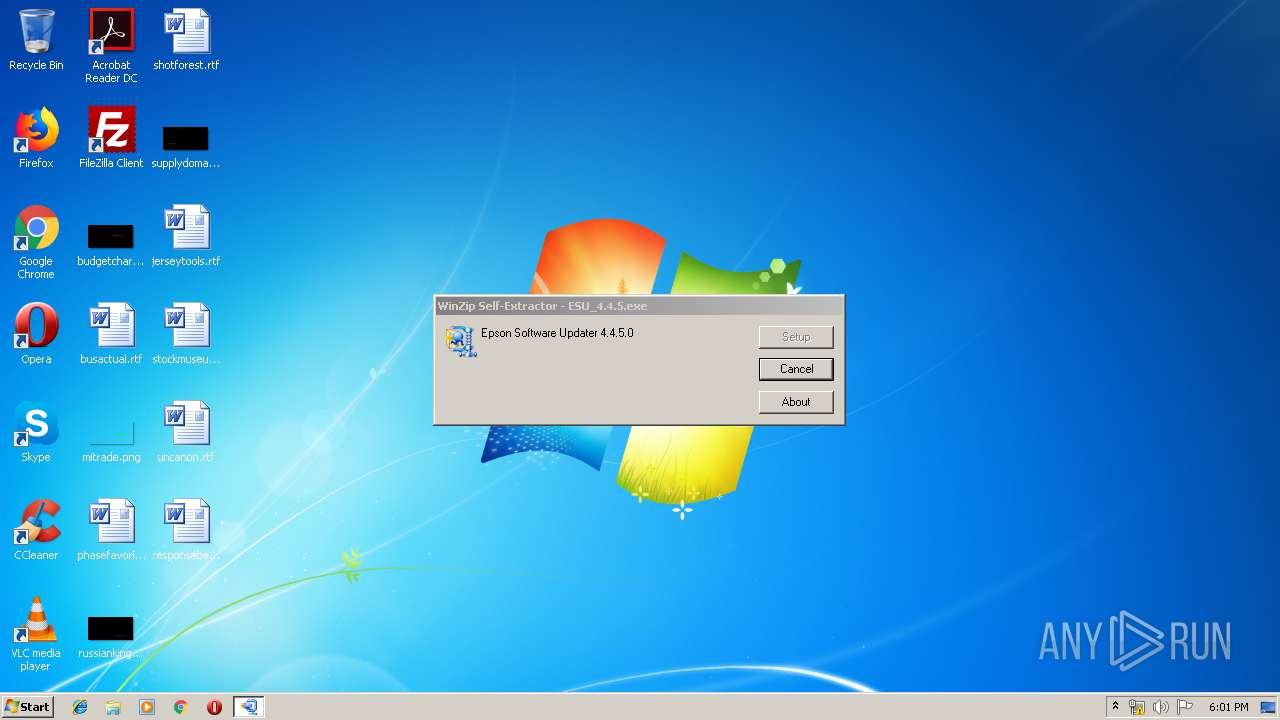
| File name: | ESU_4.4.5.exe |
| Full analysis: | https://app.any.run/tasks/da760d5f-6325-4980-ae89-0b1653753eae |
| Verdict: | No threats detected |
| Analysis date: | April 22, 2019, 17:01:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 32BC400CC7B82A99B639F08B7F2FDBE8 |
| SHA1: | DC5F05848CC1F6C29B26C416C29C33116E947362 |
| SHA256: | 105E01DDB8A1758592BF6ABC5D9365F552B1F93FE3279DEE460B513DCF148B29 |
| SSDEEP: | 98304:A7kf+368mX9FS+irPQJPZhCOa/RfmkeJ6zujMkWCTJoNTNiI1kEXJggJas:A7kf+T49FwYZ7COa/Ri010TJoNUkkE5R |
MALICIOUS
Application was dropped or rewritten from another process
- EPSDNEUL.EXE (PID: 2468)
- setup.exe (PID: 2268)
SUSPICIOUS
Executable content was dropped or overwritten
- ESU_4.4.5.exe (PID: 3852)
- ESU_4.4.5.exe (PID: 2620)
Reads internet explorer settings
- EPSDNEUL.EXE (PID: 2468)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (32.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (28.5) |
| .exe | | | Winzip Win32 self-extracting archive (generic) (23.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:02:17 03:33:57+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 86016 |
| InitializedDataSize: | 65536 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xccf4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Feb-2016 02:33:57 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 17-Feb-2016 02:33:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000145C4 | 0x00015000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51267 |
.rdata | 0x00016000 | 0x00003F82 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.2479 |
.data | 0x0001A000 | 0x0000E804 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.1761 |
.rsrc | 0x00029000 | 0x00009B6C | 0x0000A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.56407 |
_winzip_ | 0x00033000 | 0x00587000 | 0x00587000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.99908 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04419 | 1503 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.03621 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.14459 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.56342 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.99214 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.69605 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.83382 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 6.01045 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 4.68735 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
63 | 3.18826 | 764 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
GDI32.dll |
KERNEL32.dll |
SHELL32.dll (delay-loaded) |
Total processes
39
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1664 | "C:\Users\admin\AppData\Local\Temp\ESU_4.4.5.exe" | C:\Users\admin\AppData\Local\Temp\ESU_4.4.5.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2268 | .\data\setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\data\setup.exe | — | ESU_4.4.5.exe | |||||||||||
User: admin Company: Seiko Epson Corporation Integrity Level: HIGH Description: Software Updater Installer Exit code: 0 Version: 4.0.2 Modules
| |||||||||||||||
| 2468 | "C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\data\EPSDNEUL.EXE" /LO:"7" | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\data\EPSDNEUL.EXE | — | setup.exe | |||||||||||
User: admin Company: Seiko Epson Corporation Integrity Level: HIGH Description: Epson EULA Navi for x86 Exit code: 0 Version: 1.0.7.0 Modules
| |||||||||||||||
| 2620 | "C:\Users\admin\AppData\Local\Temp\ESU_4.4.5.exe" | C:\Users\admin\AppData\Local\Temp\ESU_4.4.5.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3852 | run=1 shortcut="C:\Users\admin\AppData\Local\Temp\ESU_4.4.5.exe" | C:\Users\admin\AppData\Local\Temp\e777d\ESU_4.4.5.exe | ESU_4.4.5.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
395
Read events
387
Write events
8
Delete events
0
Modification events
| (PID) Process: | (2268) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2268) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2468) EPSDNEUL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2468) EPSDNEUL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3852 | ESU_4.4.5.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\Data\Setup.msi | — | |
MD5:— | SHA256:— | |||
| 3852 | ESU_4.4.5.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\Data\VERINFO.ESI | ini | |
MD5:— | SHA256:— | |||
| 2620 | ESU_4.4.5.exe | C:\Users\admin\AppData\Local\Temp\e777d\ESU_4.4.5.exe | executable | |
MD5:— | SHA256:— | |||
| 2468 | EPSDNEUL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\200[1] | html | |
MD5:911D465B73FE634A2A8FB05AEBD3DD0C | SHA256:B17ED1B092E714E8A73ACB74B56DCF15746CFE92725C64B8ABD1718927700CCE | |||
| 2468 | EPSDNEUL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\200[1] | html | |
MD5:911D465B73FE634A2A8FB05AEBD3DD0C | SHA256:B17ED1B092E714E8A73ACB74B56DCF15746CFE92725C64B8ABD1718927700CCE | |||
| 3852 | ESU_4.4.5.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\Data\Setup.exe | executable | |
MD5:20576F86F202DB42CF05704FA4531AFF | SHA256:59224A4346B799AC5F9CB1FD6F4817565F1B3027B81011FE691FD1A8054FAC03 | |||
| 3852 | ESU_4.4.5.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\Data\EPSDNEUL.EXE | executable | |
MD5:4F106EFBE934DE5CCC7B05A5E0F5B988 | SHA256:7C1ADBA646290F2F8C0B98B5B319258B720077134B1259CE6B44013B2E5F6425 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report