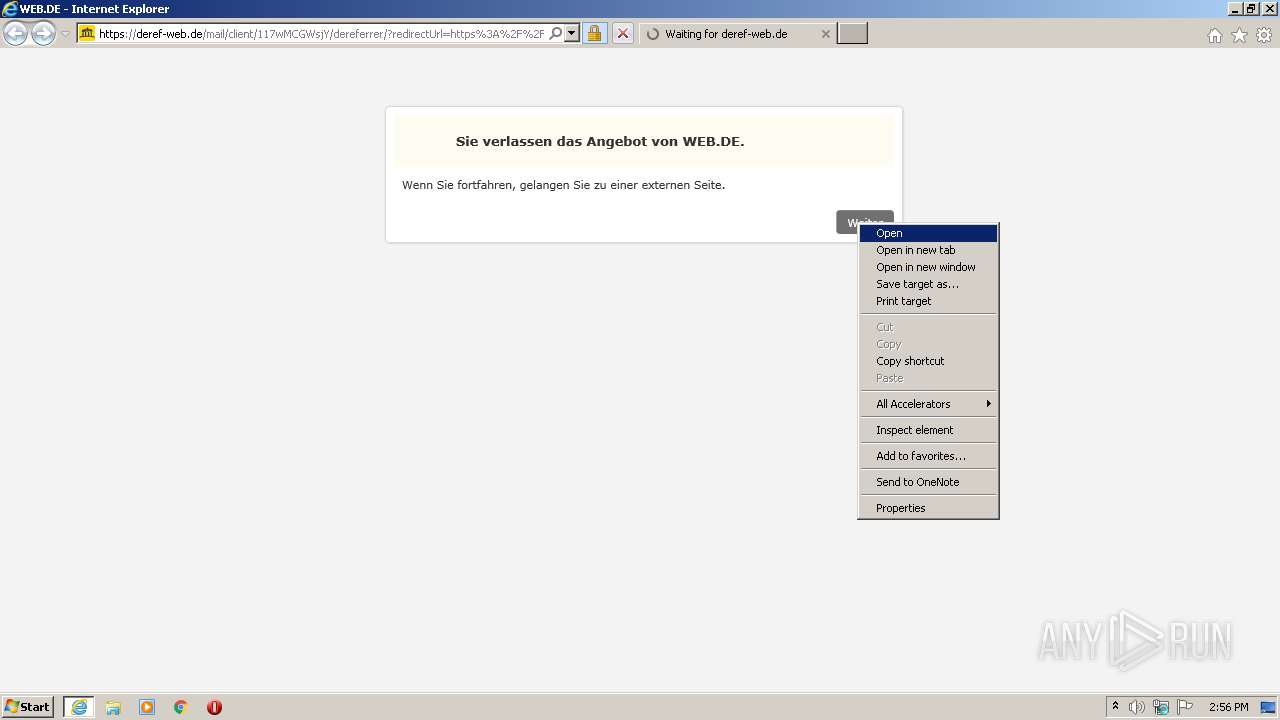
| URL: | https://deref-web.de/mail/client/117wMCGWsjY/dereferrer/?redirectUrl=https%3A%2F%2Frover.ebay.com%2Frover%2F0%2Fe12976.mnull.l3127%2F7%3Feuid%3Dfd53c0a83b0e415291542d935fcb2217%26bu%3D43060414543%26segname%3D12976%26crd%3D20200728235332%26osub%3D-1%7E1%26ch%3Dosgood%26loc%3Dhttps%253A%252F%252Fwww.ebay.de%252Fulk%252Fstart%252Fshop%26exe%3Deuid%26ext%3D39554%263%26sojTags%3Dnull%2Cbu%3Dbu%2Cch%3Dch%2Csegname%3Dsegname%2Ccrd%3Dcrd%2Curl%3Dloc%2Cosub%3Dosub |
| Full analysis: | https://app.any.run/tasks/07950598-df64-4331-aba8-2c7db1c03ff2 |
| Verdict: | Malicious activity |
| Analysis date: | July 30, 2020, 13:55:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B215B028F98DDA6EA0656345D05D2CF3 |
| SHA1: | 40A29F8C3D8B229DB3E0810D202BB9CEE82D3BF3 |
| SHA256: | 10B2D5FCB642EBDEDBF57CD3B5AE12C09F5072F35B5CFA65F1F27287E8A8126C |
| SSDEEP: | 12:2Yr+LH70Ek5WLsAMBcKBru+gQAUJtKABdAKH:2Yr+0pRjc+S2FJtbZH |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads internet explorer settings
- iexplore.exe (PID: 1996)
Reads settings of System Certificates
- iexplore.exe (PID: 1668)
Reads Internet Cache Settings
- iexplore.exe (PID: 1668)
- iexplore.exe (PID: 1996)
Changes internet zones settings
- iexplore.exe (PID: 1668)
Application launched itself
- iexplore.exe (PID: 1668)
Creates files in the user directory
- iexplore.exe (PID: 1668)
- iexplore.exe (PID: 1996)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1668)
Changes settings of System certificates
- iexplore.exe (PID: 1668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1668 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://deref-web.de/mail/client/117wMCGWsjY/dereferrer/?redirectUrl=https%3A%2F%2Frover.ebay.com%2Frover%2F0%2Fe12976.mnull.l3127%2F7%3Feuid%3Dfd53c0a83b0e415291542d935fcb2217%26bu%3D43060414543%26segname%3D12976%26crd%3D20200728235332%26osub%3D-1%7E1%26ch%3Dosgood%26loc%3Dhttps%253A%252F%252Fwww.ebay.de%252Fulk%252Fstart%252Fshop%26exe%3Deuid%26ext%3D39554%263%26sojTags%3Dnull%2Cbu%3Dbu%2Cch%3Dch%2Csegname%3Dsegname%2Ccrd%3Dcrd%2Curl%3Dloc%2Cosub%3Dosub" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1996 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1668 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
344
Read events
260
Write events
81
Delete events
3
Modification events
| (PID) Process: | (1668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1115986962 | |||
| (PID) Process: | (1668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30828153 | |||
| (PID) Process: | (1668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
27
Text files
23
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1996 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE436.tmp | — | |
MD5:— | SHA256:— | |||
| 1996 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE437.tmp | — | |
MD5:— | SHA256:— | |||
| 1668 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CE6B081CE591CE6EF3D072A662222D2C_9C4315B7BB036EAEFD984DBABC6CBC99 | der | |
MD5:— | SHA256:— | |||
| 1996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6D0F78EB80184FFBF3BBB2E13A960564_FB4D3EB8B842A531376FB2F4A71D6EAE | binary | |
MD5:— | SHA256:— | |||
| 1996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6D0F78EB80184FFBF3BBB2E13A960564_FB4D3EB8B842A531376FB2F4A71D6EAE | der | |
MD5:— | SHA256:— | |||
| 1996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | der | |
MD5:— | SHA256:— | |||
| 1996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | binary | |
MD5:— | SHA256:— | |||
| 1668 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabFBE5.tmp | — | |
MD5:— | SHA256:— | |||
| 1668 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarFBE6.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
36
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1996 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAZuXsb8%2F9QDINjnSHoBz6E%3D | US | der | 471 b | whitelisted |
1996 | iexplore.exe | GET | 200 | 46.29.101.84:80 | http://ocsp.telesec.de/ocspr/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBTFx4BvOw7Ixax9%2BP2ZItzIsVvQvwQUv1kgNgB5oKAia4zV8mHSuCzLgkoCCH45x60d2fBD | DE | der | 1.55 Kb | whitelisted |
1996 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
1996 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
1996 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAZuXsb8%2F9QDINjnSHoBz6E%3D | US | der | 471 b | whitelisted |
1996 | iexplore.exe | GET | 200 | 217.170.186.115:80 | http://ocsp.serverpass.telesec.de/ocspr/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT66Lqmxf42hHuY8hKFZzVwT4YoDAQUlMh0RvU6tEZIJvgryjQeViYEEgACEDla9uGLsVeaac0BM0qtyR8%3D | DE | der | 1.66 Kb | whitelisted |
1668 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1668 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1996 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 581 b | whitelisted |
1996 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
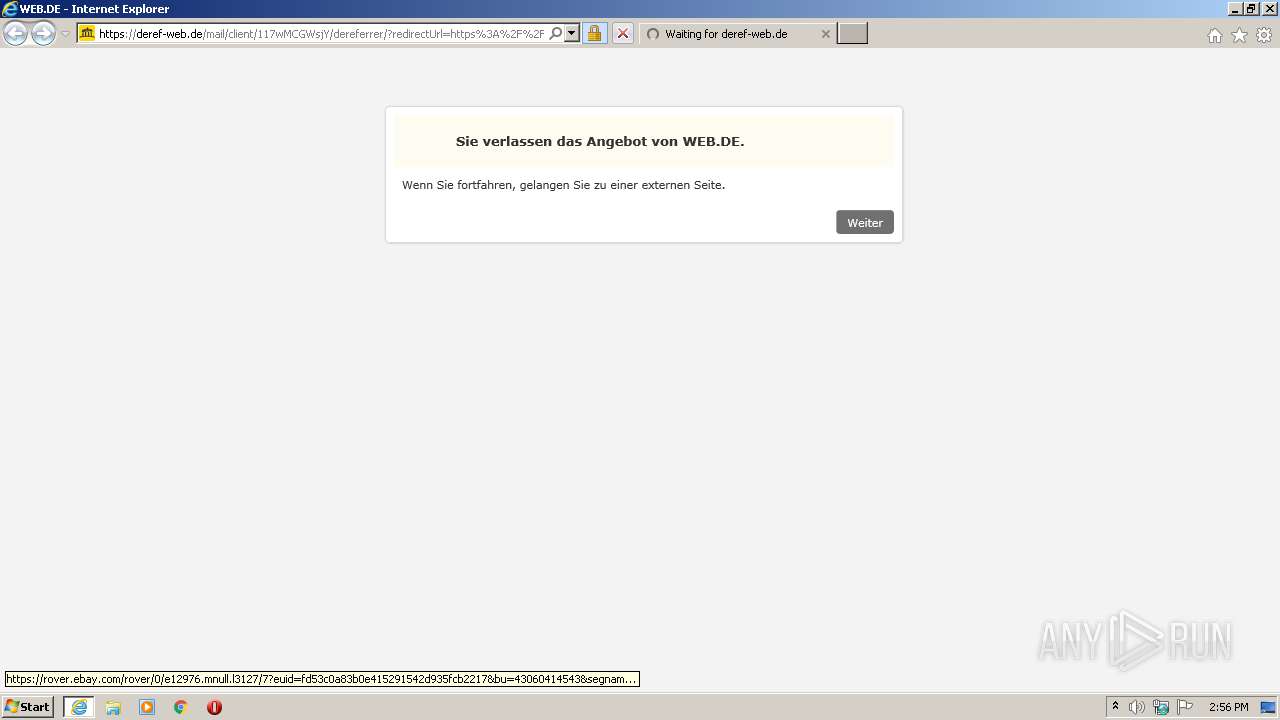
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 46.29.101.84:80 | ocsp.telesec.de | T-Systems International GmbH | DE | unknown |
1996 | iexplore.exe | 217.72.196.59:443 | deref-web.de | 1&1 Internet SE | DE | unknown |
1996 | iexplore.exe | 104.111.215.22:443 | cdn.webde.de | Akamai International B.V. | NL | whitelisted |
1996 | iexplore.exe | 217.170.186.115:80 | ocsp.telesec.de | I.T.E.N.O.S. International Telecom Network Operation Services GmbH | DE | unknown |
1996 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1668 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 104.111.215.22:443 | cdn.webde.de | Akamai International B.V. | NL | whitelisted |
1668 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1996 | iexplore.exe | 23.210.249.45:443 | img.ui-portal.de | Akamai International B.V. | NL | whitelisted |
1668 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
deref-web.de |
| unknown |
ocsp.telesec.de |
| whitelisted |
ocsp.serverpass.telesec.de |
| whitelisted |
cdn.webde.de |
| whitelisted |
img.ui-portal.de |
| suspicious |
js.ui-portal.de |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
img.web.de |
| suspicious |