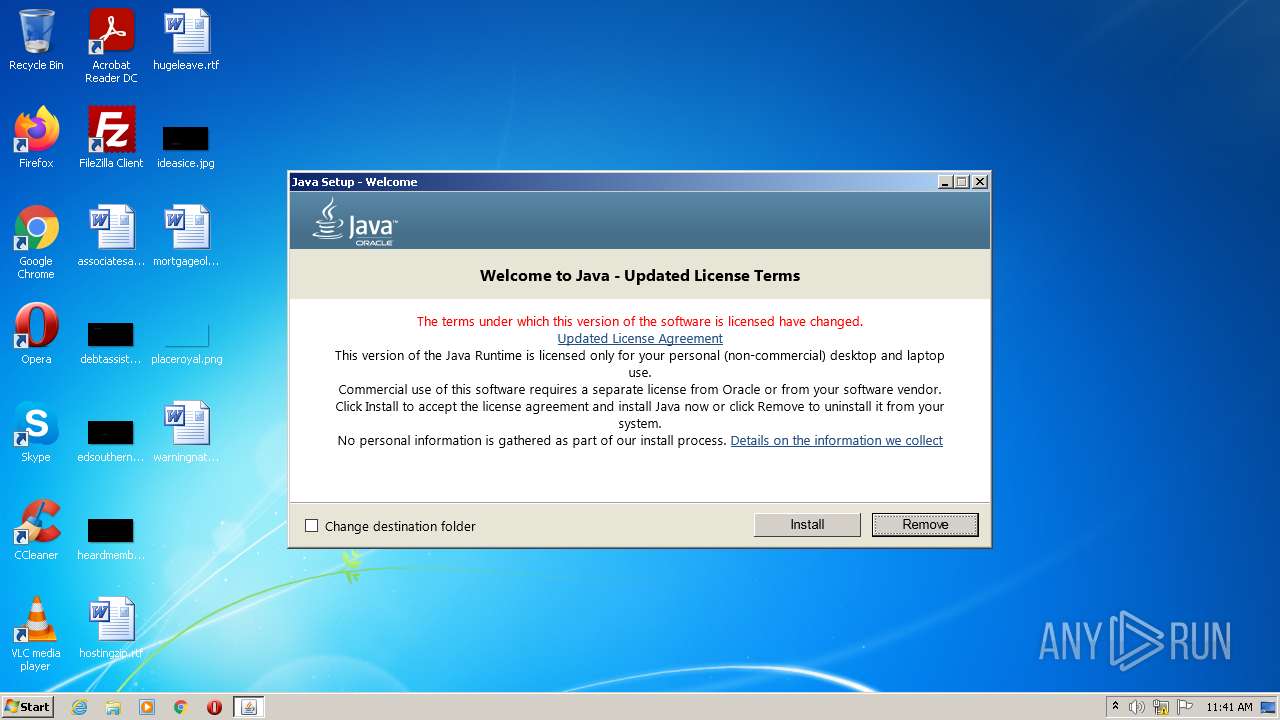
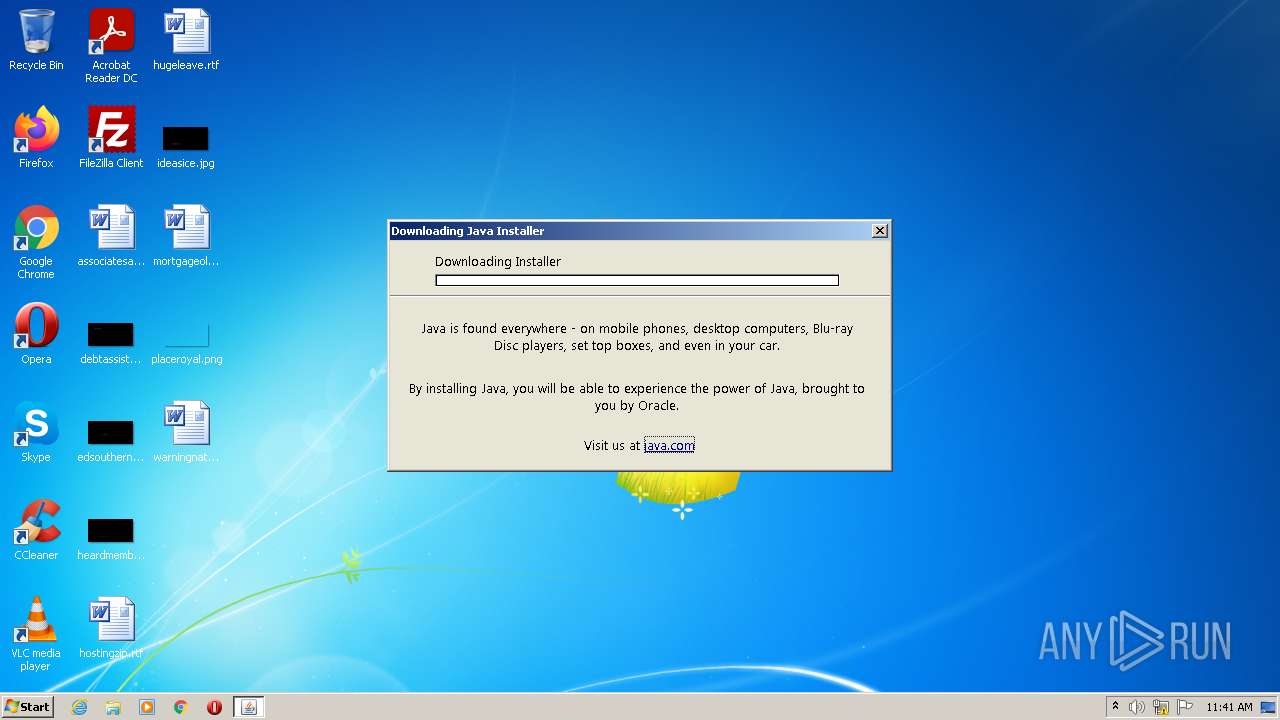
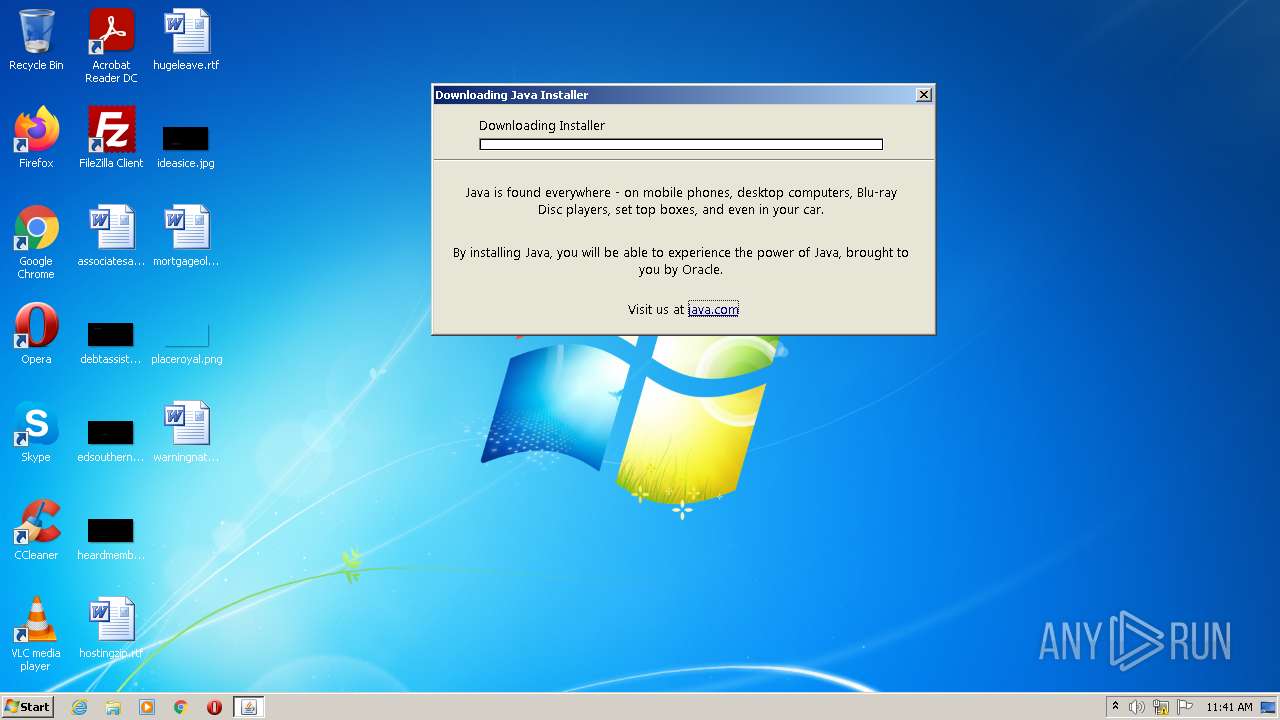
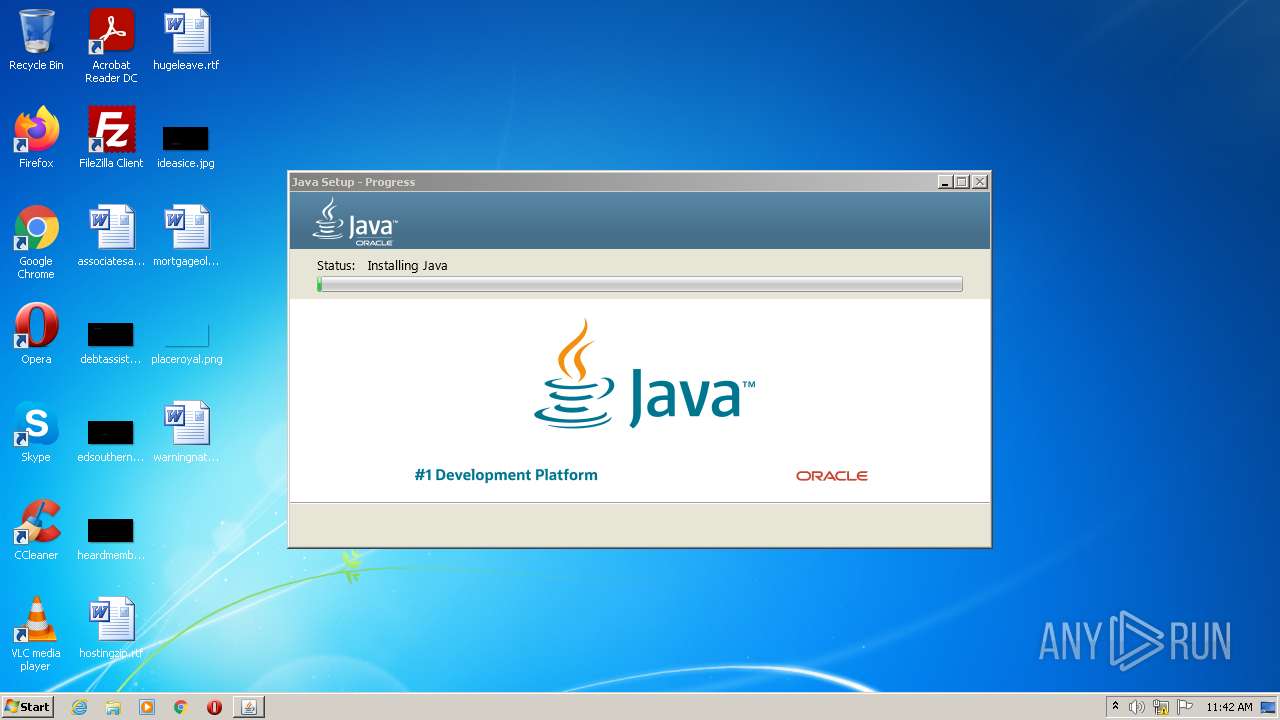
| File name: | JavaSetup8u341.exe |
| Full analysis: | https://app.any.run/tasks/e0878fd8-3f28-4b8a-b2a4-fb718e0876c0 |
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2022, 10:41:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 544EA17DF8D68DCB22927BB9A0EE91E3 |
| SHA1: | 37D3004516057888C578B9F9348A5A7E50CA9B79 |
| SHA256: | 1090139967113CA75AA46466D35CE359666BF8CAC1E01644858A76327D31419F |
| SSDEEP: | 49152:HOt2adErsZmaiTzMzIOTL97O3jUfkptVx0S827TFz+oI:HOt2yAX3TzMzYjUu5k |
MALICIOUS
Application was dropped or rewritten from another process
- JavaSetup8u341.exe (PID: 3004)
- LZMA_EXE (PID: 3176)
- LZMA_EXE (PID: 3384)
- bspatch.exe (PID: 2812)
- unpack200.exe (PID: 3436)
- unpack200.exe (PID: 2932)
- unpack200.exe (PID: 2808)
- unpack200.exe (PID: 3044)
- unpack200.exe (PID: 3220)
- unpack200.exe (PID: 584)
- unpack200.exe (PID: 3904)
- javaw.exe (PID: 2184)
- ssvagent.exe (PID: 3236)
- javaws.exe (PID: 2532)
- jp2launcher.exe (PID: 2696)
- javaws.exe (PID: 3404)
- jp2launcher.exe (PID: 1780)
- jaureg.exe (PID: 3708)
- ssvagent.exe (PID: 1856)
- javaws.exe (PID: 3324)
- javaw.exe (PID: 1208)
- javaw.exe (PID: 1836)
- jp2launcher.exe (PID: 2228)
Drops executable file immediately after starts
- JavaSetup8u341.exe (PID: 316)
- JavaSetup8u341.exe (PID: 3004)
- msiexec.exe (PID: 3752)
- installer.exe (PID: 3516)
- MSI4CD4.tmp (PID: 756)
Changes settings of System certificates
- JavaSetup8u341.exe (PID: 3004)
Loads dropped or rewritten executable
- unpack200.exe (PID: 2932)
- unpack200.exe (PID: 2808)
- unpack200.exe (PID: 584)
- unpack200.exe (PID: 3044)
- unpack200.exe (PID: 3220)
- unpack200.exe (PID: 3436)
- unpack200.exe (PID: 3904)
- javaw.exe (PID: 2184)
- installer.exe (PID: 3516)
- Explorer.EXE (PID: 1080)
- ssvagent.exe (PID: 3236)
- svchost.exe (PID: 872)
- jp2launcher.exe (PID: 2696)
- jp2launcher.exe (PID: 1780)
- ssvagent.exe (PID: 1856)
- jp2launcher.exe (PID: 2228)
- JavaSetup8u341.exe (PID: 3004)
- javaw.exe (PID: 1208)
- javaw.exe (PID: 1836)
SUSPICIOUS
Checks supported languages
