| File name: | procexp.exe |
| Full analysis: | https://app.any.run/tasks/abcd17fa-2b9c-4e97-9654-87460edd847e |
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2024, 07:45:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 94C60E6704B5DD11A139F2FFEBDE9135 |
| SHA1: | CD89F1CF9428A3EAB554A3EB9FF6CA869E5BC368 |
| SHA256: | 106BF123359D03963B1DF1011FB8560AAF1C5E811DE775DCE1D8A53758A69102 |
| SSDEEP: | 98304:kQ/qdW5SWBJdgKwBFip2LytbxPiei81/mxKkAcEgHboS3FdF:Keiqo |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops the executable file immediately after the start
- procexp.exe (PID: 6456)
- procexp64.exe (PID: 6480)
The process checks if it is being run in the virtual environment
- procexp.exe (PID: 6456)
- procexp64.exe (PID: 6480)
Executable content was dropped or overwritten
- procexp.exe (PID: 6456)
- procexp64.exe (PID: 6480)
Reads security settings of Internet Explorer
- procexp64.exe (PID: 6480)
Drops a system driver (possible attempt to evade defenses)
- procexp64.exe (PID: 6480)
Read startup parameters
- procexp64.exe (PID: 6480)
Detected use of alternative data streams (AltDS)
- procexp64.exe (PID: 6480)
Checks Windows Trust Settings
- procexp64.exe (PID: 6480)
INFO
Create files in a temporary directory
- procexp.exe (PID: 6456)
- procexp64.exe (PID: 6480)
Checks supported languages
- procexp.exe (PID: 6456)
- procexp64.exe (PID: 6480)
Reads the computer name
- procexp64.exe (PID: 6480)
- procexp.exe (PID: 6456)
Reads Environment values
- procexp64.exe (PID: 6480)
Reads product name
- procexp64.exe (PID: 6480)
Reads the software policy settings
- procexp64.exe (PID: 6480)
Creates files or folders in the user directory
- procexp64.exe (PID: 6480)
Reads Microsoft Office registry keys
- procexp64.exe (PID: 6480)
Reads the machine GUID from the registry
- procexp64.exe (PID: 6480)
Checks proxy server information
- procexp64.exe (PID: 6480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:05:28 15:50:44+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.39 |
| CodeSize: | 1014272 |
| InitializedDataSize: | 3712512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc43ce |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 17.6.0.0 |
| ProductVersionNumber: | 17.6.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Sysinternals Process Explorer |
| FileVersion: | 17.06 |
| InternalName: | Process Explorer |
| LegalCopyright: | Copyright © 1998-2024 Mark Russinovich |
| LegalTrademarks: | Copyright © 1998-2024 Mark Russinovich |
| OriginalFileName: | Procexp.exe |
| ProductName: | Process Explorer |
| ProductVersion: | 17.06 |
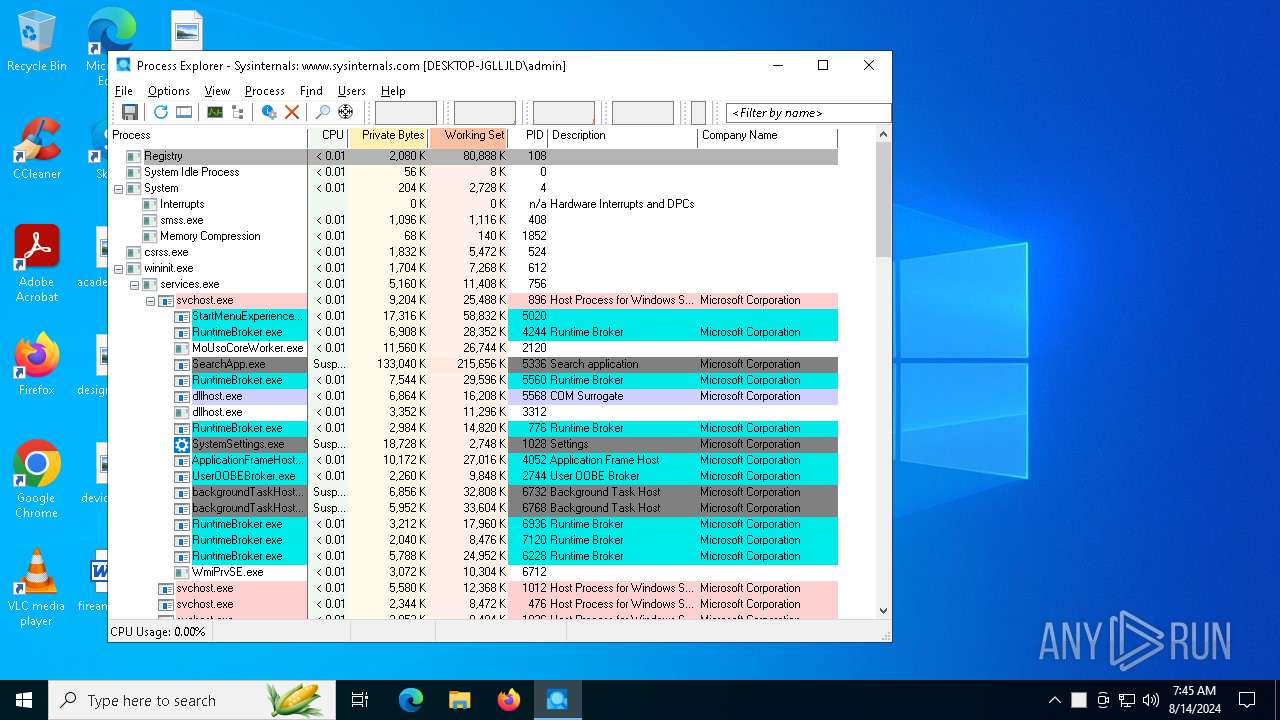
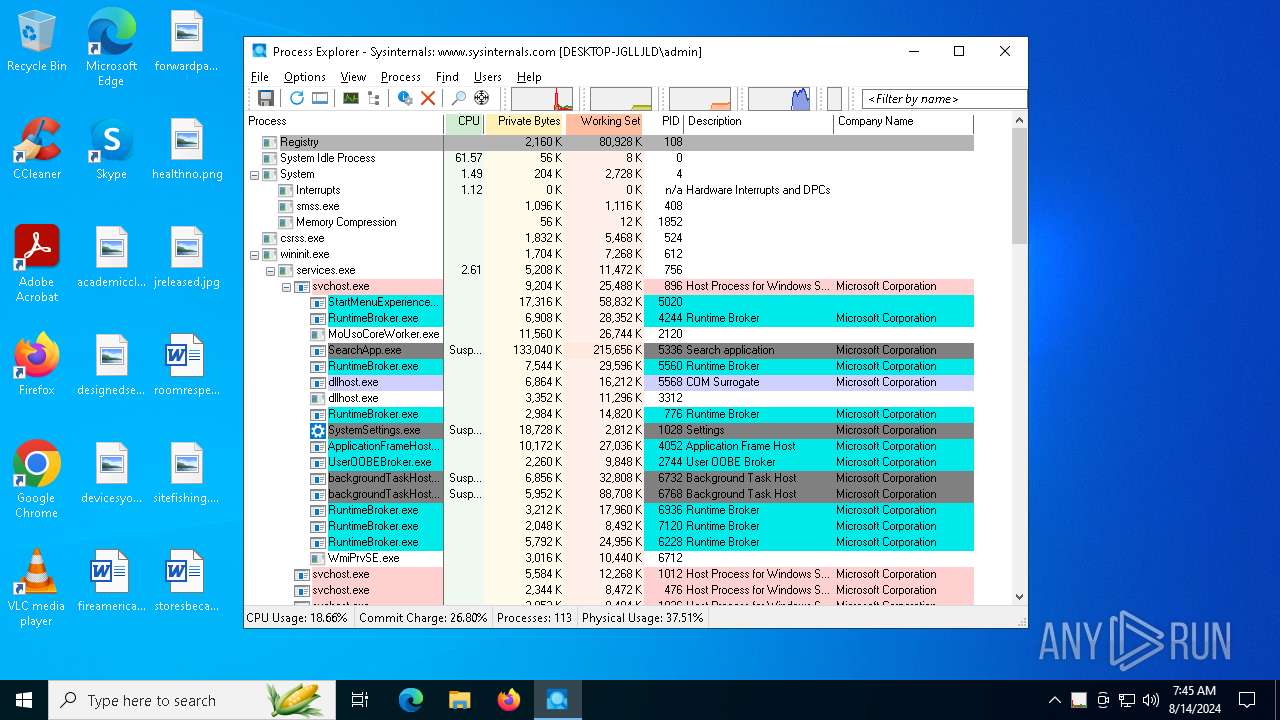
Total processes
134
Monitored processes
2
Malicious processes
2
Suspicious processes
0
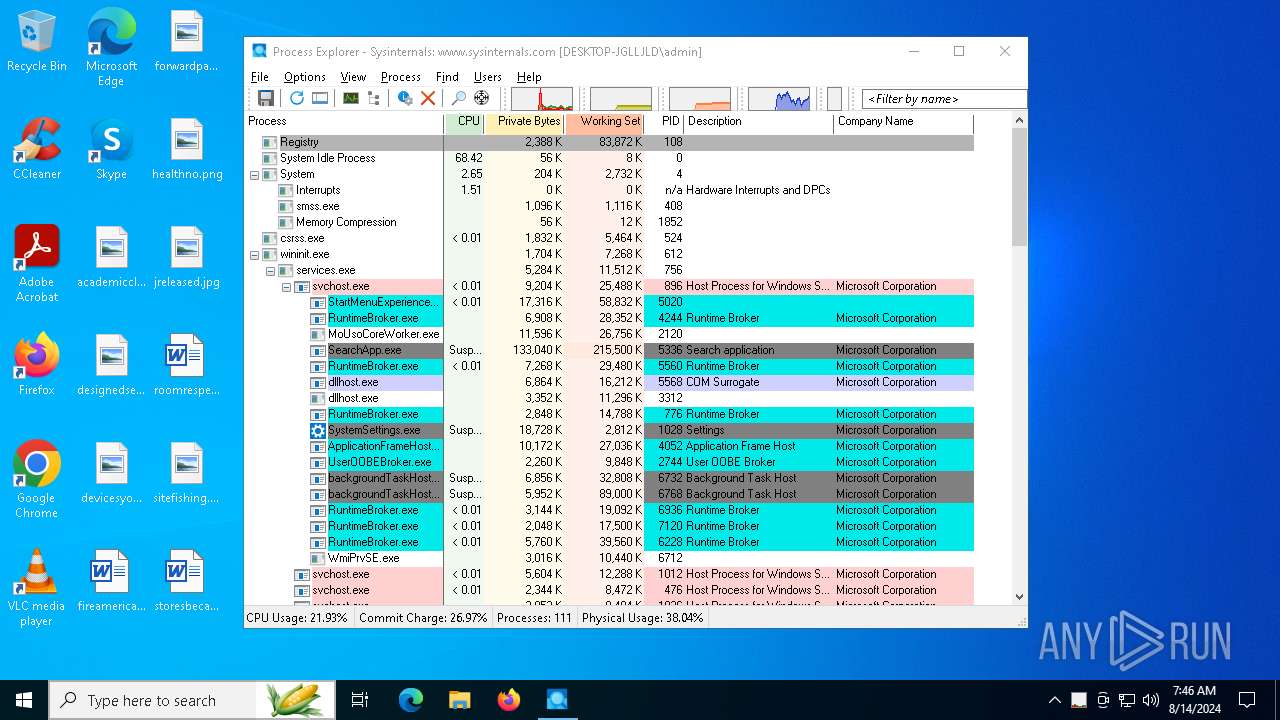
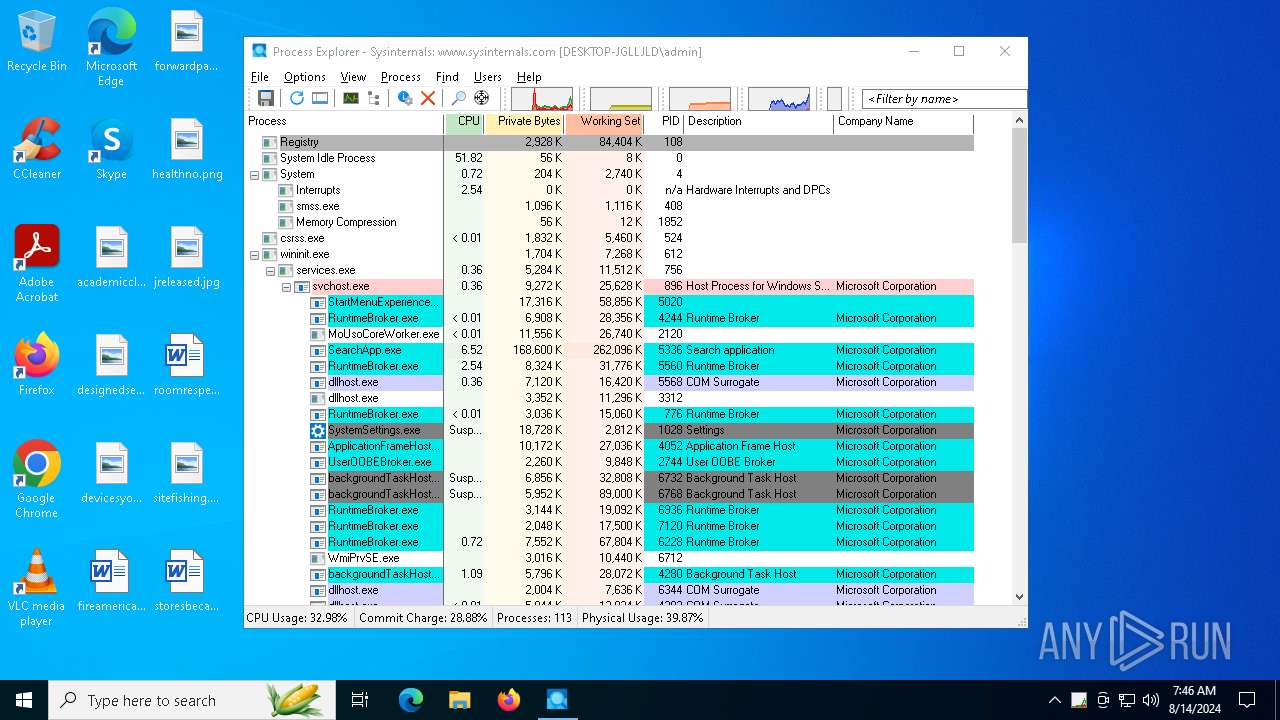
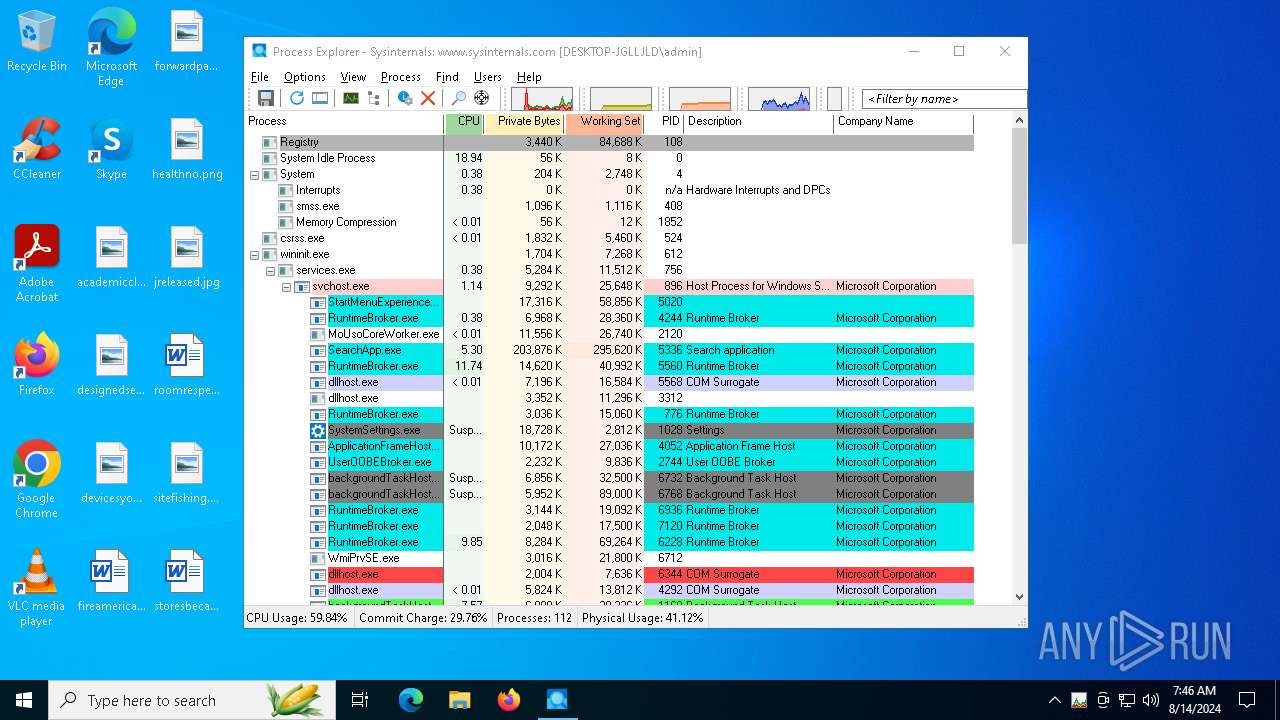
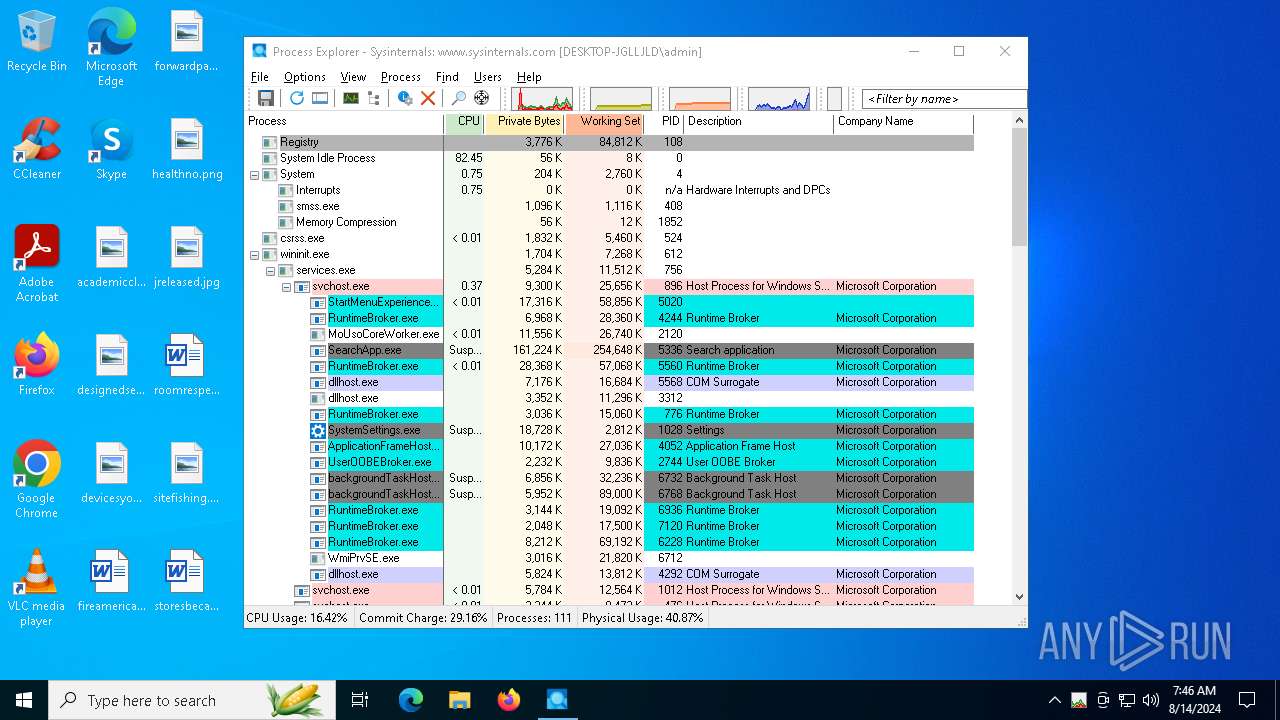
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6456 | "C:\Users\admin\AppData\Local\Temp\procexp.exe" | C:\Users\admin\AppData\Local\Temp\procexp.exe | explorer.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Sysinternals Process Explorer Version: 17.06 Modules
| |||||||||||||||
| 6480 | "C:\Users\admin\AppData\Local\Temp\procexp.exe" | C:\Users\admin\AppData\Local\Temp\procexp64.exe | procexp.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Sysinternals Process Explorer Version: 17.06 Modules
| |||||||||||||||
Total events
39 585
Read events
39 582
Write events
3
Delete events
0
Modification events
| (PID) Process: | (6456) procexp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Sysinternals\Process Explorer |
| Operation: | write | Name: | OriginalPath |
Value: C:\Users\admin\AppData\Local\Temp\procexp.exe | |||
| (PID) Process: | (6456) procexp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Sysinternals\Process Explorer |
| Operation: | write | Name: | Path |
Value: C:\Users\admin\AppData\Local\Temp\procexp64.exe | |||
| (PID) Process: | (6480) procexp64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Sysinternals\Process Explorer |
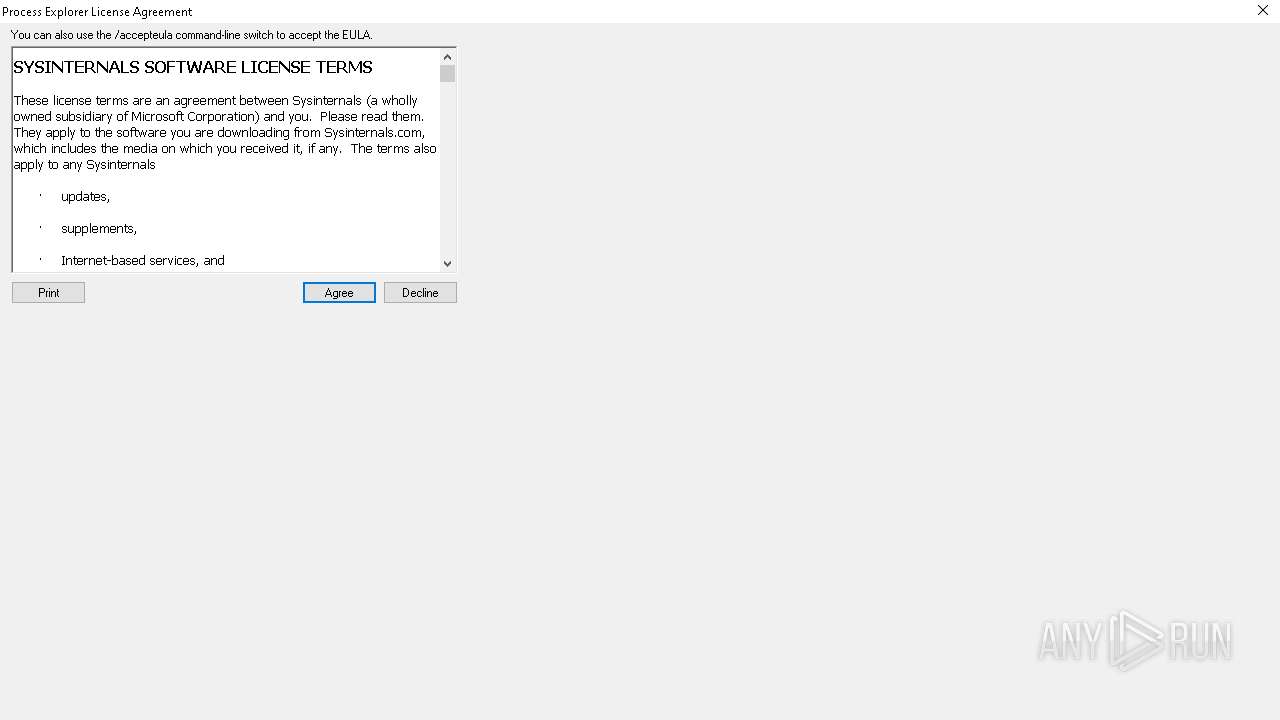
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
Executable files
2
Suspicious files
49
Text files
0
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6480 | procexp64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\45AE547469FB7137480E06153457A2DD | binary | |
MD5:E026BB8BDD992CAED4BE0D94E7054F04 | SHA256:95A479D2F776BB08F2F74337EBBA313488AE3A83BFC82BB7CA71F746333788AF | |||
| 6480 | procexp64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A583E2A51BFBDC1E492A57B7C8325850 | binary | |
MD5:C7D1234376F3389D6C220F0DCF24341B | SHA256:F67F7E62B47D1C4D9059F9F01FF40D52044EE81F594C5B8C8925C254381061E5 | |||
| 6480 | procexp64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0B8A20E1F3F4D73D52A19929F922C892 | binary | |
MD5:C56ADB9EE6563F558DE1855C603FBB15 | SHA256:CD0A7744F3347391A37C80B8D656047F66AA692E78971C94210477B68B07600F | |||
| 6480 | procexp64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\36AC0BE60E1243344AE145F746D881FE | binary | |
MD5:478669B8E30FC516B80D736FE33D99B6 | SHA256:30279B4A24439CE9B10BEE42BD91FAAF999A7B49832AF156B3CF0B879BE26E46 | |||
| 6480 | procexp64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\36AC0BE60E1243344AE145F746D881FE | binary | |
MD5:A20961D8BD1A5A7D241026D0011751FB | SHA256:4D6AE5BBEF0EACFDC09D5ADE4D145E883CF41B131E4C6988738769F1D32E12F3 | |||
| 6480 | procexp64.exe | C:\Users\admin\AppData\Local\Temp\PROCEXP152.SYS | executable | |
MD5:350AABF315C387C677BD5B9CE80BF525 | SHA256:86F635BF43A64A267A003260EB9B93FF05799F12DE84E9A2F01A02B4DD92AFC2 | |||
| 6480 | procexp64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:FB64A9EBEDF48D3895381D5B7D80743D | SHA256:EA21D495930AD76F267A33A0F593DBF0C7EA75E457FCAE49A29DAAD8BD920F42 | |||
| 6480 | procexp64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C0018BB1B5834735BFA60CD063B31956 | binary | |
MD5:4C07FED561AE9AB3878639DD22365AE2 | SHA256:D4BD75610D1D3247EE90F1F28C8D5F164CFB452FCA332504D6DBED582F76C5BC | |||
| 6480 | procexp64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3C3948BE6E525B8A8CEE9FAC91C9E392_752708131C25F4BEFB4DBDF7A5C73862 | binary | |
MD5:5BFA51F3A417B98E7443ECA90FC94703 | SHA256:BEBE2853A3485D1C2E5C5BE4249183E0DDAFF9F87DE71652371700A89D937128 | |||
| 6480 | procexp64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\60E31627FDA0A46932B0E5948949F2A5 | binary | |
MD5:E1E7AD0A838CE99FBC07A22EBF1CA421 | SHA256:4C44A5C081C239DB7C2896E523AD71EC264923BFD1B44E5F36CBE9DD57E2011F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
60
DNS requests
33
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2616 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6768 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6480 | procexp64.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
6480 | procexp64.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl%20 | unknown | — | — | whitelisted |
6808 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6480 | procexp64.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
6480 | procexp64.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_2010-07-06.crl | unknown | — | — | whitelisted |
6480 | procexp64.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
6480 | procexp64.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2876 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5796 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5796 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5336 | SearchApp.exe | 2.16.110.200:443 | www.bing.com | Akamai International B.V. | DE | unknown |
2616 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |