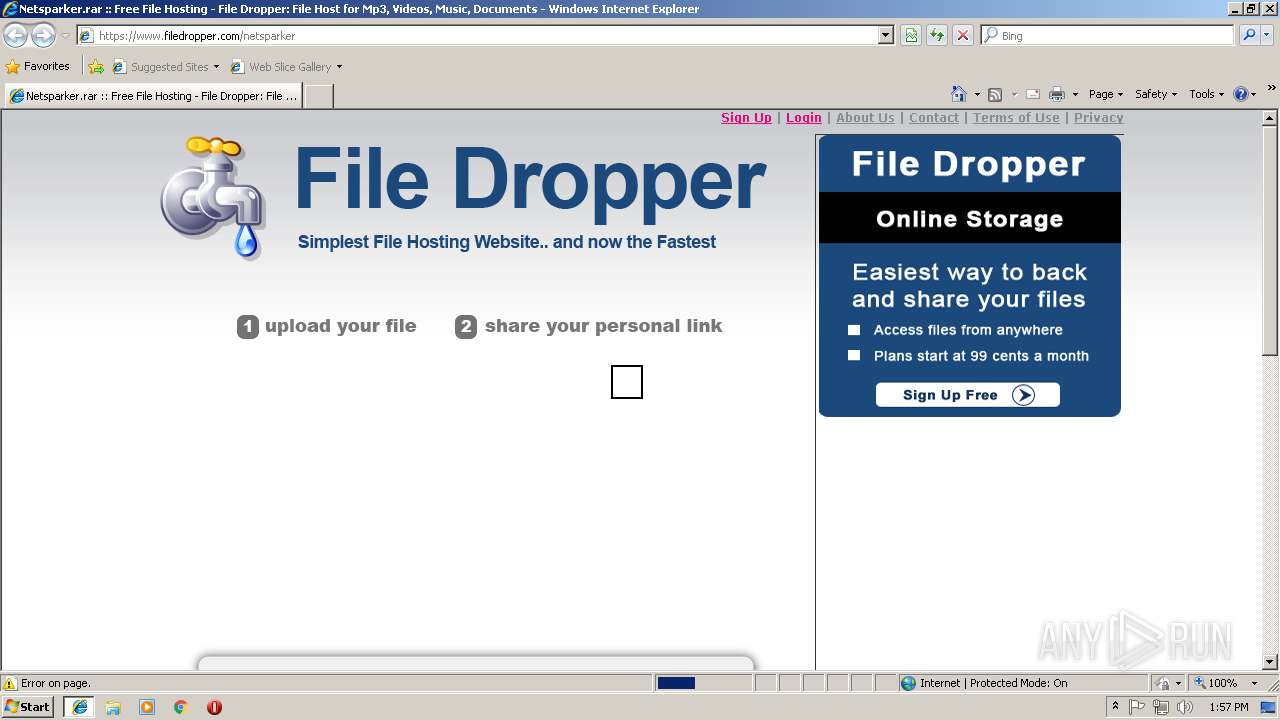
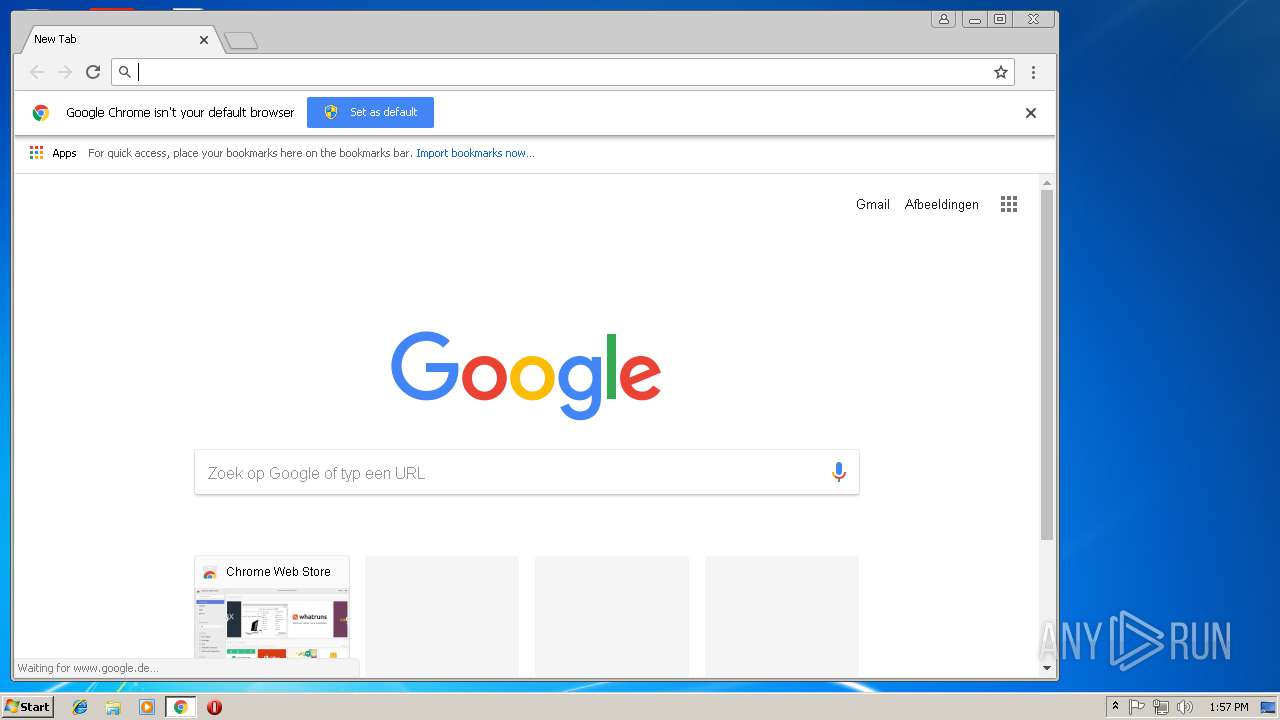
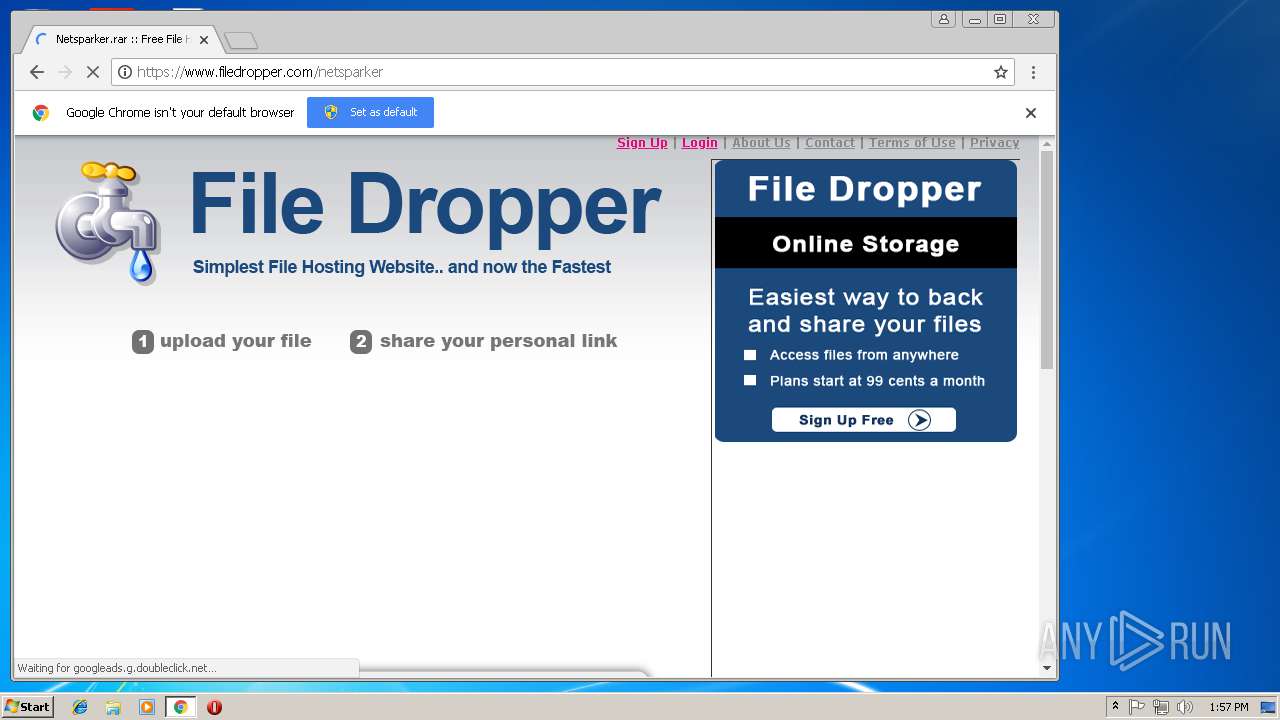
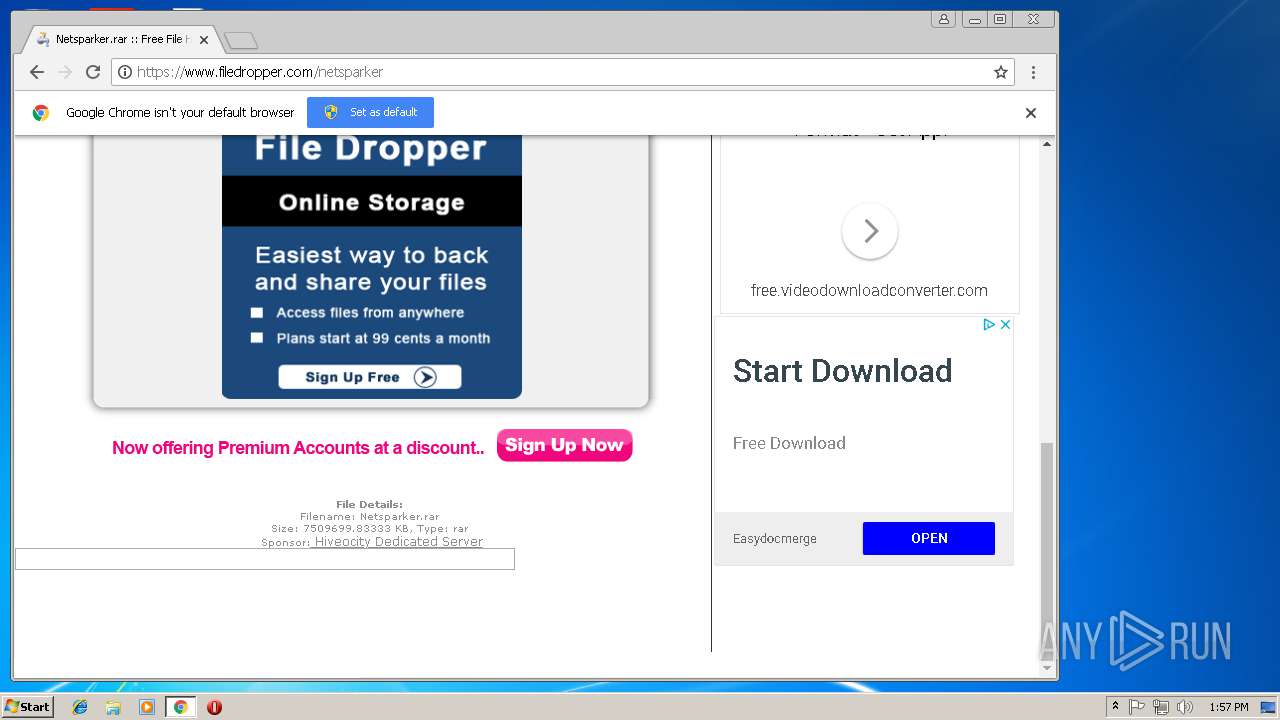
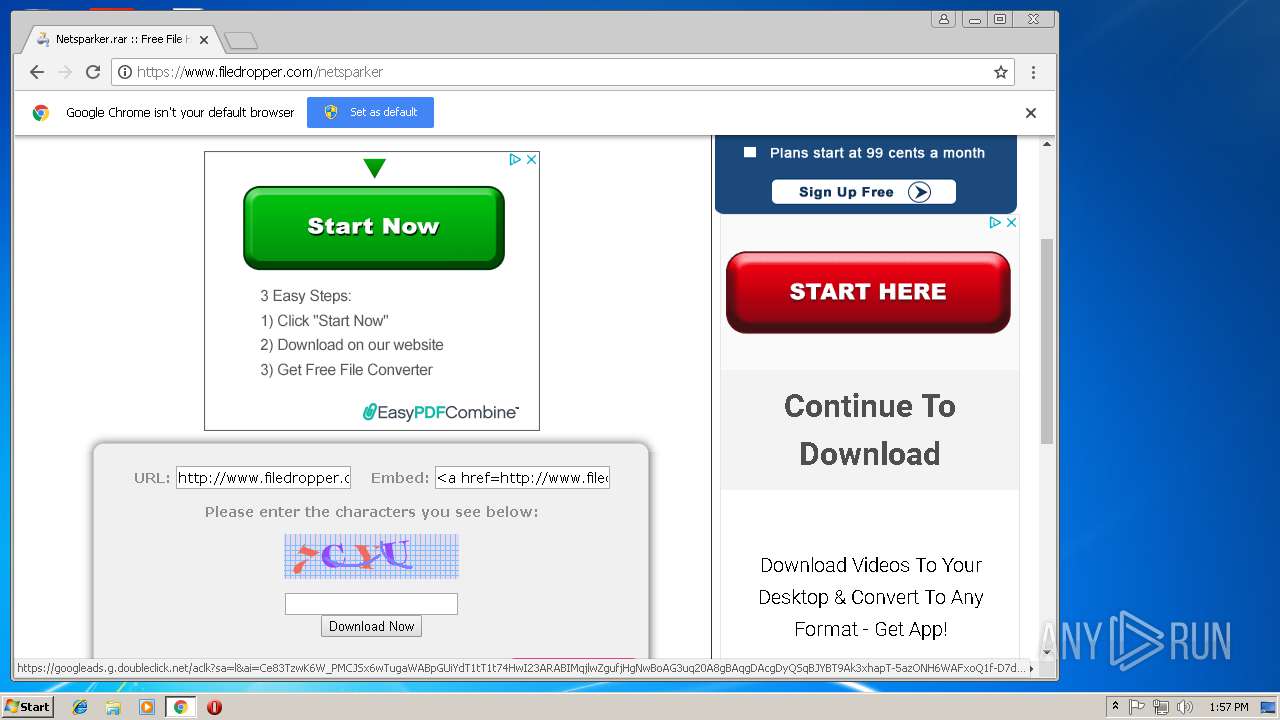
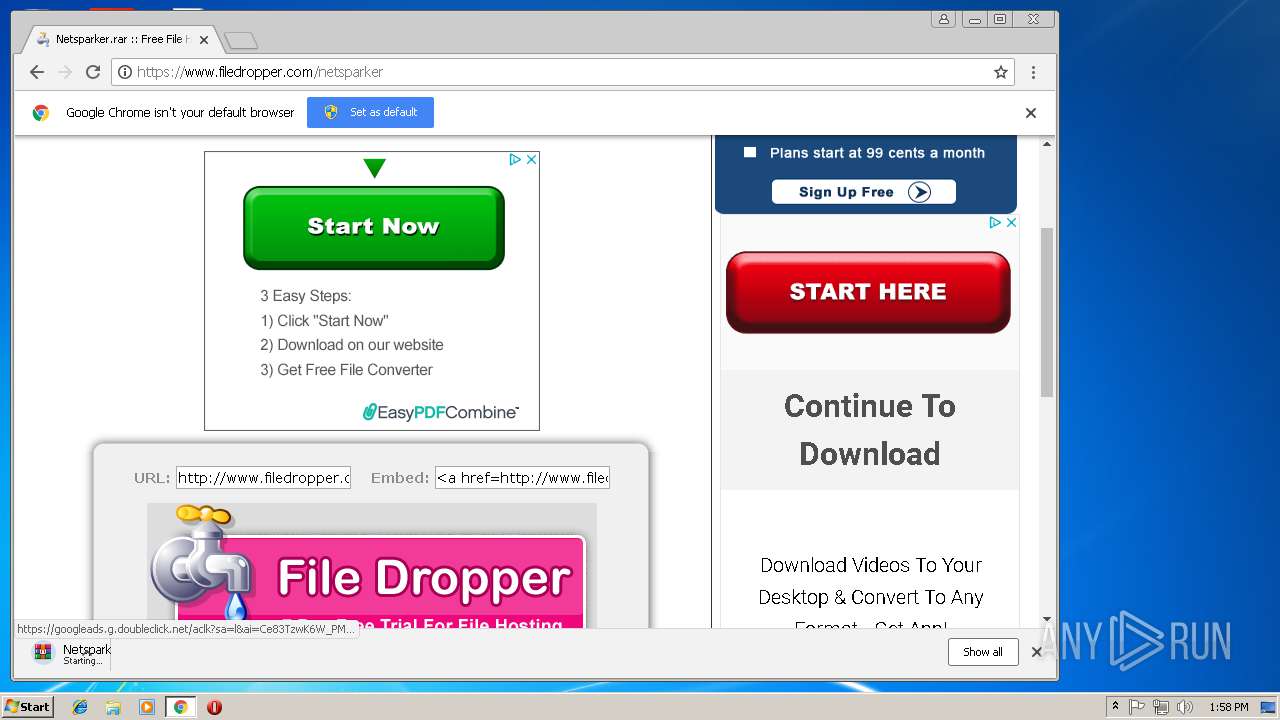
| URL: | https://www.filedropper.com/netsparker |
| Full analysis: | https://app.any.run/tasks/a553a8c7-73c0-4061-a08c-6927ea02bba5 |
| Verdict: | Malicious activity |
| Analysis date: | October 07, 2018, 12:57:06 |
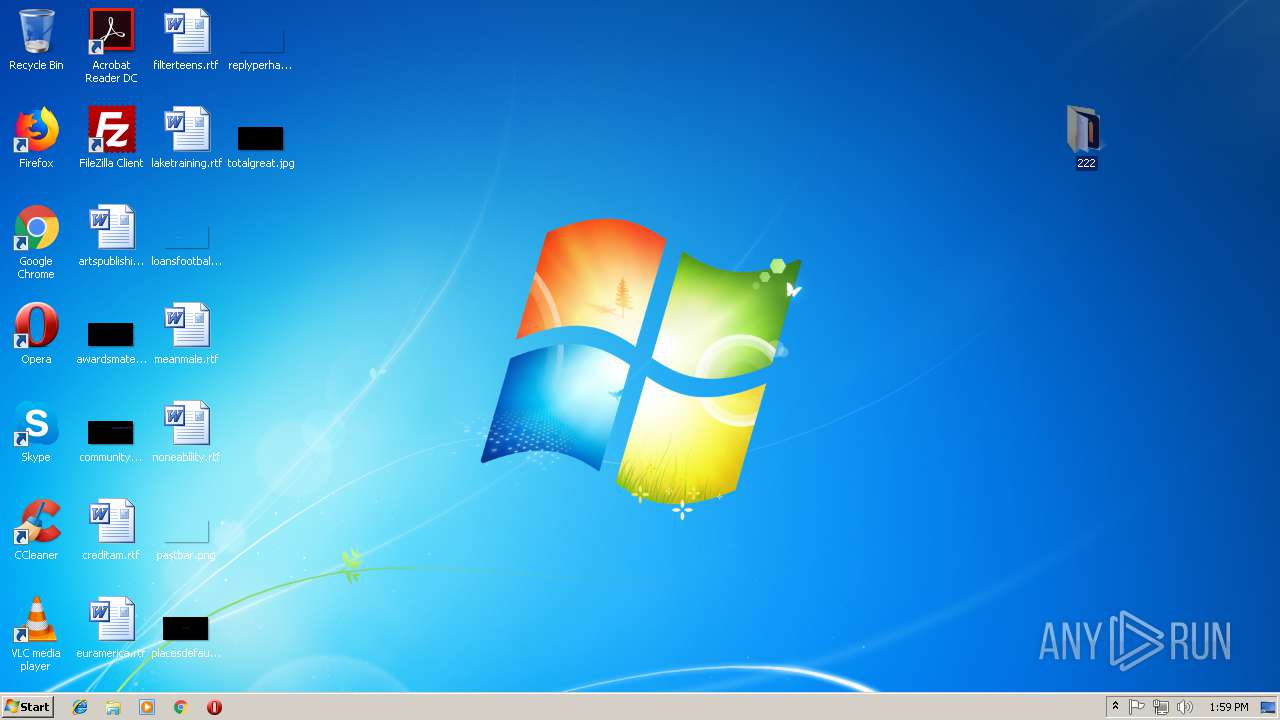
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 38D221BDB61DEEA27826D88A02CE822B |
| SHA1: | 04147CDB7B36253D40F5A909449FFD8728812D07 |
| SHA256: | 1053F7B9818528C16652EC2FF27C534F7737881C69B7876D9D9A0B1ADE1A3F40 |
| SSDEEP: | 3:N8DSLQuXreWVE/:2OLQzSE/ |
MALICIOUS
Application was dropped or rewritten from another process
- PdfGenerator.exe (PID: 360)
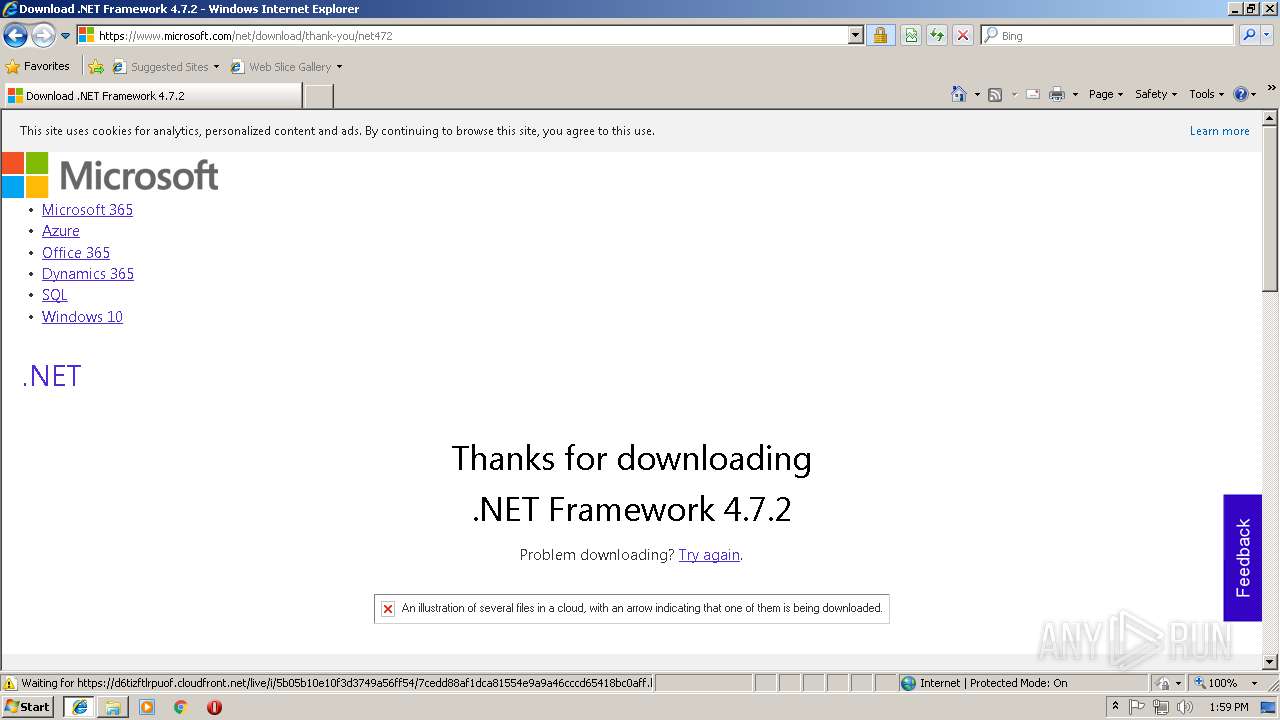
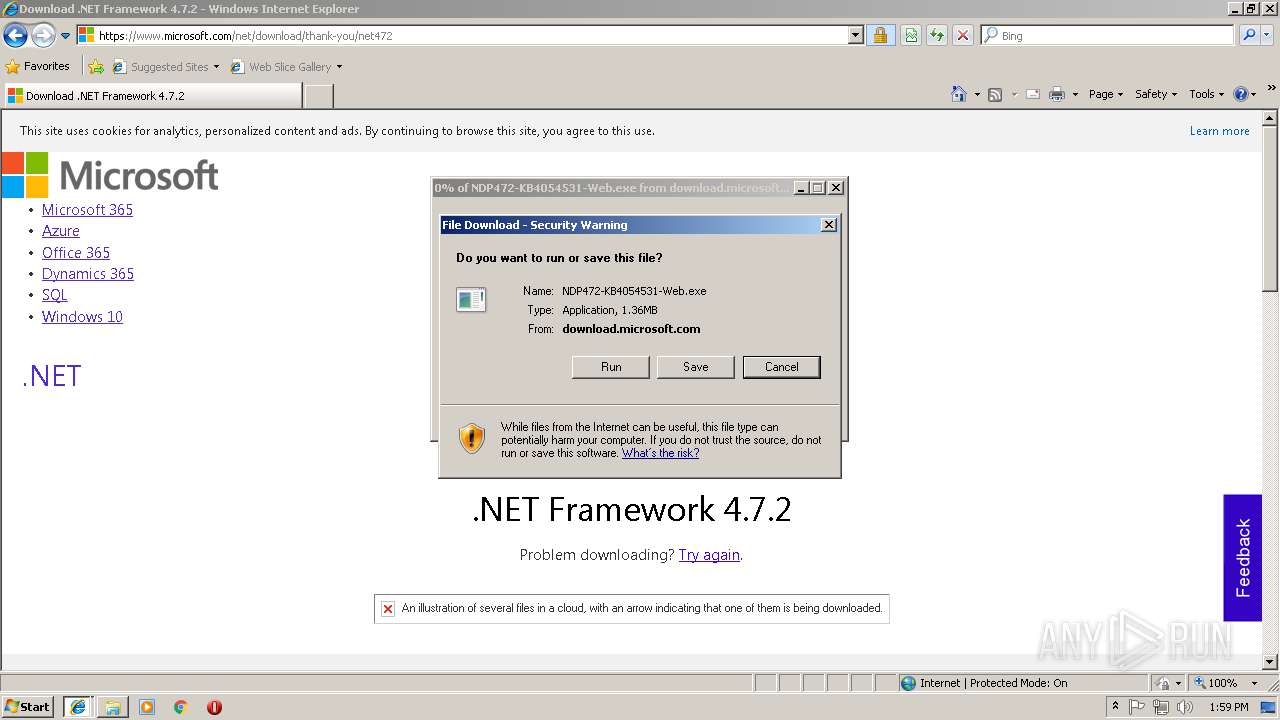
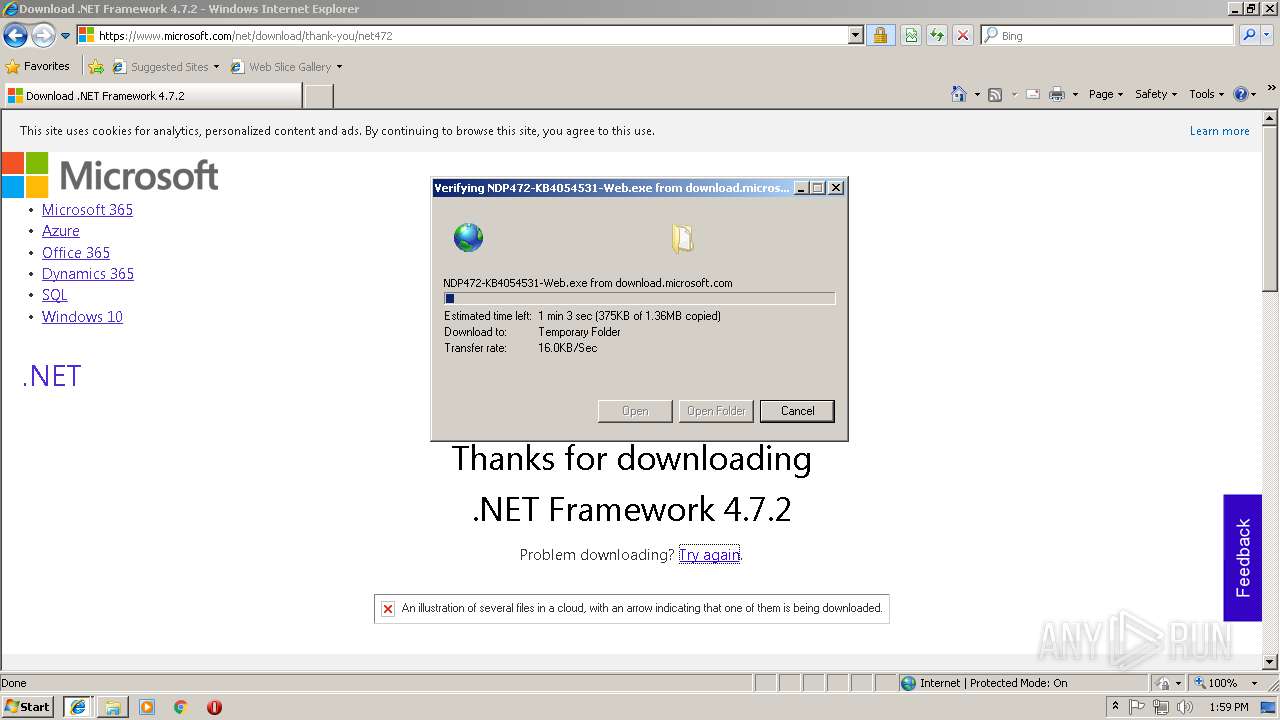
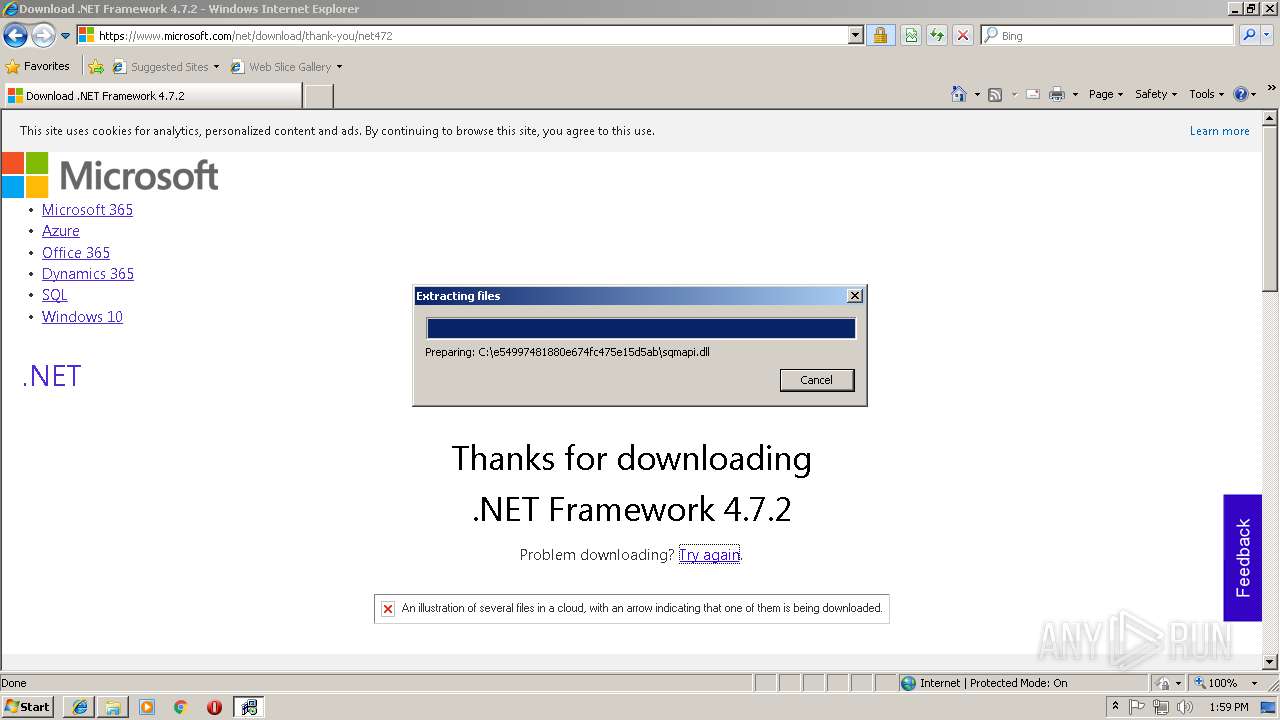
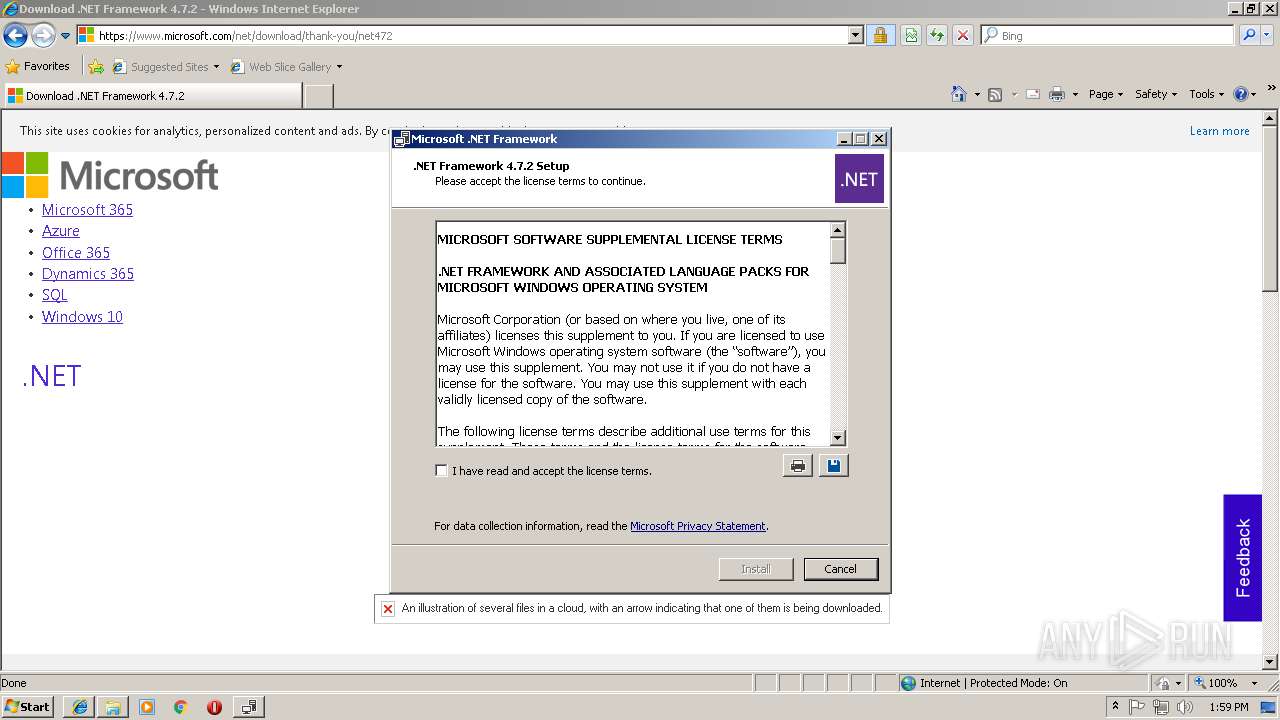
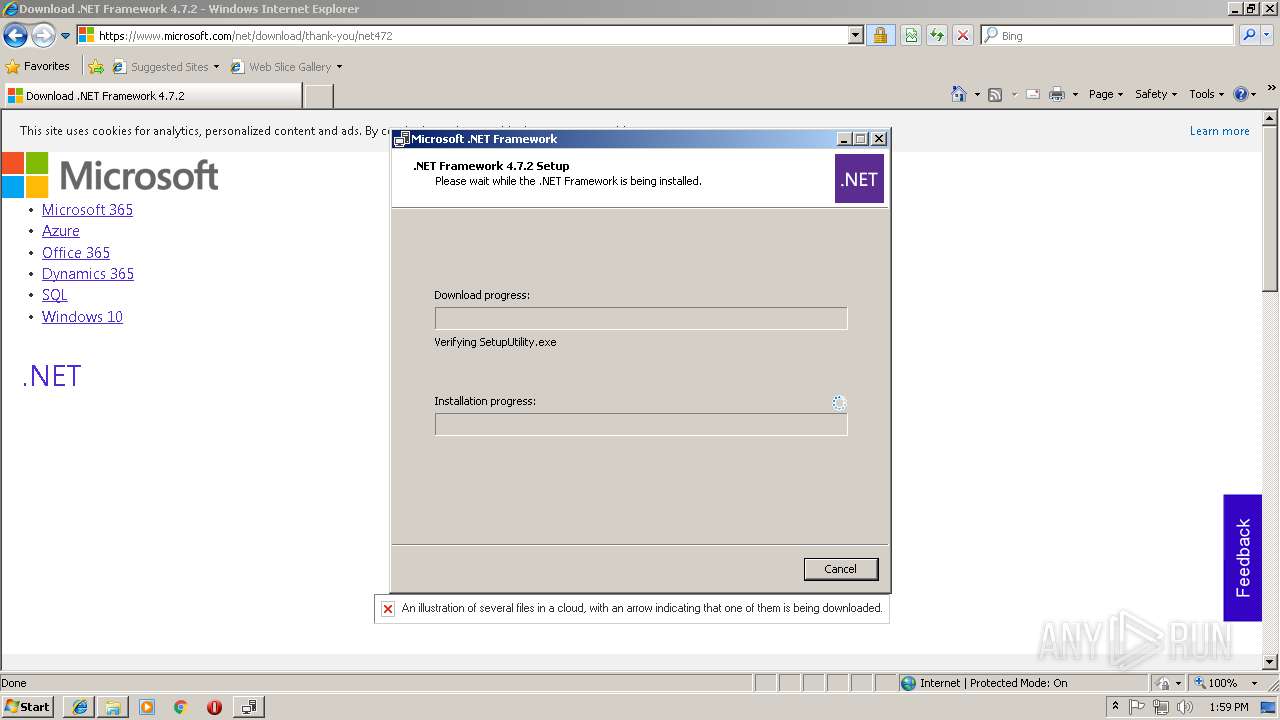
- NDP472-KB4054531-Web[1].exe (PID: 3900)
- SetupUtility.exe (PID: 2516)
- SetupUtility.exe (PID: 2472)
- NDP472-KB4054531-Web[1].exe (PID: 2120)
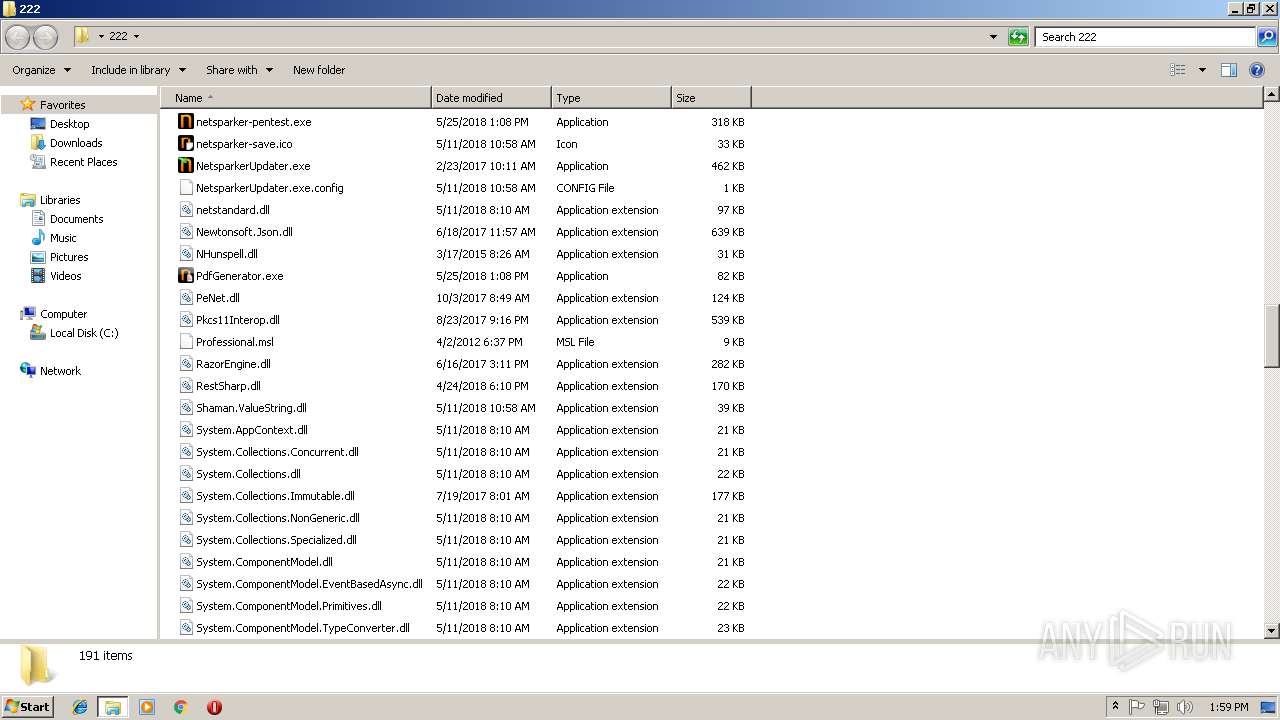
- NetSparker.exe (PID: 2760)
- Setup.exe (PID: 940)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2660)
- Setup.exe (PID: 940)
Changes settings of System certificates
- Setup.exe (PID: 940)
SUSPICIOUS
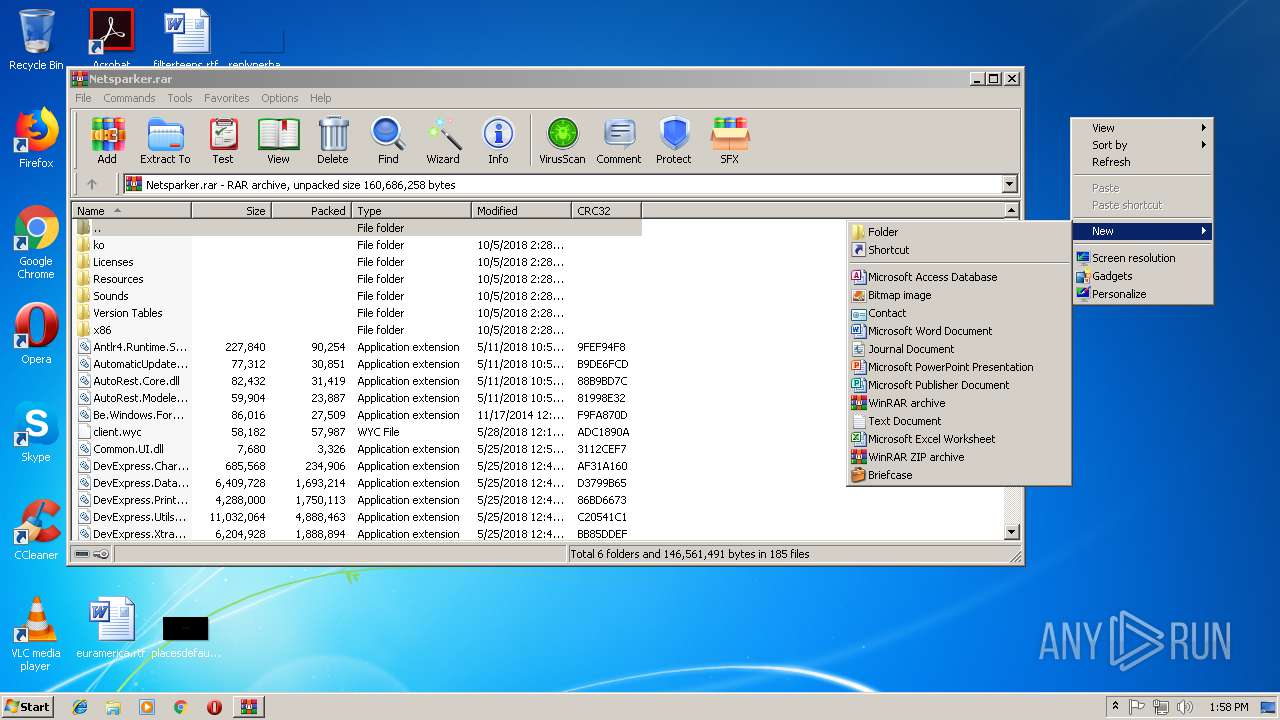
Executable content was dropped or overwritten
- iexplore.exe (PID: 3244)
- iexplore.exe (PID: 3552)
- TMP708B.tmp.exe (PID: 3232)
- NDP472-KB4054531-Web[1].exe (PID: 2120)
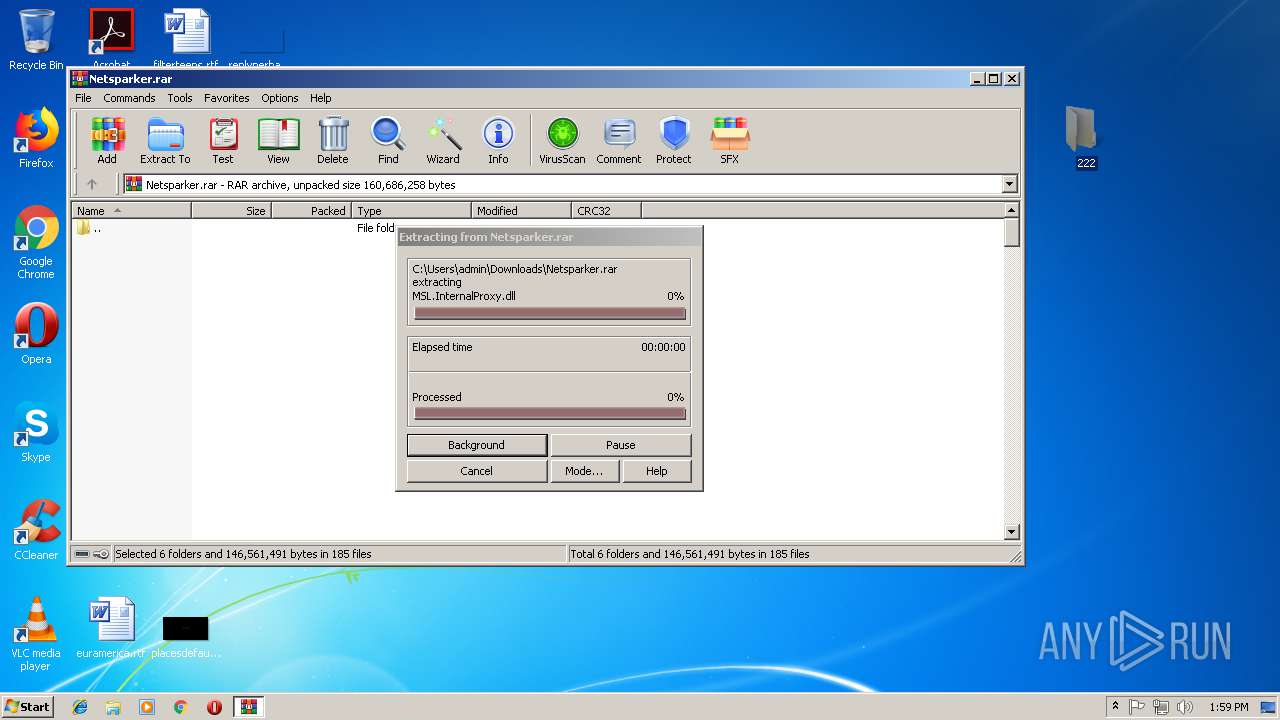
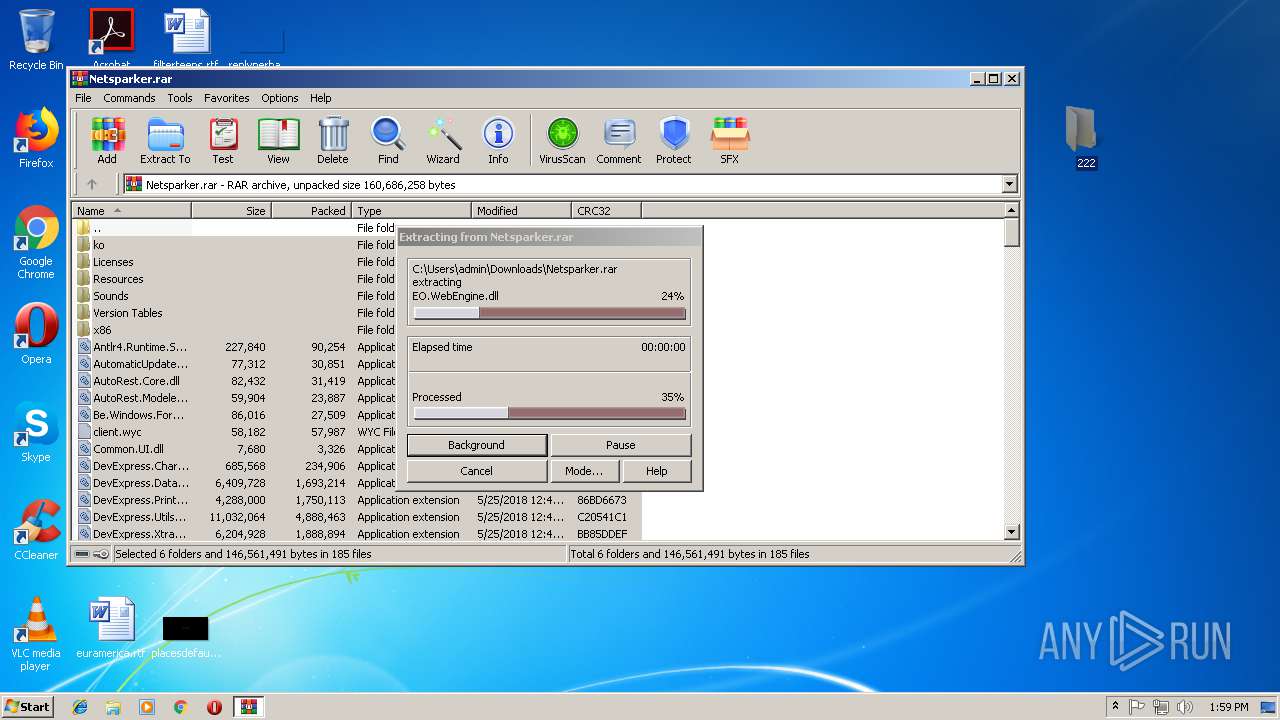
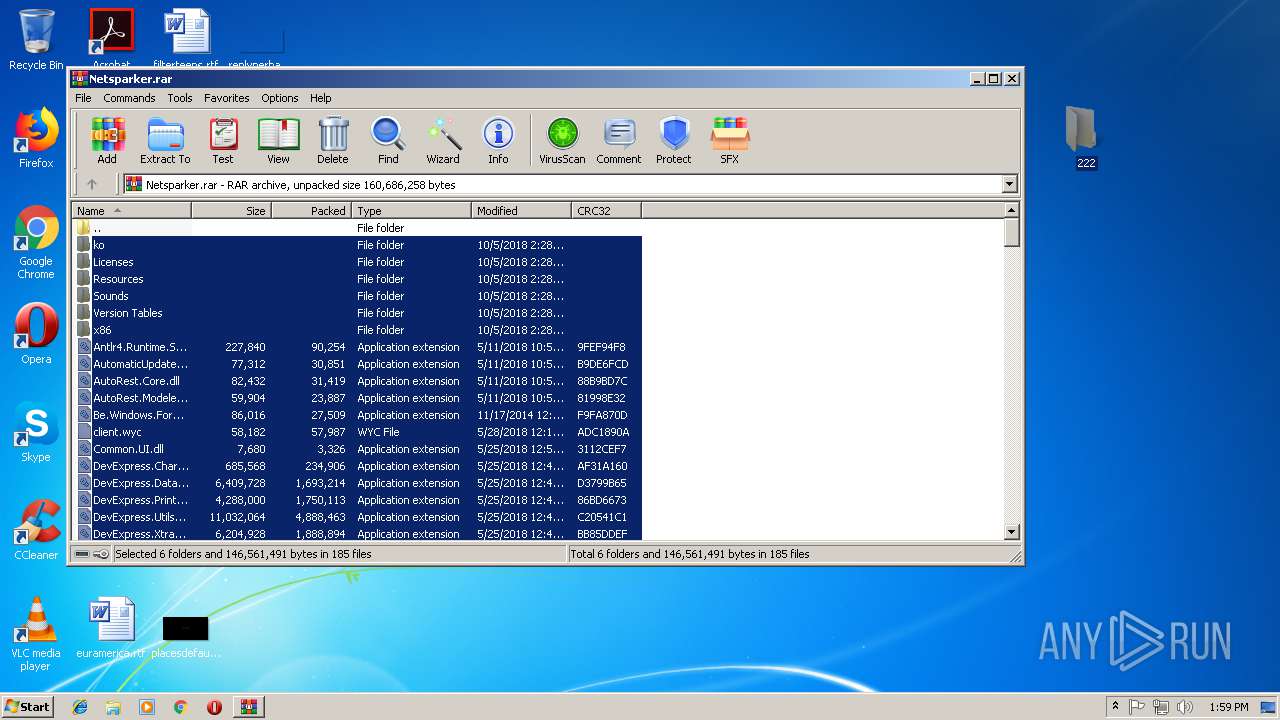
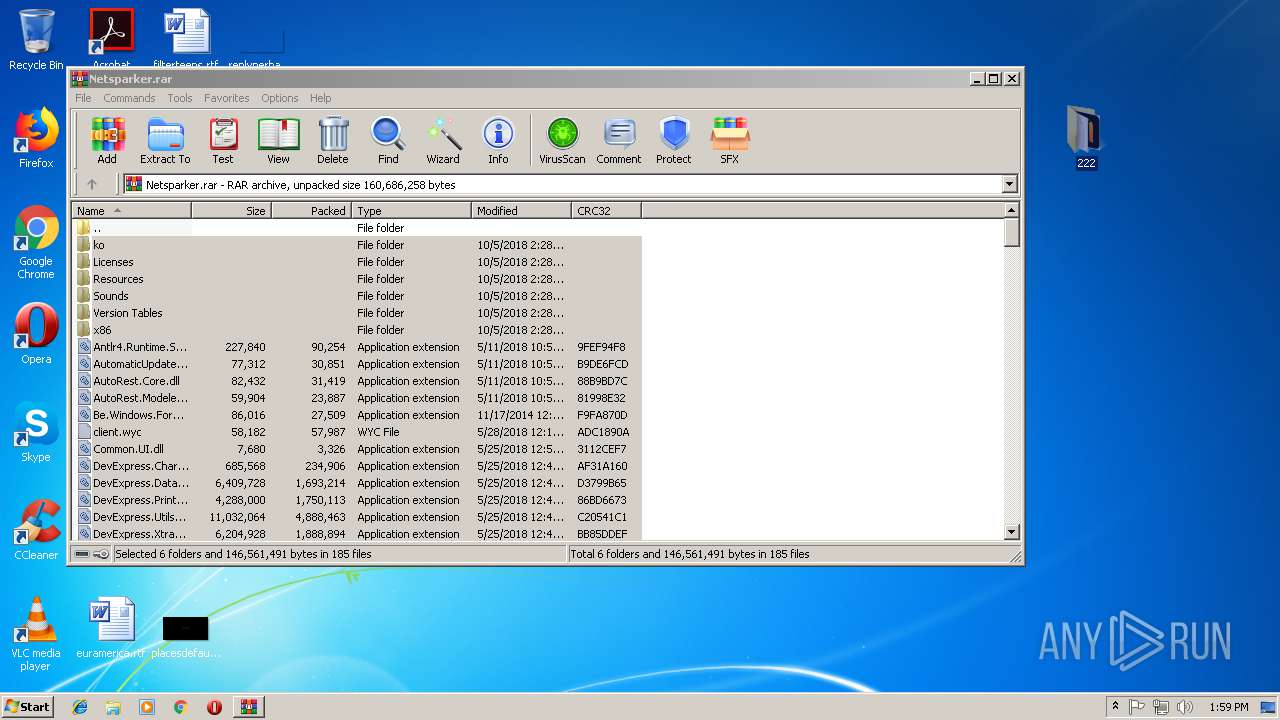
- WinRAR.exe (PID: 2808)
- Setup.exe (PID: 940)
Adds / modifies Windows certificates
- Setup.exe (PID: 940)
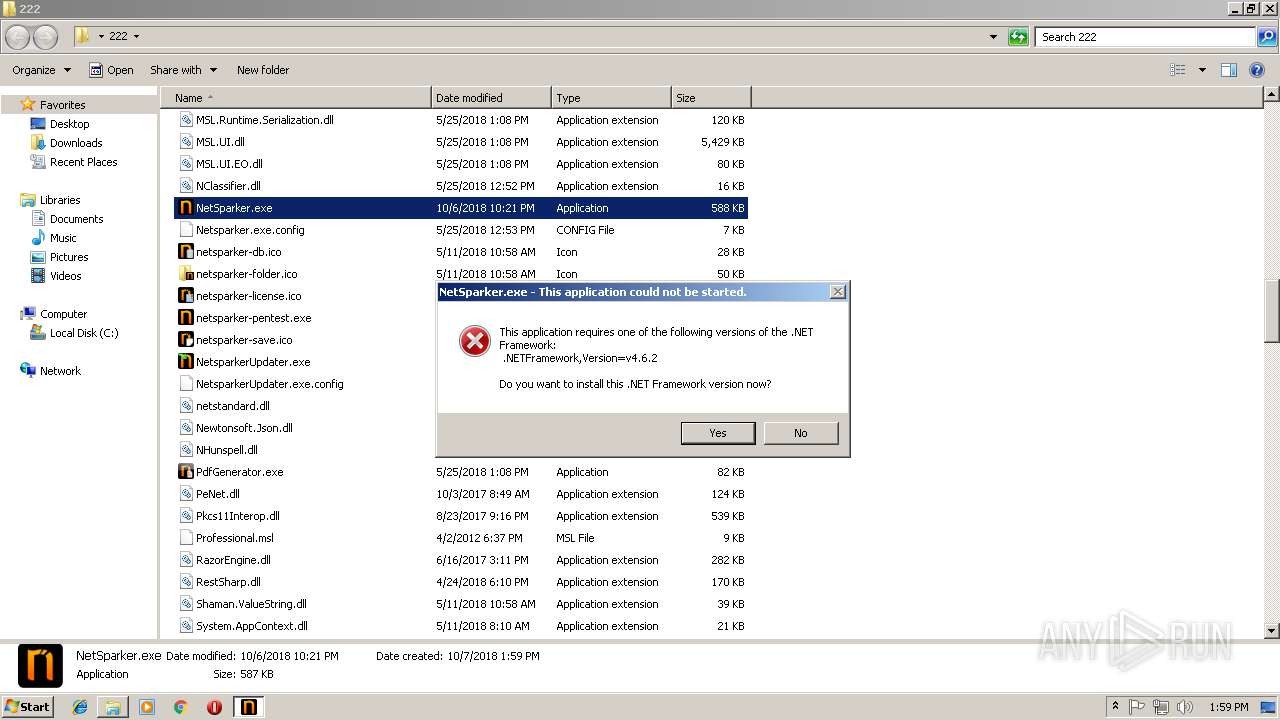
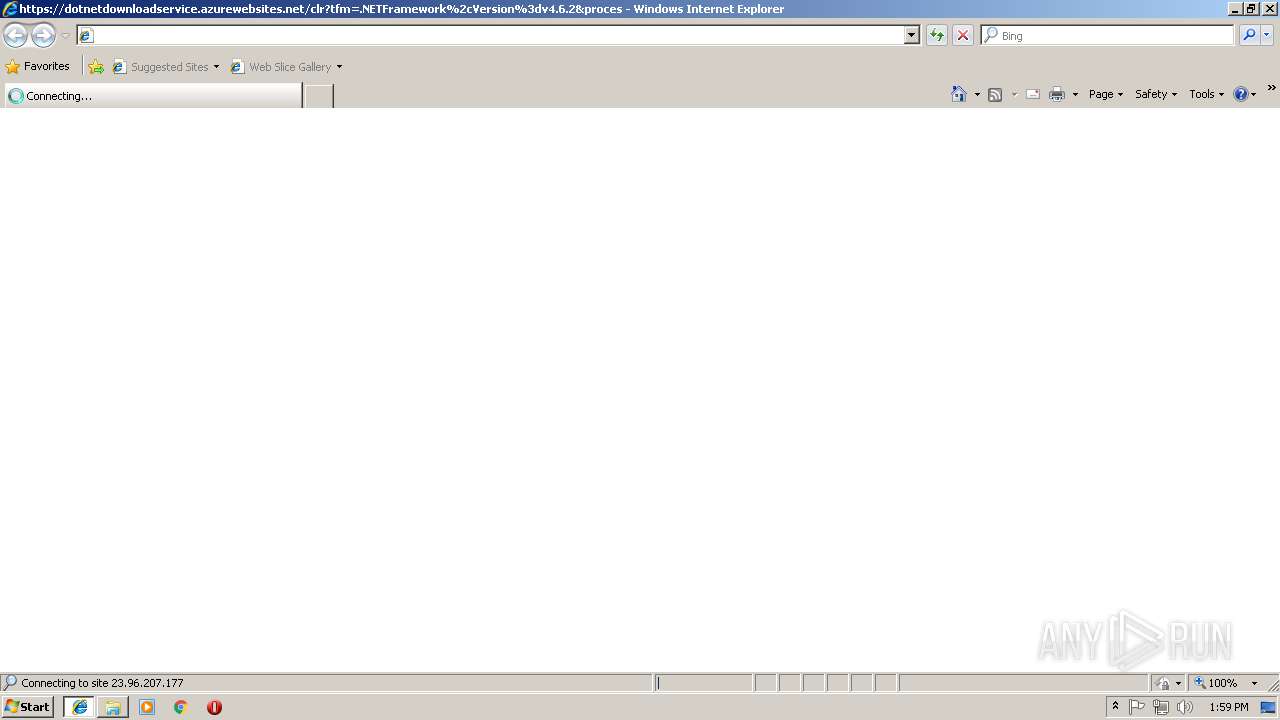
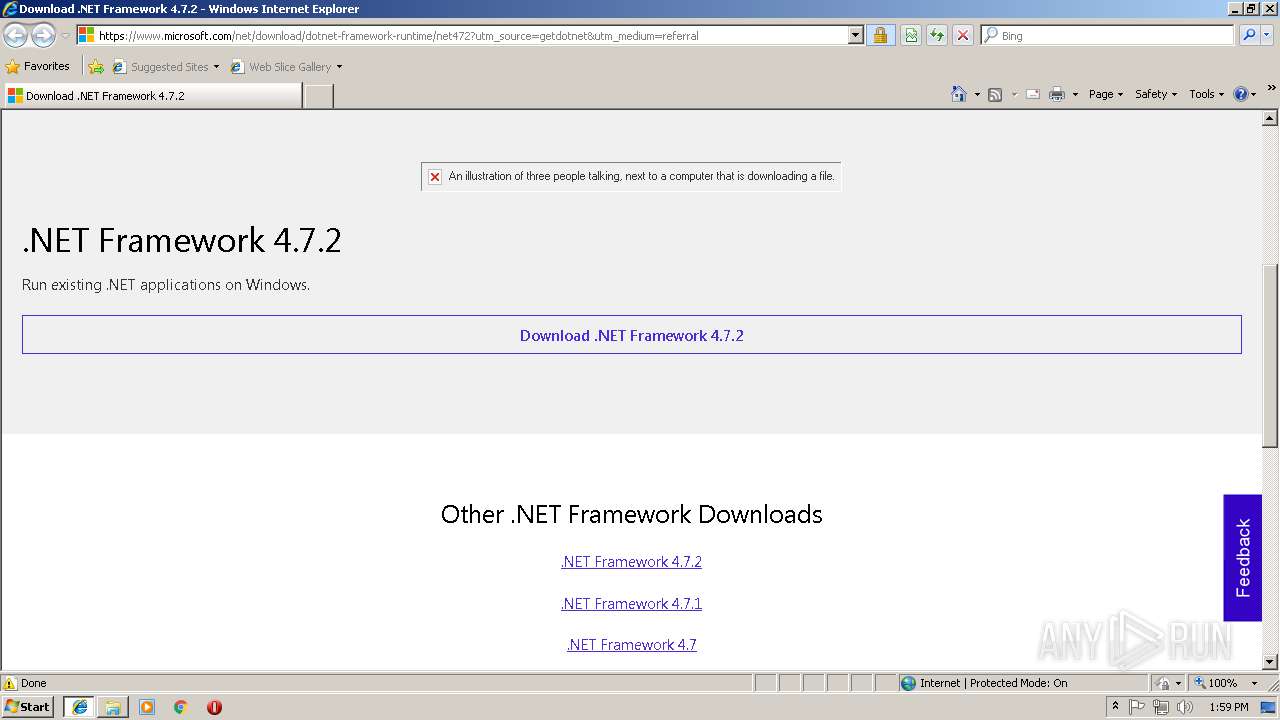
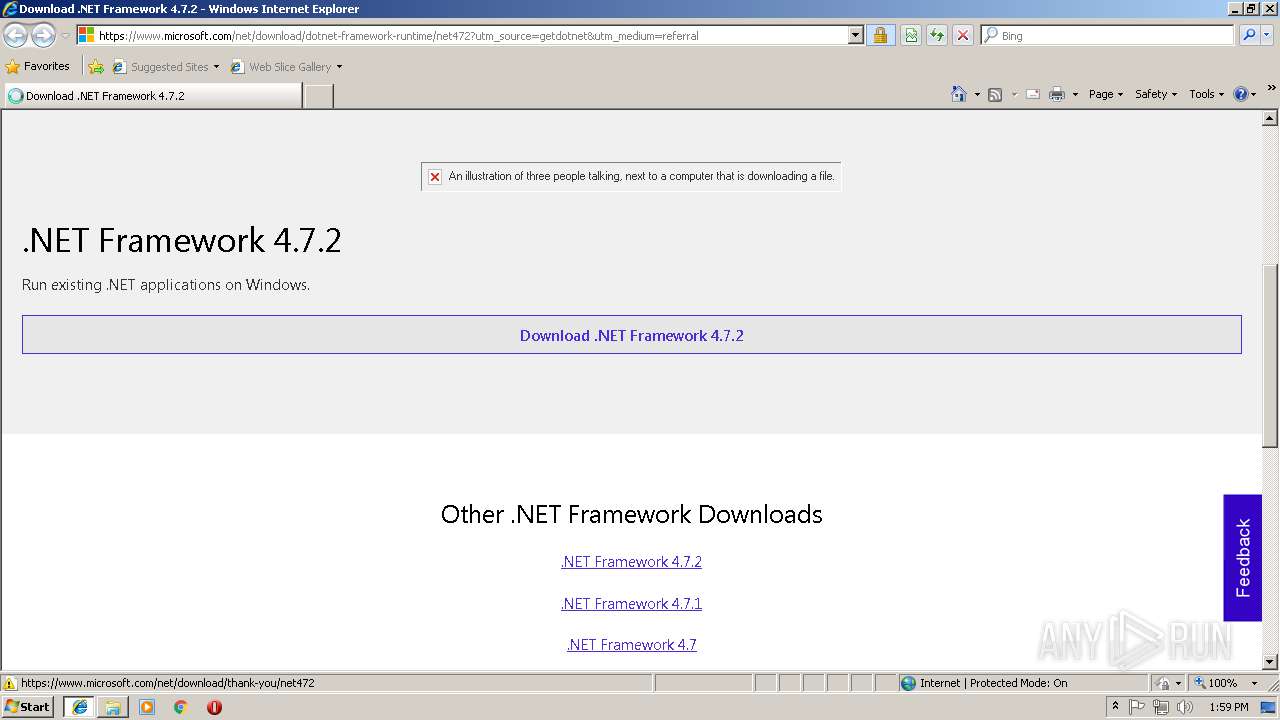
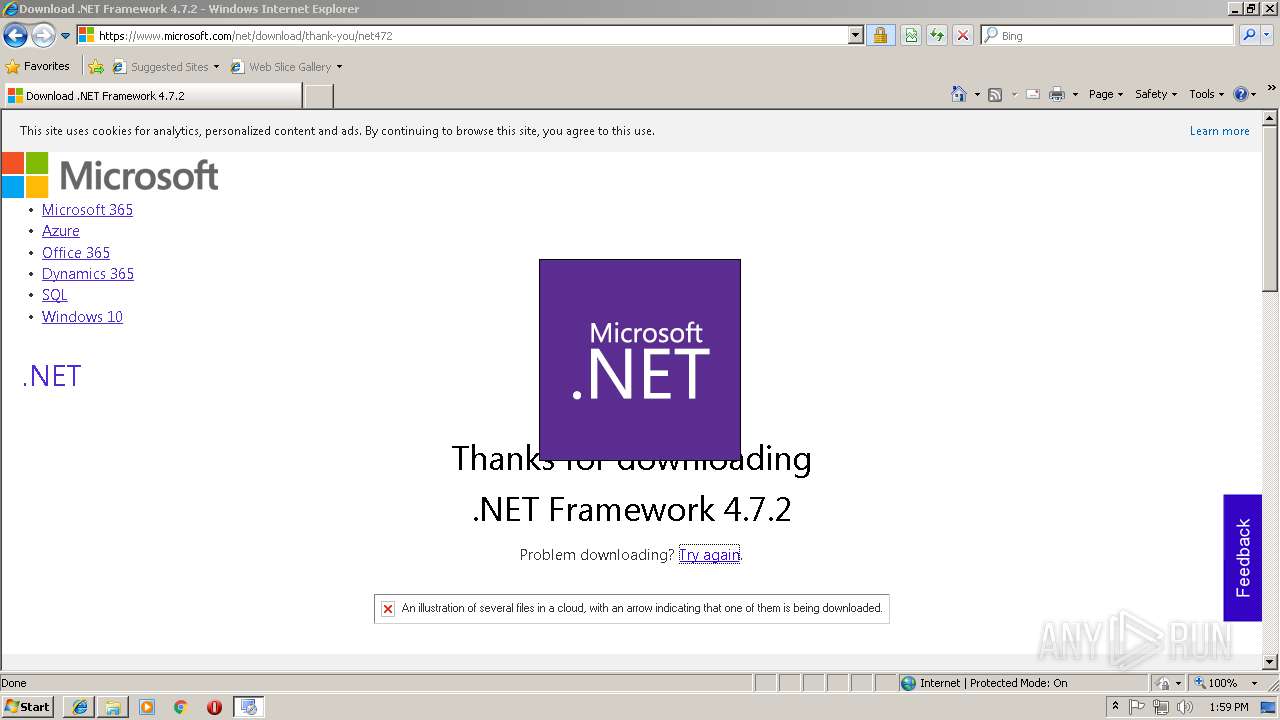
Starts Internet Explorer
- NetSparker.exe (PID: 2760)
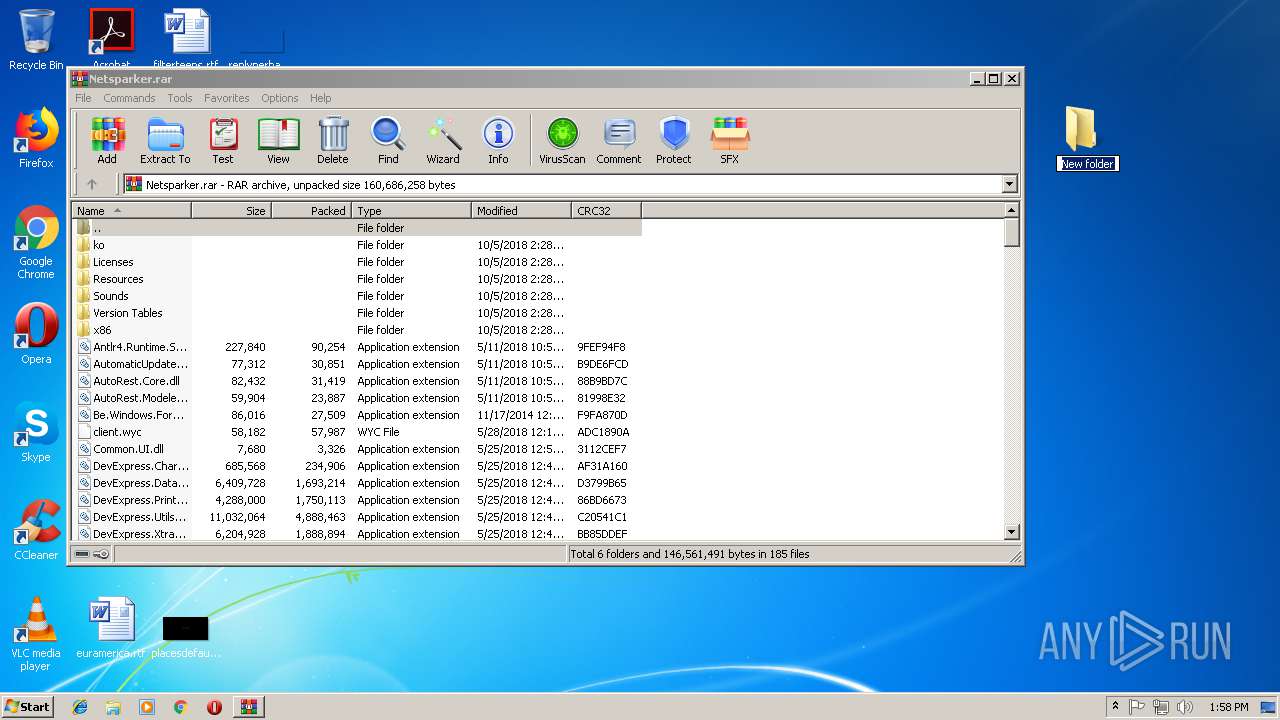
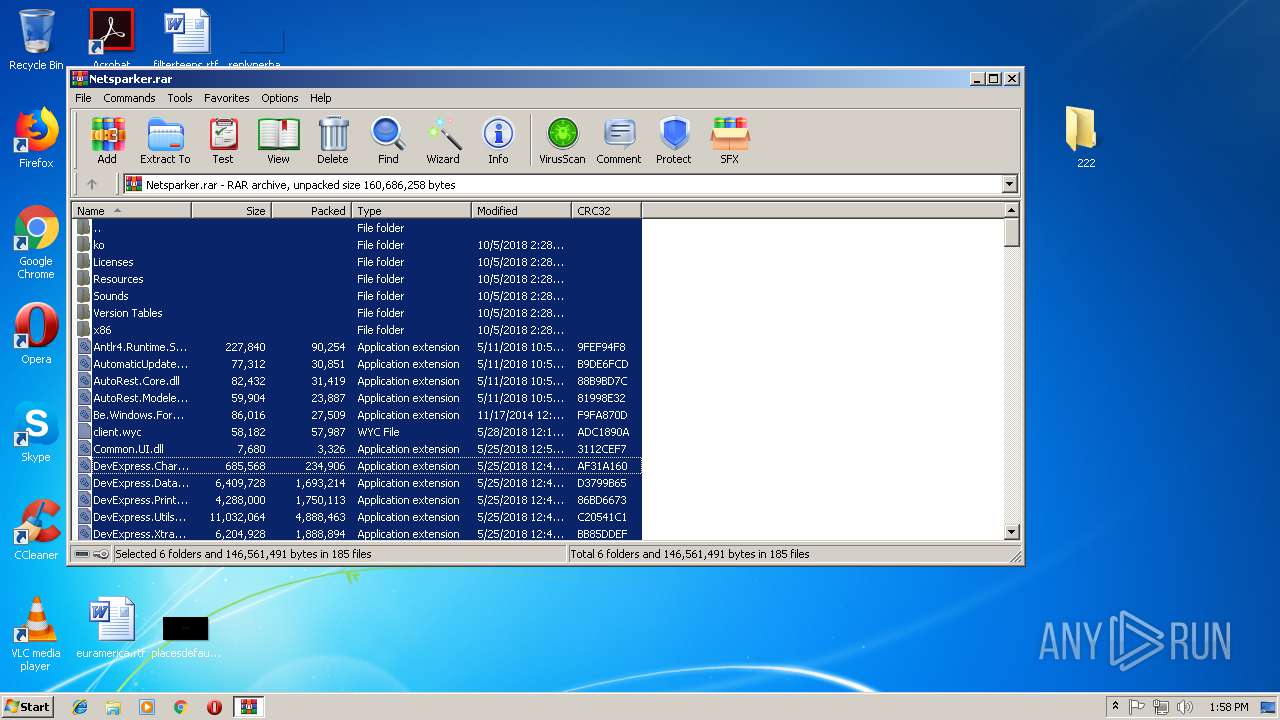
Creates files in the user directory
- Setup.exe (PID: 940)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2480)
- iexplore.exe (PID: 3552)
Reads Internet Cache Settings
- iexplore.exe (PID: 2108)
- chrome.exe (PID: 3696)
- iexplore.exe (PID: 3244)
Application launched itself
- chrome.exe (PID: 3696)
Creates files in the user directory
- iexplore.exe (PID: 2108)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3576)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3552)
Reads settings of System Certificates
- iexplore.exe (PID: 3552)
- Setup.exe (PID: 940)
Reads internet explorer settings
- iexplore.exe (PID: 2108)
- iexplore.exe (PID: 3244)
Dropped object may contain Bitcoin addresses
- Setup.exe (PID: 940)
Changes settings of System certificates
- iexplore.exe (PID: 3552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
27
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
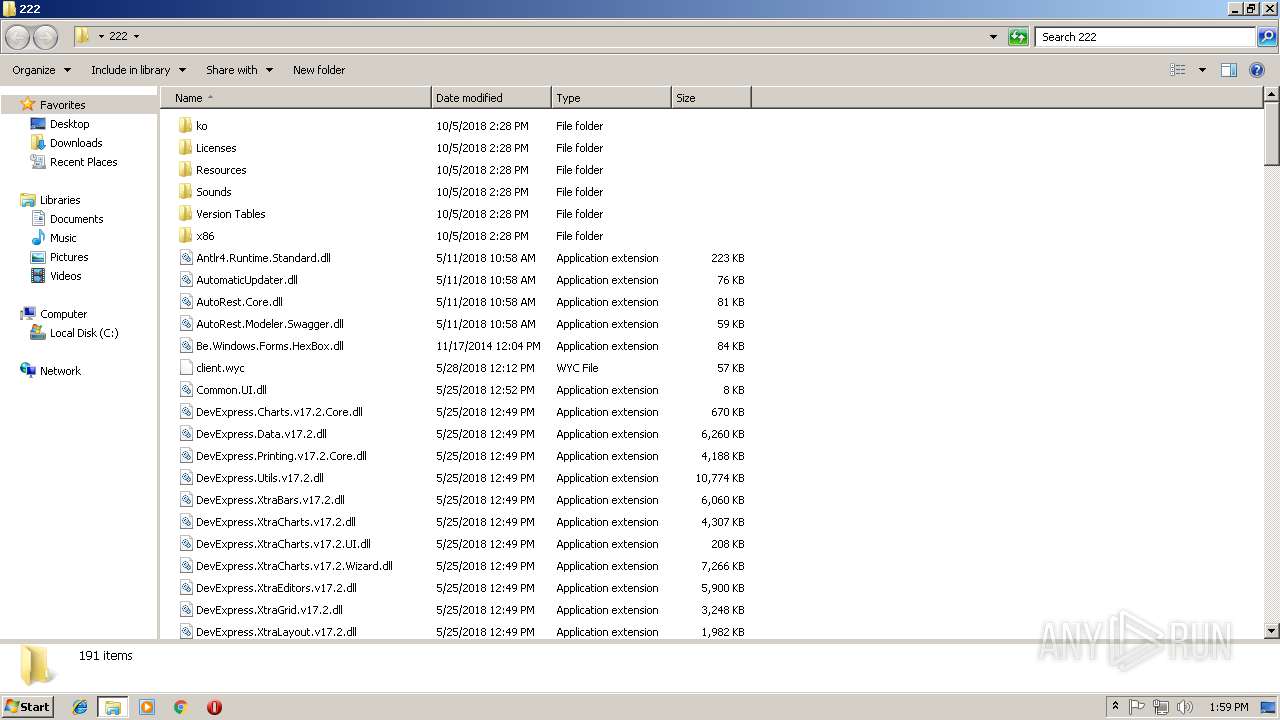
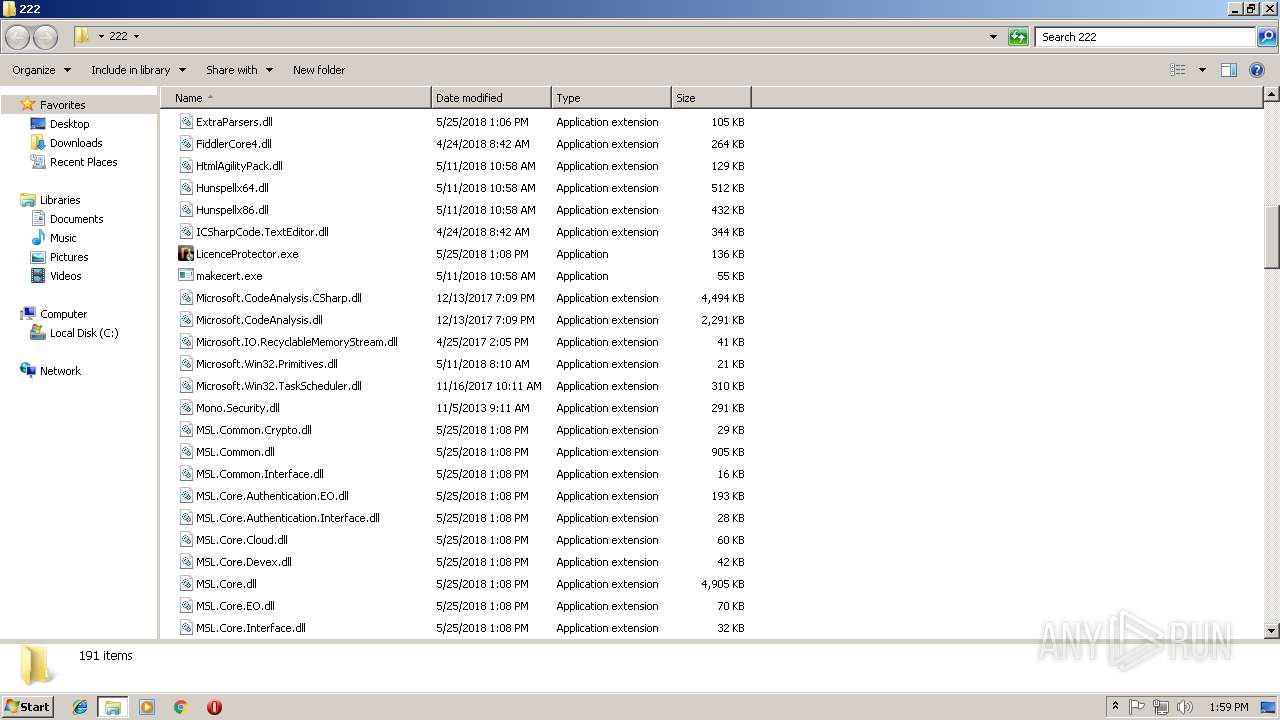
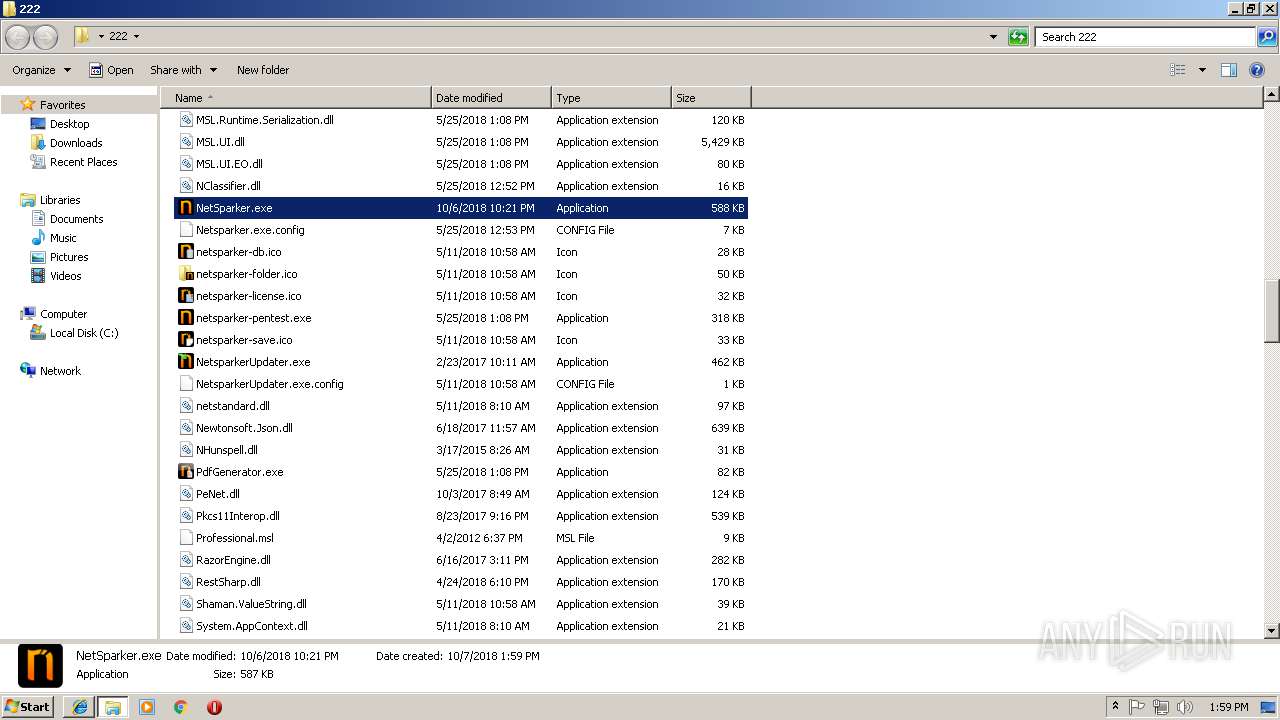
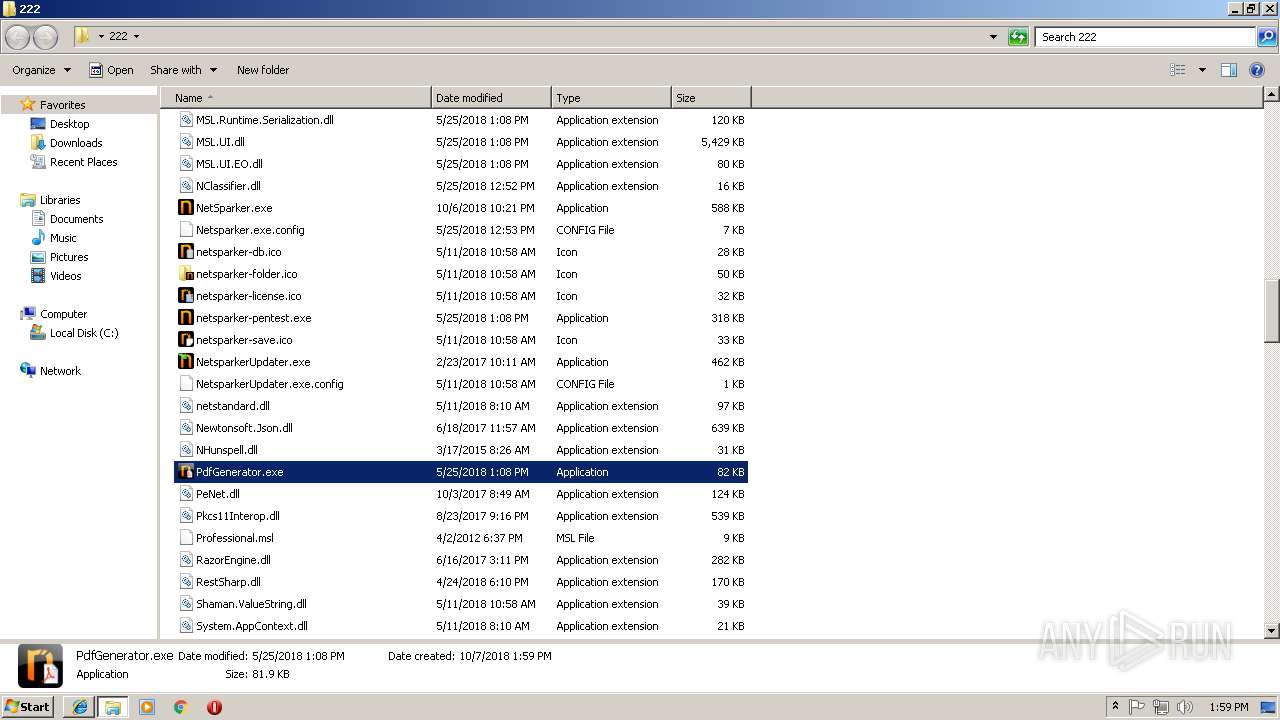
| 360 | "C:\Users\admin\Desktop\222\PdfGenerator.exe" | C:\Users\admin\Desktop\222\PdfGenerator.exe | — | explorer.exe | |||||||||||
User: admin Company: Netsparker Ltd Integrity Level: MEDIUM Description: PdfGenerator Exit code: 4294967295 Version: 5.0.0.19747 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=840,8664370332148790303,8498792308172476847,131072 --enable-features=PasswordImport --service-pipe-token=3625F2B0EB1B69E4C97F07E4CB3B1C87 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3625F2B0EB1B69E4C97F07E4CB3B1C87 --renderer-client-id=6 --mojo-platform-channel-handle=2112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 940 | C:\e54997481880e674fc475e15d5ab\\Setup.exe /x86 /x64 /web | C:\e54997481880e674fc475e15d5ab\Setup.exe | NDP472-KB4054531-Web[1].exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 14.7.3081.0 built by: NET472REL1 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2744 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=840,8664370332148790303,8498792308172476847,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=84218F964050CE1A9D3C987D4F20FBE4 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=84218F964050CE1A9D3C987D4F20FBE4 --renderer-client-id=7 --mojo-platform-channel-handle=3728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=840,8664370332148790303,8498792308172476847,131072 --enable-features=PasswordImport --service-pipe-token=AA1093366806F92782938FCAC7034474 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=AA1093366806F92782938FCAC7034474 --renderer-client-id=3 --mojo-platform-channel-handle=2120 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2480 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 3221225547 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
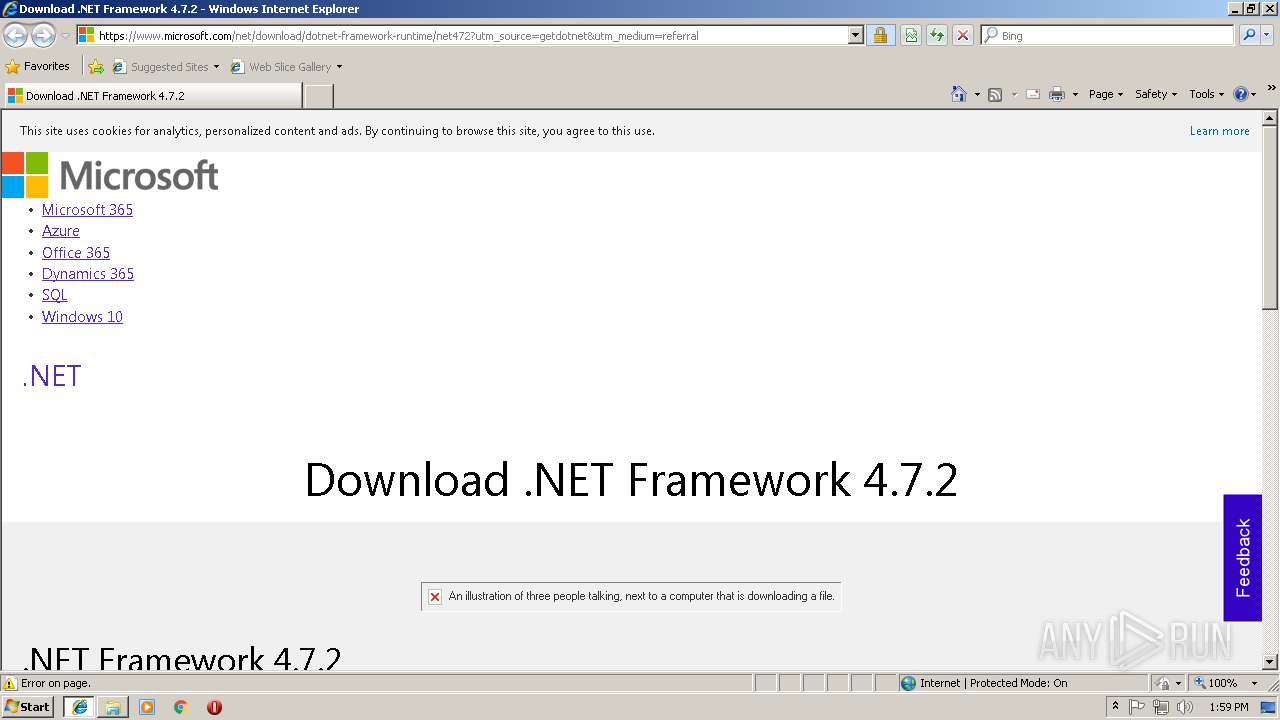
| 2120 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\NDP472-KB4054531-Web[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\NDP472-KB4054531-Web[1].exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.7.2 Setup Exit code: 0 Version: 4.7.03081.00 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f8000b0,0x6f8000c0,0x6f8000cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=840,8664370332148790303,8498792308172476847,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=6B5B945B41B7B015DBBD3C7248AEF7A7 --mojo-platform-channel-handle=3596 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
3 146
Read events
2 866
Write events
274
Delete events
6
Modification events
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {8A1CD92F-CA30-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2480) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070A00000007000C0039001B009900 | |||
Executable files
232
Suspicious files
86
Text files
406
Unknown types
32
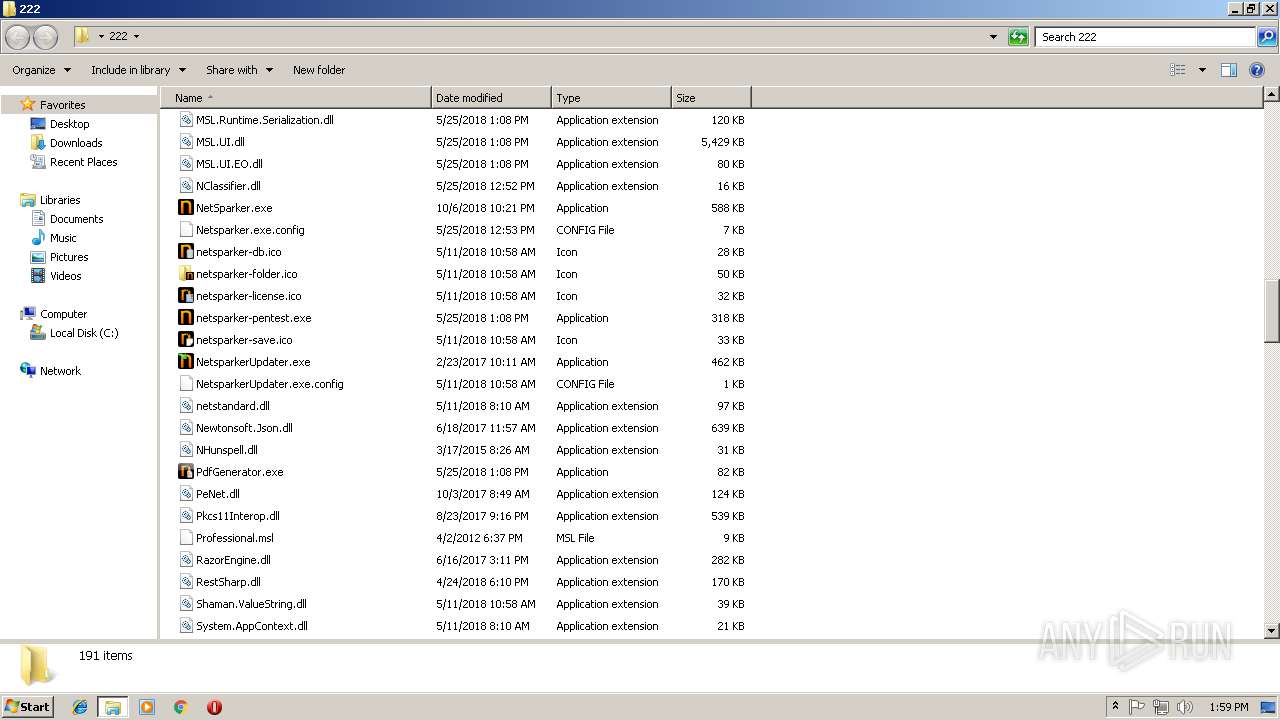
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2480 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2480 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\bg[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\f[1].txt | text | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\download[1].gif | image | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\spacer[1].png | image | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\sign-up-buton[1].png | image | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\steps_wide[1].png | image | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\f[1].txt | text | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@filedropper[2].txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
78
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2108 | iexplore.exe | GET | 301 | 144.76.226.41:80 | http://www.filedropper.com/images/filedropper_banner.png | DE | html | 265 b | suspicious |
3696 | chrome.exe | GET | 301 | 144.76.226.41:80 | http://www.filedropper.com/images/filedropper_banner.png | DE | html | 265 b | suspicious |
2108 | iexplore.exe | GET | 200 | 104.20.2.47:80 | http://c.statcounter.com/3541212/0/872cdcc5/1/ | US | image | 49 b | whitelisted |
3696 | chrome.exe | GET | 200 | 104.20.3.47:80 | http://c.statcounter.com/3541212/0/872cdcc5/1/ | US | image | 49 b | whitelisted |
2480 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2480 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2108 | iexplore.exe | 216.58.207.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2108 | iexplore.exe | 144.76.226.41:80 | www.filedropper.com | Hetzner Online GmbH | DE | unknown |
2108 | iexplore.exe | 144.76.226.41:443 | www.filedropper.com | Hetzner Online GmbH | DE | unknown |
2108 | iexplore.exe | 172.217.22.66:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2108 | iexplore.exe | 216.58.206.2:443 | adservice.google.com | Google Inc. | US | whitelisted |
2108 | iexplore.exe | 172.217.16.162:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2108 | iexplore.exe | 52.59.170.168:443 | odr.mookie1.com | Amazon.com, Inc. | DE | unknown |
2108 | iexplore.exe | 104.20.2.47:80 | c.statcounter.com | Cloudflare Inc | US | shared |
2108 | iexplore.exe | 172.217.16.168:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.filedropper.com |
| suspicious |
pagead2.googlesyndication.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
adservice.google.be |
| whitelisted |
adservice.google.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
c.statcounter.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
tpc.googlesyndication.com |
| whitelisted |