- JavaSetup8u341.exe (PID: 316)
- JavaSetup8u341.exe (PID: 3004)
- LZMA_EXE (PID: 3176)
- LZMA_EXE (PID: 3384)
- msiexec.exe (PID: 3752)
- MsiExec.exe (PID: 2632)
- installer.exe (PID: 3516)
- bspatch.exe (PID: 2812)
- unpack200.exe (PID: 2808)
- unpack200.exe (PID: 2932)
- unpack200.exe (PID: 3220)
- unpack200.exe (PID: 584)
- unpack200.exe (PID: 3044)
- unpack200.exe (PID: 3904)
- unpack200.exe (PID: 3436)
- javaw.exe (PID: 2184)
- javaws.exe (PID: 2532)
- jp2launcher.exe (PID: 2696)
- ssvagent.exe (PID: 3236)
- javaws.exe (PID: 3404)
- jp2launcher.exe (PID: 1780)
- MsiExec.exe (PID: 3904)
- MsiExec.exe (PID: 1212)
- MsiExec.exe (PID: 3536)
- MsiExec.exe (PID: 3464)
- MsiExec.exe (PID: 1820)
- MSI4CD4.tmp (PID: 756)
- javaws.exe (PID: 3324)
- jp2launcher.exe (PID: 2228)
- jaureg.exe (PID: 3708)
- MsiExec.exe (PID: 2336)
- ssvagent.exe (PID: 1856)
- javaw.exe (PID: 1208)
- javaw.exe (PID: 1836)
Reads the computer name
- JavaSetup8u341.exe (PID: 3004)
- JavaSetup8u341.exe (PID: 316)
- msiexec.exe (PID: 3752)
- MsiExec.exe (PID: 2632)
- installer.exe (PID: 3516)
- javaws.exe (PID: 2532)
- jp2launcher.exe (PID: 2696)
- javaws.exe (PID: 3404)
- jp2launcher.exe (PID: 1780)
- MsiExec.exe (PID: 3904)
- MsiExec.exe (PID: 1212)
- MsiExec.exe (PID: 3536)
- MsiExec.exe (PID: 3464)
- MsiExec.exe (PID: 1820)
- MSI4CD4.tmp (PID: 756)
- jp2launcher.exe (PID: 2228)
- javaws.exe (PID: 3324)
- MsiExec.exe (PID: 2336)
- javaw.exe (PID: 1208)
- javaw.exe (PID: 1836)
Drops a file with a compile date too recent
- JavaSetup8u341.exe (PID: 316)
- JavaSetup8u341.exe (PID: 3004)
- msiexec.exe (PID: 3752)
- installer.exe (PID: 3516)
- MSI4CD4.tmp (PID: 756)
Reads Microsoft Outlook installation path
- JavaSetup8u341.exe (PID: 3004)
Executable content was dropped or overwritten
- JavaSetup8u341.exe (PID: 316)
- LZMA_EXE (PID: 3176)
- JavaSetup8u341.exe (PID: 3004)
- msiexec.exe (PID: 3752)
- installer.exe (PID: 3516)
- MSI4CD4.tmp (PID: 756)
Starts application with an unusual extension
- JavaSetup8u341.exe (PID: 3004)
Reads internet explorer settings
- JavaSetup8u341.exe (PID: 3004)
Adds / modifies Windows certificates
- JavaSetup8u341.exe (PID: 3004)
Reads the Windows organization settings
- msiexec.exe (PID: 3752)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3752)
Reads CPU info
- msiexec.exe (PID: 3752)
Creates a directory in Program Files
- msiexec.exe (PID: 3752)
- installer.exe (PID: 3516)
- MSI4CD4.tmp (PID: 756)
Creates files in the program directory
- unpack200.exe (PID: 3044)
- unpack200.exe (PID: 2932)
- bspatch.exe (PID: 2812)
- unpack200.exe (PID: 2808)
- unpack200.exe (PID: 3220)
- unpack200.exe (PID: 584)
- installer.exe (PID: 3516)
- unpack200.exe (PID: 3436)
- unpack200.exe (PID: 3904)
- javaw.exe (PID: 2184)
- MSI4CD4.tmp (PID: 756)
Check for Java to be installed
- installer.exe (PID: 3516)
- jp2launcher.exe (PID: 2696)
- ssvagent.exe (PID: 3236)
- jp2launcher.exe (PID: 1780)
- JavaSetup8u341.exe (PID: 3004)
- msiexec.exe (PID: 3752)
- MSI4CD4.tmp (PID: 756)
- ssvagent.exe (PID: 1856)
- jp2launcher.exe (PID: 2228)
- javaw.exe (PID: 1208)
Changes default file association
- installer.exe (PID: 3516)
- MSI4CD4.tmp (PID: 756)
Changes the autorun value in the registry
- msiexec.exe (PID: 3752)
Creates/Modifies COM task schedule object
- ssvagent.exe (PID: 1856)
- ssvagent.exe (PID: 3236)
- installer.exe (PID: 3516)
- MSI4CD4.tmp (PID: 756)
INFO
Reads settings of System Certificates
- JavaSetup8u341.exe (PID: 3004)
- msiexec.exe (PID: 3752)
Checks Windows Trust Settings
- JavaSetup8u341.exe (PID: 3004)
- msiexec.exe (PID: 3752)
Application launched itself
- msiexec.exe (PID: 3752)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2632)
- MsiExec.exe (PID: 3904)
- MSI4CD4.tmp (PID: 756)
Creates files in the program directory
- msiexec.exe (PID: 3752)
Creates a software uninstall entry
- msiexec.exe (PID: 3752)
Searches for installed software
- msiexec.exe (PID: 3752)
Starts application with an unusual extension
- msiexec.exe (PID: 3752)
Application was dropped or rewritten from another process
- MSI4CD4.tmp (PID: 756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| ProductVersion: | 8.0.3410.10 |
|---|---|
| ProductName: | Java Platform SE 8 U341 |
| OriginalFileName: | online_wrapper-cab.exe |
| LegalCopyright: | Copyright © 2022 |
| InternalName: | Setup Launcher |
| FullVersion: | 1.8.0_341-b10 |
| FileVersion: | 8.0.3410.10 |
| FileDescription: | Java Platform SE binary |
| CompanyName: | Oracle Corporation |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 8.0.3410.10 |
| FileVersionNumber: | 8.0.3410.10 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0xf565 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2071552 |
| CodeSize: | 182784 |
| LinkerVersion: | 14.16 |
| PEType: | PE32 |
| TimeStamp: | 2022:06:16 19:04:12+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jun-2022 17:04:12 |
| Detected languages: |
|
| CompanyName: | Oracle Corporation |
| FileDescription: | Java Platform SE binary |
| FileVersion: | 8.0.3410.10 |
| Full Version: | 1.8.0_341-b10 |
| InternalName: | Setup Launcher |
| LegalCopyright: | Copyright © 2022 |
| OriginalFilename: | online_wrapper-cab.exe |
| ProductName: | Java Platform SE 8 U341 |
| ProductVersion: | 8.0.3410.10 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Jun-2022 17:04:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002C8C0 | 0x0002CA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66376 |
.rdata | 0x0002E000 | 0x00012580 | 0x00012600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.47242 |
.data | 0x00041000 | 0x000020D8 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.60759 |
.rsrc | 0x00044000 | 0x001E2410 | 0x001E2600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.84554 |
.reloc | 0x00227000 | 0x00002DAC | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56698 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.8258 | 382 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.96826 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 2.90069 | 488 | UNKNOWN | English - United States | RT_ICON |
4 | 3.0155 | 296 | UNKNOWN | English - United States | RT_ICON |
5 | 5.58618 | 3752 | UNKNOWN | English - United States | RT_ICON |
6 | 5.53853 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.94465 | 1736 | UNKNOWN | English - United States | RT_ICON |
8 | 2.81361 | 1384 | UNKNOWN | English - United States | RT_ICON |
9 | 5.4261 | 9640 | UNKNOWN | English - United States | RT_ICON |
10 | 5.68846 | 4264 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
