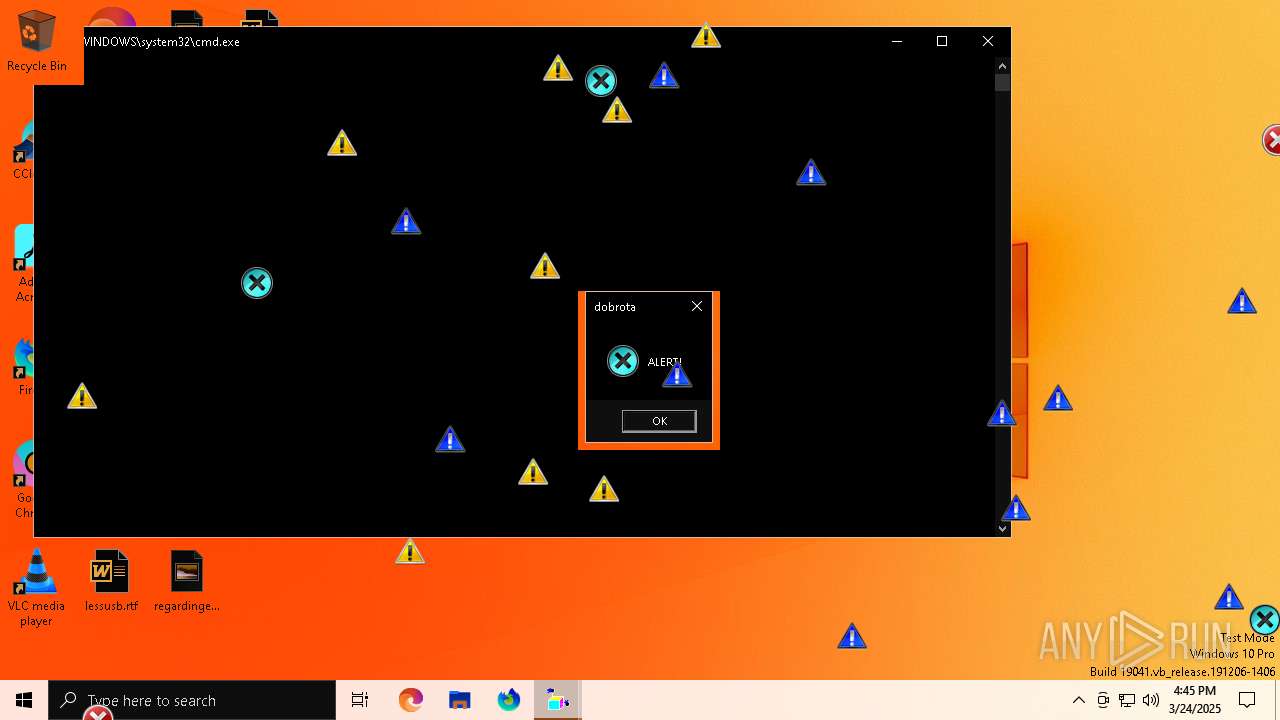
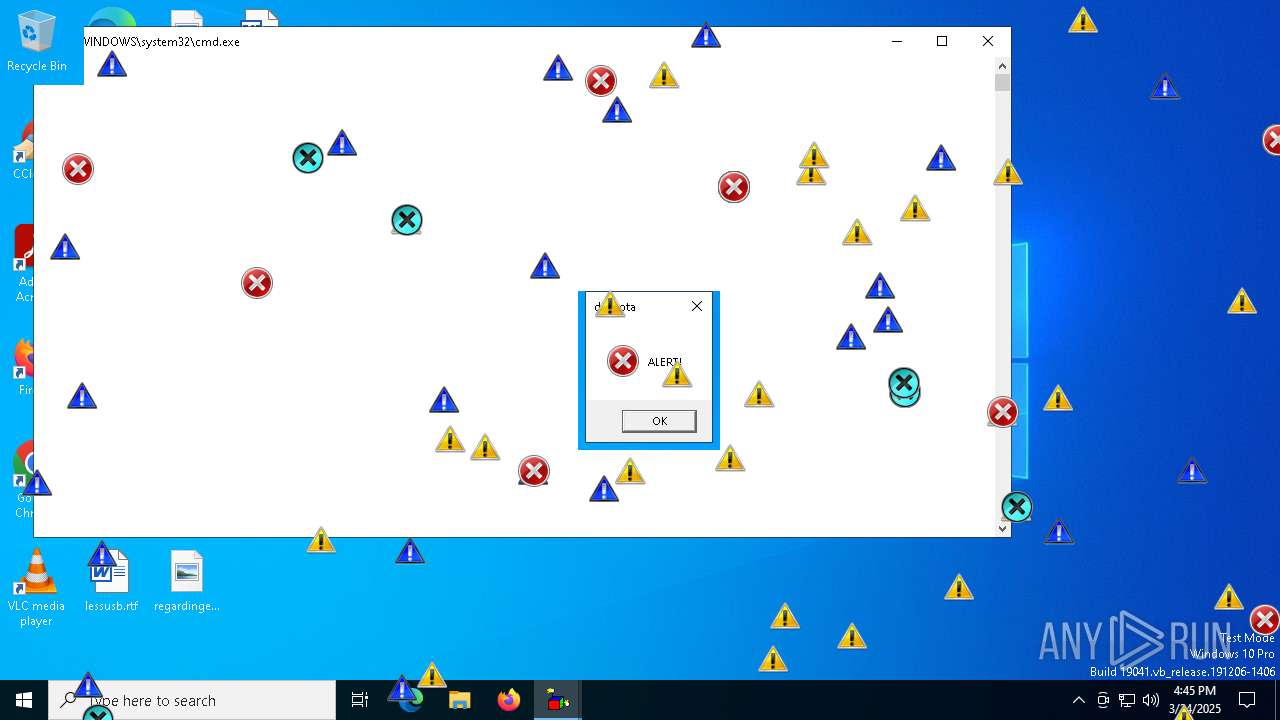
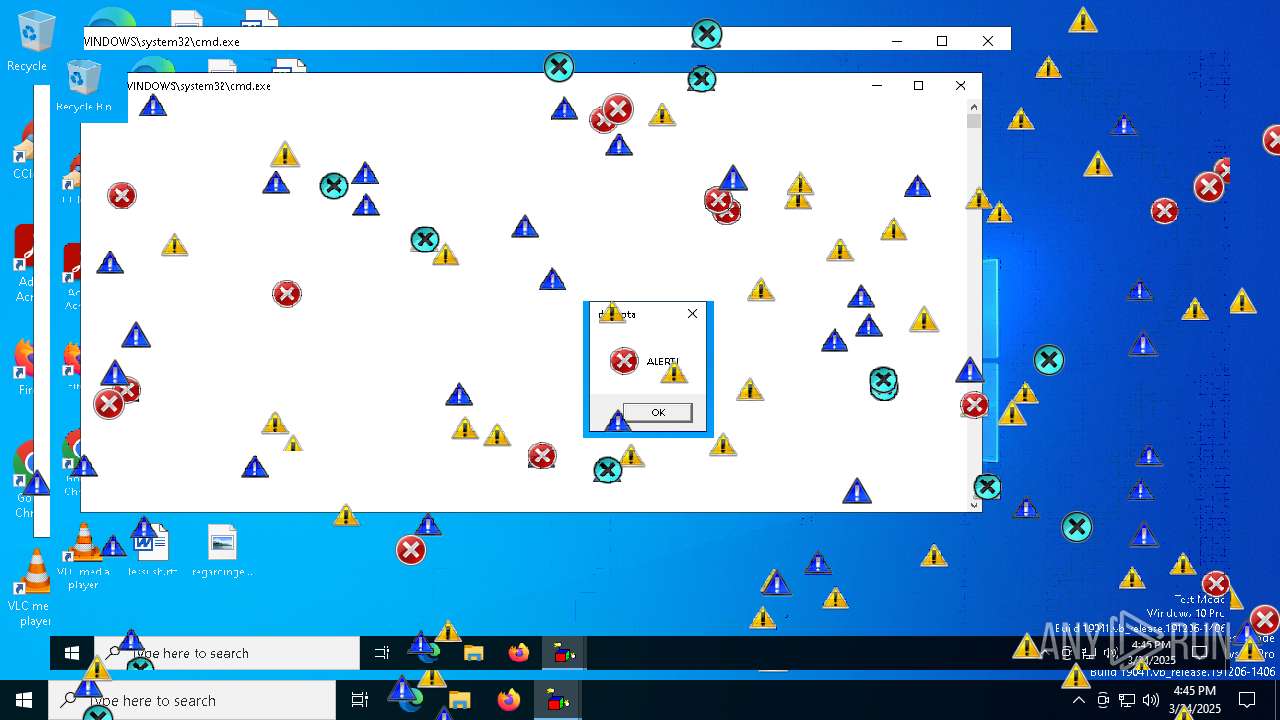
| File name: | dobrota.exe |
| Full analysis: | https://app.any.run/tasks/14366b9e-ab44-4e30-9b04-e8e49fbf9424 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 16:45:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 1C33F964FBF5B3642D02E4B20BA6F2AC |
| SHA1: | DCEC14364A4548CE394906487A37F98BB1D12198 |
| SHA256: | 10A45DC010DF96CBD65BFD8A59E906CA5F98DD6F7541CF02BDFC17DF8384BB8F |
| SSDEEP: | 98304:sAY5AutzlARgPsNejO66rrQ97TKf2Ssk953qhdr5DoGrYRQWwIRcahreL9dFRVqA:OCmG/vRePgOh |
MALICIOUS
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 7784)
SUSPICIOUS
The executable file from the user directory is run by the CMD process
- mbr.exe (PID: 7732)
- INVERS.exe (PID: 7812)
- erroricons.exe (PID: 7792)
- crazywarningicons.exe (PID: 7820)
- crazyinvers.exe (PID: 7840)
- erroriconscursor.exe (PID: 7872)
- toonel.exe (PID: 7900)
Starts CMD.EXE for commands execution
- dobrota.exe (PID: 7408)
Executable content was dropped or overwritten
- dobrota.exe (PID: 7408)
The process executes VB scripts
- cmd.exe (PID: 7608)
Executing commands from a ".bat" file
- dobrota.exe (PID: 7408)
Working with threads in the GNU C Compiler (GCC) libraries related mutex has been found
- INVERS.exe (PID: 7812)
- crazyinvers.exe (PID: 7840)
SQL CE related mutex has been found
- wscript.exe (PID: 7784)
INFO
Reads the computer name
- dobrota.exe (PID: 7408)
Checks supported languages
- dobrota.exe (PID: 7408)
- erroricons.exe (PID: 7792)
- crazywarningicons.exe (PID: 7820)
- erroriconscursor.exe (PID: 7872)
- toonel.exe (PID: 7900)
Checks proxy server information
