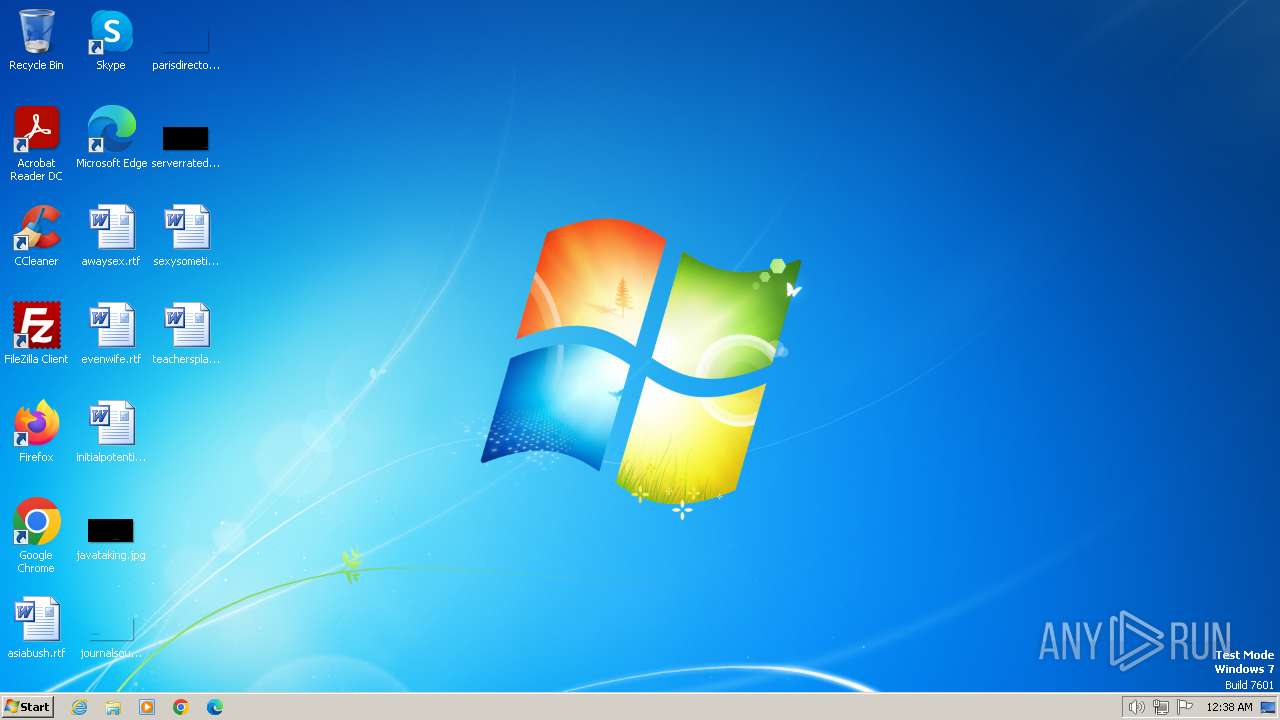
| File name: | dobrota.exe |
| Full analysis: | https://app.any.run/tasks/dc392d33-b6b1-4c55-9a76-a8a9d31ff102 |
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2024, 23:38:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1C33F964FBF5B3642D02E4B20BA6F2AC |
| SHA1: | DCEC14364A4548CE394906487A37F98BB1D12198 |
| SHA256: | 10A45DC010DF96CBD65BFD8A59E906CA5F98DD6F7541CF02BDFC17DF8384BB8F |
| SSDEEP: | 98304:sAY5AutzlARgPsNejO66rrQ97TKf2Ssk953qhdr5DoGrYRQWwIRcahreL9dFRVqA:OCmG/vRePgOh |
MALICIOUS
Drops the executable file immediately after the start
- dobrota.exe (PID: 3884)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 1476)
SUSPICIOUS
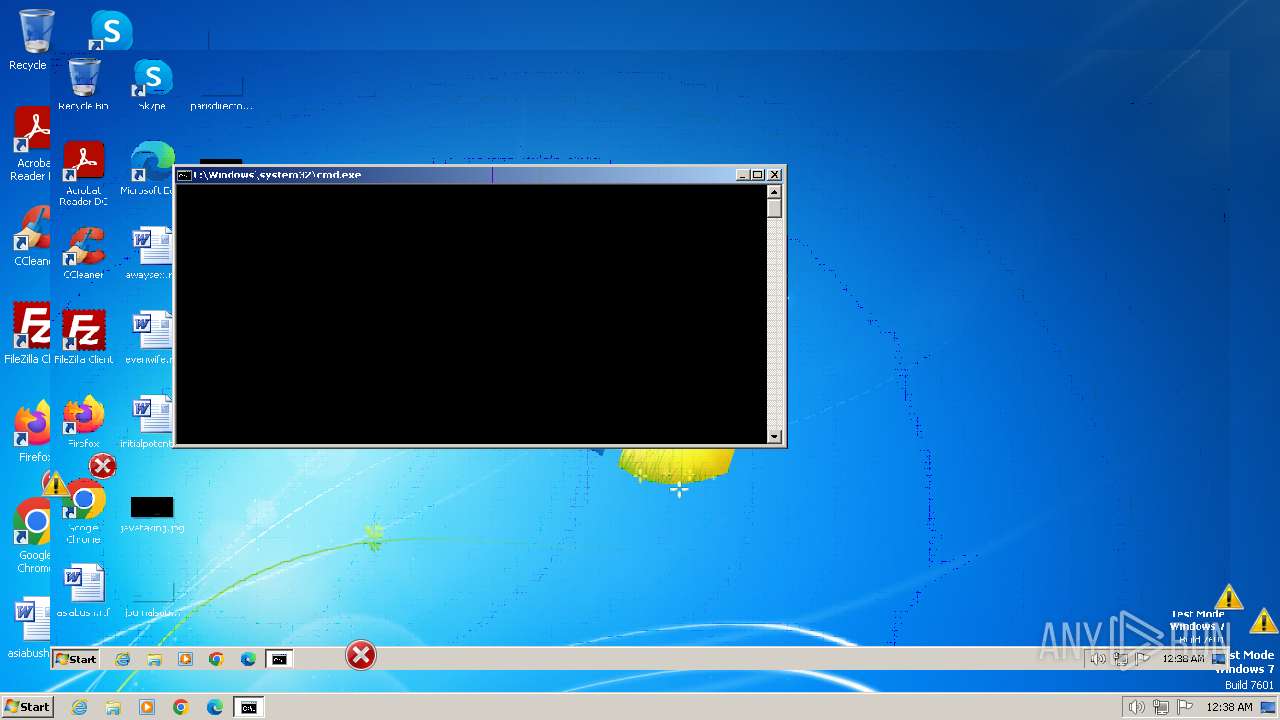
Executing commands from a ".bat" file
- dobrota.exe (PID: 3884)
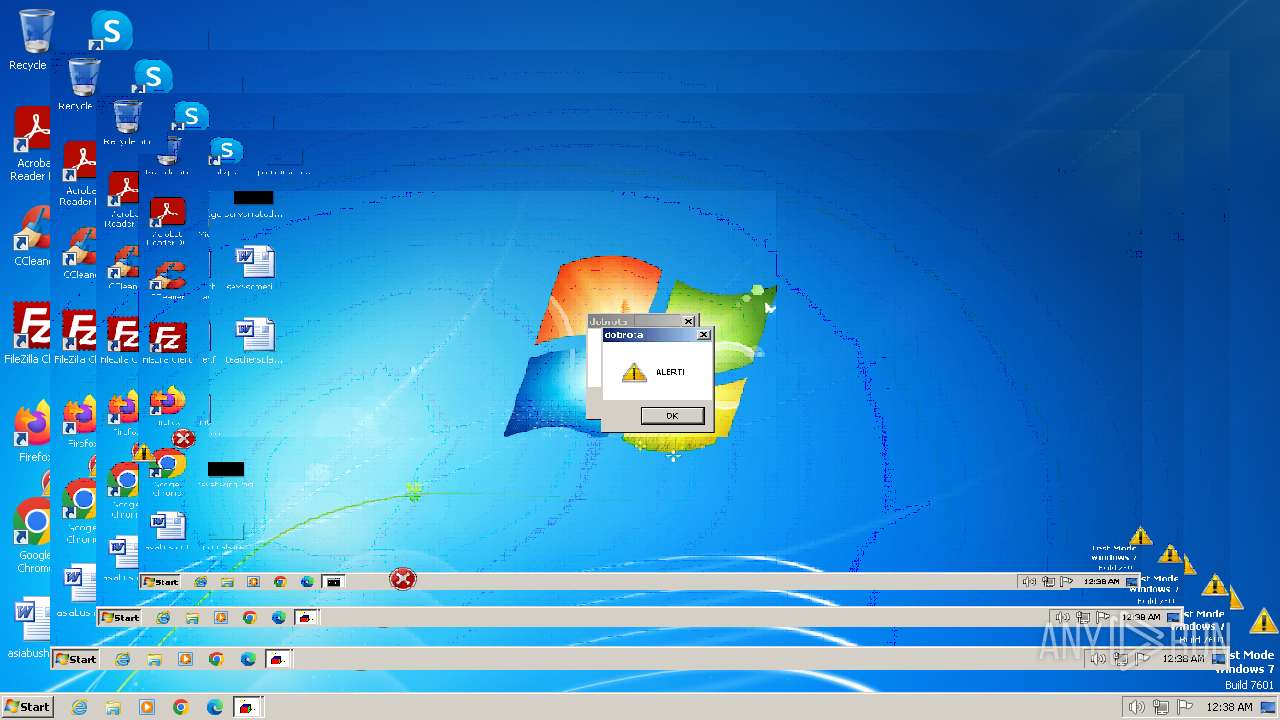
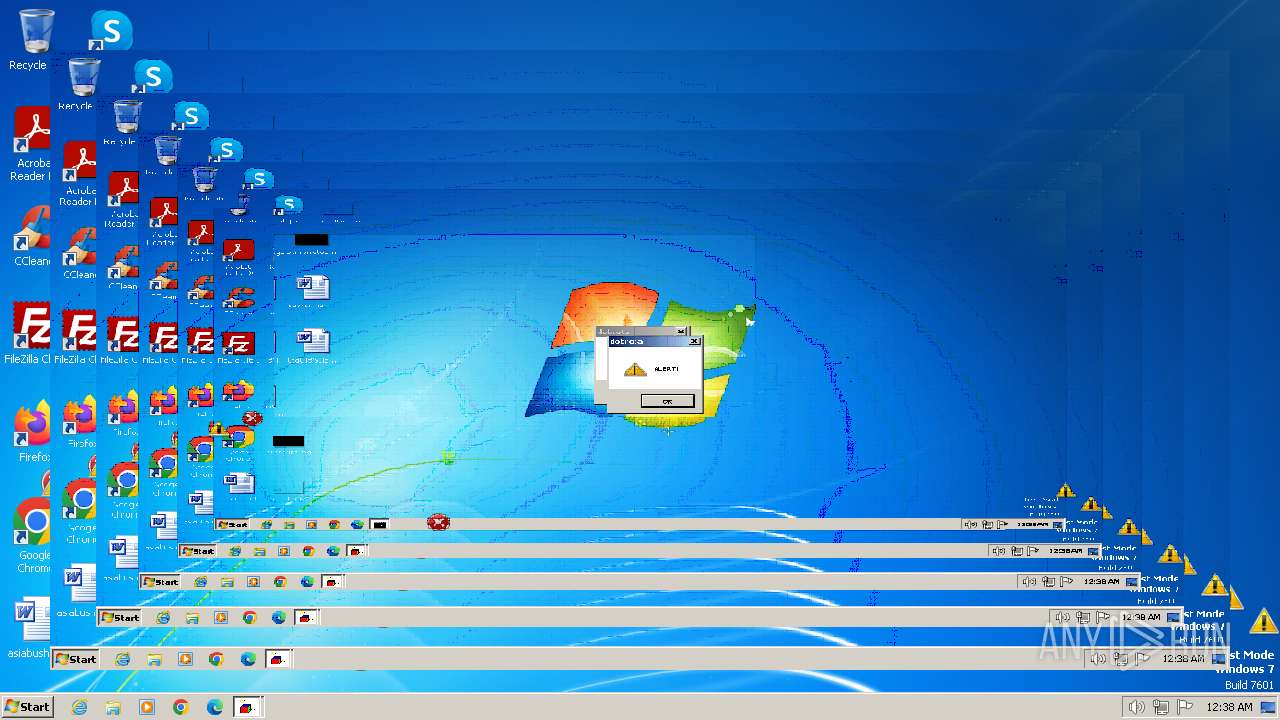
