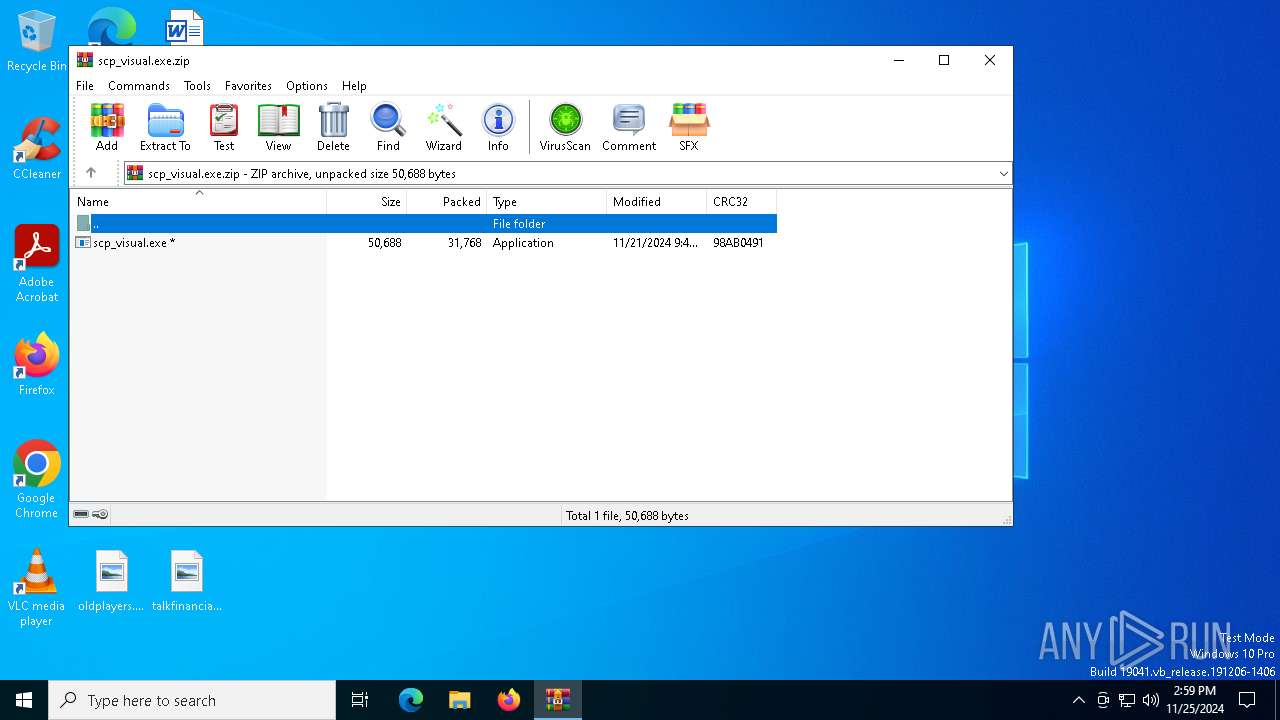
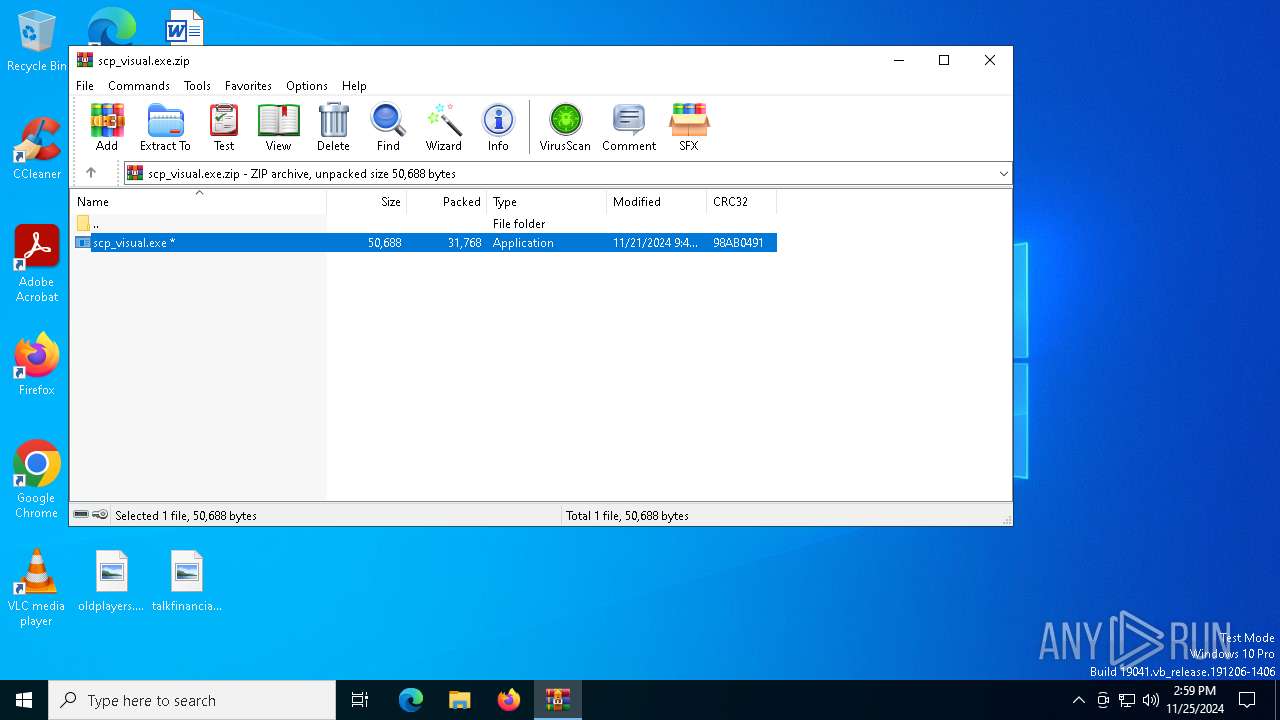
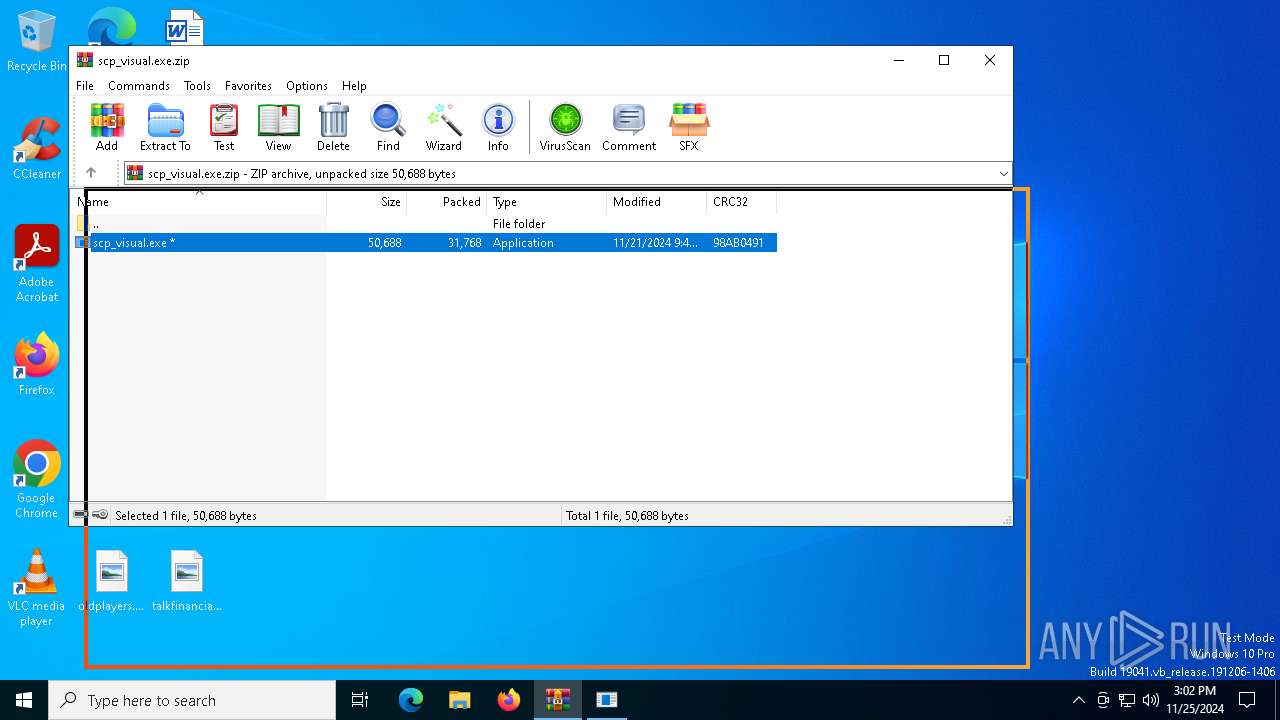
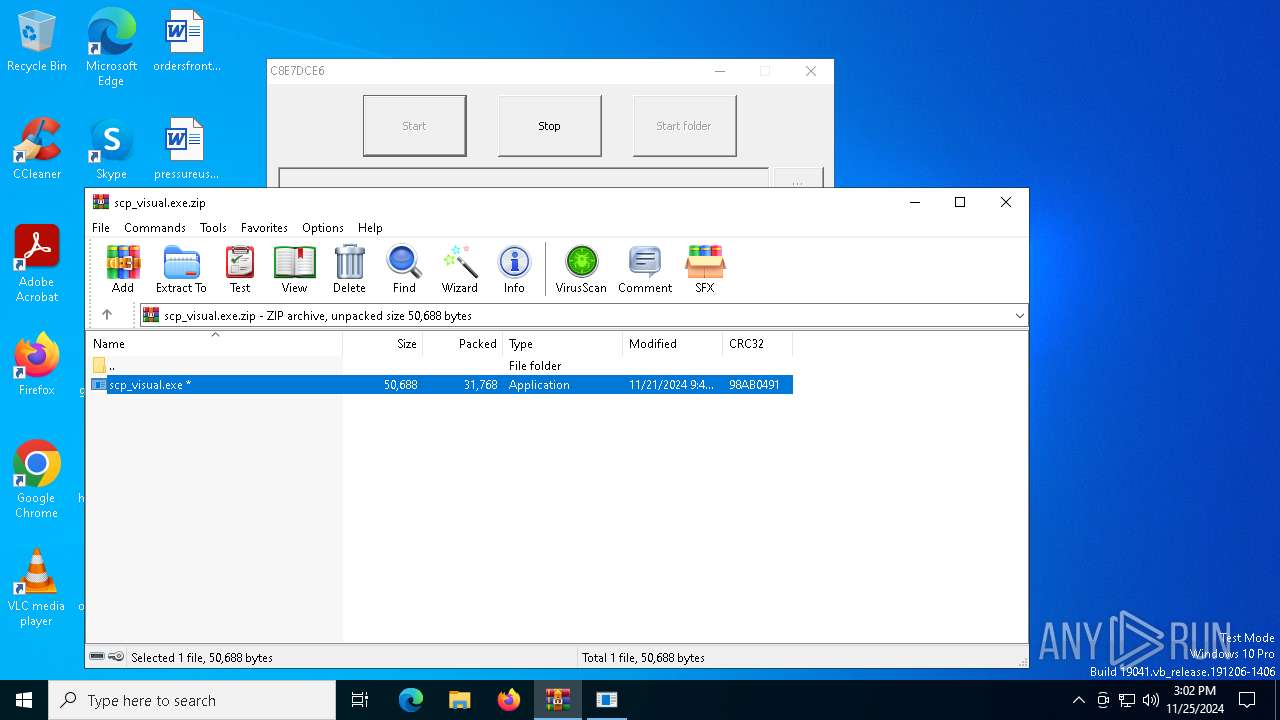
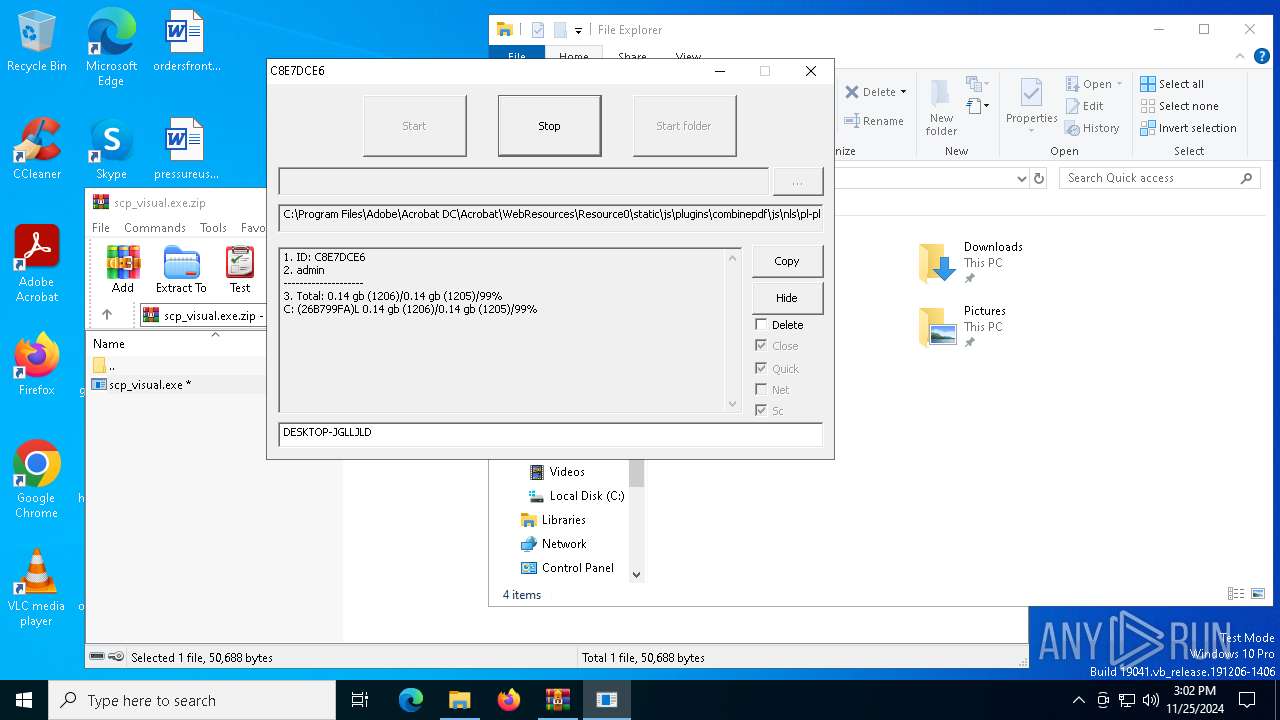
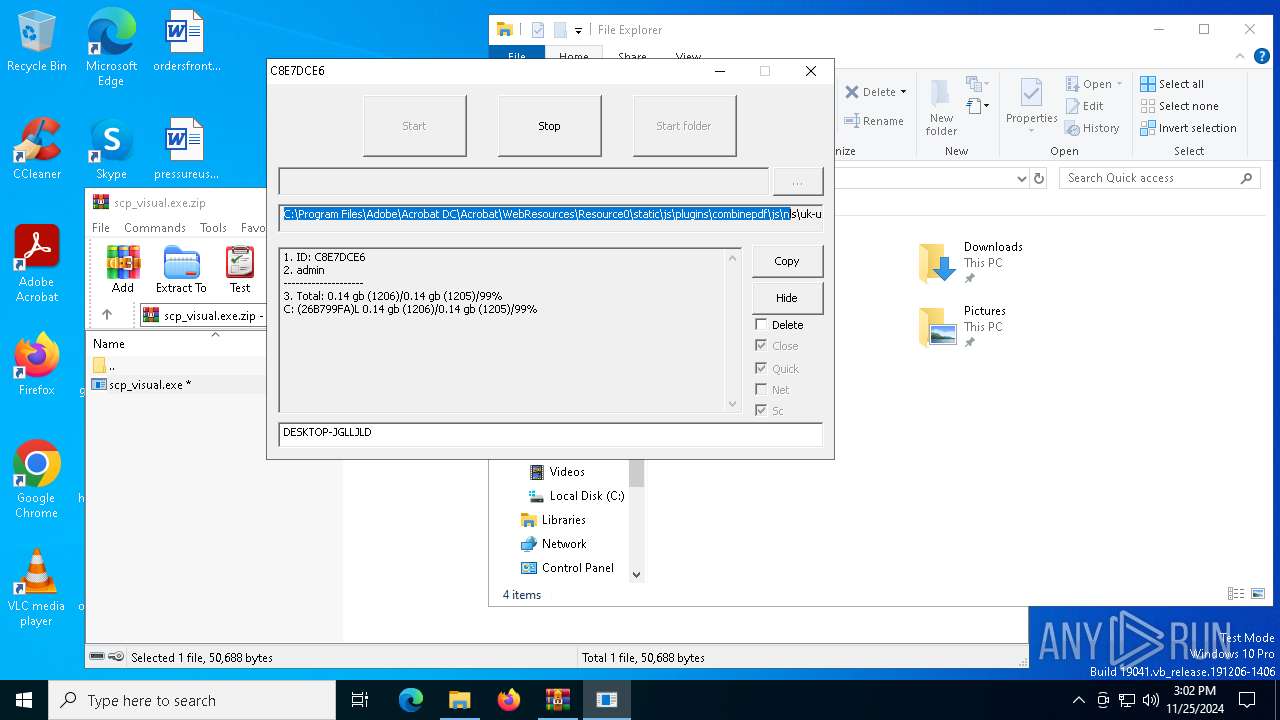
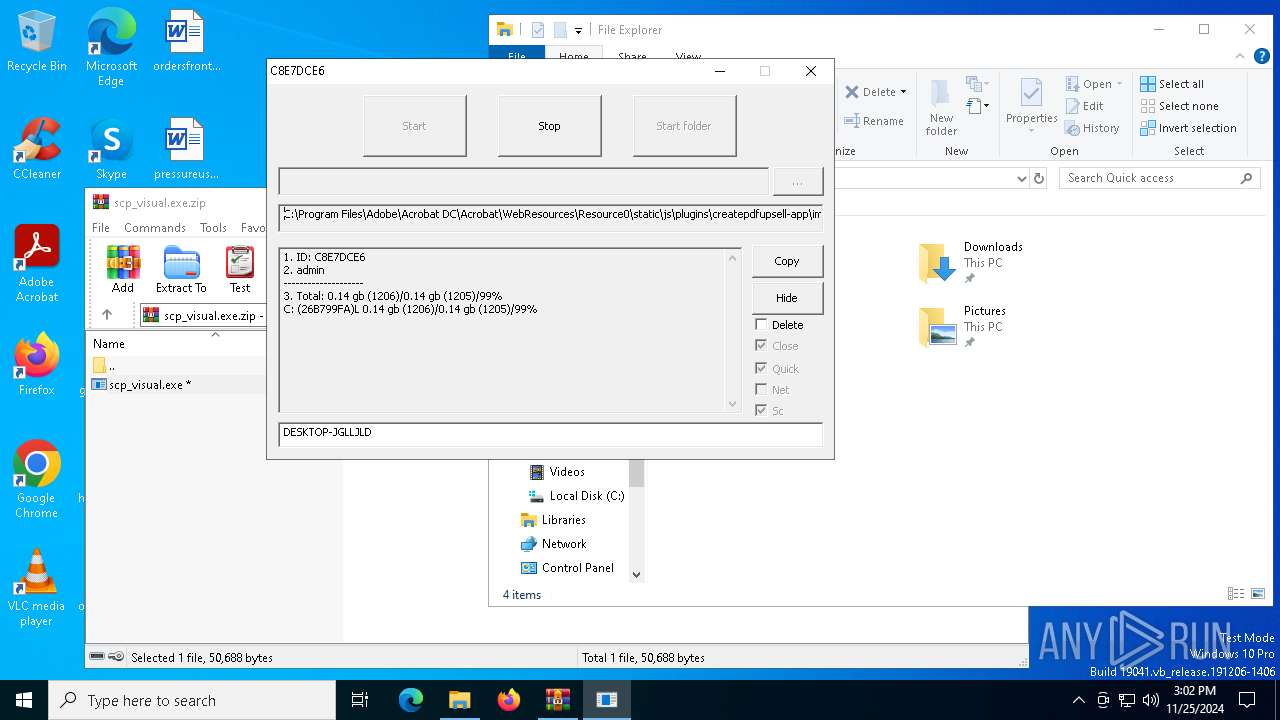
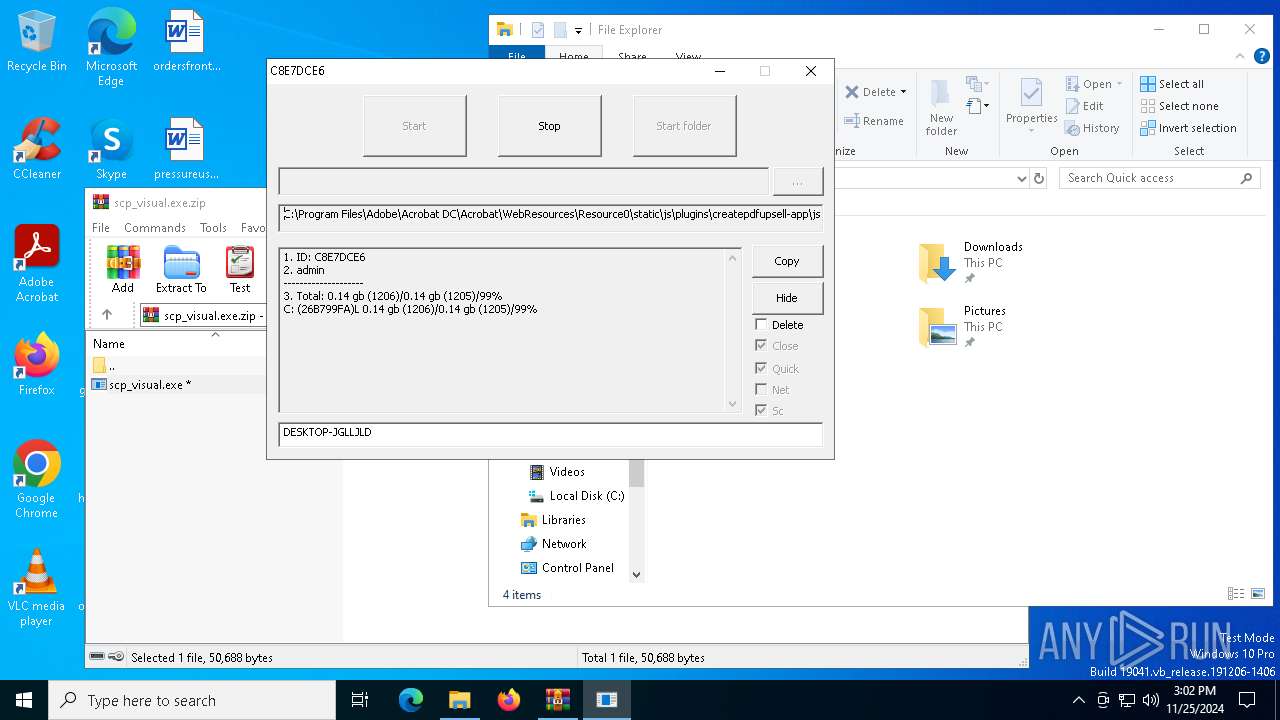
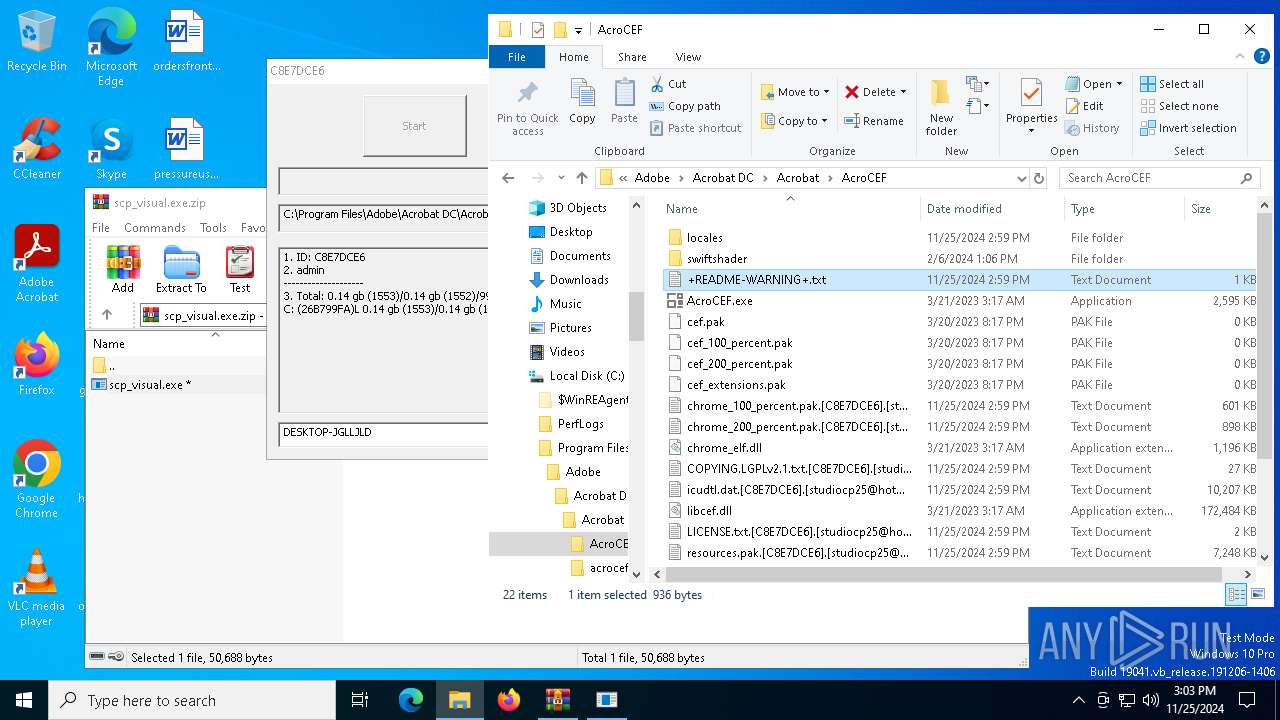
| File name: | scp_visual.exe.zip |
| Full analysis: | https://app.any.run/tasks/bc259250-5a11-4c35-917b-d8ede8d69fee |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2024, 14:59:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 6CCFC286DCF77A37A9B2AE41036A8CE6 |
| SHA1: | 381DD90D2D1C1DFE6C55DB559839DC17FA3F5C81 |
| SHA256: | 108BAAC62A51AC89C781568BB728385949812F0D7F9B3C8E5FE570A45FA71313 |
| SSDEEP: | 768:3+NbgPurrzjEy6V8mkNevM+gVOcmoZvKSzAybdH9om0Cieqln:BPcoDkn+5oZvKSzH9omvjg |
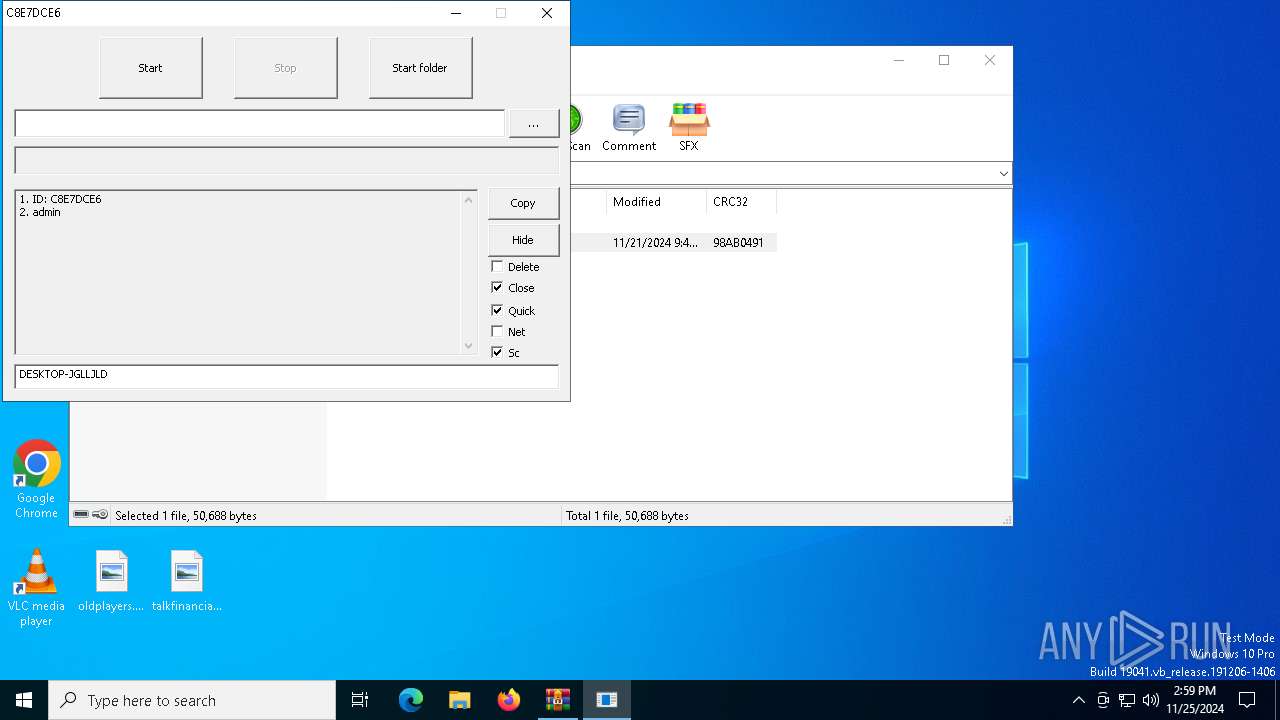
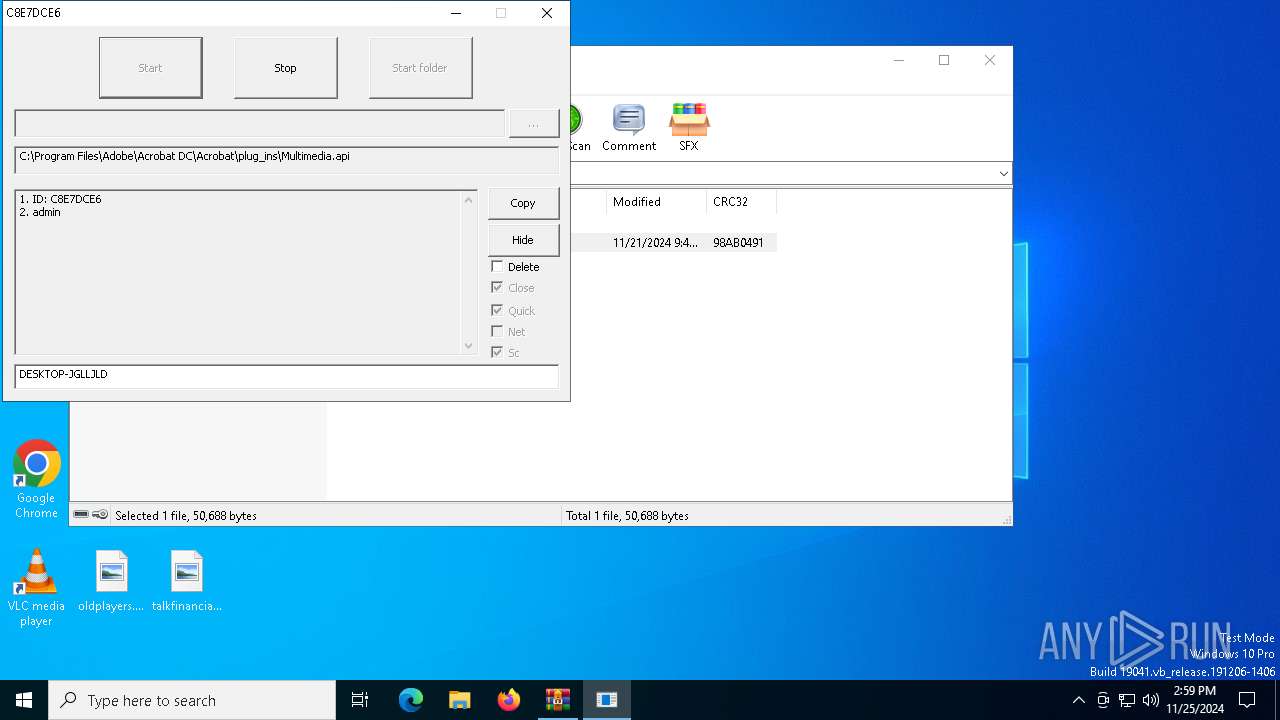
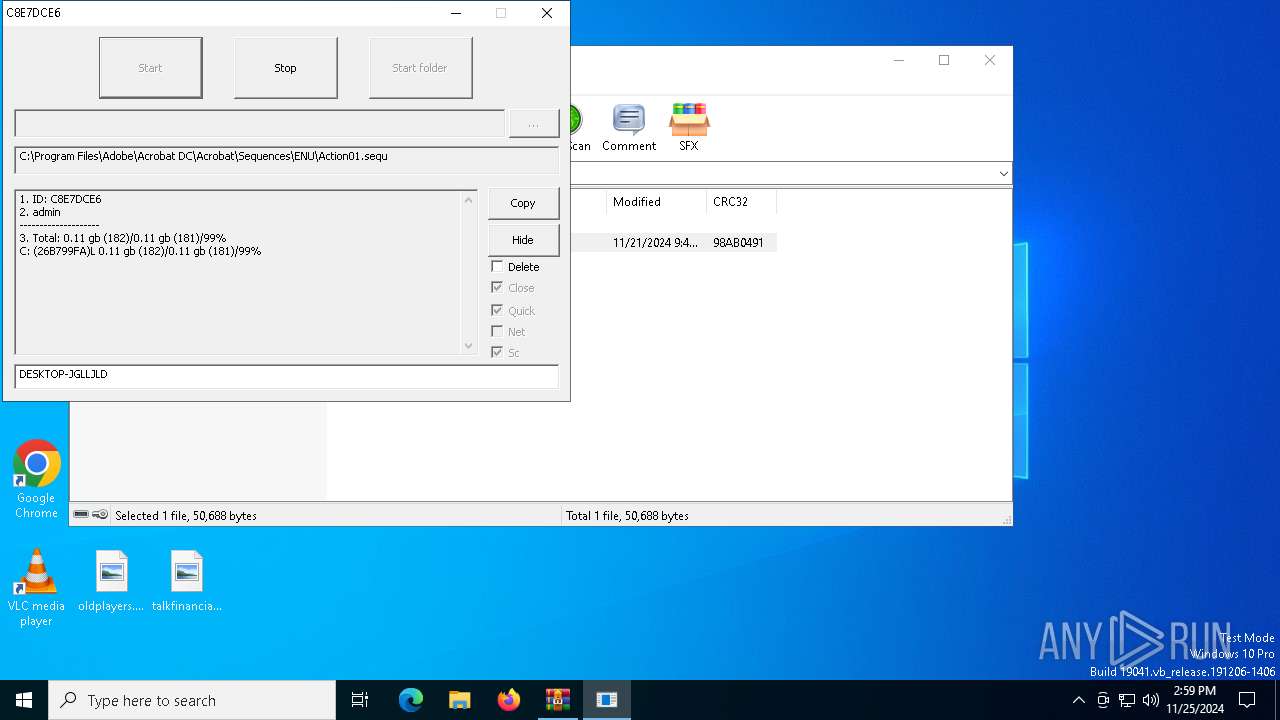
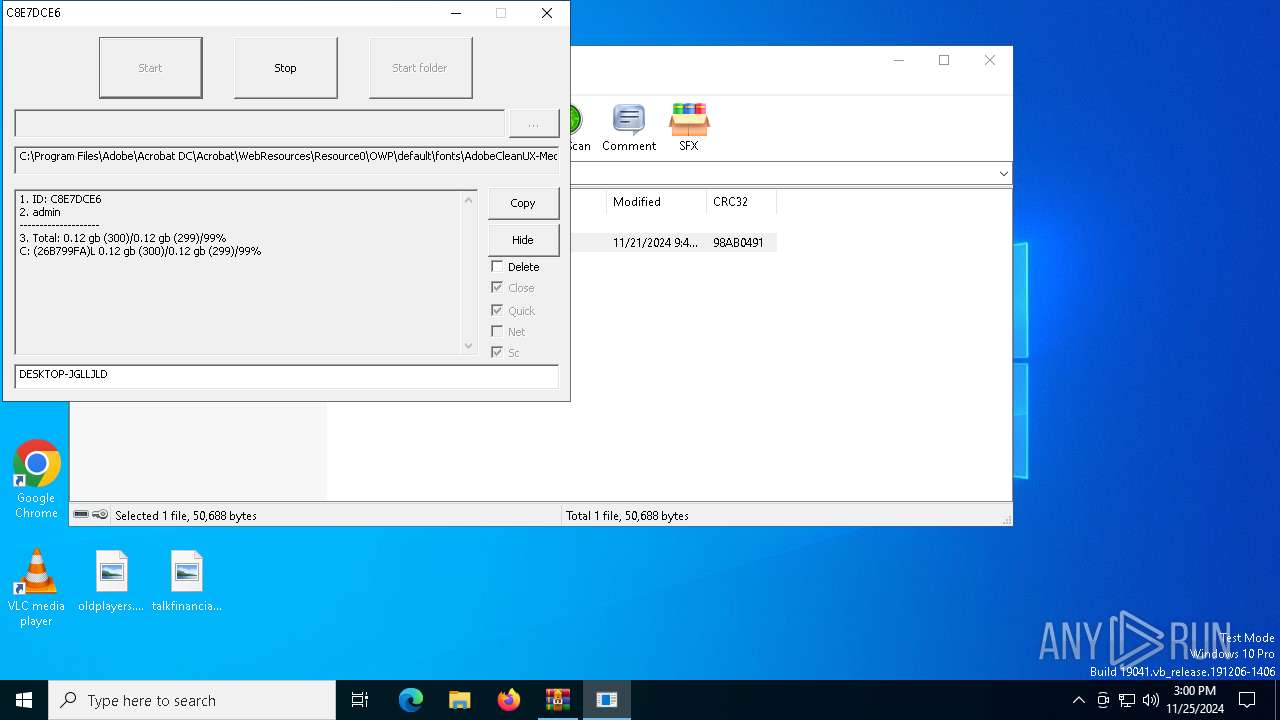
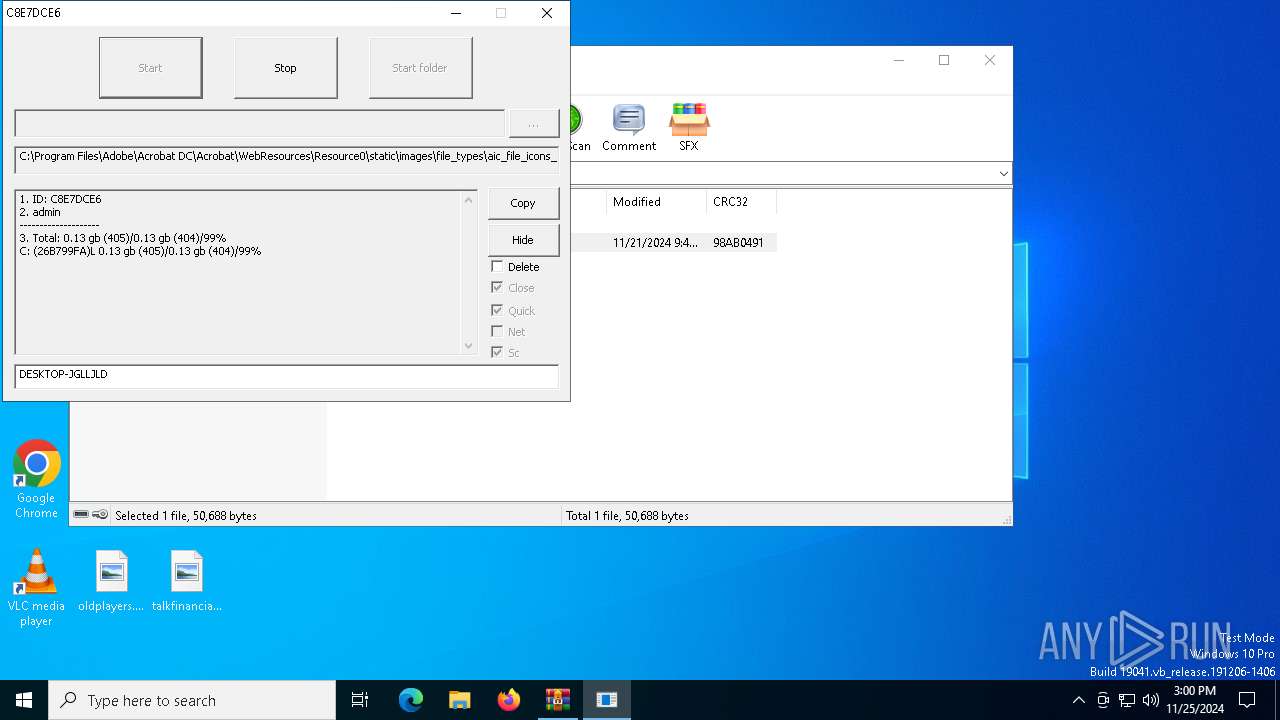
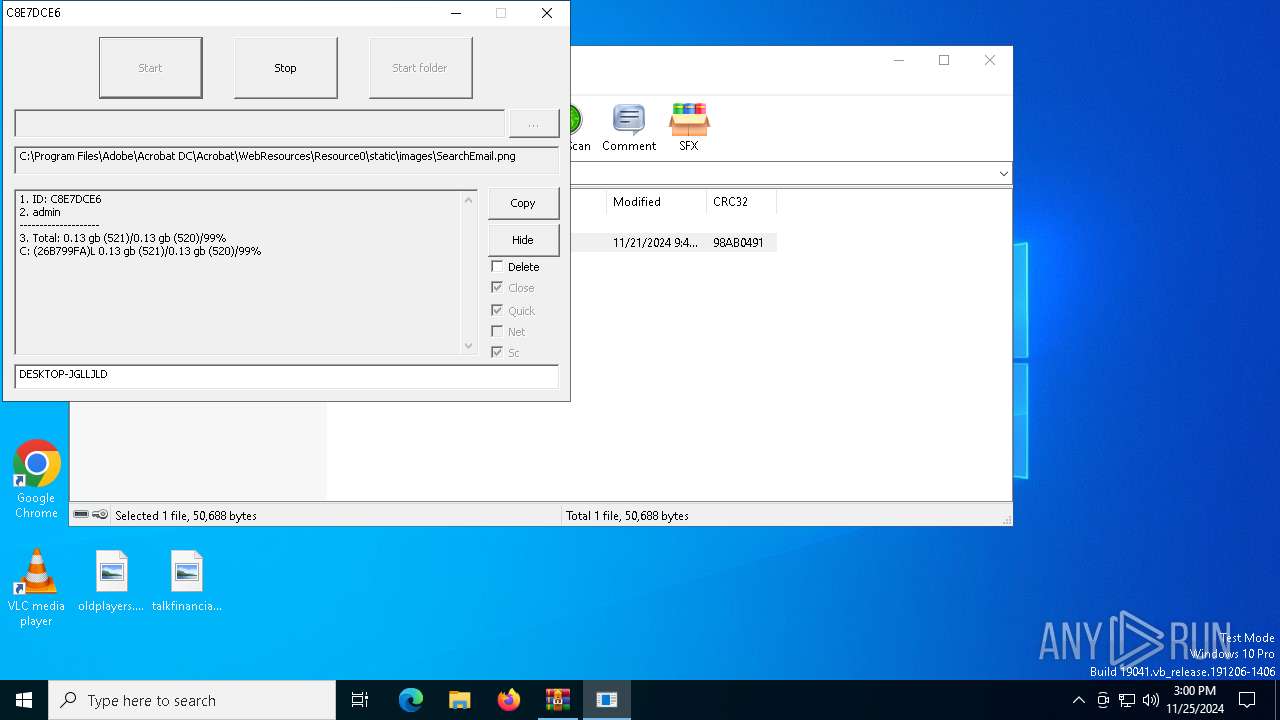
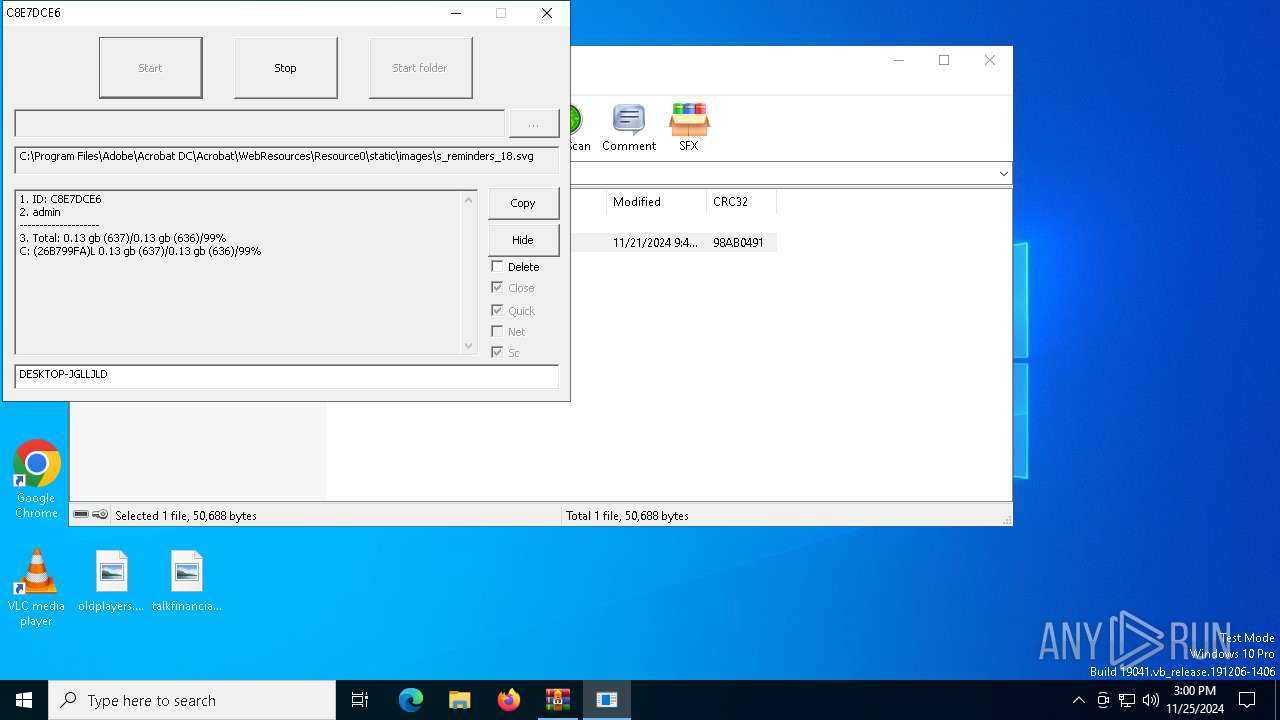
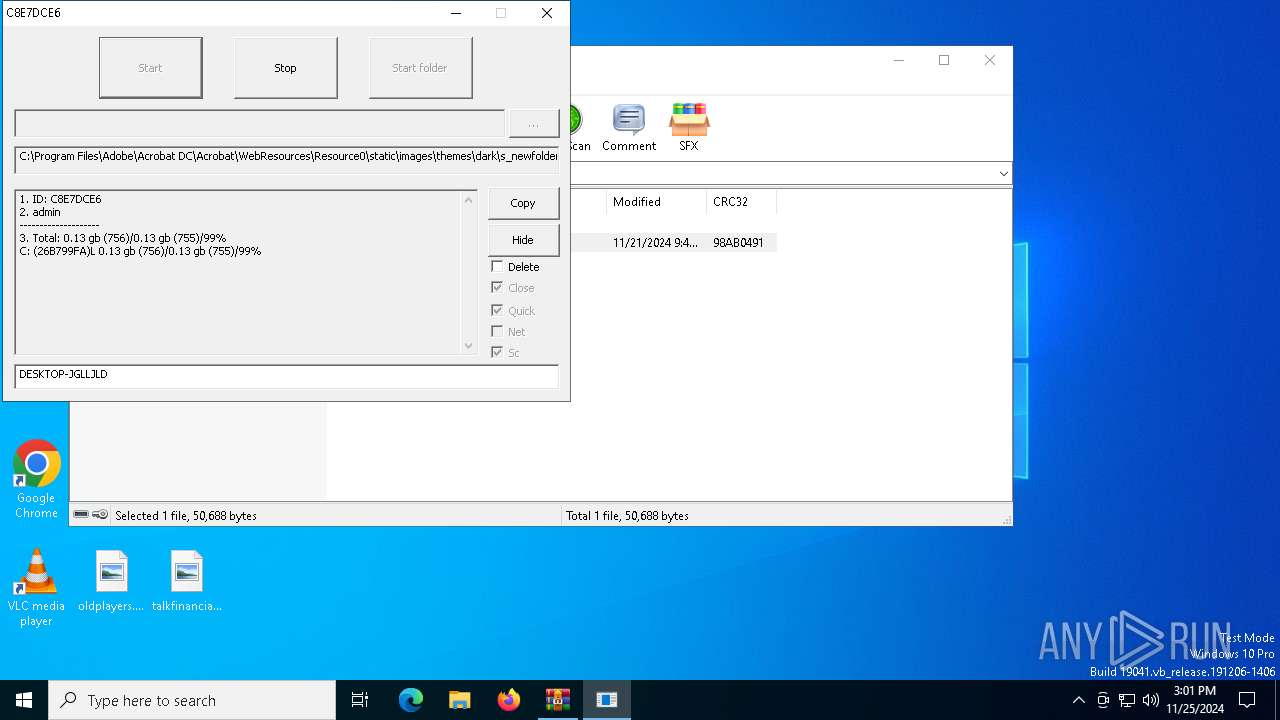
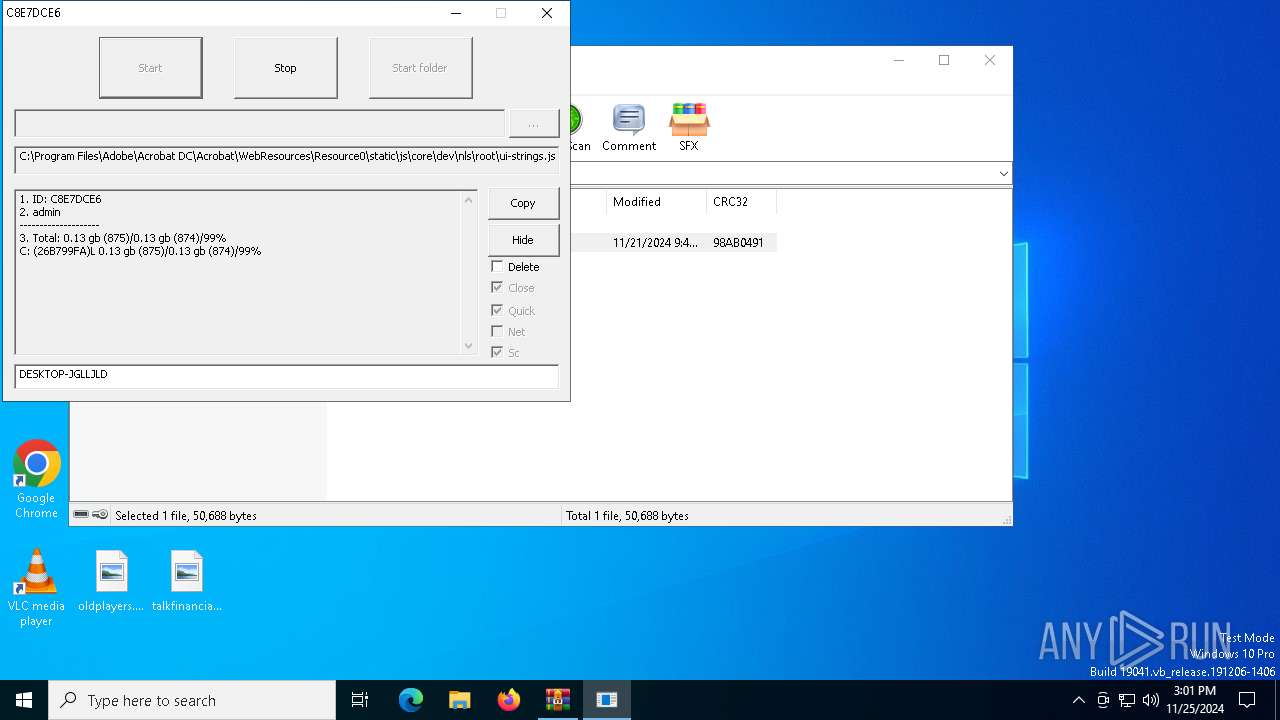
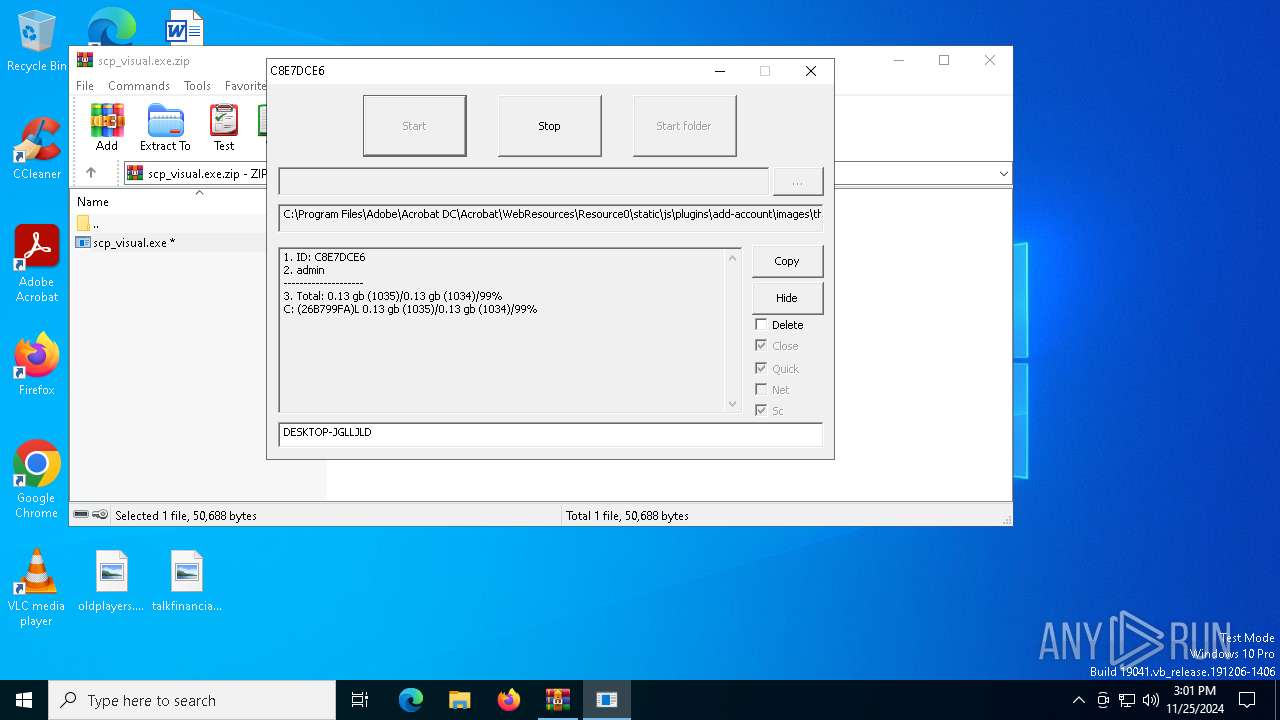
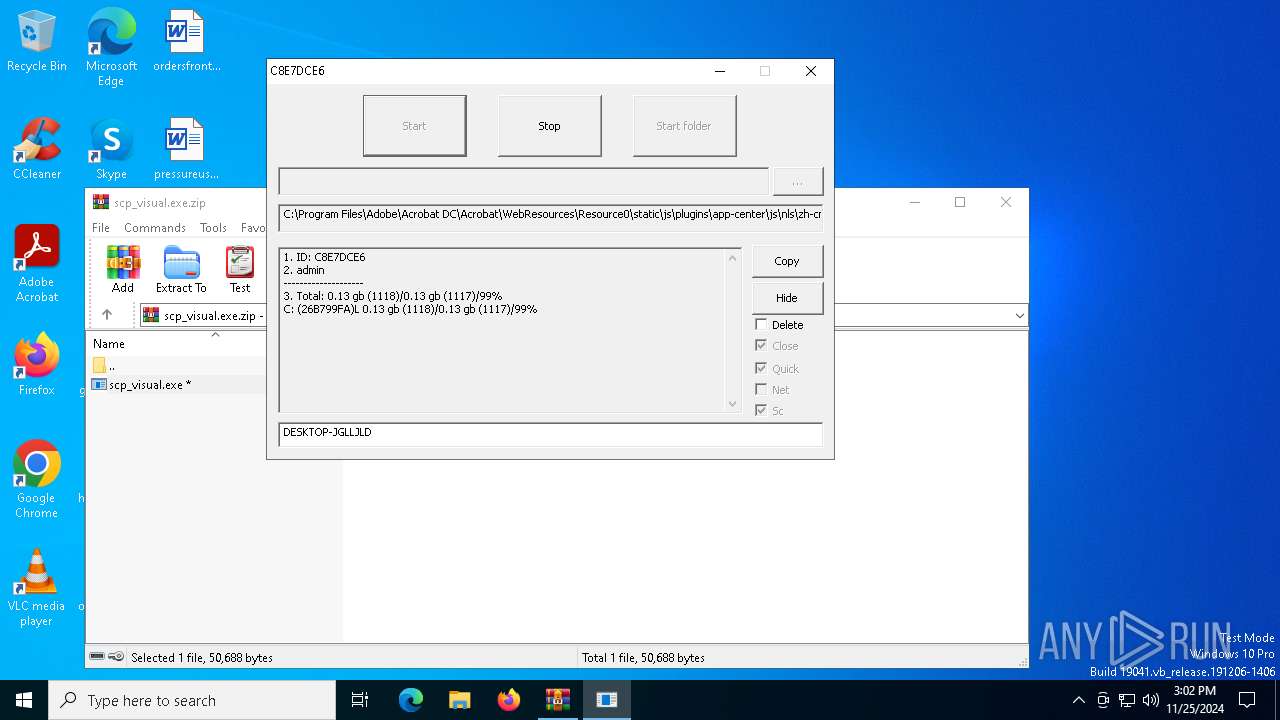
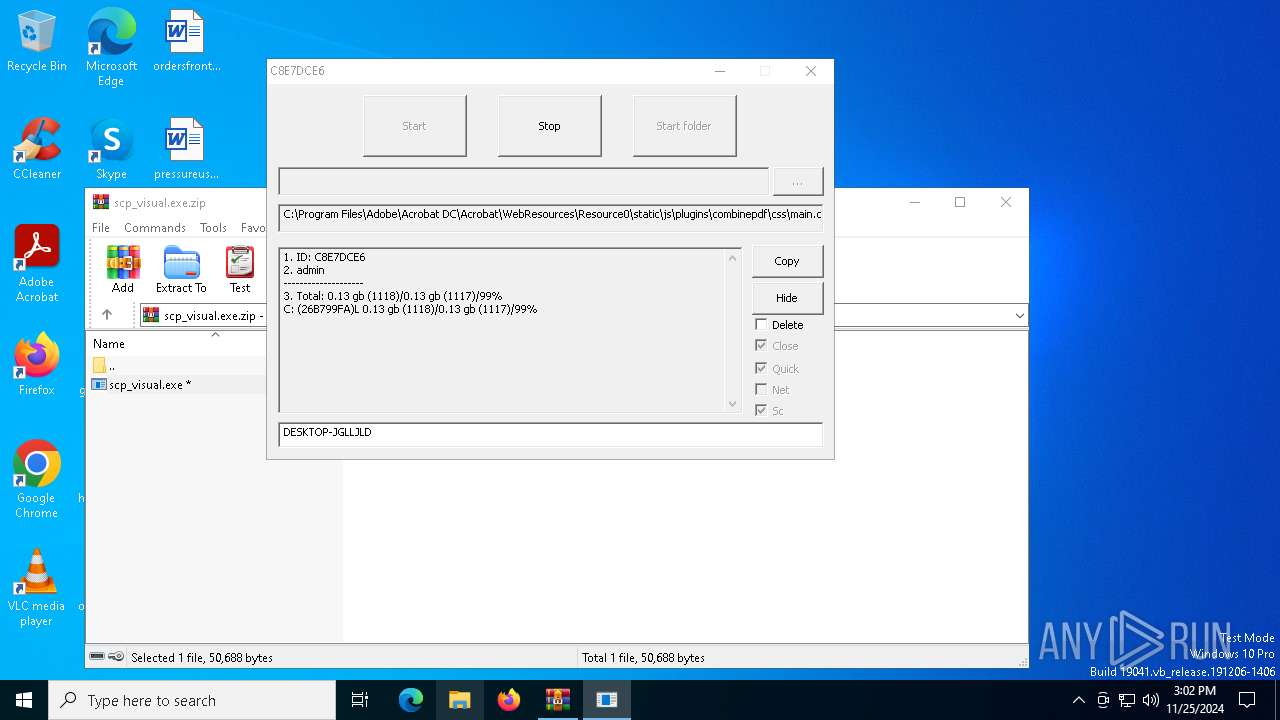
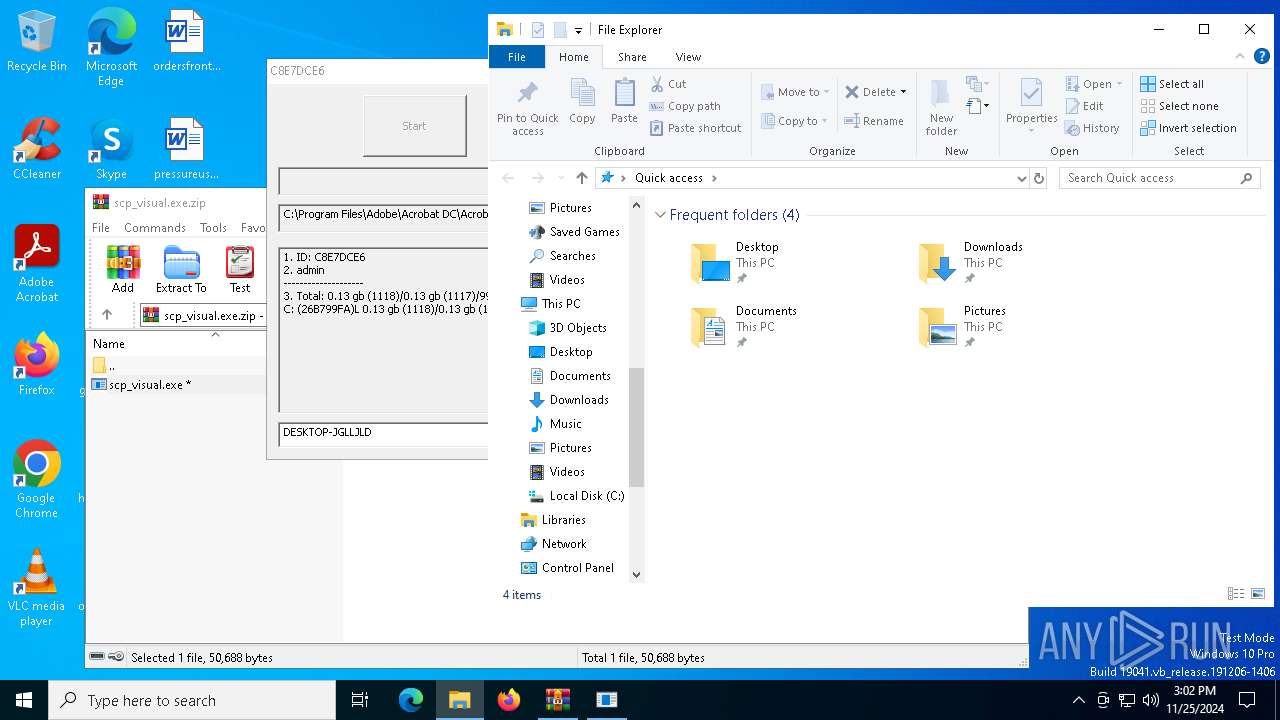
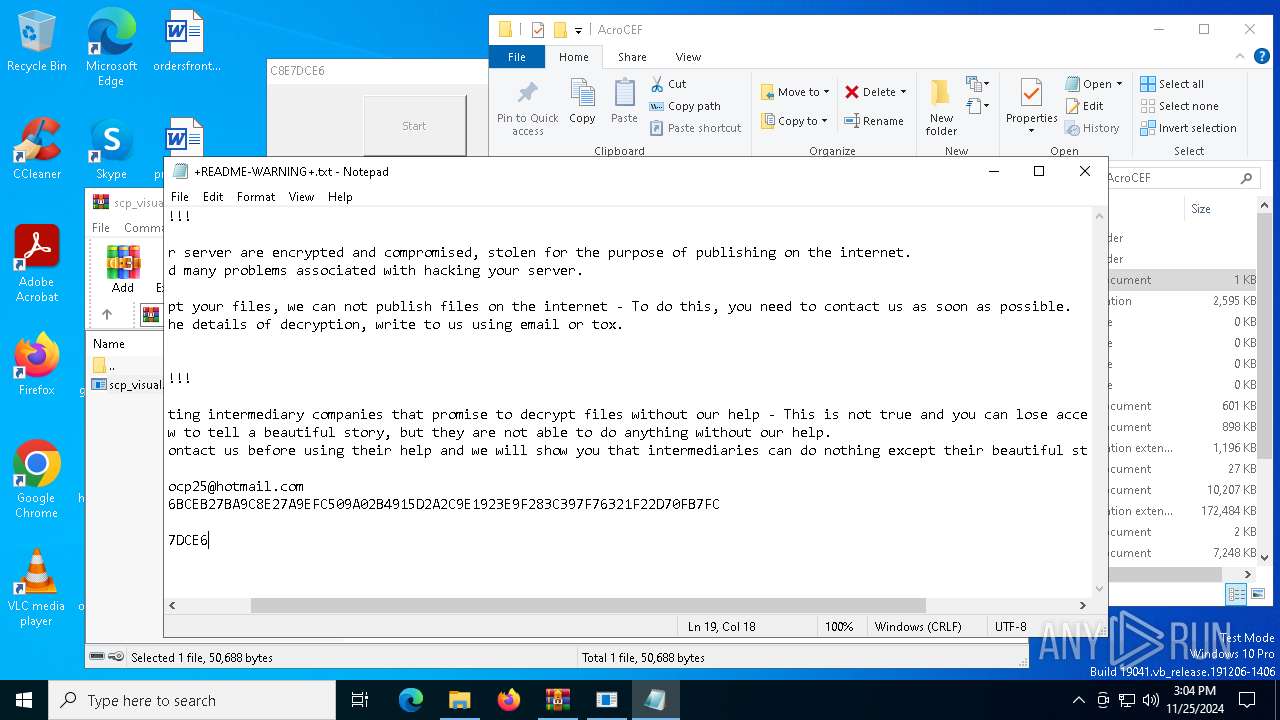
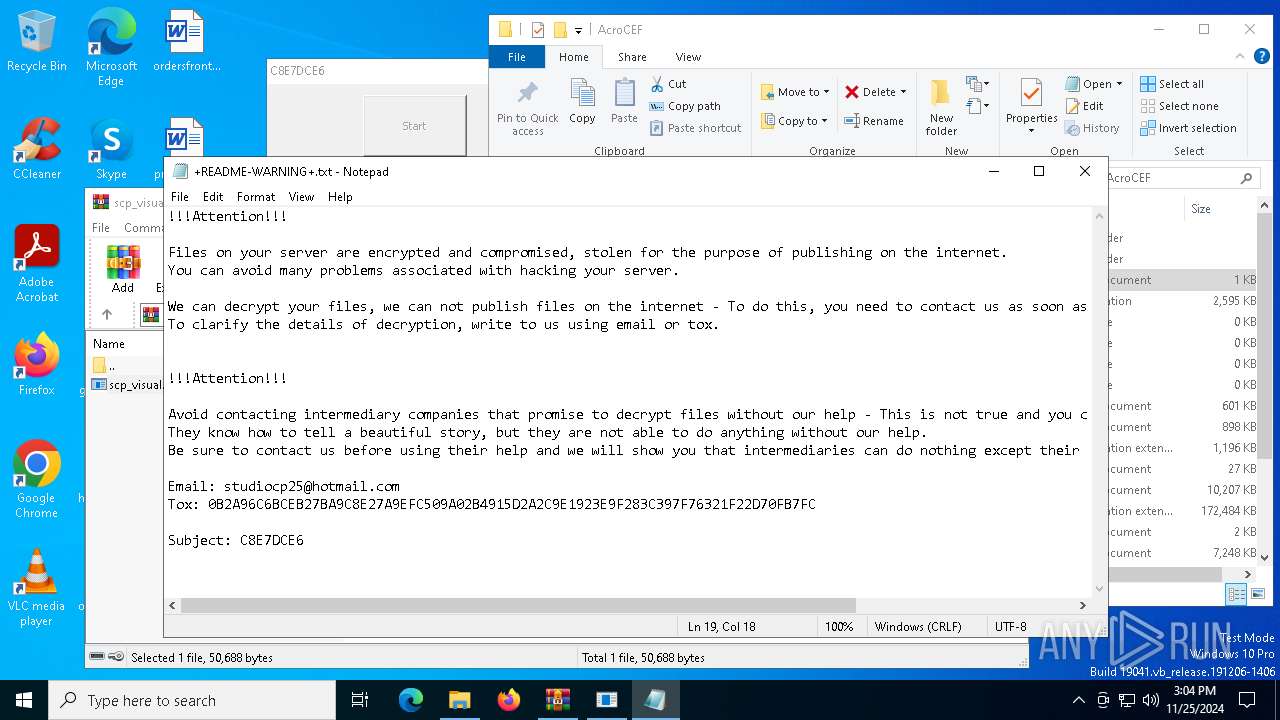
MALICIOUS
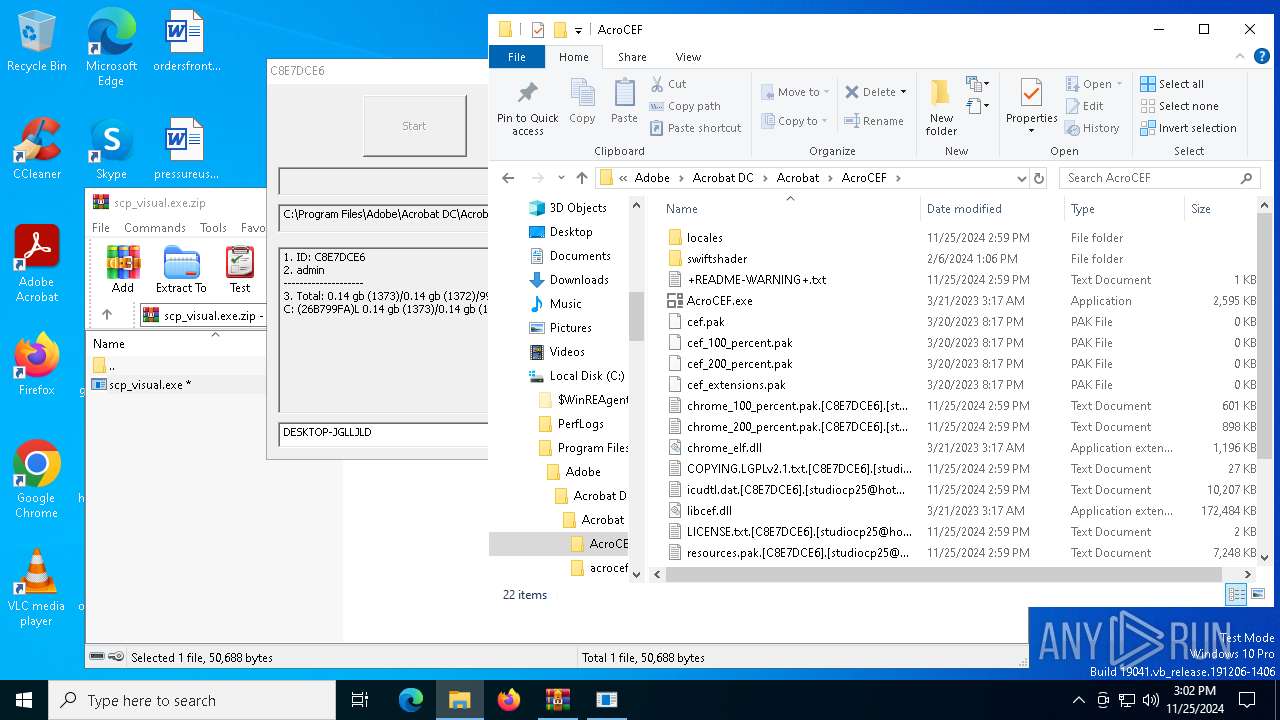
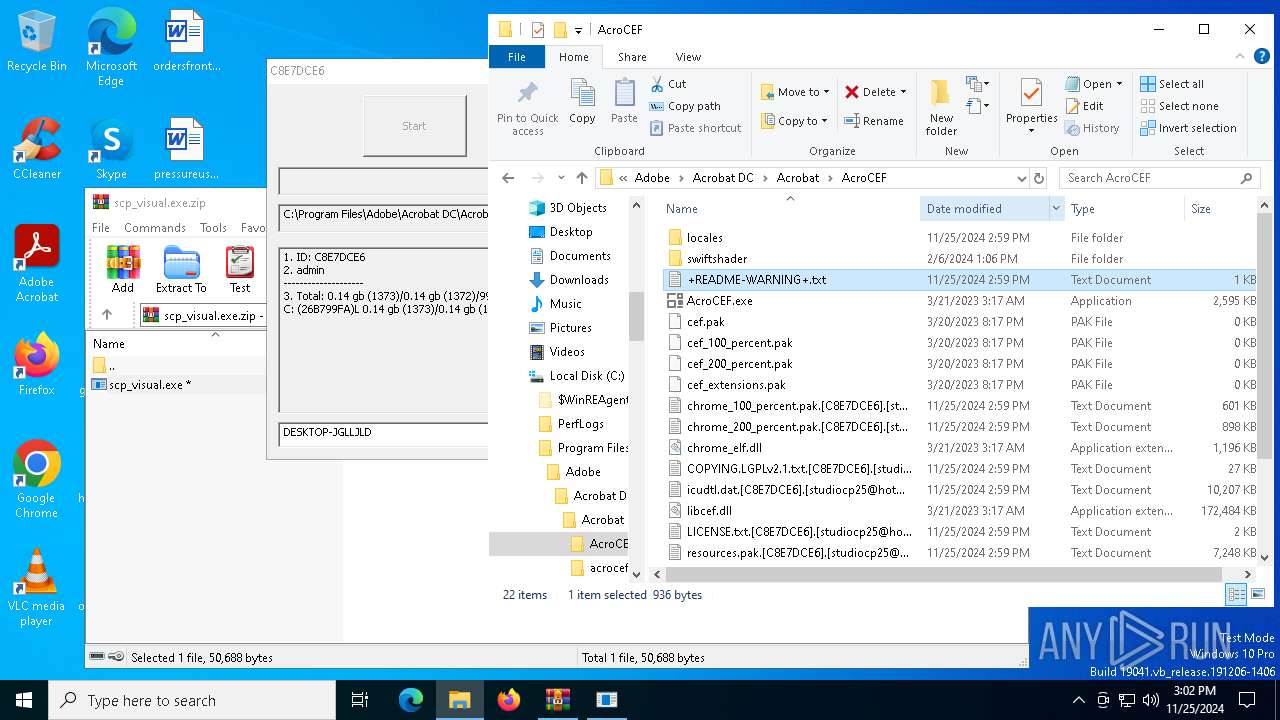
Generic archive extractor
- WinRAR.exe (PID: 6508)
Deletes shadow copies
- cmd.exe (PID: 3988)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 4520)
- wbengine.exe (PID: 6012)
- vds.exe (PID: 1616)
Application launched itself
- scp_visual.exe (PID: 6396)
Starts CMD.EXE for commands execution
- scp_visual.exe (PID: 3732)
INFO
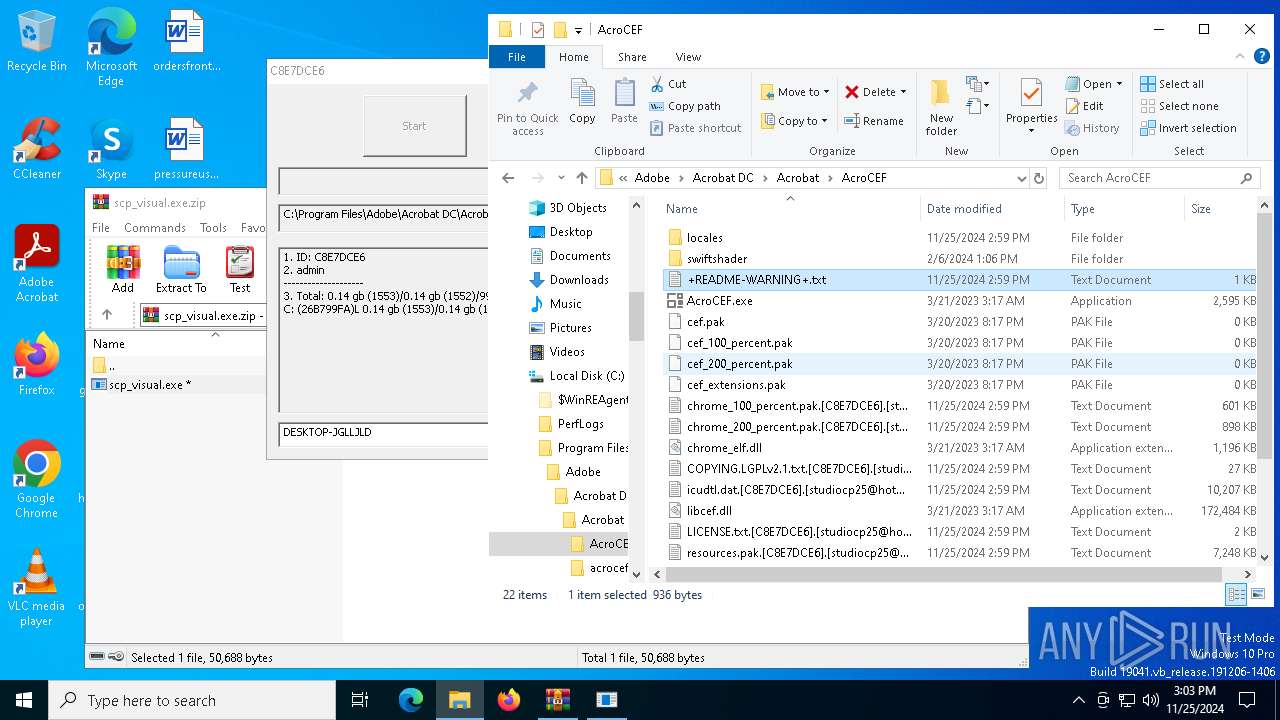
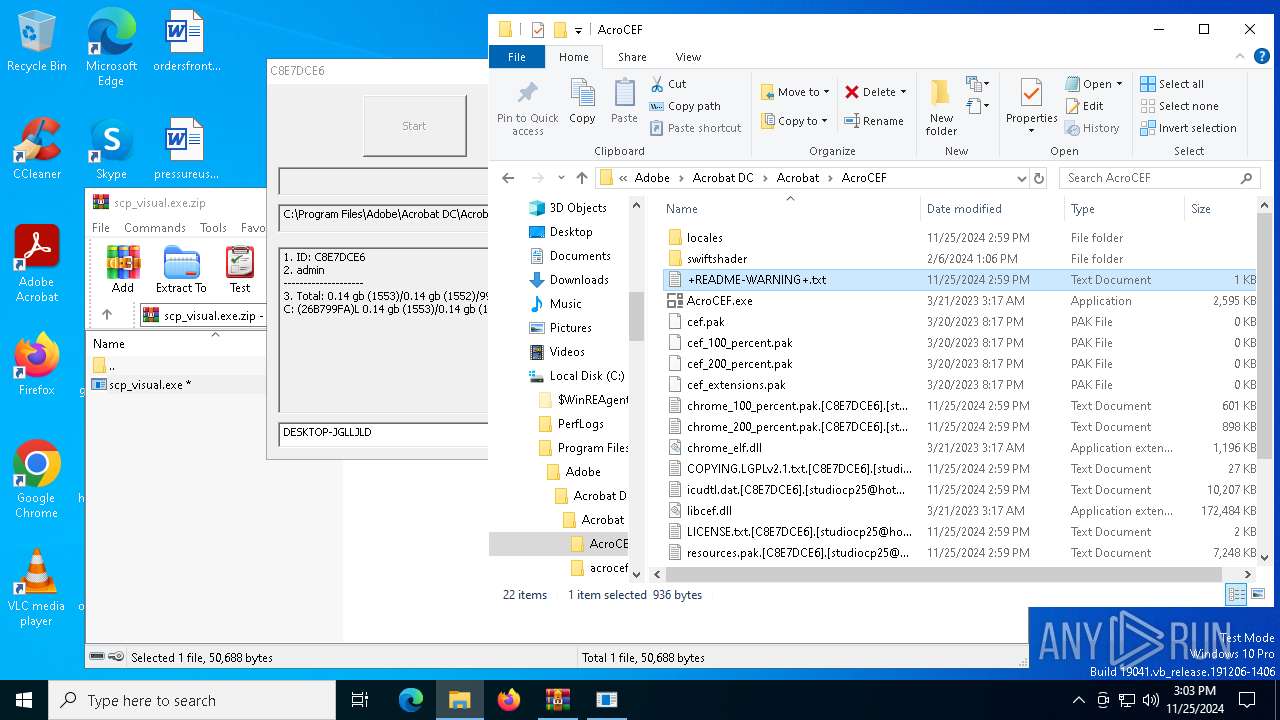
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6508)