- wscript.exe (PID: 7784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:06:11 09:16:47+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 201728 |
| InitializedDataSize: | 114688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1eef0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
142
Monitored processes
16
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7288 | "C:\Users\admin\AppData\Local\Temp\dobrota.exe" | C:\Users\admin\AppData\Local\Temp\dobrota.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 7408 | "C:\Users\admin\AppData\Local\Temp\dobrota.exe" | C:\Users\admin\AppData\Local\Temp\dobrota.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 7452 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7504 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7608 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\RarSFX0\start_dobrota.bat" " | C:\Windows\SysWOW64\cmd.exe | — | dobrota.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7732 | mbr.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\mbr.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 7784 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX0\sound.vbs" | C:\Windows\SysWOW64\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7792 | erroricons.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\erroricons.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7812 | INVERS.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\INVERS.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
3 005
Read events
2 936
Write events
68
Delete events
1
Modification events
| (PID) Process: | (7608) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (7784) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\General |
| Operation: | write | Name: | UniqueID |
Value: {BEAD2573-2029-4C75-8273-78C20E520726} | |||
| (PID) Process: | (7784) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\General |
| Operation: | write | Name: | ComputerName |
Value: DESKTOP-JGLLJLD | |||
| (PID) Process: | (7784) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\General |
| Operation: | write | Name: | VolumeSerialNumber |
Value: 649566714 | |||
| (PID) Process: | (7784) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\MediaPlayer\Player\Settings |
| Operation: | delete value | Name: | Client ID |
Value: {CECDFD5C-8F08-4FEF-8713-FAA895A422EB} | |||
| (PID) Process: | (7784) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\Namespace |
| Operation: | write | Name: | LocalBase |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML | |||
| (PID) Process: | (7784) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\Namespace |
| Operation: | write | Name: | DTDFile |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.DTD | |||
| (PID) Process: | (7784) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\Namespace |
| Operation: | write | Name: | LocalDelta |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNSD.XML | |||
| (PID) Process: | (7784) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\Namespace |
| Operation: | write | Name: | RemoteDelta |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNSR.XML | |||
| (PID) Process: | (7784) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\MediaPlayer\Preferences\ProxySettings\HTTP |
| Operation: | write | Name: | ProxyStyle |
Value: 1 | |||
Executable files
9
Suspicious files
1
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7408 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\dobrota.mp3 | — | |
MD5:— | SHA256:— | |||
| 7732 | mbr.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 7408 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\libgcc_s_dw2-1.dll | executable | |
MD5:E2AC23418781F632311513944EDD0A4C | SHA256:B4CC93CF4D7C2906C1929C079CD98EF00C7A33832E132AC57ADDE71857082E36 | |||
| 7408 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\sound.vbs | text | |
MD5:C36C15E1F99E1C0D093B9B089B1073C5 | SHA256:3D6123CAE8AC645D9C9D33B0DADA869A7FDD5117A2BF0F9080E4E30FE5BED736 | |||
| 7408 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\toonel.exe | executable | |
MD5:A84257E64CFBD9F6C0A574AF416BC0D1 | SHA256:FE7FF85B95EC06CE0F3CB49FDFA4D36DE1F08669D36D381794AAF597510AFAD7 | |||
| 7408 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\libstdc++-6.dll | executable | |
MD5:0C4A3DE21D6551D43D1F8A11D4F09390 | SHA256:D0DE05720C15F6B7105B90EAF005952BEB73161DF5D1B24EECD5BB892E1C6C8E | |||
| 7408 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\INVERS.exe | executable | |
MD5:5134F289DBF4ABAE370E3F36B637B73E | SHA256:E69C9383B5D9FE4E069DDEE15797C52E9116F883AD3B1717D2519621AB2751B2 | |||
| 7408 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\erroriconscursor.exe | executable | |
MD5:135EEB256E92D261066CFD3FFD31FB3E | SHA256:F0FE346146C30129ED6F507906C973F1A54C7D8DD8821C97E9B6EDC42545699D | |||
| 7408 | dobrota.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\messages.vbs | text | |
MD5:35FBF9BF29760B9E120B37900B3C1343 | SHA256:E1CDAB59DF6508013E8B91C71043C8ECFE81B94A037706147ED19ADF992539E6 | |||
| 7784 | wscript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML | text | |
MD5:5433EAB10C6B5C6D55B7CBD302426A39 | SHA256:23DBF7014E99E93AF5F2760F18EE1370274F06A453145C8D539B66D798DAD131 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report