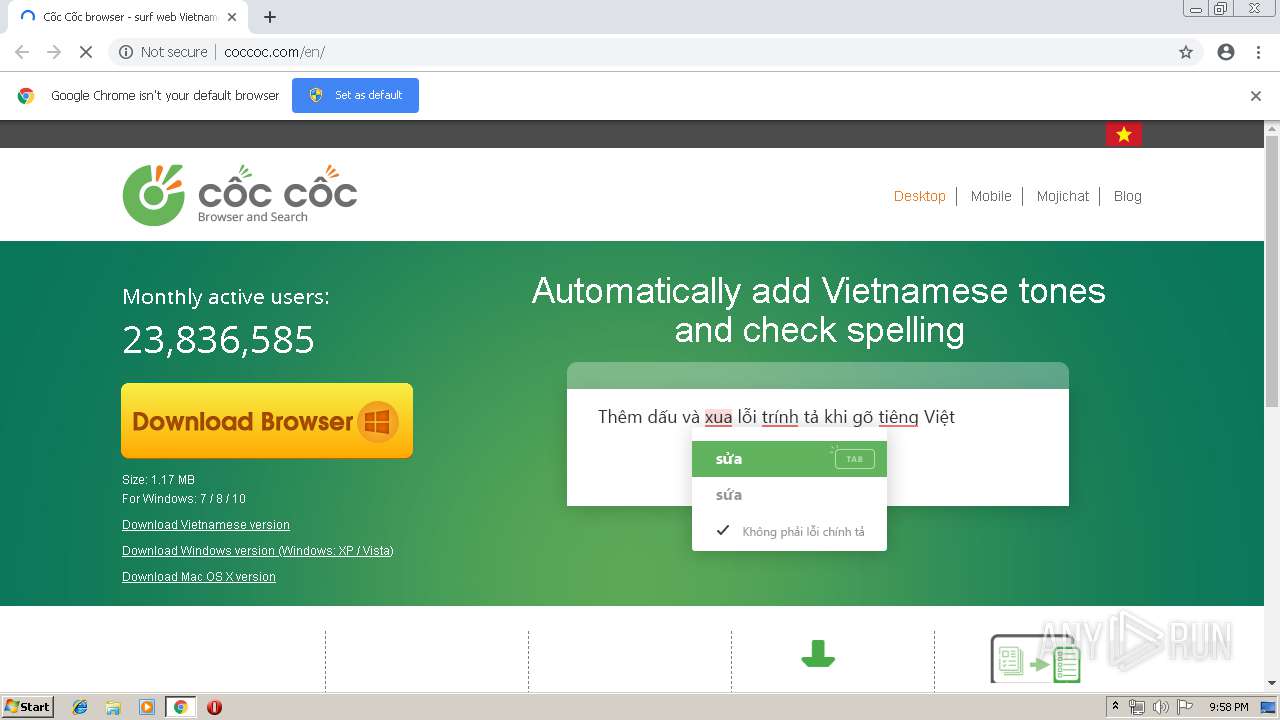
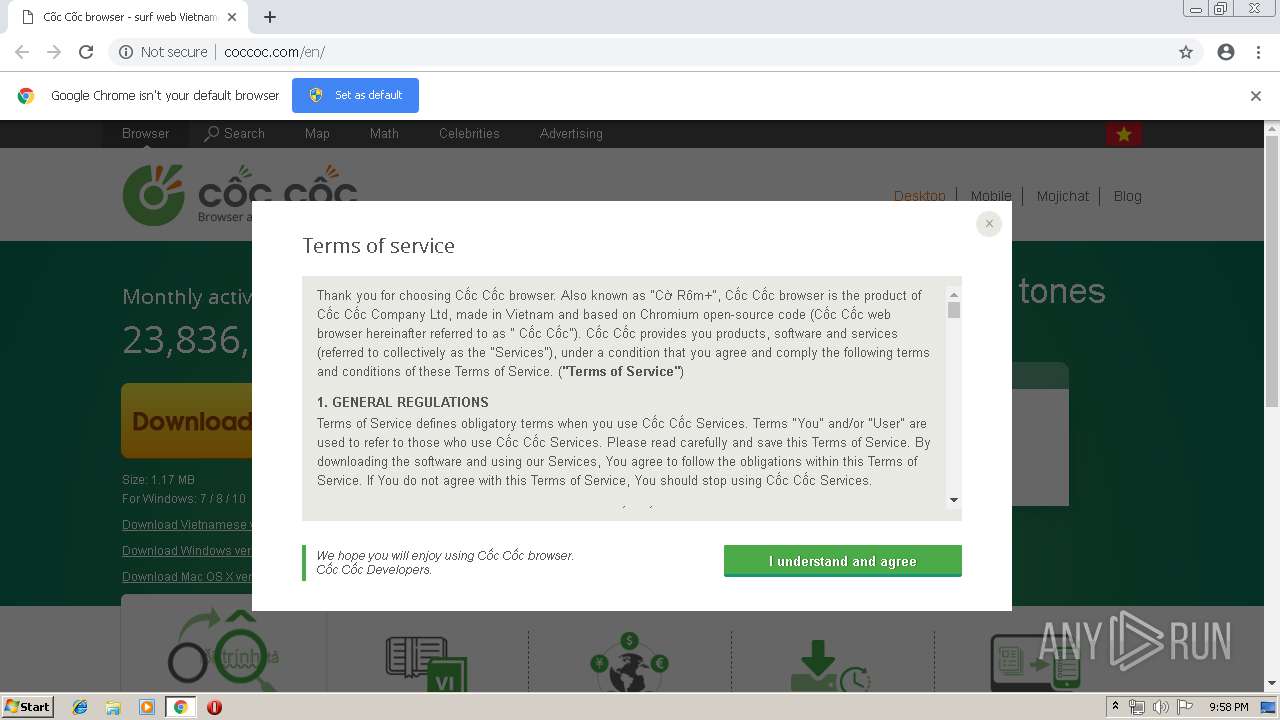
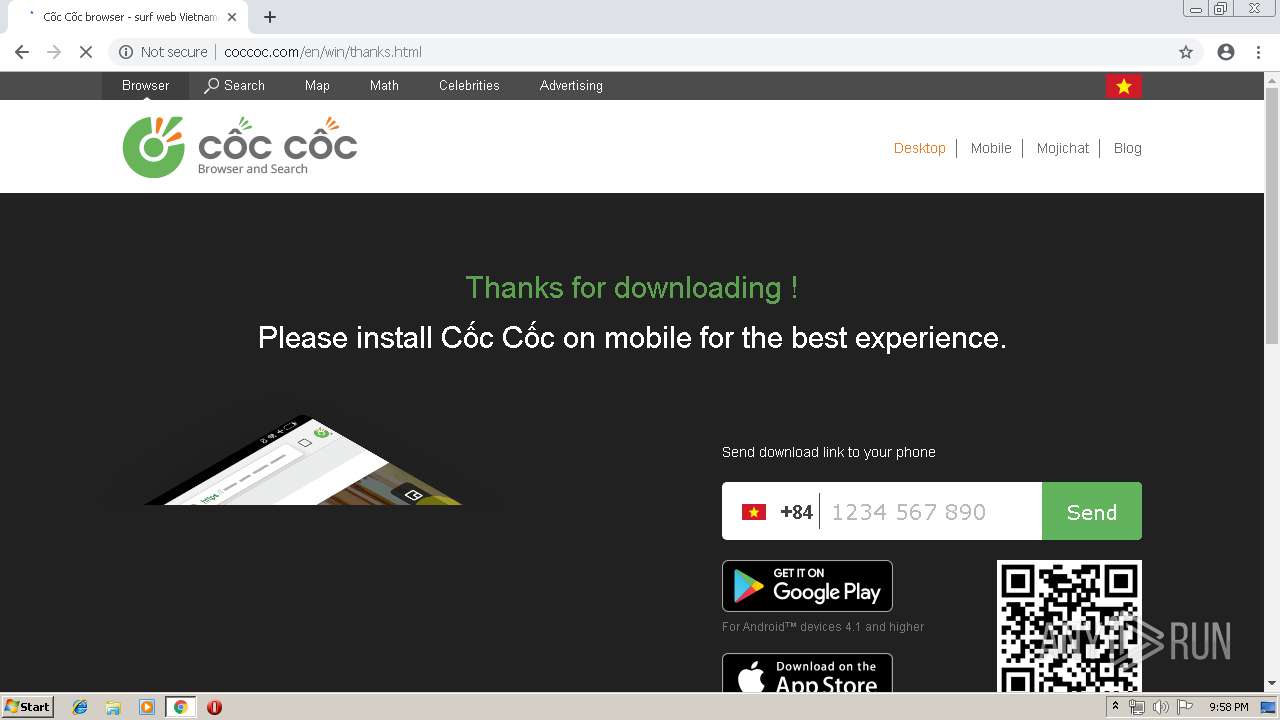
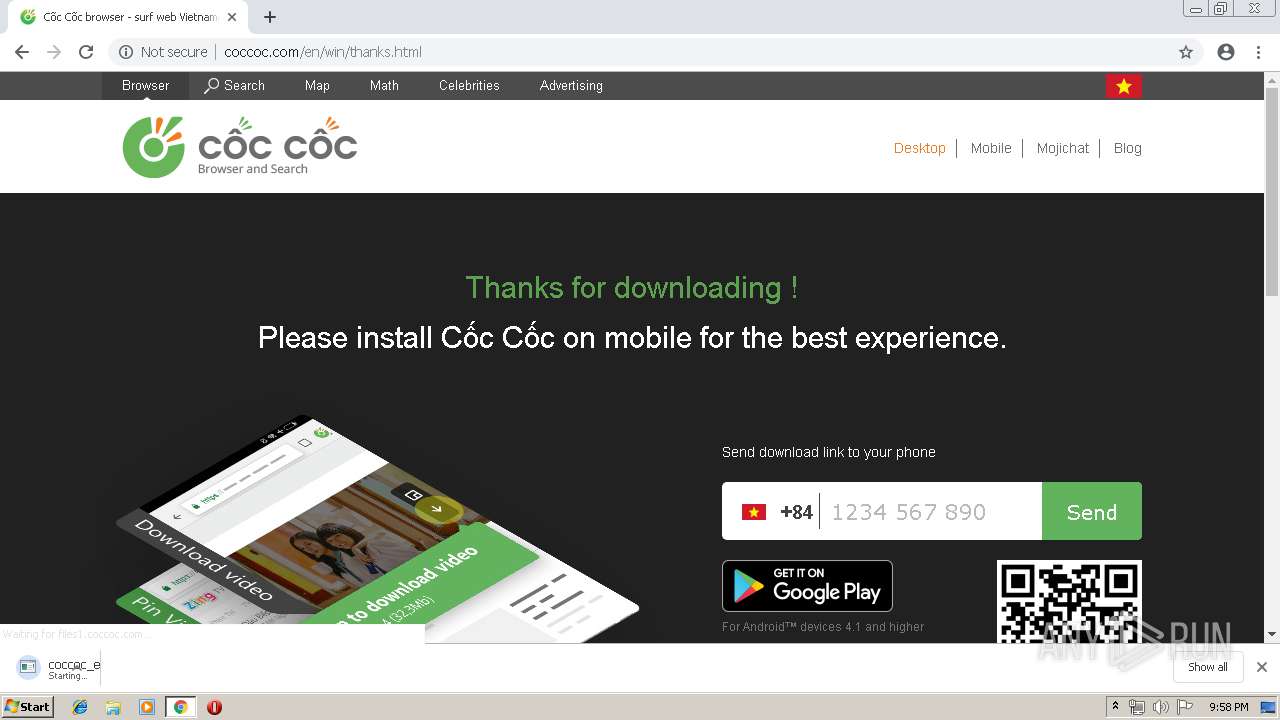
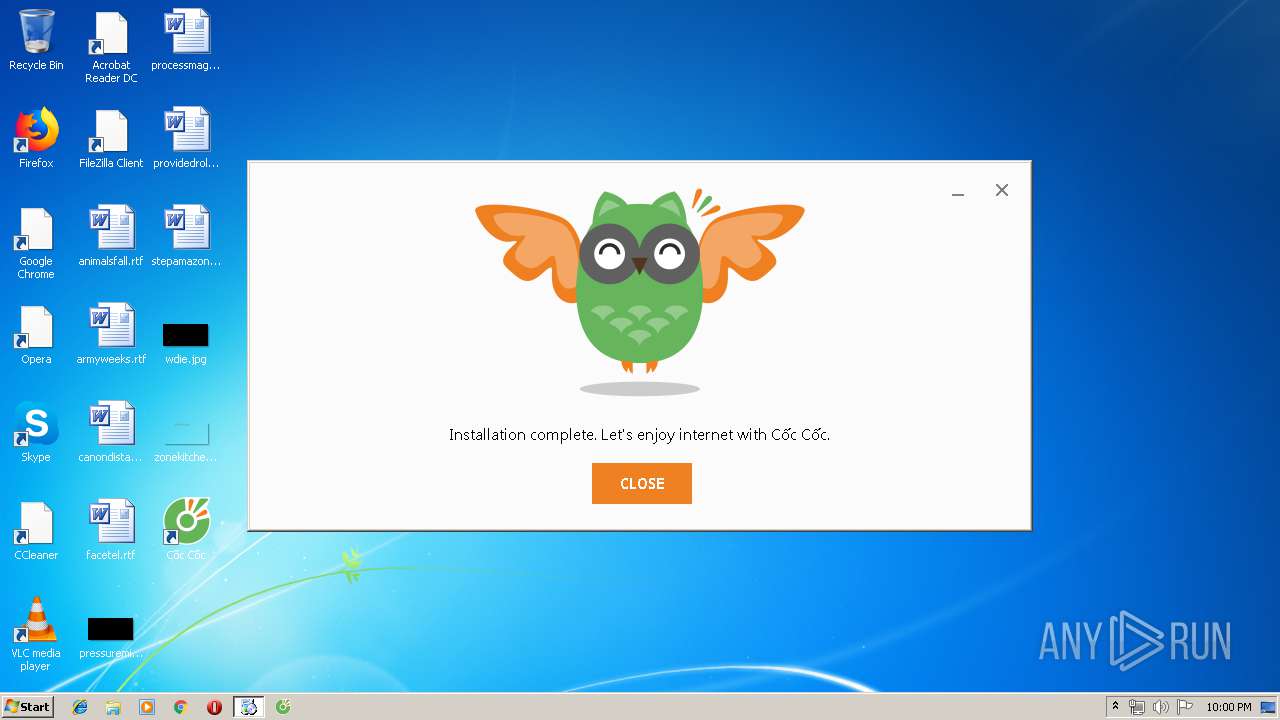
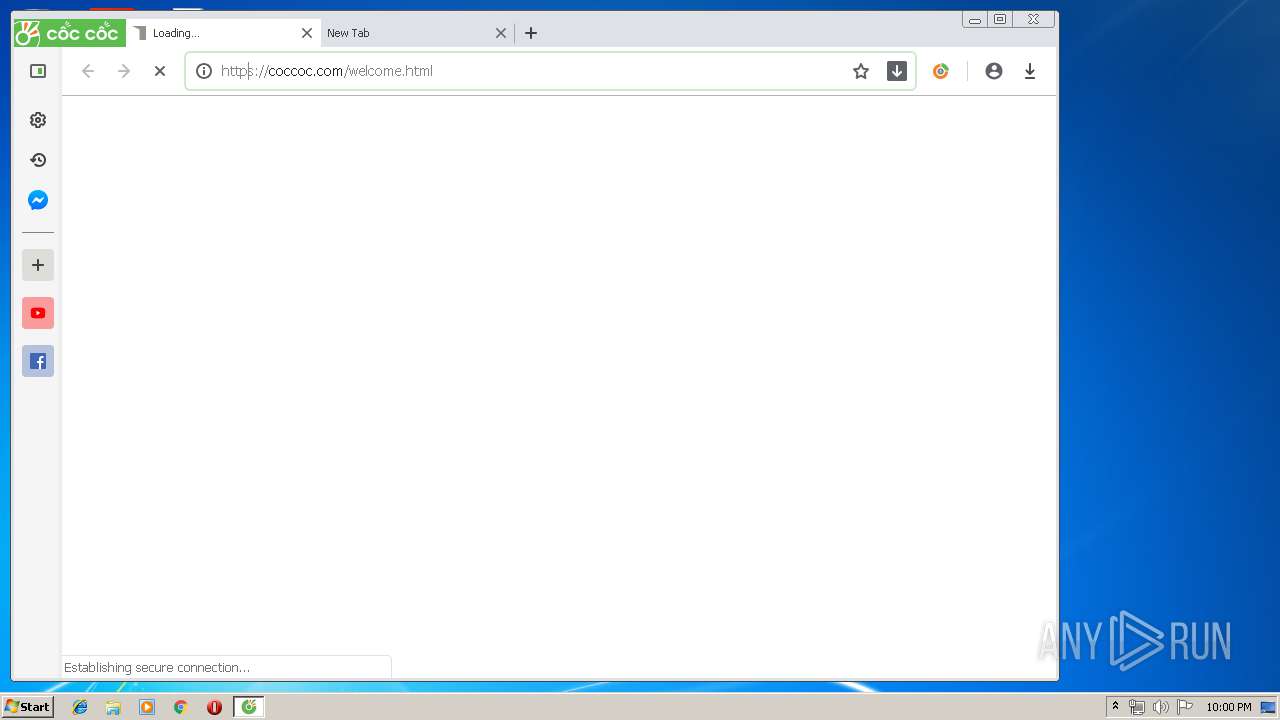
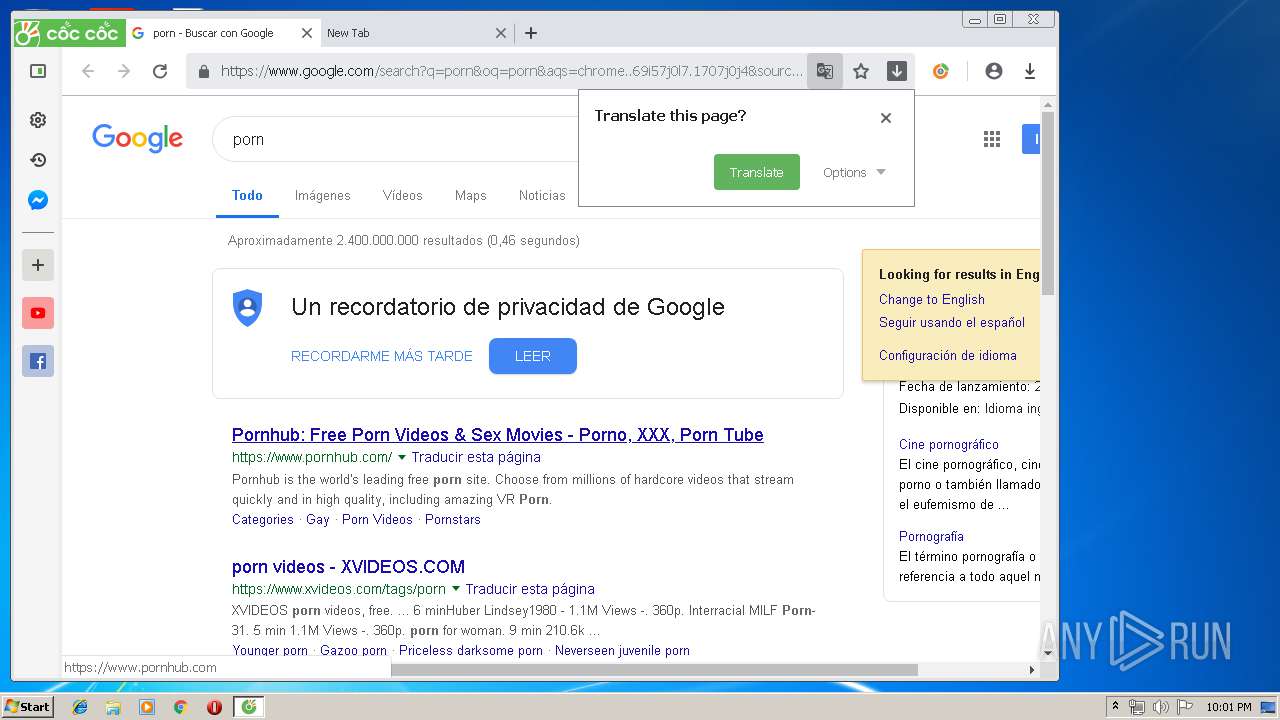
| URL: | http://coccoc.com/en/ |
| Full analysis: | https://app.any.run/tasks/706079c0-9f7d-4453-814f-7d71dfec55b8 |
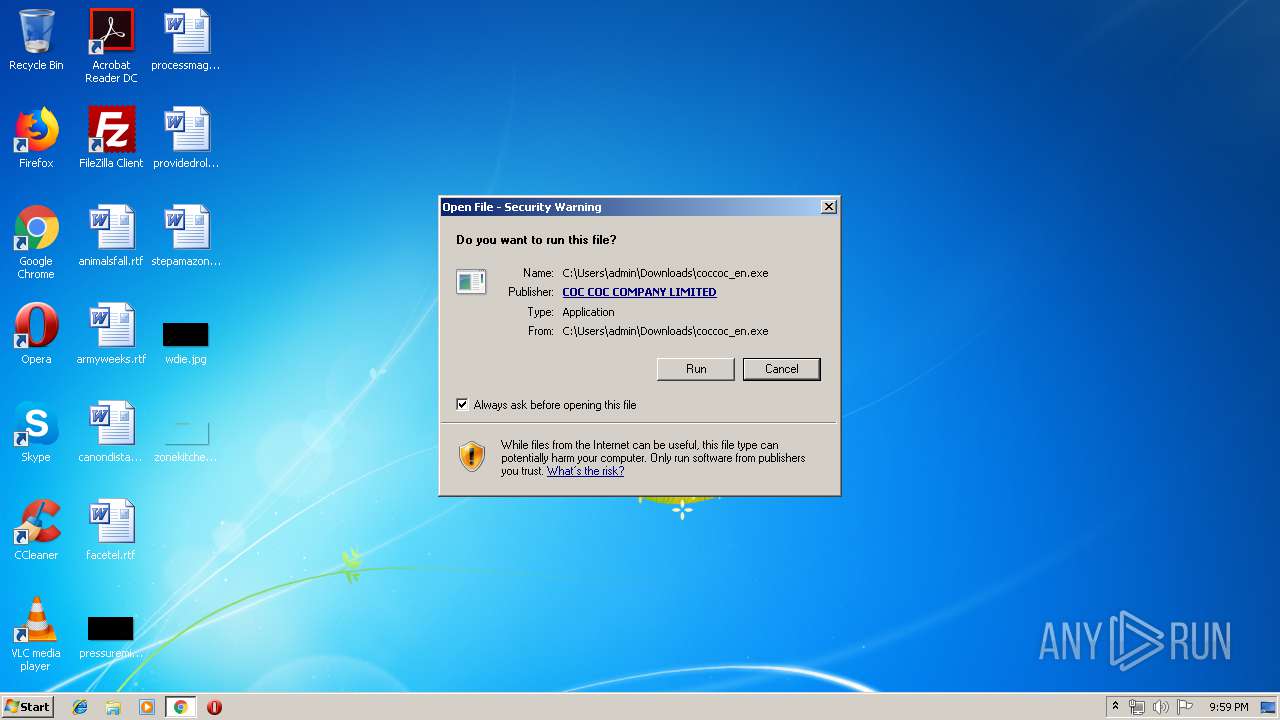
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2019, 20:58:26 |
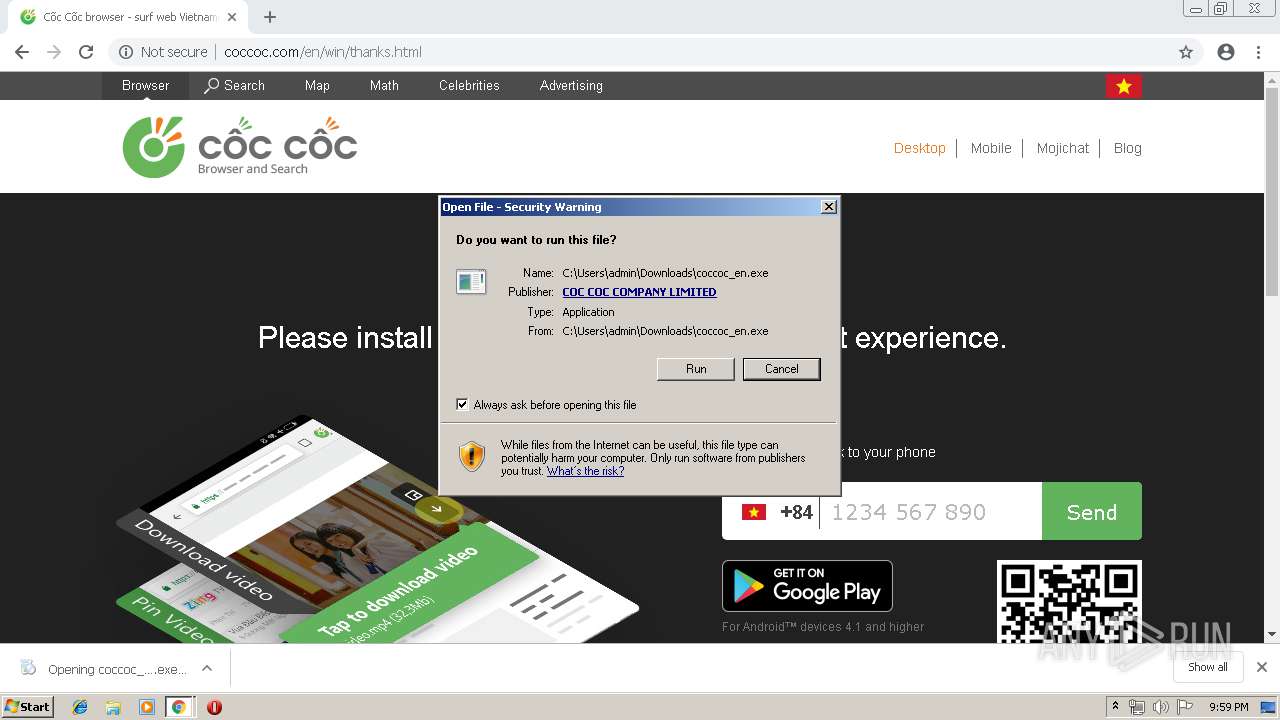
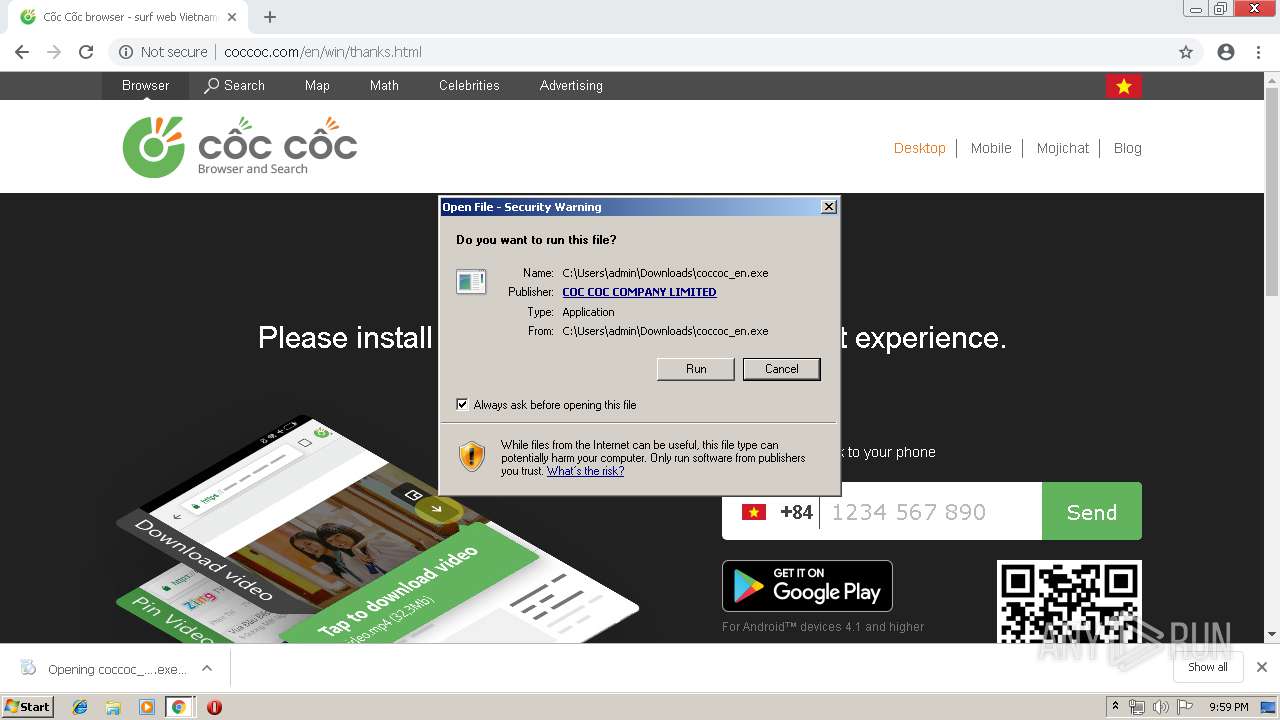
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C931C82286FD9AB6DFB4DE5DE9006522 |
| SHA1: | 766DD967606EBD7674E1769A3B61BF3A43363DD7 |
| SHA256: | 107F08940CD54D653B8F53FF716B759A52DCA3CB4460101A7925F500D340D890 |
| SSDEEP: | 3:N1KdKGGJGK3Fn:CIGiGun |
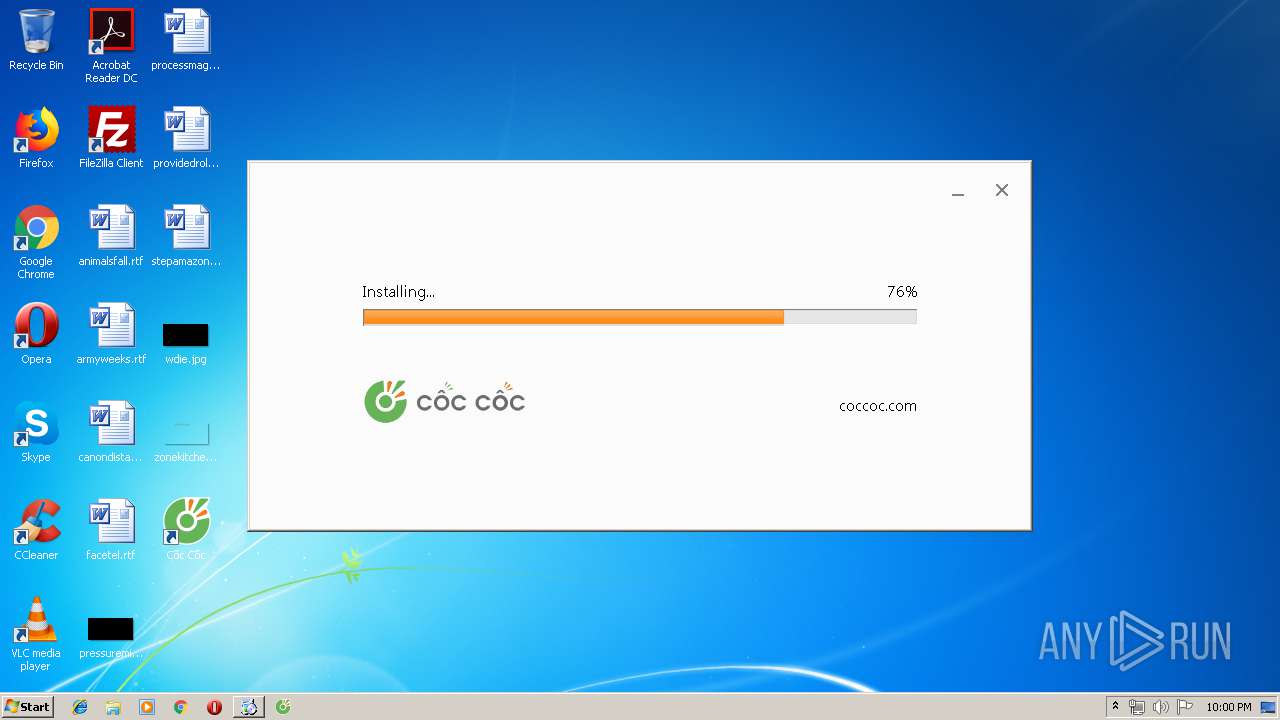
MALICIOUS
Changes the autorun value in the registry
- CocCocUpdate.exe (PID: 916)
- setup.exe (PID: 1500)
Loads the Task Scheduler COM API
- CocCocUpdate.exe (PID: 916)
Loads the Task Scheduler DLL interface
- CocCocUpdate.exe (PID: 916)
Application was dropped or rewritten from another process
- CocCocUpdate.exe (PID: 916)
- coccoc_en.exe (PID: 3656)
- CocCocUpdate.exe (PID: 2144)
- CocCocUpdate.exe (PID: 3264)
- CocCocUpdate.exe (PID: 3108)
- setup.exe (PID: 1924)
- setup.exe (PID: 1500)
- CocCocCrashHandler.exe (PID: 2404)
- setup.exe (PID: 3216)
- setup.exe (PID: 3408)
- browser.exe (PID: 3468)
- browser.exe (PID: 3180)
- CocCocUpdate.exe (PID: 3748)
- browser.exe (PID: 1644)
- browser.exe (PID: 3276)