Executes as Windows Service
- OfficeClickToRun.exe (PID: 3224)
Manual execution by a user
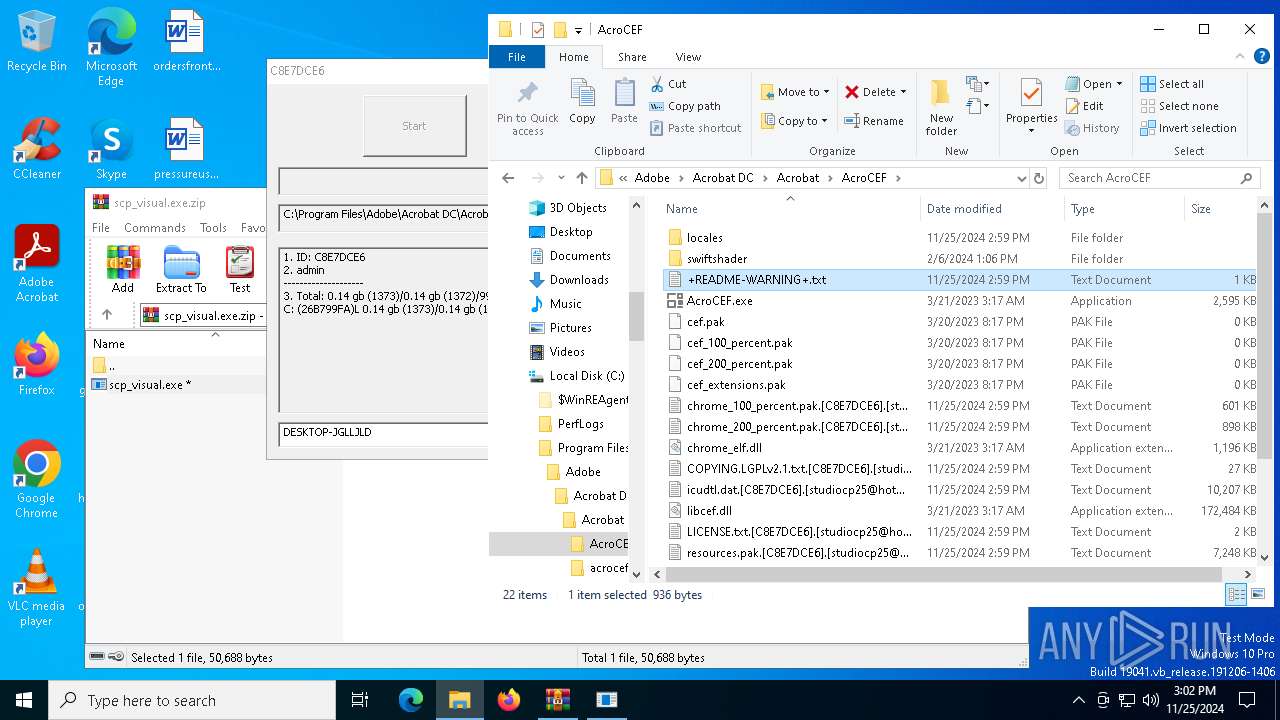
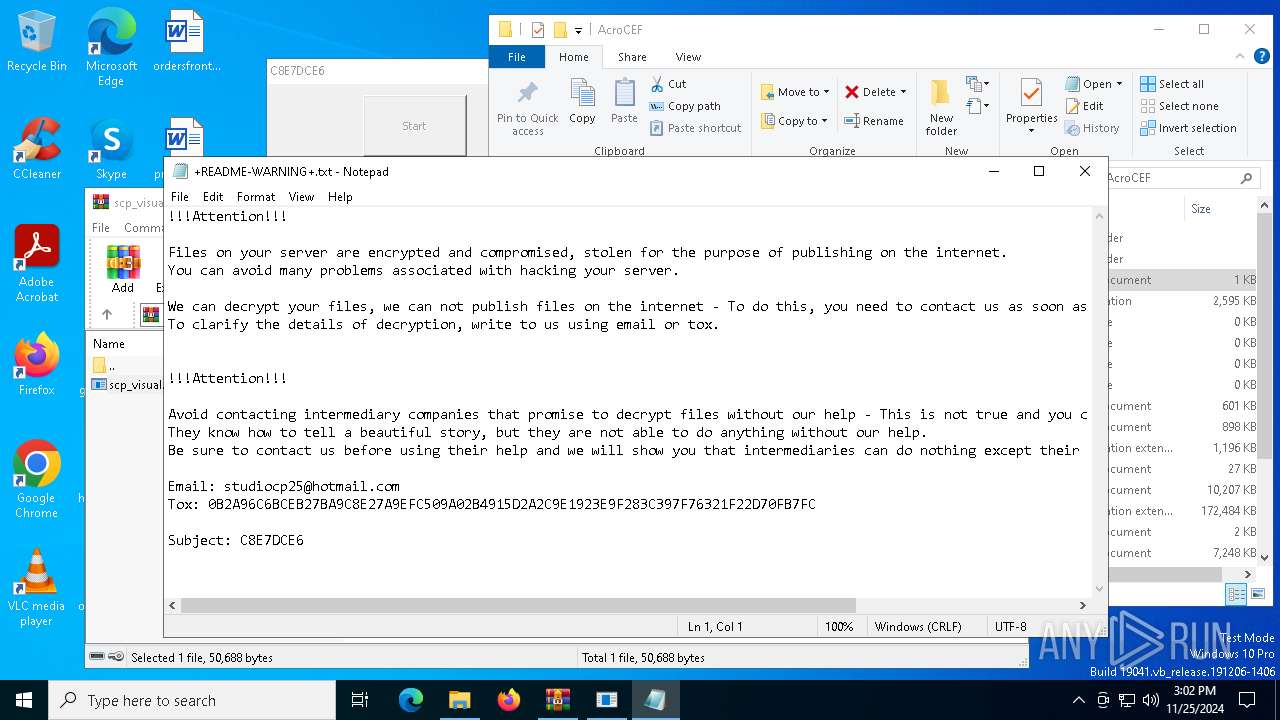
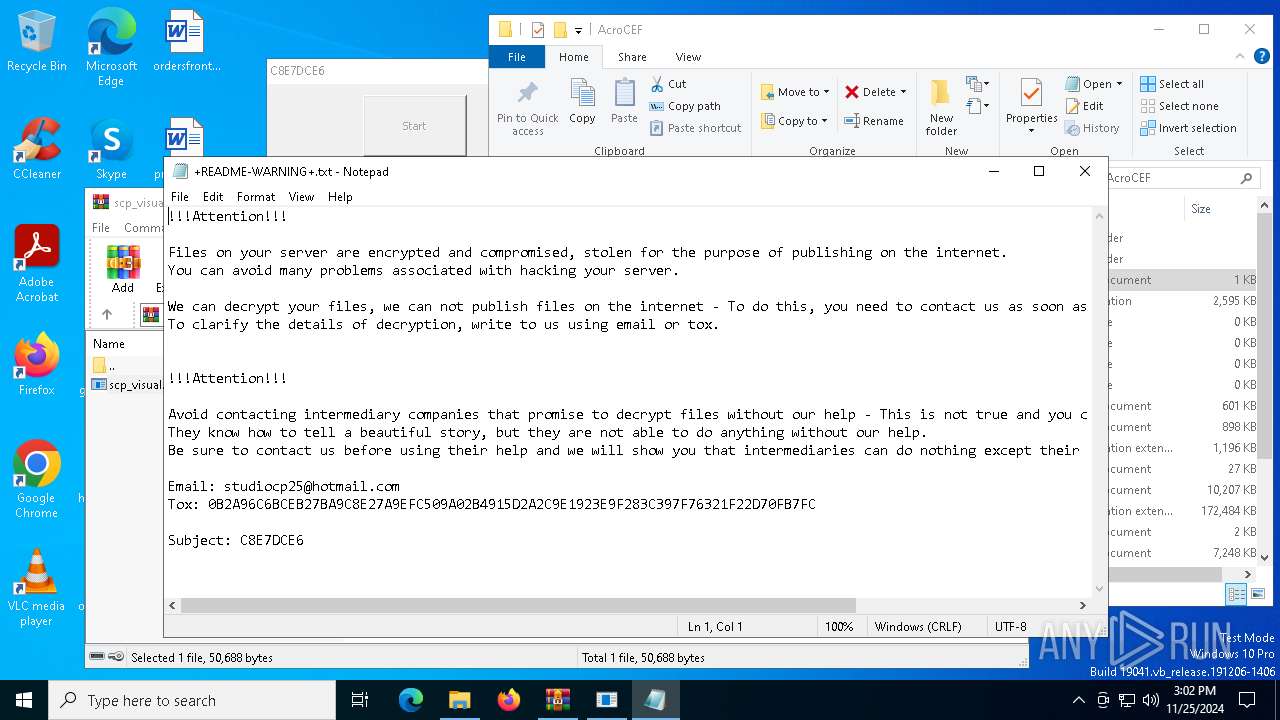
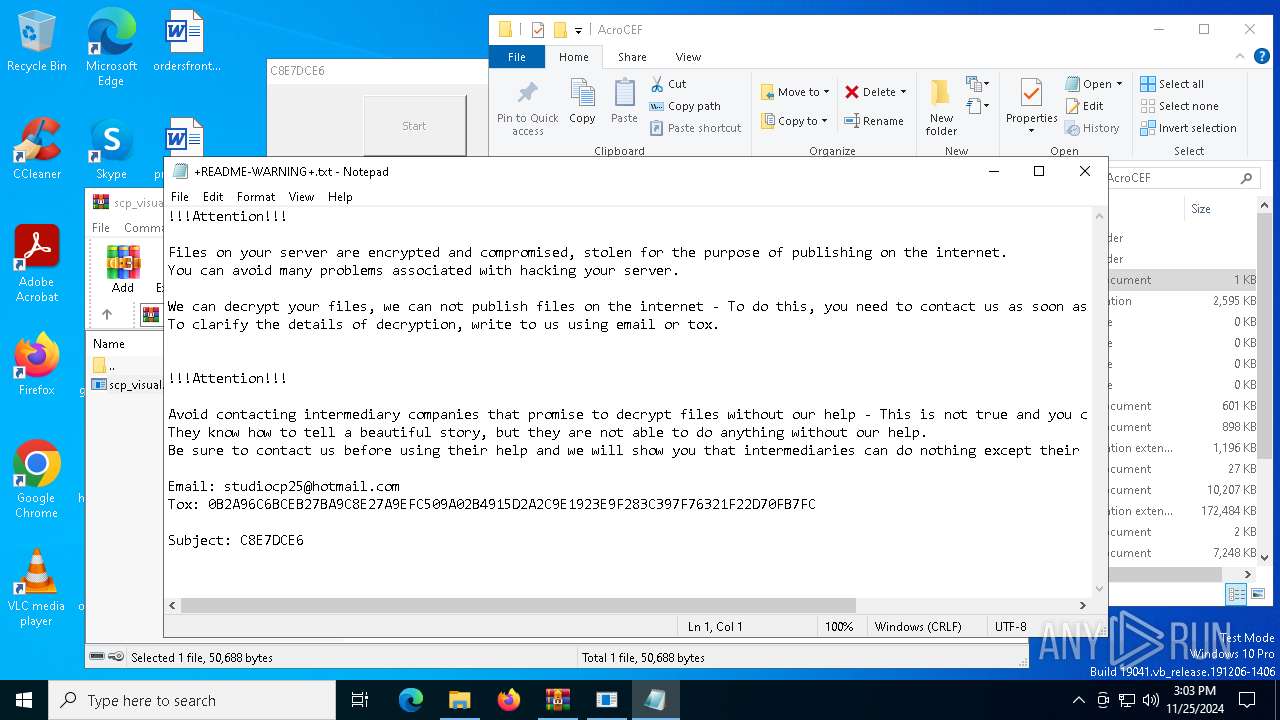
- notepad.exe (PID: 3076)
- notepad.exe (PID: 3112)
- notepad.exe (PID: 6984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:11:21 21:47:30 |
| ZipCRC: | 0x98ab0491 |
| ZipCompressedSize: | 31768 |
| ZipUncompressedSize: | 50688 |
| ZipFileName: | scp_visual.exe |
Total processes
149
Monitored processes
17
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1616 | C:\WINDOWS\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
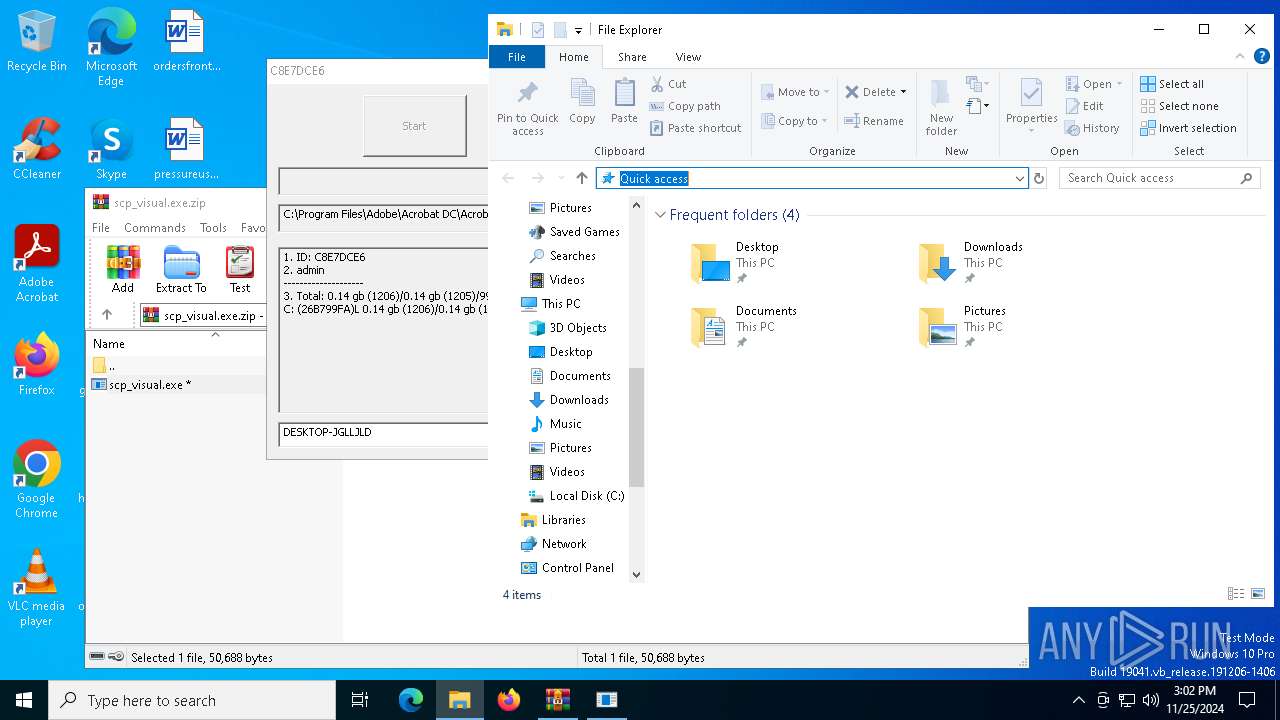
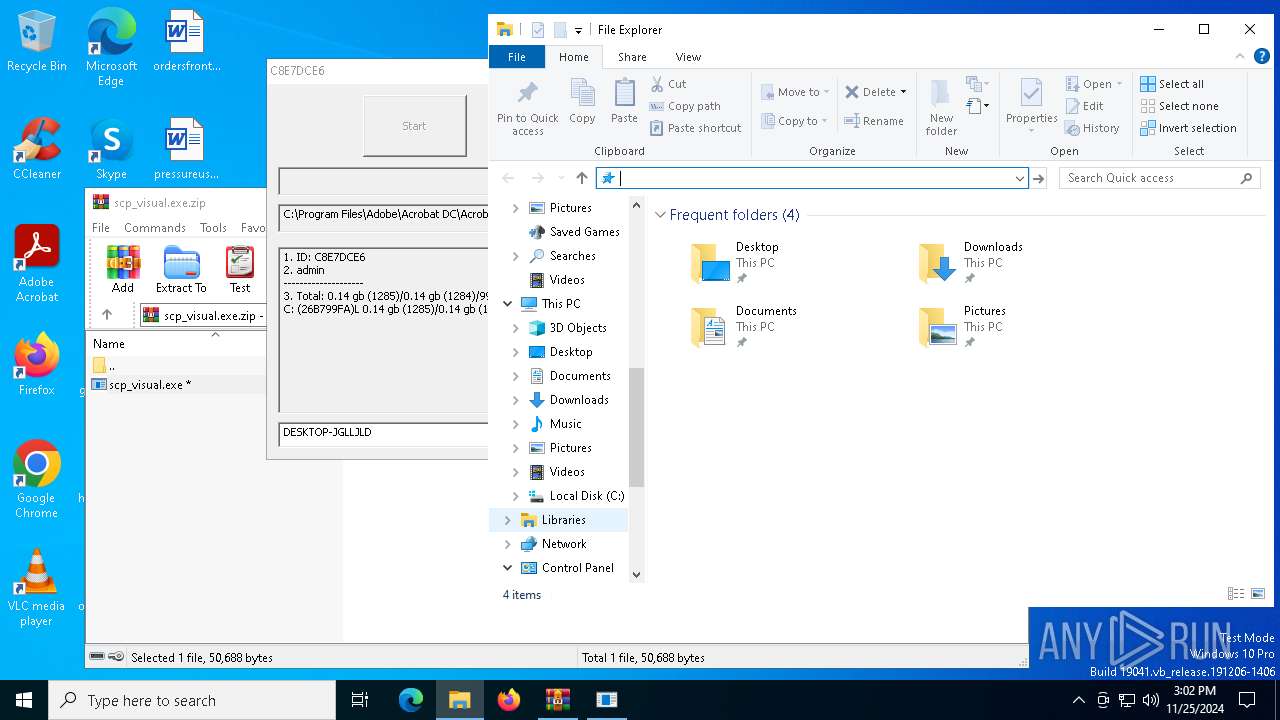
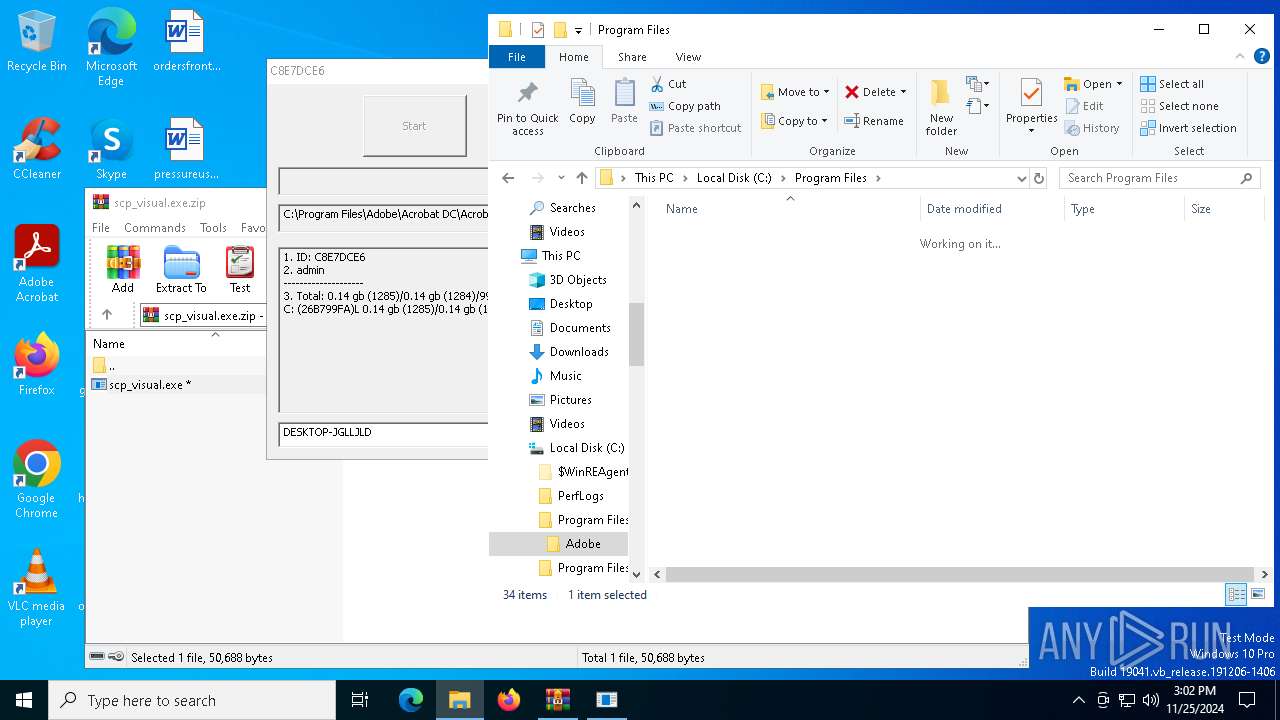
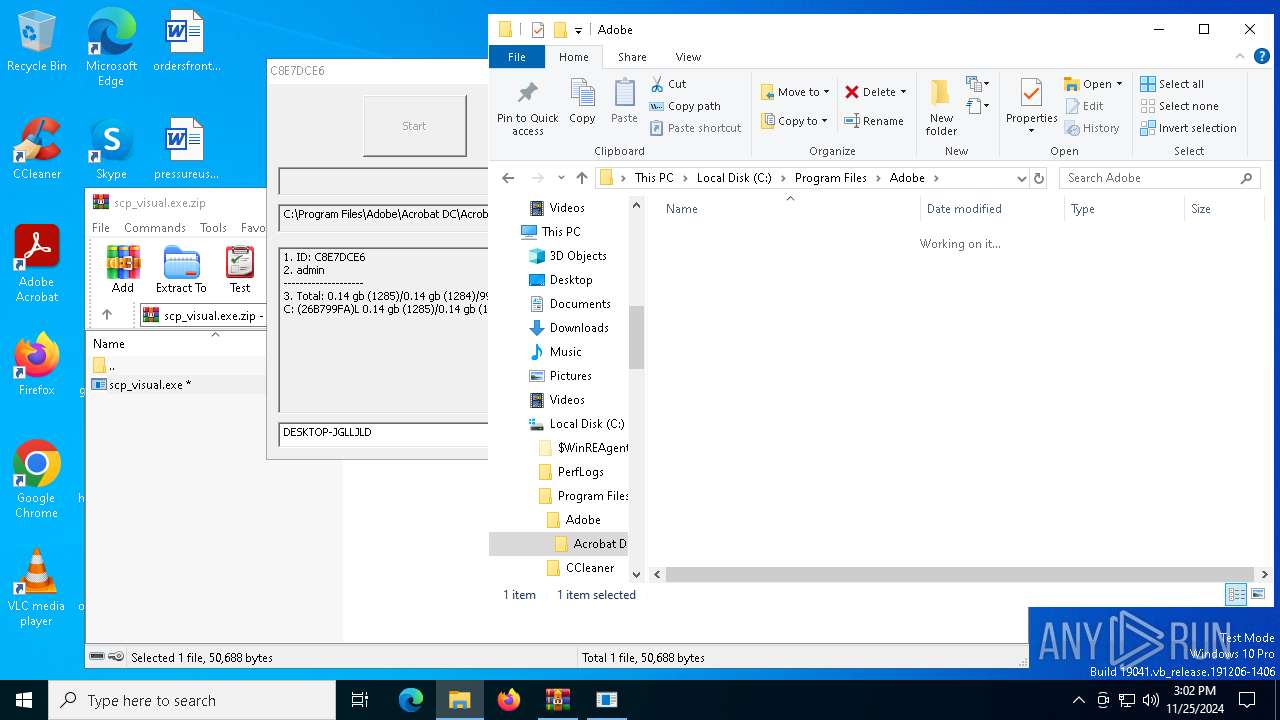
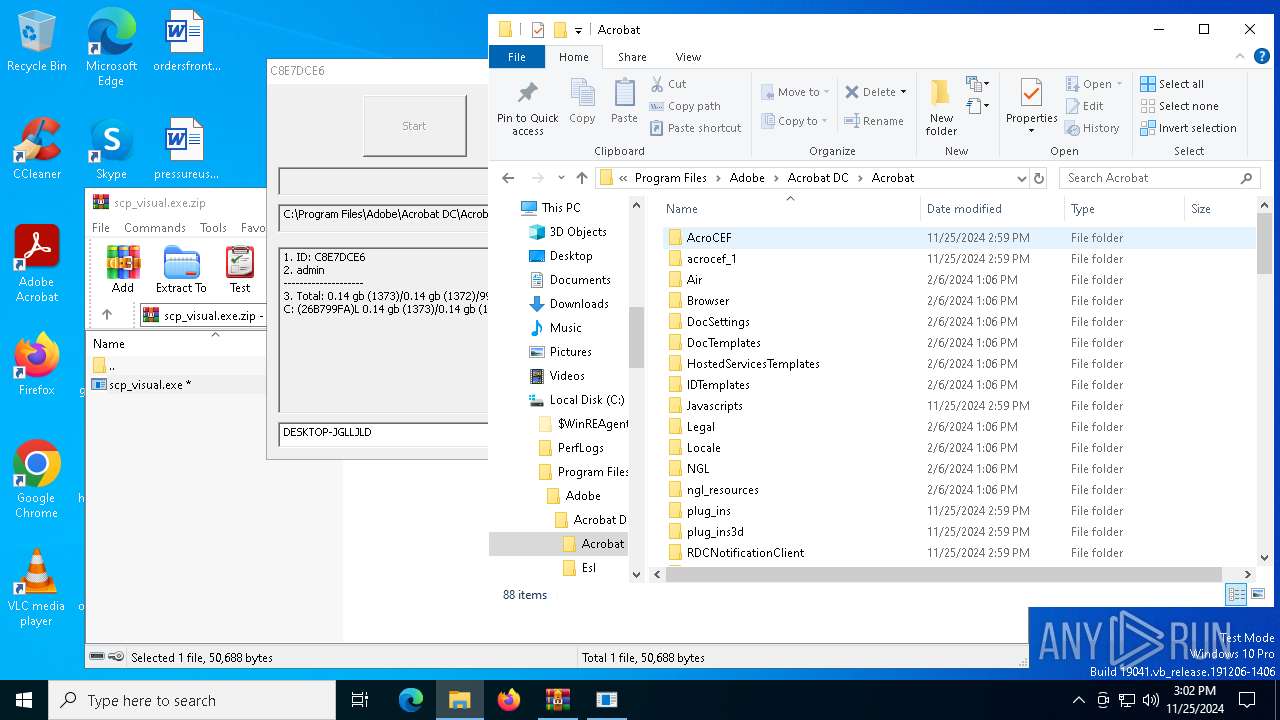
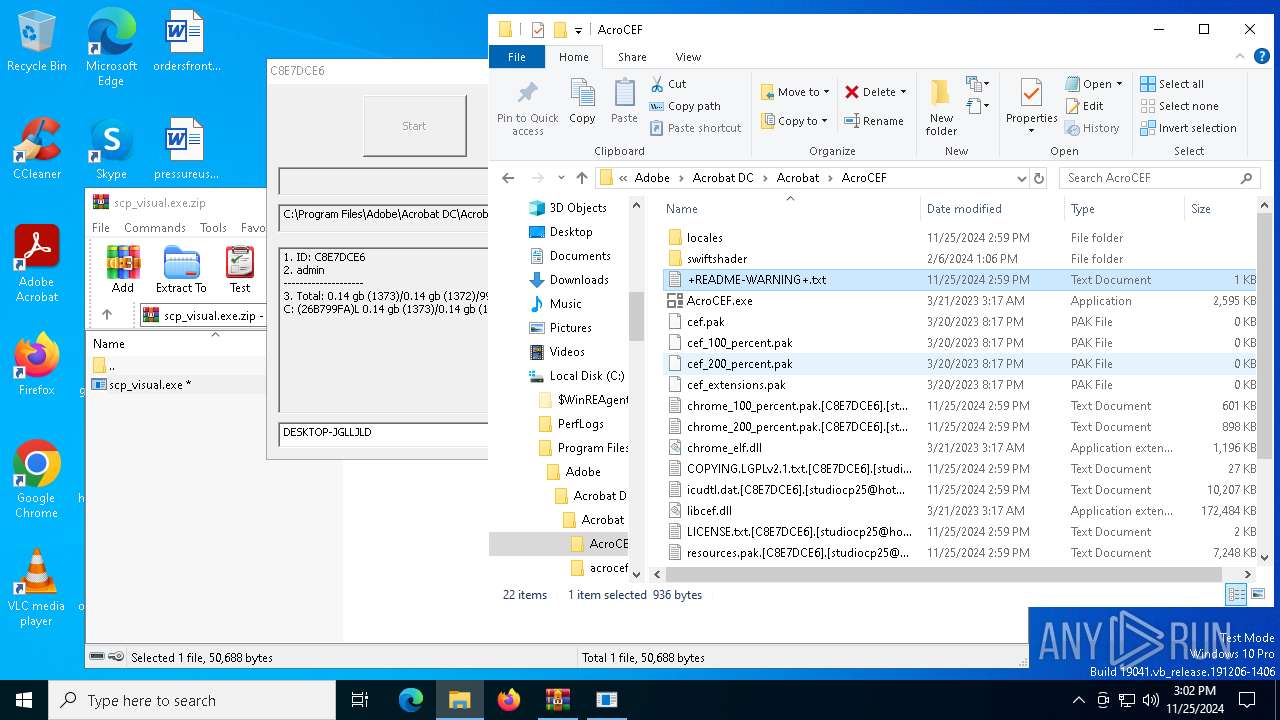
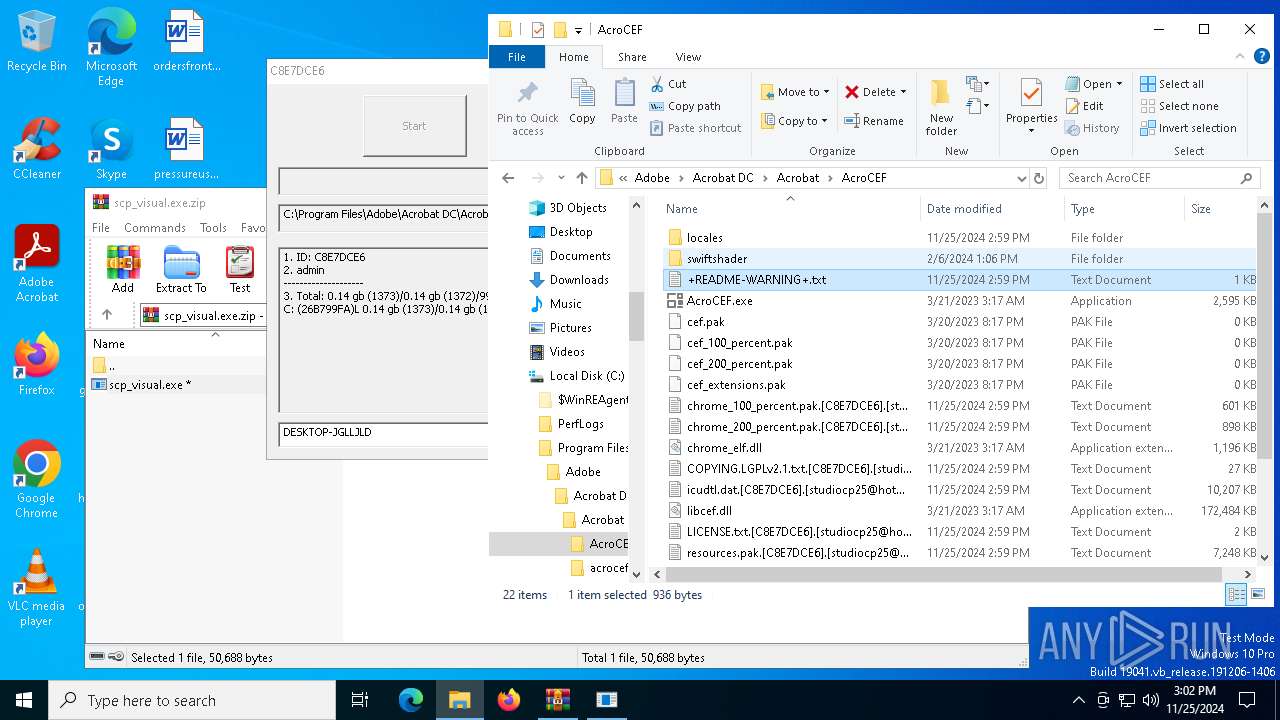
| 3076 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Program Files\Adobe\Acrobat DC\Acrobat\AcroCEF\+README-WARNING+.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3112 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Program Files\Adobe\Acrobat DC\Acrobat\AcroCEF\+README-WARNING+.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3224 | "C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeClickToRun.exe" /service | C:\Program Files\Common Files\microsoft shared\ClickToRun\OfficeClickToRun.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Office Click-to-Run (SxS) Version: 16.0.16026.20140 Modules
| |||||||||||||||
| 3732 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb6508.7003\scp_visual.exe" e | C:\Users\admin\AppData\Local\Temp\Rar$EXb6508.7003\scp_visual.exe | scp_visual.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 3988 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | scp_visual.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4320 | wbadmin delete catalog -quiet | C:\Windows\System32\wbadmin.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® BLB Backup Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4520 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4704 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4708 | C:\WINDOWS\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Loader Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 613
Read events
5 604
Write events
9
Delete events
0
Modification events
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\scp_visual.exe.zip | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
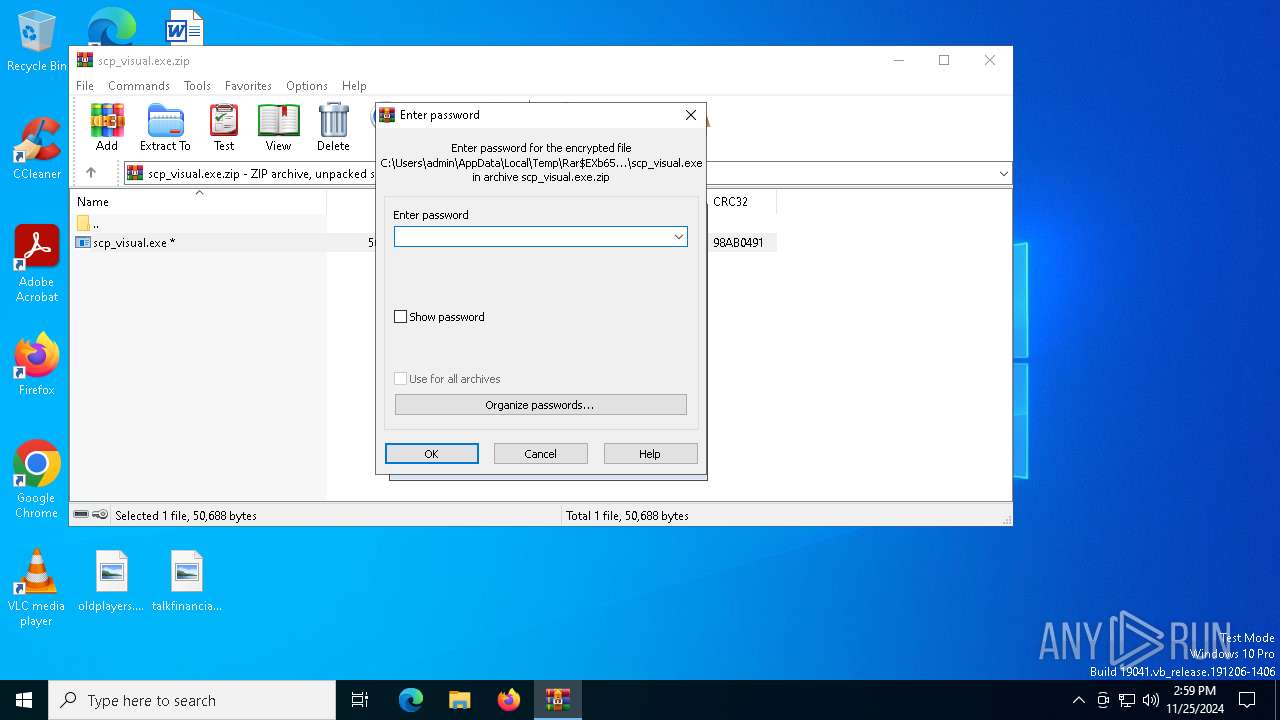
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
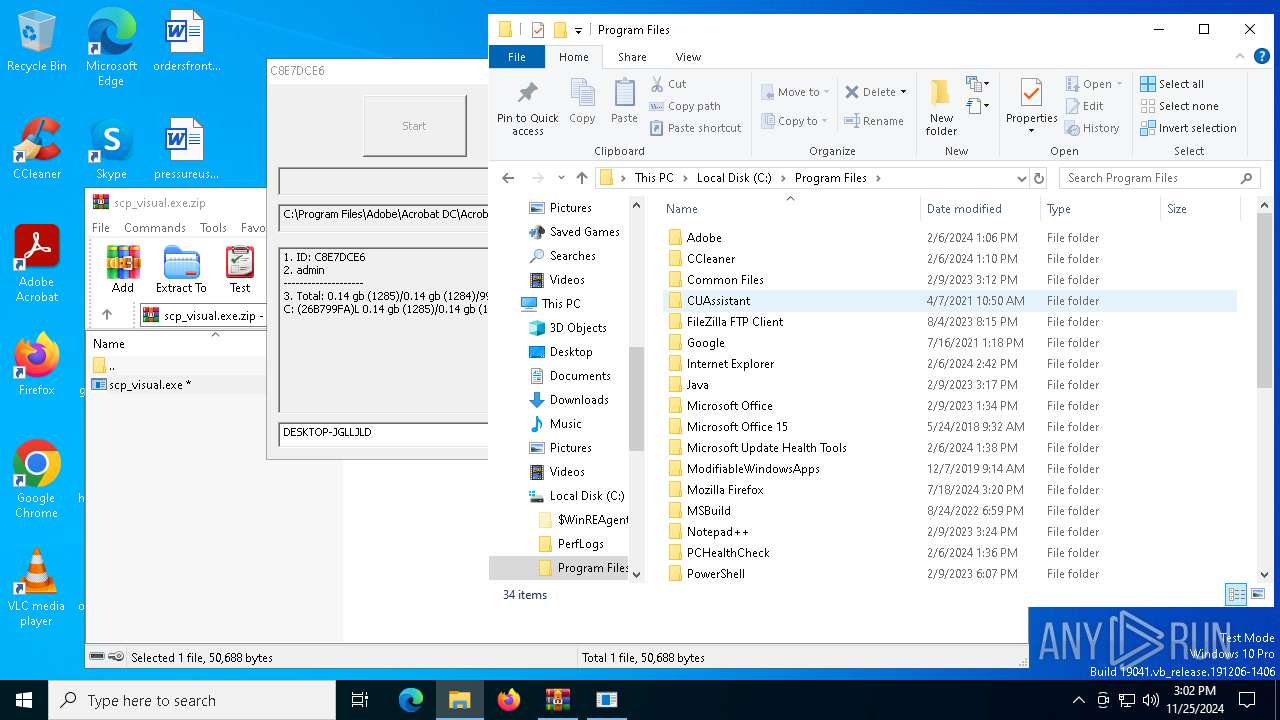
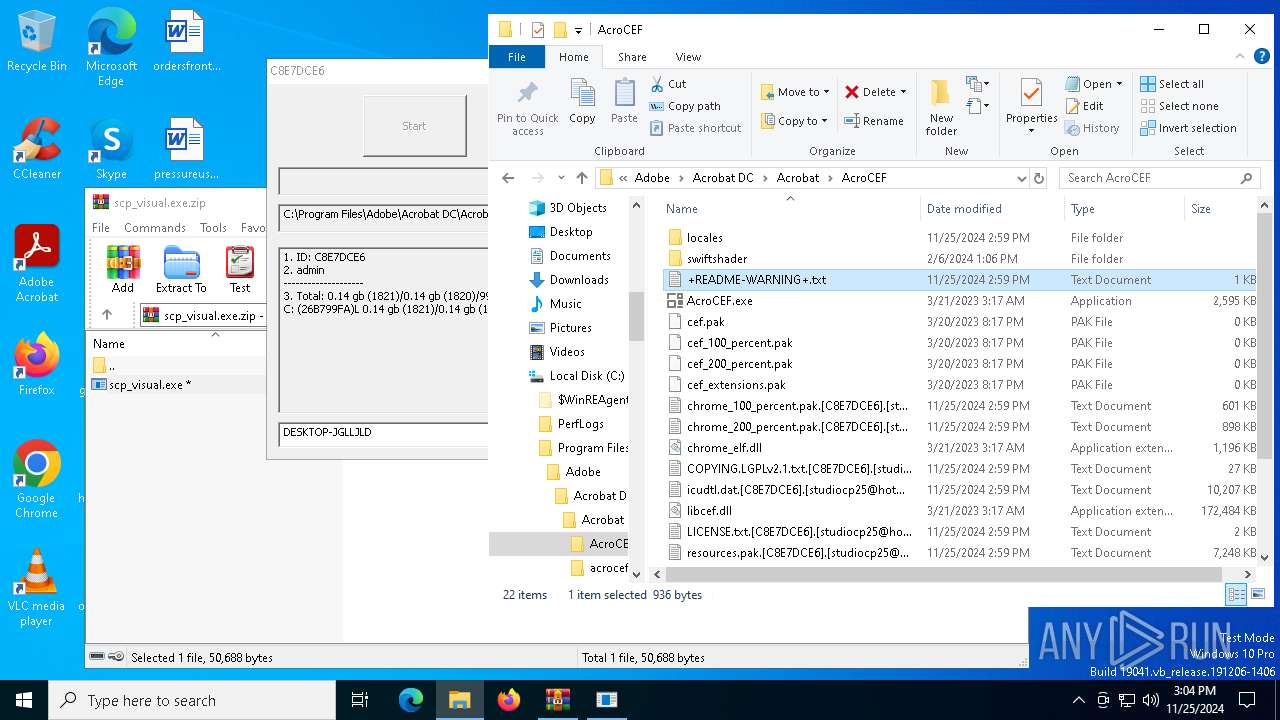
Executable files
7
Suspicious files
2 747
Text files
827
Unknown types
0
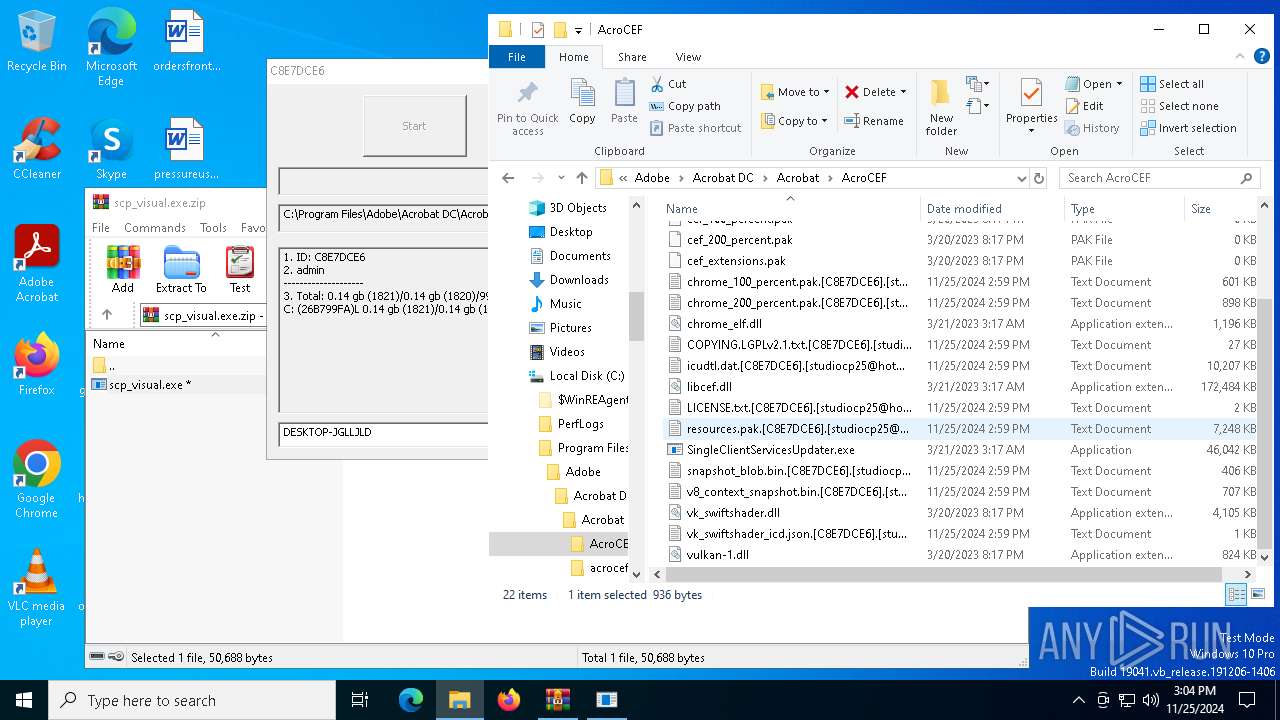
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
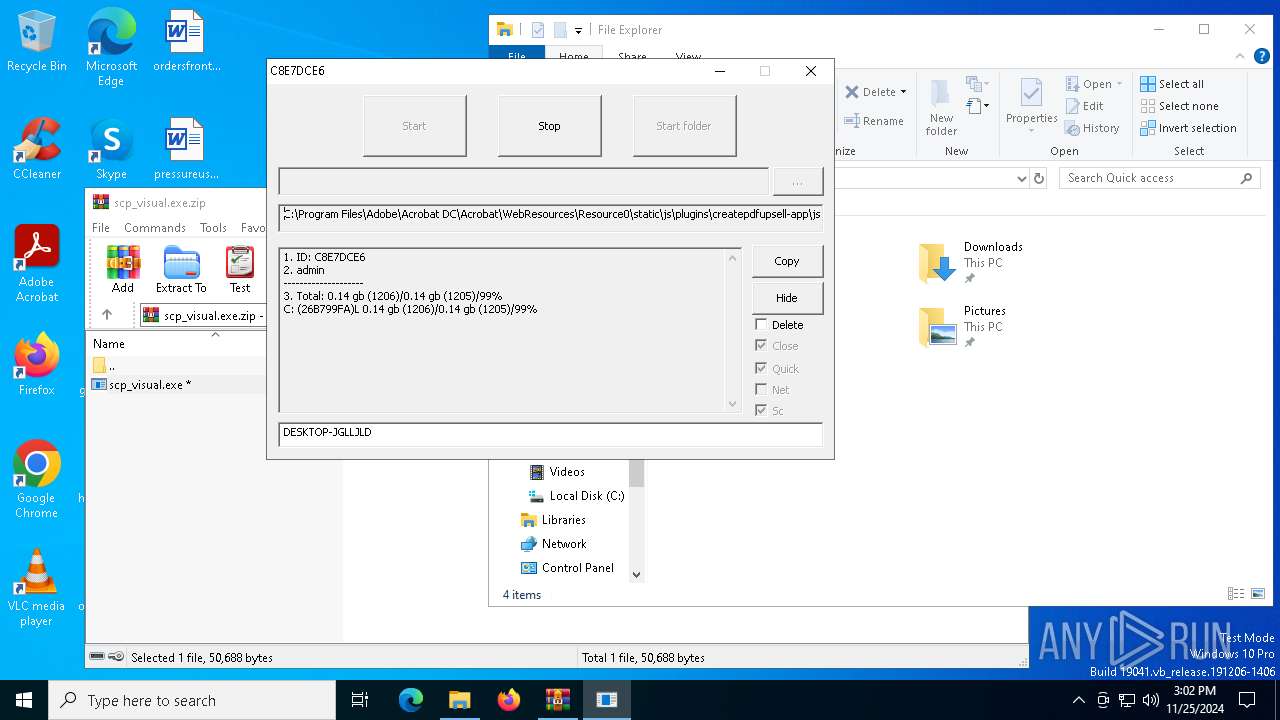
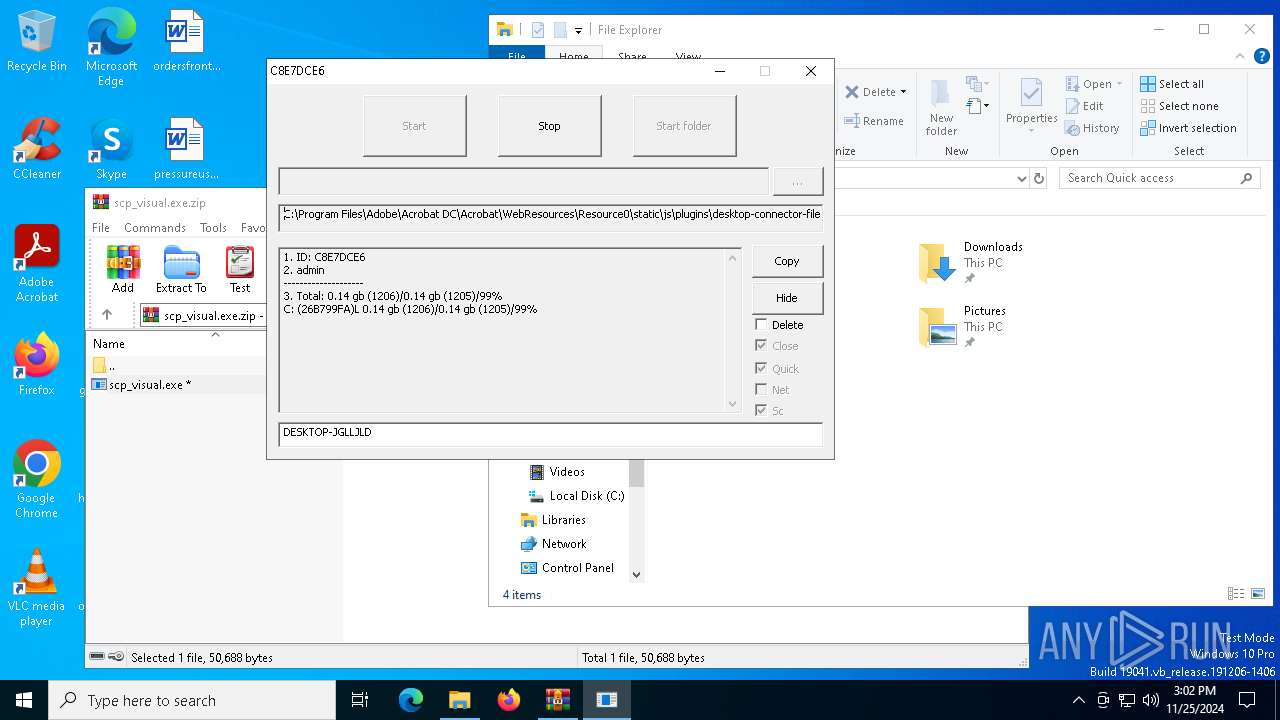
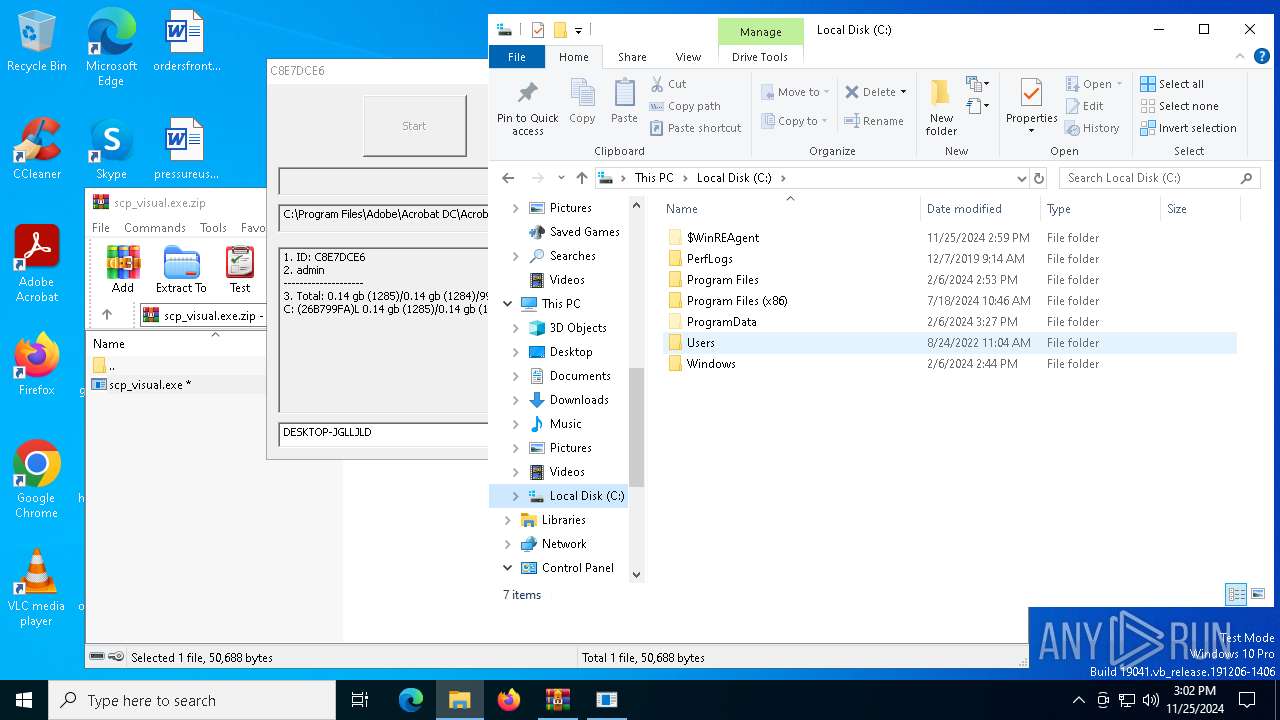
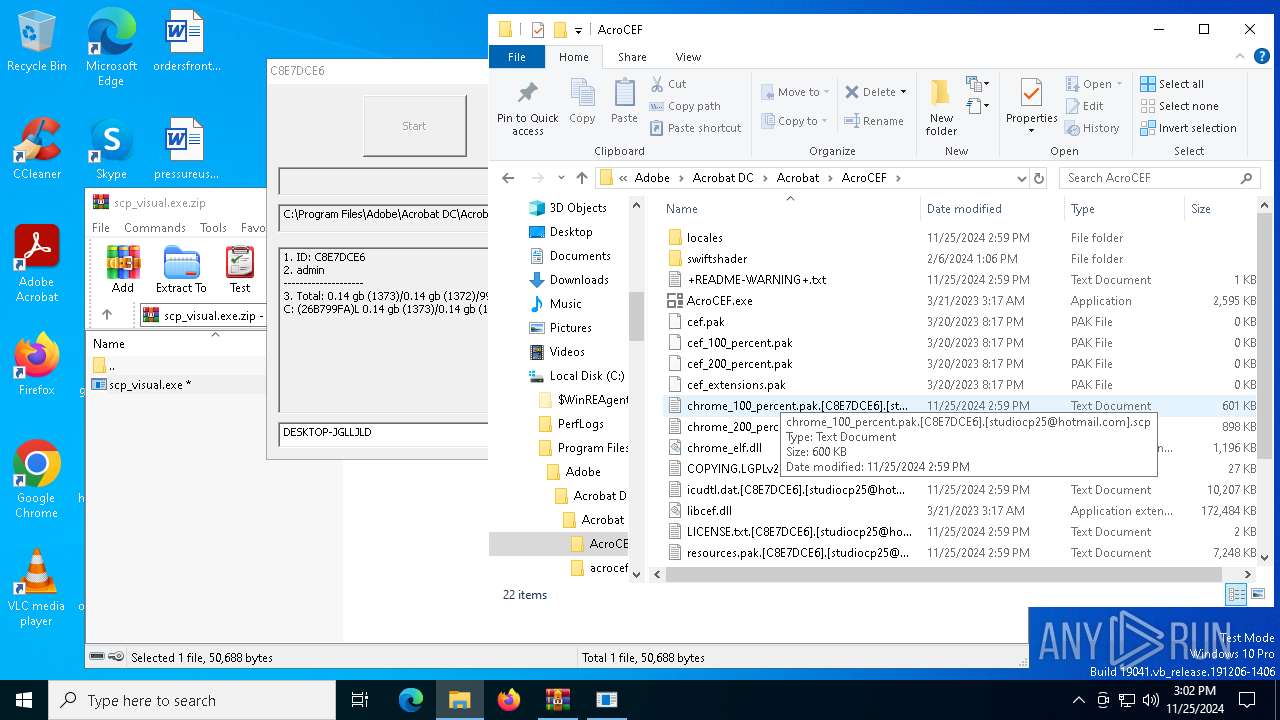
| 3732 | scp_visual.exe | C:\$WinREAgent\Backup\location.txt.[C8E7DCE6].[studiocp25@hotmail.com].scp | binary | |
MD5:A442AFFB8AFB4428B15C0A7A3E911B81 | SHA256:97CE505FD9367E202AB5F861379724F54236F9261900699F9DBEEC98833C1227 | |||
| 3732 | scp_visual.exe | C:\found.000\dir0000.chk\UpdateSessionOrchestration.048.etl.[C8E7DCE6].[studiocp25@hotmail.com].scp | binary | |
MD5:A4ED92AFF95FDBE713B9D21AB071CBB9 | SHA256:B2E4533D7C98C1A4ACC99147C0E946F346BE7E7517C92B8EE9843C31F6B21098 | |||
| 3732 | scp_visual.exe | C:\found.000\dir0000.chk\UpdateSessionOrchestration.016.etl.[C8E7DCE6].[studiocp25@hotmail.com].scp | binary | |
MD5:95C18BA44997D57AEC42D295585A2749 | SHA256:B89A8EFF3A77F6749C39FDE16F1387206A6555EDC8DCA72D21E8EE070A2DEF2E | |||
| 3732 | scp_visual.exe | C:\found.000\dir0000.chk\+README-WARNING+.txt | text | |
MD5:A716283E6A49F42EC7706DEDE1AA007C | SHA256:F1BFAA1AF9F871DB2BEA5FE25EB87D0BFF0B5B70211866BA3D81EDA1D0B7B173 | |||
| 3732 | scp_visual.exe | C:\found.000\dir0000.chk\UpdateSessionOrchestration.058.etl.[C8E7DCE6].[studiocp25@hotmail.com].scp | binary | |
MD5:D228A03993AFC8E893D5CED1001D6483 | SHA256:B5F670DDCFF8A365CB061179D14157771652E46D90670D420E514FD195880FA6 | |||
| 3732 | scp_visual.exe | C:\found.000\dir0000.chk\UpdateSessionOrchestration.055.etl.[C8E7DCE6].[studiocp25@hotmail.com].scp | binary | |
MD5:D10728F7F54BE47A27FD8862CA04E55D | SHA256:00B904C6754830A61A84E3B16626A7E0AE83334B0BE817A27E8AA6A4EC168634 | |||
| 3732 | scp_visual.exe | C:\found.000\dir0001.chk\WmiApRpl.h.[C8E7DCE6].[studiocp25@hotmail.com].scp | binary | |
MD5:62E2F30F2E86E0F8FE0DCAE69C475452 | SHA256:143C3BB0F1E535DD878BB395382CA95A681E435124ED37298780CB5E92E0E283 | |||
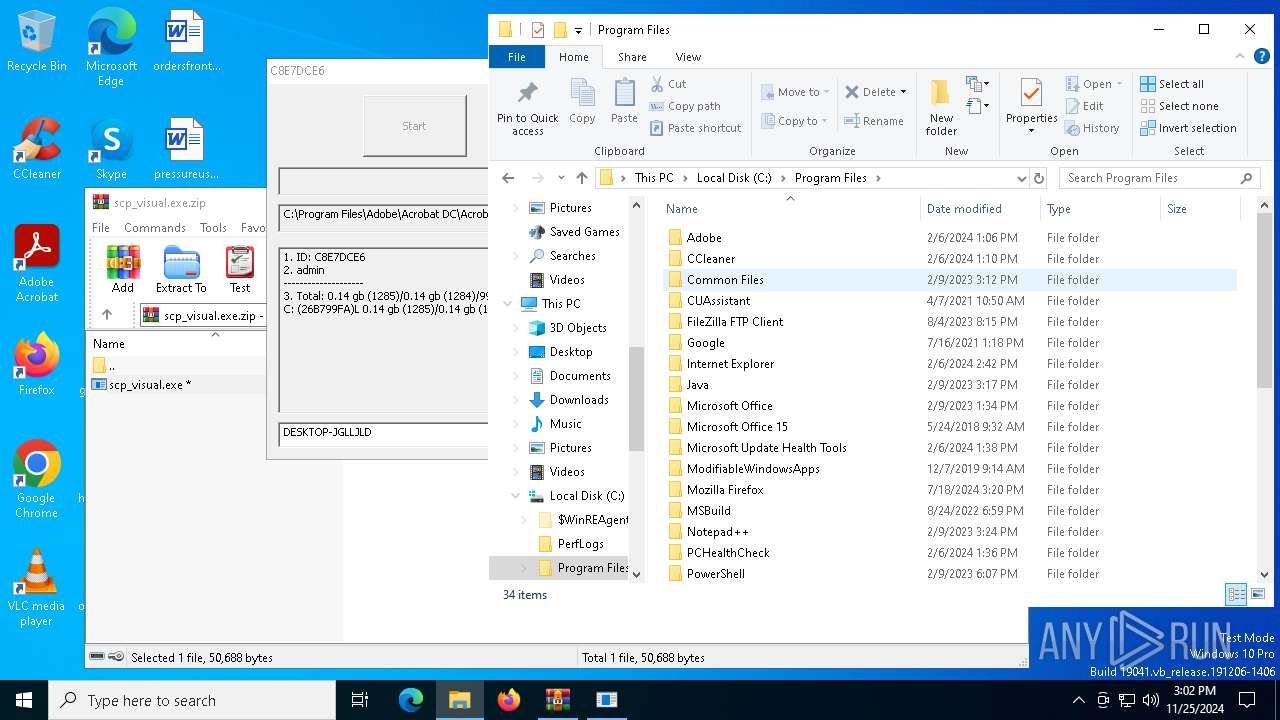
| 6508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6508.7003\scp_visual.exe | executable | |
MD5:605F80F837E82C891C7FE7BBEA34F5C8 | SHA256:1B242153C890019BC4AC43FD4FA3D685BC8E634B98F64587736D7E3B00BAD1DE | |||
| 3732 | scp_visual.exe | C:\found.000\file00000003.chk.[C8E7DCE6].[studiocp25@hotmail.com].scp | binary | |
MD5:3EC37FF0D624D39E3C294B5B10E631A3 | SHA256:1F932A8659FE5DFEB8C19EBD305A3AFFBA3B23320285E947F28682EC7253E624 | |||
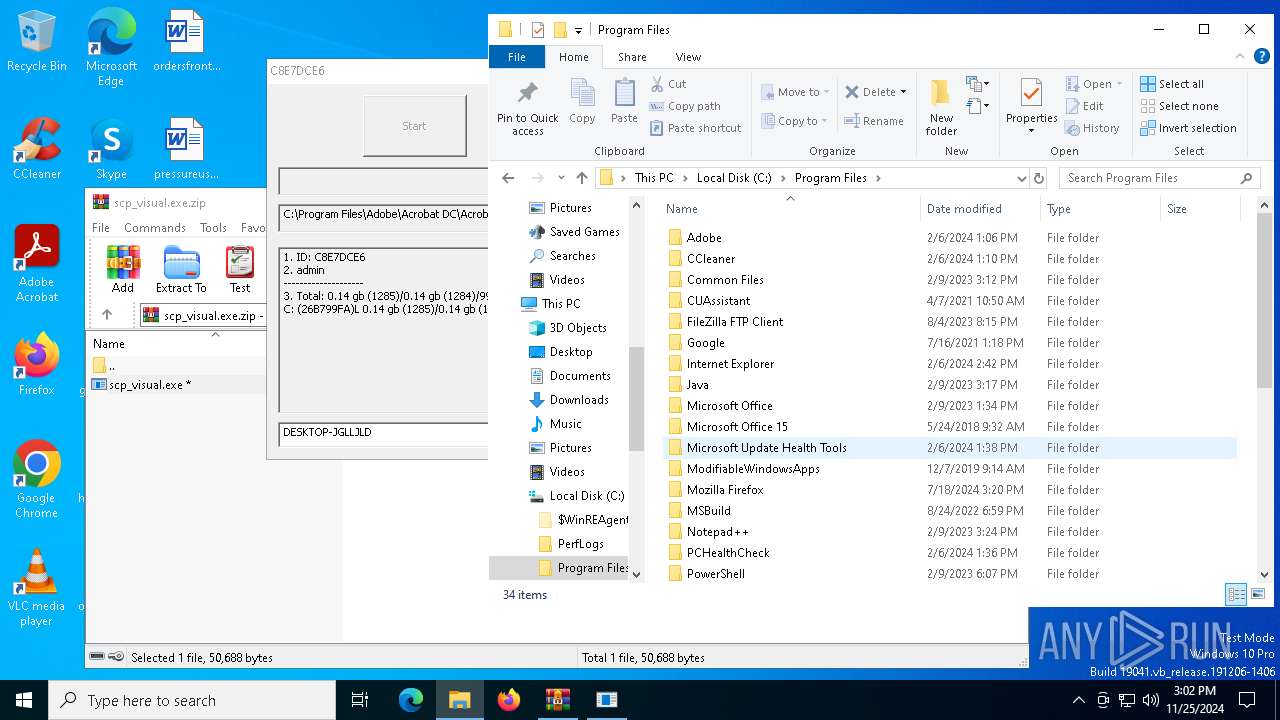
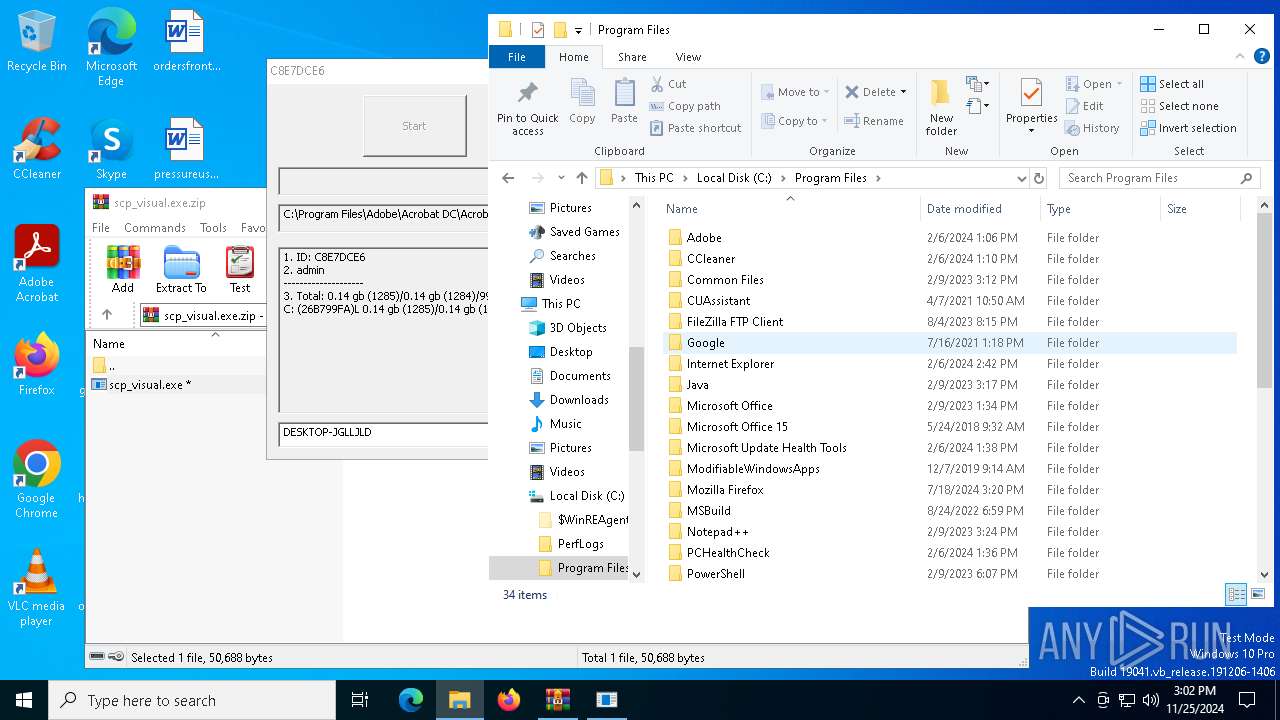
| 3732 | scp_visual.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\AcroCEF\icudtl.dat.[C8E7DCE6].[studiocp25@hotmail.com].scp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
32
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.99:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6308 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6744 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6308 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.99:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.160:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2736 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
Process | Message |
|---|---|
wbadmin.exe | Invalid parameter passed to C runtime function.
|