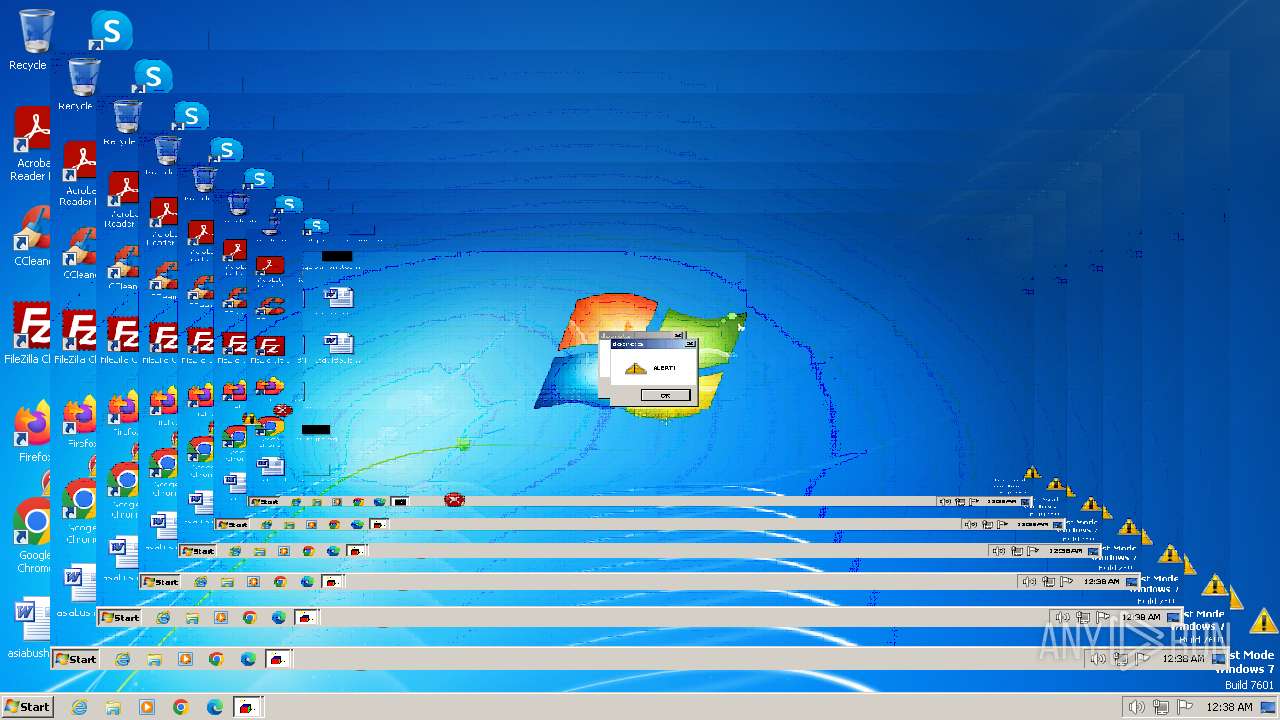
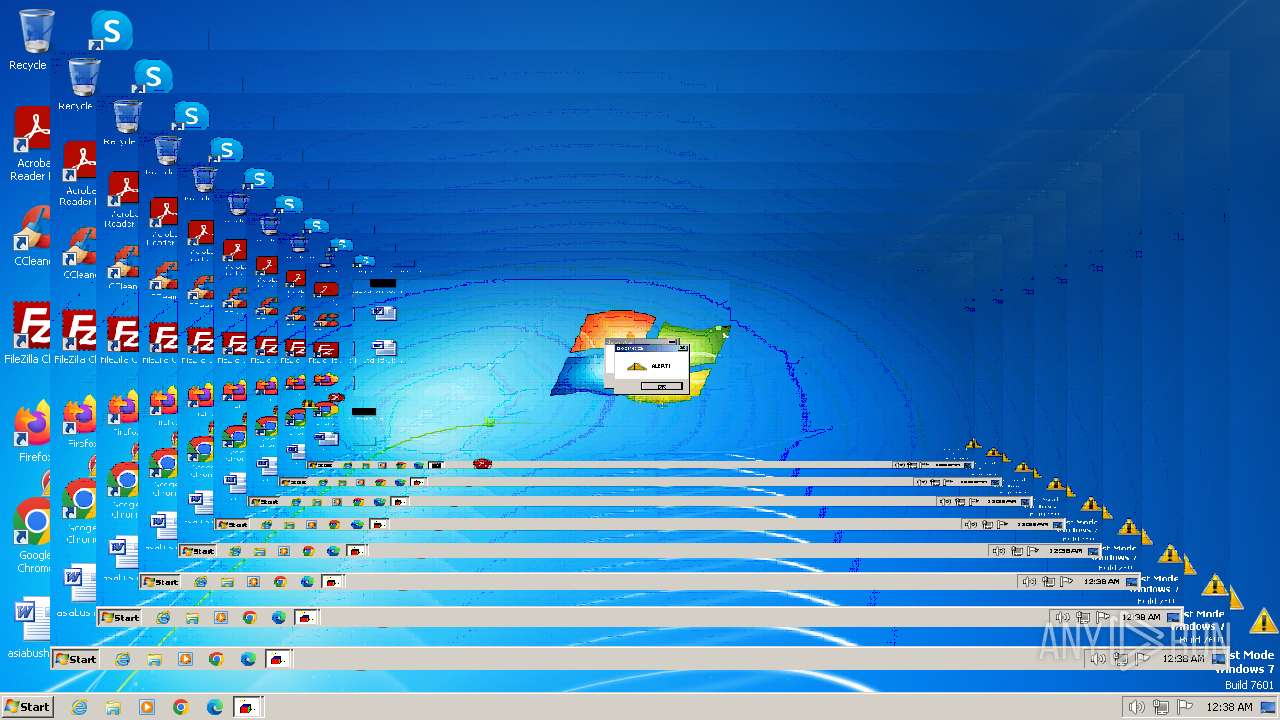
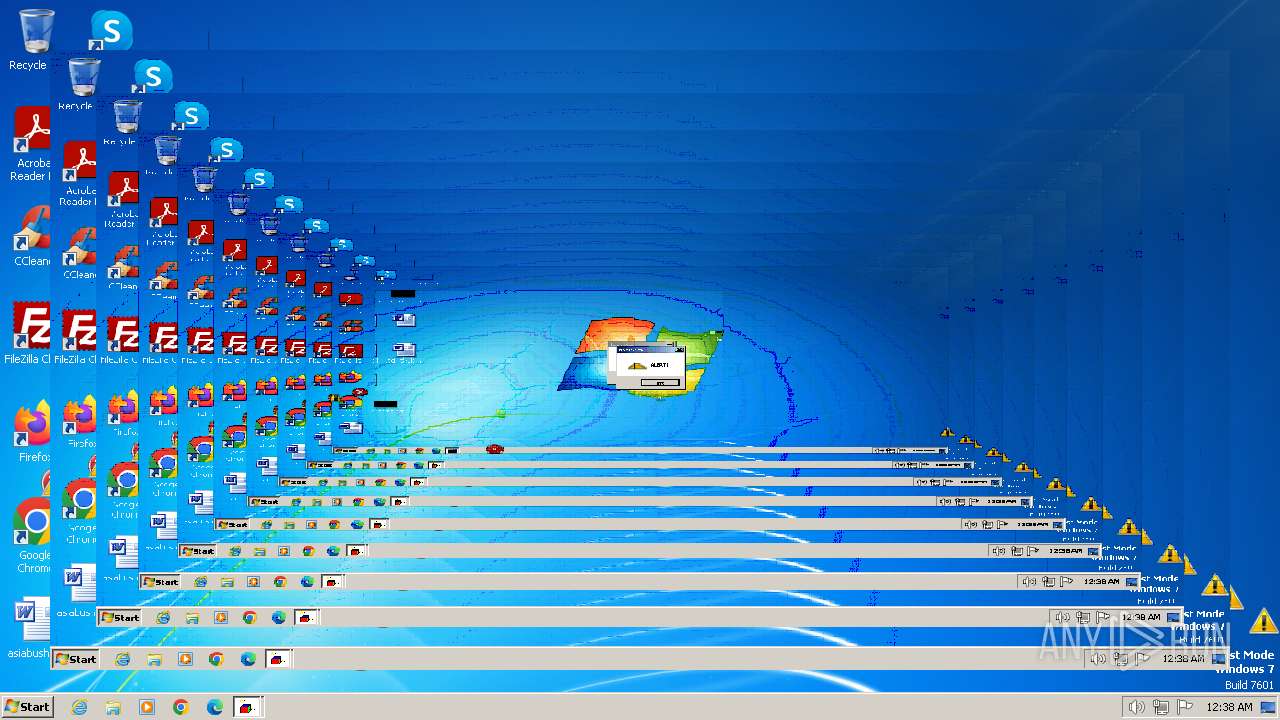
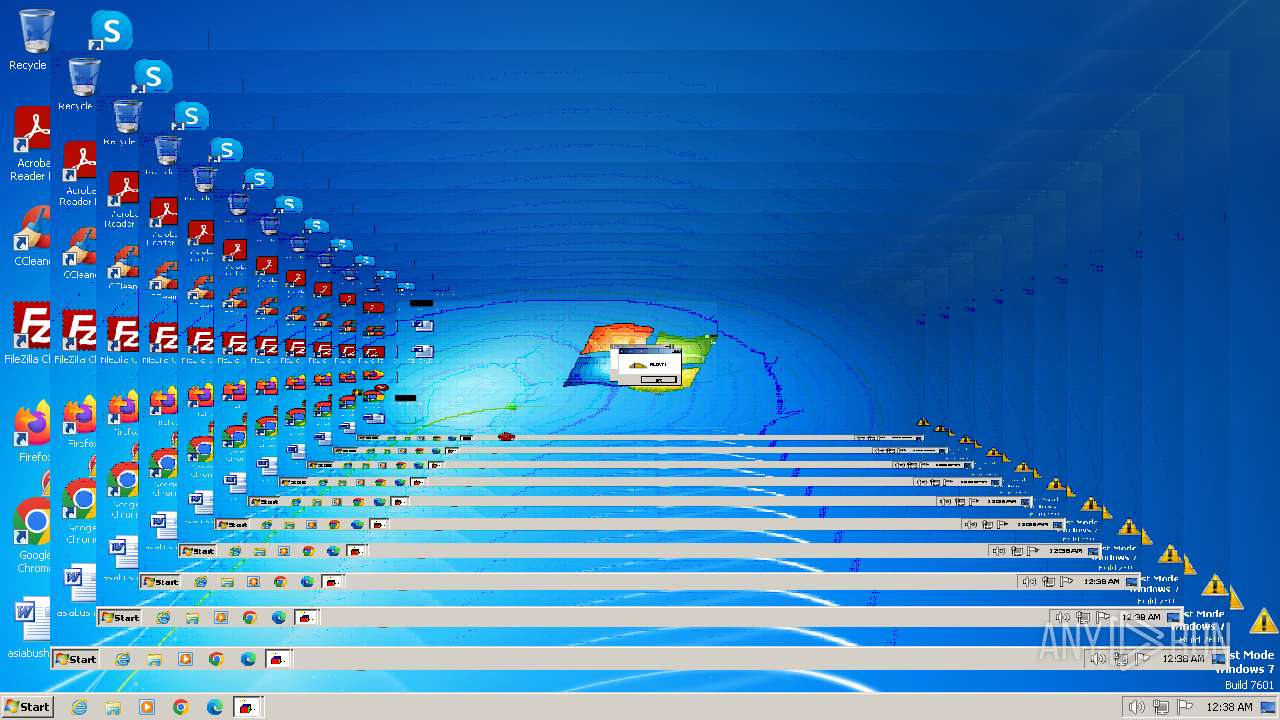
The executable file from the user directory is run by the CMD process
- crazywarningicons.exe (PID: 1680)
- erroriconscursor.exe (PID: 764)
- mbr.exe (PID: 2496)
- toonel.exe (PID: 1616)
- INVERS.exe (PID: 2544)
- erroricons.exe (PID: 2512)
- crazyinvers.exe (PID: 3844)
Reads security settings of Internet Explorer
- dobrota.exe (PID: 3884)
Executable content was dropped or overwritten
- dobrota.exe (PID: 3884)
Reads the Internet Settings
- cmd.exe (PID: 3112)
- wscript.exe (PID: 1476)
- dobrota.exe (PID: 3884)
The process executes VB scripts
- cmd.exe (PID: 3112)
Starts CMD.EXE for commands execution
- dobrota.exe (PID: 3884)
INFO
Checks supported languages
- erroricons.exe (PID: 2512)
- dobrota.exe (PID: 3884)
- mbr.exe (PID: 2496)