Total processes
85
Monitored processes
37
Malicious processes
25
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Users\admin\AppData\Local\Temp\JavaSetup8u341.exe" | C:\Users\admin\AppData\Local\Temp\JavaSetup8u341.exe | Explorer.EXE | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 0 Version: 8.0.3410.10 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Java\jre1.8.0_341\bin\unpack200.exe" -r "C:\Program Files\Java\jre1.8.0_341\lib/jsse.pack" "C:\Program Files\Java\jre1.8.0_341\lib/jsse.jar" | C:\Program Files\Java\jre1.8.0_341\bin\unpack200.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.3410.10 Modules
| |||||||||||||||
| 756 | "C:\Windows\Installer\MSI4CD4.tmp" INSTALLDIR="C:\Program Files\Java\jre1.8.0_271\\" ProductCode={26A24AE4-039D-4CA4-87B4-2F32180271F0} /s BASEIMAGECHECKSUMSHA256= | C:\Windows\Installer\MSI4CD4.tmp | msiexec.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 872 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1080 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | SearchFilterHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1208 | -Djdk.disableLastUsageTracking -cp "C:\Program Files\Java\jre1.8.0_341\bin\..\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -getUserWebJavaStatus | C:\Program Files\Java\jre1.8.0_341\bin\javaw.exe | — | JavaSetup8u341.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.3410.10 Modules
| |||||||||||||||
| 1212 | C:\Windows\system32\MsiExec.exe -Embedding A0C027A11BB7C2A7D0CFB6BA1463528C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Java\jre1.8.0_341\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_341" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMzQxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMzQxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzM0MVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURzdW4uYXd0Lndhcm11cD10cnVlAC1YYm9vdGNsYXNzcGF0aC9hOkM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF8zNDFcbGliXGphdmF3cy5qYXI7QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzM0MVxsaWJcZGVwbG95LmphcjtDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMzQxXGxpYlxwbHVnaW4uamFyAC1EamF2YS5hd3QuaGVhZGxlc3M9dHJ1ZQAtRGpubHB4Lmp2bT1DOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMzQxXGJpblxqYXZhdy5leGU= -ma LXdhaXQALWZpeAAtc2hvcnRjdXQALXNpbGVudAAtbm90V2ViSmF2YQ== | C:\Program Files\Java\jre1.8.0_341\bin\jp2launcher.exe | — | javaws.exe | |||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.341.2.10 Modules
| |||||||||||||||
| 1820 | C:\Windows\system32\MsiExec.exe -Embedding E31FFA5B2427D00F7D31AA2DA72BE957 E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1836 | -Djdk.disableLastUsageTracking -cp "C:\Program Files\Java\jre1.8.0_341\bin\..\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -getUserPreviousDecisionsExist 30 | C:\Program Files\Java\jre1.8.0_341\bin\javaw.exe | — | JavaSetup8u341.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.3410.10 Modules
| |||||||||||||||
Total events
163 275
Read events
24 199
Write events
84 455
Delete events
54 621
Modification events
| (PID) Process: | (3004) JavaSetup8u341.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3004) JavaSetup8u341.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3004) JavaSetup8u341.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3004) JavaSetup8u341.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3004) JavaSetup8u341.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3004) JavaSetup8u341.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3004) JavaSetup8u341.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3004) JavaSetup8u341.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3004) JavaSetup8u341.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3004) JavaSetup8u341.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
327
Suspicious files
51
Text files
214
Unknown types
52
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3004 | JavaSetup8u341.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_341\jds1078078.tmp | — | |
MD5:— | SHA256:— | |||
| 3004 | JavaSetup8u341.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_341\jre1.8.0_341full.msi | — | |
MD5:— | SHA256:— | |||
| 3384 | LZMA_EXE | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_341\msi.tmp | — | |
MD5:— | SHA256:— | |||
| 3752 | msiexec.exe | C:\Windows\Installer\119279.msi | — | |
MD5:— | SHA256:— | |||
| 3752 | msiexec.exe | C:\Program Files\Java\jre1.8.0_341\installer.exe | — | |
MD5:— | SHA256:— | |||
| 3752 | msiexec.exe | C:\Windows\Installer\11927d.msi | — | |
MD5:— | SHA256:— | |||
| 3516 | installer.exe | C:\ProgramData\Oracle\Java\installcache\1155812.tmp\diff | — | |
MD5:— | SHA256:— | |||
| 3752 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFC8890DAAE55AFBAA.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3516 | installer.exe | C:\ProgramData\Oracle\Java\installcache\1155812.tmp\baseimagefam8 | — | |
MD5:— | SHA256:— | |||
| 3516 | installer.exe | C:\ProgramData\Oracle\Java\installcache\baseimagefam8 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
15
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3004 | JavaSetup8u341.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3004 | JavaSetup8u341.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
3004 | JavaSetup8u341.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3004 | JavaSetup8u341.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAwpAY7lUOZZolQKk7Nh4vo%3D | US | der | 471 b | whitelisted |
3004 | JavaSetup8u341.exe | GET | 200 | 8.241.9.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?053cfc456071b46b | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3004 | JavaSetup8u341.exe | 96.16.157.168:443 | javadl-esd-secure.oracle.com | Akamai Technologies, Inc. | US | suspicious |
3004 | JavaSetup8u341.exe | 8.241.9.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3004 | JavaSetup8u341.exe | 23.35.228.85:443 | sdlc-esd.oracle.com | Zayo Bandwidth Inc | US | malicious |
3004 | JavaSetup8u341.exe | 96.16.130.135:443 | www.java.com | Akamai International B.V. | US | suspicious |
3004 | JavaSetup8u341.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3004 | JavaSetup8u341.exe | 13.36.218.177:443 | sjremetrics.java.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
javadl-esd-secure.oracle.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
javadl.oracle.com |
| whitelisted |
sdlc-esd.oracle.com |
| whitelisted |
rps-svcs.oracle.com |
| suspicious |
www.java.com |
| whitelisted |
sjremetrics.java.com |
| whitelisted |