- browser.exe (PID: 3864)
- browser.exe (PID: 3652)
- browser.exe (PID: 2540)
- browser.exe (PID: 2316)
- browser.exe (PID: 756)
- browser.exe (PID: 2108)
- browser.exe (PID: 2500)
- browser.exe (PID: 2512)
- browser.exe (PID: 2772)
- browser.exe (PID: 3304)
- browser.exe (PID: 1864)
- browser.exe (PID: 2980)
- browser.exe (PID: 2352)
- browser.exe (PID: 3240)
- browser.exe (PID: 2688)
- browser.exe (PID: 1032)
- browser.exe (PID: 2716)
- browser.exe (PID: 3704)
- browser.exe (PID: 832)
- browser.exe (PID: 1700)
- browser.exe (PID: 2156)
- browser.exe (PID: 3912)
- browser.exe (PID: 1740)
- browser.exe (PID: 3316)
- browser.exe (PID: 3380)
- browser.exe (PID: 3116)
- browser.exe (PID: 2820)
- browser.exe (PID: 3096)
- browser.exe (PID: 3840)
- browser.exe (PID: 2436)
- browser.exe (PID: 3188)
- browser.exe (PID: 2332)
- browser.exe (PID: 2104)
- browser.exe (PID: 4028)
- browser.exe (PID: 2740)
Loads dropped or rewritten executable
- CocCocUpdate.exe (PID: 3108)
- CocCocUpdate.exe (PID: 916)
- CocCocUpdate.exe (PID: 2144)
- CocCocUpdate.exe (PID: 3264)
- browser.exe (PID: 3180)
- browser.exe (PID: 3468)
- browser.exe (PID: 3276)
- CocCocUpdate.exe (PID: 3748)
- browser.exe (PID: 1644)
- browser.exe (PID: 2540)
- browser.exe (PID: 3652)
- browser.exe (PID: 3864)
- browser.exe (PID: 2740)
- browser.exe (PID: 2316)
- browser.exe (PID: 756)
- browser.exe (PID: 2108)
- browser.exe (PID: 2500)
- browser.exe (PID: 2512)
- browser.exe (PID: 3304)
- browser.exe (PID: 1864)
- browser.exe (PID: 2980)
- browser.exe (PID: 2772)
- browser.exe (PID: 2352)
- browser.exe (PID: 3240)
- browser.exe (PID: 2688)
- browser.exe (PID: 2716)
- browser.exe (PID: 832)
- browser.exe (PID: 1032)
- browser.exe (PID: 3704)
- browser.exe (PID: 1700)
- browser.exe (PID: 2156)
- browser.exe (PID: 3912)
- browser.exe (PID: 1740)
- browser.exe (PID: 3316)
- browser.exe (PID: 2820)
- browser.exe (PID: 3380)
- browser.exe (PID: 3096)
- browser.exe (PID: 3116)
- browser.exe (PID: 3840)
- browser.exe (PID: 3188)
- browser.exe (PID: 2436)
- browser.exe (PID: 2332)
- browser.exe (PID: 4028)
SUSPICIOUS
Creates files in the user directory
- CocCocUpdate.exe (PID: 916)
- setup.exe (PID: 1500)
- browser.exe (PID: 3180)
Executable content was dropped or overwritten
- chrome.exe (PID: 2228)
- CocCocUpdate.exe (PID: 916)
- chrome.exe (PID: 1476)
- coccoc_en.exe (PID: 3656)
- 72.0.3626.136_coccocsetup.exe (PID: 2296)
- setup.exe (PID: 1500)
Creates COM task schedule object
- CocCocUpdate.exe (PID: 3108)
Creates files in the Windows directory
- CocCocUpdate.exe (PID: 916)
Starts itself from another location
- CocCocUpdate.exe (PID: 916)
- setup.exe (PID: 1500)
Creates a software uninstall entry
- setup.exe (PID: 1500)
Application launched itself
- setup.exe (PID: 1500)
- CocCocUpdate.exe (PID: 3264)
- browser.exe (PID: 3180)
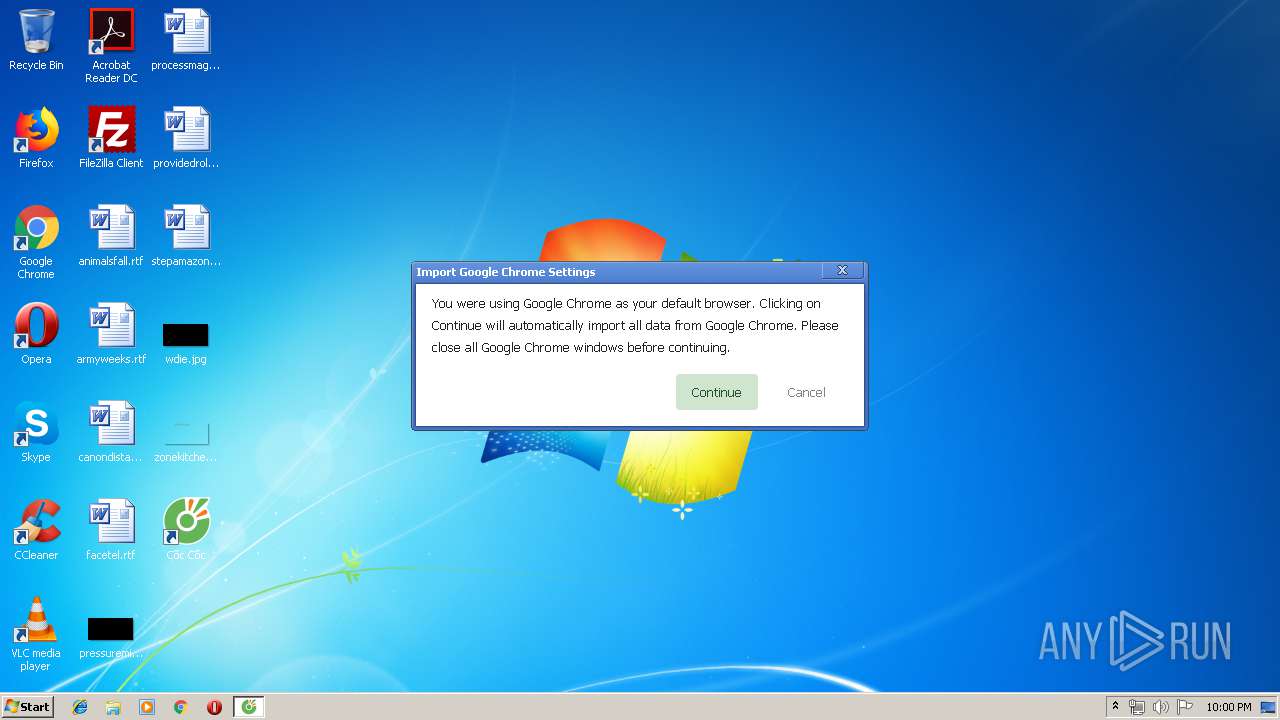
Modifies the open verb of a shell class
- setup.exe (PID: 1500)
- setup.exe (PID: 3408)
INFO
Application launched itself
- chrome.exe (PID: 1476)
Dropped object may contain TOR URL's
- chrome.exe (PID: 1476)
Dropped object may contain Bitcoin addresses
- setup.exe (PID: 1500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
113
Monitored processes
76
Malicious processes
20
Suspicious processes
20
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 756 | "C:\Users\admin\AppData\Local\CocCoc\Browser\Application\browser.exe" --type=utility --field-trial-handle=900,12282213321513558243,15121057333651143142,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16492760495948927238 --mojo-platform-channel-handle=3920 --ignored=" --type=renderer " /prefetch:8 | C:\Users\admin\AppData\Local\CocCoc\Browser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: Coc Coc Co., Ltd. Integrity Level: LOW Description: CocCoc Exit code: 0 Version: 72.0.3626.136 Modules
| |||||||||||||||
| 832 | "C:\Users\admin\AppData\Local\CocCoc\Browser\Application\browser.exe" --type=renderer --field-trial-handle=900,12282213321513558243,15121057333651143142,131072 --disable-gpu-compositing --service-pipe-token=4808869543572969672 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4808869543572969672 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5544 /prefetch:1 | C:\Users\admin\AppData\Local\CocCoc\Browser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: Coc Coc Co., Ltd. Integrity Level: LOW Description: CocCoc Exit code: 0 Version: 72.0.3626.136 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,11803774206547213923,26424685011001398,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14269718683485427037 --mojo-platform-channel-handle=4180 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,11803774206547213923,26424685011001398,131072 --enable-features=PasswordImport --service-pipe-token=10318226432789589661 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10318226432789589661 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 916 | C:\Users\admin\AppData\Local\Temp\GUMC797.tmp\CocCocUpdate.exe /installsource taggedmi /install "appguid={C0CC0CBB-47DD-46FF-A04D-7011A06486E1}&appname=C%E1%BB%91c%20C%E1%BB%91c&needsadmin=false&lang=en&client={00000000-0000-0000-0000-000000000000}&brand=XXXX" | C:\Users\admin\AppData\Local\Temp\GUMC797.tmp\CocCocUpdate.exe | coccoc_en.exe | ||||||||||||
User: admin Company: Coc Coc Co., Ltd. Integrity Level: MEDIUM Description: CocCoc Update Exit code: 0 Version: 2.5.15.103 Modules
| |||||||||||||||
| 1032 | "C:\Users\admin\AppData\Local\CocCoc\Browser\Application\browser.exe" --type=renderer --field-trial-handle=900,12282213321513558243,15121057333651143142,131072 --disable-gpu-compositing --service-pipe-token=11194038459942261554 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11194038459942261554 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5608 /prefetch:1 | C:\Users\admin\AppData\Local\CocCoc\Browser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: Coc Coc Co., Ltd. Integrity Level: LOW Description: CocCoc Exit code: 0 Version: 72.0.3626.136 Modules
| |||||||||||||||
| 1208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,11803774206547213923,26424685011001398,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10527586866431337215 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10527586866431337215 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://coccoc.com/en/ | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1500 | "C:\Users\admin\AppData\Local\Temp\CR_A7FBA.tmp\setup.exe" --install-archive="C:\Users\admin\AppData\Local\Temp\CR_A7FBA.tmp\BROWSER.PACKED.7Z" --verbose-logging --do-not-launch-chrome --do-not-launch-chrome --make-coccoc-default --auto-launch-coccoc --make-torrent-client --force-add-firewall-rules | C:\Users\admin\AppData\Local\Temp\CR_A7FBA.tmp\setup.exe | 72.0.3626.136_coccocsetup.exe | ||||||||||||
User: admin Company: Coc Coc Co., Ltd. Integrity Level: MEDIUM Description: Coc Coc Installer Exit code: 0 Version: 72.0.3626.136 Modules
| |||||||||||||||
| 1644 | "C:\Users\admin\AppData\Local\CocCoc\Browser\Application\browser.exe" --type=renderer --field-trial-handle=900,12282213321513558243,15121057333651143142,131072 --service-pipe-token=7136260584755284380 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7136260584755284380 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1876 /prefetch:1 | C:\Users\admin\AppData\Local\CocCoc\Browser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: Coc Coc Co., Ltd. Integrity Level: LOW Description: CocCoc Exit code: 0 Version: 72.0.3626.136 Modules
| |||||||||||||||
Total events
5 244
Read events
2 461
Write events
2 764
Delete events
19
Modification events
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1476-13199749122159875 |
Value: 259 | |||
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1476) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
41
Suspicious files
209
Text files
538
Unknown types
63
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1fd514b2-b2df-43fa-8582-359af64ed3a4.tmp | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
72
TCP/UDP connections
172
DNS requests
111
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2228 | chrome.exe | GET | 200 | 104.108.60.107:80 | http://d-track.send.microadinc.com/bl_track_with_gcm.cgi?co_account_id=12827&group=&country_id=5&ver=2.1.0&referrer=&cbt=90f591c25f4ad8016a1da532e9 | NL | — | — | suspicious |
2228 | chrome.exe | GET | 200 | 123.30.175.29:80 | http://coccoc.com/themes/default/browser/img/en/coccoc-feature.png | VN | image | 39.4 Kb | whitelisted |
2228 | chrome.exe | GET | 200 | 123.30.175.29:80 | http://coccoc.com/themes/default/browser/min/browser-min.js?1554715743 | VN | text | 50.0 Kb | whitelisted |
2228 | chrome.exe | GET | 200 | 123.30.175.29:80 | http://coccoc.com/themes/default/browser/img/vi/b3.png | VN | image | 35.5 Kb | whitelisted |
2228 | chrome.exe | GET | 200 | 123.30.175.29:80 | http://coccoc.com/themes/default/browser/img/vi/b2.png | VN | image | 11.9 Kb | whitelisted |
2228 | chrome.exe | GET | 200 | 123.30.175.29:80 | http://coccoc.com/themes/default/browser/img/vi/b1.png | VN | image | 14.1 Kb | whitelisted |
2228 | chrome.exe | GET | 200 | 123.30.175.29:80 | http://coccoc.com/themes/default/browser/img/vi/b4.png | VN | image | 26.2 Kb | whitelisted |
2228 | chrome.exe | GET | 200 | 123.30.175.29:80 | http://coccoc.com/themes/default/browser/min/browser.png?3dfef5905d3e50a2b7d79229c2c67816 | VN | image | 214 Kb | whitelisted |
2228 | chrome.exe | GET | 200 | 123.30.175.29:80 | http://coccoc.com/themes/default/browser/min/browser-min.css?1554715794 | VN | text | 11.6 Kb | whitelisted |
2228 | chrome.exe | GET | 200 | 123.30.175.29:80 | http://coccoc.com/themes/default/browser/img/bg.jpg | VN | image | 25.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2228 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
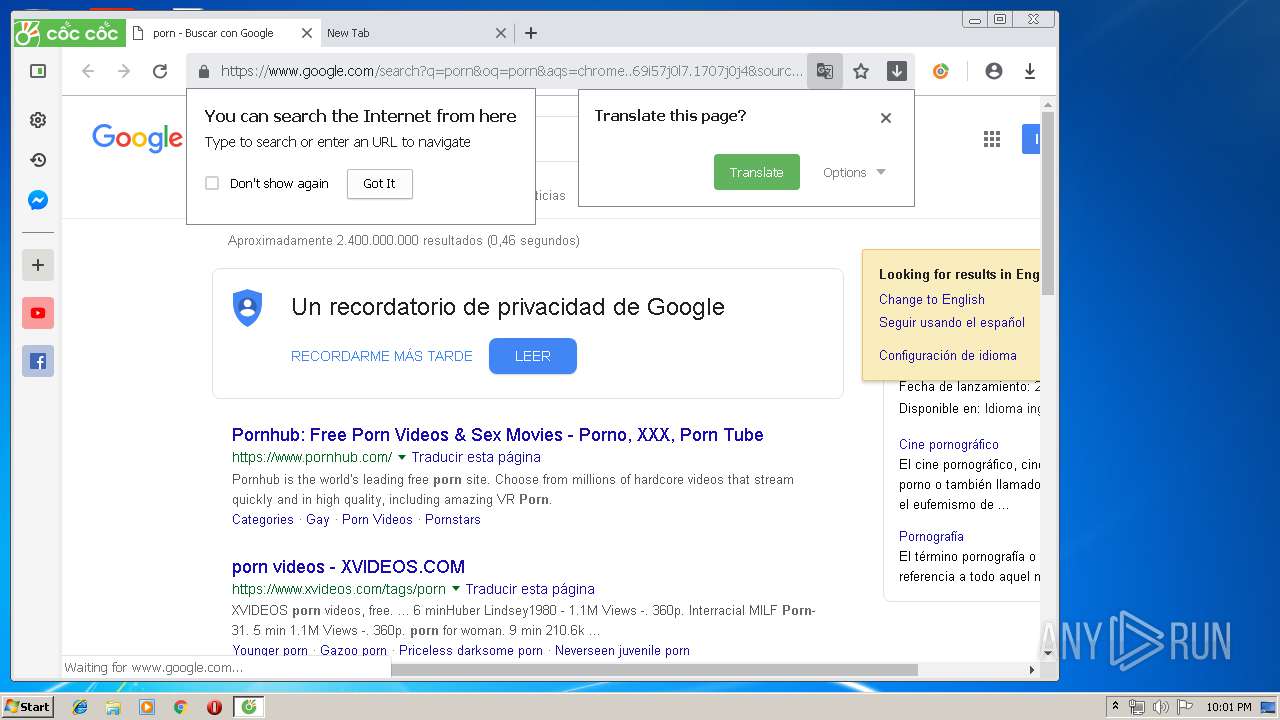
2228 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 216.58.208.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 172.217.23.142:443 | www.youtube.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 31.13.90.36:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
2228 | chrome.exe | 172.217.18.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 13.32.219.75:80 | d-cache.microadinc.com | Amazon.com, Inc. | US | unknown |
2228 | chrome.exe | 204.79.197.200:443 | bat.bing.com | Microsoft Corporation | US | whitelisted |
2228 | chrome.exe | 172.217.16.142:443 | www.youtube.com | Google Inc. | US | whitelisted |
2228 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
coccoc.com |
| whitelisted |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
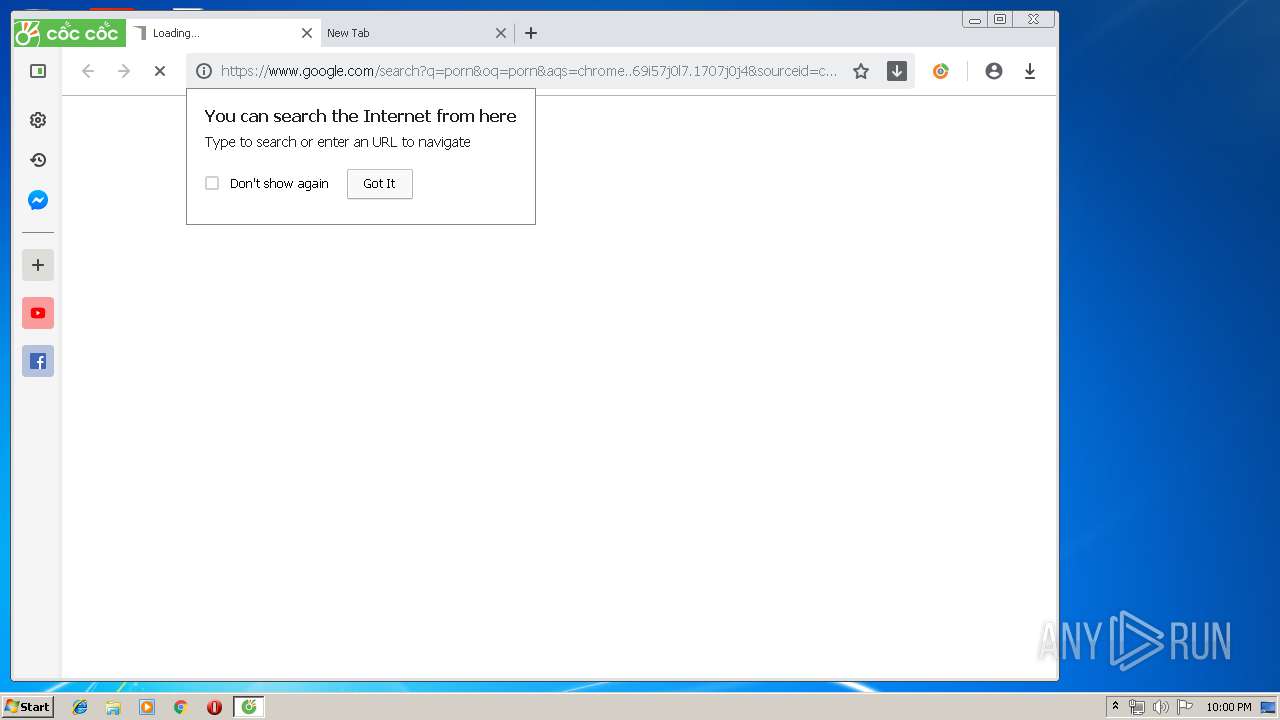
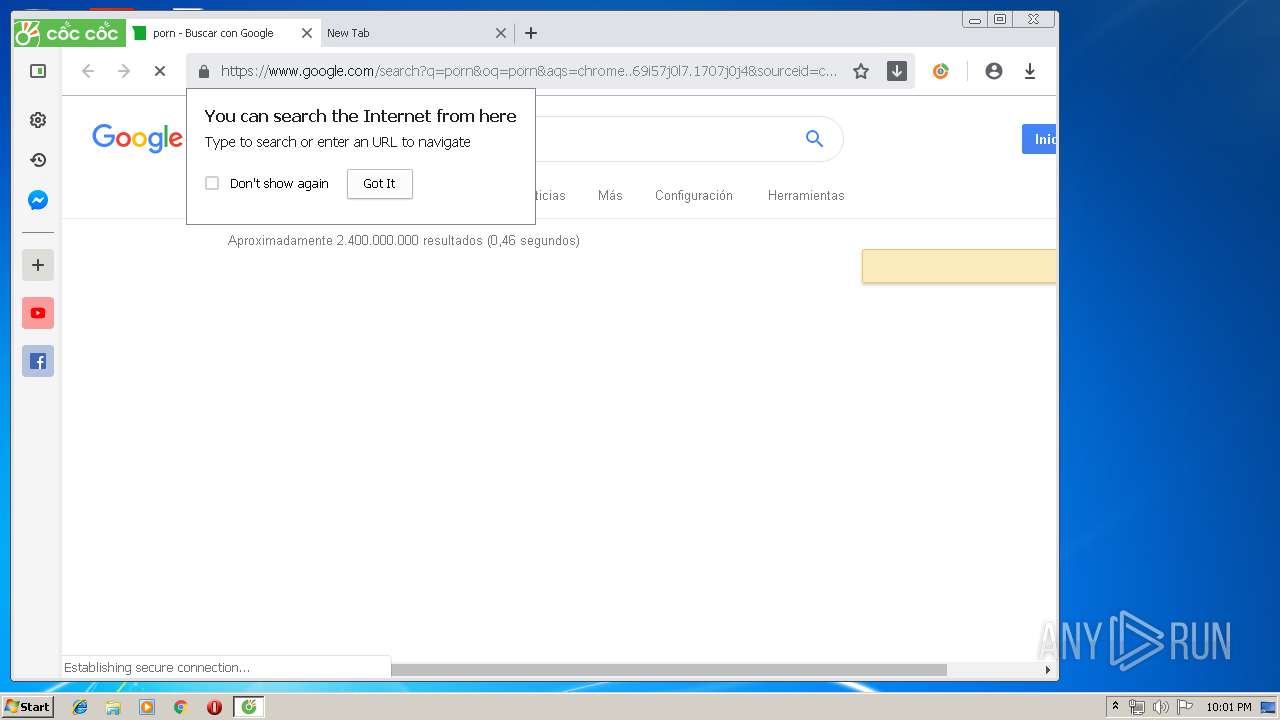
www.google.com |
| malicious |
www.googletagmanager.com |
| whitelisted |
www.youtube.com |
| whitelisted |
topbar.coccoc.com |
| unknown |
www.facebook.com |
| whitelisted |
blog.coccoc.com |
| unknown |
itunes.apple.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3180 | browser.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
3180 | browser.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
1 ETPRO signatures available at the full report