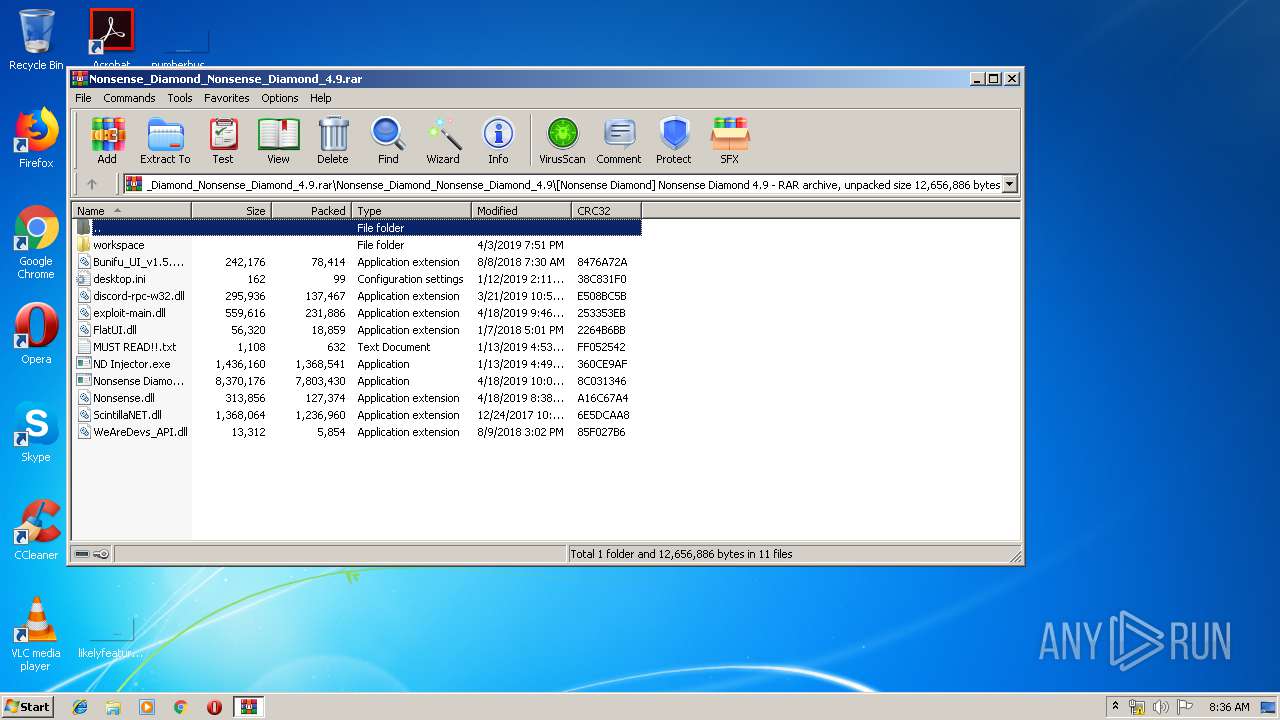
| File name: | Nonsense_Diamond_Nonsense_Diamond_4.9.rar |
| Full analysis: | https://app.any.run/tasks/87d98323-c892-4d7a-b6ad-622454690a4e |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 07:35:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2A3E582FB680A209D98C5154682B1264 |
| SHA1: | 8626B47650AE3DBC2BE33AF8FC564ADDA876FB7E |
| SHA256: | 1071ABEB6D73511059BAAFCC4B0509249C666A968496CD9B8D857B089D2A8A94 |
| SSDEEP: | 196608:C5Jg0LZWU/B4xYsd89TKyUC2nwELIQsmiiT+wCkmoob2nizO1SMblb:QUUpGYsd88yUbwELIQf1TQCizE |
MALICIOUS
Application was dropped or rewritten from another process
- Nonsense Diamond.exe (PID: 928)
Loads dropped or rewritten executable
- Nonsense Diamond.exe (PID: 928)
SUSPICIOUS
Writes to a desktop.ini file (may be used to cloak folders)
- WinRAR.exe (PID: 128)
Modifies the open verb of a shell class
- Nonsense Diamond.exe (PID: 928)
Reads internet explorer settings
- Nonsense Diamond.exe (PID: 928)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 128)
- Nonsense Diamond.exe (PID: 928)
Creates files in the user directory
- Nonsense Diamond.exe (PID: 928)
INFO
Reads settings of System Certificates
- Nonsense Diamond.exe (PID: 928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
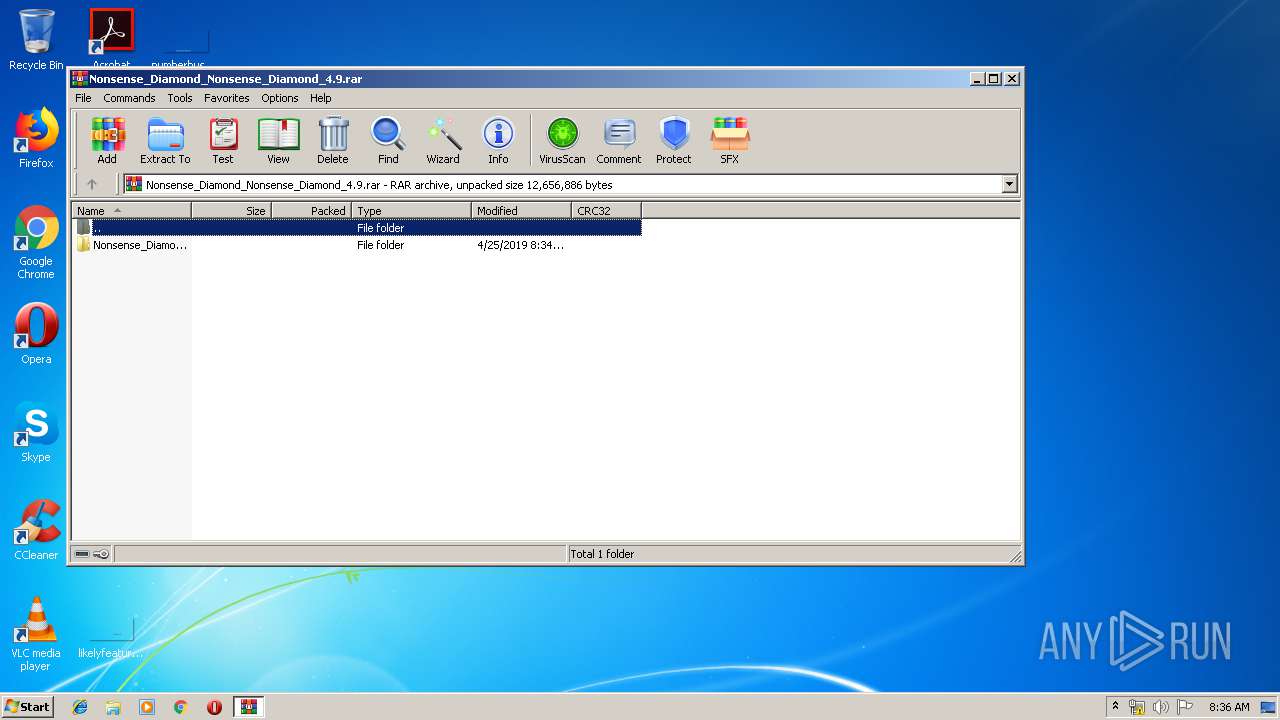
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
33
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Nonsense_Diamond_Nonsense_Diamond_4.9.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
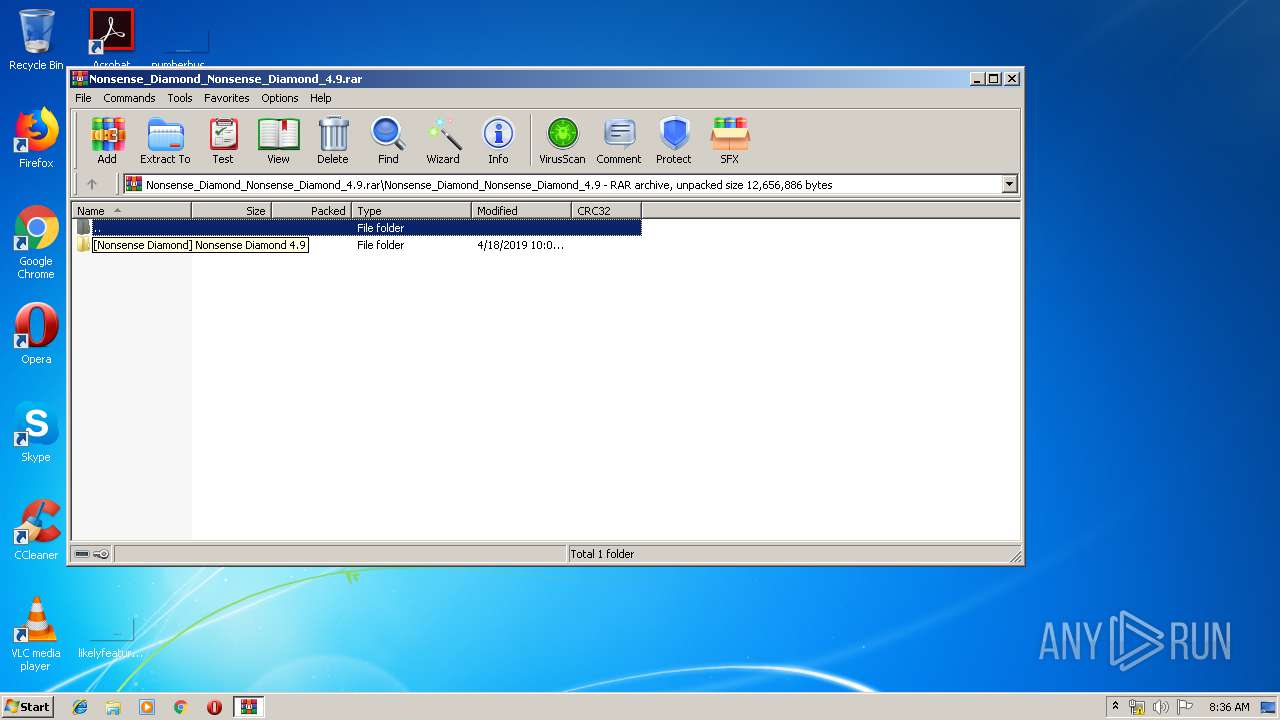
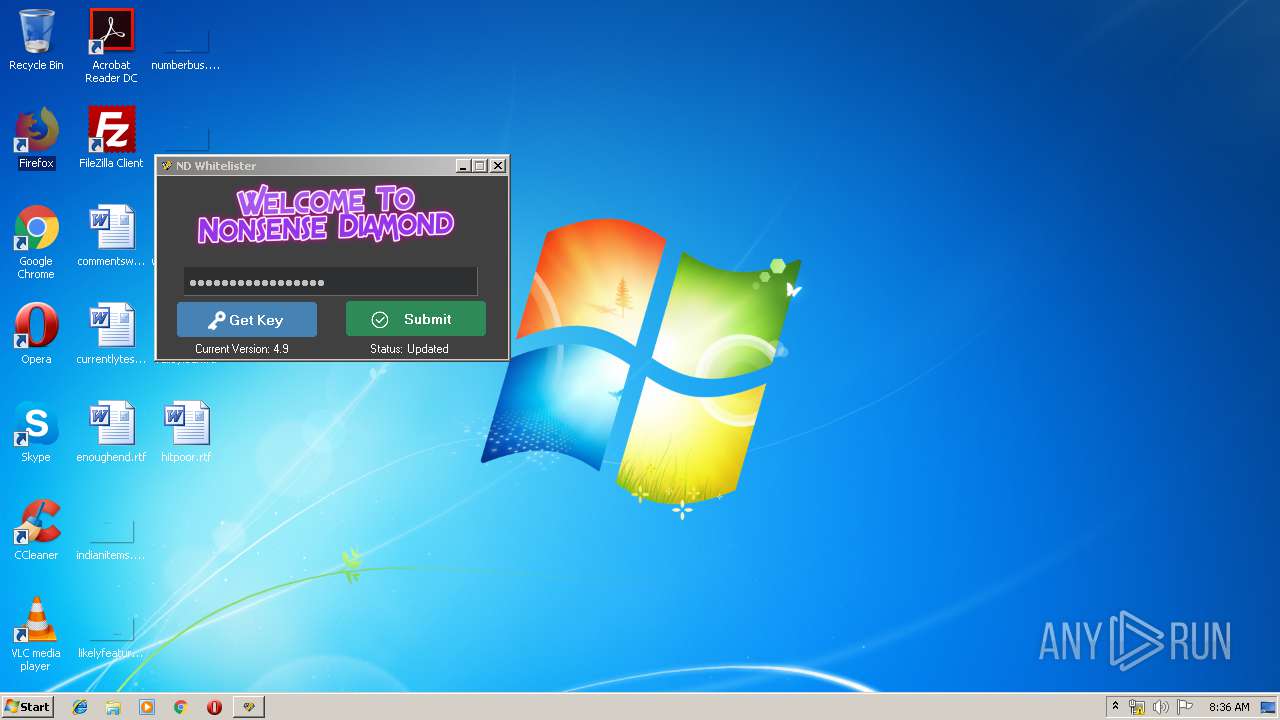
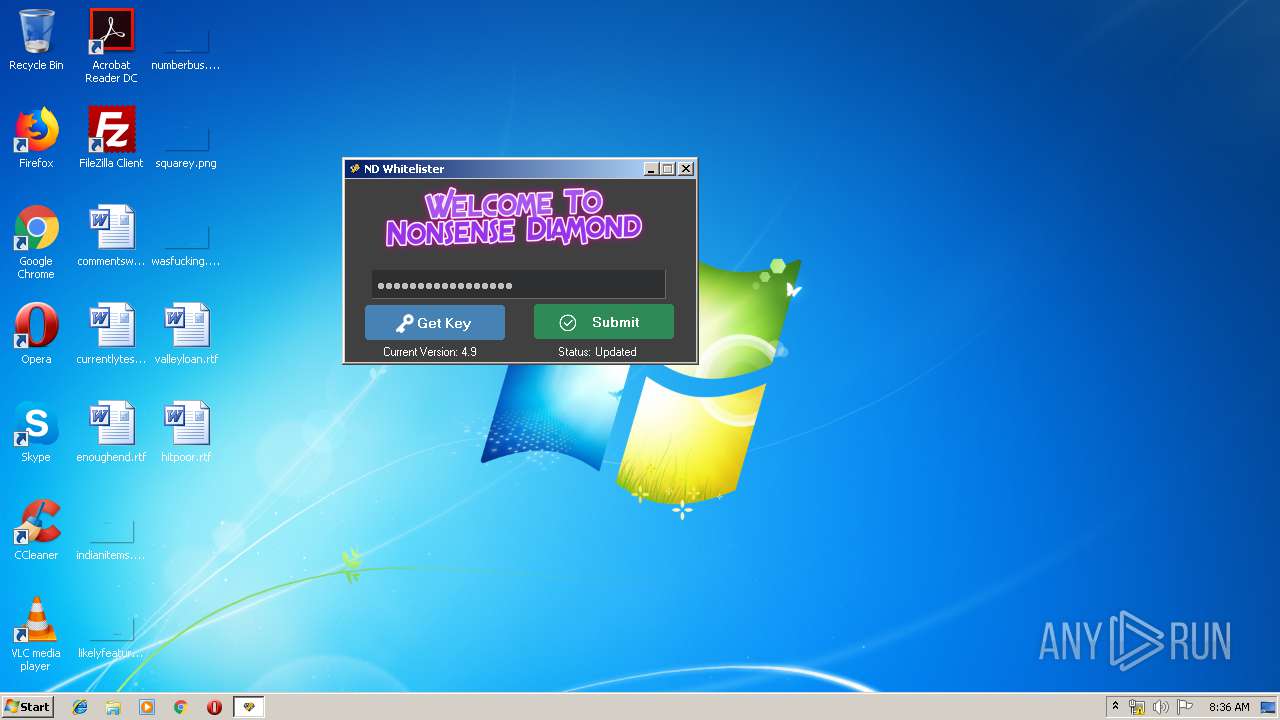
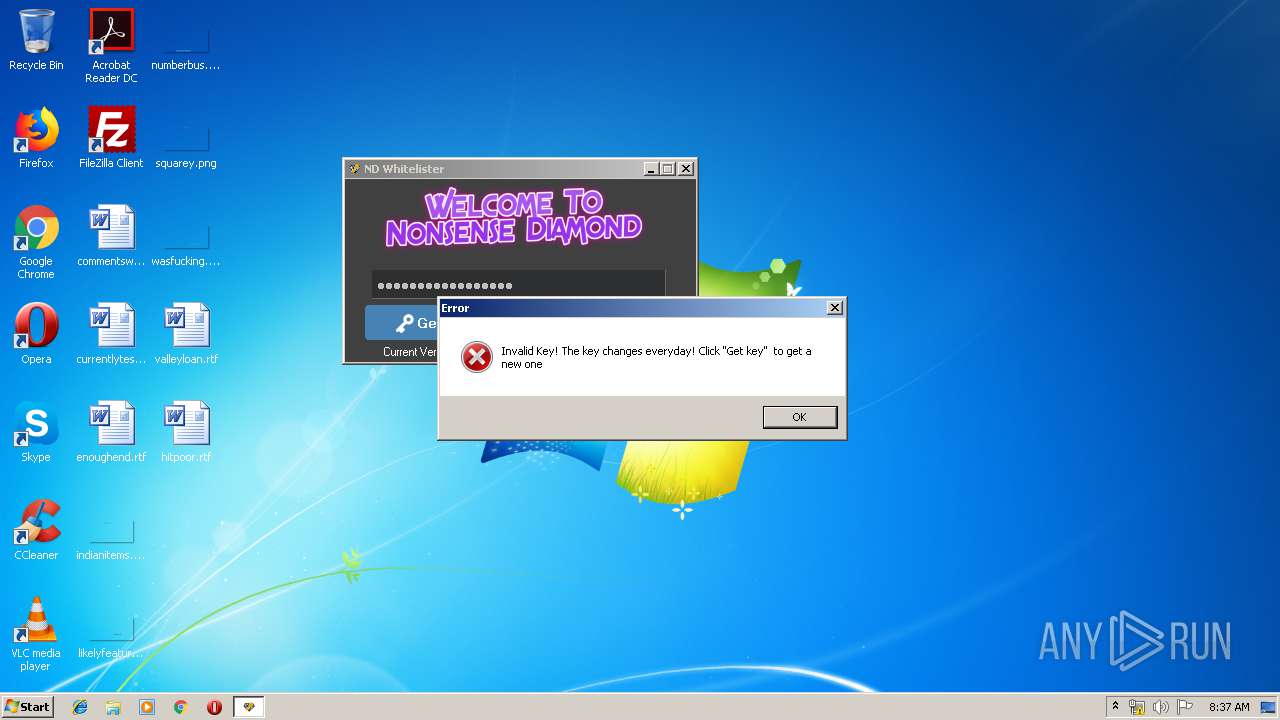
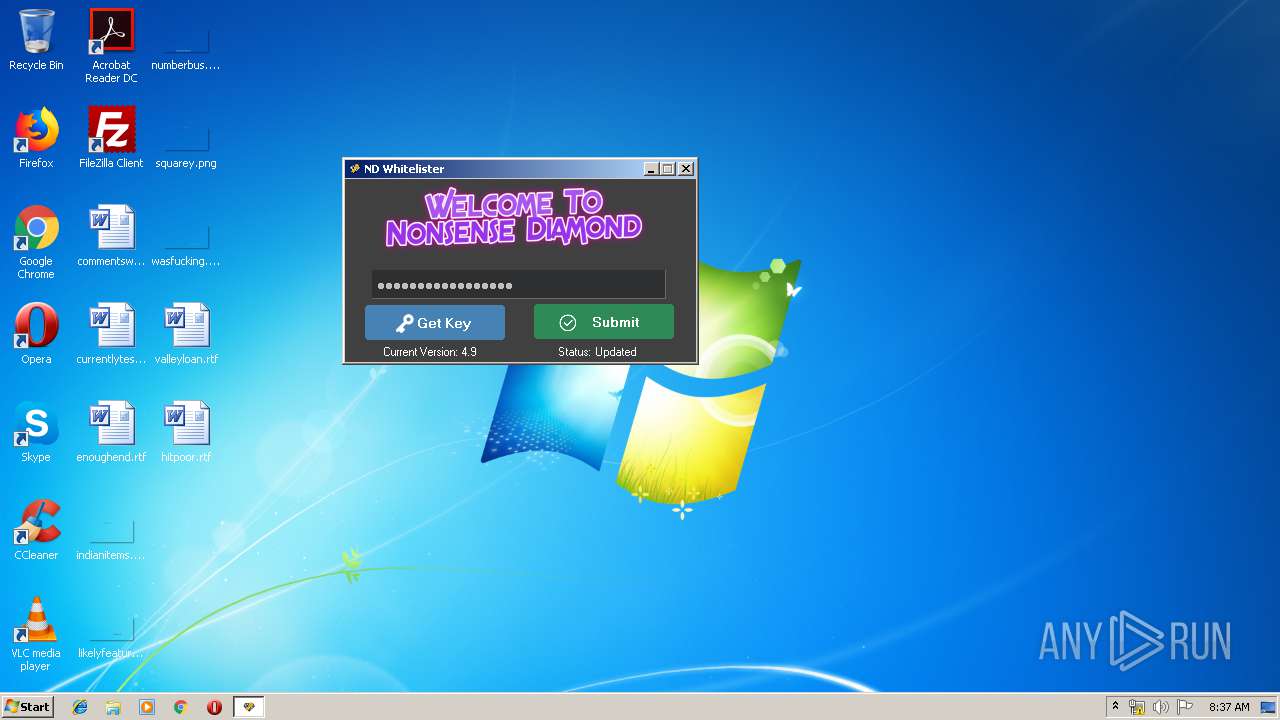
| 928 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa128.28608\Nonsense_Diamond_Nonsense_Diamond_4.9\[Nonsense Diamond] Nonsense Diamond 4.9\Nonsense Diamond.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa128.28608\Nonsense_Diamond_Nonsense_Diamond_4.9\[Nonsense Diamond] Nonsense Diamond 4.9\Nonsense Diamond.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Nonsense Diamond Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
584
Read events
523
Write events
61
Delete events
0
Modification events
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Nonsense_Diamond_Nonsense_Diamond_4.9.rar | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
10
Suspicious files
0
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 928 | Nonsense Diamond.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[1].txt | — | |
MD5:— | SHA256:— | |||
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa128.28608\Nonsense_Diamond_Nonsense_Diamond_4.9\[Nonsense Diamond] Nonsense Diamond 4.9\desktop.ini | ini | |
MD5:— | SHA256:— | |||
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa128.28608\Nonsense_Diamond_Nonsense_Diamond_4.9\[Nonsense Diamond] Nonsense Diamond 4.9\exploit-main.dll | executable | |
MD5:— | SHA256:— | |||
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa128.28608\Nonsense_Diamond_Nonsense_Diamond_4.9\[Nonsense Diamond] Nonsense Diamond 4.9\MUST READ!!.txt | text | |
MD5:— | SHA256:— | |||
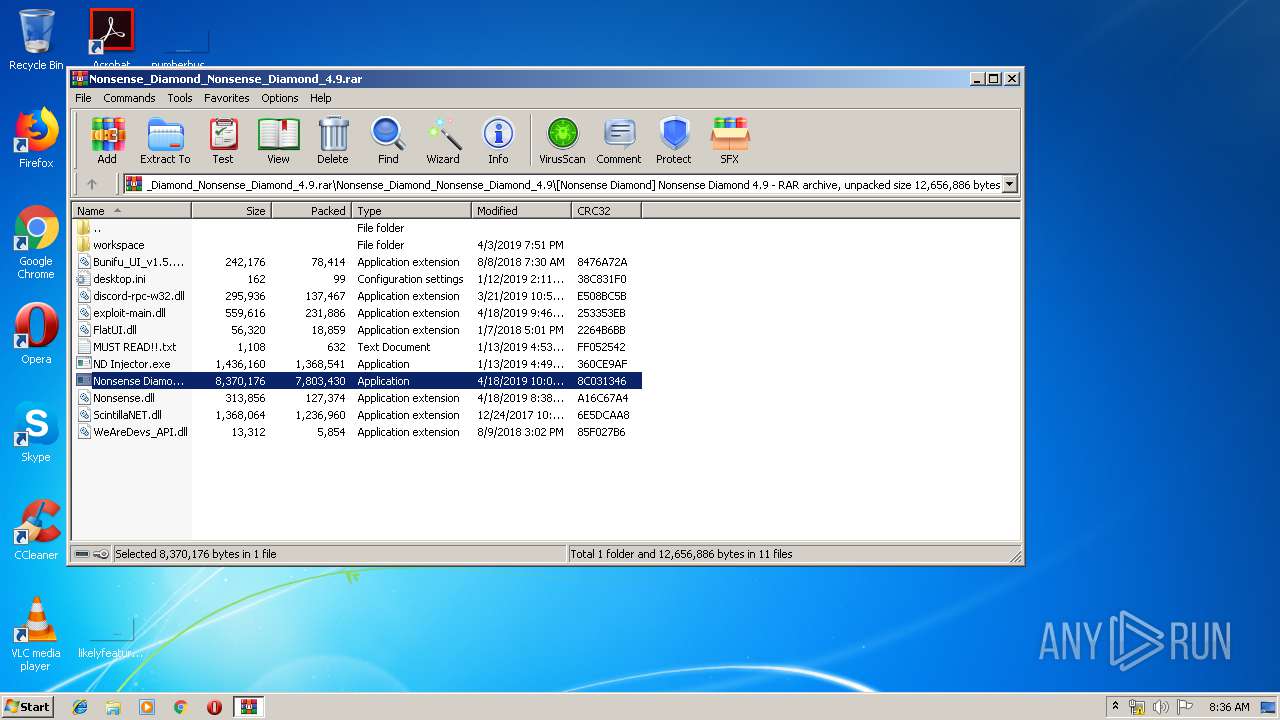
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa128.28608\Nonsense_Diamond_Nonsense_Diamond_4.9\[Nonsense Diamond] Nonsense Diamond 4.9\Nonsense Diamond.exe | executable | |
MD5:— | SHA256:— | |||
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa128.28608\Nonsense_Diamond_Nonsense_Diamond_4.9\[Nonsense Diamond] Nonsense Diamond 4.9\ND Injector.exe | executable | |
MD5:— | SHA256:— | |||
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa128.28608\Nonsense_Diamond_Nonsense_Diamond_4.9\[Nonsense Diamond] Nonsense Diamond 4.9\discord-rpc-w32.dll | executable | |
MD5:A1C35901AD26A30C5B7836771B6BADFF | SHA256:517240600B04D454CC5AB7B03E43C4AF5A0B831FD2515F25C015A83652AD4CAC | |||
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa128.28608\Nonsense_Diamond_Nonsense_Diamond_4.9\[Nonsense Diamond] Nonsense Diamond 4.9\FlatUI.dll | executable | |
MD5:B63F5C816F8799857B9B8F95B6E2A9B0 | SHA256:058C926A8818479B06AB9402F2A6C85EB0F64626C2956102D6699AD413AFE2FB | |||
| 928 | Nonsense Diamond.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[2].txt | text | |
MD5:— | SHA256:— | |||
| 928 | Nonsense Diamond.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\google_com[1].txt | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
928 | Nonsense Diamond.exe | 172.217.16.206:443 | google.com | Google Inc. | US | whitelisted |
928 | Nonsense Diamond.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
928 | Nonsense Diamond.exe | 104.31.78.245:443 | www.sparecomputing.com | Cloudflare Inc | US | shared |
928 | Nonsense Diamond.exe | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
google.com |
| malicious |
www.google.com |
| malicious |
www.sparecomputing.com |
| suspicious |