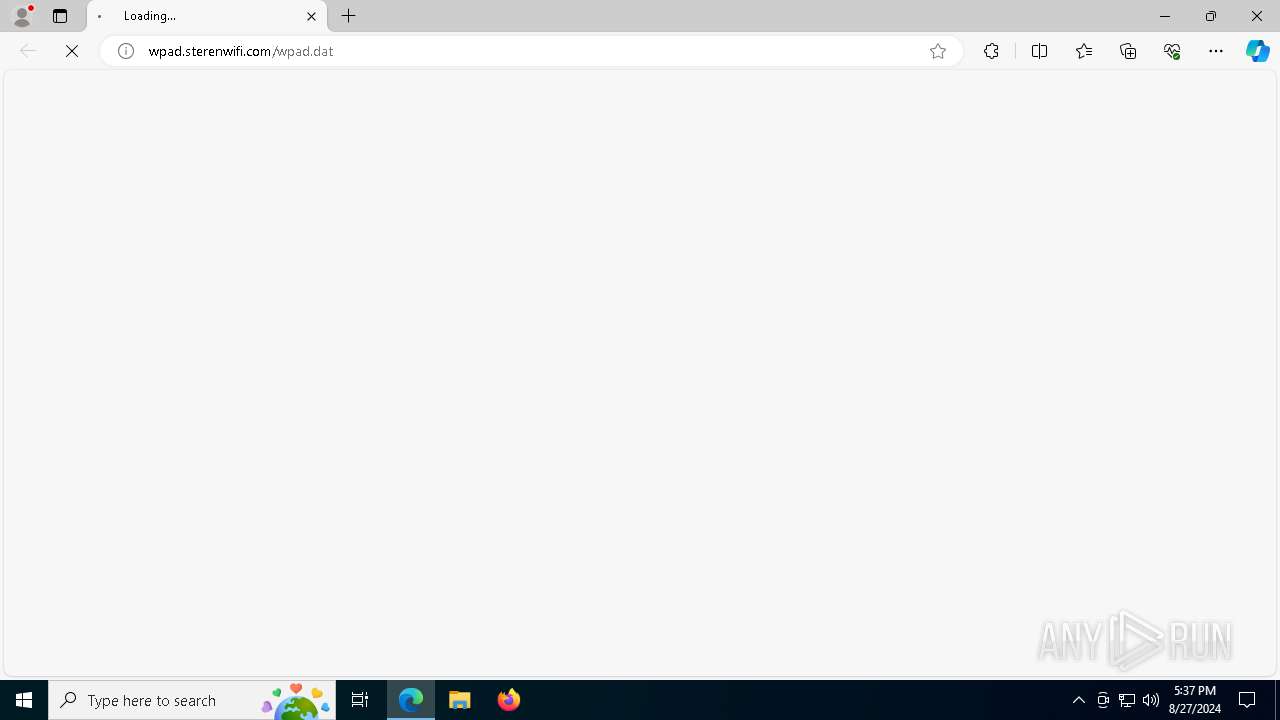
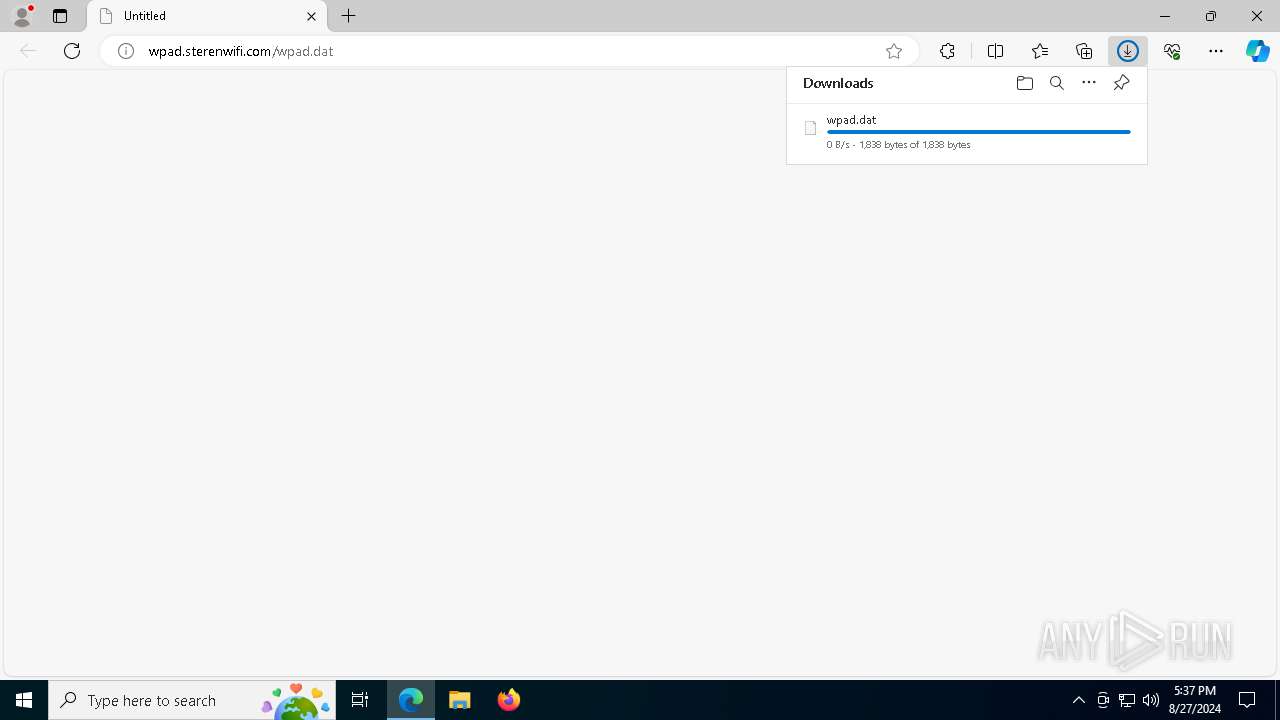
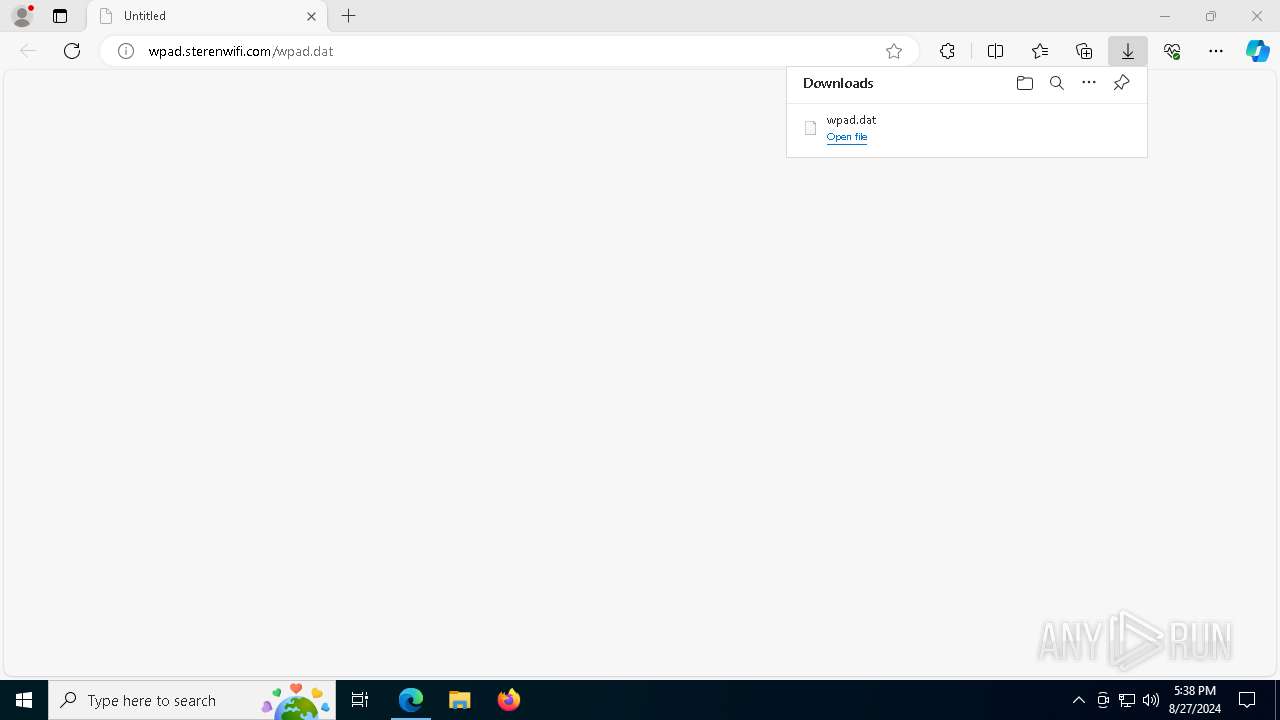
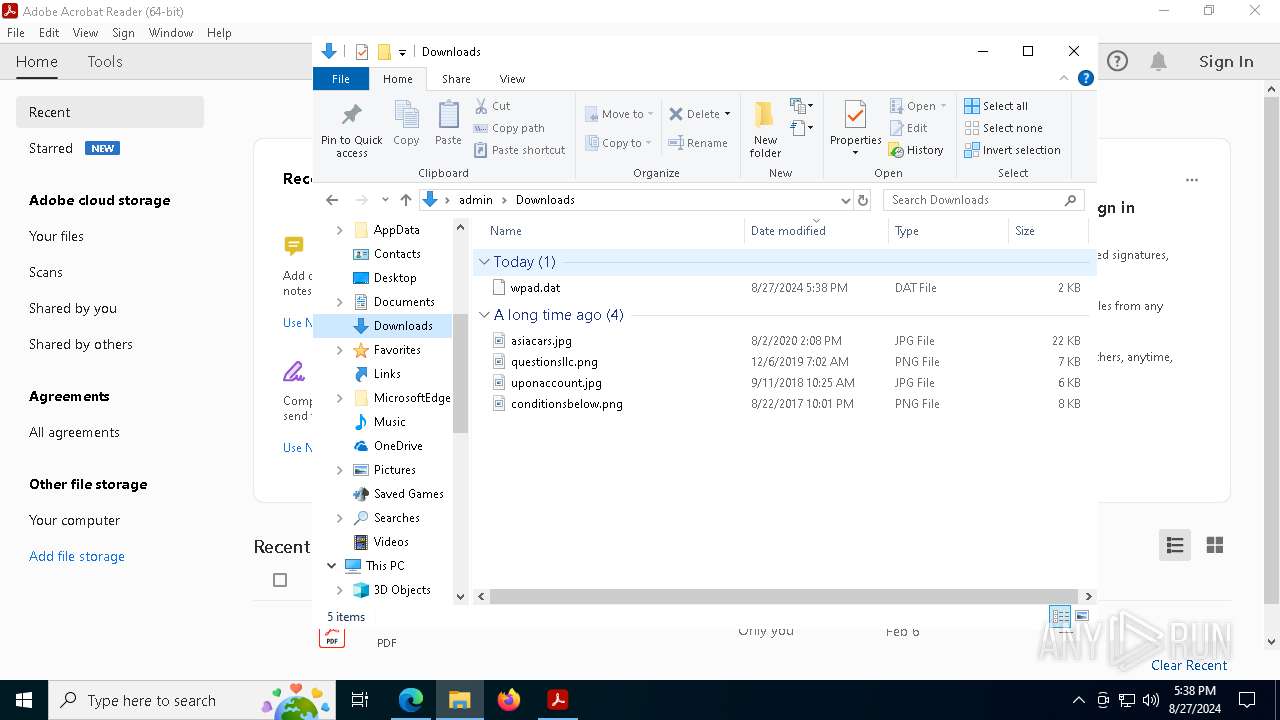
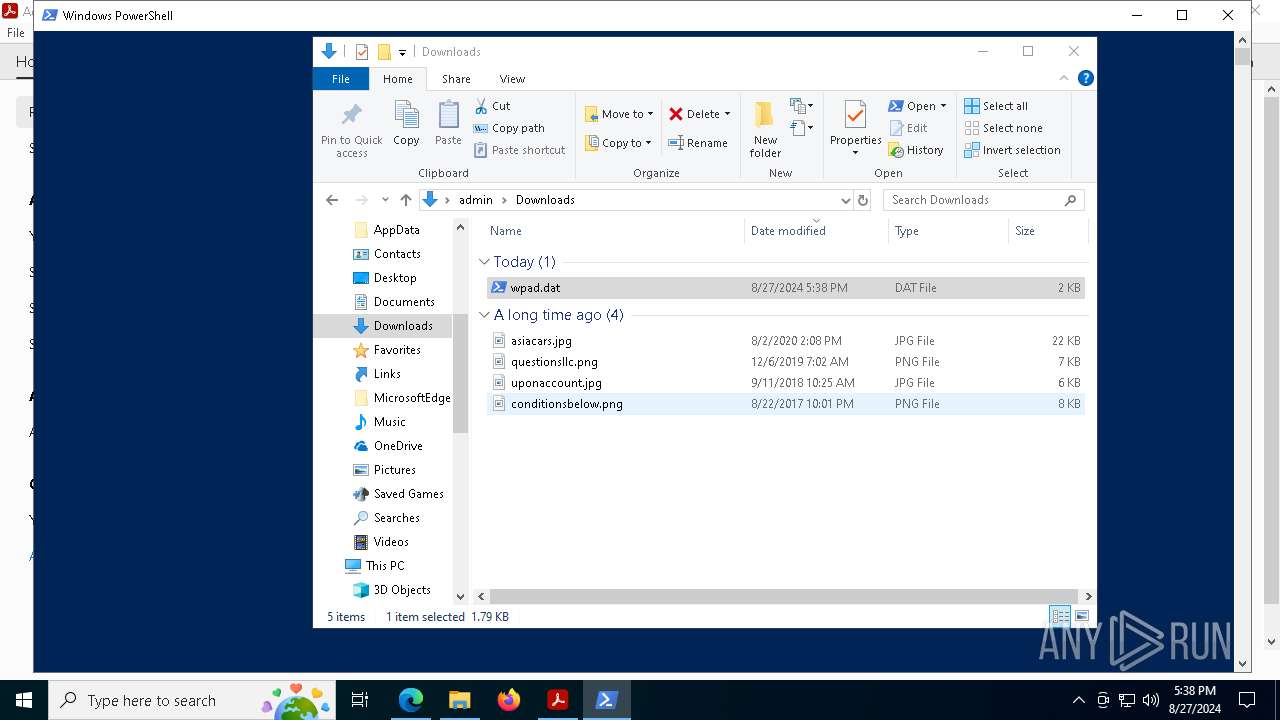
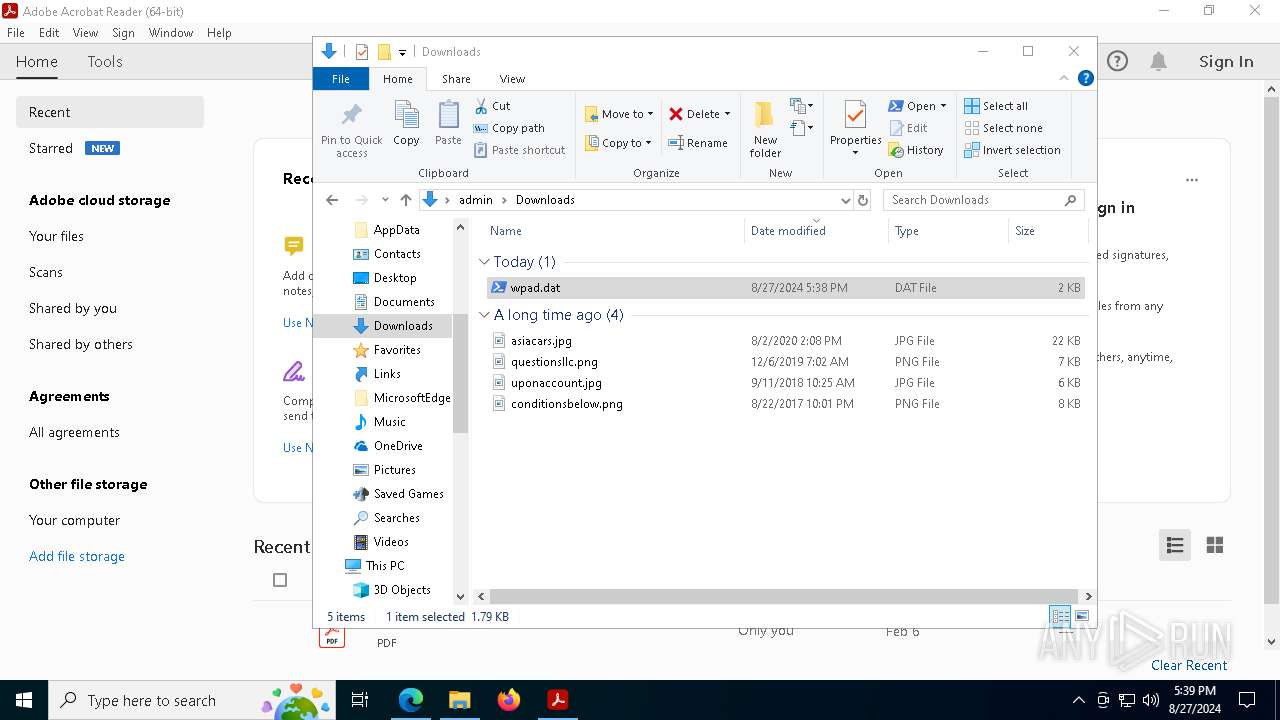
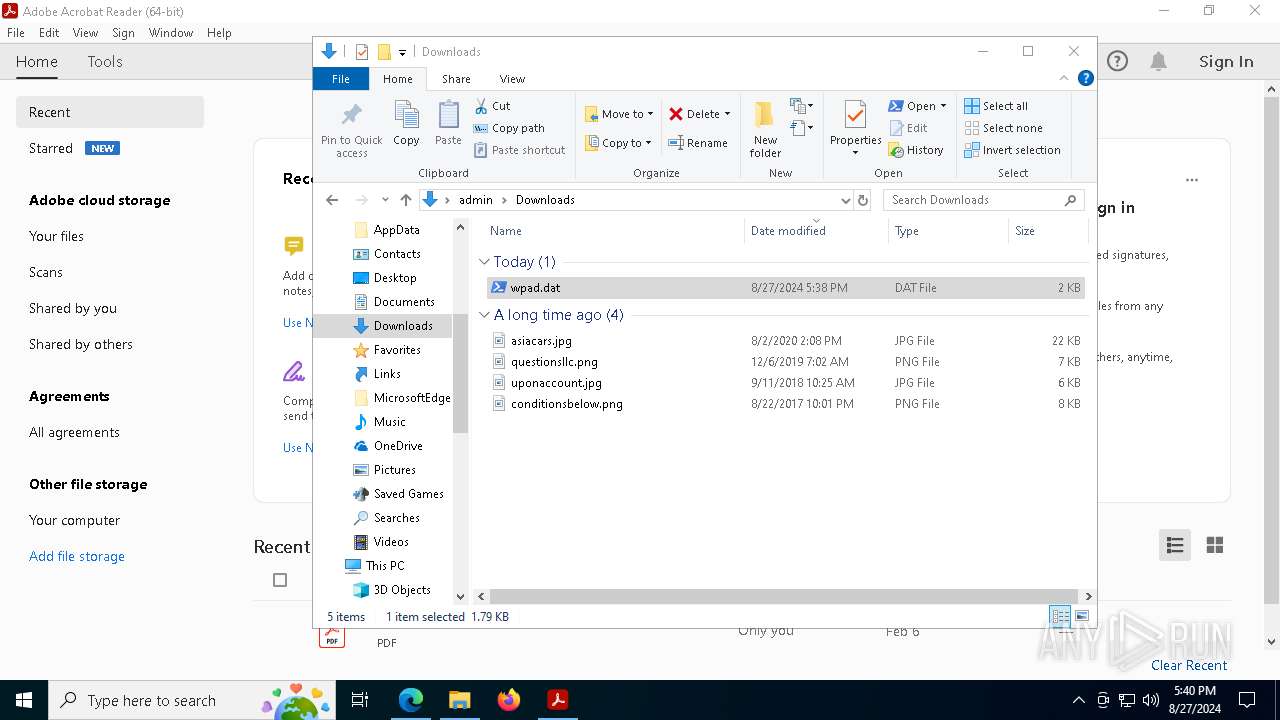
| URL: | http://wpad.sterenwifi.com/wpad.dat |
| Full analysis: | https://app.any.run/tasks/58ac6c04-f307-4c32-9cd1-e2d9a98fc6da |
| Verdict: | Malicious activity |
| Analysis date: | August 27, 2024, 17:37:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 4F5B9B4B45AF4B931C076143C99FAEF0 |
| SHA1: | FD553532E4240663689BC46BBE03167A21ACCB23 |
| SHA256: | 10BF184C41C71FF1CD0A056B57EF0FFA746C2E81DF79871210BB2A5634CF9011 |
| SSDEEP: | 3:N1KJVwe/QQd:Cj4Qd |
MALICIOUS
No malicious indicators.SUSPICIOUS
Potential Corporate Privacy Violation
- msedge.exe (PID: 5000)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 6124)
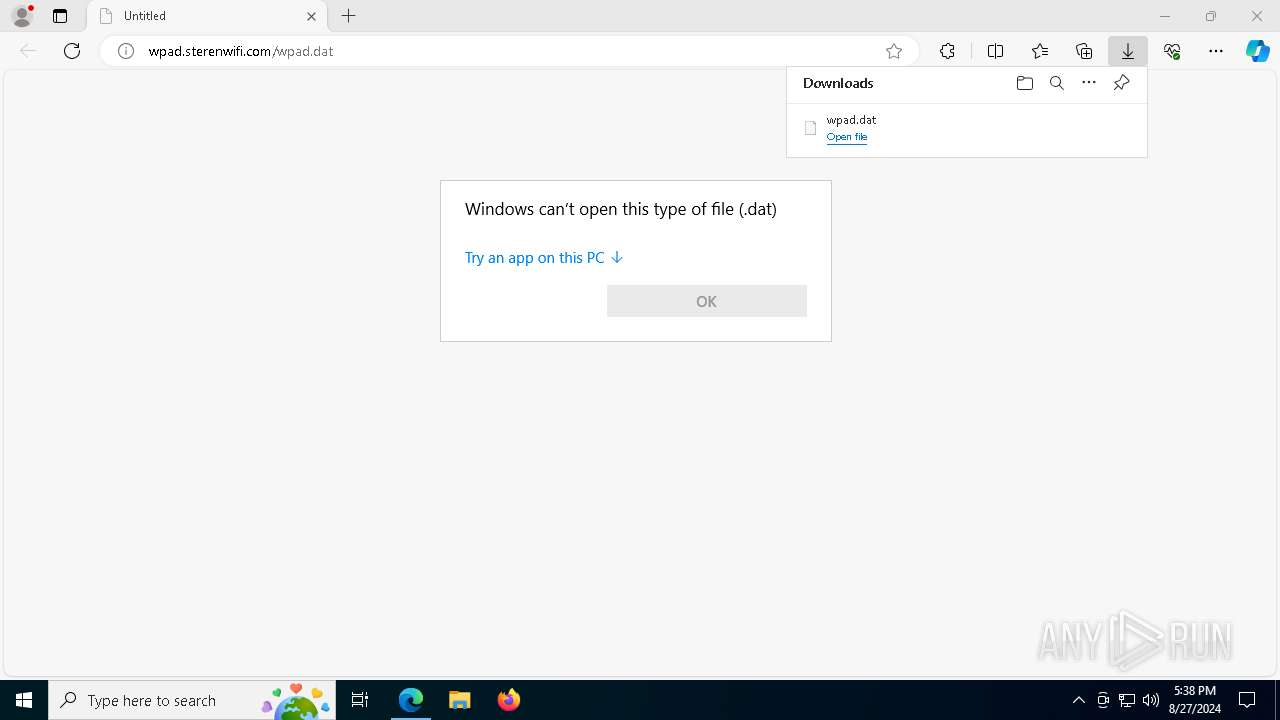
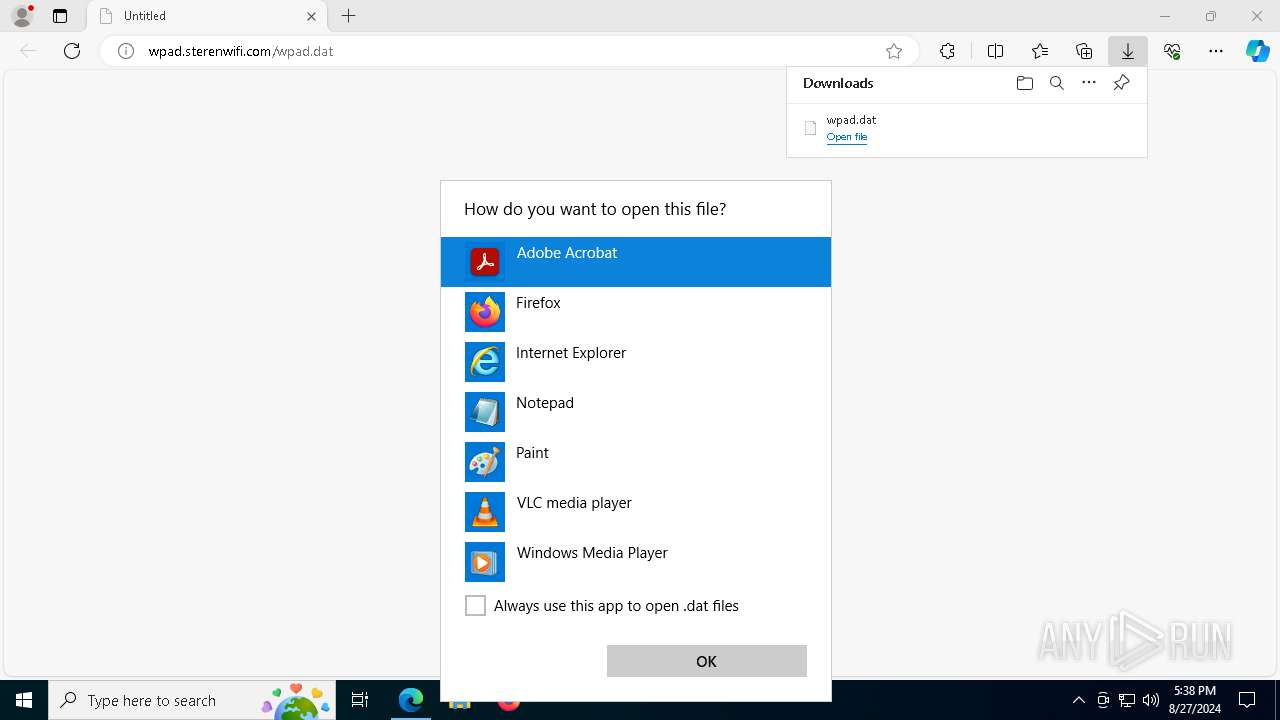
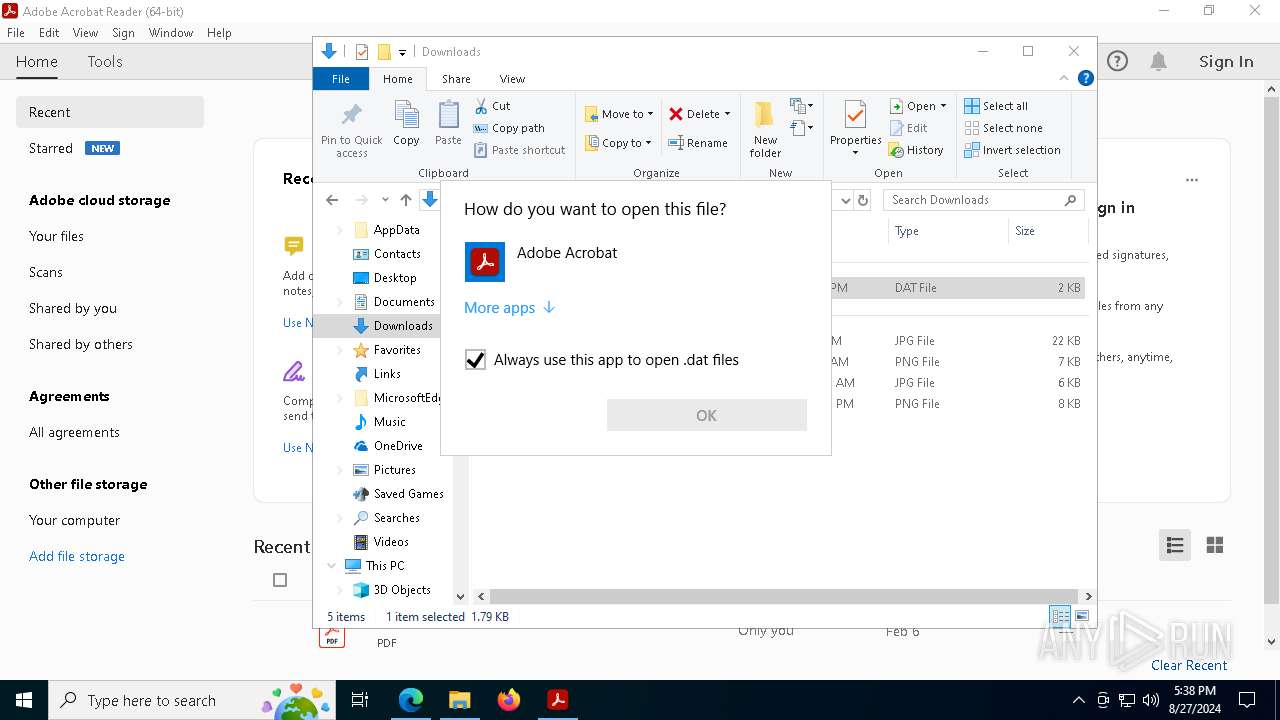
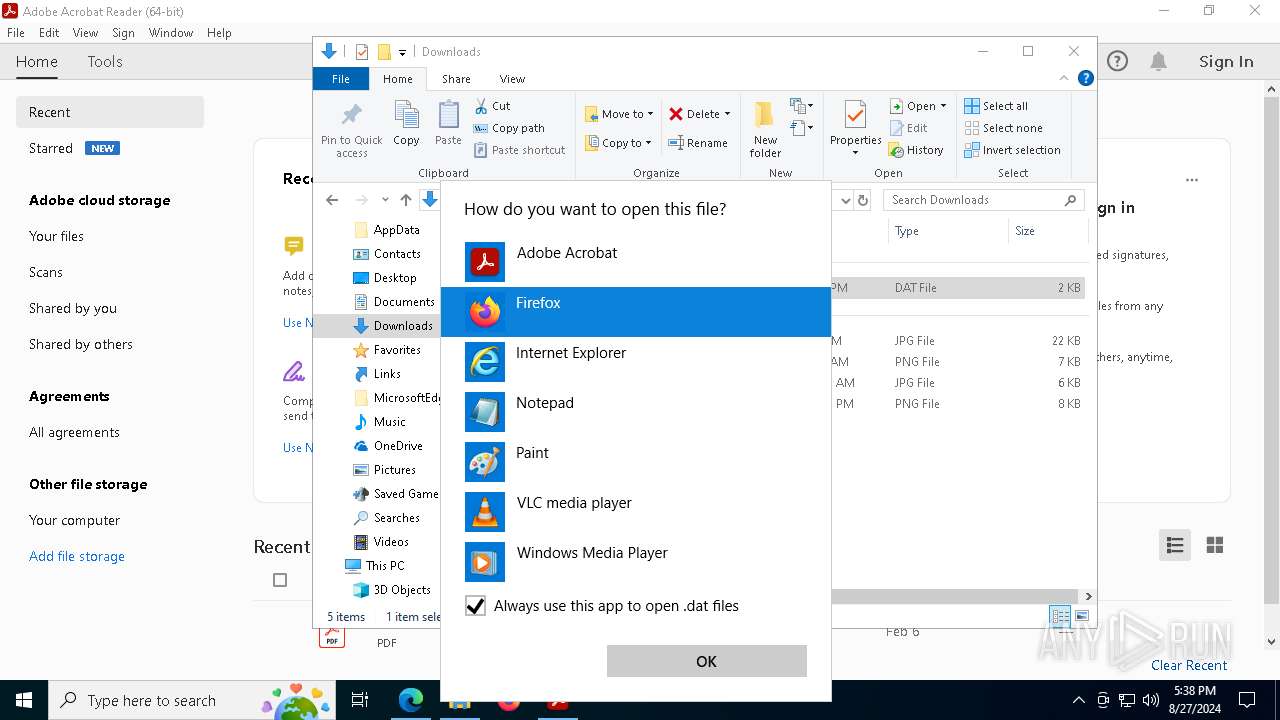
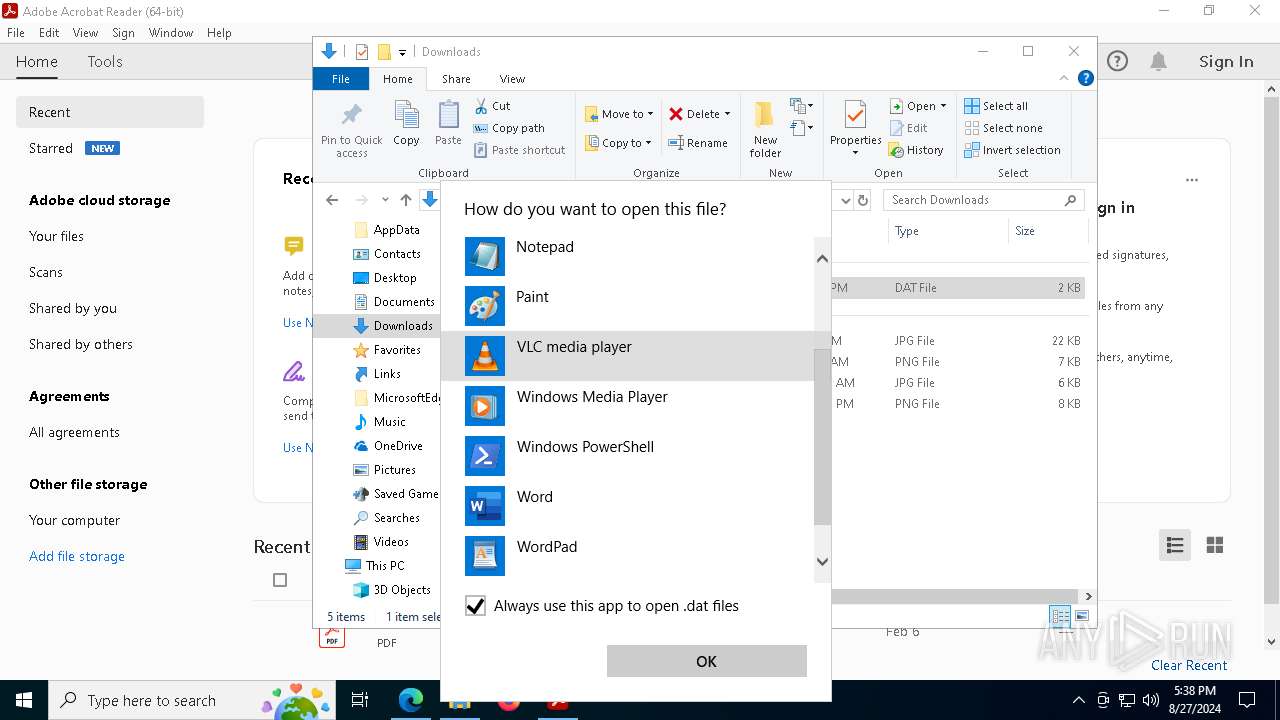
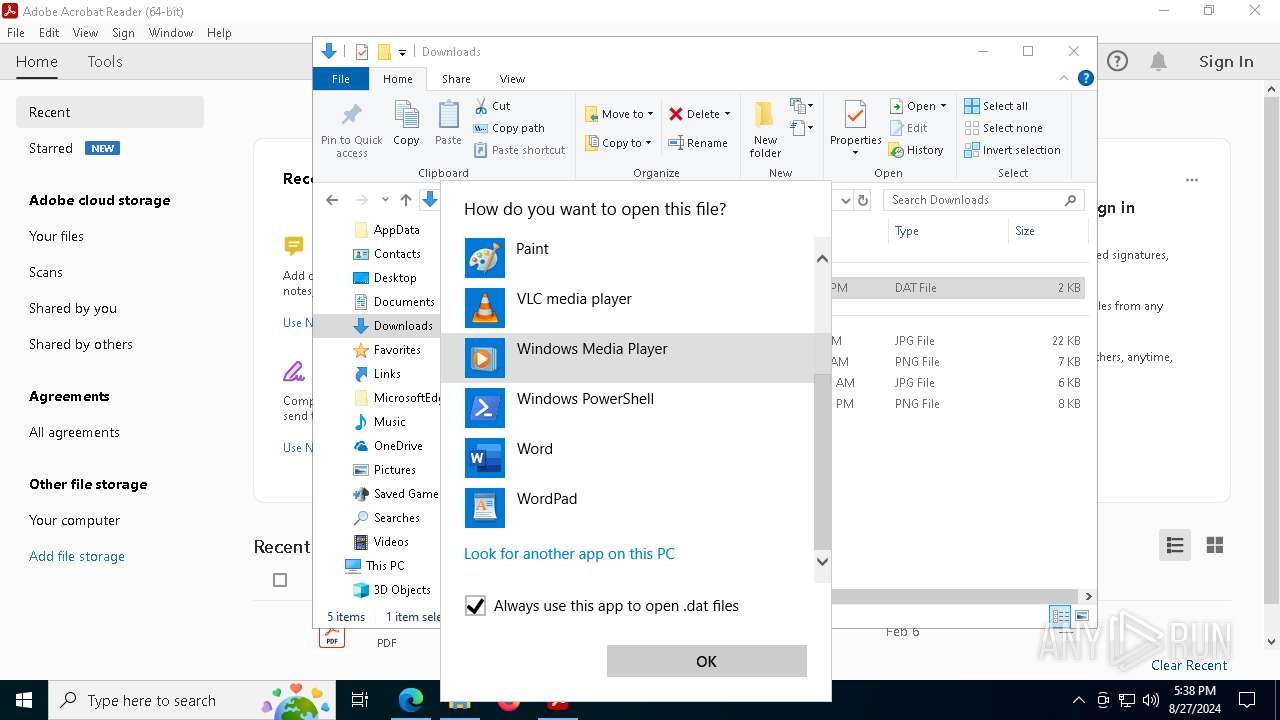
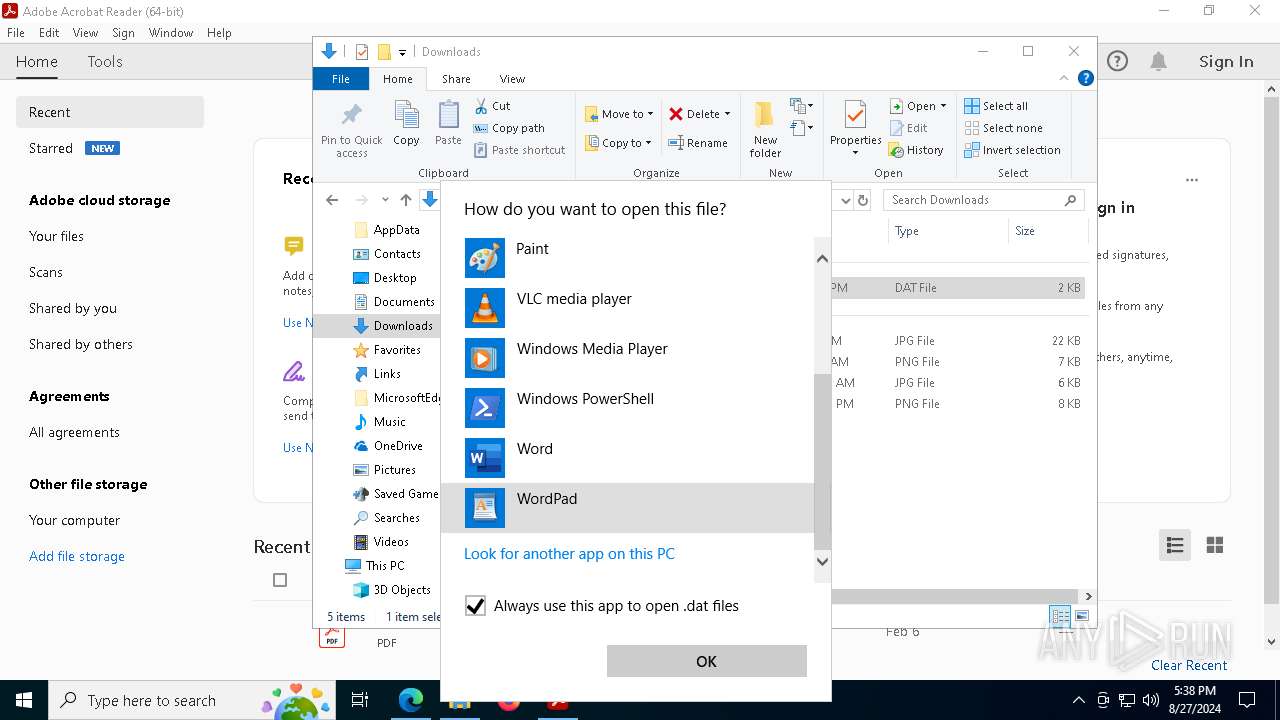
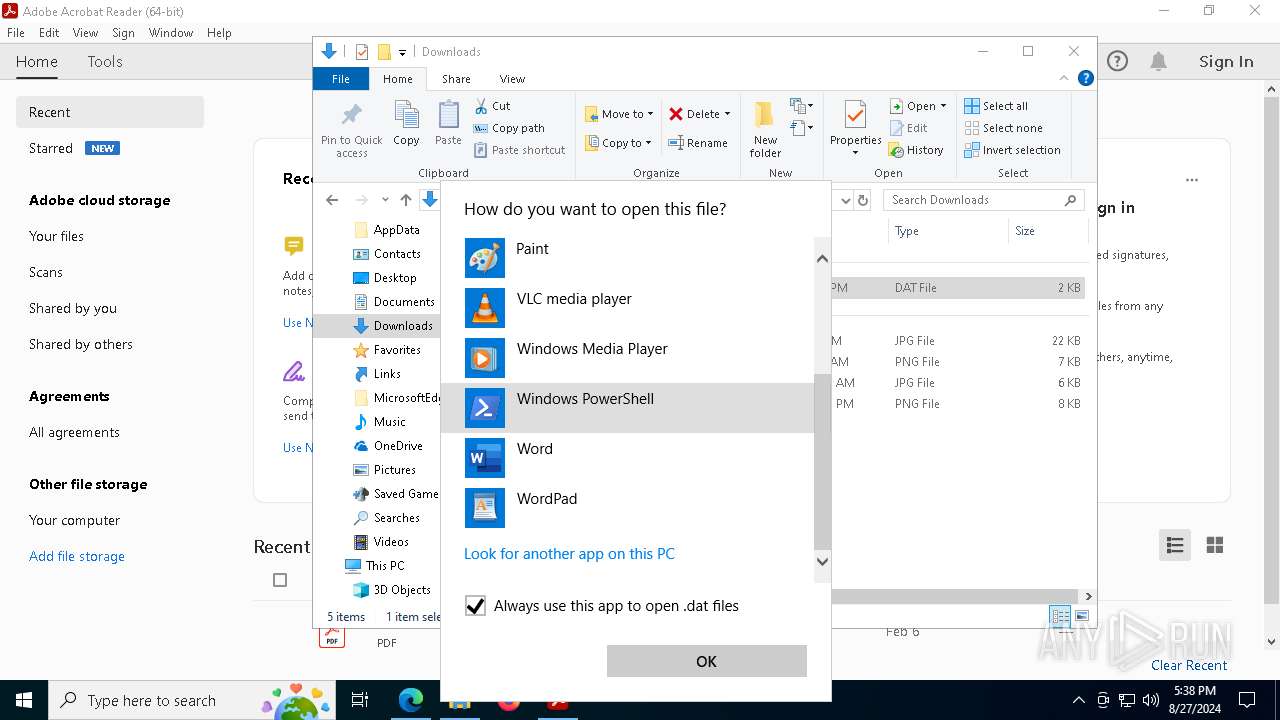
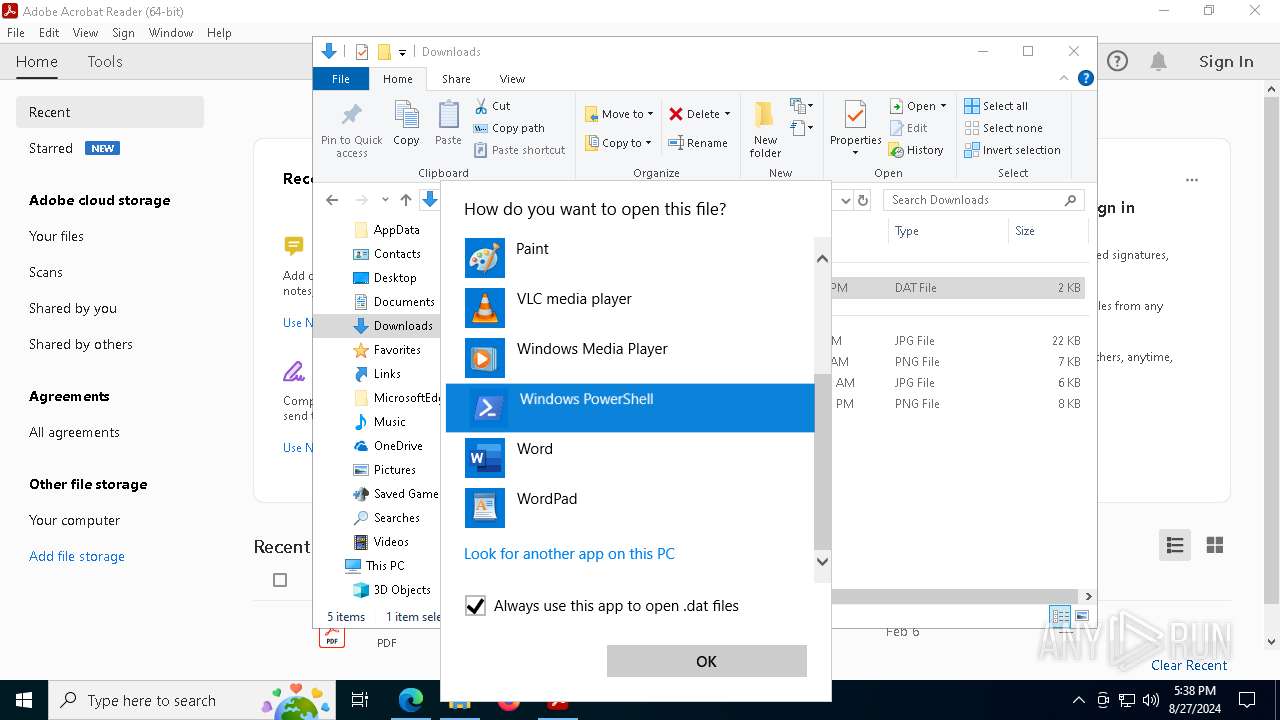
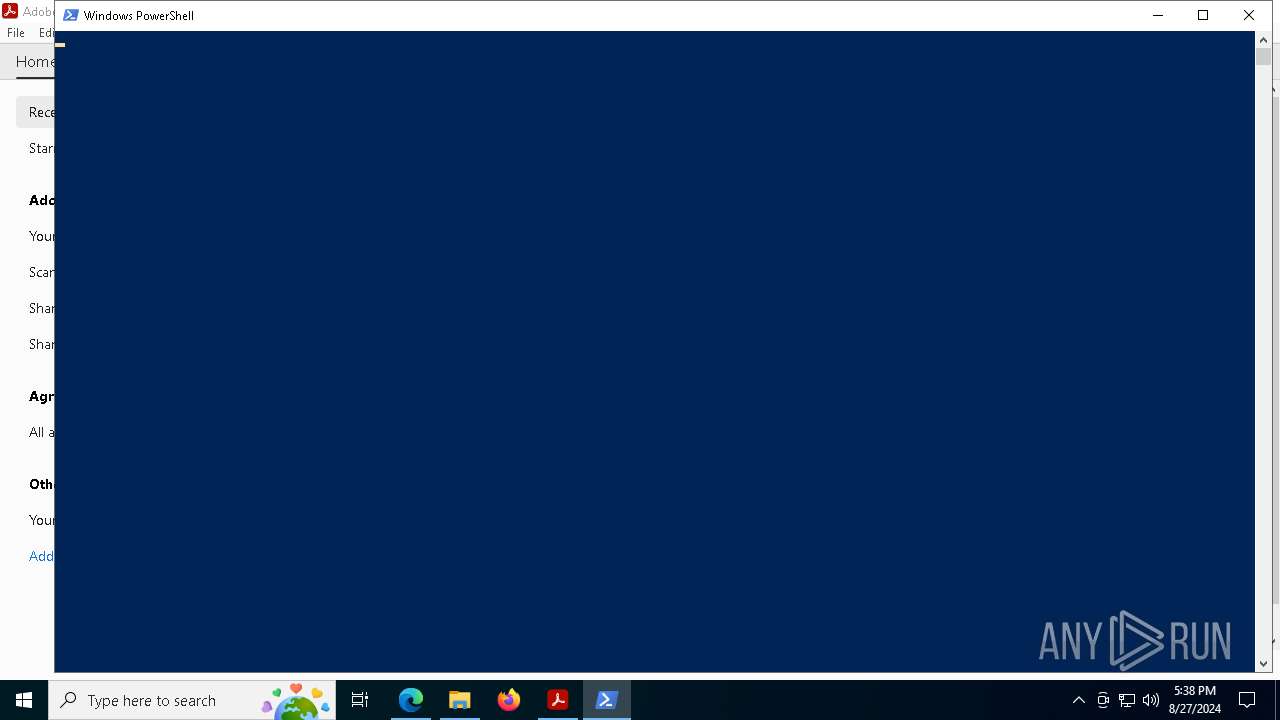
Starts POWERSHELL.EXE for commands execution
- OpenWith.exe (PID: 6336)
- powershell.exe (PID: 6124)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 4068)
- powershell.exe (PID: 3208)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 3244)
- powershell.exe (PID: 7388)
- powershell.exe (PID: 5908)
- powershell.exe (PID: 6208)
- powershell.exe (PID: 7048)
- powershell.exe (PID: 7180)
- powershell.exe (PID: 7468)
- powershell.exe (PID: 8100)
- powershell.exe (PID: 2108)
- powershell.exe (PID: 7364)
- powershell.exe (PID: 6644)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 6100)
- powershell.exe (PID: 7672)
- powershell.exe (PID: 6840)
- powershell.exe (PID: 5180)
- powershell.exe (PID: 5540)
- powershell.exe (PID: 6644)
- powershell.exe (PID: 8)
- powershell.exe (PID: 5292)
- powershell.exe (PID: 6672)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 6580)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 7232)
- powershell.exe (PID: 4444)
- powershell.exe (PID: 2768)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 7396)
- powershell.exe (PID: 6984)
- powershell.exe (PID: 812)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 2400)
- powershell.exe (PID: 7672)
- powershell.exe (PID: 7368)
- powershell.exe (PID: 5184)
- powershell.exe (PID: 4160)
- powershell.exe (PID: 6236)
- powershell.exe (PID: 6364)
- powershell.exe (PID: 6380)
- powershell.exe (PID: 7968)
- powershell.exe (PID: 2328)
- powershell.exe (PID: 3696)
- powershell.exe (PID: 7900)
- powershell.exe (PID: 3292)
- powershell.exe (PID: 6580)
- powershell.exe (PID: 7328)
- powershell.exe (PID: 7348)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 6428)
- powershell.exe (PID: 7468)
- powershell.exe (PID: 7388)
- powershell.exe (PID: 3104)
- powershell.exe (PID: 7188)
- powershell.exe (PID: 7664)
- powershell.exe (PID: 3424)
- powershell.exe (PID: 7384)
- powershell.exe (PID: 2024)
- powershell.exe (PID: 7396)
- powershell.exe (PID: 3032)
- powershell.exe (PID: 6100)
- powershell.exe (PID: 3244)
- powershell.exe (PID: 6916)
- powershell.exe (PID: 2264)
- powershell.exe (PID: 788)
- powershell.exe (PID: 4936)
- powershell.exe (PID: 4196)
- powershell.exe (PID: 5040)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 6340)
- powershell.exe (PID: 7672)
- powershell.exe (PID: 1700)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 3328)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 7056)
- powershell.exe (PID: 7352)
- powershell.exe (PID: 6200)
- powershell.exe (PID: 6512)
Application launched itself
- powershell.exe (PID: 6124)
- powershell.exe (PID: 7468)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 6208)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 4068)
- powershell.exe (PID: 3208)
- powershell.exe (PID: 3244)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 7388)
- powershell.exe (PID: 5908)
- powershell.exe (PID: 7180)
- powershell.exe (PID: 7048)
- powershell.exe (PID: 2108)
- powershell.exe (PID: 6644)
- powershell.exe (PID: 7364)
- powershell.exe (PID: 6840)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 6100)
- powershell.exe (PID: 7672)
- powershell.exe (PID: 5180)
- powershell.exe (PID: 8100)
- powershell.exe (PID: 6644)
- powershell.exe (PID: 8)
- powershell.exe (PID: 5292)
- powershell.exe (PID: 6672)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 6580)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 4444)
- powershell.exe (PID: 7232)
- powershell.exe (PID: 5540)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 7396)
- powershell.exe (PID: 6984)
- powershell.exe (PID: 7672)
- powershell.exe (PID: 812)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 2400)
- powershell.exe (PID: 7368)
- powershell.exe (PID: 2768)
- powershell.exe (PID: 4160)
- powershell.exe (PID: 5184)
- powershell.exe (PID: 6364)
- powershell.exe (PID: 6236)
- powershell.exe (PID: 6380)
- powershell.exe (PID: 7968)
- powershell.exe (PID: 2328)
- powershell.exe (PID: 3696)
- powershell.exe (PID: 7900)
- powershell.exe (PID: 3292)
- powershell.exe (PID: 6580)
- powershell.exe (PID: 7328)
- powershell.exe (PID: 7388)
- powershell.exe (PID: 6428)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 3104)
- powershell.exe (PID: 7188)
- powershell.exe (PID: 7664)
- powershell.exe (PID: 7468)
- powershell.exe (PID: 3424)
- powershell.exe (PID: 7348)
- powershell.exe (PID: 4936)
- powershell.exe (PID: 7384)
- powershell.exe (PID: 2024)
- powershell.exe (PID: 3244)
- powershell.exe (PID: 3032)
- powershell.exe (PID: 6100)
- powershell.exe (PID: 6916)
- powershell.exe (PID: 7396)
- powershell.exe (PID: 2264)
- powershell.exe (PID: 788)
- powershell.exe (PID: 7056)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 5040)
- powershell.exe (PID: 4196)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 6340)
- powershell.exe (PID: 7672)
- powershell.exe (PID: 3328)
- powershell.exe (PID: 1700)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 6200)
- powershell.exe (PID: 6512)
- powershell.exe (PID: 7352)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 5072)
- OpenWith.exe (PID: 4068)
- OpenWith.exe (PID: 6336)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 4068)
- OpenWith.exe (PID: 6336)
Reads the computer name
- identity_helper.exe (PID: 7636)
Reads Environment values
- identity_helper.exe (PID: 7636)
Checks supported languages
- identity_helper.exe (PID: 7636)
- acrobat_sl.exe (PID: 3832)
Application launched itself
- AcroCEF.exe (PID: 7280)
- Acrobat.exe (PID: 2684)
- msedge.exe (PID: 5072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
362
Monitored processes
231
Malicious processes
15
Suspicious processes
28
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\Downloads\wpad.dat" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
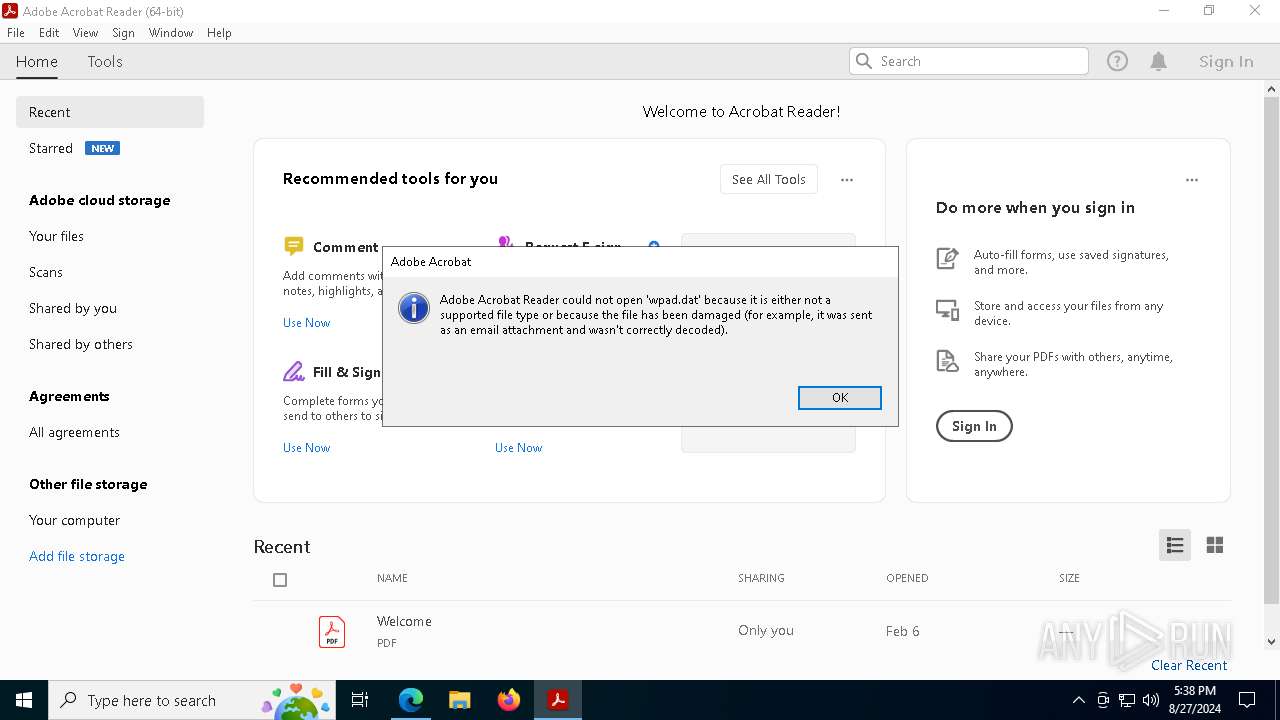
| 240 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" --type=renderer /prefetch:1 "C:\Users\admin\Downloads\wpad.dat" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | — | Acrobat.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Version: 23.1.20093.0 Modules
| |||||||||||||||
| 368 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5308 --field-trial-handle=2344,i,12547420954304934282,545646080137617158,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 508 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2608 --field-trial-handle=2344,i,12547420954304934282,545646080137617158,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2340 --field-trial-handle=2344,i,12547420954304934282,545646080137617158,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 788 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\Downloads\wpad.dat" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\Downloads\wpad.dat" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
725 628
Read events
724 594
Write events
1 026
Delete events
8
Modification events
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
3
Suspicious files
602
Text files
292
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF129b4e.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF129b4e.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF129b5d.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF129b8c.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF129b4e.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
55
DNS requests
54
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5816 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6912 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a50df300-a388-43f2-a3cd-e7b7e11aaa7c?P1=1725367777&P2=404&P3=2&P4=UMFk3wSZvOpWiV1cMEEiAj9zCblijtyYp5nl7tM8LzgfY3ilQAfwvrvle2Z8Kj%2bdPj62wdeCu9ZZD86RXh3PMg%3d%3d | unknown | — | — | whitelisted |
7636 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5000 | msedge.exe | GET | 200 | 46.8.8.100:80 | http://wpad.sterenwifi.com/wpad.dat | unknown | — | — | malicious |
2684 | Acrobat.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
7636 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6912 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a50df300-a388-43f2-a3cd-e7b7e11aaa7c?P1=1725367777&P2=404&P3=2&P4=UMFk3wSZvOpWiV1cMEEiAj9zCblijtyYp5nl7tM8LzgfY3ilQAfwvrvle2Z8Kj%2bdPj62wdeCu9ZZD86RXh3PMg%3d%3d | unknown | — | — | whitelisted |
6912 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a50df300-a388-43f2-a3cd-e7b7e11aaa7c?P1=1725367777&P2=404&P3=2&P4=UMFk3wSZvOpWiV1cMEEiAj9zCblijtyYp5nl7tM8LzgfY3ilQAfwvrvle2Z8Kj%2bdPj62wdeCu9ZZD86RXh3PMg%3d%3d | unknown | — | — | whitelisted |
6912 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a50df300-a388-43f2-a3cd-e7b7e11aaa7c?P1=1725367777&P2=404&P3=2&P4=UMFk3wSZvOpWiV1cMEEiAj9zCblijtyYp5nl7tM8LzgfY3ilQAfwvrvle2Z8Kj%2bdPj62wdeCu9ZZD86RXh3PMg%3d%3d | unknown | — | — | whitelisted |
6912 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a50df300-a388-43f2-a3cd-e7b7e11aaa7c?P1=1725367777&P2=404&P3=2&P4=UMFk3wSZvOpWiV1cMEEiAj9zCblijtyYp5nl7tM8LzgfY3ilQAfwvrvle2Z8Kj%2bdPj62wdeCu9ZZD86RXh3PMg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2248 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6880 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5000 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5072 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5000 | msedge.exe | 13.107.246.60:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5000 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5000 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5000 | msedge.exe | 94.245.104.56:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
wpad.sterenwifi.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5000 | msedge.exe | Generic Protocol Command Decode | ET INFO WinHttp AutoProxy Request wpad.dat Possible BadTunnel |
1 ETPRO signatures available at the full report