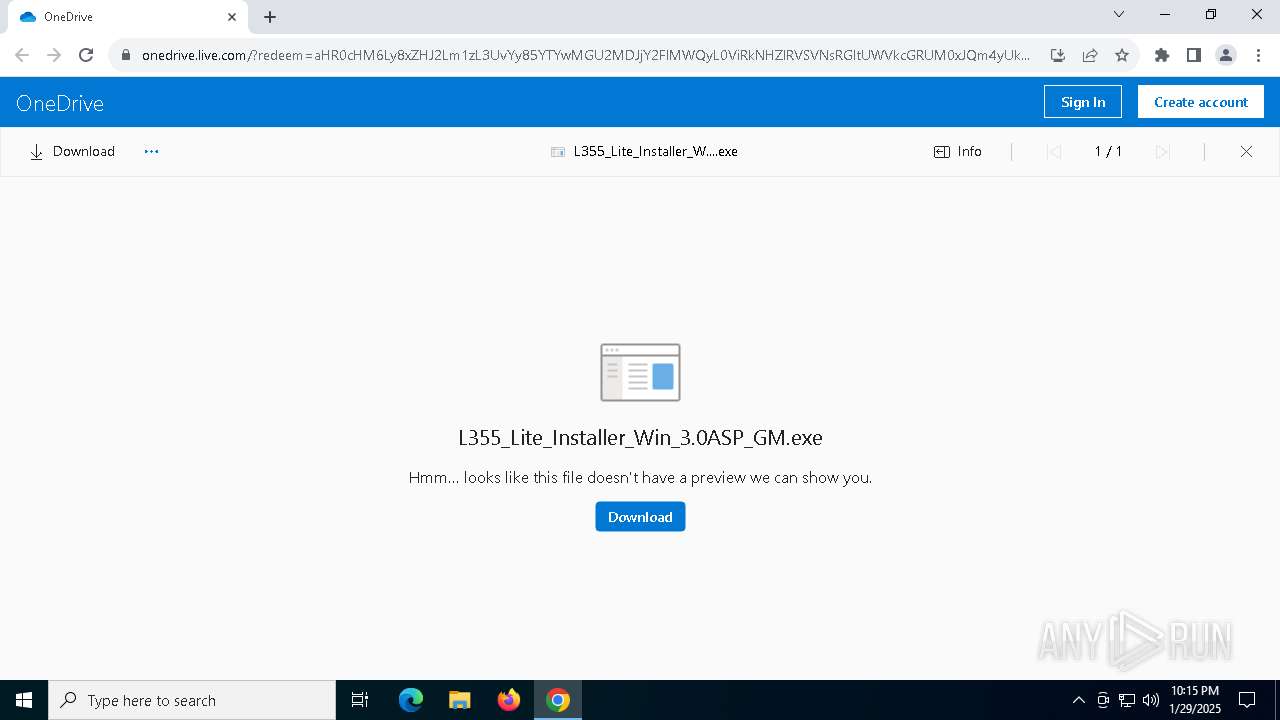
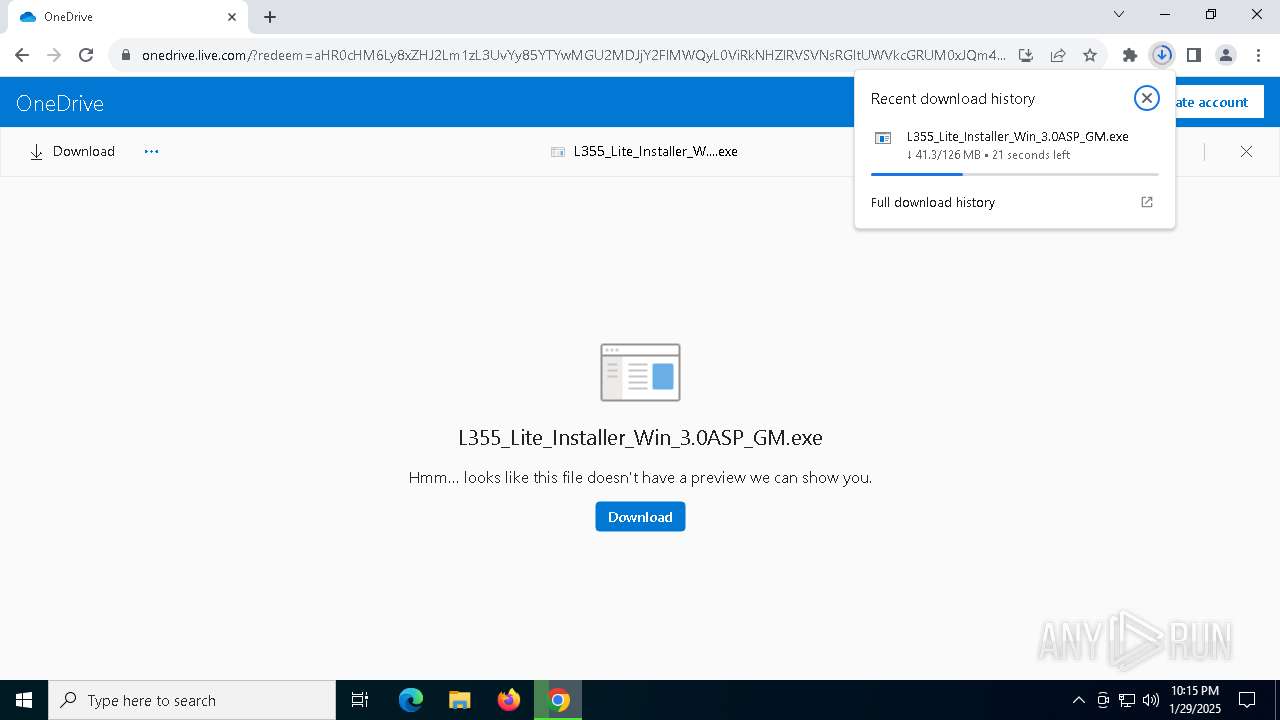
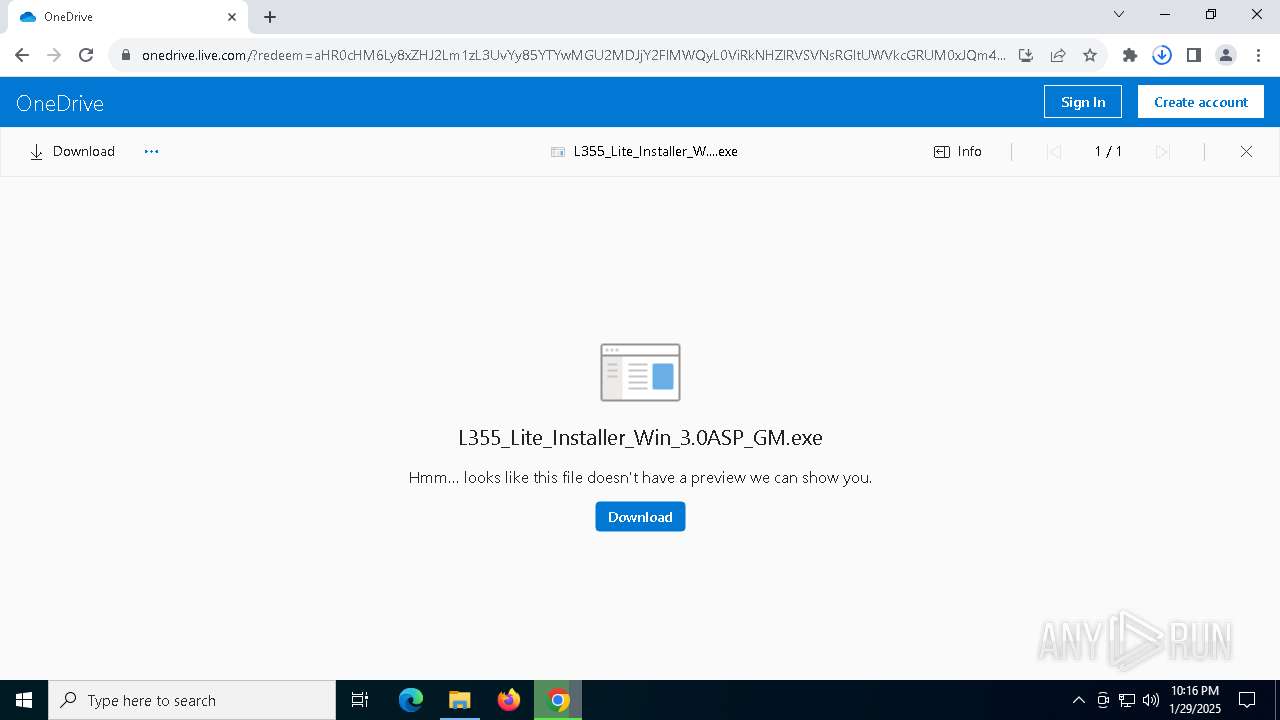
| URL: | https://1drv.ms/u/c/9a600e602ccae1d2/EbFCGfTUISlDimQedpdT3LIBn2RL0R3T_1TLMpu6ggX5kw?e=2M7HMW |
| Full analysis: | https://app.any.run/tasks/4324a226-04a0-4a2c-9c76-e8027ff30cc5 |
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2025, 22:15:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1A5BD5BDF56049FE458D93C611C5BFA8 |
| SHA1: | 5B5D42BD826AFA964A59B3809FF90D10CB1D254D |
| SHA256: | 10CCB5ABC04255963AF9EB43B888B466C8F592F82CF0A8D62DE005CD055AAC01 |
| SSDEEP: | 3:N8qDLIWKfbT/28HN2DX3dRVQtQ2o3y:2qXy33t2DdH2o3y |
MALICIOUS
Executing a file with an untrusted certificate
- Setup.exe (PID: 5980)
- Setup.exe (PID: 6844)
- EPCP.exe (PID: 2904)
- ENPSETUP.EXE (PID: 6316)
- ADSETUP64.EXE (PID: 6600)
- ISBEW64.exe (PID: 6260)
- Setup.exe (PID: 1876)
SUSPICIOUS
Process drops legitimate windows executable
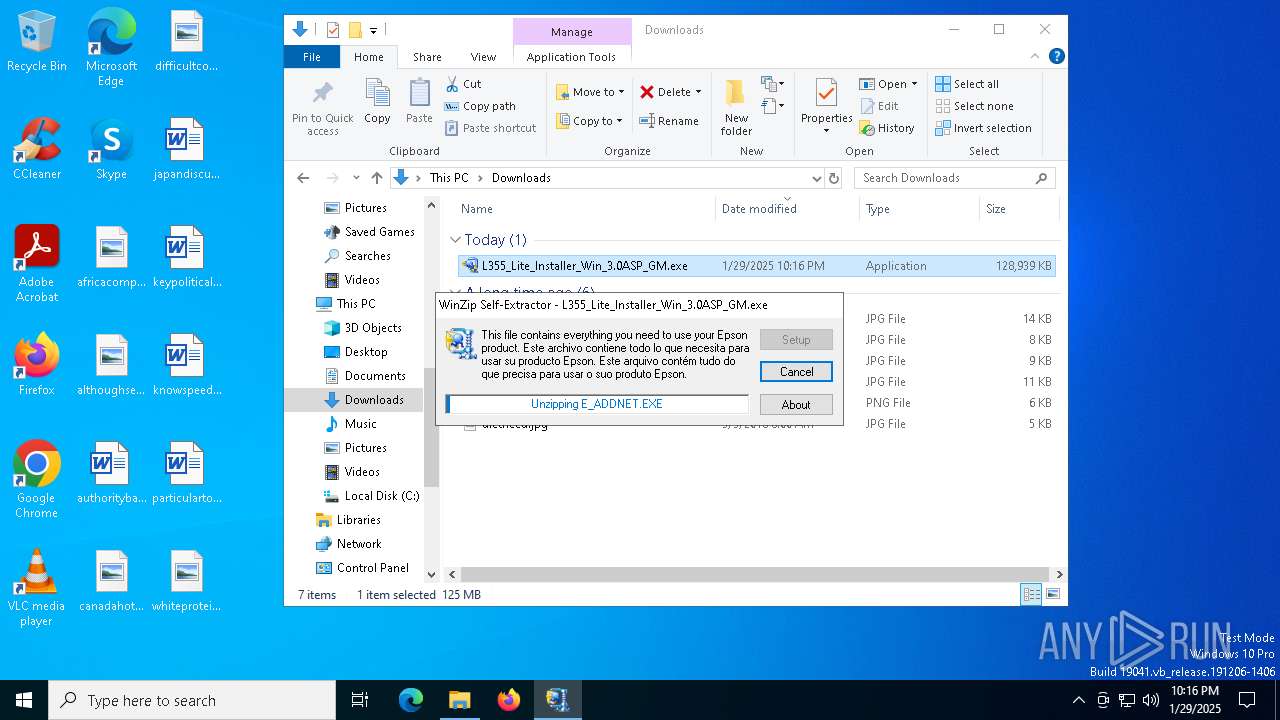
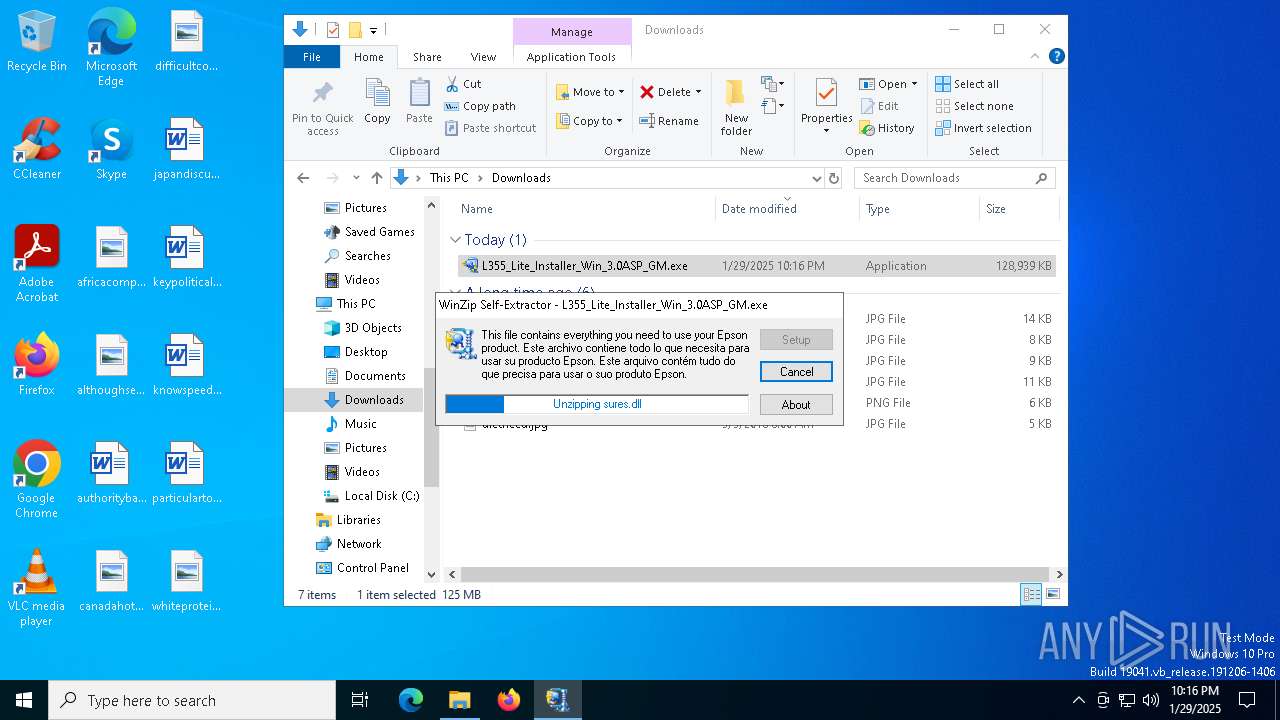
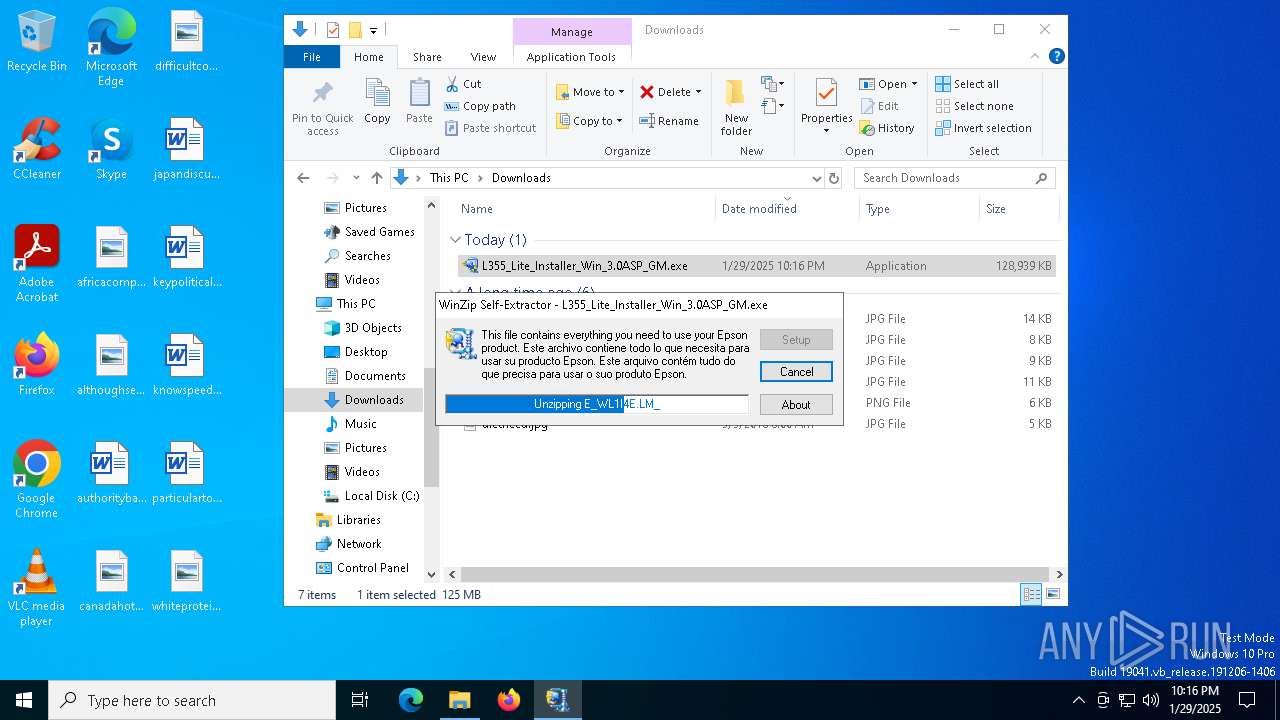
- L355_Lite_Installer_Win_3.0ASP_GM.exe (PID: 900)
- Setup.exe (PID: 5572)
- SETUP64.EXE (PID: 1612)
- drvinst.exe (PID: 5548)
- msiexec.exe (PID: 3692)
- ENPSETUP.EXE (PID: 6316)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 5532)
- Setup.exe (PID: 5572)
- SETUP64.EXE (PID: 1612)
- Setup.exe (PID: 5980)
- Setup.exe (PID: 6844)
- ENPE.exe (PID: 3128)
Executable content was dropped or overwritten
- L355_Lite_Installer_Win_3.0ASP_GM.exe (PID: 900)
- Setup.exe (PID: 5572)
- SETUP64.EXE (PID: 1612)
- drvinst.exe (PID: 5548)
- ENPE.exe (PID: 3128)
- ADSETUP64.EXE (PID: 6600)
- ENPSETUP.EXE (PID: 6316)
- Setup.exe (PID: 5680)
- drvinst.exe (PID: 7052)
Checks Windows Trust Settings
- Setup.exe (PID: 5572)
- SETUP64.EXE (PID: 1612)
- msiexec.exe (PID: 3692)
- drvinst.exe (PID: 5548)
- drvinst.exe (PID: 7052)
There is functionality for taking screenshot (YARA)
- Setup.exe (PID: 5572)
The process drops C-runtime libraries
- L355_Lite_Installer_Win_3.0ASP_GM.exe (PID: 900)
- msiexec.exe (PID: 3692)
Creates files in the driver directory
- drvinst.exe (PID: 5548)
- drvinst.exe (PID: 7052)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3692)
Executes as Windows Service
- VSSVC.exe (PID: 3888)
- EPCP.exe (PID: 3092)
- escsvc64.exe (PID: 6740)
Searches for installed software
- dllhost.exe (PID: 6196)
- ENPSETUP.EXE (PID: 6316)
Creates a software uninstall entry
- ADSETUP64.EXE (PID: 6600)
- ENPSETUP.EXE (PID: 6316)
- Setup.exe (PID: 5680)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 6364)
- msiexec.exe (PID: 3692)
Application launched itself
- chrome.exe (PID: 6364)
Checks supported languages
- ShellExperienceHost.exe (PID: 5532)
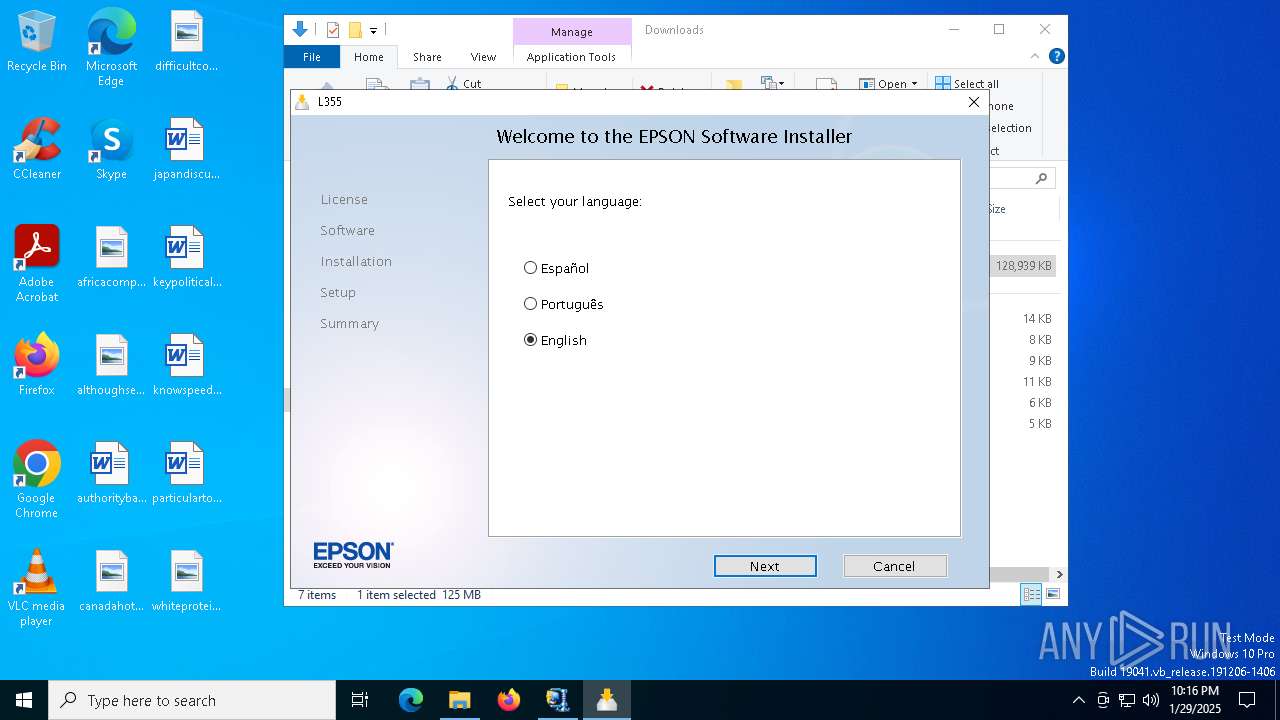
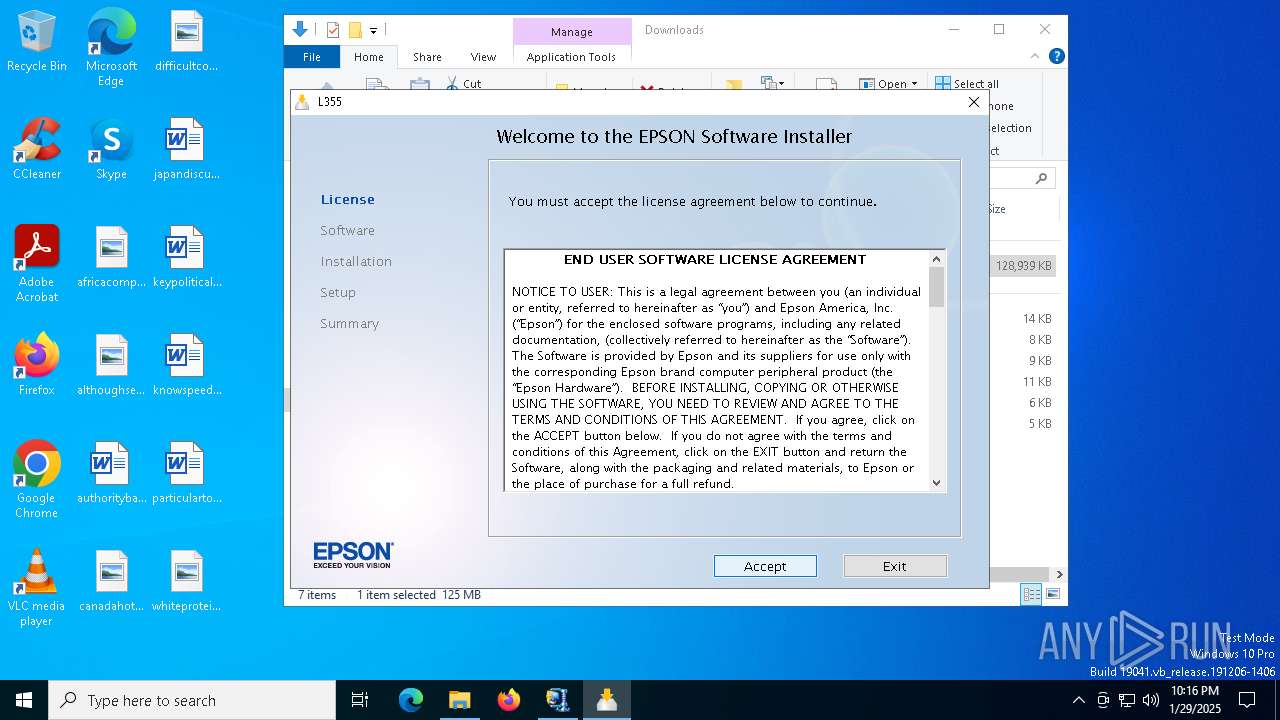
- Setup.exe (PID: 5572)
- L355_Lite_Installer_Win_3.0ASP_GM.exe (PID: 900)
- drvinst.exe (PID: 5548)
- SETUP64.EXE (PID: 1612)
- Setup.exe (PID: 5980)
- msiexec.exe (PID: 3692)
- Setup.exe (PID: 6844)
- msiexec.exe (PID: 7092)
- EPCP.exe (PID: 2904)
- msiexec.exe (PID: 2088)
- ENPE.exe (PID: 3128)
- EPCP.exe (PID: 3092)
- ENPSETUP.EXE (PID: 6316)
- ISBEW64.exe (PID: 6260)
- ADSETUP64.EXE (PID: 6600)
- Setup.exe (PID: 5680)
- drvinst.exe (PID: 7052)
- escsvc64.exe (PID: 6748)
- Setup.exe (PID: 1876)
- msiexec.exe (PID: 3080)
- MSIB33.tmp (PID: 1868)
- escsvc64.exe (PID: 6740)
Reads the computer name
- ShellExperienceHost.exe (PID: 5532)
- L355_Lite_Installer_Win_3.0ASP_GM.exe (PID: 900)
- Setup.exe (PID: 5572)
- SETUP64.EXE (PID: 1612)
- drvinst.exe (PID: 5548)
- Setup.exe (PID: 5980)
- msiexec.exe (PID: 3692)
- Setup.exe (PID: 6844)
- EPCP.exe (PID: 2904)
- msiexec.exe (PID: 2088)
- EPCP.exe (PID: 3092)
- msiexec.exe (PID: 7092)
- ENPE.exe (PID: 3128)
- ENPSETUP.EXE (PID: 6316)
- ISBEW64.exe (PID: 6260)
- ADSETUP64.EXE (PID: 6600)
- Setup.exe (PID: 5680)
- drvinst.exe (PID: 7052)
- escsvc64.exe (PID: 6748)
- escsvc64.exe (PID: 6740)
- msiexec.exe (PID: 3080)
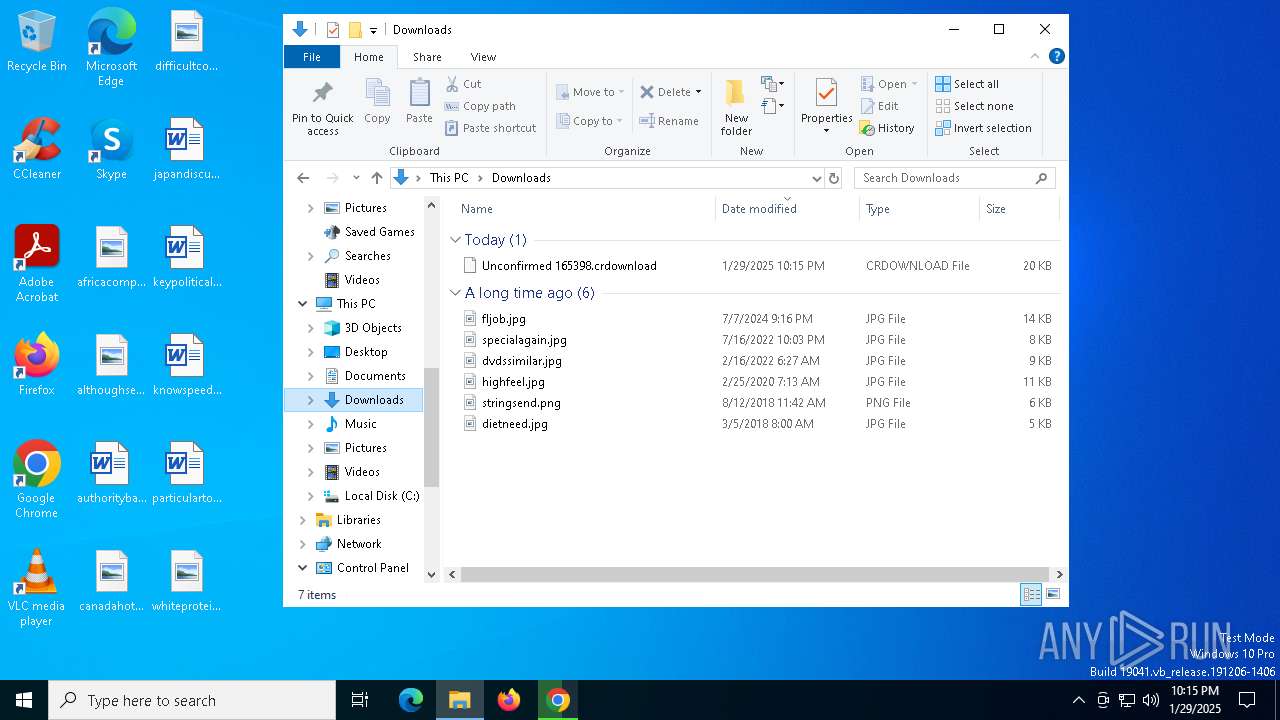
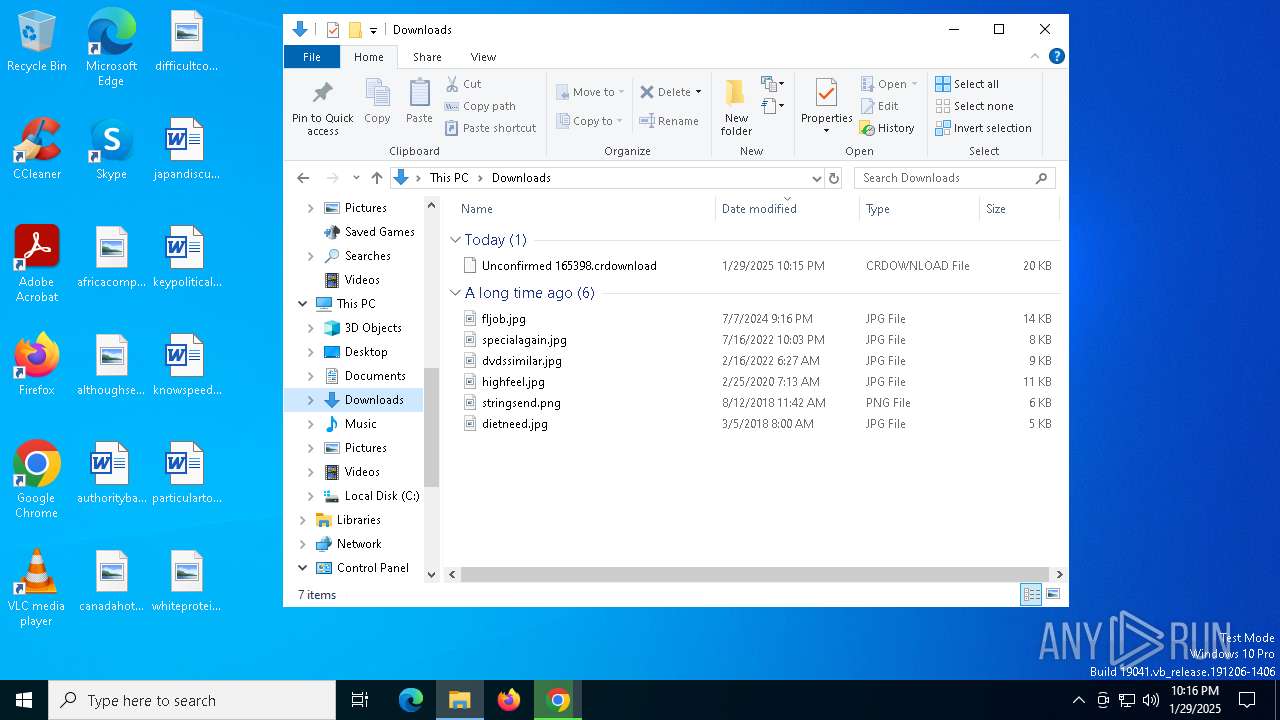
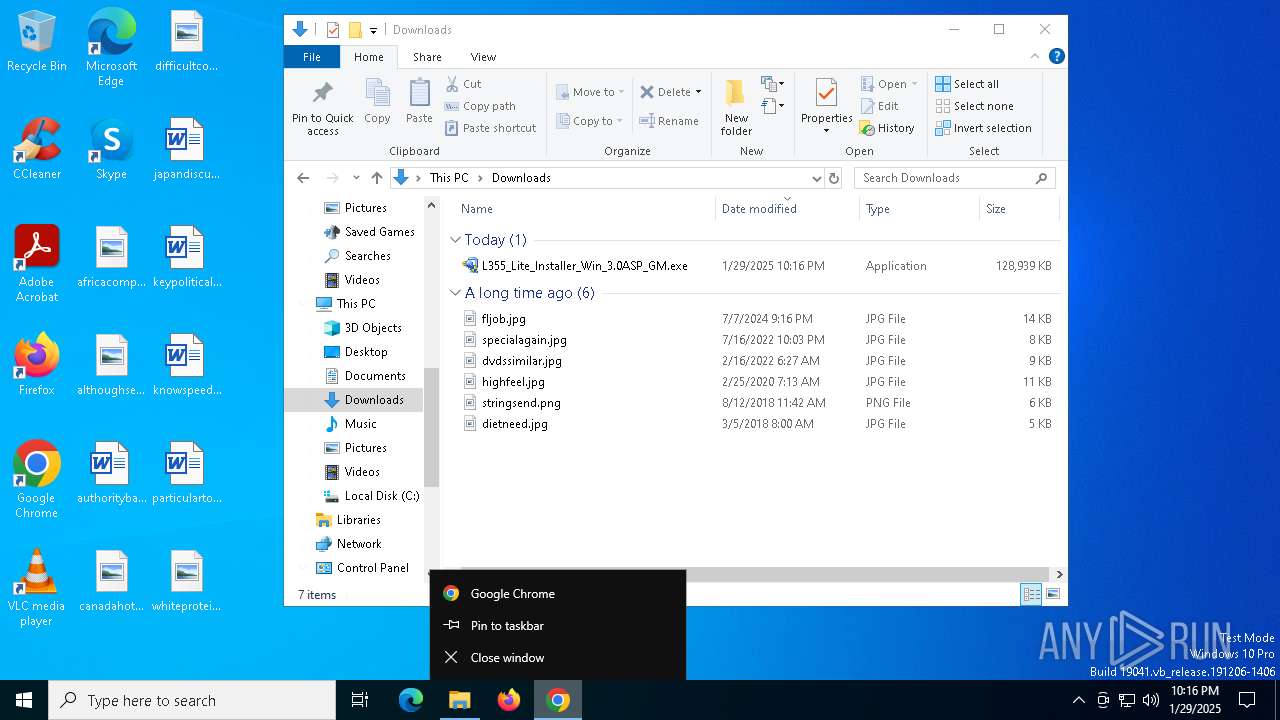
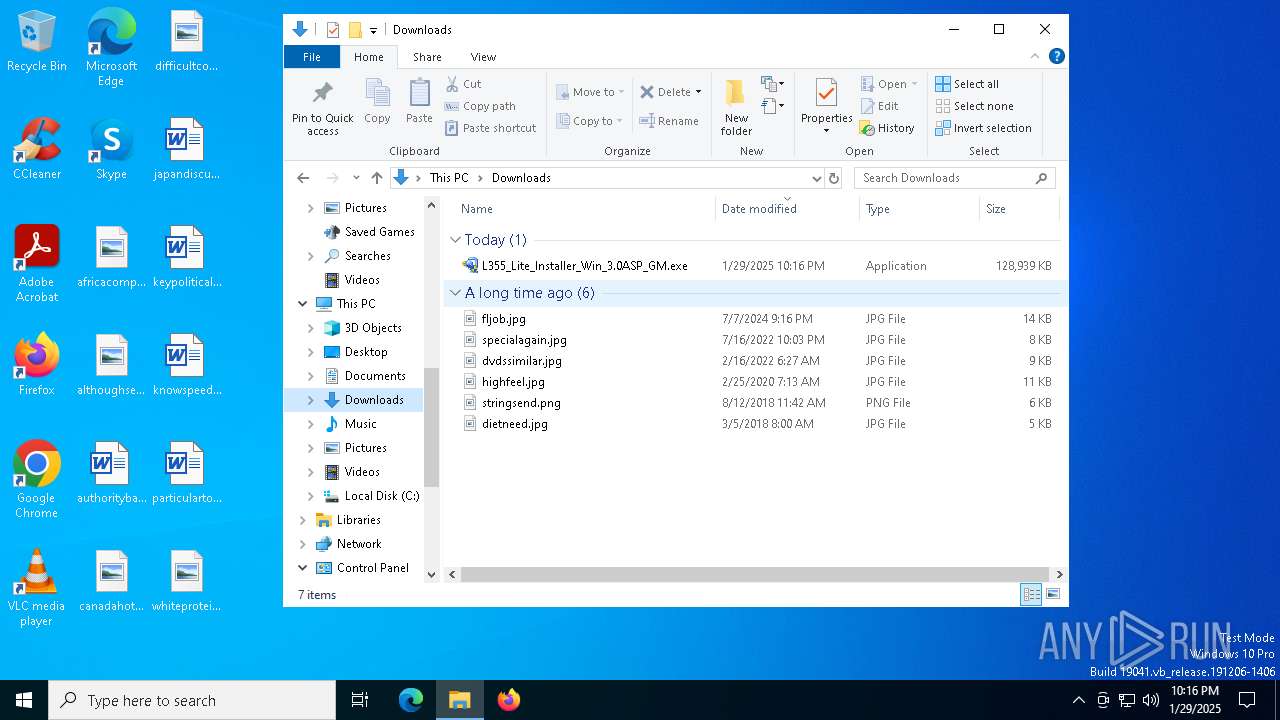
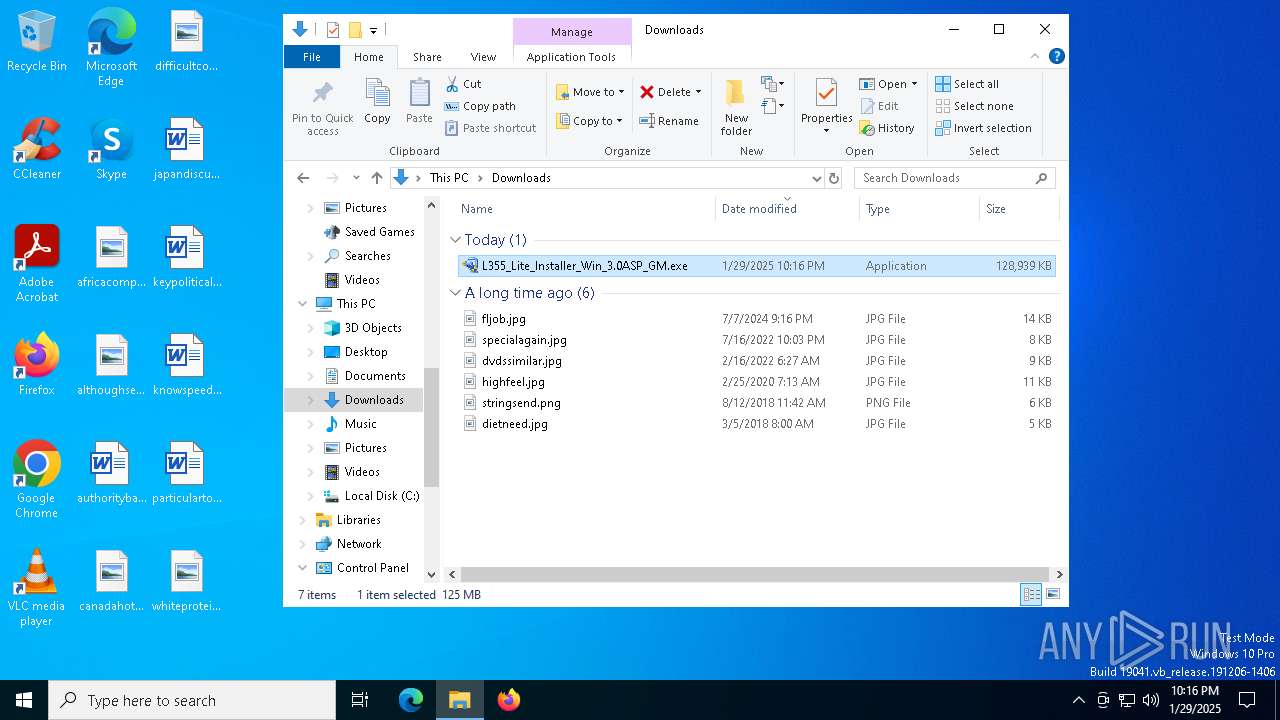
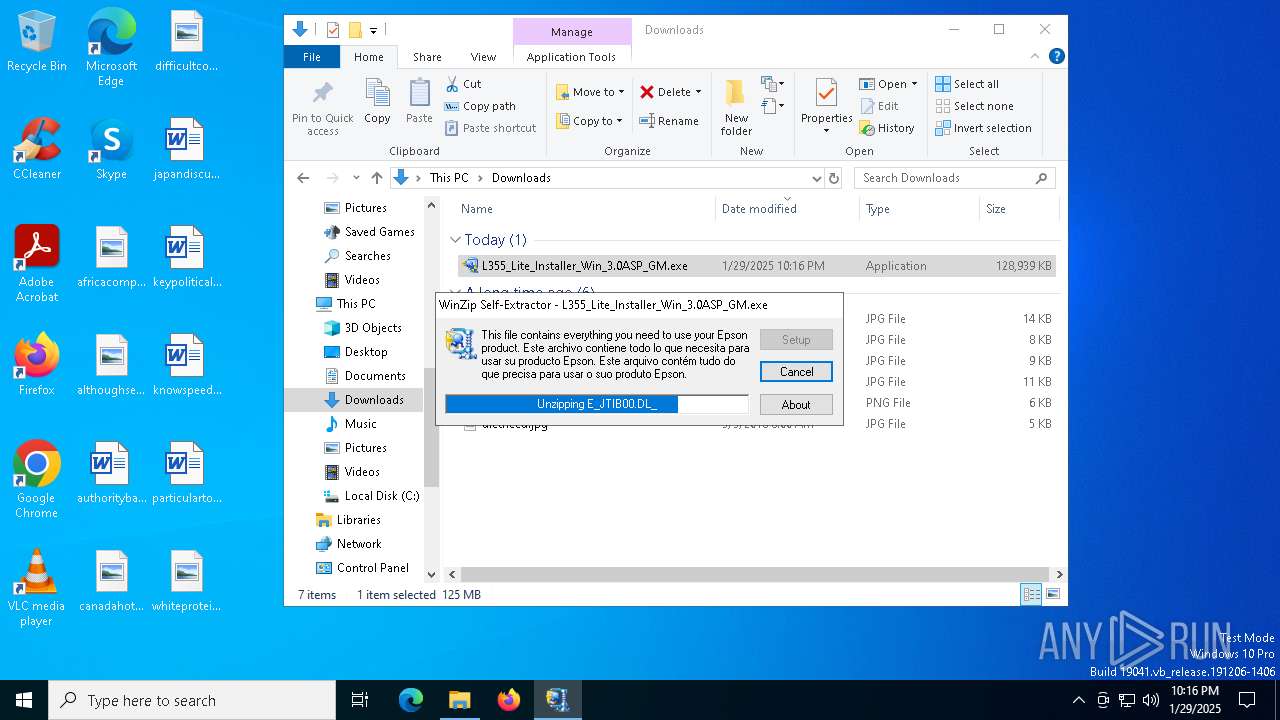
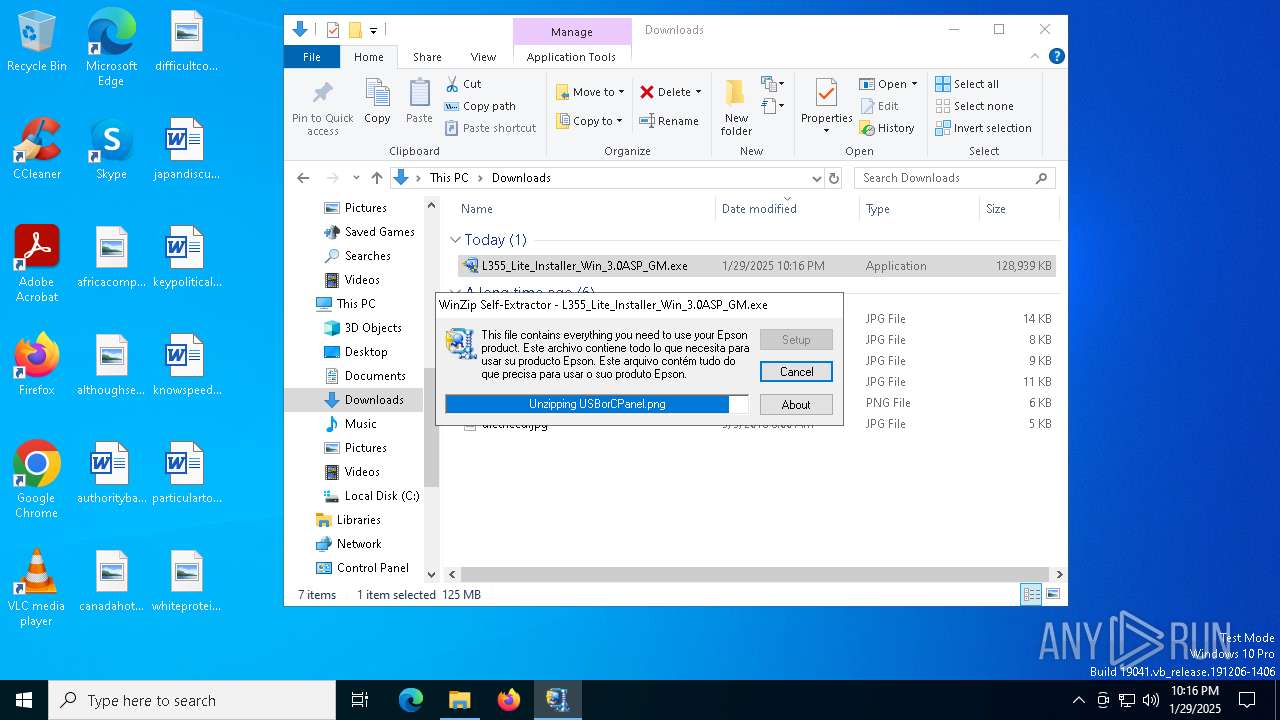
Manual execution by a user
- L355_Lite_Installer_Win_3.0ASP_GM.exe (PID: 900)
- L355_Lite_Installer_Win_3.0ASP_GM.exe (PID: 1412)
Create files in a temporary directory
- L355_Lite_Installer_Win_3.0ASP_GM.exe (PID: 900)
- Setup.exe (PID: 5572)
- SETUP64.EXE (PID: 1612)
- splwow64.exe (PID: 6616)
- ENPSETUP.EXE (PID: 6316)
- Setup.exe (PID: 5680)
The sample compiled with japanese language support
- L355_Lite_Installer_Win_3.0ASP_GM.exe (PID: 900)
- SETUP64.EXE (PID: 1612)
- drvinst.exe (PID: 5548)
- msiexec.exe (PID: 3692)
- Setup.exe (PID: 5680)
- drvinst.exe (PID: 7052)
Reads the software policy settings
- Setup.exe (PID: 5572)
- SETUP64.EXE (PID: 1612)
- msiexec.exe (PID: 3692)
- drvinst.exe (PID: 5548)
- drvinst.exe (PID: 7052)
Reads the machine GUID from the registry
- Setup.exe (PID: 5572)
- SETUP64.EXE (PID: 1612)
- drvinst.exe (PID: 5548)
- msiexec.exe (PID: 3692)
- ENPSETUP.EXE (PID: 6316)
- drvinst.exe (PID: 7052)
Checks proxy server information
- Setup.exe (PID: 5572)
Creates files or folders in the user directory
- Setup.exe (PID: 5572)
- msiexec.exe (PID: 3692)
- ENPSETUP.EXE (PID: 6316)
Process checks computer location settings
- Setup.exe (PID: 5572)
- Setup.exe (PID: 5980)
- Setup.exe (PID: 6844)
- msiexec.exe (PID: 7092)
- ENPE.exe (PID: 3128)
The sample compiled with english language support
- L355_Lite_Installer_Win_3.0ASP_GM.exe (PID: 900)
- Setup.exe (PID: 5572)
- drvinst.exe (PID: 5548)
- SETUP64.EXE (PID: 1612)
- msiexec.exe (PID: 3692)
- ENPE.exe (PID: 3128)
- ENPSETUP.EXE (PID: 6316)
- ADSETUP64.EXE (PID: 6600)
- Setup.exe (PID: 5680)
- drvinst.exe (PID: 7052)
Creates files in the program directory
- SETUP64.EXE (PID: 1612)
- ENPSETUP.EXE (PID: 6316)
- ADSETUP64.EXE (PID: 6600)
- Setup.exe (PID: 5680)
Reads Environment values
- SETUP64.EXE (PID: 1612)
Reads product name
- SETUP64.EXE (PID: 1612)
Creates a software uninstall entry
- msiexec.exe (PID: 3692)
Reads security settings of Internet Explorer
- splwow64.exe (PID: 6616)
Creates or modifies Windows services
- msiexec.exe (PID: 2088)
Manages system restore points
- SrTasks.exe (PID: 5836)
The sample compiled with czech language support
- Setup.exe (PID: 5680)
- msiexec.exe (PID: 3692)
The sample compiled with arabic language support
- Setup.exe (PID: 5680)
The sample compiled with chinese language support
- Setup.exe (PID: 5680)
- msiexec.exe (PID: 3692)
The sample compiled with bulgarian language support
- Setup.exe (PID: 5680)
The sample compiled with polish language support
- Setup.exe (PID: 5680)
- msiexec.exe (PID: 3692)
The sample compiled with Italian language support
- Setup.exe (PID: 5680)
- msiexec.exe (PID: 3692)
The sample compiled with russian language support
- Setup.exe (PID: 5680)
- msiexec.exe (PID: 3692)
The sample compiled with french language support
- Setup.exe (PID: 5680)
- msiexec.exe (PID: 3692)
The sample compiled with korean language support
- Setup.exe (PID: 5680)
- msiexec.exe (PID: 3692)
The sample compiled with turkish language support
- Setup.exe (PID: 5680)
The sample compiled with spanish language support
- Setup.exe (PID: 5680)
- msiexec.exe (PID: 3692)
The sample compiled with portuguese language support
- Setup.exe (PID: 5680)
The sample compiled with swedish language support
- Setup.exe (PID: 5680)
The sample compiled with slovak language support
- Setup.exe (PID: 5680)
Starts application with an unusual extension
- msiexec.exe (PID: 3692)
The sample compiled with german language support
- msiexec.exe (PID: 3692)
- Setup.exe (PID: 5680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
189
Monitored processes
46
Malicious processes
9
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\Common\Download Navigator\Setup.msi" /qn | C:\Windows\SysWOW64\msiexec.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | "C:\Users\admin\Downloads\L355_Lite_Installer_Win_3.0ASP_GM.exe" | C:\Users\admin\Downloads\L355_Lite_Installer_Win_3.0ASP_GM.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1064 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1412 | "C:\Users\admin\Downloads\L355_Lite_Installer_Win_3.0ASP_GM.exe" | C:\Users\admin\Downloads\L355_Lite_Installer_Win_3.0ASP_GM.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1604 | msiexec.exe /i "C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\Common\Event Manager\MSI\EEM.msi" /qn UI_INSTALL=YES SHORTCUT=YES | C:\Windows\SysWOW64\msiexec.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1612 | "C:\USERS\ADMIN\APPDATA\LOCAL\TEMP\EPSON L355 SERIES\DRIVER\PRINTER\DRIVER\WINX64\SETUP\WINX64\SETUP\SETUP64.EXE" /Q:"DEVICEOP.EXE" /P /NODISP /LID:0x0009 /nocopygauge /RG:A | C:\Users\admin\AppData\Local\Temp\EPSON L355 Series\Driver\Printer\Driver\WINX64\SETUP\WINX64\SETUP\SETUP64.EXE | Setup.exe | ||||||||||||
User: admin Company: Seiko Epson Corporation Integrity Level: HIGH Description: Epson Printer Driver Setup for x64 Exit code: 0 Version: 7.9.2 Modules
| |||||||||||||||
| 1868 | "C:\WINDOWS\Installer\MSIB33.tmp" | C:\Windows\Installer\MSIB33.tmp | — | msiexec.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1876 | "C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\Common\Event Manager\Setup.exe" /qn | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\Common\Event Manager\Setup.exe | — | Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Setup Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2088 | C:\Windows\syswow64\MsiExec.exe -Embedding 47D3A1F1DC97F2DE727F0CD24E412738 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2904 | "C:\Program Files\EPSON\EpsonCustomerParticipation\EPCP.exe" /Service | C:\Program Files\EPSON\EpsonCustomerParticipation\EPCP.exe | — | msiexec.exe | |||||||||||
User: admin Company: SEIKO EPSON CORPORATION Integrity Level: HIGH Description: Epson Customer Participation Exit code: 0 Version: 1.4.0.0 Modules
| |||||||||||||||
Total events
37 751
Read events
35 353
Write events
2 356
Delete events
42
Modification events
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5256) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000007335CD689B72DB01 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | GoogleChromeAutoLaunch_A822CA3D40D4B8944864CFEA751D8D57 |
Value: | |||
| (PID) Process: | (5572) Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5572) Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
2 069
Suspicious files
1 643
Text files
874
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF136d53.TMP | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF136d53.TMP | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF136d53.TMP | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF136d53.TMP | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF136d63.TMP | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
85
DNS requests
74
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7148 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6248 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7148 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5572 | Setup.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
5572 | Setup.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
5572 | Setup.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
5572 | Setup.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAnJ%2FWM9gZs%2FhzEAvoPP3UE%3D | unknown | — | — | whitelisted |
5572 | Setup.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA0HeCoTP8b5pXKW4TH%2F0Xk%3D | unknown | — | — | whitelisted |
5572 | Setup.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEA%2FRu8p5a9f43UyC4QqaljE%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
6364 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6660 | chrome.exe | 13.107.42.12:443 | 1drv.ms | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6660 | chrome.exe | 173.194.79.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6660 | chrome.exe | 13.107.139.11:443 | onedrive.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6660 | chrome.exe | 2.19.126.140:443 | res-1.cdn.office.net | Akamai International B.V. | DE | whitelisted |
6660 | chrome.exe | 51.105.104.217:443 | p.sfx.ms | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
1drv.ms |
| shared |
accounts.google.com |
| whitelisted |
onedrive.live.com |
| whitelisted |
res-1.cdn.office.net |
| whitelisted |
p.sfx.ms |
| whitelisted |
api.onedrive.com |
| whitelisted |
login.live.com |
| whitelisted |
api-badgerp.svc.ms |
| unknown |
ocsp.digicert.com |
| whitelisted |