| File name: | ayvhl.pif |
| Full analysis: | https://app.any.run/tasks/1b25db4b-cfaf-4820-9929-7d7eda3d503c |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2024, 09:45:12 |
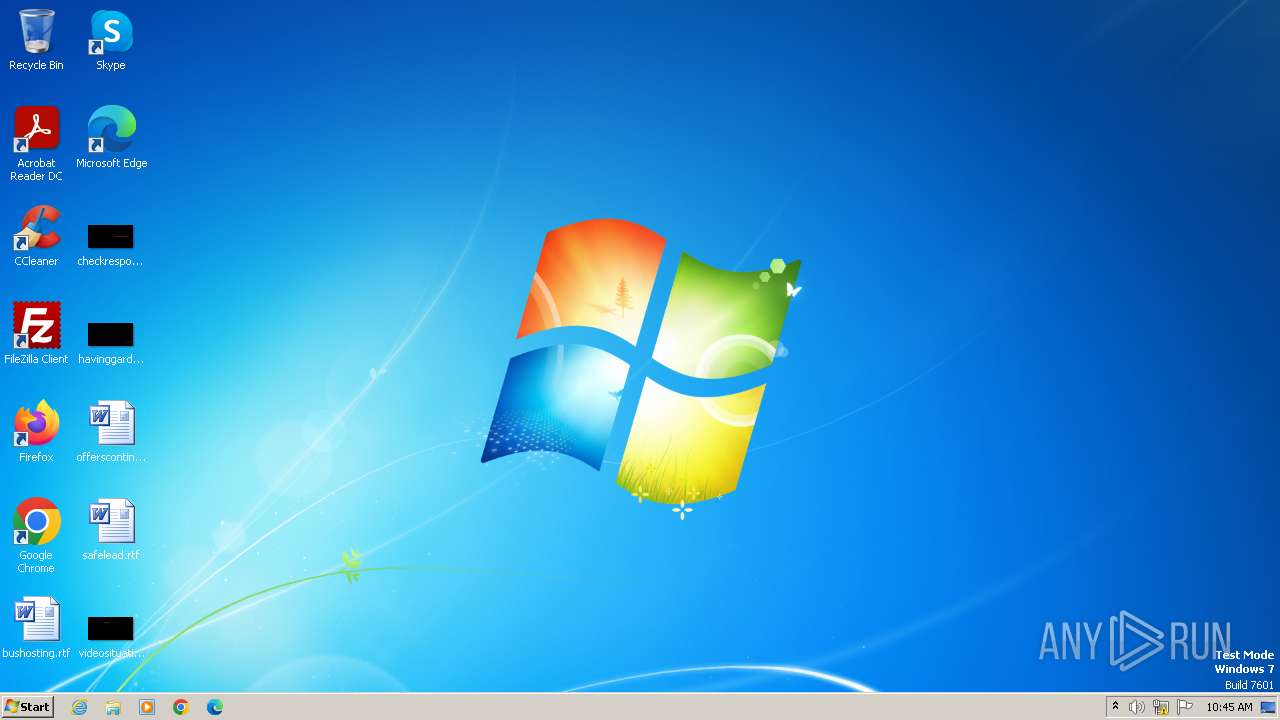
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 911AAB5D52CB7F1ACF18B262B2EF952C |
| SHA1: | D5813DFDE9DE5DA23D5B6B0C39CCC0E0CE50EF11 |
| SHA256: | 10E0AA48BA33EFD6D7300D1E7416884886EA10330CF6AB556C41193D1D5F69EC |
| SSDEEP: | 3072:5UP692HadMoIPFXvTyKyl3K4qbflaJA9kNF4sQ4Q:5UiGoI9L5yl3K4qzlaJe24x |
MALICIOUS
Application was injected by another process
- dwm.exe (PID: 544)
- taskeng.exe (PID: 296)
- explorer.exe (PID: 1180)
- ctfmon.exe (PID: 1416)
Runs injected code in another process
- ayvhl.pif.exe (PID: 3968)
Drops the executable file immediately after the start
- ayvhl.pif.exe (PID: 3968)
Changes appearance of the Explorer extensions
- ayvhl.pif.exe (PID: 3968)
UAC/LUA settings modification
- ayvhl.pif.exe (PID: 3968)
Changes Security Center notification settings
- ayvhl.pif.exe (PID: 3968)
SUSPICIOUS
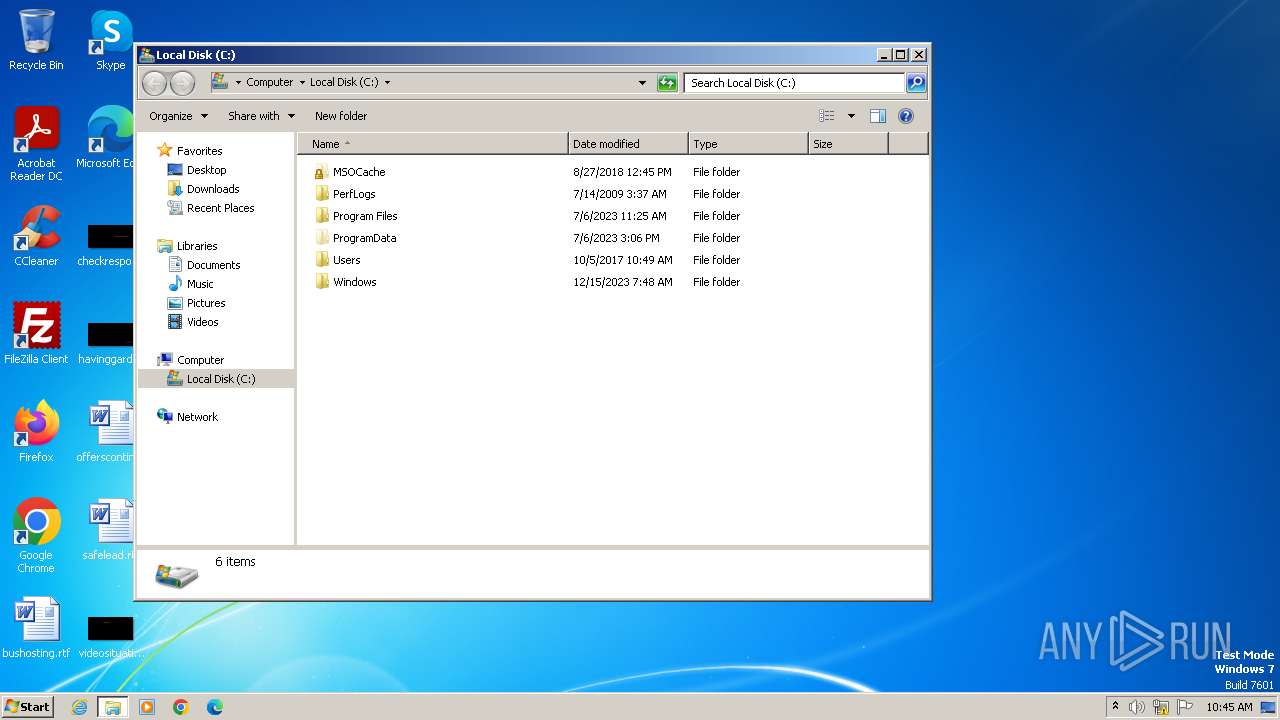
Creates file in the systems drive root
- explorer.exe (PID: 1180)
- ayvhl.pif.exe (PID: 3968)
Executable content was dropped or overwritten
- ayvhl.pif.exe (PID: 3968)
INFO
Checks supported languages
- ayvhl.pif.exe (PID: 3968)
Reads the machine GUID from the registry
- ayvhl.pif.exe (PID: 3968)
Reads security settings of Internet Explorer
- explorer.exe (PID: 1180)
Reads the Internet Settings
- explorer.exe (PID: 1180)
Create files in a temporary directory
- ayvhl.pif.exe (PID: 3968)
Reads the computer name
- ayvhl.pif.exe (PID: 3968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | DOS Executable Generic (100) |
|---|
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2002:02:10 13:15:37+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 512 |
| InitializedDataSize: | - |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1040 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
32
Monitored processes
5
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | taskeng.exe {7D66FB6A-BD74-4FE5-8B2A-4F4BBBAF9944} | C:\Windows\System32\taskeng.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 544 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1180 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1416 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3968 | "C:\Users\admin\AppData\Local\Temp\ayvhl.pif.exe" | C:\Users\admin\AppData\Local\Temp\ayvhl.pif.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
