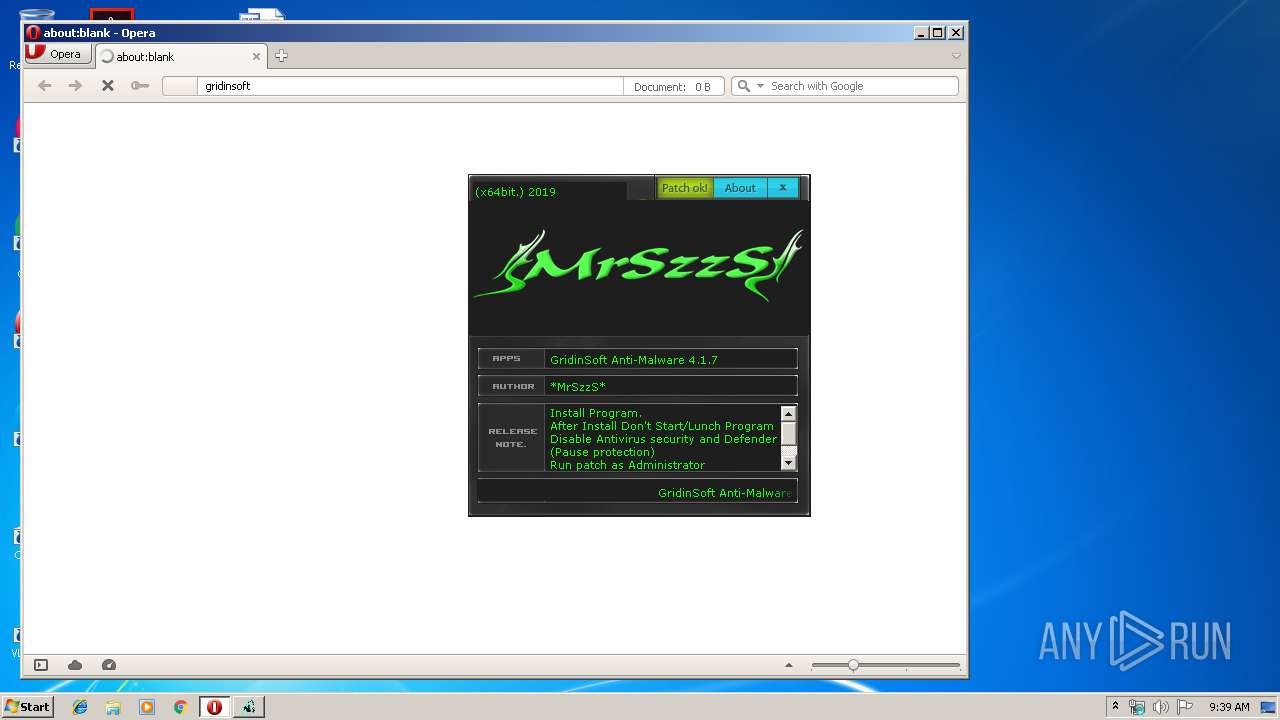
| File name: | (x64bit.).MrSzzS-patch.exe |
| Full analysis: | https://app.any.run/tasks/7d9fd50b-fa01-4d54-a421-487c7d0746e3 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2019, 09:38:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 31678EC8187CED5F390EADBD308D48DB |
| SHA1: | 7AFCCEA73BB8CBEEA795485F15E496668023483E |
| SHA256: | 10A5575B213C3D3AC4CA7EC4B9E67155E5BFD8F77154D019F9A07B0323B410AA |
| SSDEEP: | 24576:qlHUfBQVQyoTOPiNax4dI0MnJ9BYRrt3bu1H+P:40fpyoTi4axX01P3 |
MALICIOUS
Loads dropped or rewritten executable
- (x64bit.).MrSzzS-patch.exe (PID: 1916)
SUSPICIOUS
Executable content was dropped or overwritten
- (x64bit.).MrSzzS-patch.exe (PID: 1916)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2856)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2856)
Starts CMD.EXE for commands execution
- (x64bit.).MrSzzS-patch.exe (PID: 1916)
Creates files in the program directory
- (x64bit.).MrSzzS-patch.exe (PID: 1916)
INFO
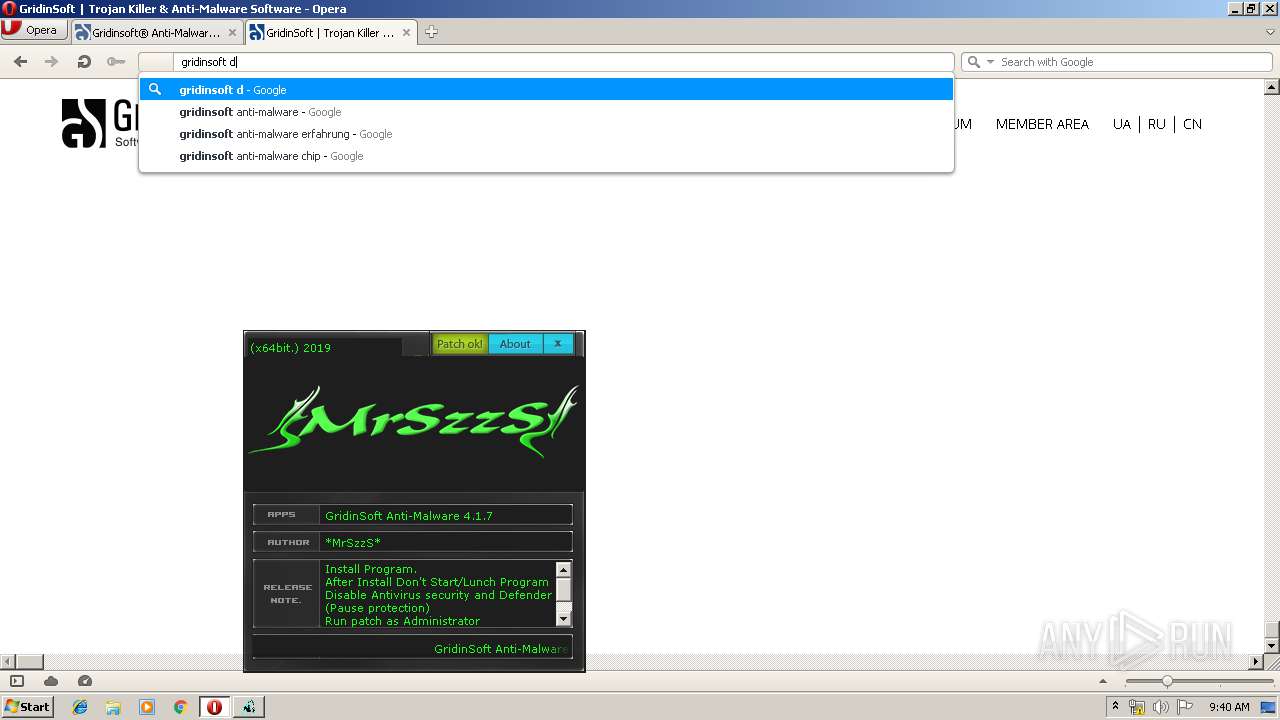
Manual execution by user
- opera.exe (PID: 952)
Creates files in the user directory
- opera.exe (PID: 952)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:21 21:59:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 512 |
| InitializedDataSize: | 835072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x102b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Dec-2012 20:59:46 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Dec-2012 20:59:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000001F6 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.06408 |
.rdata | 0x00002000 | 0x000001D8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.27064 |
.data | 0x00003000 | 0x00000034 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.568988 |
.rsrc | 0x00004000 | 0x000CB678 | 0x000CB800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99264 |
.reloc | 0x000D0000 | 0x00000052 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.736046 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85663 | 898 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
500 | 1.91924 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
DLL | 7.99981 | 822272 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
kernel32.dll |
Total processes
45
Monitored processes
7
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 952 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 1608 | taskkill.exe /f /t /im gsam.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1916 | "C:\Users\admin\AppData\Local\Temp\(x64bit.).MrSzzS-patch.exe" | C:\Users\admin\AppData\Local\Temp\(x64bit.).MrSzzS-patch.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1940 | reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\GridinSoft\Anti-Malware" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2856 | cmd /c "C:\Program Files\GridinSoft Anti-Malware\stop.bat" | C:\Windows\system32\cmd.exe | — | (x64bit.).MrSzzS-patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2932 | "C:\Users\admin\AppData\Local\Temp\(x64bit.).MrSzzS-patch.exe" | C:\Users\admin\AppData\Local\Temp\(x64bit.).MrSzzS-patch.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3932 | "C:\Windows\regedit.exe" /s "C:\Users\admin\AppData\Local\Temp\\regpatch.reg" | C:\Windows\regedit.exe | — | (x64bit.).MrSzzS-patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
804
Read events
681
Write events
122
Delete events
1
Modification events
| (PID) Process: | (1916) (x64bit.).MrSzzS-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0028007800360034006200690074002E0029002E004D00720053007A007A0053002D00700061007400630068002E00650078006500000043003A005C00500072006F006700720061006D002000460069006C00650073005C00470072006900640069006E0053006F0066007400200041006E00740069002D004D0061006C0077006100720065000000 | |||
| (PID) Process: | (1916) (x64bit.).MrSzzS-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (1916) (x64bit.).MrSzzS-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1916) (x64bit.).MrSzzS-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 01000000070000000200000009000000080000000000000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1916) (x64bit.).MrSzzS-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000040000000200000003000000FFFFFFFF | |||
| (PID) Process: | (1916) (x64bit.).MrSzzS-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\1 |
| Operation: | write | Name: | 5 |
Value: 74003100000000007D4FE24C100047524944494E7E3100005C0008000400EFBE7D4FE24C7D4FE24C2A000000DECB000000000E000000000000000000000000000000470072006900640069006E0053006F0066007400200041006E00740069002D004D0061006C007700610072006500000018000000 | |||
| (PID) Process: | (1916) (x64bit.).MrSzzS-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\1 |
| Operation: | write | Name: | MRUListEx |
Value: 050000000400000003000000010000000000000002000000FFFFFFFF | |||
| (PID) Process: | (1916) (x64bit.).MrSzzS-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1916) (x64bit.).MrSzzS-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\1\5 |
| Operation: | write | Name: | NodeSlot |
Value: 112 | |||
| (PID) Process: | (1916) (x64bit.).MrSzzS-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\1\5 |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
Executable files
2
Suspicious files
181
Text files
226
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1916 | (x64bit.).MrSzzS-patch.exe | C:\Users\admin\AppData\Local\Temp\regpatch.reg | — | |
MD5:— | SHA256:— | |||
| 952 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr49C5.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr4A05.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4YV4BLNVF1BXBCHZF886.temp | — | |
MD5:— | SHA256:— | |||
| 952 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr6B88.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr7741.tmp | — | |
MD5:— | SHA256:— | |||
| 1916 | (x64bit.).MrSzzS-patch.exe | C:\Program Files\GridinSoft Anti-Malware\stop.bat | text | |
MD5:— | SHA256:— | |||
| 1916 | (x64bit.).MrSzzS-patch.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:— | SHA256:— | |||
| 952 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
68
TCP/UDP connections
430
DNS requests
125
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
952 | opera.exe | GET | 302 | 172.217.18.3:80 | http://www.google.com.ua/search?client=opera&q=gridinsoft&sourceid=opera&ie=utf-8&oe=utf-8&channel=suggest | US | html | 339 b | whitelisted |
952 | opera.exe | GET | 302 | 172.217.18.3:80 | http://www.google.com.ua/search?q=gridinsoft&sourceid=opera&ie=utf-8&oe=utf-8&channel=suggest | US | html | 323 b | whitelisted |
952 | opera.exe | GET | 200 | 172.217.22.99:80 | http://crl.pki.goog/gsr2/gsr2.crl | US | der | 950 b | whitelisted |
952 | opera.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDO9A16CtM3pwgAAAAAHYok | US | der | 472 b | whitelisted |
952 | opera.exe | GET | 200 | 216.58.210.14:80 | http://clients1.google.com/complete/search?q=gridi&client=opera-suggest-omnibox&hl=de | US | text | 107 b | whitelisted |
952 | opera.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBaORV%2BLyHv2AgAAAABLjUQ%3D | US | der | 471 b | whitelisted |
952 | opera.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEEAqmCMtyGwTCAAAAAAdibE%3D | US | der | 471 b | whitelisted |
952 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.comodoca.com/COMODORSACertificationAuthority.crl | US | der | 812 b | whitelisted |
952 | opera.exe | GET | 200 | 216.58.210.14:80 | http://clients1.google.com/complete/search?q=gridinsof&client=opera-suggest-omnibox&hl=de | US | text | 132 b | whitelisted |
952 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 581 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
952 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
952 | opera.exe | 172.217.22.99:80 | crl.pki.goog | Google Inc. | US | whitelisted |
952 | opera.exe | 216.58.210.14:80 | clients1.google.com | Google Inc. | US | whitelisted |
952 | opera.exe | 172.217.18.3:80 | www.google.com.ua | Google Inc. | US | whitelisted |
952 | opera.exe | 185.26.182.112:80 | sitecheck2.opera.com | Opera Software AS | — | malicious |
952 | opera.exe | 172.217.18.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
952 | opera.exe | 172.217.16.131:443 | id.google.com.ua | Google Inc. | US | whitelisted |
952 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
952 | opera.exe | 192.241.129.49:443 | gridinsoft.com | Digital Ocean, Inc. | US | suspicious |
952 | opera.exe | 172.217.18.163:443 | id.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
crl.pki.goog |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
id.google.com.ua |
| whitelisted |
id.google.com |
| whitelisted |
gridinsoft.com |
| suspicious |