- erroriconscursor.exe (PID: 764)
- crazywarningicons.exe (PID: 1680)
- crazyinvers.exe (PID: 3844)
- toonel.exe (PID: 1616)
- INVERS.exe (PID: 2544)
Reads the computer name
- dobrota.exe (PID: 3884)
Create files in a temporary directory
- dobrota.exe (PID: 3884)
Checks proxy server information
- wscript.exe (PID: 1476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:06:11 09:16:47+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 201728 |
| InitializedDataSize: | 114688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1eef0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
53
Monitored processes
13
Malicious processes
2
Suspicious processes
1
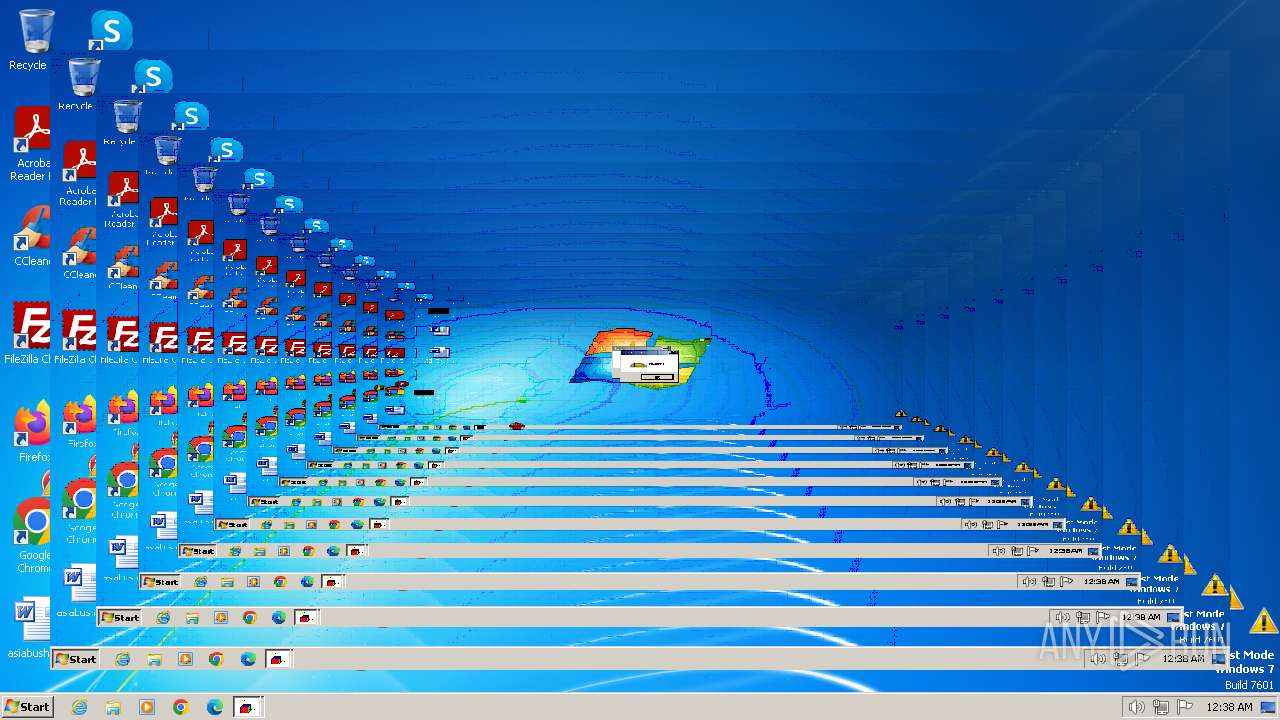
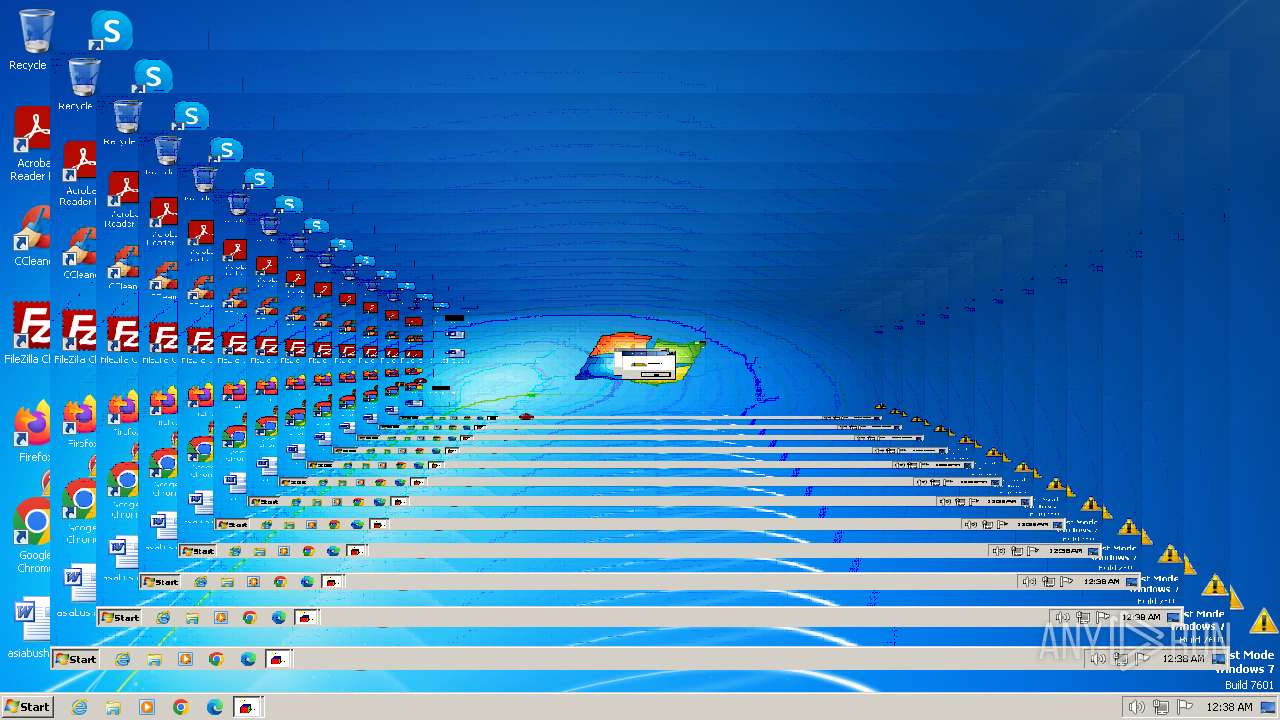
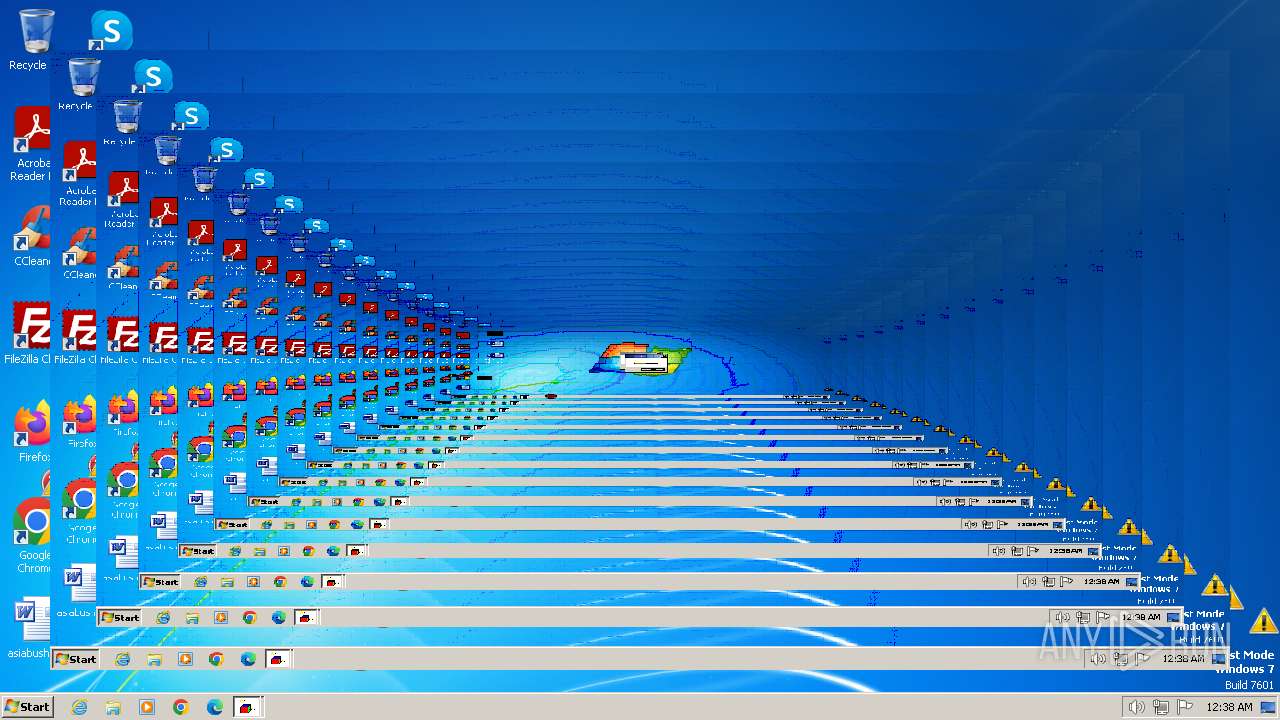
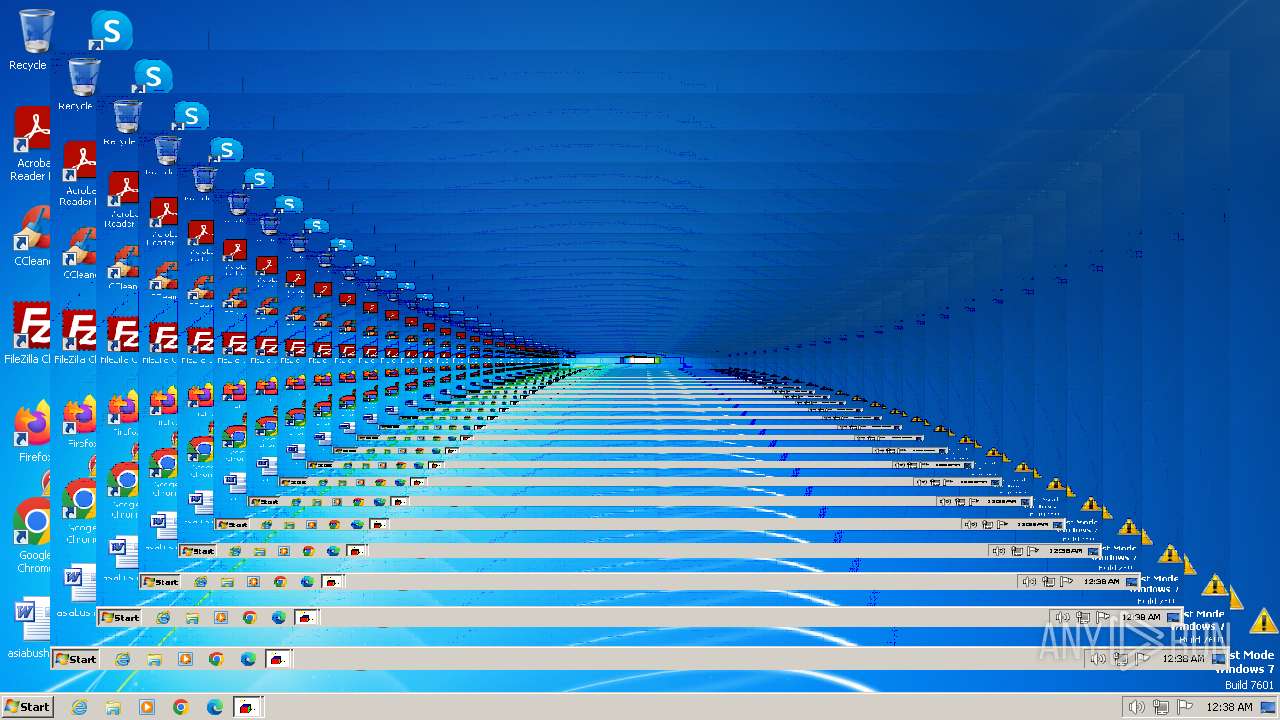
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | erroriconscursor.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\erroriconscursor.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1476 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX0\sound.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1616 | toonel.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\toonel.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1680 | crazywarningicons.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\crazywarningicons.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2496 | mbr.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\mbr.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2512 | erroricons.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\erroricons.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2532 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX0\messages.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2536 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX0\messages2.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2544 | INVERS.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\INVERS.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 3112 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\RarSFX0\start_dobrota.bat" " | C:\Windows\System32\cmd.exe | — | dobrota.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
6 521
Read events
6 470
Write events
47
Delete events
4
Modification events
| (PID) Process: | (3884) dobrota.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3884) dobrota.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3884) dobrota.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3884) dobrota.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3112) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3112) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3112) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3112) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1476) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1476) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
9
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3884 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\dobrota.mp3 | — | |
MD5:— | SHA256:— | |||
| 2496 | mbr.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 3884 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\INVERS.exe | executable | |
MD5:5134F289DBF4ABAE370E3F36B637B73E | SHA256:E69C9383B5D9FE4E069DDEE15797C52E9116F883AD3B1717D2519621AB2751B2 | |||
| 3884 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\erroricons.exe | executable | |
MD5:7F31508D95BE3FE50E4E9AA646E86A12 | SHA256:994EFDB644CA1ACB029DFD8D8EEBA440E1CB74D93841B17F21165B9900730B15 | |||
| 3884 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\sound.vbs | text | |
MD5:C36C15E1F99E1C0D093B9B089B1073C5 | SHA256:3D6123CAE8AC645D9C9D33B0DADA869A7FDD5117A2BF0F9080E4E30FE5BED736 | |||
| 3884 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\erroriconscursor.exe | executable | |
MD5:135EEB256E92D261066CFD3FFD31FB3E | SHA256:F0FE346146C30129ED6F507906C973F1A54C7D8DD8821C97E9B6EDC42545699D | |||
| 3884 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\libgcc_s_dw2-1.dll | executable | |
MD5:E2AC23418781F632311513944EDD0A4C | SHA256:B4CC93CF4D7C2906C1929C079CD98EF00C7A33832E132AC57ADDE71857082E36 | |||
| 3884 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\mbr.exe | executable | |
MD5:8562ED46D745DCEB3CC268693CA25C83 | SHA256:EA5D21E6598D52B30E9D055BC406C6227BBADB5C493ADDB27B32FB16A6DCAE8C | |||
| 3884 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\messages2.vbs | text | |
MD5:63954D8930E517637C254F9DA0749E7A | SHA256:BFFA14678B8C39C2FBFA54B76FBAC5F750AEBC8DC2954DA10A55B7F1F90F351C | |||
| 3884 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\toonel.exe | executable | |
MD5:A84257E64CFBD9F6C0A574AF416BC0D1 | SHA256:FE7FF85B95EC06CE0F3CB49FDFA4D36DE1F08669D36D381794AAF597510AFAD7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
9
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 217.20.57.26:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | US | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | GB | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1372 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1372 | svchost.exe | 217.20.57.26:80 | ctldl.windowsupdate.com | — | US | unknown |
1372 | svchost.exe | 23.32.238.107:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
1060 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |