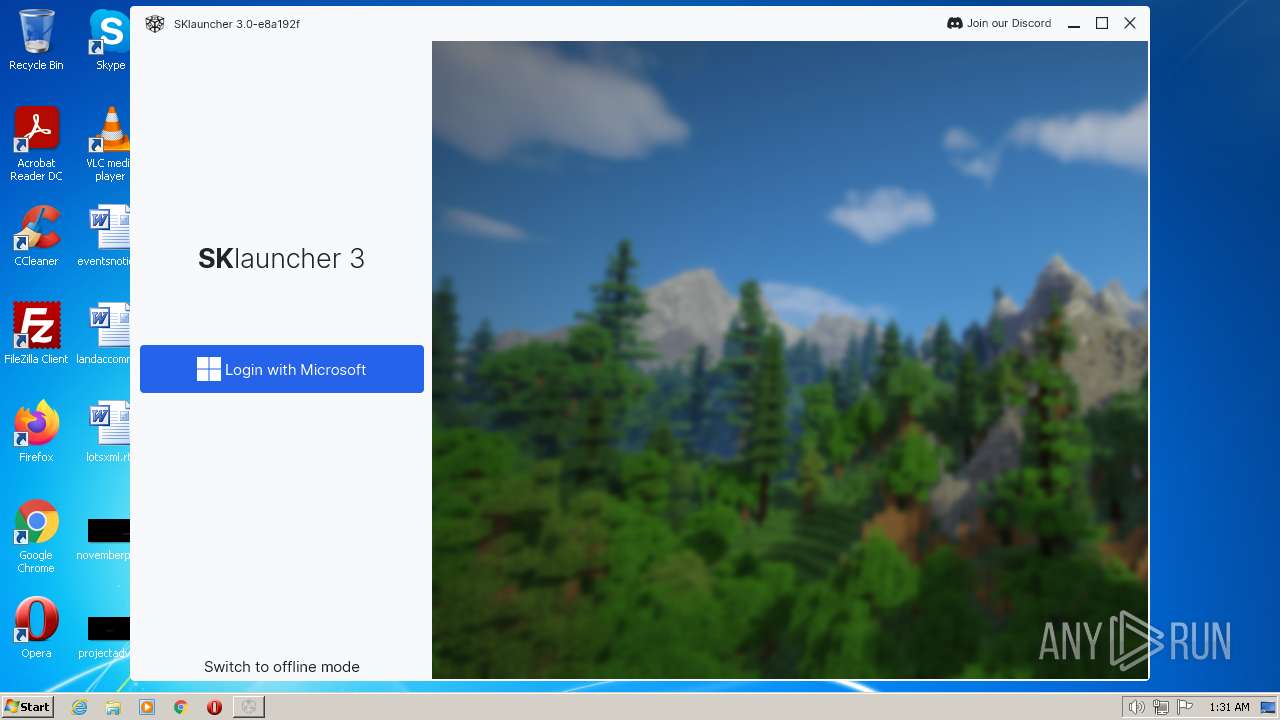
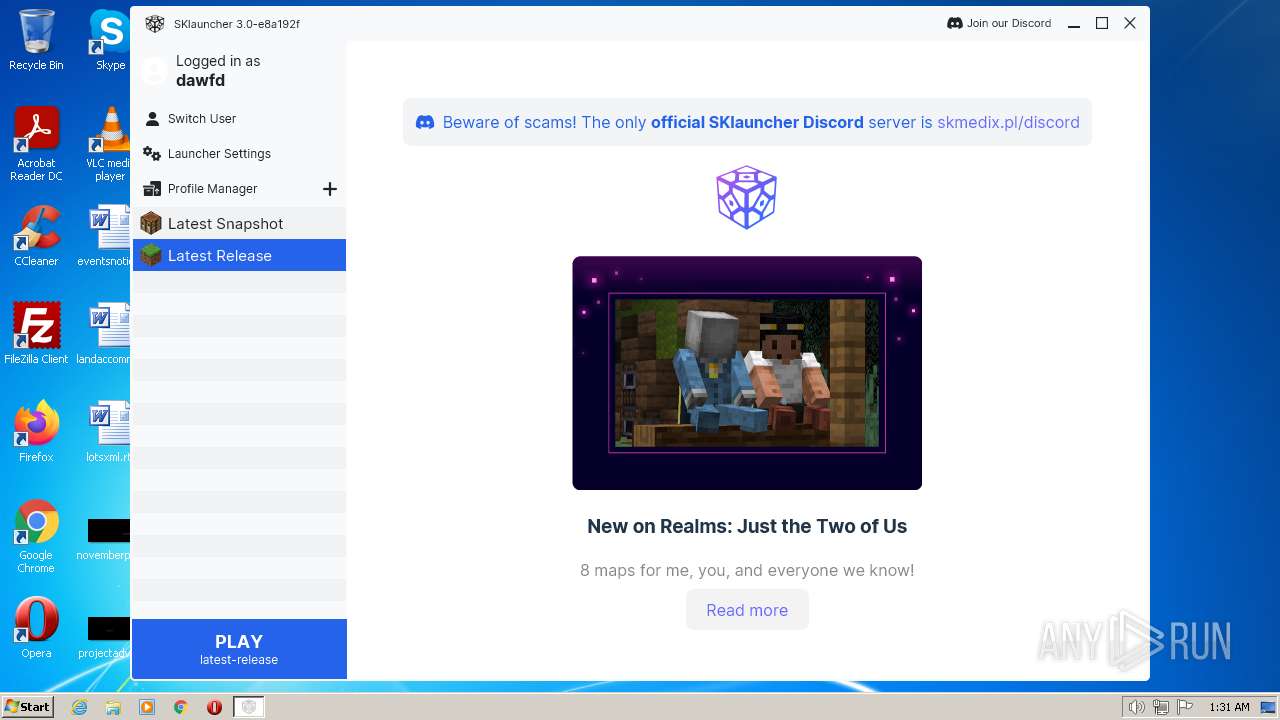
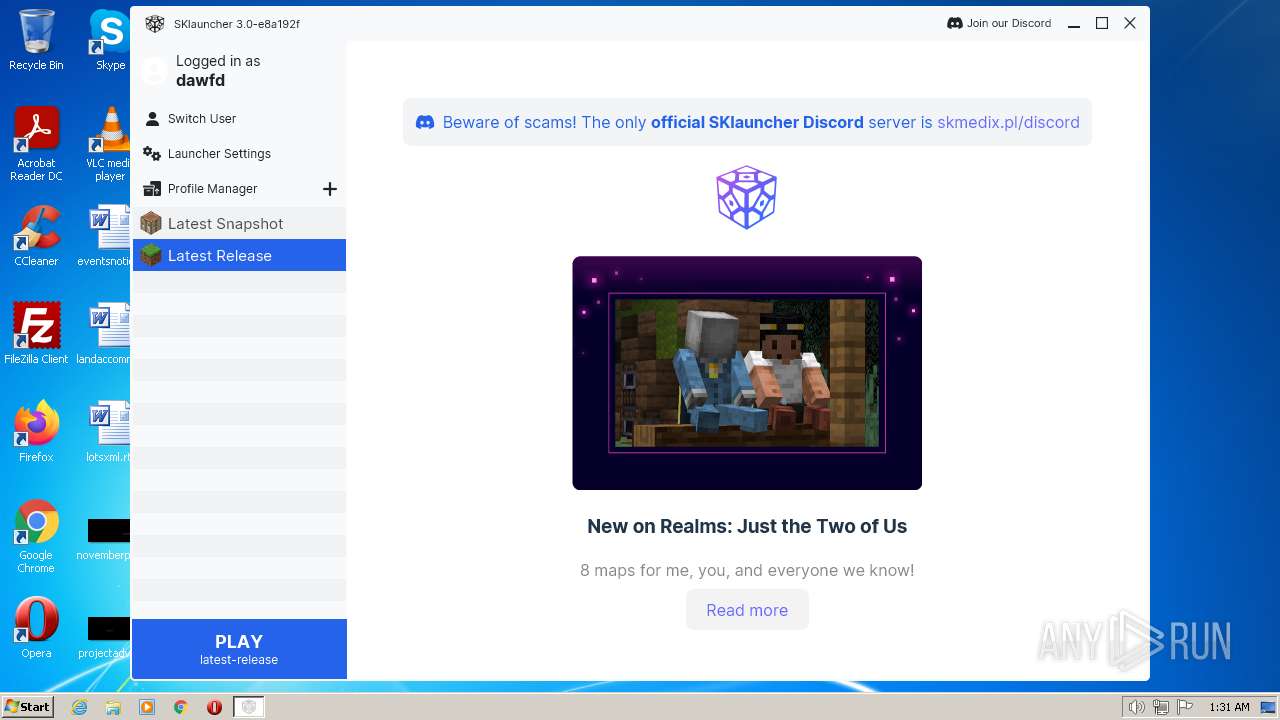
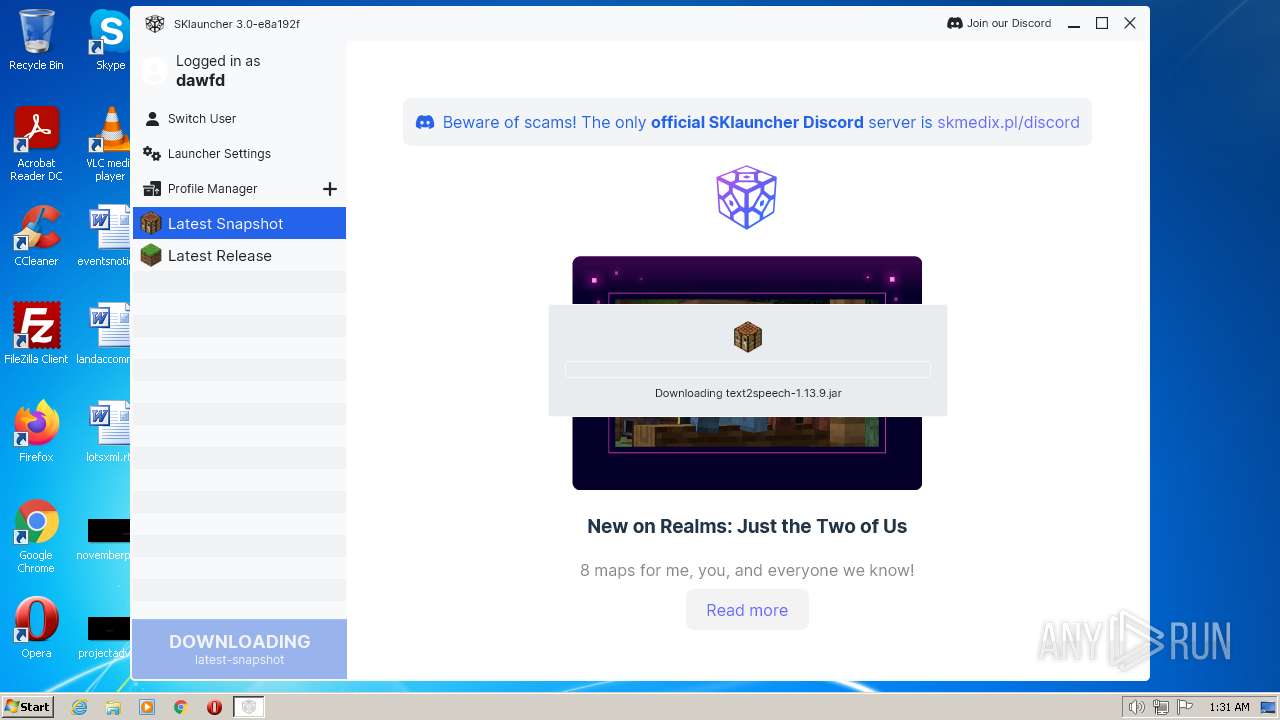
| File name: | SKlauncher 3.0.exe |
| Full analysis: | https://app.any.run/tasks/6bafeb8b-05f8-416b-9096-ddd17dd02068 |
| Verdict: | Malicious activity |
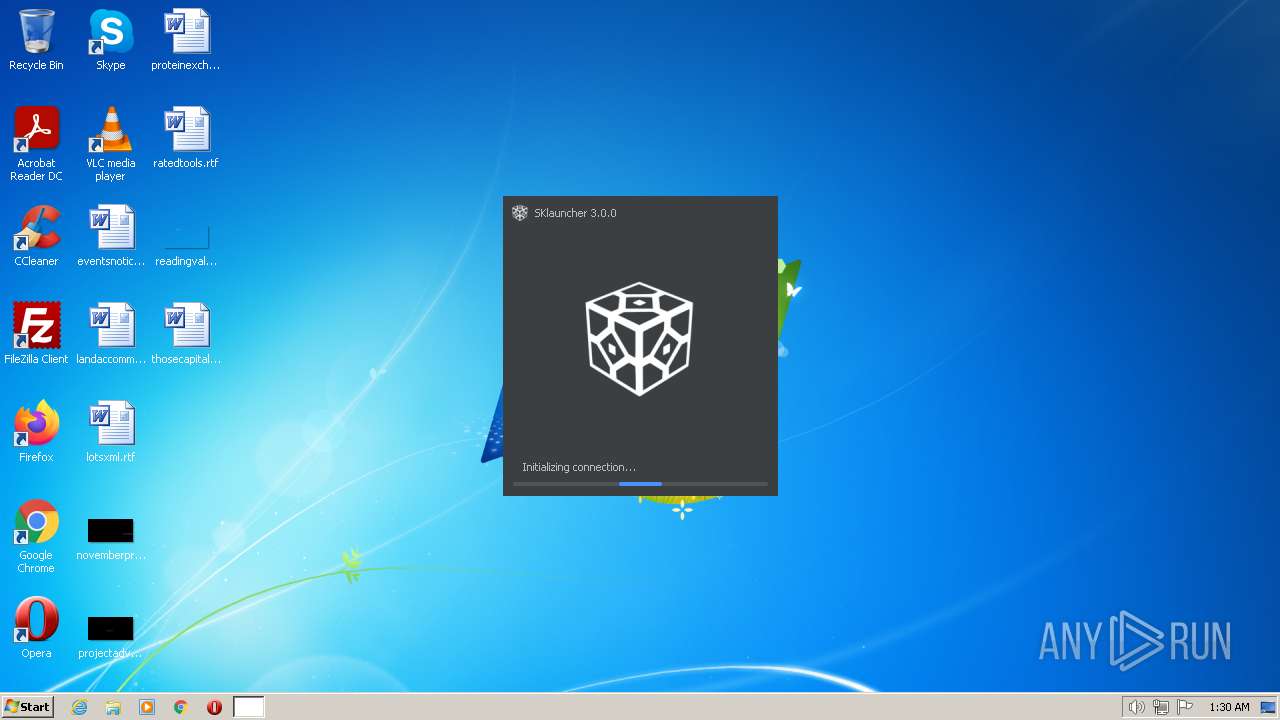
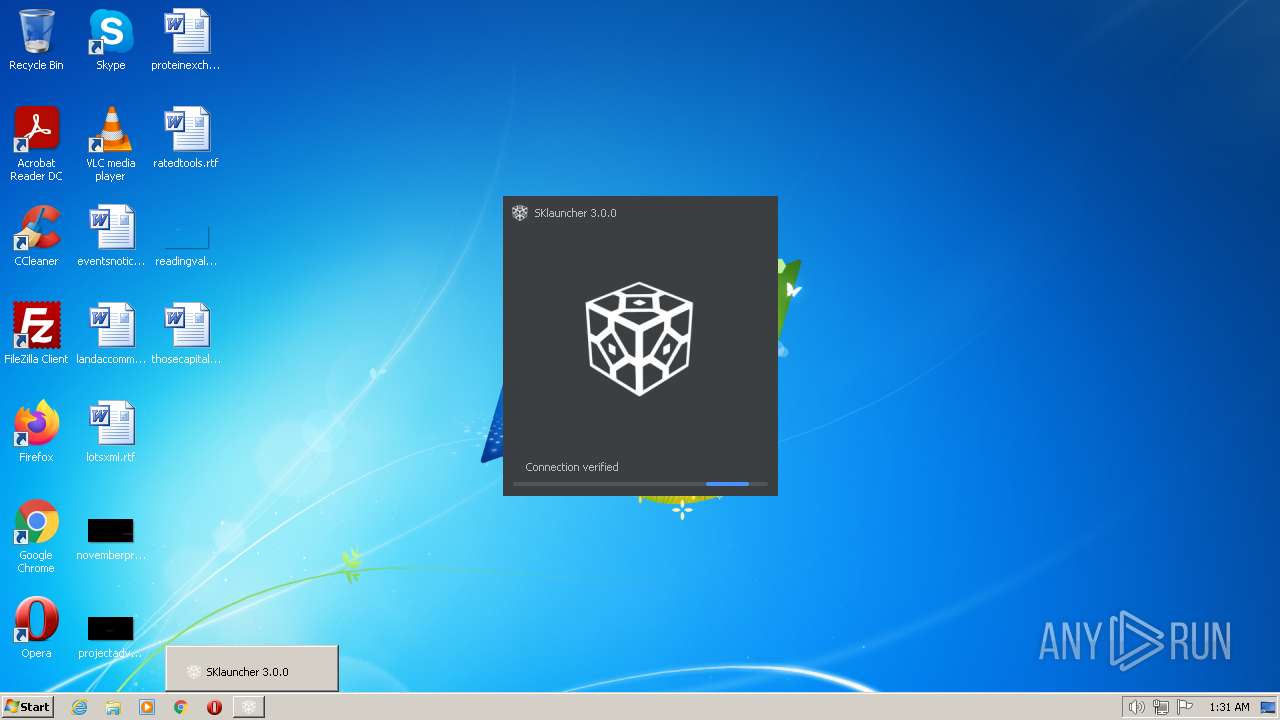
| Analysis date: | February 26, 2023, 01:30:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 32C7E3347F8E532E675D154EB07F4CCF |
| SHA1: | 5CA004745E2CDAB497A7D6EF29C7EFB25DC4046D |
| SHA256: | 107BB526C374D6FD9F45317C0C16E83AB50076F2BCD630CAF3D6794596FAE69B |
| SSDEEP: | 24576:Dh199z42ojP6a7HJlF9eu5XFQZSIZeNGdmEE8H17UBcegl:R9zbgH3euNFQZr/oEE892cfl |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks for Java to be installed
- SKlauncher 3.0.exe (PID: 3452)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 3600)
Process downloads binary or script
- javaw.exe (PID: 3600)
Process requests binary or script from the Internet
- javaw.exe (PID: 3600)
INFO
Checks supported languages
- SKlauncher 3.0.exe (PID: 3452)
- javaw.exe (PID: 3600)
Reads the computer name
- javaw.exe (PID: 3600)
Creates files in the program directory
- javaw.exe (PID: 3600)
The process checks LSA protection
- icacls.exe (PID: 3084)
- javaw.exe (PID: 3600)
Create files in a temporary directory
- javaw.exe (PID: 3600)
Reads the machine GUID from the registry
- javaw.exe (PID: 3600)
Creates files or folders in the user directory
- javaw.exe (PID: 3600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductVersion: | 3 |
|---|---|
| ProductName: | SKlauncher |
| OriginalFileName: | SKlauncher 3.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Mojang |
| InternalName: | SKlauncher |
| FileVersion: | 3 |
| FileDescription: | The Minecraft Launcher |
| CompanyName: | - |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 3.0.0.0 |
| FileVersionNumber: | 3.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x1590 |
| UninitializedDataSize: | 36352 |
| InitializedDataSize: | 134144 |
| CodeSize: | 23040 |
| LinkerVersion: | 2.22 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| TimeStamp: | 2022:11:23 21:53:50+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Nov-2022 21:53:50 |
| Detected languages: |
|
| TLS Callbacks: | 2 callback(s) detected. |
| CompanyName: | - |
| FileDescription: | The Minecraft Launcher |
| FileVersion: | 3.0 |
| InternalName: | SKlauncher |
| LegalCopyright: | Mojang |
| LegalTrademarks: | - |
| OriginalFilename: | SKlauncher 3.exe |
| ProductName: | SKlauncher |
| ProductVersion: | 3.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 23-Nov-2022 21:53:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005970 | 0x00005A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.17063 |
.data | 0x00007000 | 0x00000010 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.11837 |
.rdata | 0x00008000 | 0x00000918 | 0x00000A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.27517 |
.eh_fram\x14\x11 | 0x00009000 | 0x00001114 | 0x00001200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.82235 |
.bss | 0x0000B000 | 0x00008DCC | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00014000 | 0x00000CC0 | 0x00000E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.91037 |
.CRT | 0x00015000 | 0x00000018 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0980042 |
.tls | 0x00016000 | 0x00000020 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.231158 |
.rsrc | 0x00017000 | 0x0001DBA4 | 0x0001DC00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.59488 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.22078 | 712 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 2.72548 | 9 | UNKNOWN | Process Default Language | RT_RCDATA |
3 | 2.21658 | 16936 | UNKNOWN | Process Default Language | RT_ICON |
4 | 2.50989 | 9640 | UNKNOWN | Process Default Language | RT_ICON |
5 | 2.61209 | 4264 | UNKNOWN | Process Default Language | RT_ICON |
6 | 2.73885 | 1128 | UNKNOWN | Process Default Language | RT_ICON |
10 | 3.61687 | 17 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
advapi32.dll |
kernel32.dll |
msvcrt.dll |
shell32.dll |
user32.dll |
Total processes
42
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1400 | cmd /c reg query HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize /v AppsUseLightTheme | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3084 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3452 | "C:\Users\admin\AppData\Local\Temp\SKlauncher 3.0.exe" | C:\Users\admin\AppData\Local\Temp\SKlauncher 3.0.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: The Minecraft Launcher Exit code: 0 Version: 3.0 Modules
| |||||||||||||||
| 3456 | reg query HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize /v AppsUseLightTheme | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3600 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -Xms32m -Xmx256m -jar "C:\Users\admin\AppData\Local\Temp\SKlauncher 3.0.exe" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | SKlauncher 3.0.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
Total events
1 594
Read events
1 590
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3600) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
30
Suspicious files
34
Text files
16
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3600 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher\sklauncher.pack | — | |
MD5:— | SHA256:— | |||
| 3600 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:B3569B90E3477F689E82C02BEB2DCBC0 | SHA256:E8697404A5E10D60C92BE131CB6D843FD04C7B6B2EF27A6E216B11A191ABFEA3 | |||
| 3600 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher-fx.jar | compressed | |
MD5:F38573AE88BBF1274E8C8234FA58F4FB | SHA256:F93C126504D905E77FDC988F76D5031F4255A4B6A027EFE43BCADAC05977E3B5 | |||
| 3600 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio5942703897425643872.tmp | image | |
MD5:4BC22D05B225A34A3DDB4F17D2469B77 | SHA256:FACE76C9C4FAD9476A1D80483D41772C805808A1383012B1C22065E30D32EDE6 | |||
| 3600 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF669606820079986543.tmp | pi2 | |
MD5:52355593E805F6C172BFDC156A39A031 | SHA256:529BE850E06F62F8904F22BDA77E45BDE4834498FDBEC4FF4201FA3177447A3A | |||
| 3600 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher\sklauncher.vmoptions | text | |
MD5:3EDB37854568C0FD14D5C5A023935D13 | SHA256:EDF8639AD0FE09DFC08F18FF0424ED6E2C0F09047956EA65C2318362986649FE | |||
| 3600 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher\sklauncher_data.bin | text | |
MD5:C4AD3B656E974093272CBF73D1A0883A | SHA256:AFB8207711104BA2750E80244F1109D626ACB2D329D3A66A61824E20B6A711CE | |||
| 3600 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF2817512326042122430.tmp | pi2 | |
MD5:C10484D6B9BE5C545CF20FFDBE27ECB2 | SHA256:D253C410F4D0FD7F16D7B2ECAEA19B60FB877CB94F5B2752FDA272A3A86FA908 | |||
| 3600 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF873880936163165123.tmp | pi2 | |
MD5:BFD684D243ED4A7AA6CA778841D78257 | SHA256:2188C12B90E2970F97ADF7D4946E06EACA8FD3CF1566CAE60CFC72135781AA1F | |||
| 3600 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF6254923803590415119.tmp | pi2 | |
MD5:52355593E805F6C172BFDC156A39A031 | SHA256:529BE850E06F62F8904F22BDA77E45BDE4834498FDBEC4FF4201FA3177447A3A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
33
DNS requests
12
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3600 | javaw.exe | GET | 200 | 185.199.109.153:80 | http://beta.skmedix.pl/?dark=false&lang=en-US&perf=false | NL | html | 301 b | malicious |
3600 | javaw.exe | GET | 200 | 185.199.109.153:80 | http://beta.skmedix.pl/assets/index-694b8d6e.js | NL | text | 66.0 Kb | malicious |
3600 | javaw.exe | GET | 200 | 185.199.109.153:80 | http://beta.skmedix.pl/assets/index-8e5899e4.css | NL | text | 1.80 Kb | malicious |
3600 | javaw.exe | GET | 200 | 185.199.109.153:80 | http://beta.skmedix.pl/skl.svg | NL | image | 2.14 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3600 | javaw.exe | 185.199.109.153:80 | beta.skmedix.pl | FASTLY | US | shared |
3600 | javaw.exe | 104.16.249.249:443 | cloudflare-dns.com | CLOUDFLARENET | — | shared |
3600 | javaw.exe | 13.107.237.45:443 | sessionserver.mojang.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3600 | javaw.exe | 13.107.228.27:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3600 | javaw.exe | 104.192.141.1:443 | bitbucket.org | AMAZON-02 | US | suspicious |
3600 | javaw.exe | 188.114.96.3:443 | files.skmedix.pl | CLOUDFLARENET | NL | malicious |
3600 | javaw.exe | 142.250.185.206:443 | www.google-analytics.com | GOOGLE | US | whitelisted |
3600 | javaw.exe | 3.5.16.151:443 | bbuseruploads.s3.amazonaws.com | AMAZON-AES | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
files.skmedix.pl |
| malicious |
bitbucket.org |
| shared |
bbuseruploads.s3.amazonaws.com |
| shared |
authserver.mojang.com |
| suspicious |
sessionserver.mojang.com |
| suspicious |
launchermeta.mojang.com |
| whitelisted |
piston-meta.mojang.com |
| suspicious |
cloudflare-dns.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
beta.skmedix.pl |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3600 | javaw.exe | Misc activity | ET INFO Observed Cloudflare DNS over HTTPS Domain (cloudflare-dns .com in TLS SNI) |
3600 | javaw.exe | Misc activity | ET INFO Cloudflare DNS Over HTTPS Certificate Inbound |