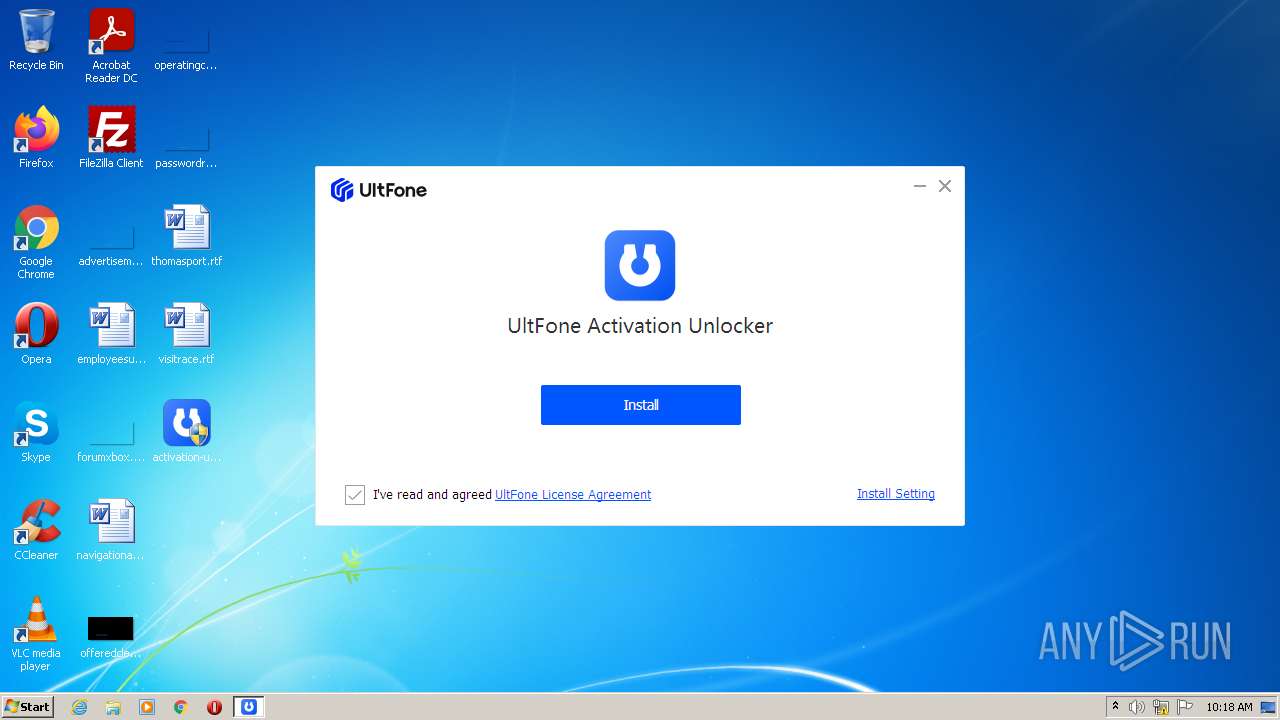
| File name: | activation-unlocker.exe |
| Full analysis: | https://app.any.run/tasks/3a0e4d07-aca5-4f5f-b94a-d92b8c73cb1b |
| Verdict: | Malicious activity |
| Analysis date: | July 28, 2022, 09:17:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 51E129D5D7FF7FB91951981C07DF1425 |
| SHA1: | C006D22ADFDCEA489D0F6296C507A513B7DE2BDE |
| SHA256: | 10E09B6CE7F0B46257174DF3364BE6AAD8C00F0A6795EC41453C94D47117DC33 |
| SSDEEP: | 49152:E4mj8j13MWUfnZcHp+I2ZBTMhvrJHOlqRVA0JcVPE3dVpvwGhf:WmM7BcJX23MKeVA9VM3L9Jf |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- activation-unlocker.exe (PID: 3224)
Reads the computer name
- activation-unlocker.exe (PID: 3224)
Reads Environment values
- activation-unlocker.exe (PID: 3224)
Checks for external IP
- activation-unlocker.exe (PID: 3224)
INFO
Reads settings of System Certificates
- activation-unlocker.exe (PID: 3224)
Checks Windows Trust Settings
- activation-unlocker.exe (PID: 3224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| ProductName: | 20211218142510 |
|---|---|
| FileDescription: | UltFone Activation Unlocker |
| ProductVersion: | 2.6.0.5 |
| LegalCopyright: | Copyright © 2007-2021 UltFone Co.,Ltd. |
| FileVersion: | 2.6.0.5 |
| CompanyName: | UltFone Co., Ltd. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 2.6.0.5 |
| FileVersionNumber: | 2.6.0.5 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x3871a0 |
| UninitializedDataSize: | 2064384 |
| InitializedDataSize: | 249856 |
| CodeSize: | 1634304 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2021:12:18 07:25:33+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Dec-2021 06:25:33 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000150 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 18-Dec-2021 06:25:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x001F8000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x001F9000 | 0x0018F000 | 0x0018E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.91116 |
.rsrc | 0x00388000 | 0x0003D000 | 0x0003C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.63931 |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2504 | "C:\Users\admin\Desktop\activation-unlocker.exe" | C:\Users\admin\Desktop\activation-unlocker.exe | — | Explorer.EXE | |||||||||||
User: admin Company: UltFone Co., Ltd. Integrity Level: MEDIUM Description: UltFone Activation Unlocker Exit code: 3221226540 Version: 2.6.0.5 Modules
| |||||||||||||||
| 3224 | "C:\Users\admin\Desktop\activation-unlocker.exe" | C:\Users\admin\Desktop\activation-unlocker.exe | Explorer.EXE | ||||||||||||
User: admin Company: UltFone Co., Ltd. Integrity Level: HIGH Description: UltFone Activation Unlocker Exit code: 0 Version: 2.6.0.5 Modules
| |||||||||||||||
Total events
4 918
Read events
4 871
Write events
47
Delete events
0
Modification events
| (PID) Process: | (3224) activation-unlocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3224) activation-unlocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3224) activation-unlocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3224) activation-unlocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3224) activation-unlocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3224) activation-unlocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3224) activation-unlocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3224) activation-unlocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3224) activation-unlocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3224) activation-unlocker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
0
Suspicious files