6 116
Read events
6 046
Write events
70
Delete events
0
Modification events
| (PID) Process: | (1180) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1180) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 01000000070000000200000006000000000000000B0000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1180) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000A8FA8805F9782D42A5F5C018EB4C458500000000020000000000106600000001000020000000CC2C5962345B04662569F6110A11B982E2AADBE61B97C5EC585E7782BED6DE56000000000E8000000002000020000000CC526F5DE046083A6CF743D0D997A369F692FB43AB216B12DEF6517D455D24EB3000000005CA8A0D78890B1096F81861BE0797F00EE759EEFD8160E5FF87D81C129B525EC4E21FF47BB1A51EFB6BC964081304C74000000065B2C403CC15A8281030397FB72FDB7B1B55CA5C3FCC595358AF41A23BC2940A84FAC9CA39F0446F5F37F9B5E92B1803548B151F35459502781916A0D4362741 | |||
| (PID) Process: | (1180) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (1180) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\34\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (3968) ayvhl.pif.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | Hidden |
Value: 2 | |||
| (PID) Process: | (3968) ayvhl.pif.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusOverride |
Value: 1 | |||
| (PID) Process: | (3968) ayvhl.pif.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusDisableNotify |
Value: 1 | |||
| (PID) Process: | (3968) ayvhl.pif.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | FirewallDisableNotify |
Value: 1 | |||
| (PID) Process: | (3968) ayvhl.pif.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | FirewallOverride |
Value: 1 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | ayvhl.pif.exe | C:\Windows\SYSTEM.INI | binary | |
MD5:18F05FC655DB3C2141E0BF670BBAD37E | SHA256:A9C364D95FC38D55FC1CD1860DFF4ED1AB2BD09BC3FF48F4B3171B549A184CC1 | |||
| 3968 | ayvhl.pif.exe | C:\Users\admin\AppData\Local\Temp\wincmvtc.exe | executable | |
MD5:25AA9BB549ECC7BB6100F8D179452508 | SHA256:DF83A0D6940600E4C4954F4874FCD4DD73E781E6690C3BF56F51C95285484A3C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |