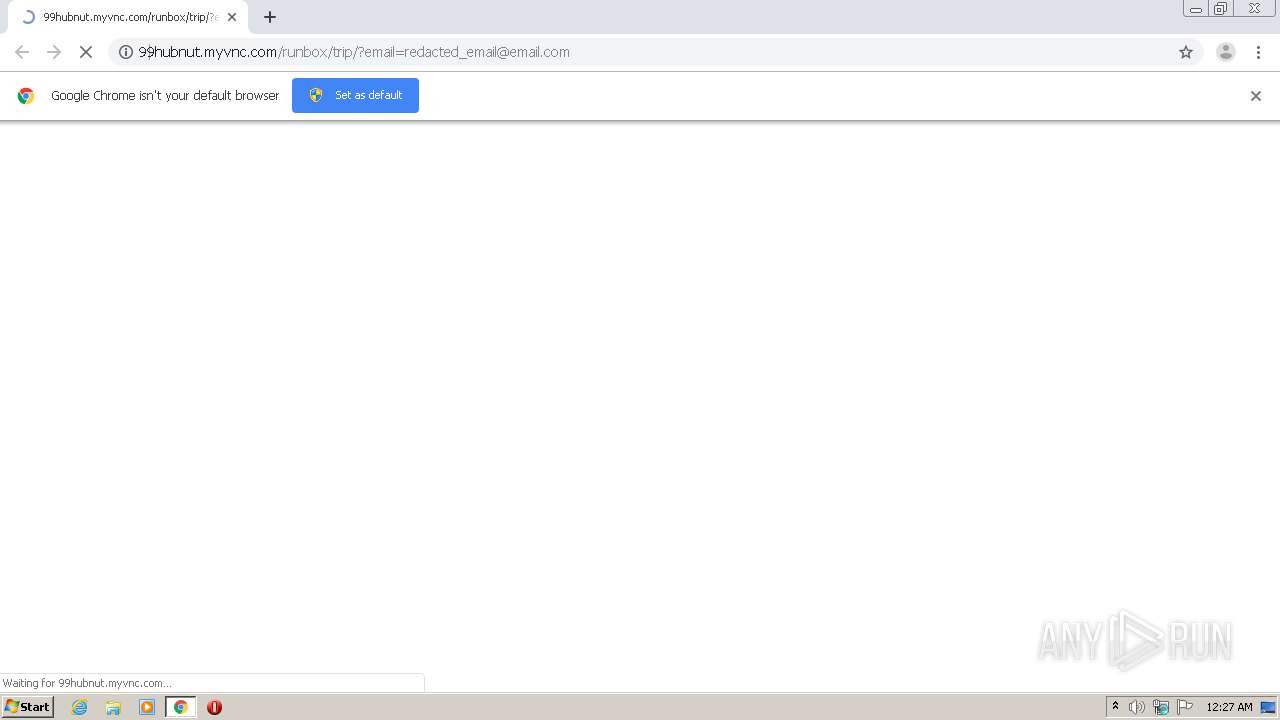
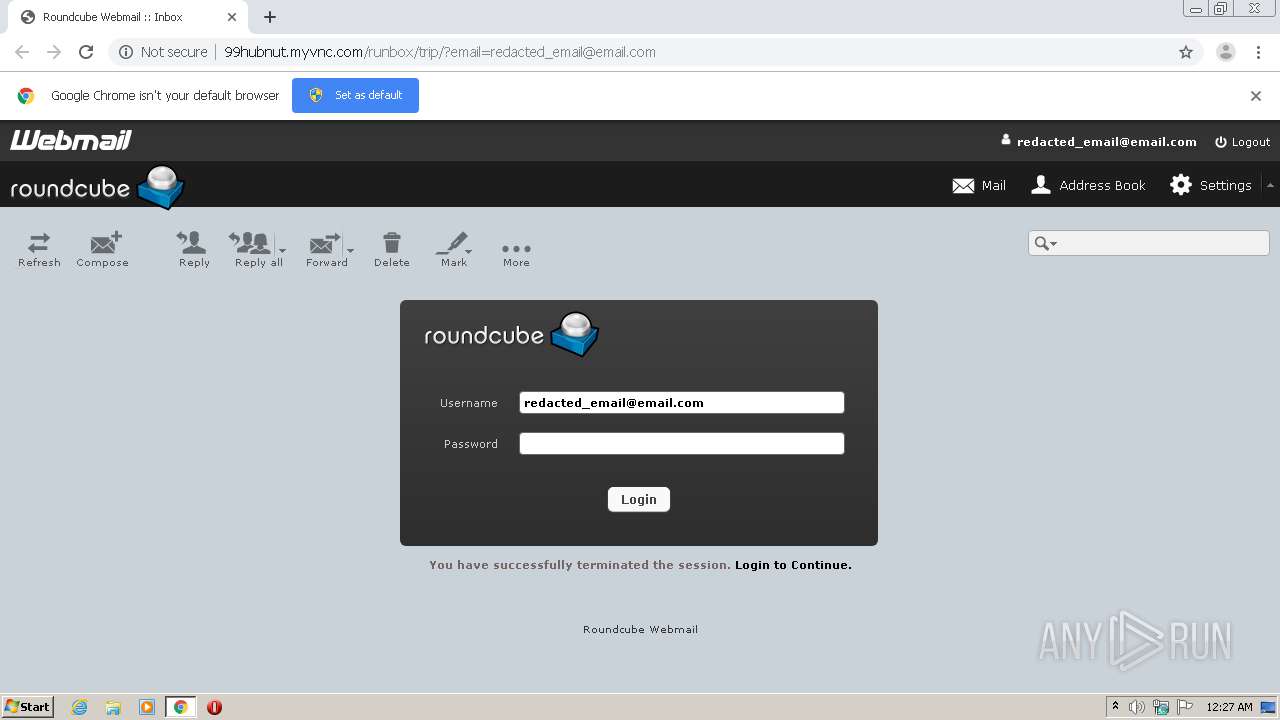
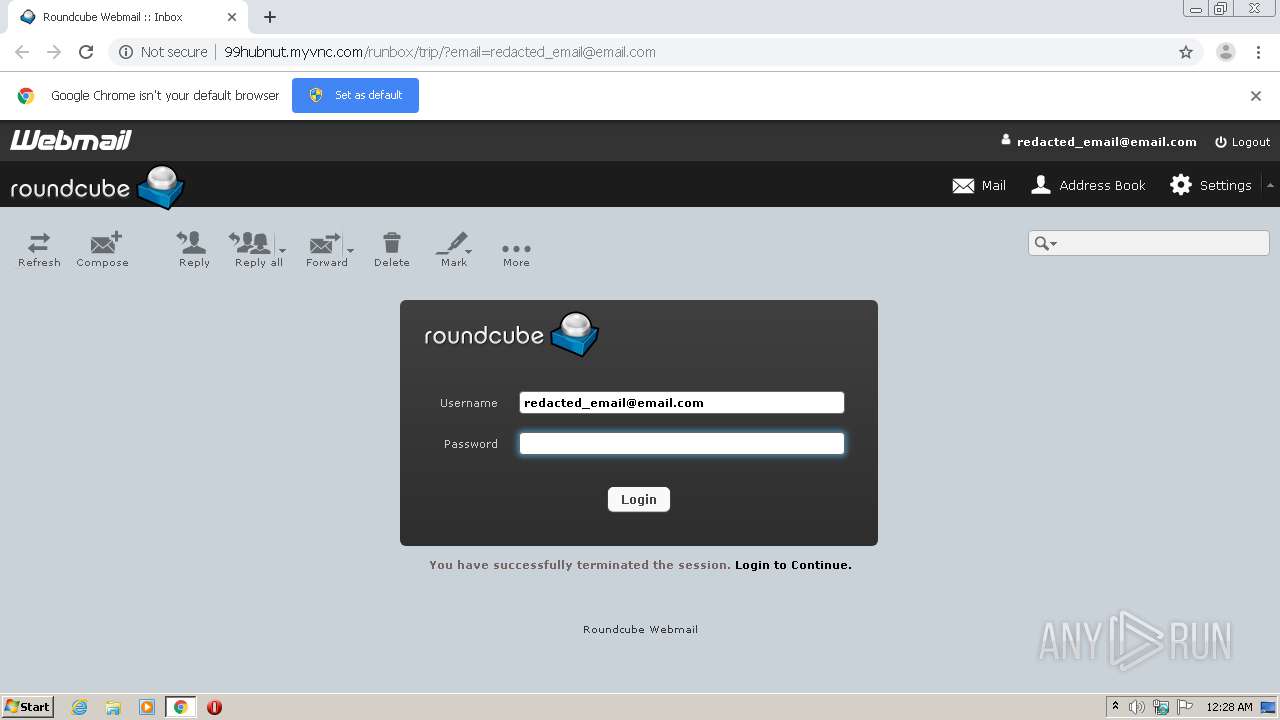
| URL: | http://99hubnut.myvnc.com/runbox/trip/?email=redacted_email@email.com |
| Full analysis: | https://app.any.run/tasks/109f8cc3-5629-429a-b191-73cfe998e299 |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 23:27:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A409DB866A8E5A215E5246090E3E151B |
| SHA1: | F1EABA8C9F90FA007FD4E16454CC7B9952841F2D |
| SHA256: | 10C3A944633A134863684233D6124FDE762360942794FC7E540D571E7B2BE057 |
| SSDEEP: | 3:N1K8HyyT1KxEI6Gtlrd2n:C8lKCI6ikn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3072)
Reads the hosts file
- chrome.exe (PID: 2540)
- chrome.exe (PID: 3072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
15
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,16805644732473507455,3767778484909709940,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=25677635575968068 --mojo-platform-channel-handle=3448 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,16805644732473507455,3767778484909709940,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4512348294813329836 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,16805644732473507455,3767778484909709940,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=106739331669340074 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2600 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,16805644732473507455,3767778484909709940,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2623884394895845389 --mojo-platform-channel-handle=1556 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,16805644732473507455,3767778484909709940,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11883289296871151166 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,16805644732473507455,3767778484909709940,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11030314093893187562 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,16805644732473507455,3767778484909709940,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8956649501149572229 --mojo-platform-channel-handle=2672 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3076 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://99hubnut.myvnc.com/runbox/trip/?email=redacted_email@email.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,16805644732473507455,3767778484909709940,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13576528105813280414 --mojo-platform-channel-handle=3372 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
592
Read events
518
Write events
70
Delete events
4
Modification events
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3072-13247623670084125 |
Value: 259 | |||
| (PID) Process: | (3072) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3072) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3072) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3072) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3072) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3072) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3072) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3072) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (3072) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
6
Text files
67
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E20F6-C00.pma | — | |
MD5:— | SHA256:— | |||
| 3072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0db7e297-0225-476e-93f3-b41331dc632f.tmp | — | |
MD5:— | SHA256:— | |||
| 3072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF165086.TMP | text | |
MD5:— | SHA256:— | |||
| 3072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF165086.TMP | text | |
MD5:— | SHA256:— | |||
| 3072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1650b5.TMP | text | |
MD5:— | SHA256:— | |||
| 3072 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF1650c4.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
16
DNS requests
8
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2540 | chrome.exe | GET | 200 | 34.123.157.13:80 | http://99hubnut.myvnc.com/runbox/trip/?email=redacted_email@email.com | US | html | 2.35 Kb | suspicious |
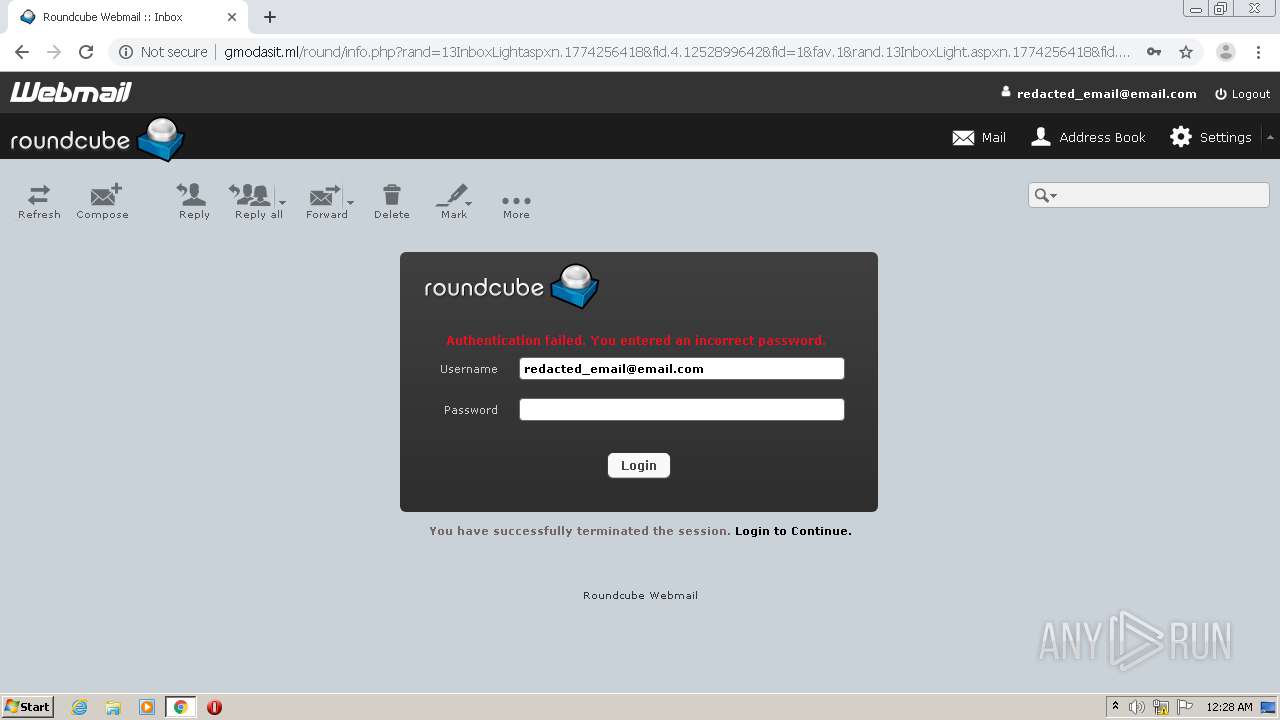
2540 | chrome.exe | POST | 302 | 80.208.227.135:80 | http://gmodasit.ml/round/jasb.php | LT | — | — | suspicious |
2540 | chrome.exe | GET | 200 | 80.208.227.135:80 | http://gmodasit.ml/round/info.php?rand=13InboxLightaspxn.1774256418&fid.4.1252899642&fid=1&fav.1&rand.13InboxLight.aspxn.1774256418&fid.1252899642&fid.1&fav.1&email=redacted_email@email.com&.rand=13InboxLight.aspx?n=1774256418&fid=4 | LT | html | 2.38 Kb | suspicious |
2540 | chrome.exe | GET | 200 | 34.123.157.13:80 | http://99hubnut.myvnc.com/runbox/trip/index_files/webmail.png | US | image | 1.86 Kb | suspicious |
2540 | chrome.exe | GET | 200 | 34.123.157.13:80 | http://99hubnut.myvnc.com/runbox/trip/index_files/user.png | US | image | 384 b | suspicious |
2540 | chrome.exe | GET | 200 | 34.123.157.13:80 | http://99hubnut.myvnc.com/runbox/trip/index_files/images/buttons.png | US | image | 8.92 Kb | suspicious |
2540 | chrome.exe | GET | 200 | 34.123.157.13:80 | http://99hubnut.myvnc.com/runbox/trip/index_files/styles.min.css | US | text | 8.89 Kb | suspicious |
2540 | chrome.exe | GET | 200 | 34.123.157.13:80 | http://99hubnut.myvnc.com/runbox/trip/index_files/roundcube_logo.png | US | image | 3.70 Kb | suspicious |
2540 | chrome.exe | GET | 200 | 80.208.227.135:80 | http://gmodasit.ml/round/index_files/user.png | LT | image | 384 b | suspicious |
2540 | chrome.exe | GET | 200 | 34.123.157.13:80 | http://99hubnut.myvnc.com/runbox/trip/index_files/favicon.ico | US | image | 33.6 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2540 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2540 | chrome.exe | 34.123.157.13:80 | 99hubnut.myvnc.com | — | US | suspicious |
2540 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2540 | chrome.exe | 172.217.18.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
2540 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2540 | chrome.exe | 80.208.227.135:80 | gmodasit.ml | UAB Rakrejus | LT | suspicious |
2540 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
99hubnut.myvnc.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
gmodasit.ml |
| suspicious |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.myvnc .com |
2540 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Myvnc.com |
2540 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Myvnc.com |
2540 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Myvnc.com |
2540 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Myvnc.com |
2540 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Myvnc.com |
2540 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Myvnc.com |
2540 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Connection To DDNS Domain Myvnc.com |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ml Domain |
2540 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Successful Generic Phish to .ml Domain 2018-10-23 |
3 ETPRO signatures available at the full report