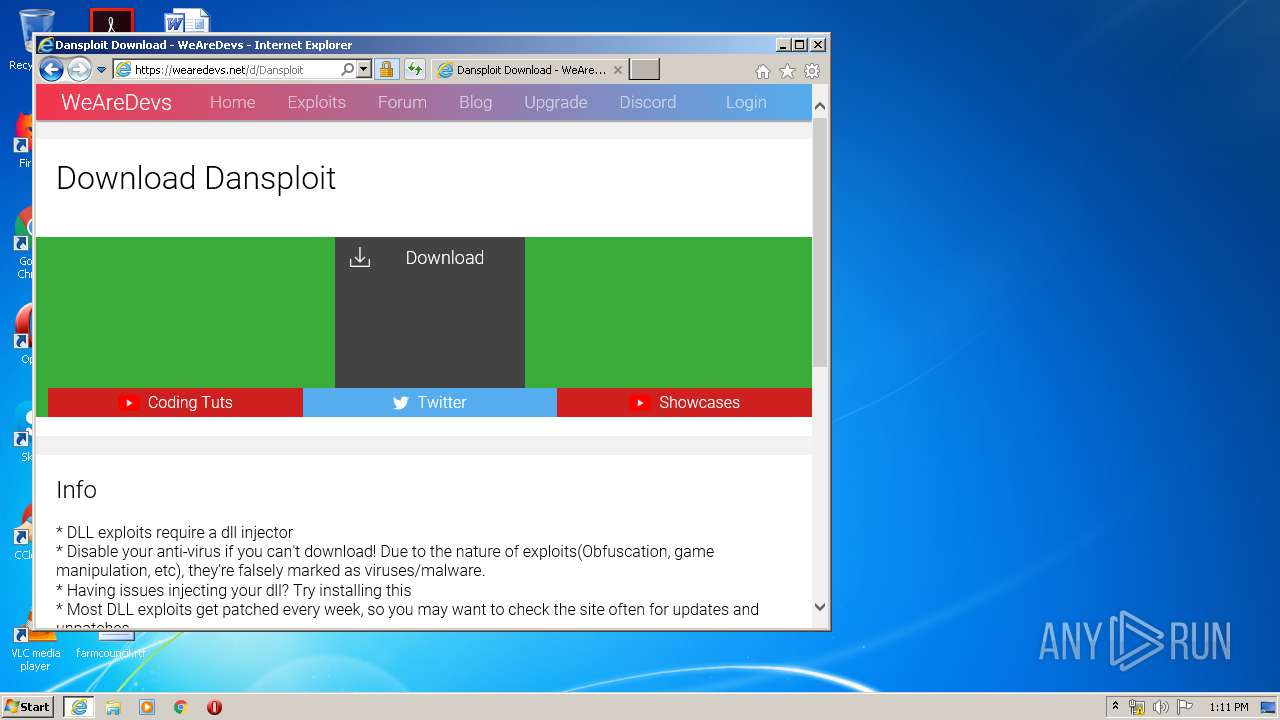
| FileDescription: | DanielNiewold |
| FileVersion: | 1.0.0.0 |
| InternalName: | Dansploit Discord.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | Dansploit Discord.exe |
| ProductName: | Dansploit© |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 10-Mar-2019 22:01:17 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | DanielNiewold |
| FileVersion: | 1.0.0.0 |
| InternalName: | Dansploit Discord.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFilename: | Dansploit Discord.exe |
| ProductName: | Dansploit© |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 10-Mar-2019 22:01:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000020D4 | 0x00002200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.33922 |
.rsrc | 0x00006000 | 0x000064D8 | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.5117 |
.reloc | 0x0000E000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 6.30529 | 4136 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 6.3981 | 2344 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 6.43665 | 1064 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.48187 | 62 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
53
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2084 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2736 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
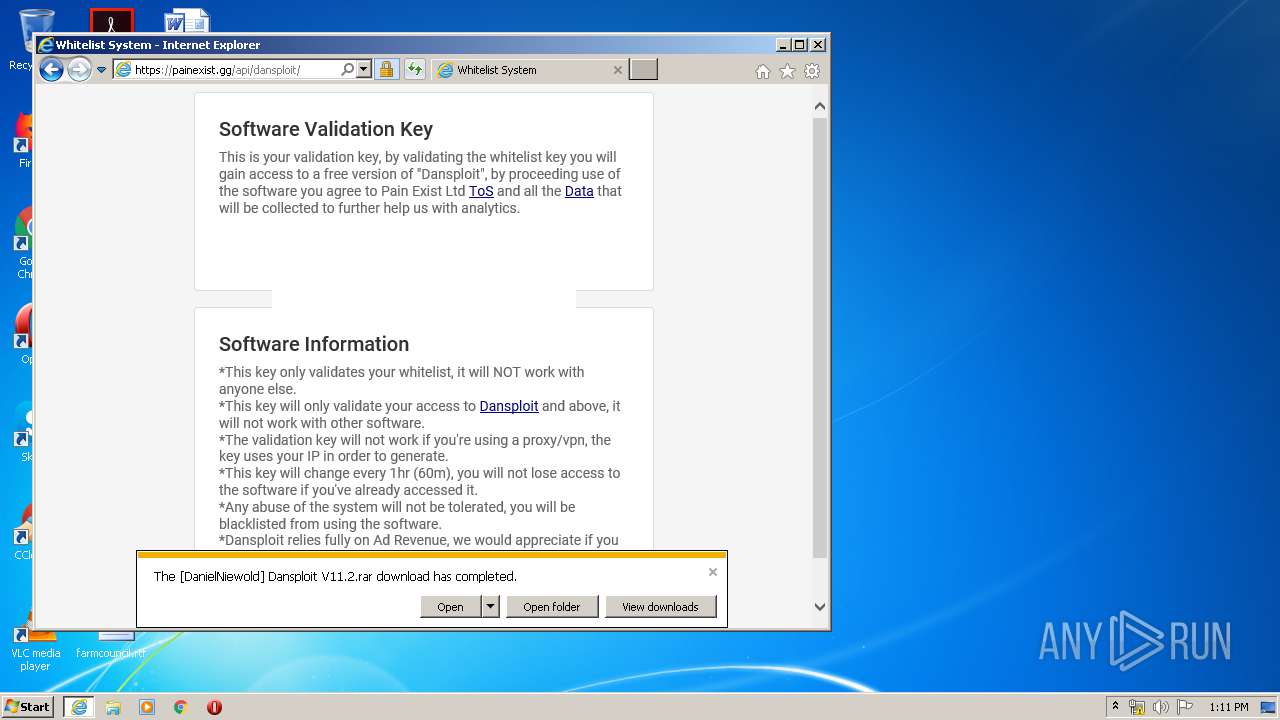
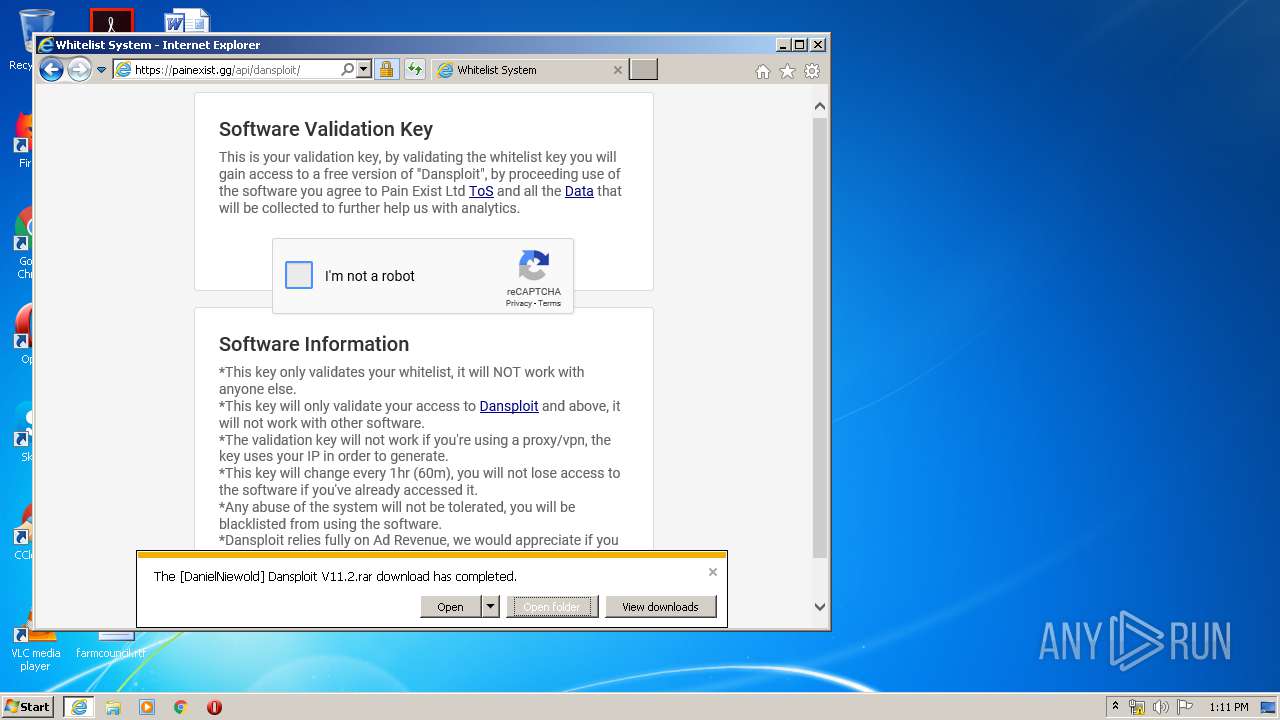
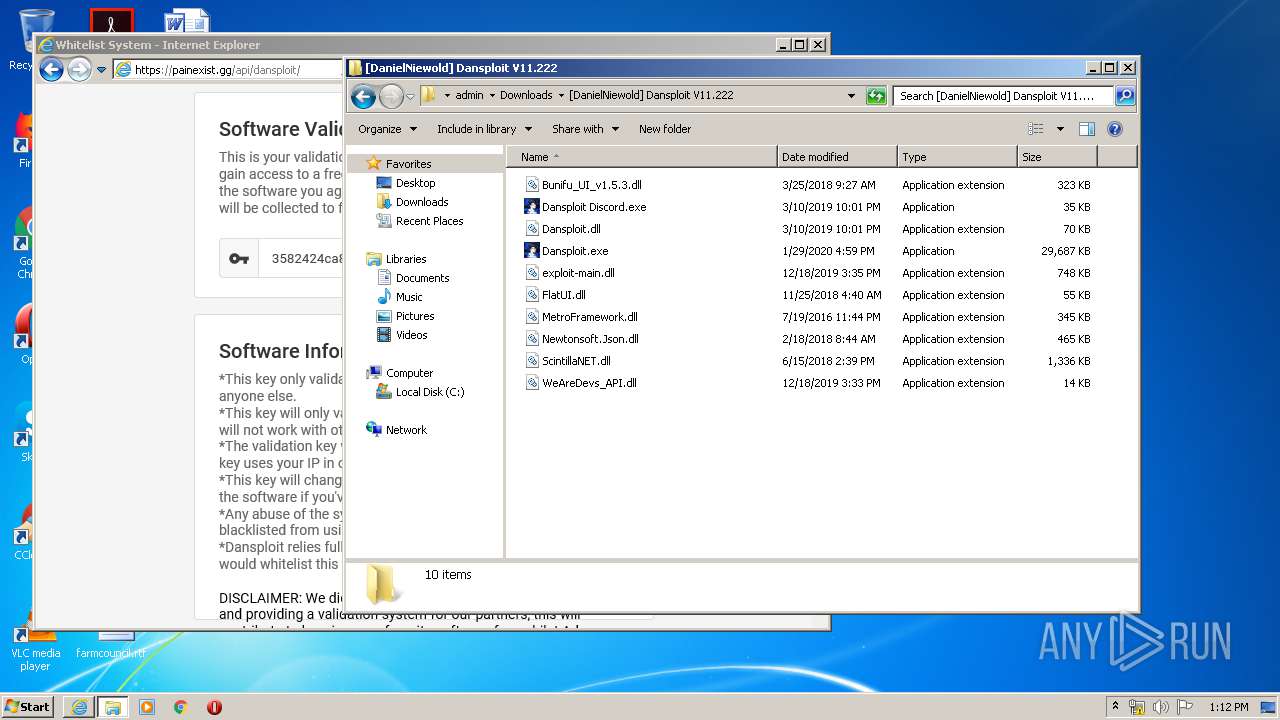
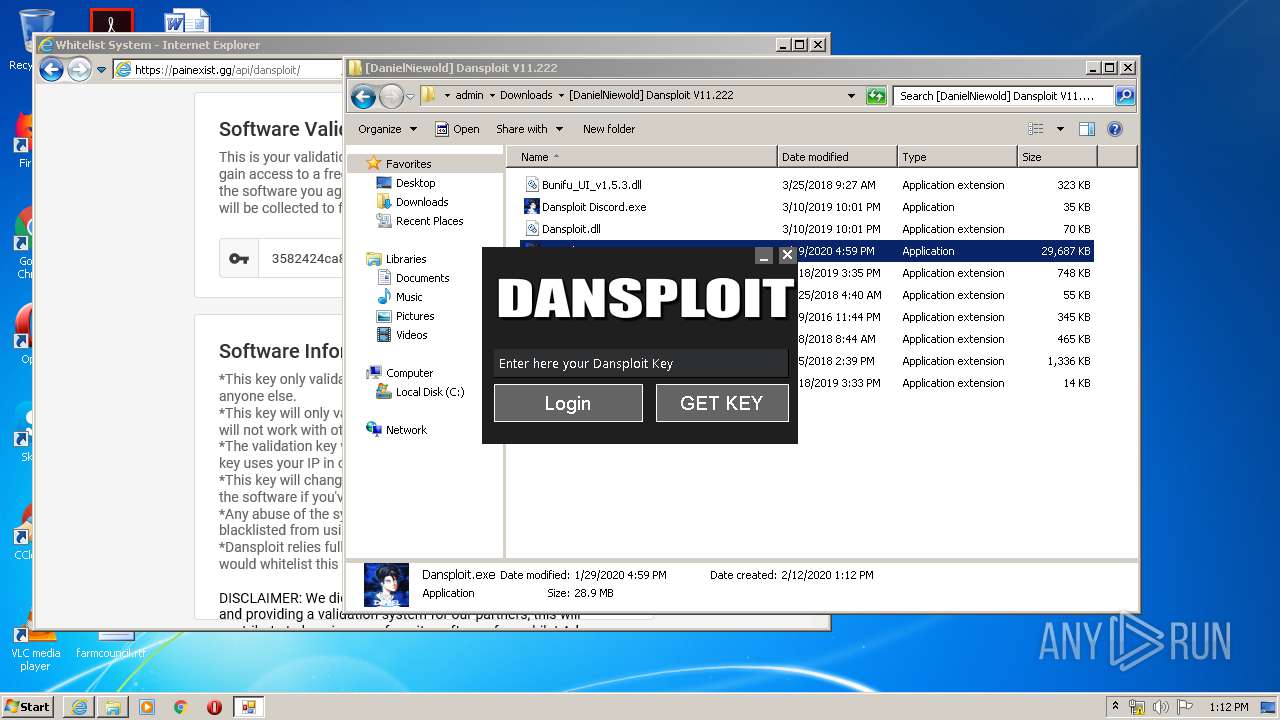
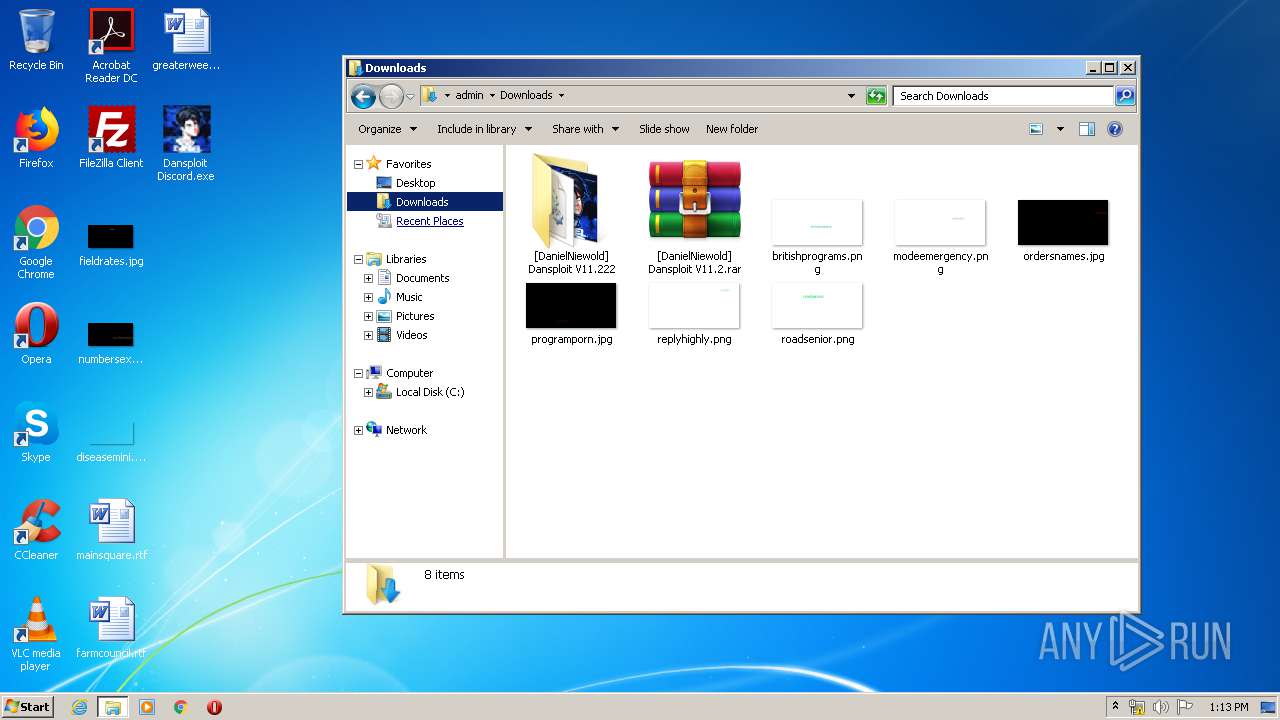
| 2388 | "C:\Users\admin\Downloads\[DanielNiewold] Dansploit V11.222\Dansploit Discord.exe" | C:\Users\admin\Downloads\[DanielNiewold] Dansploit V11.222\Dansploit Discord.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DanielNiewold Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
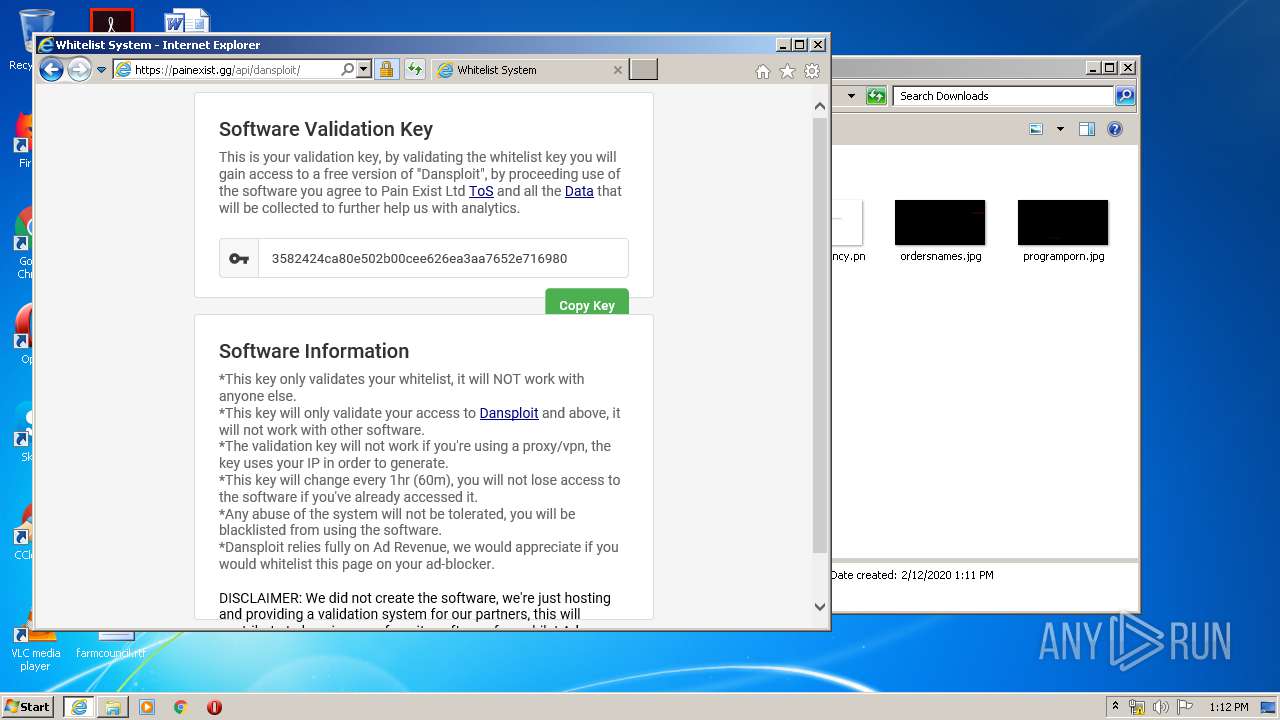
| 2736 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
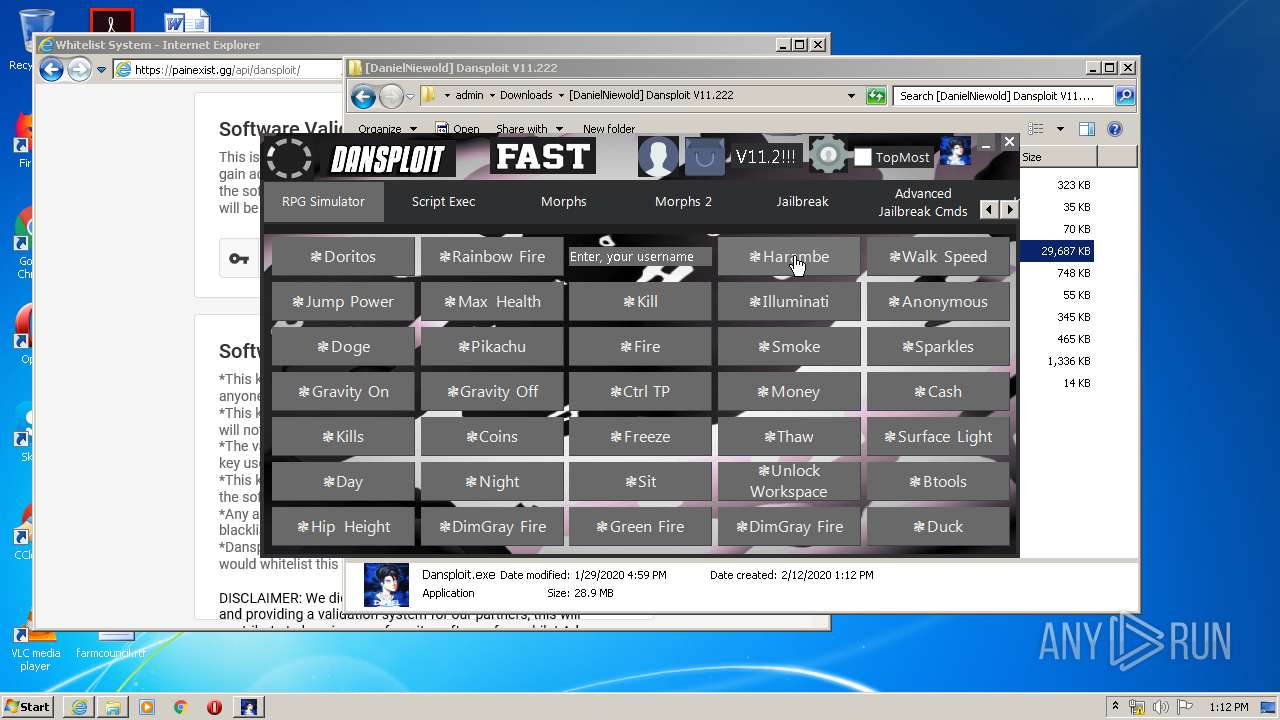
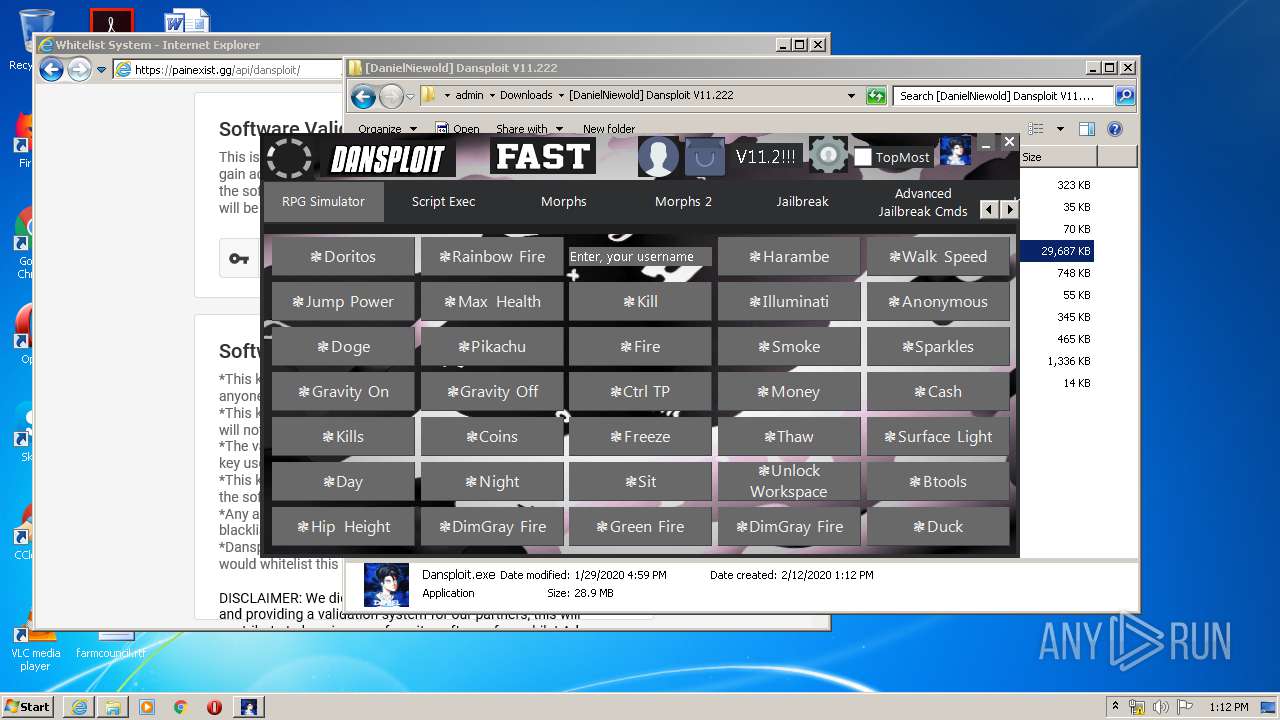
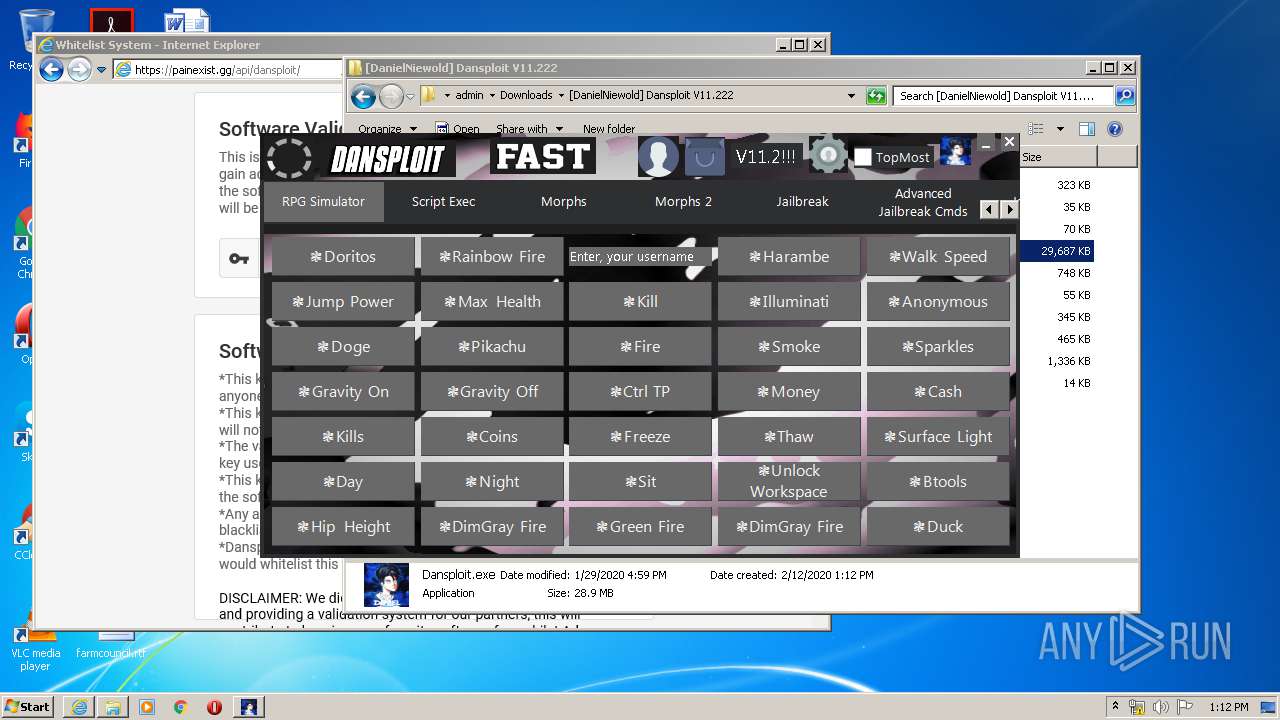
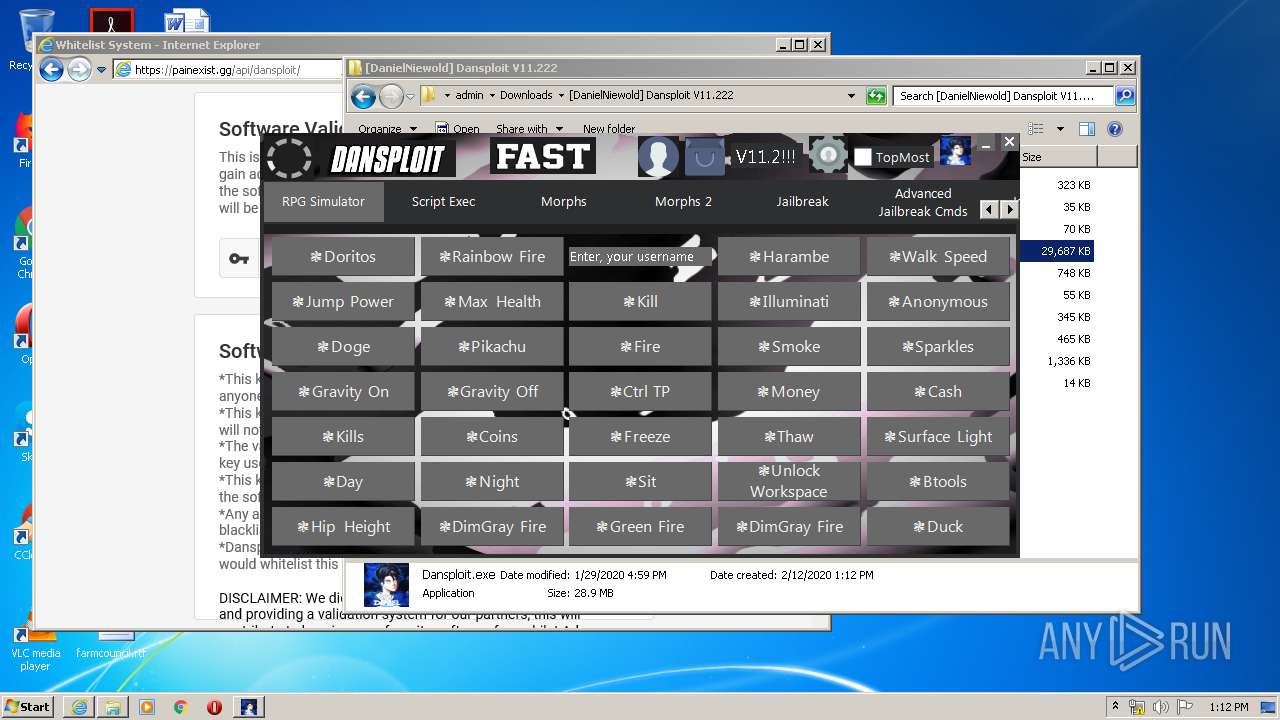
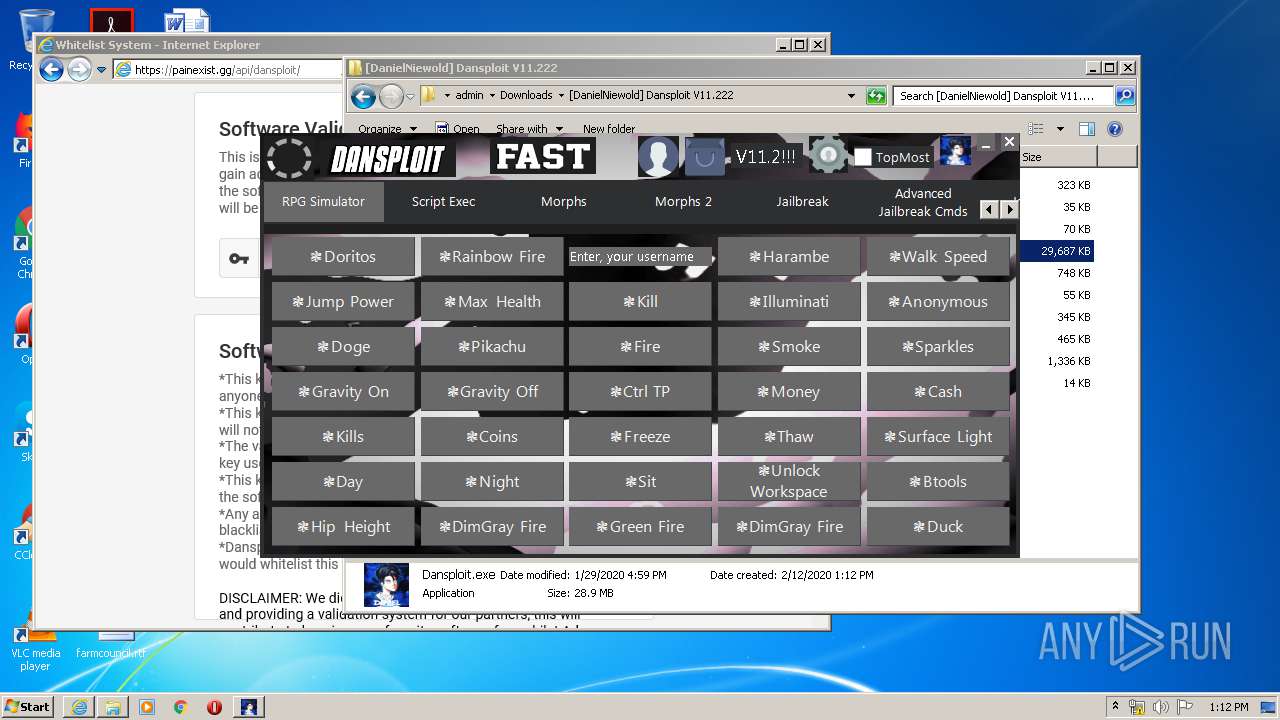
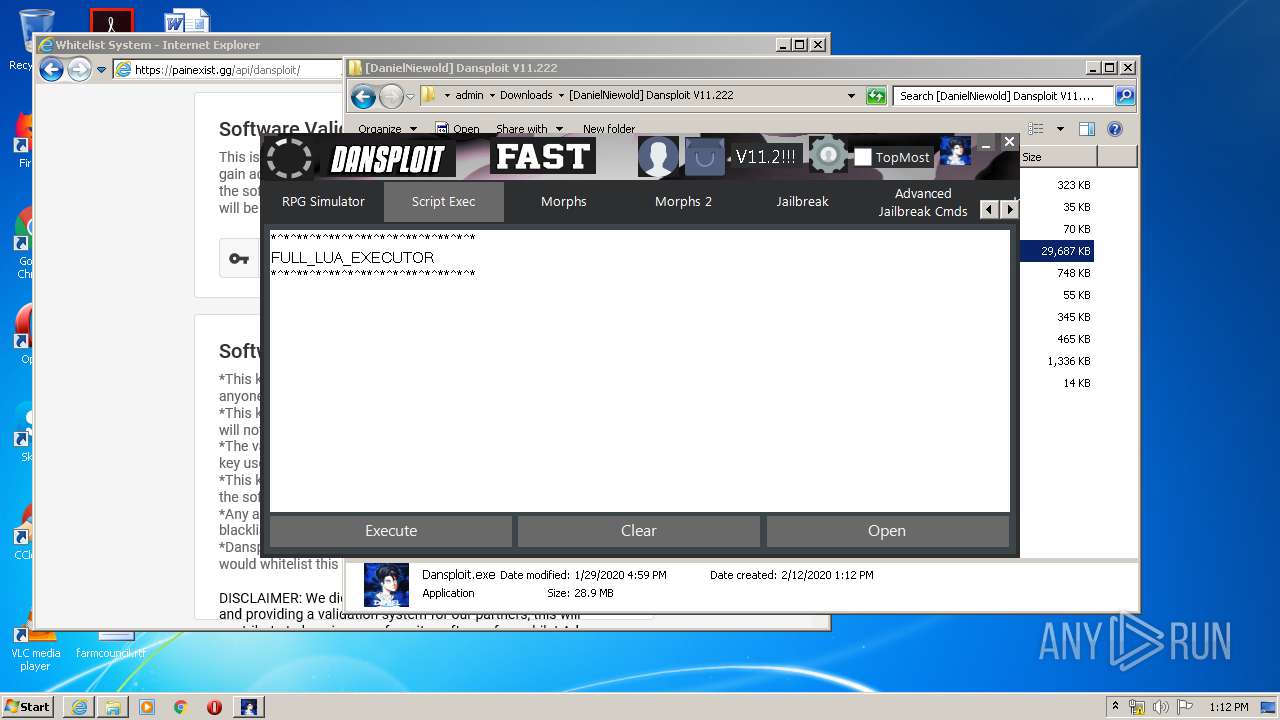
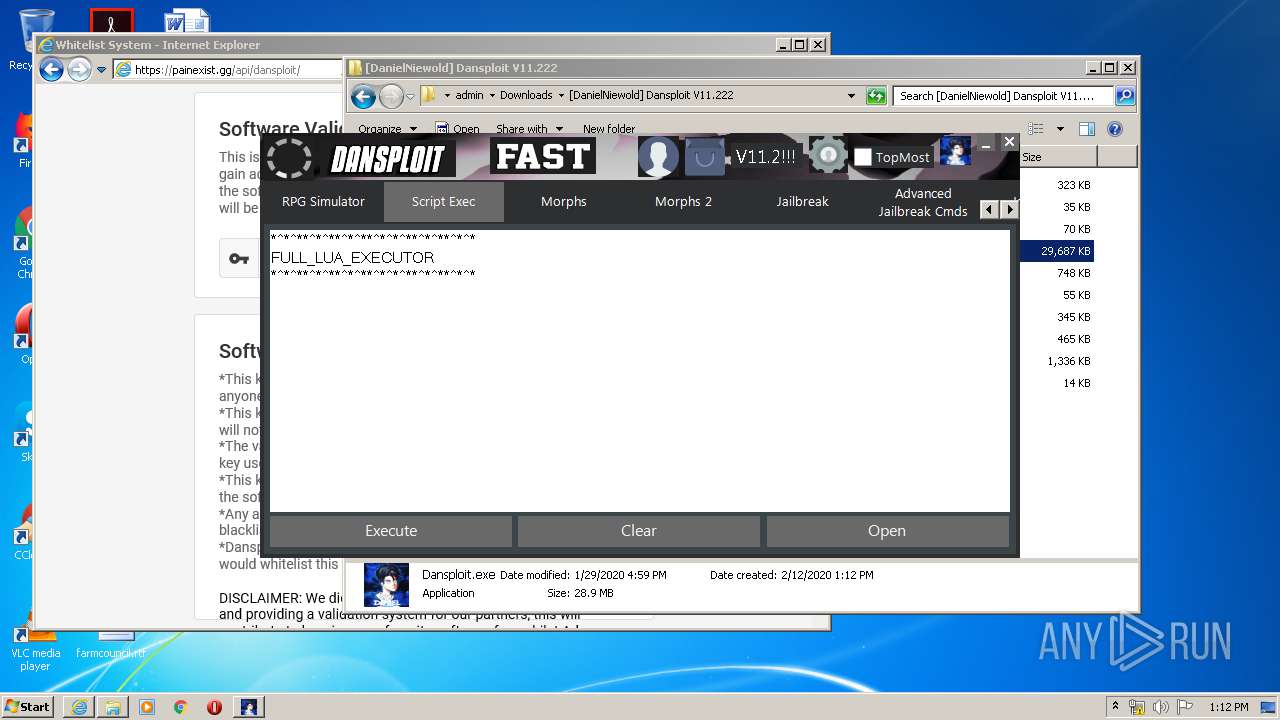
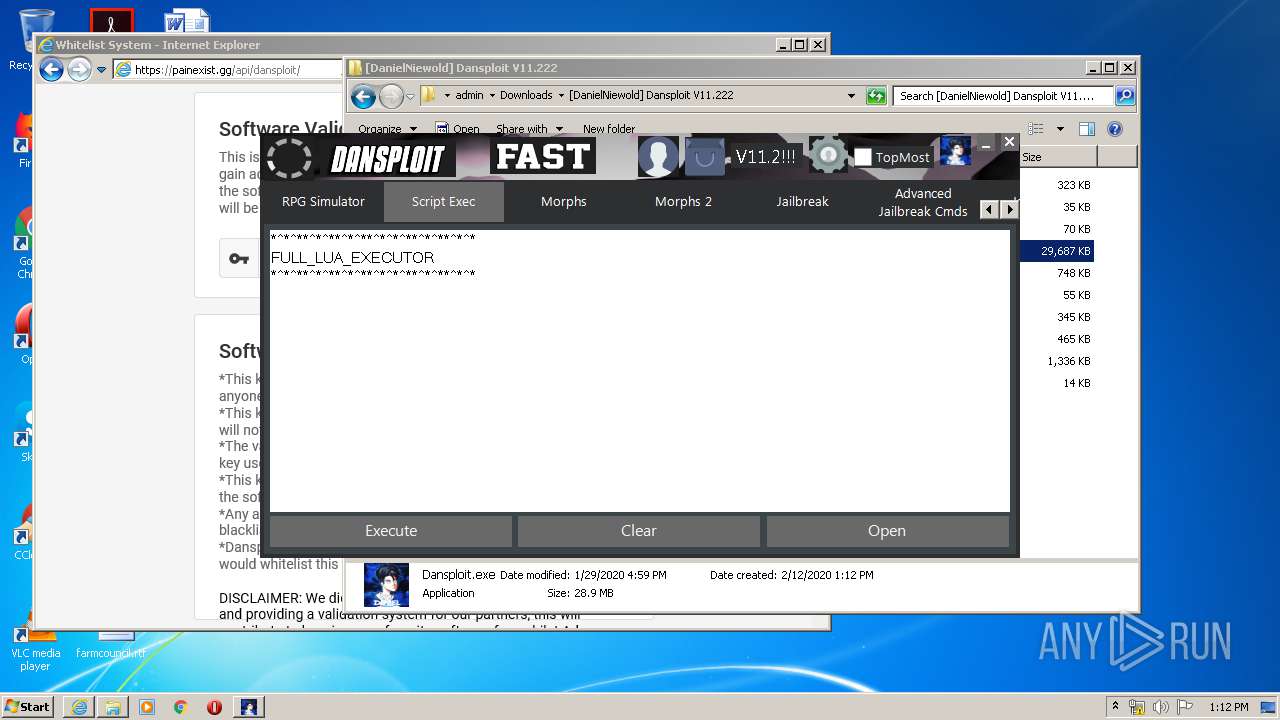
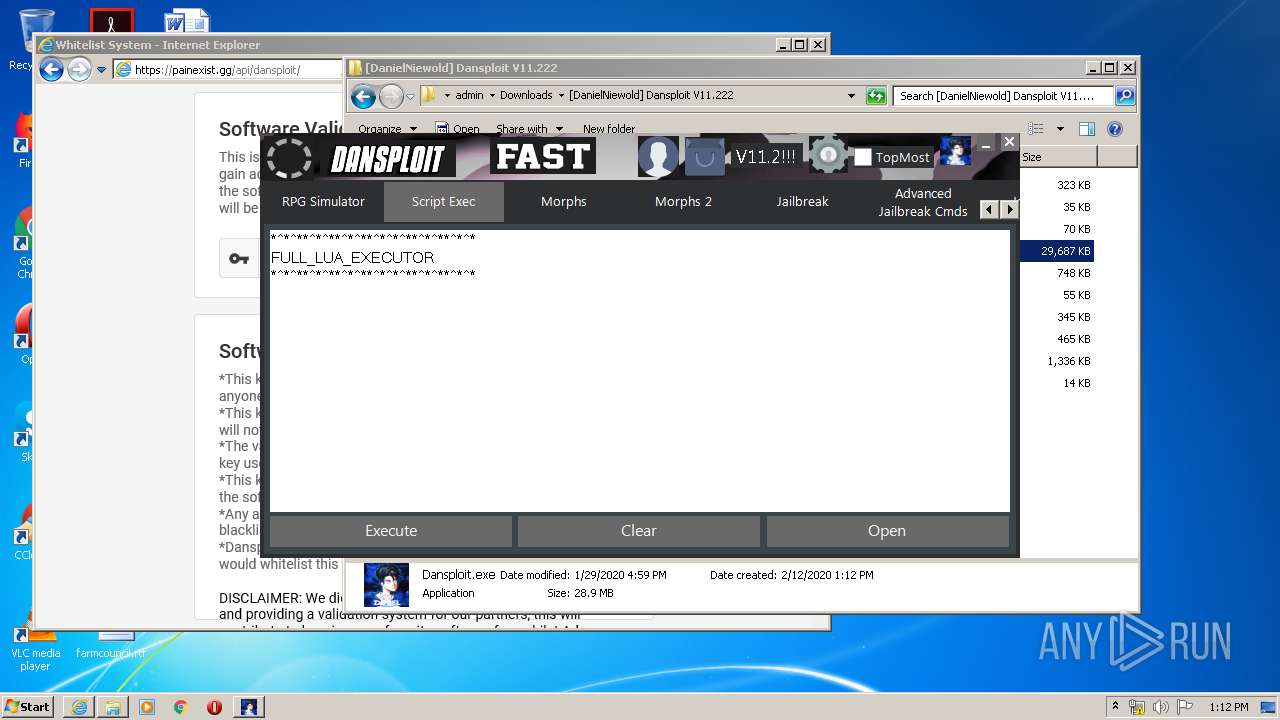
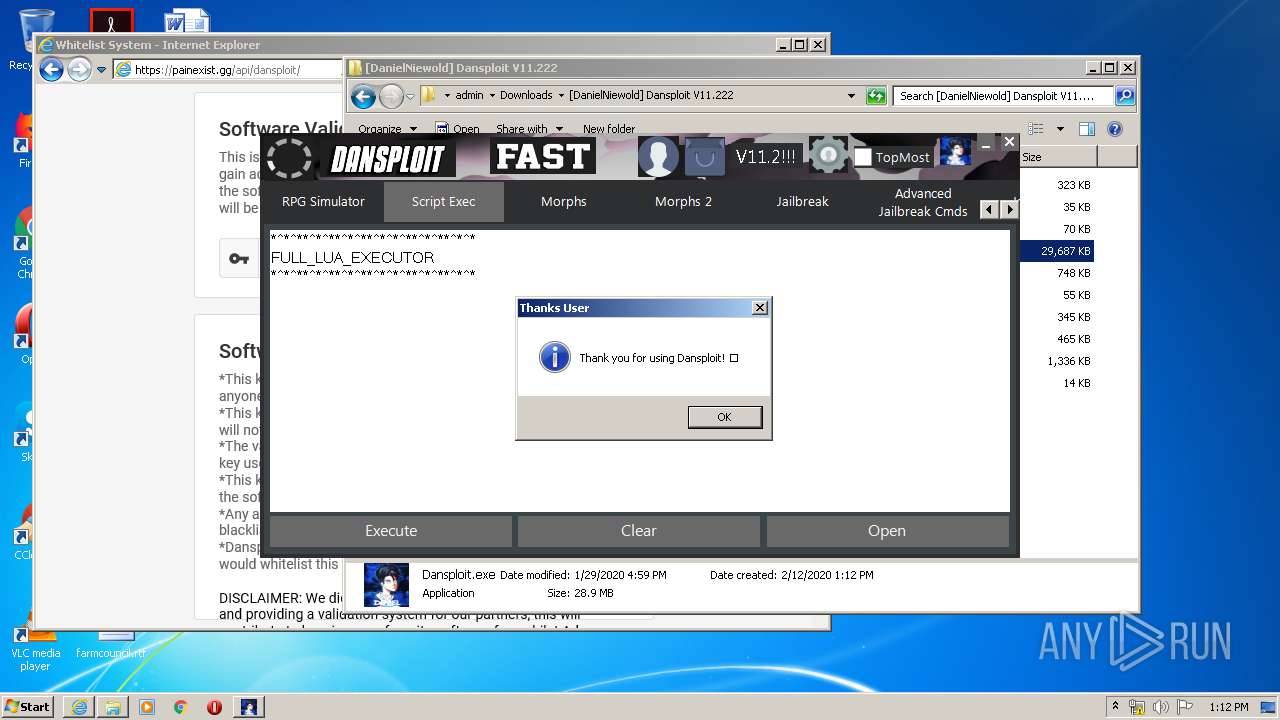
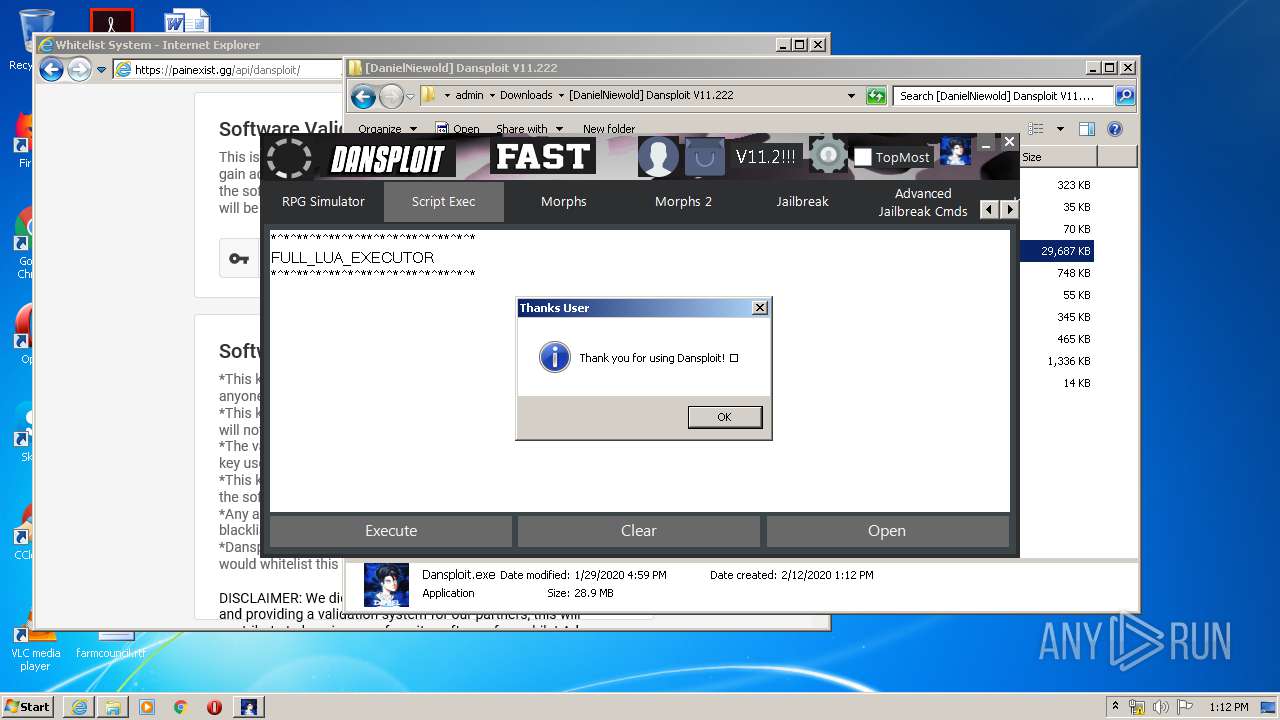
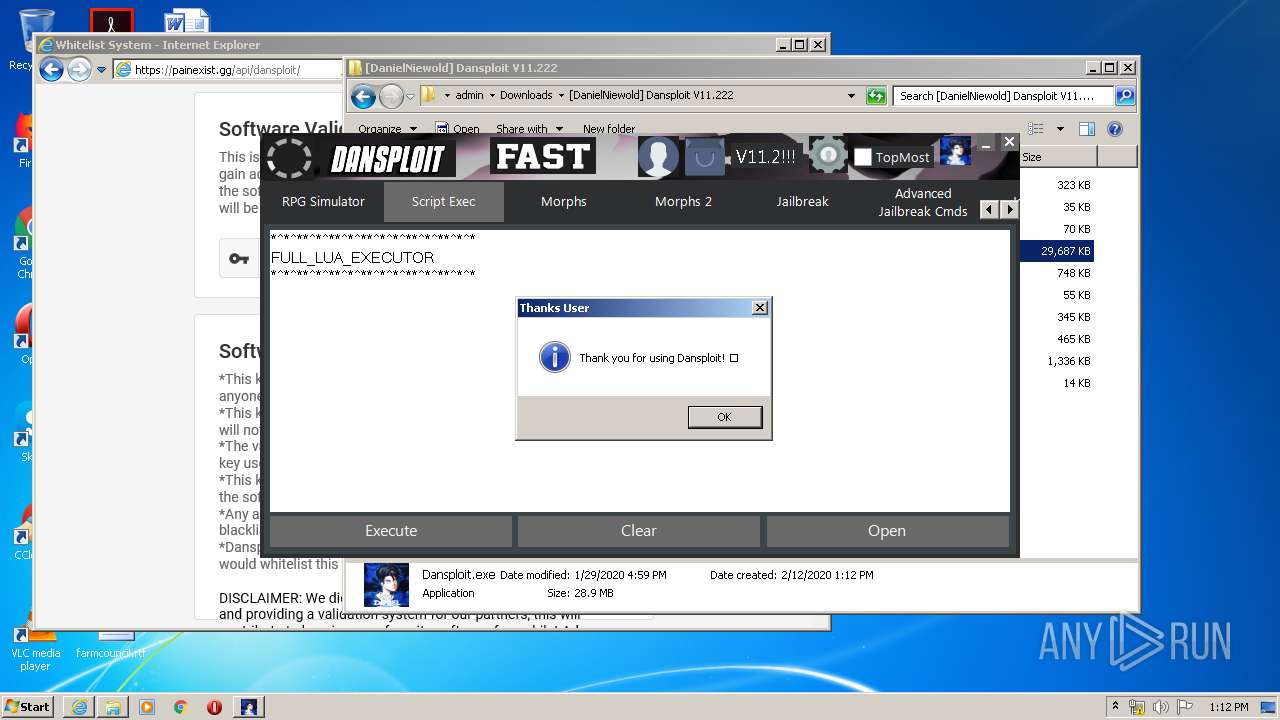
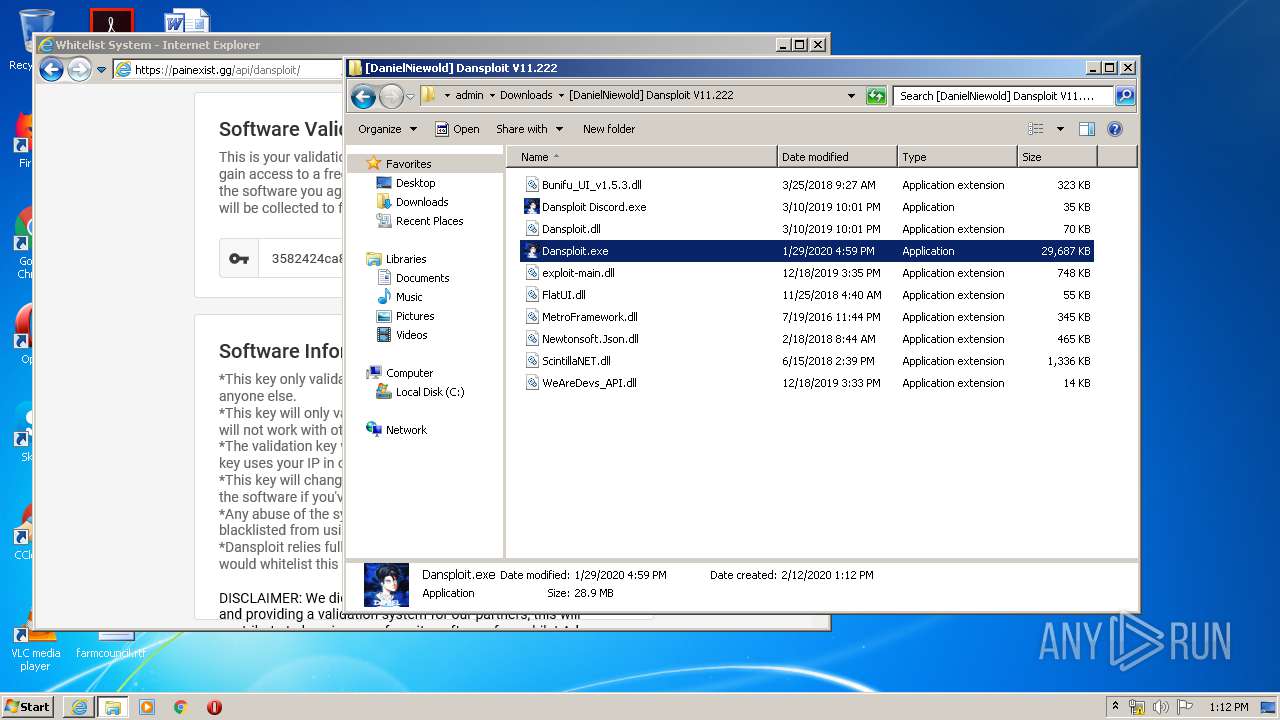
| 2780 | "C:\Users\admin\Downloads\[DanielNiewold] Dansploit V11.222\Dansploit.exe" | C:\Users\admin\Downloads\[DanielNiewold] Dansploit V11.222\Dansploit.exe | explorer.exe | ||||||||||||
User: admin Company: HP Inc. Integrity Level: MEDIUM Description: Dansploit Rewrite Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3072 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2736 CREDAT:2626835 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3080 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3196 | "C:\Users\admin\Desktop\Dansploit Discord.exe" | C:\Users\admin\Desktop\Dansploit Discord.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: DanielNiewold Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
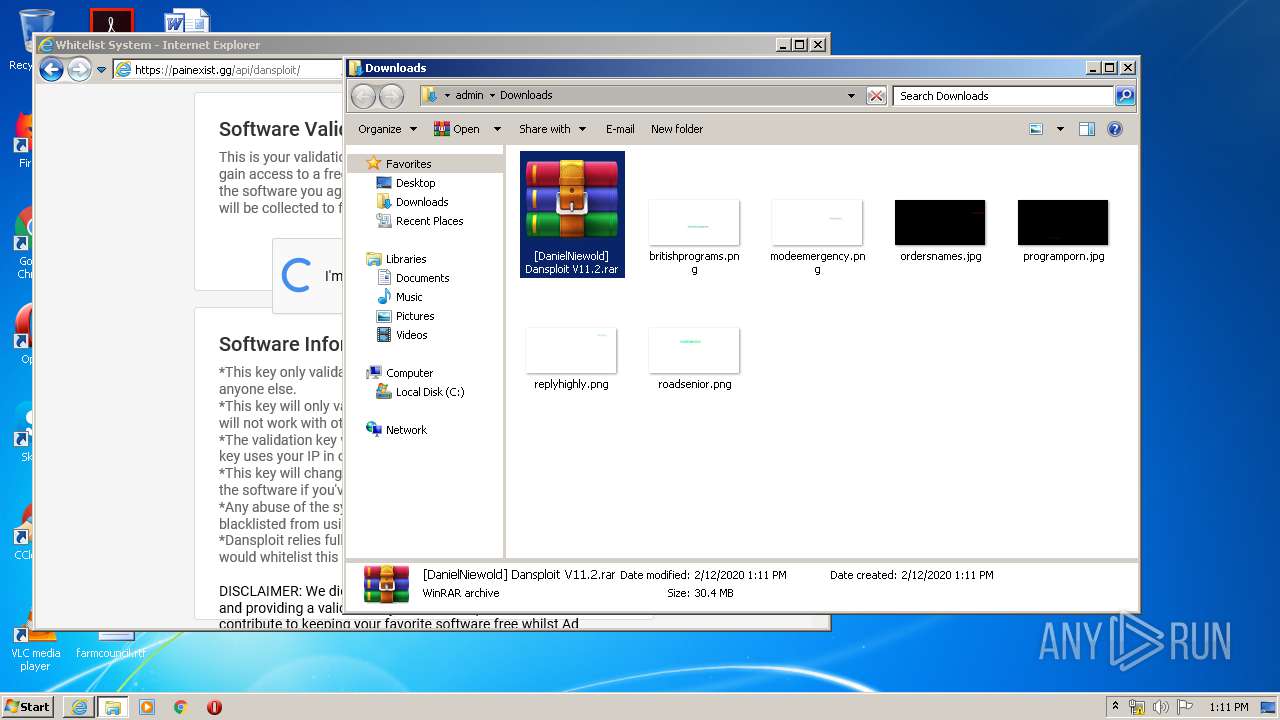
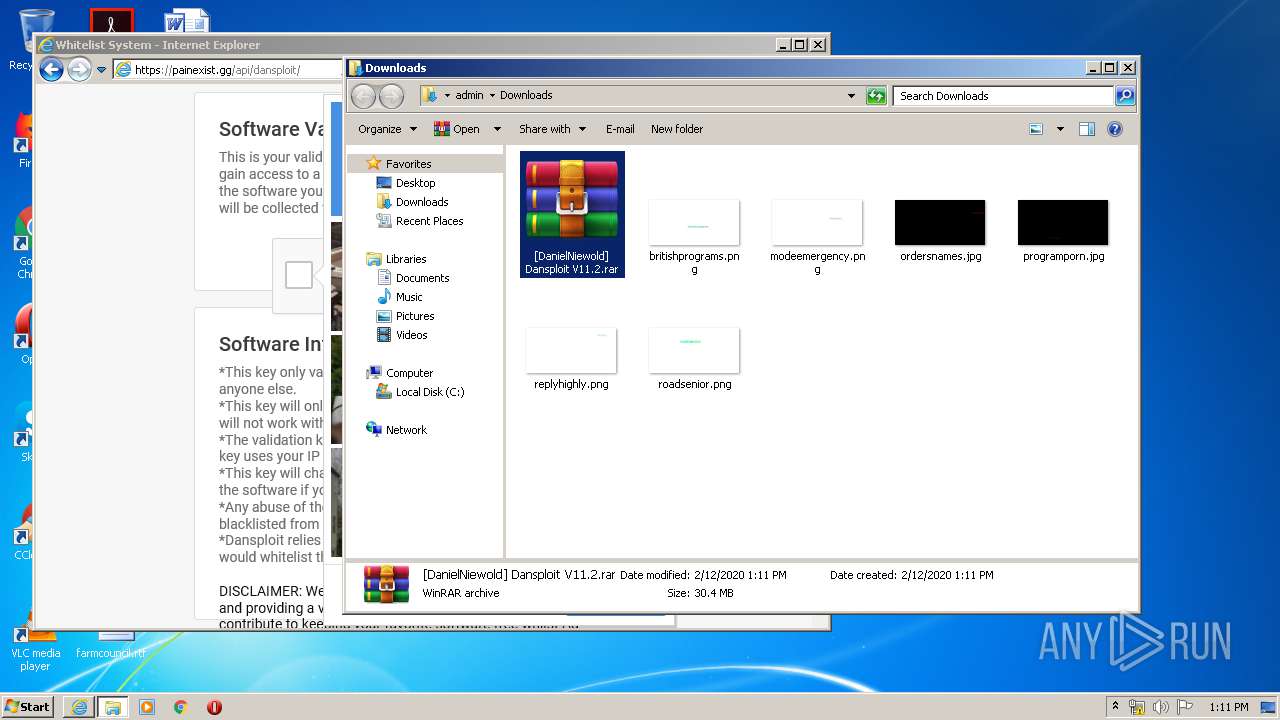
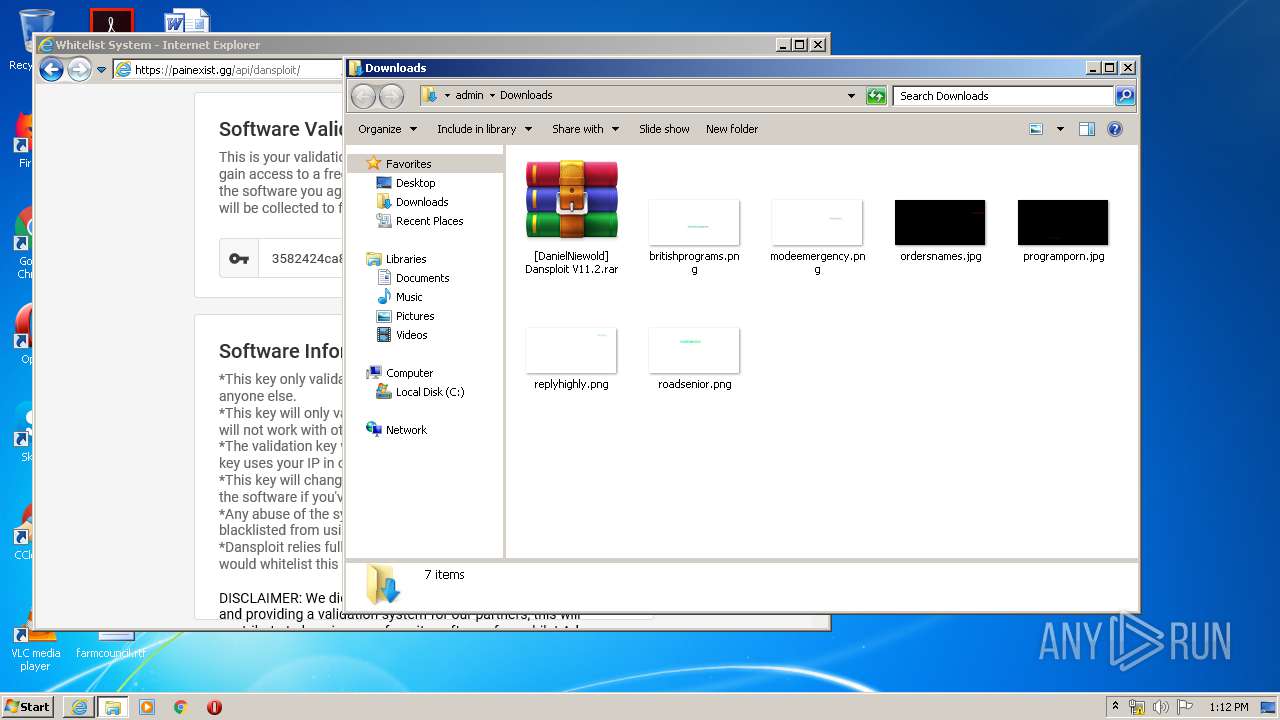
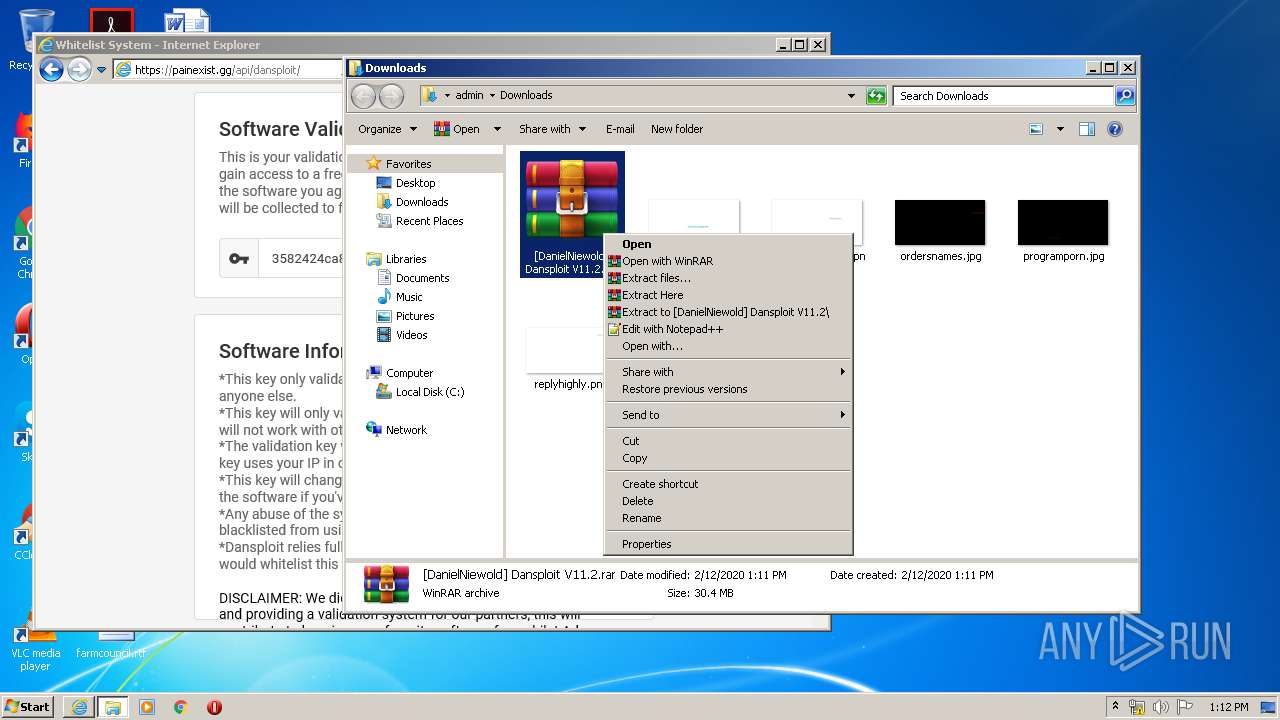
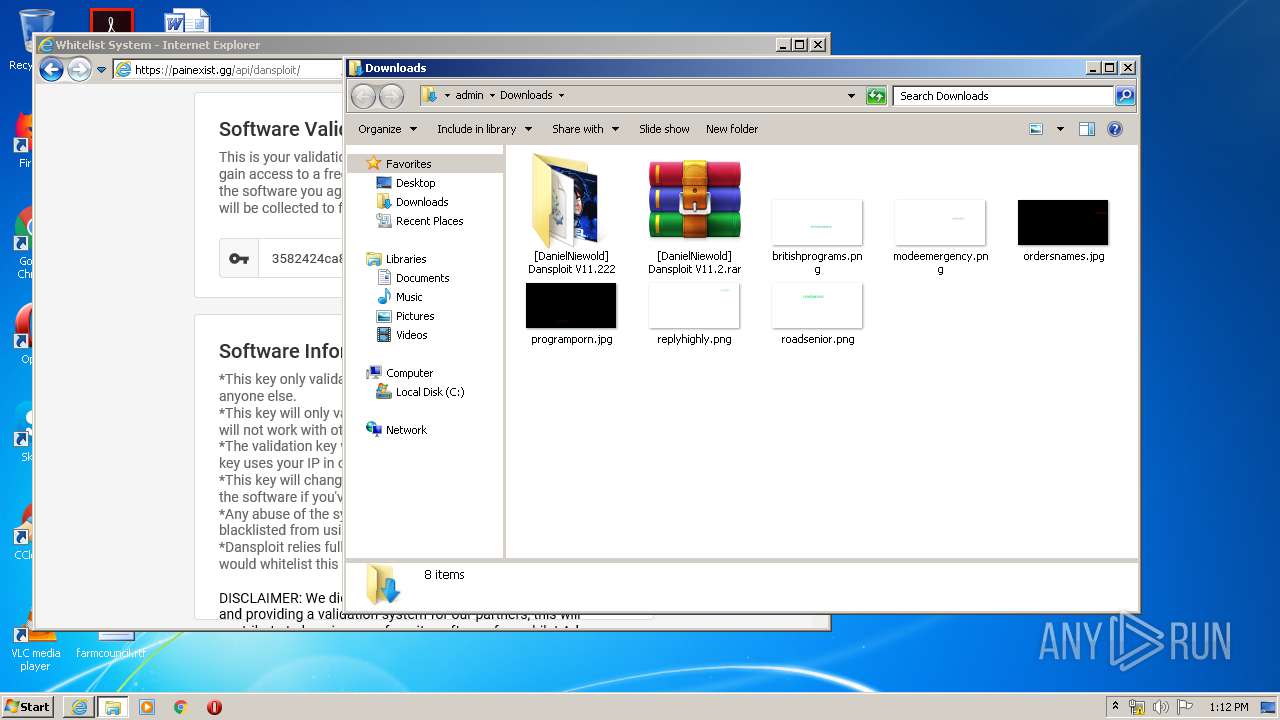
| 3536 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\[DanielNiewold] Dansploit V11.2.rar" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3664 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
11 014
Read events
2 198
Write events
5 971
Delete events
2 845
Modification events
| (PID) Process: | (2736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3589548896 | |||
| (PID) Process: | (2736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30794149 | |||
| (PID) Process: | (2736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
10
Suspicious files
134
Text files
213
Unknown types
63
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2084 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\ATAW4WDX.txt | — | |
MD5:— | SHA256:— | |||
| 2084 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\22ETW4VR.txt | — | |
MD5:— | SHA256:— | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2084 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[1].htm | — | |
MD5:— | SHA256:— | |||
| 2084 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsmlUHQQV3WH.xml | xml | |
MD5:9116ACCA5CD0FE3DB67FEF93724A831F | SHA256:9E592B97A54570994764DDCFCABBEE86A48B552FF1FDC842E2E328C71697EB33 | |||
| 2084 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[7].xml | xml | |
MD5:30960748DDBFAD393733F06733B41025 | SHA256:A99AFDEF443D0C37918B30224E149AE440992BA0A0A3878C02083654EBB1B0E0 | |||
| 2084 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\Z7401AIY.txt | text | |
MD5:90703B1FE7726C930D8537D05E0DB742 | SHA256:01470D8C44A0552638242B341A0C08166E578F86415E0F05E90FC62A73E17469 | |||
| 2084 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[2].xml | xml | |
MD5:DEE32D0AB592251C01A7C348C35CE4CD | SHA256:D40DB7BC1CA4171A28A5CD43AFA4AB300D4CDB4B2EB7A40F8A0F3AFD0DCBF660 | |||
| 2084 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[5].xml | xml | |
MD5:376B99B1C74F943FA7861B3E5BE3707A | SHA256:3E572CEFDA4AB741EAE93A7305731FB140DEE856C0A0B709A98571176BF8EA3B | |||
| 2084 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\O2L5O031.txt | text | |
MD5:05117371A786AC6B304701C40403B5FA | SHA256:94D5568D74A832FA575040D9DEDDD72C8C34B1A0C2589A81A9BECD119982C59C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
98
TCP/UDP connections
145
DNS requests
49
Threats
0
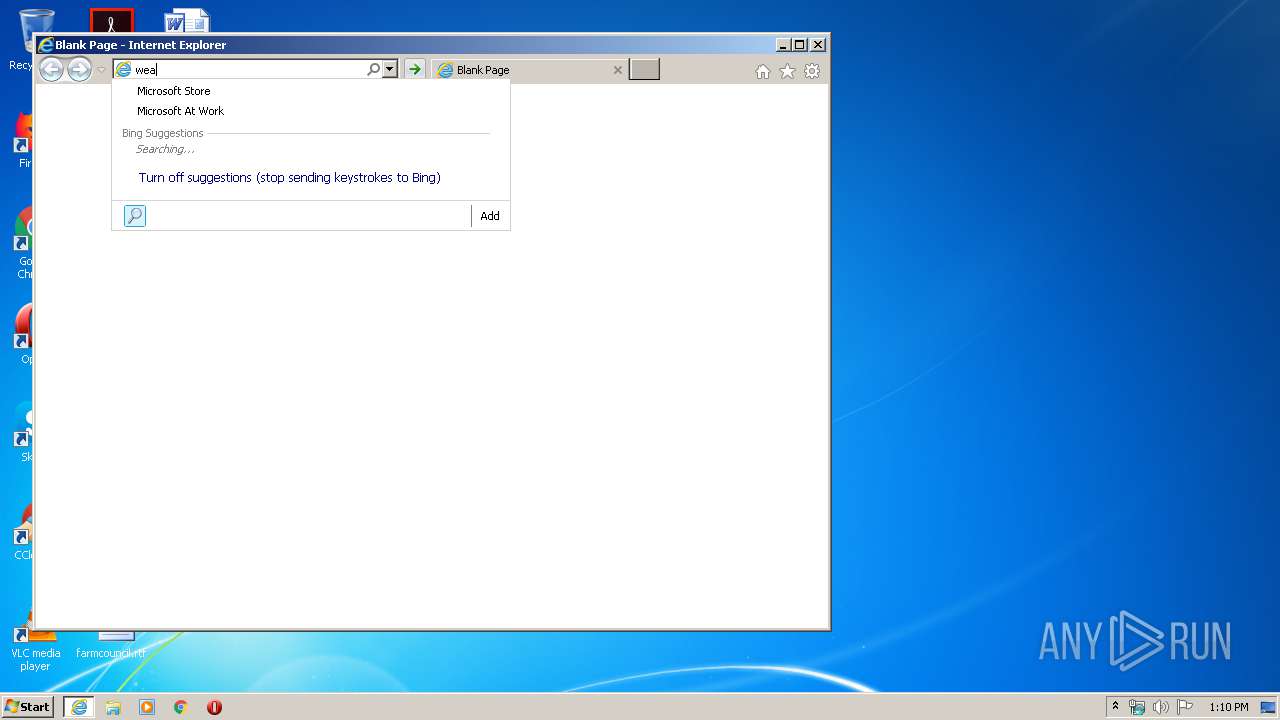
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
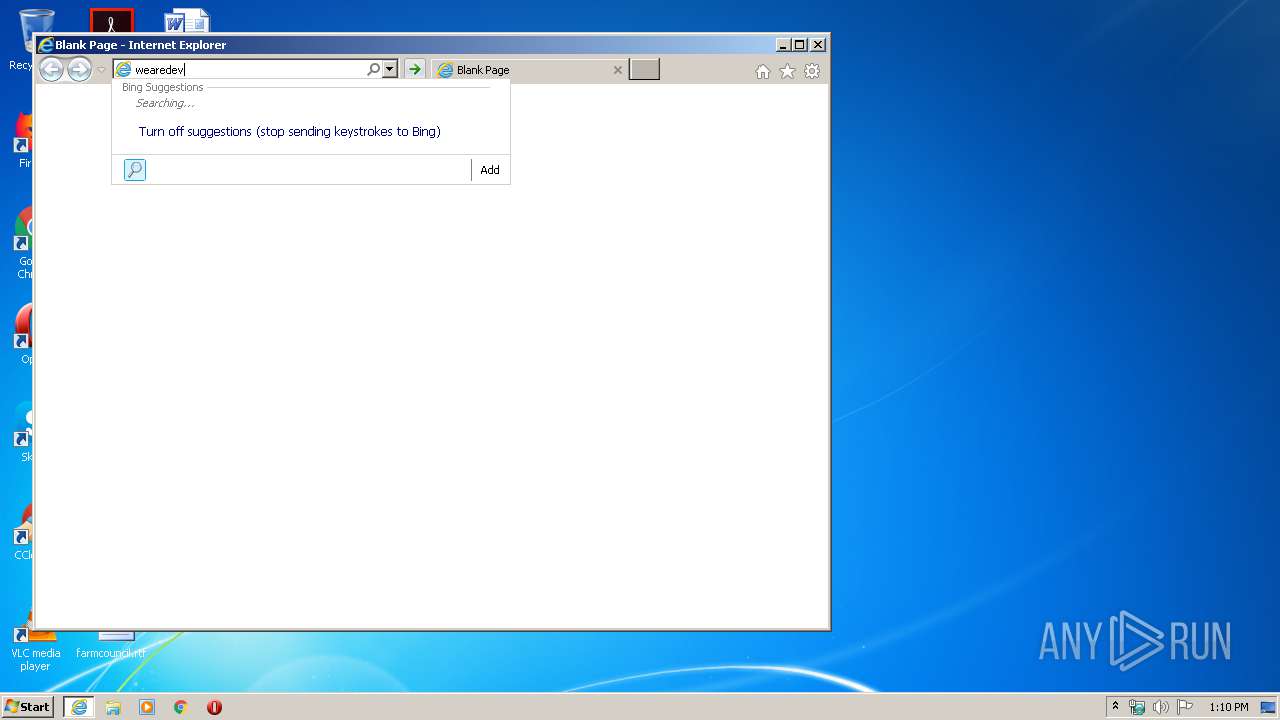
2084 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=wear&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 226 b | whitelisted |
2084 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=weared&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
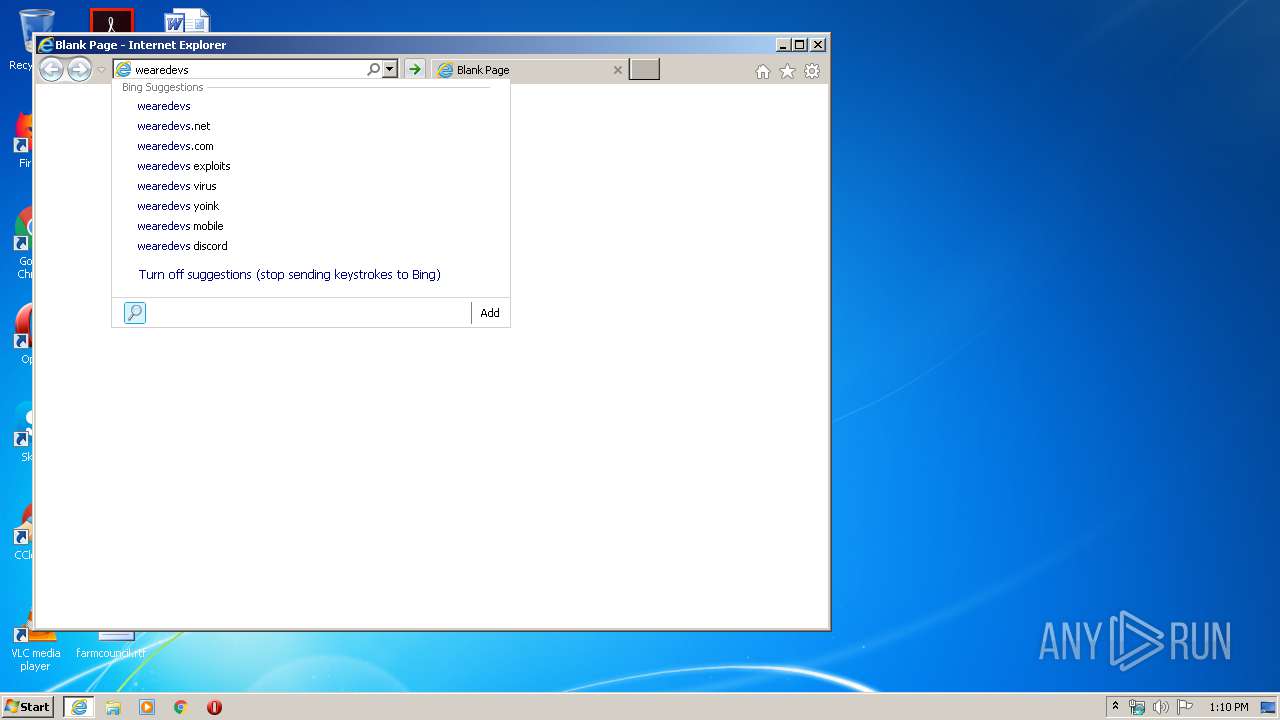
2084 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=wearedevs&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 227 b | whitelisted |
2736 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2084 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=wearedevs.ne&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 216 b | whitelisted |
2084 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=wearedevs.net&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 218 b | whitelisted |
2084 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=wearedevs.&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 216 b | whitelisted |
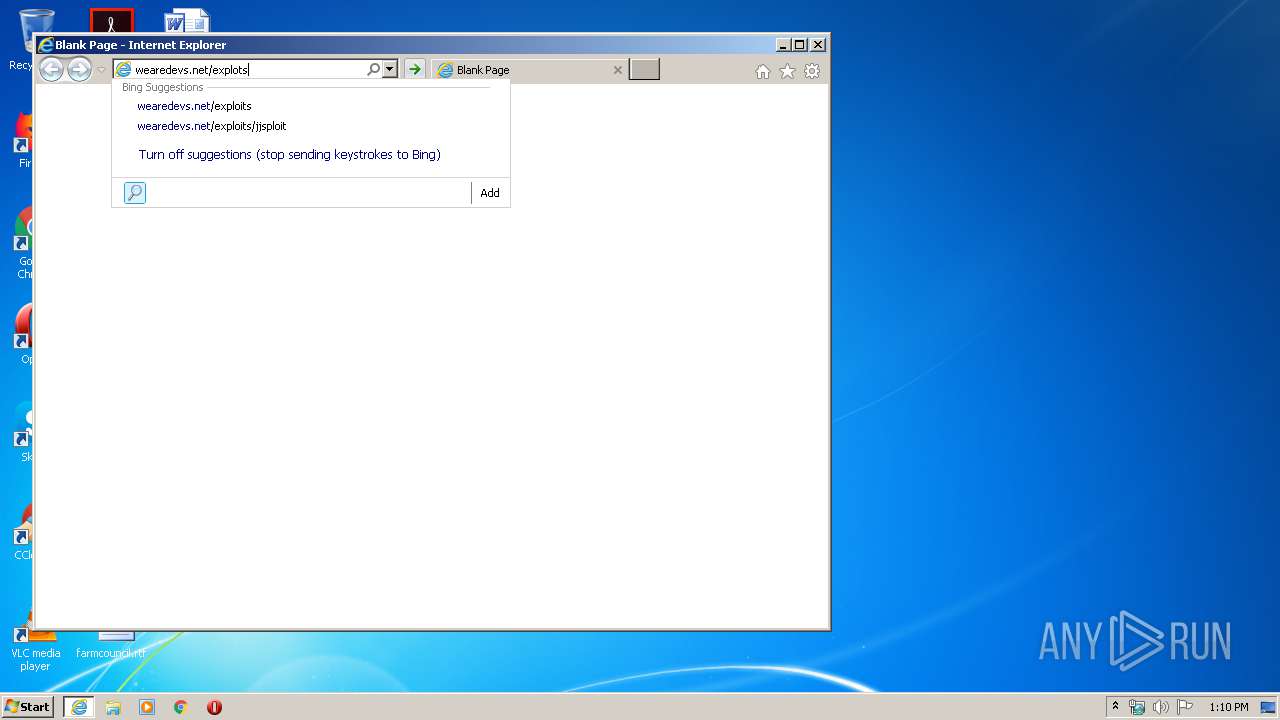
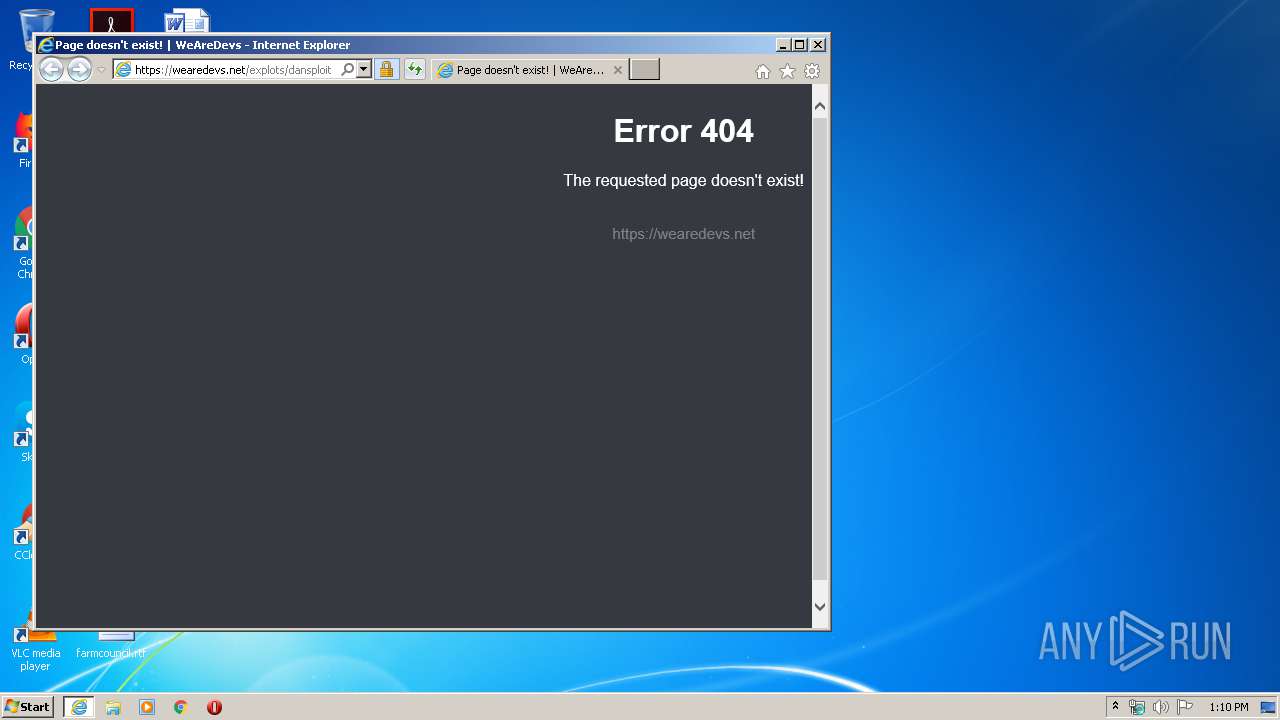
2084 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=wearedevs.net%2Fexplots%2Fdan&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 176 b | whitelisted |
2084 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=wearedevs.n&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 213 b | whitelisted |
2084 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=wearedevs.net%2F&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 229 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2084 | iexplore.exe | 172.217.21.194:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2084 | iexplore.exe | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
2736 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
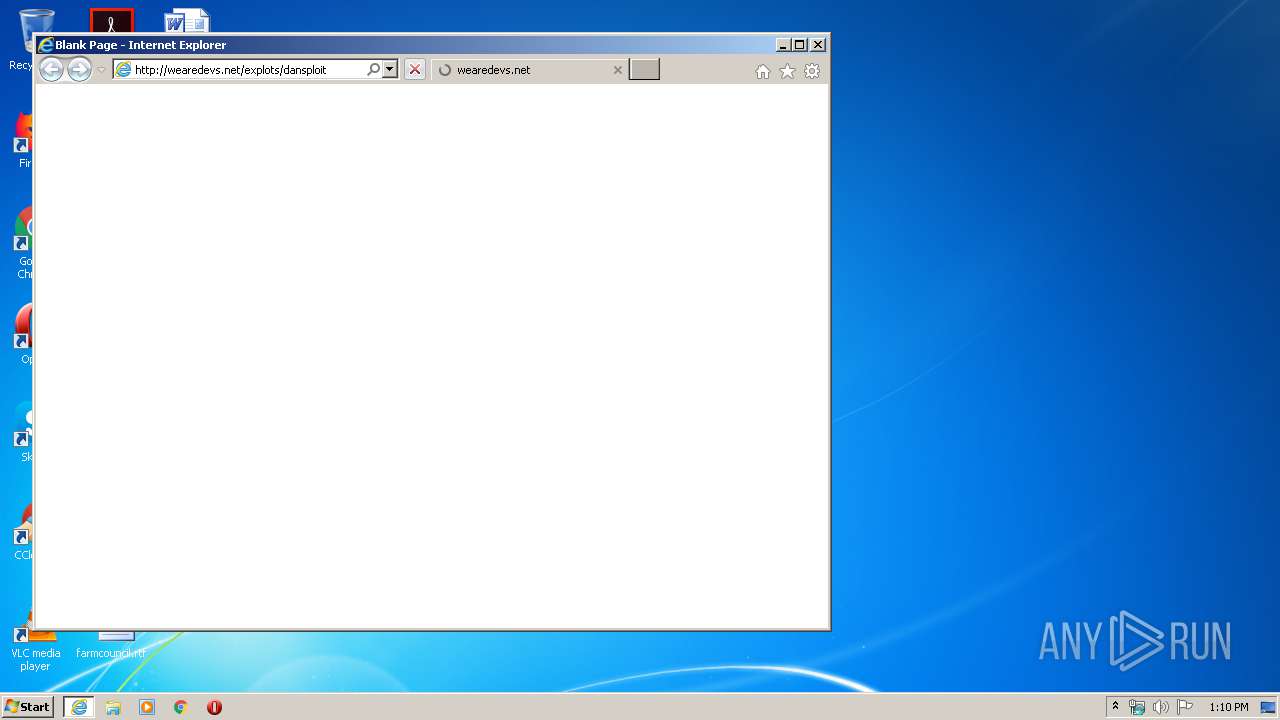
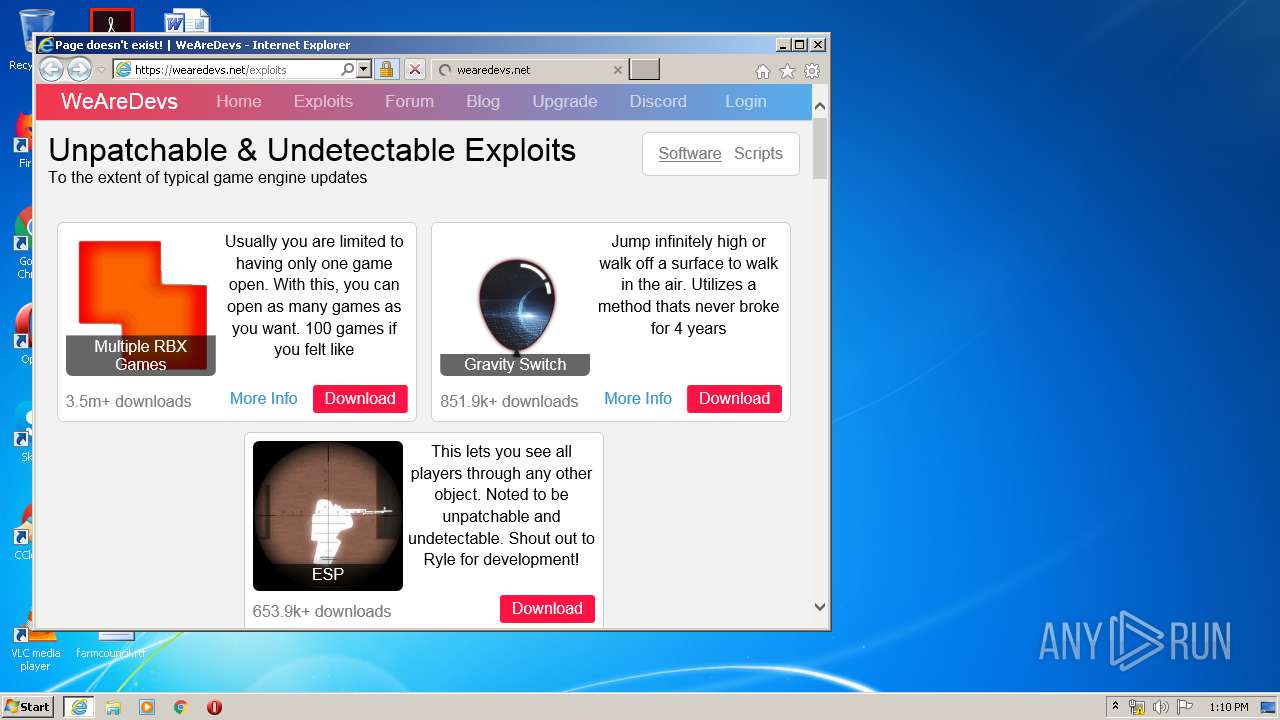
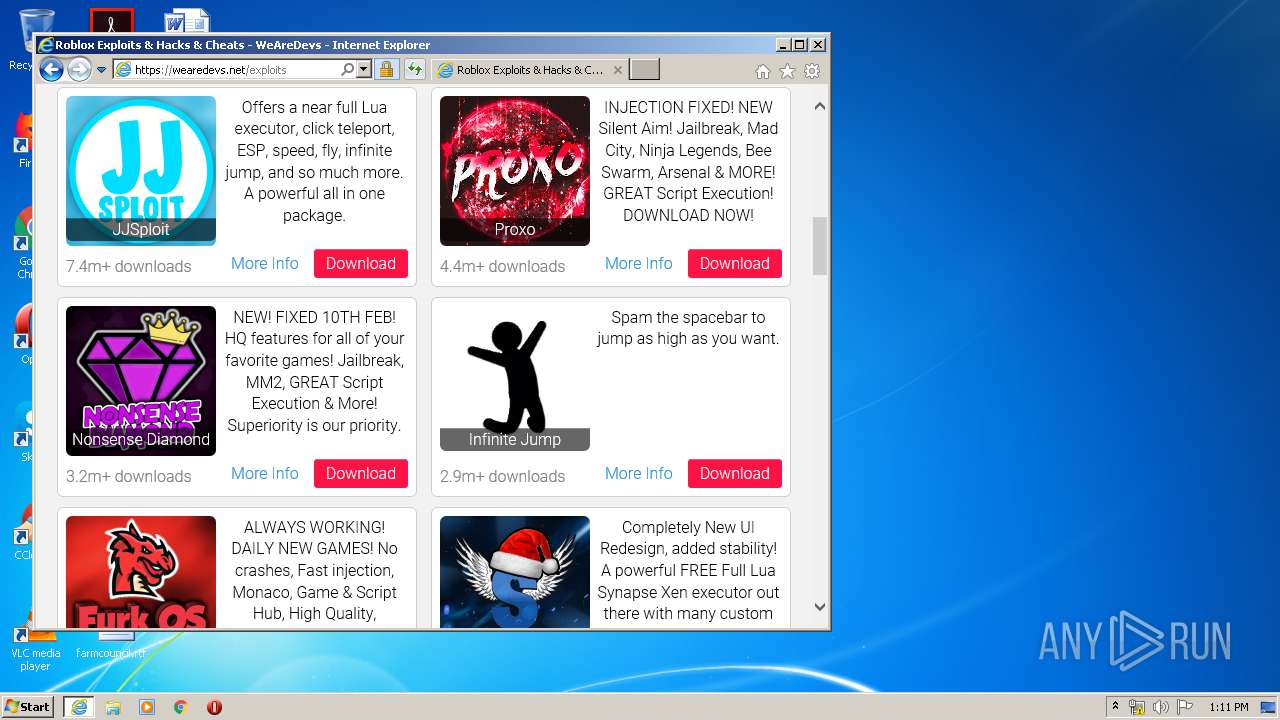
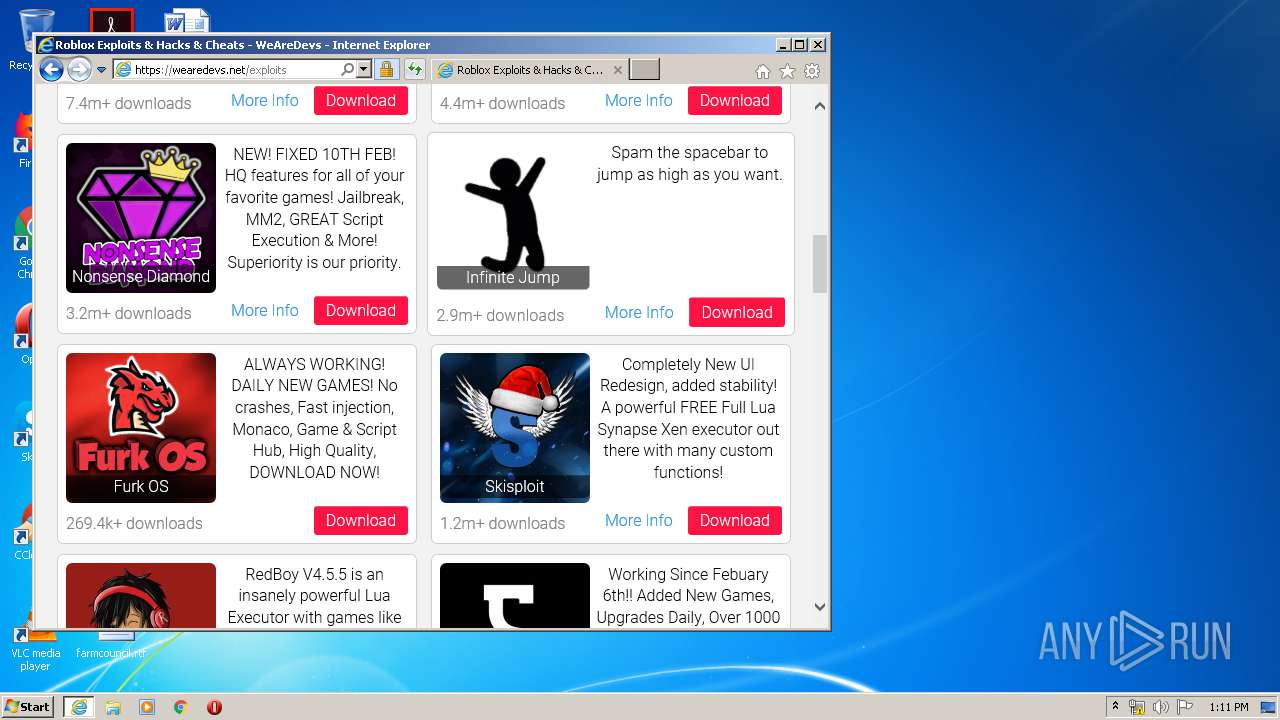
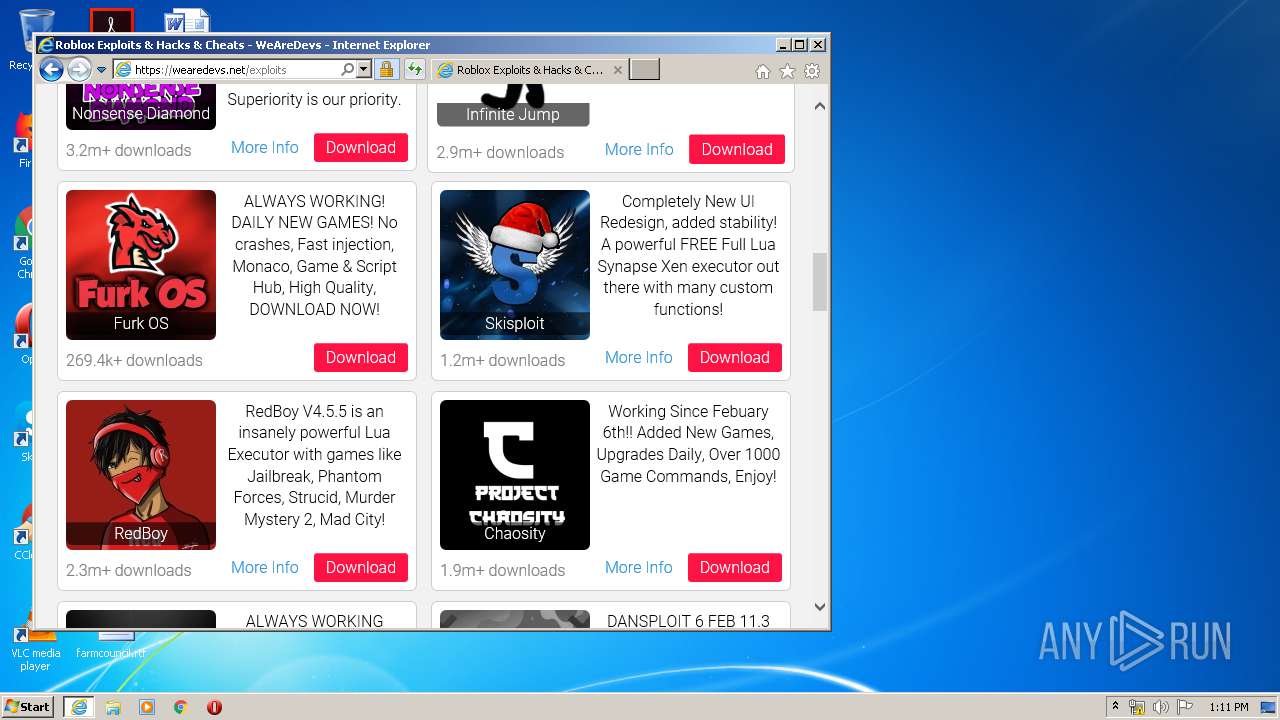
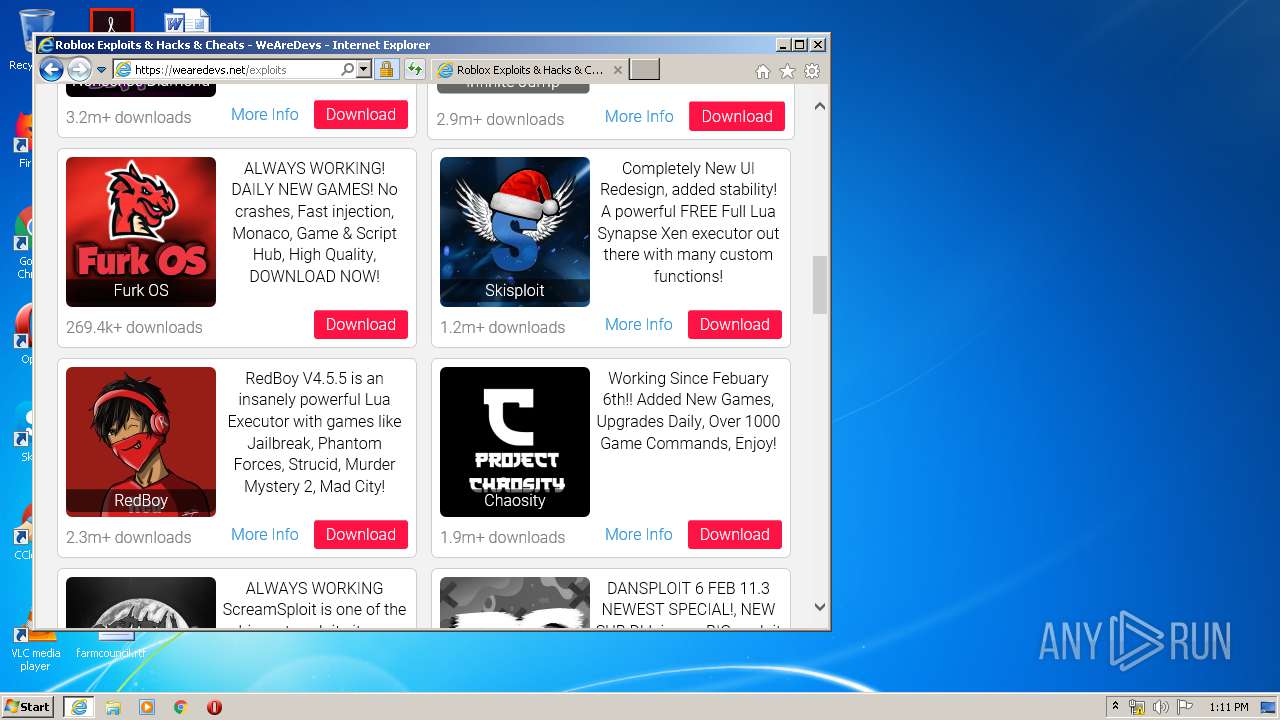
2084 | iexplore.exe | 104.26.6.147:80 | wearedevs.net | Cloudflare Inc | US | suspicious |
2084 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2084 | iexplore.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2084 | iexplore.exe | 172.217.23.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2084 | iexplore.exe | 104.26.6.147:443 | wearedevs.net | Cloudflare Inc | US | suspicious |
2084 | iexplore.exe | 172.217.21.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2084 | iexplore.exe | 172.217.23.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
wearedevs.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |