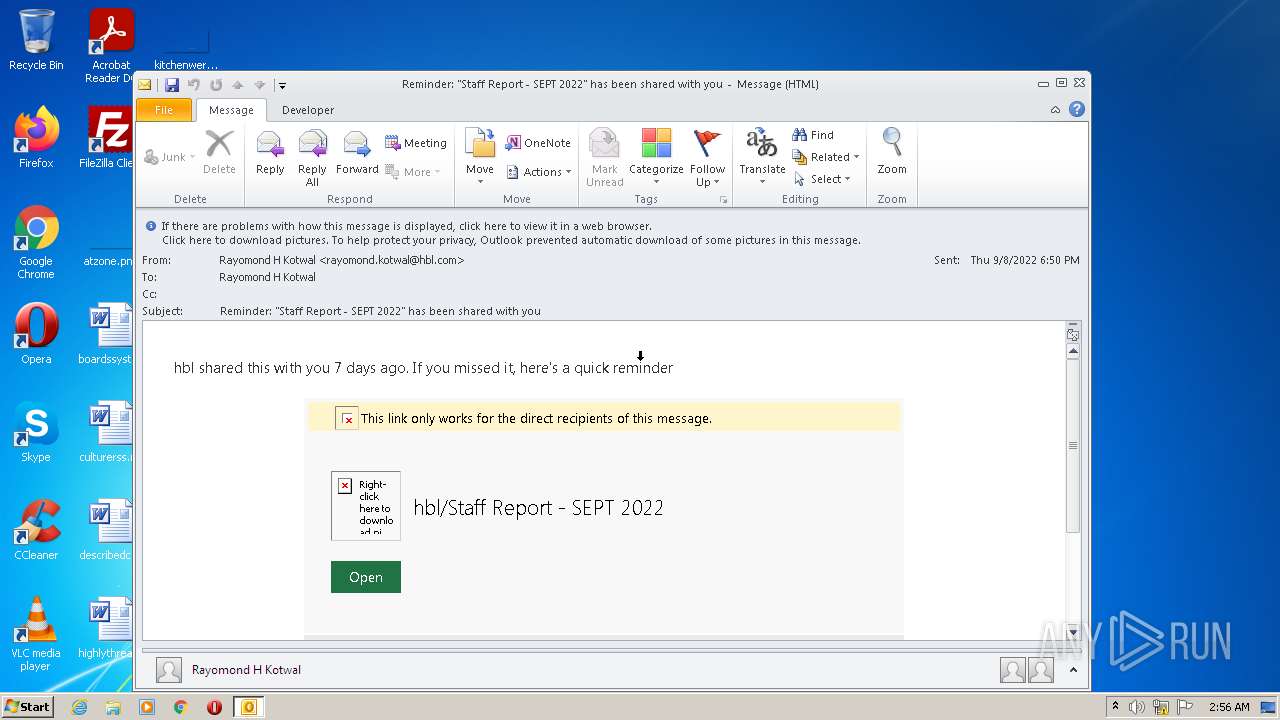
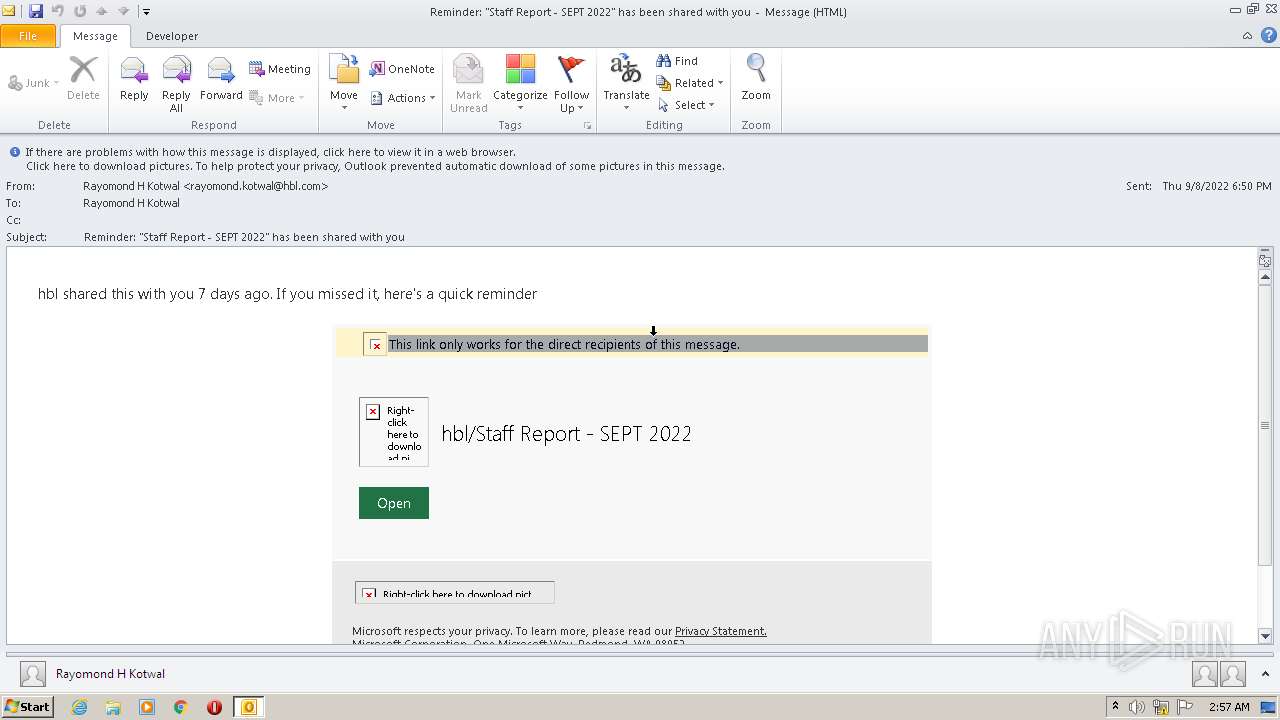
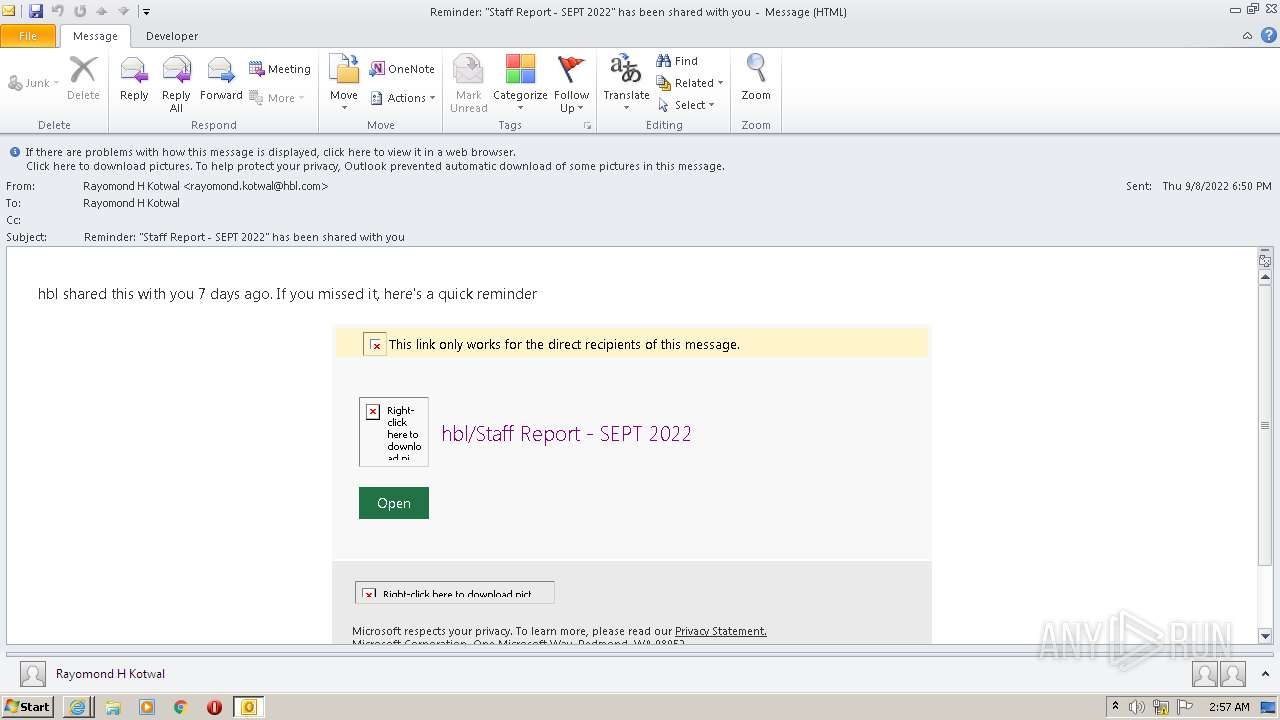
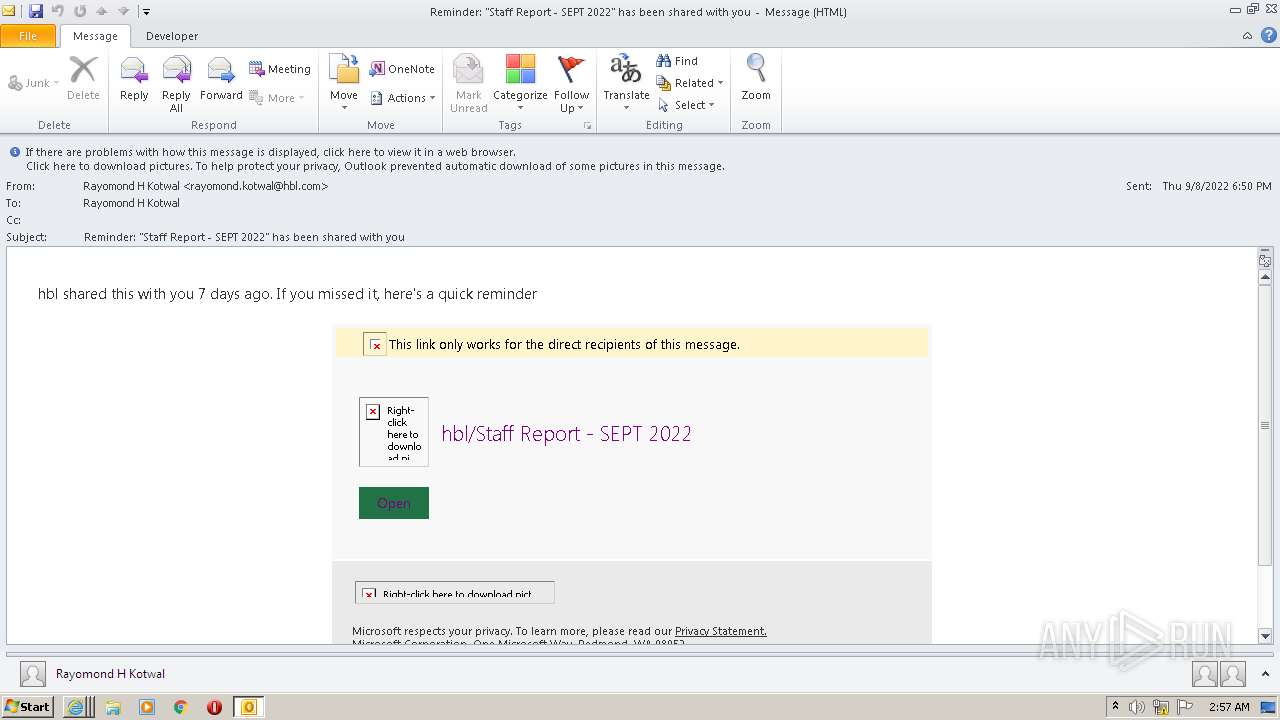
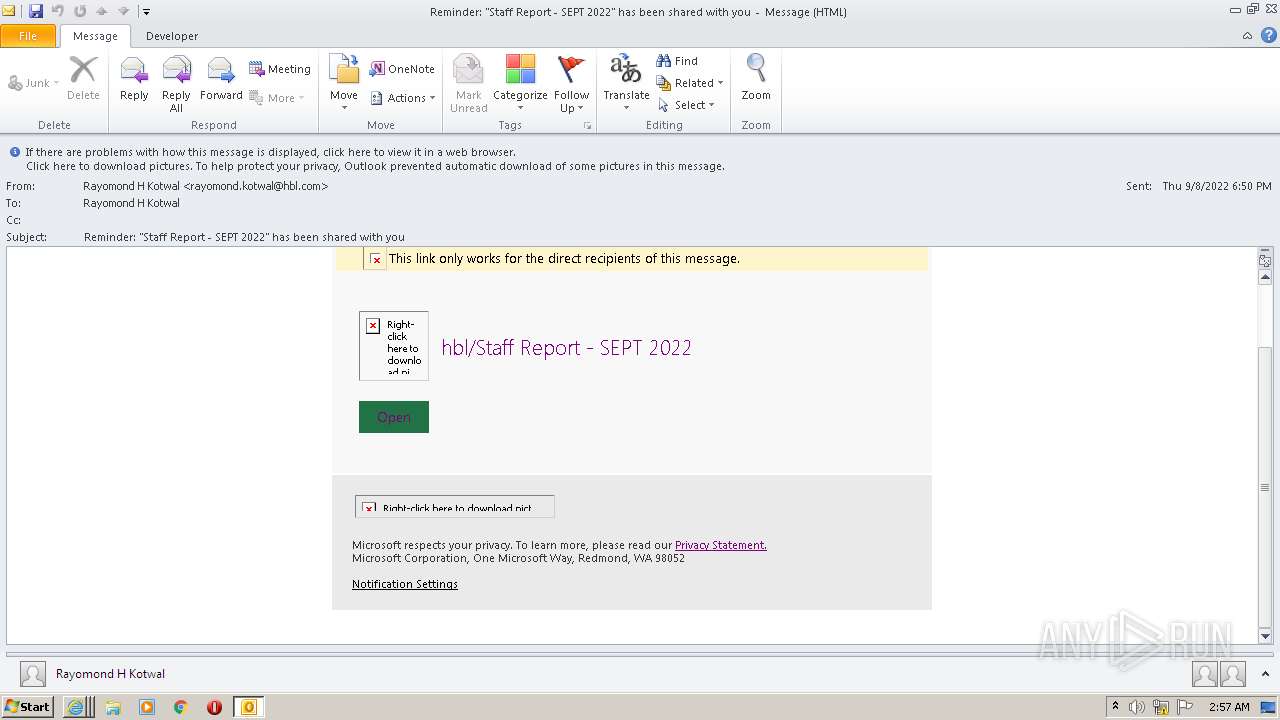
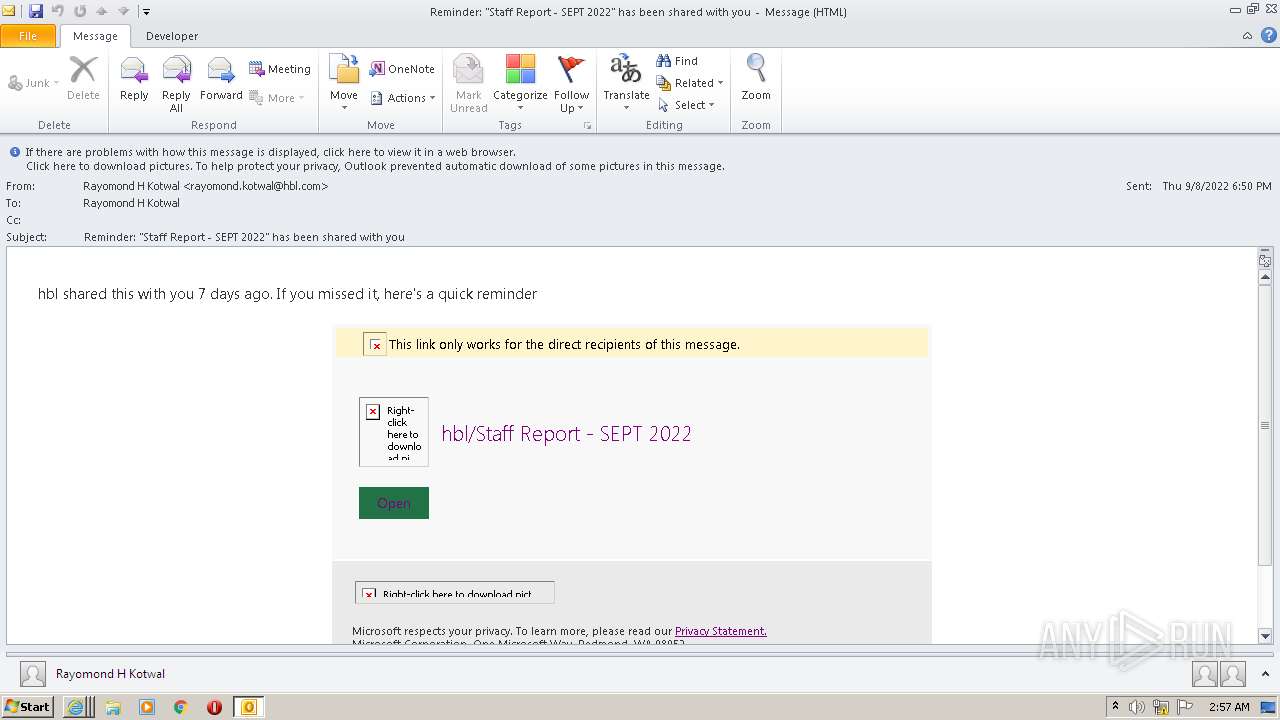
| File name: | Reminder Staff Report - SEPT 2022 has been shared with you.msg |
| Full analysis: | https://app.any.run/tasks/e4611c99-1b7b-46d2-a130-e3a142bea95a |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 01:56:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 5E3F44DCBD0F6703A4F226F20352255D |
| SHA1: | 4ACEC9ADA5E24478787A16E28B05897A99FF6F51 |
| SHA256: | 1073DAA8583AD739233397F9D1555DF4024C93757DF319E66D2BF33E62CCA104 |
| SSDEEP: | 1536:yaq2i5oS41gitCShqq3QxvtldB4LbwO4wpr9YHuwMI:r+aS+5hqqOfdB4Lbw7wpr9KM |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 1388)
SUSPICIOUS
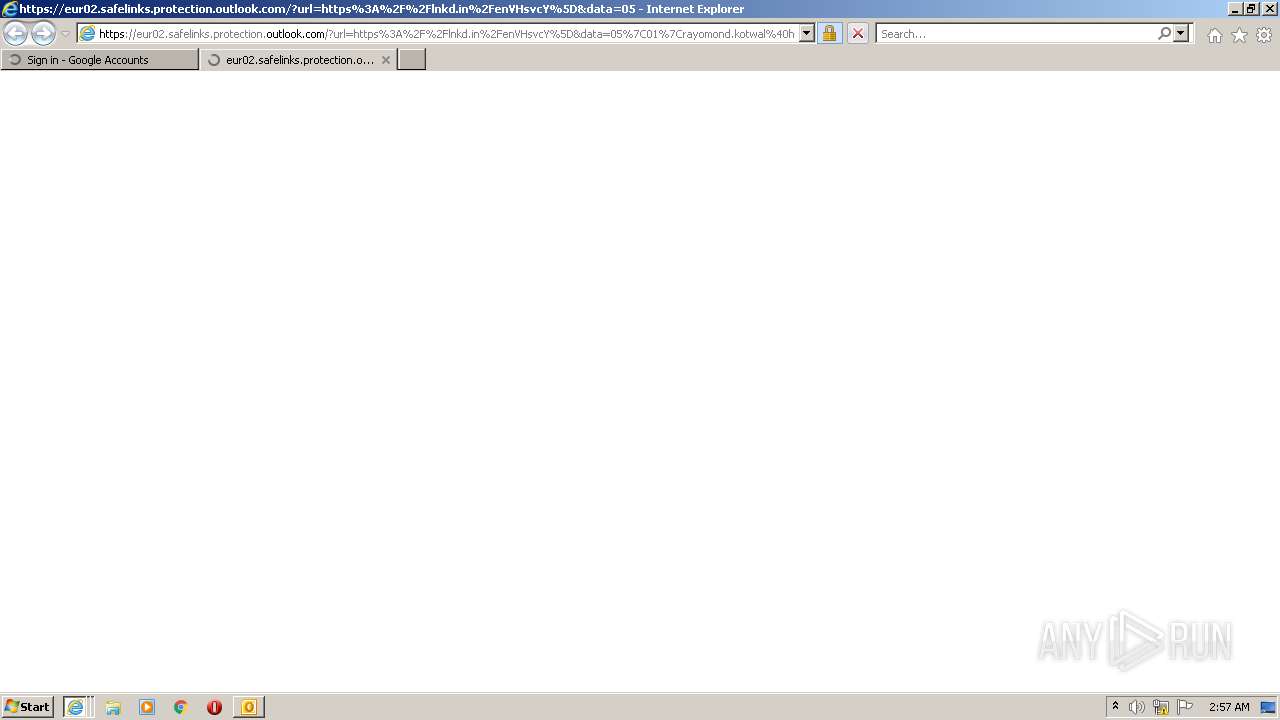
Starts Internet Explorer
- OUTLOOK.EXE (PID: 1388)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3212)
- iexplore.exe (PID: 4044)
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 1344)
INFO
Checks supported languages
- iexplore.exe (PID: 1168)
- OUTLOOK.EXE (PID: 1388)
- iexplore.exe (PID: 3212)
- iexplore.exe (PID: 400)
- iexplore.exe (PID: 4044)
- iexplore.exe (PID: 1344)
- iexplore.exe (PID: 3804)
Reads the computer name
- OUTLOOK.EXE (PID: 1388)
- iexplore.exe (PID: 1168)
- iexplore.exe (PID: 3212)
- iexplore.exe (PID: 400)
- iexplore.exe (PID: 4044)
- iexplore.exe (PID: 1344)
- iexplore.exe (PID: 3804)
Searches for installed software
- OUTLOOK.EXE (PID: 1388)
Creates files in the user directory
- OUTLOOK.EXE (PID: 1388)
- iexplore.exe (PID: 4044)
- iexplore.exe (PID: 3212)
- iexplore.exe (PID: 1344)
Application launched itself
- iexplore.exe (PID: 1168)
- iexplore.exe (PID: 400)
Changes internet zones settings
- iexplore.exe (PID: 1168)
- iexplore.exe (PID: 400)
Reads settings of System Certificates
- iexplore.exe (PID: 3212)
- iexplore.exe (PID: 400)
- iexplore.exe (PID: 4044)
- iexplore.exe (PID: 1344)
- iexplore.exe (PID: 1168)
- iexplore.exe (PID: 3804)
Checks Windows Trust Settings
- iexplore.exe (PID: 3212)
- iexplore.exe (PID: 4044)
- iexplore.exe (PID: 1168)
- iexplore.exe (PID: 1344)
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 400)
Adds / modifies Windows certificates
- iexplore.exe (PID: 400)
- iexplore.exe (PID: 1168)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1388)
Reads internet explorer settings
- iexplore.exe (PID: 4044)
- iexplore.exe (PID: 1344)
- iexplore.exe (PID: 3212)
Changes settings of System certificates
- iexplore.exe (PID: 1168)
- iexplore.exe (PID: 400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
44
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
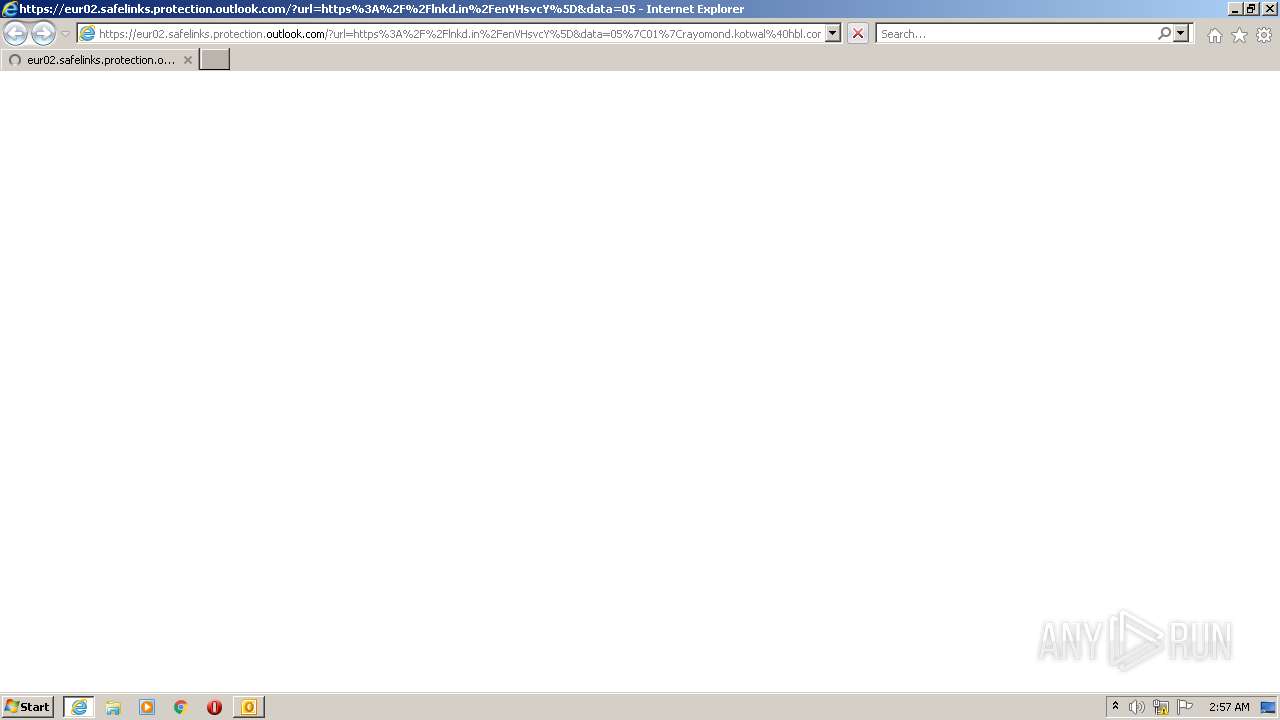
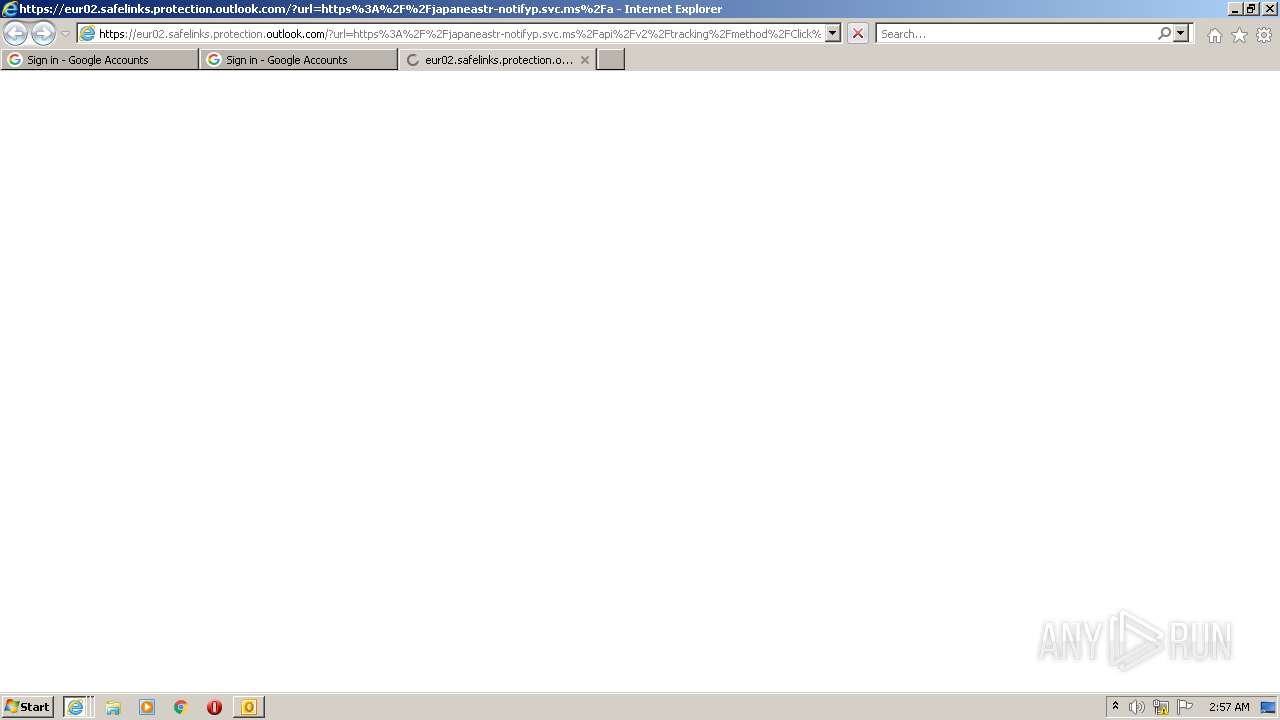
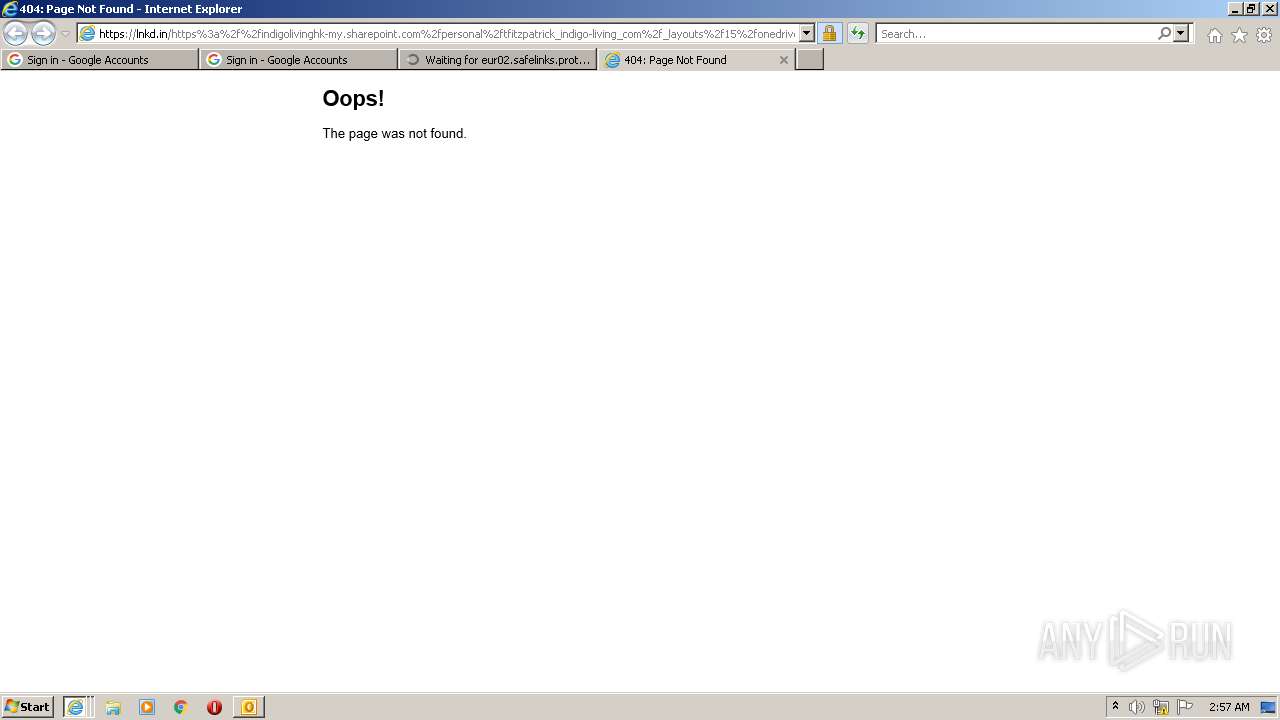
| 400 | "C:\Program Files\Internet Explorer\iexplore.exe" https://eur02.safelinks.protection.outlook.com/?url=https%3A%2F%2Flnkd.in%2FenVHsvcY%5D&data=05%7C01%7Crayomond.kotwal%40hbl.com%7C6ec78fb3e287424ccd9108da91c29002%7Cc219af2ace6c45bf863be09d59889053%7C0%7C0%7C637982562068100064%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C1000%7C%7C%7C&sdata=Mi55Ozr%2FEx3G5AbQL0pSy0LZUaANKCP9jtuBsMak80k%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Internet Explorer\iexplore.exe" https://eur02.safelinks.protection.outlook.com/?url=https%3A%2F%2Flnkd.in%2FenVHsvcY%5D&data=05%7C01%7Crayomond.kotwal%40hbl.com%7C6ec78fb3e287424ccd9108da91c29002%7Cc219af2ace6c45bf863be09d59889053%7C0%7C0%7C637982562068100064%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C1000%7C%7C%7C&sdata=Mi55Ozr%2FEx3G5AbQL0pSy0LZUaANKCP9jtuBsMak80k%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
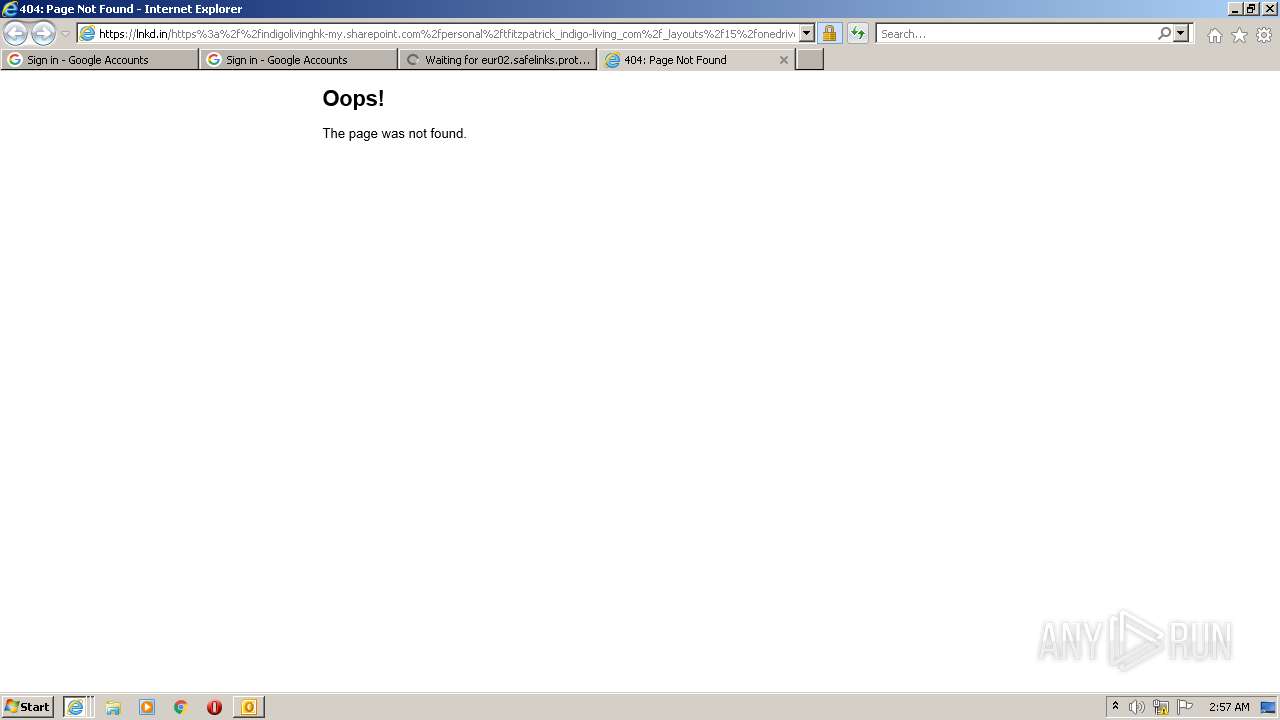
| 1344 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1168 CREDAT:3544331 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Reminder Staff Report - SEPT 2022 has been shared with you.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3212 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1168 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3804 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1168 CREDAT:3282208 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4044 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:400 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
36 066
Read events
35 213
Write events
828
Delete events
25
Modification events
| (PID) Process: | (1388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1388) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
14
Text files
37
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1388 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR96E1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1388 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 1388 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 1388 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1388 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_A5CE06CBB17D2A4D8D9D92D1C0606C06.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 1388 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 3212 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3212 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\2F23D0F5E4D72862517E1CB26A329742_F6FACC49395CFA949BCE851E73323C49 | der | |
MD5:— | SHA256:— | |||
| 3212 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2F23D0F5E4D72862517E1CB26A329742_F6FACC49395CFA949BCE851E73323C49 | binary | |
MD5:— | SHA256:— | |||
| 3212 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
100
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3212 | iexplore.exe | GET | 200 | 142.250.187.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
4044 | iexplore.exe | GET | 200 | 142.250.187.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
400 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD6a7qQTCYd8hJU9n3M3mXb | US | der | 472 b | whitelisted |
3212 | iexplore.exe | GET | 200 | 142.250.187.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC0vpGxlCExvgo1I2m1R%2FQ8 | US | der | 472 b | whitelisted |
400 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1168 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
4044 | iexplore.exe | GET | 200 | 142.250.187.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC0vpGxlCExvgo1I2m1R%2FQ8 | US | der | 472 b | whitelisted |
3212 | iexplore.exe | GET | 200 | 142.250.187.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEBXPb1cPSgPtCgATpFPzqkg%3D | US | der | 471 b | whitelisted |
3212 | iexplore.exe | GET | 200 | 142.250.187.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
4044 | iexplore.exe | GET | 200 | 142.250.187.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3212 | iexplore.exe | 104.47.6.28:443 | eur02.safelinks.protection.outlook.com | MICROSOFT-CORP-MSN-AS-BLOCK | AT | whitelisted |
1388 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3212 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
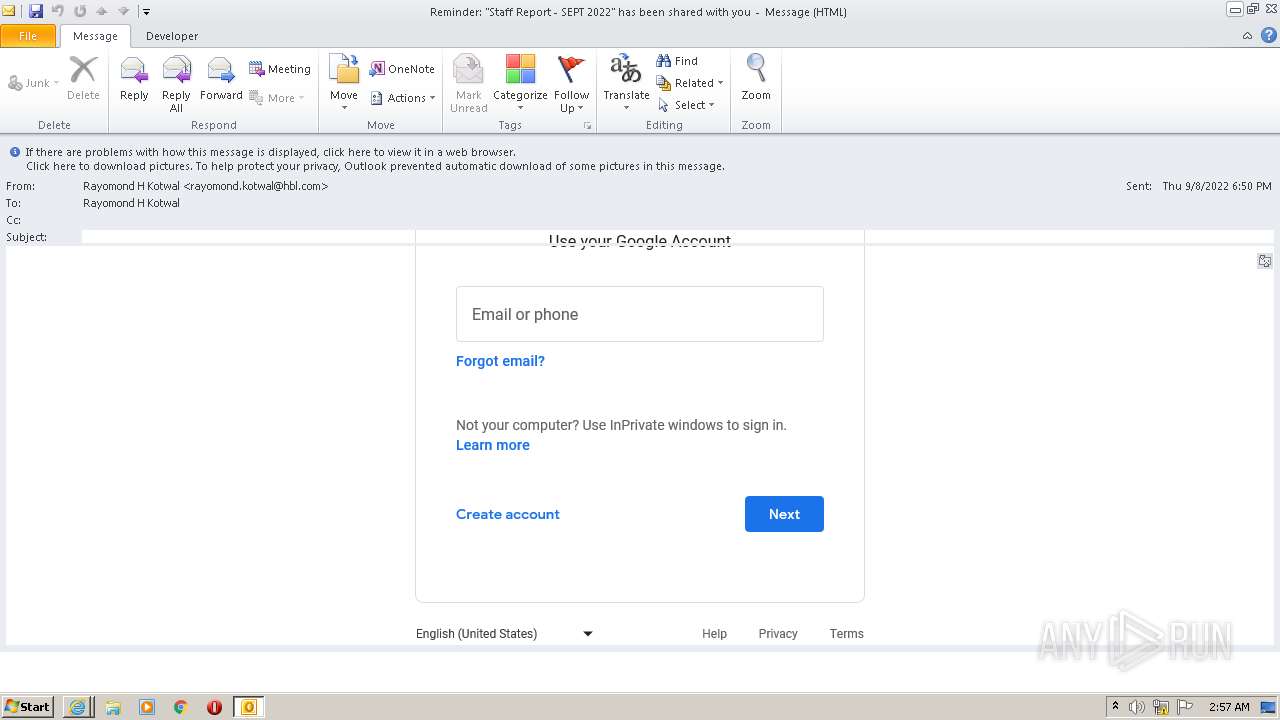
4044 | iexplore.exe | 13.107.42.14:443 | lnkd.in | MICROSOFT-CORP-MSN-AS-BLOCK | US | suspicious |
4044 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
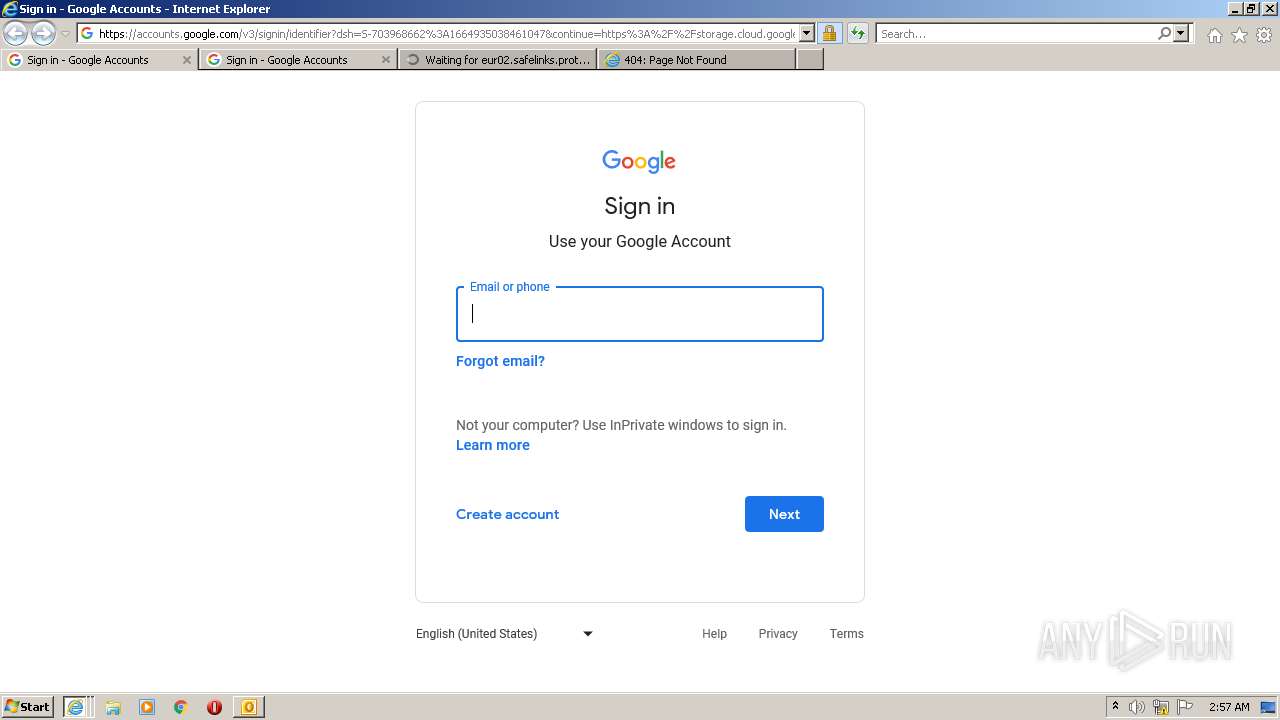
4044 | iexplore.exe | 216.58.214.142:443 | storage.cloud.google.com | GOOGLE | US | whitelisted |
3212 | iexplore.exe | 216.58.214.142:443 | storage.cloud.google.com | GOOGLE | US | whitelisted |
4044 | iexplore.exe | 142.250.187.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
4044 | iexplore.exe | 104.47.6.28:443 | eur02.safelinks.protection.outlook.com | MICROSOFT-CORP-MSN-AS-BLOCK | AT | whitelisted |
3212 | iexplore.exe | 13.107.42.14:443 | lnkd.in | MICROSOFT-CORP-MSN-AS-BLOCK | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
eur02.safelinks.protection.outlook.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
lnkd.in |
| whitelisted |
storage.cloud.google.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
accounts.google.com |
| shared |