4
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3224 | activation-unlocker.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9FF67FB3141440EED32363089565AE60_5254E016A8D8A25F217615AF6D5E3C4B | der | |
MD5:— | SHA256:— | |||
| 3224 | activation-unlocker.exe | C:\Users\admin\AppData\Local\Temp\TS_GetDownloaderInfo.log | text | |
MD5:— | SHA256:— | |||
| 3224 | activation-unlocker.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9FF67FB3141440EED32363089565AE60_5254E016A8D8A25F217615AF6D5E3C4B | binary | |
MD5:— | SHA256:— | |||
| 3224 | activation-unlocker.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\210AXXCG.txt | text | |
MD5:— | SHA256:— | |||
| 3224 | activation-unlocker.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3224 | activation-unlocker.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 3224 | activation-unlocker.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 3224 | activation-unlocker.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
16
DNS requests
6
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3224 | activation-unlocker.exe | GET | — | 104.18.25.249:80 | http://www.tenorshare.com/downloads/service/softwarelog.txt | US | — | — | whitelisted |
3224 | activation-unlocker.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3224 | activation-unlocker.exe | GET | — | 104.18.25.249:80 | http://www.tenorshare.com/downloads/service/softwarelog.txt | US | — | — | whitelisted |
3224 | activation-unlocker.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAuykd09tnRVq%2BfZSwVO%2BVg%3D | US | der | 279 b | whitelisted |
3224 | activation-unlocker.exe | POST | 200 | 142.250.179.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
3224 | activation-unlocker.exe | POST | 200 | 142.250.179.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
3224 | activation-unlocker.exe | POST | 200 | 142.250.179.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
3224 | activation-unlocker.exe | POST | 200 | 142.250.179.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
3224 | activation-unlocker.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?da650993c166bf29 | US | compressed | 4.70 Kb | whitelisted |
3224 | activation-unlocker.exe | POST | 200 | 142.250.179.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3224 | activation-unlocker.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3224 | activation-unlocker.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
3224 | activation-unlocker.exe | 104.18.25.249:80 | www.tenorshare.com | Cloudflare Inc | US | suspicious |
3224 | activation-unlocker.exe | 104.18.24.30:443 | check.mobie.app | Cloudflare Inc | US | unknown |
3224 | activation-unlocker.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3224 | activation-unlocker.exe | 142.250.179.78:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
check.mobie.app |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.tenorshare.com |
| whitelisted |
ip-api.com |
| malicious |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3224 | activation-unlocker.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
3224 | activation-unlocker.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3224 | activation-unlocker.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
3224 | activation-unlocker.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3224 | activation-unlocker.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3224 | activation-unlocker.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3224 | activation-unlocker.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
4 ETPRO signatures available at the full report