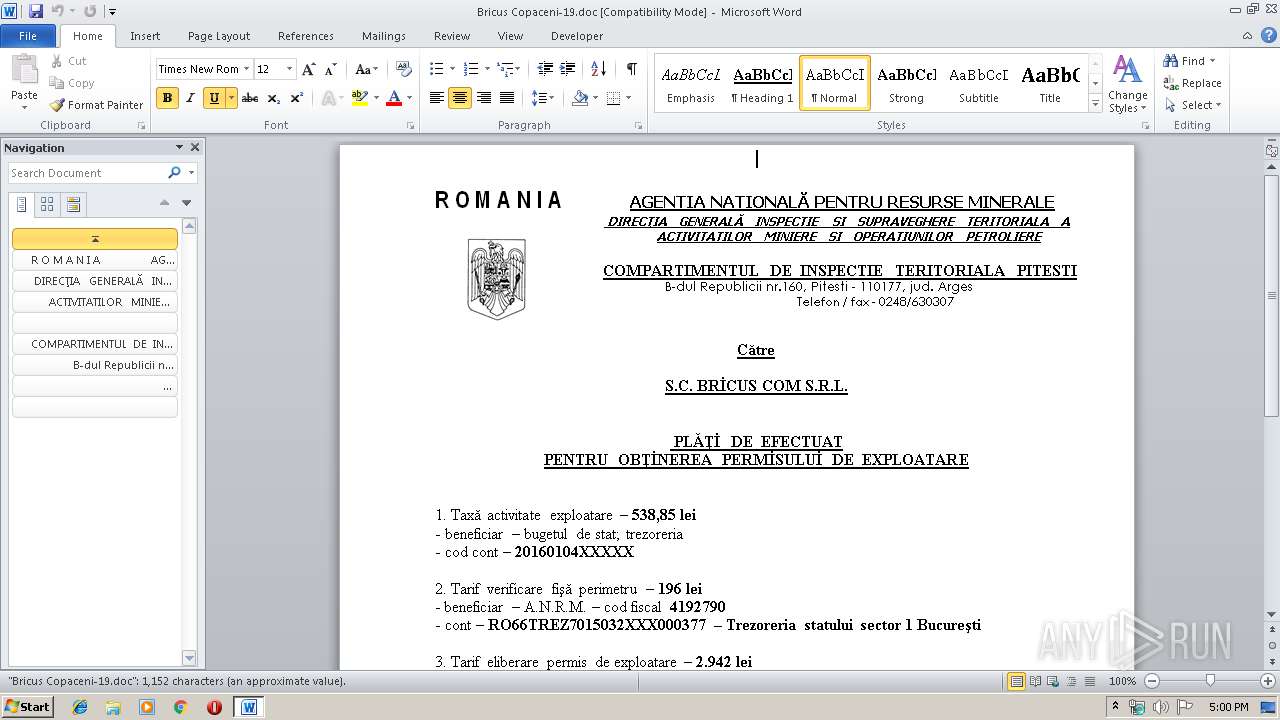
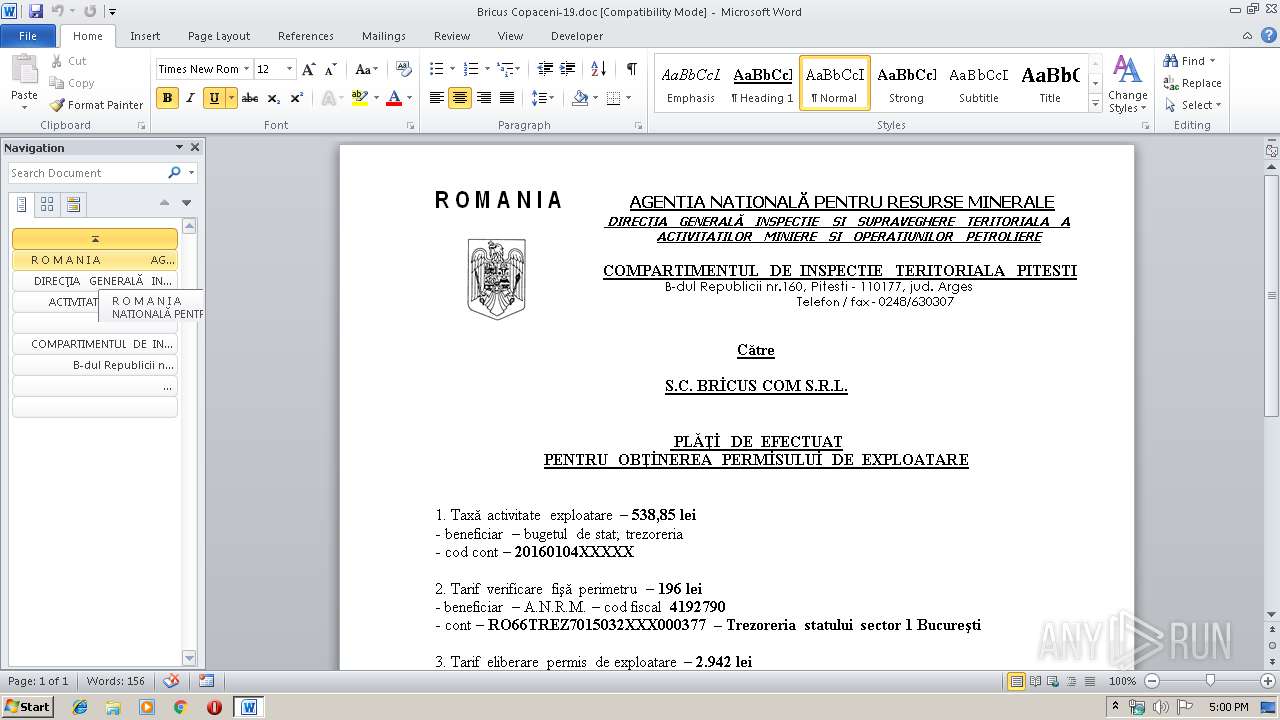
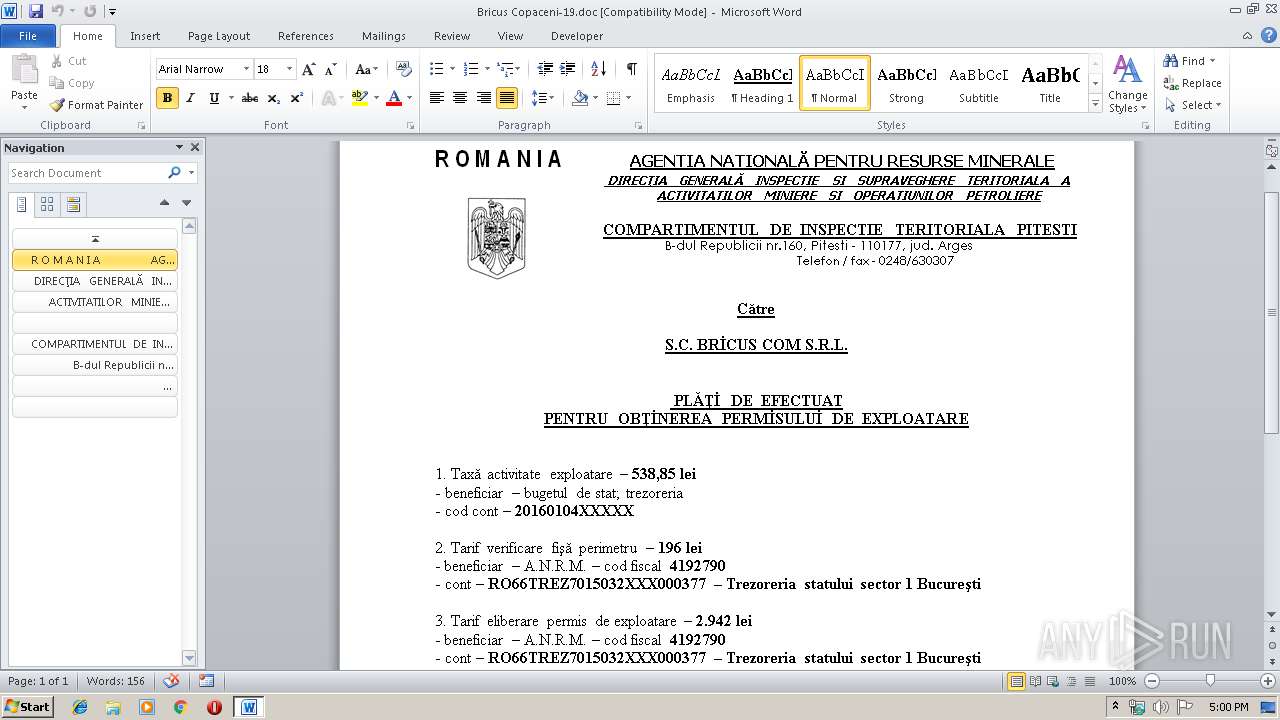
| File name: | Bricus Copaceni-19.doc |
| Full analysis: | https://app.any.run/tasks/e1d835be-3f77-466f-866c-6a406e8955e1 |
| Verdict: | No threats detected |
| Analysis date: | September 10, 2019, 15:59:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1250, Title: PLATI DE EFECTUAT PT, Author: C.I.T. Pitesti, Template: Normal, Last Saved By: Sorin, Revision Number: 3, Name of Creating Application: Microsoft Office Word, Total Editing Time: 03:00, Last Printed: Tue Jan 12 20:52:00 2016, Create Time/Date: Mon Sep 9 05:22:00 2019, Last Saved Time/Date: Mon Sep 9 05:25:00 2019, Number of Pages: 1, Number of Words: 205, Number of Characters: 1192, Security: 0 |
| MD5: | 9911DB44EDDAC4BCA6C623F5A24045B9 |
| SHA1: | E710FAA46A55A67EA80B7D5615C9065923B2AA72 |
| SHA256: | 105E981D97F4308E1DBA3547378A82CA350F89770716AFE45C126C06CDE4860A |
| SSDEEP: | 1536:r+fBemPmEwtsKjuVVfBemPmDO1QlJ8LI66rvZwtsKjuVP9:ruO4KjUjOa1QL8LX6bKjUP |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3424)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
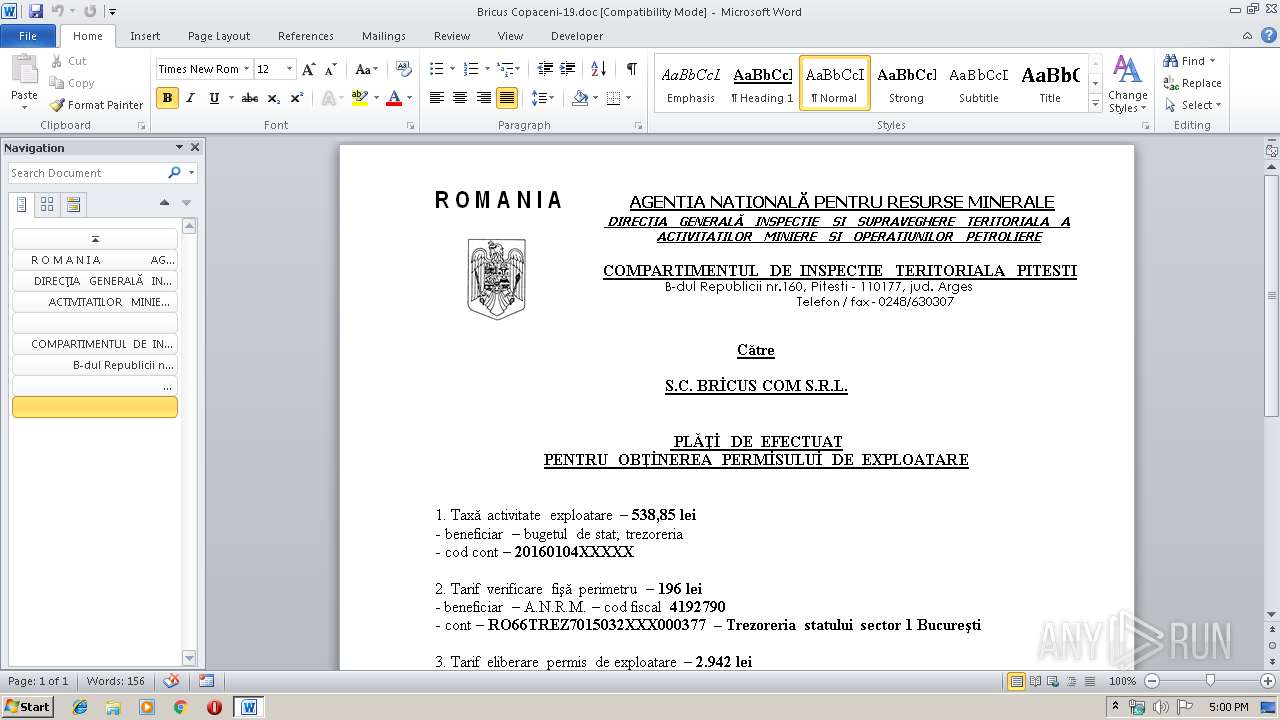
| Title: | PLATI DE EFECTUAT PT |
|---|---|
| Author: | C.I.T. Pitesti |
| Template: | Normal |
| LastModifiedBy: | Sorin |
| RevisionNumber: | 3 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 3.0 minutes |
| LastPrinted: | 2016:01:12 20:52:00 |
| CreateDate: | 2019:09:09 04:22:00 |
| ModifyDate: | 2019:09:09 04:25:00 |
| Pages: | 1 |
| Words: | 205 |
| Characters: | 1192 |
| Security: | None |
| CodePage: | Windows Latin 2 (Central European) |
| Company: | ANRM |
| Lines: | 9 |
| Paragraphs: | 2 |
| CharCountWithSpaces: | 1395 |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3424 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Bricus Copaceni-19.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 139
Read events
794
Write events
340
Delete events
5
Modification events
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | y# |
Value: 797F2300600D0000010000000000000000000000 | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1328152606 | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328152720 | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328152721 | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 600D00003CBC96CDF067D50100000000 | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 3 $ |
Value: 33202400600D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 3 $ |
Value: 33202400600D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9B6A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$icus Copaceni-19.doc | pgc | |
MD5:AC148F6266B12C5283F2D75C15C0C94A | SHA256:B8DFD43C19E7B622A633D931471CB2C2E7E02486D7FC4EC92AE194DC7C8A8241 | |||
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:62F2DA178DD59EBA6B61EE250E55F925 | SHA256:8CF938206B83D51659082A32A71F3A9F077217F5A2E07A98541350C60245A244 | |||
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryES0c0a.lex | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report