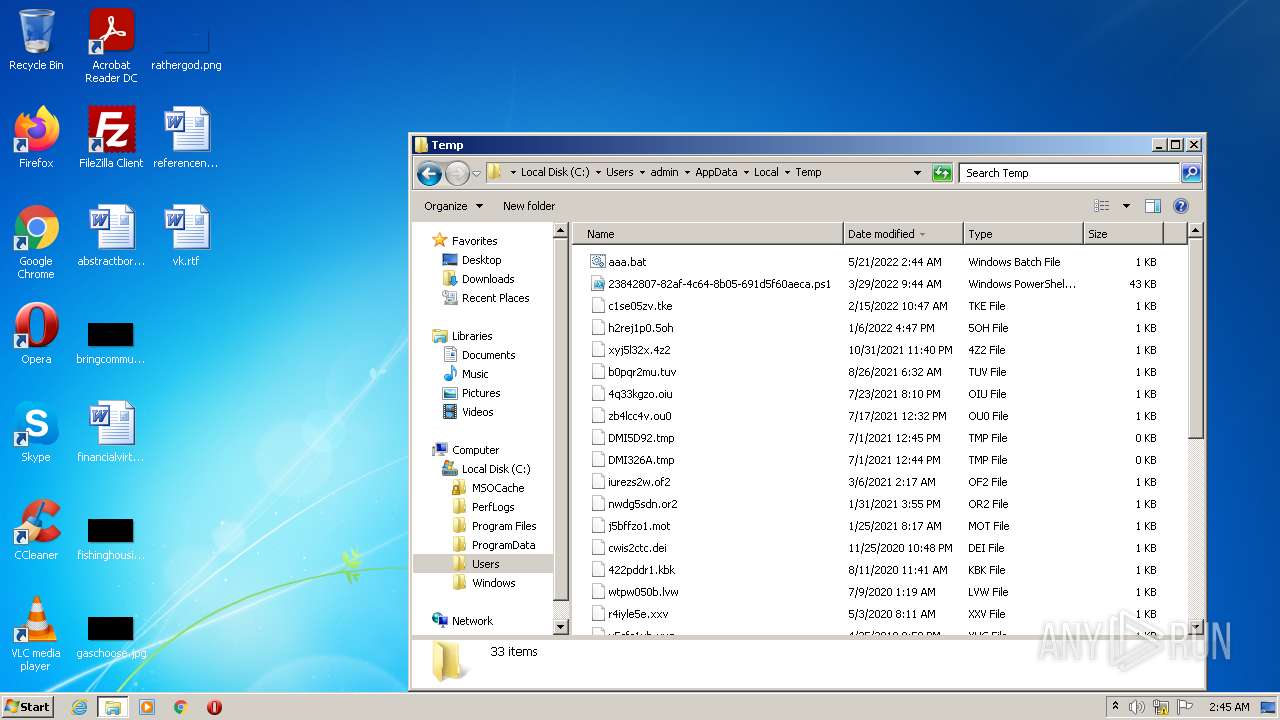
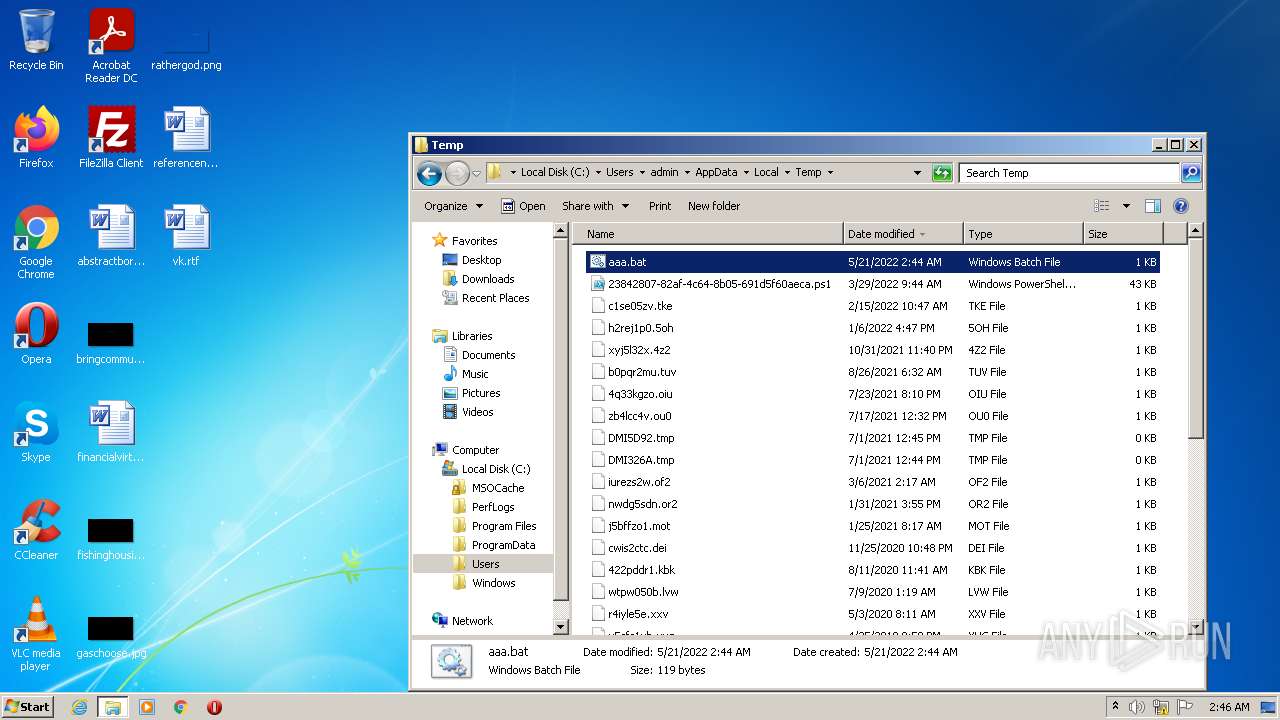
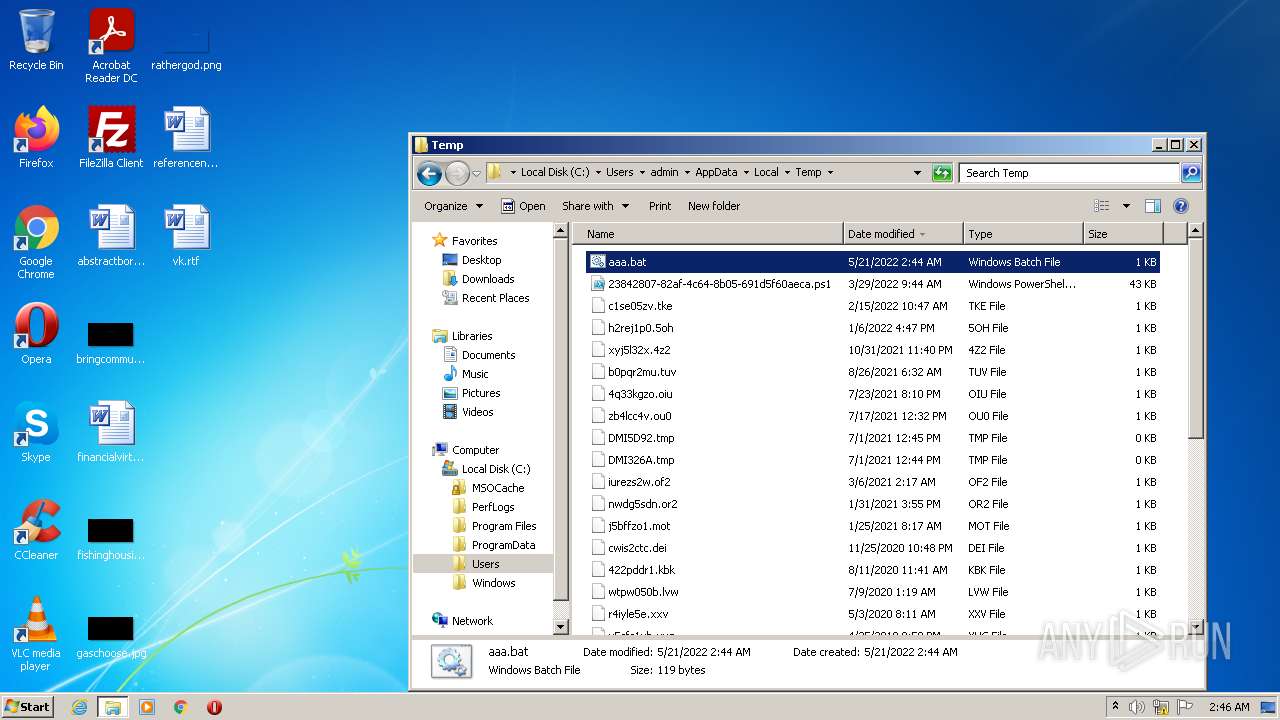
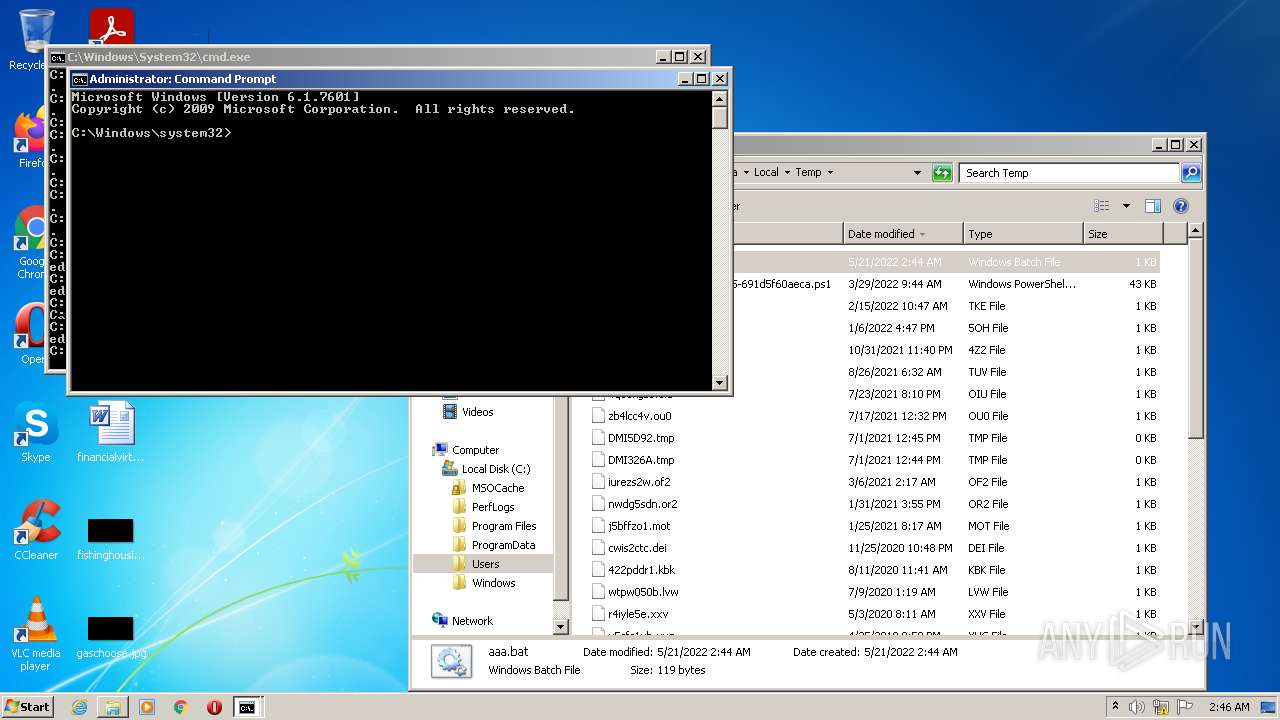
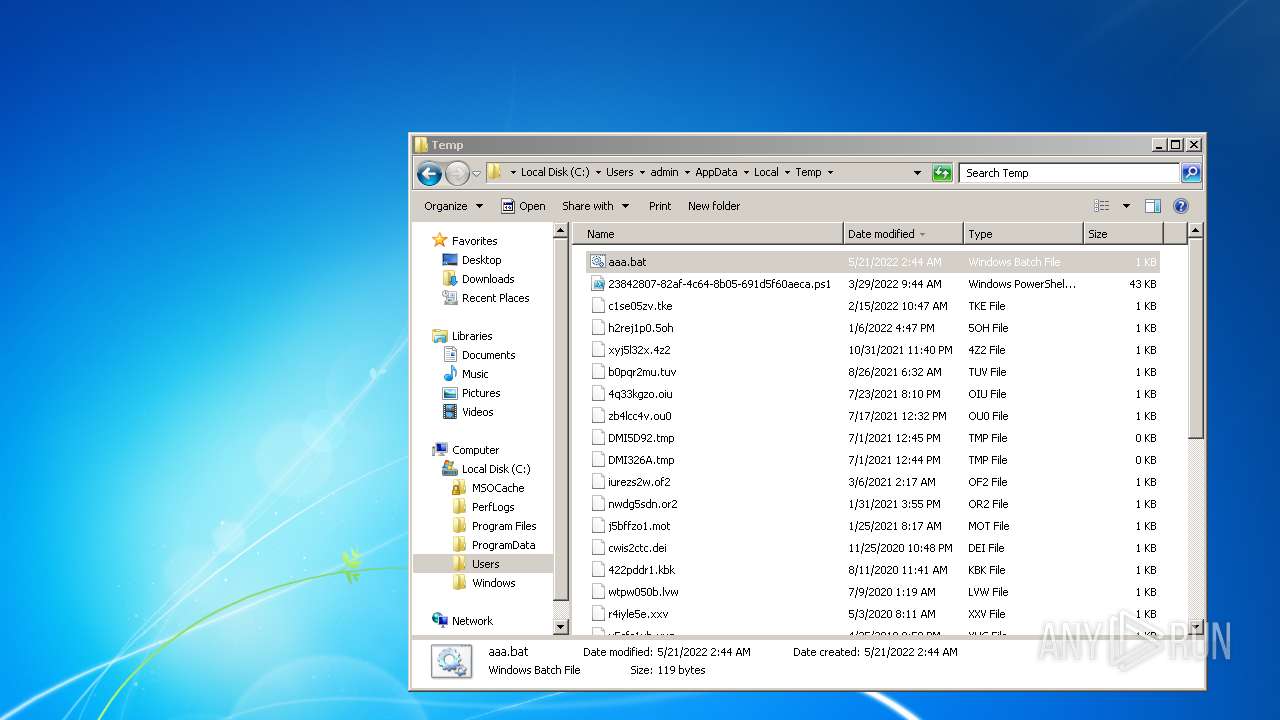
| File name: | aaa.bat |
| Full analysis: | https://app.any.run/tasks/bae58f77-18ff-4568-8f0e-8fff35a71664 |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 01:44:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | BFAD8ACE4F5C13AEA00B550AC90F2E89 |
| SHA1: | BFD7A211D85C898B1598BAF1B8DA0610C472442C |
| SHA256: | 104DDCD65A91FEB9EF11C0B4AD9780B2E1BE973797AE3006A93D4D2D044DA394 |
| SSDEEP: | 3:Z3Dc0aKWAIcewo5SM1KWAIMADyLWAHRKjKAw/uWwcm0M1KWAIQ:Z3c5GewoMa5ec3AxpQ0a5e |
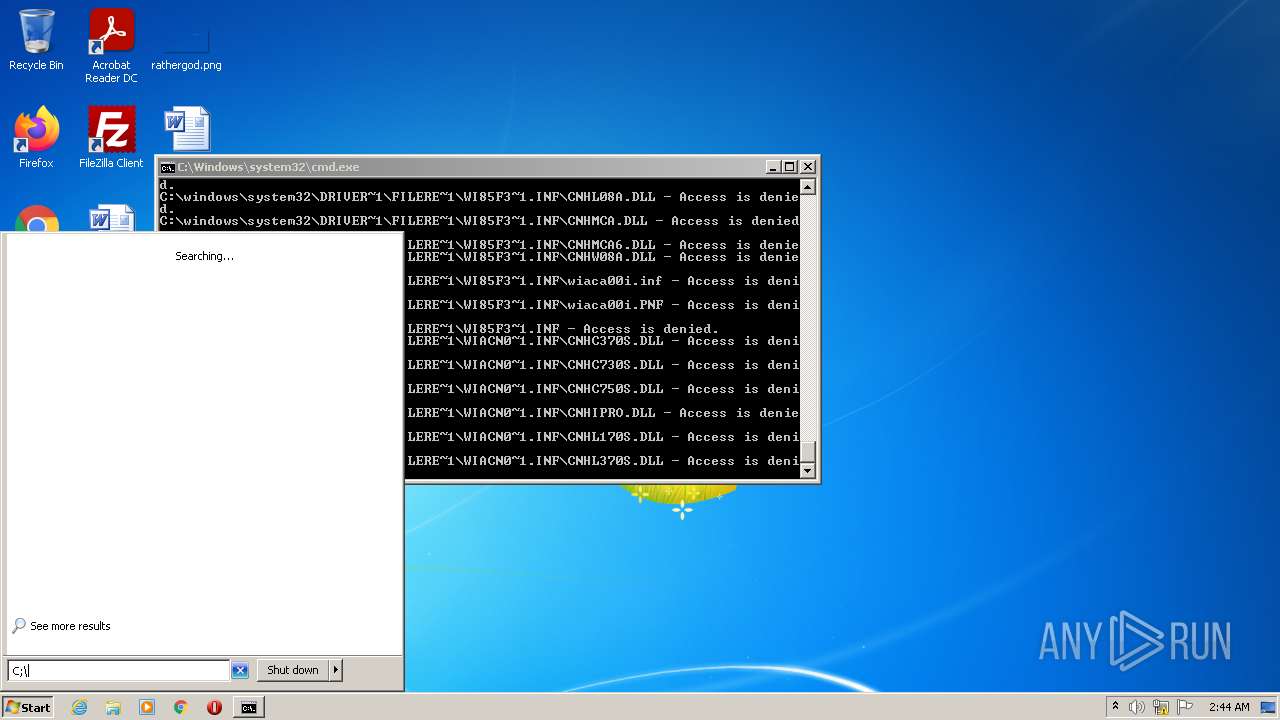
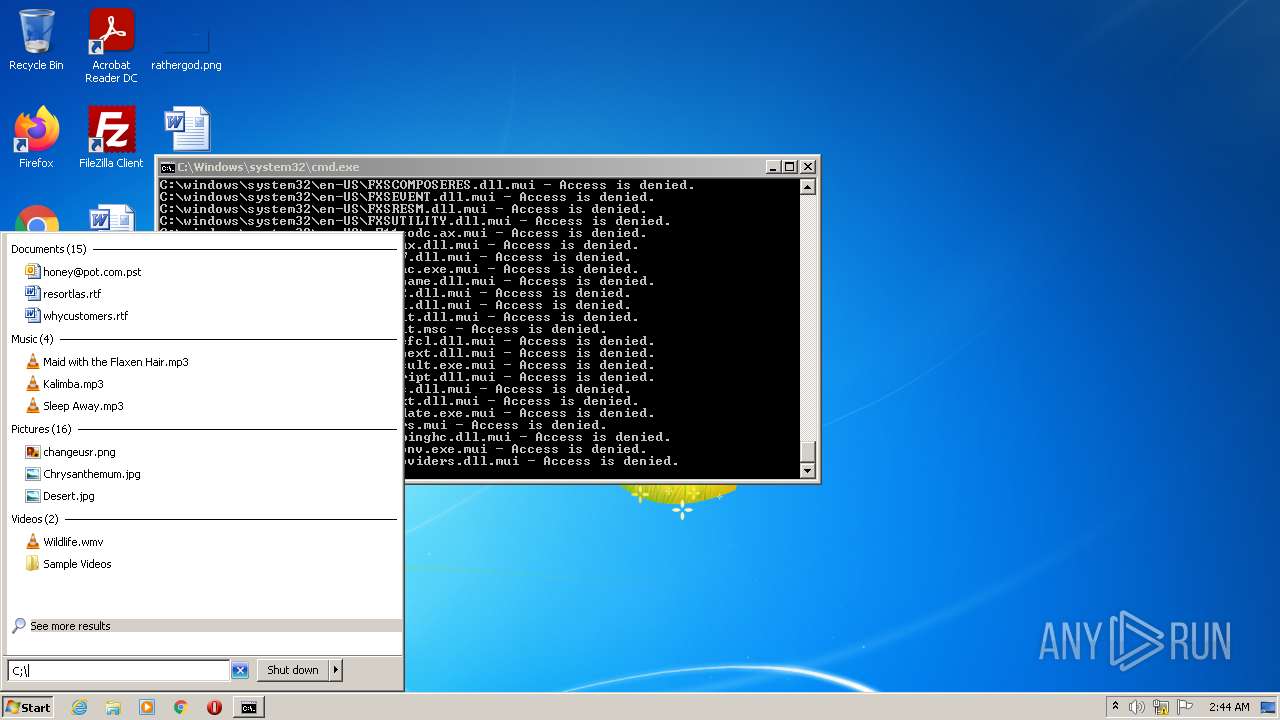
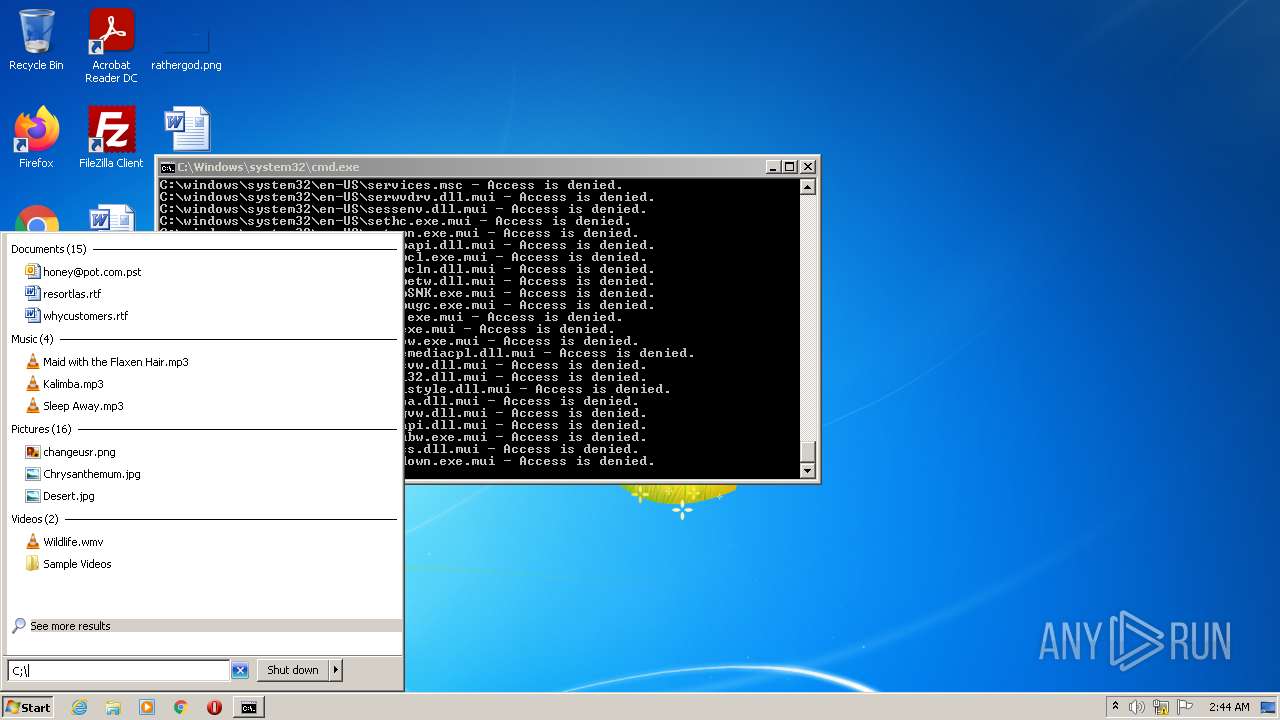
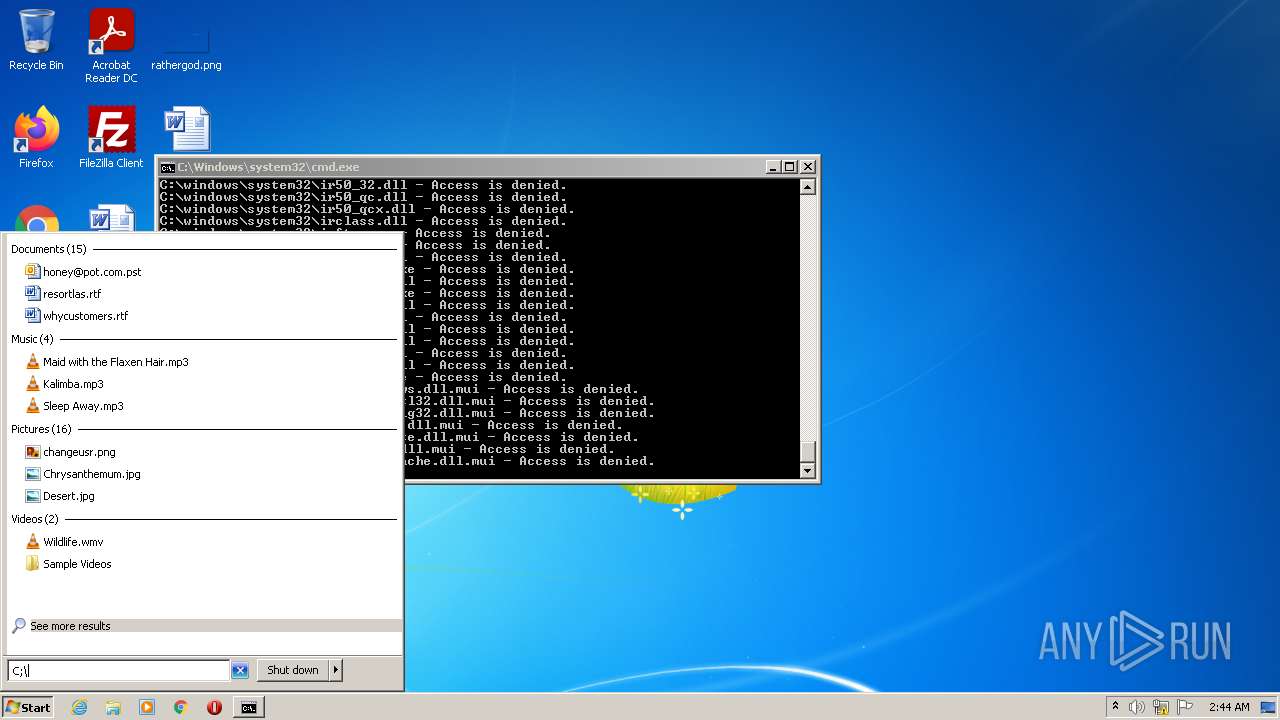
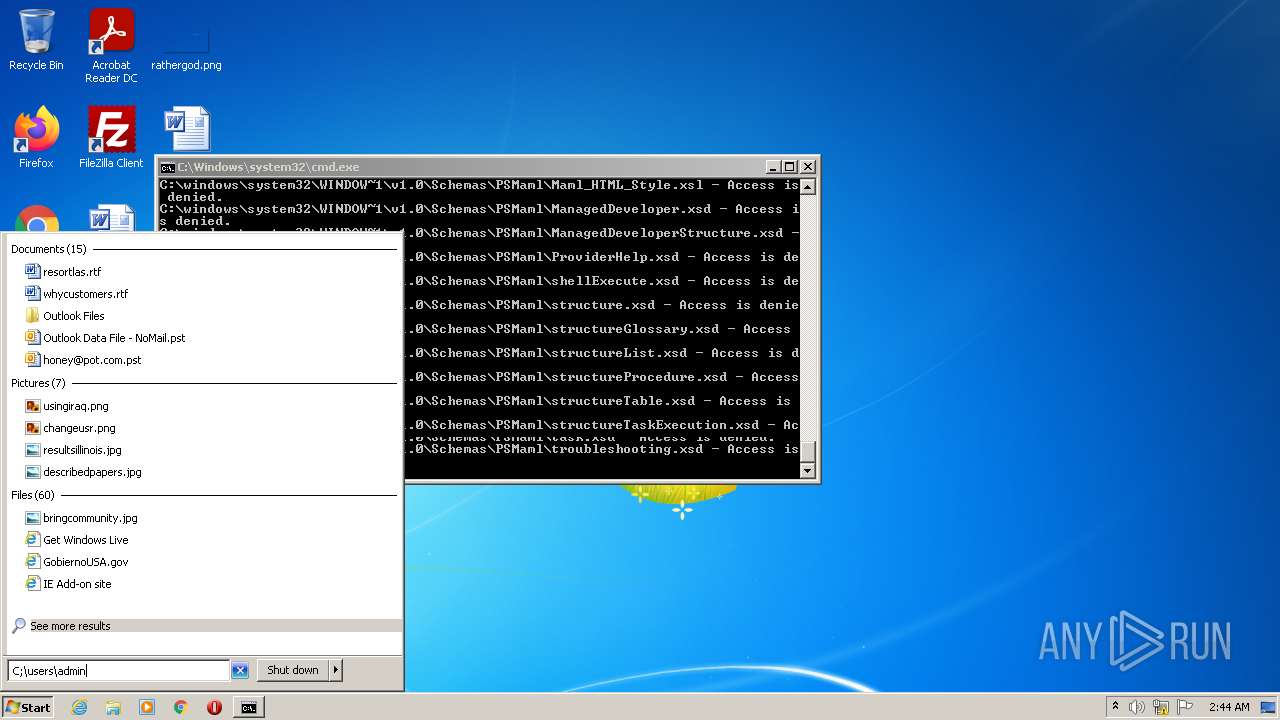
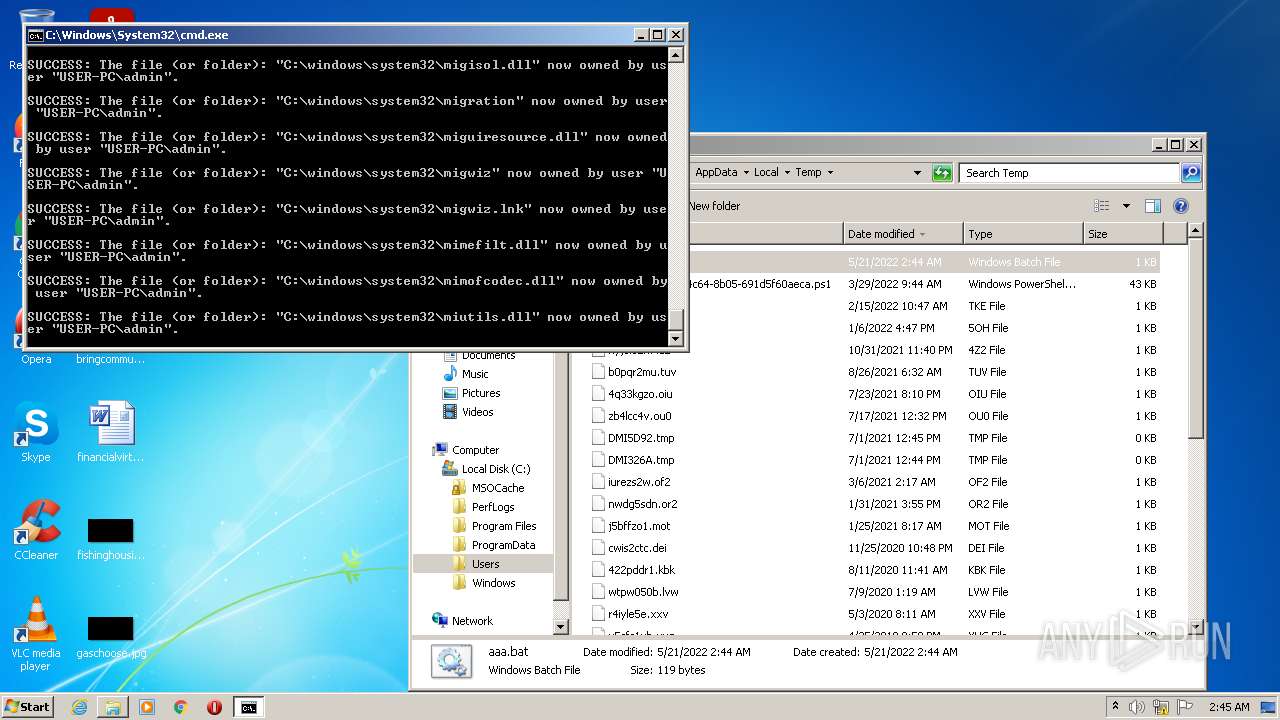
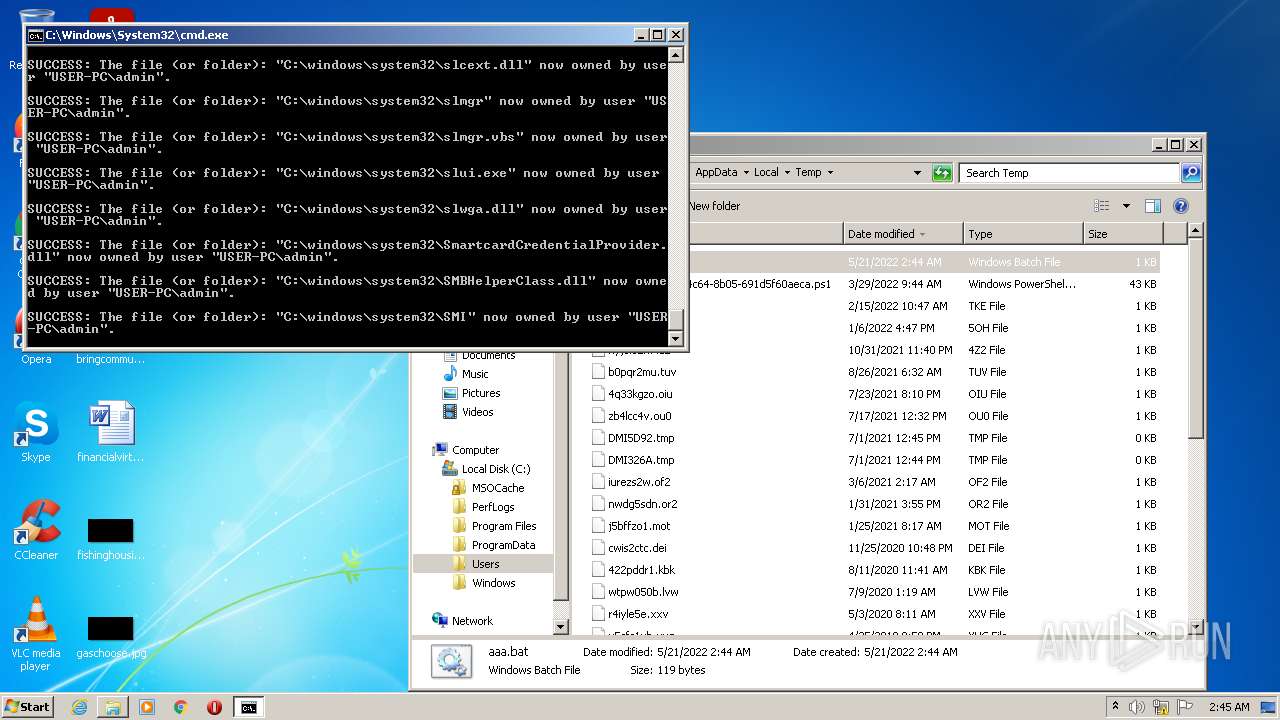
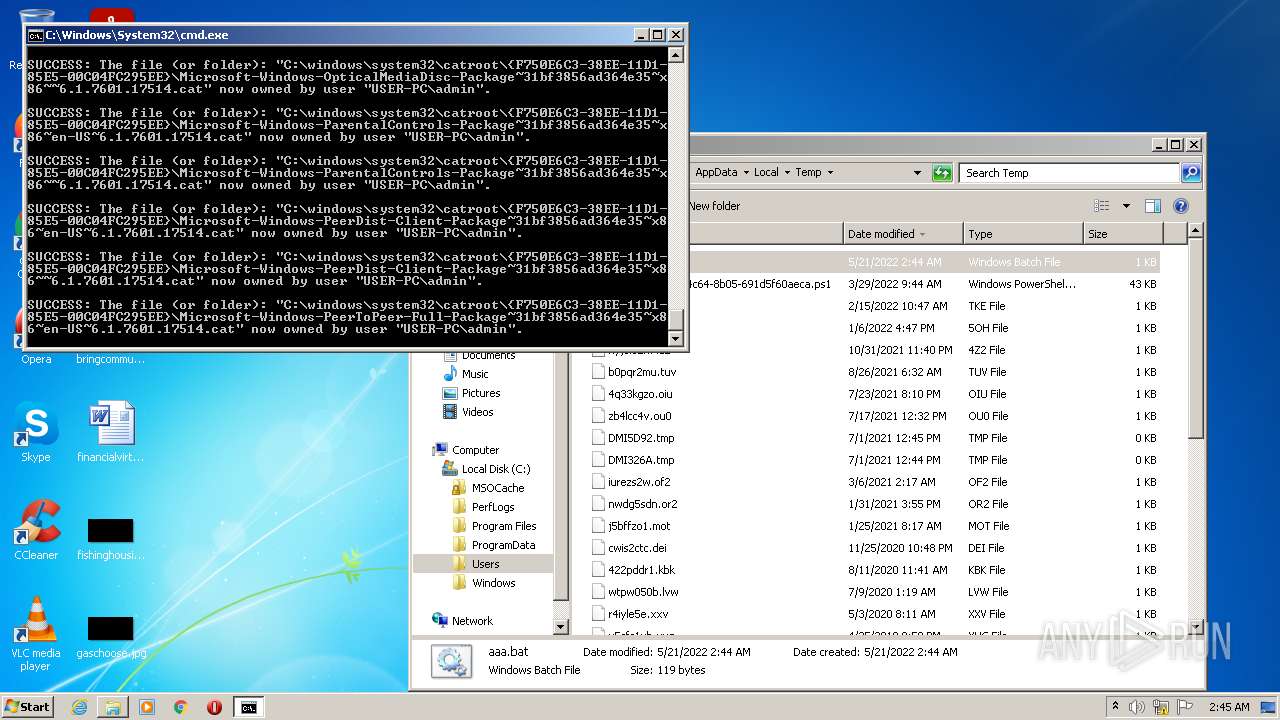
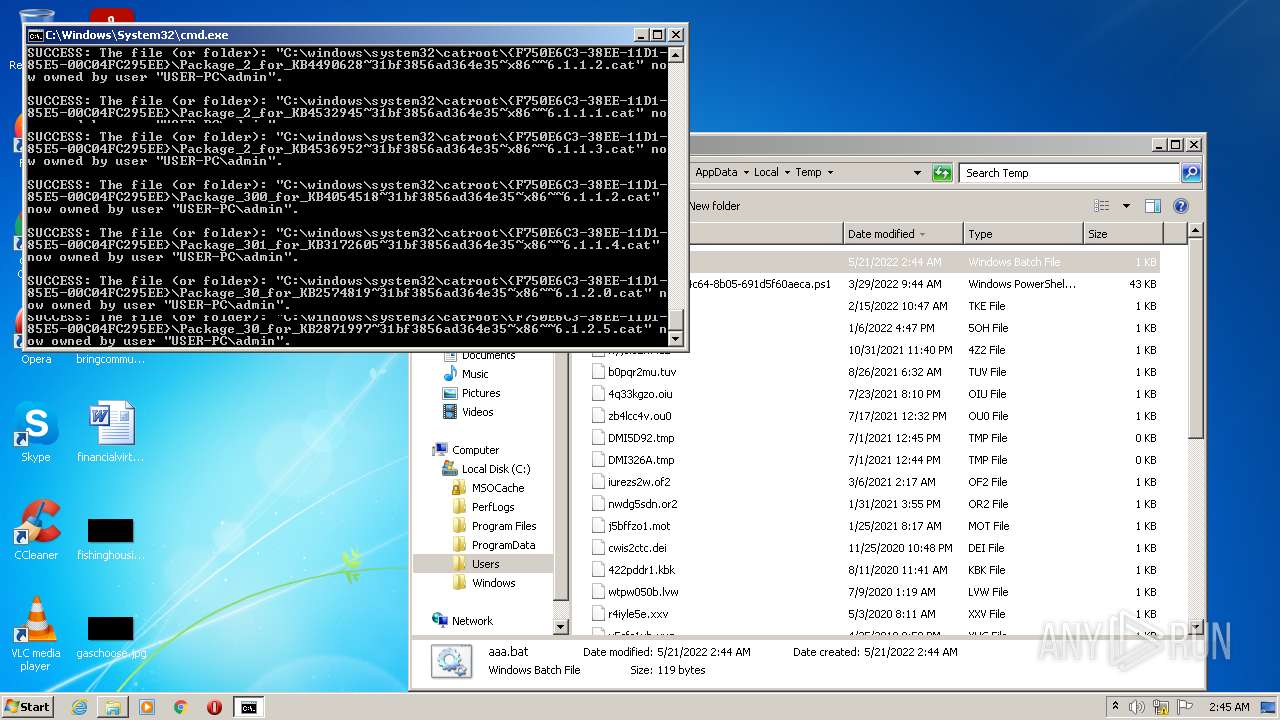
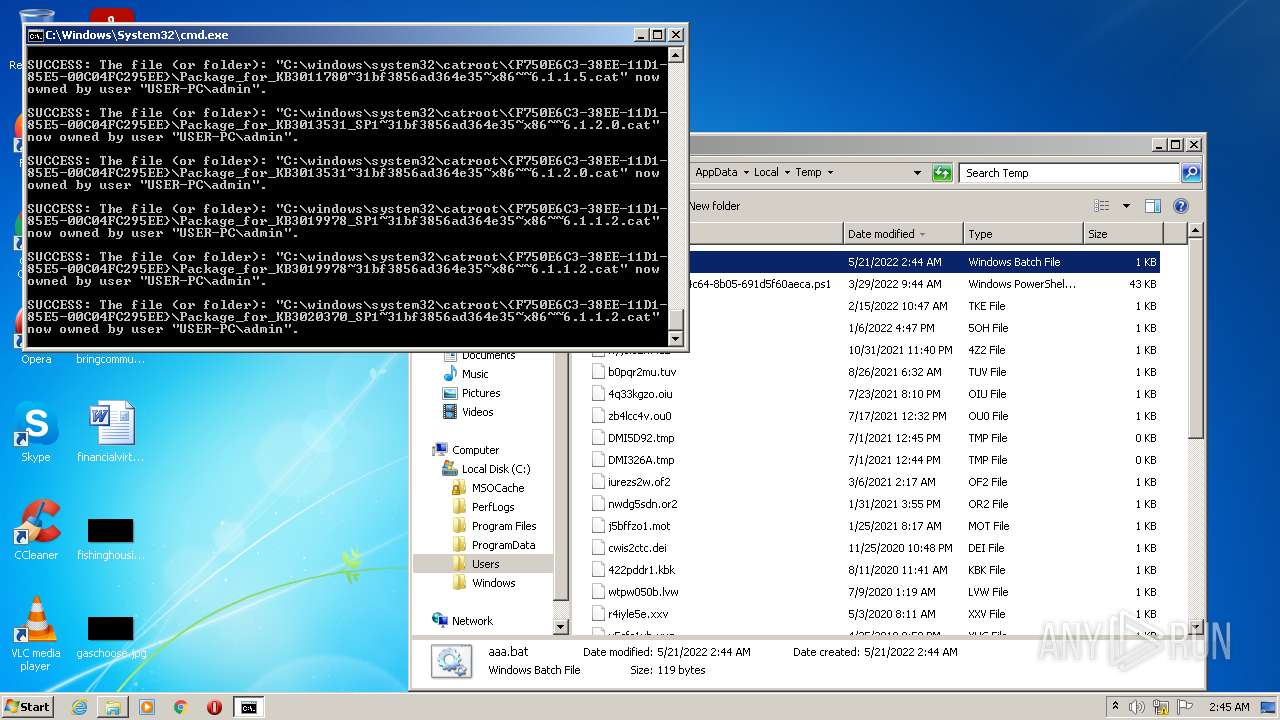
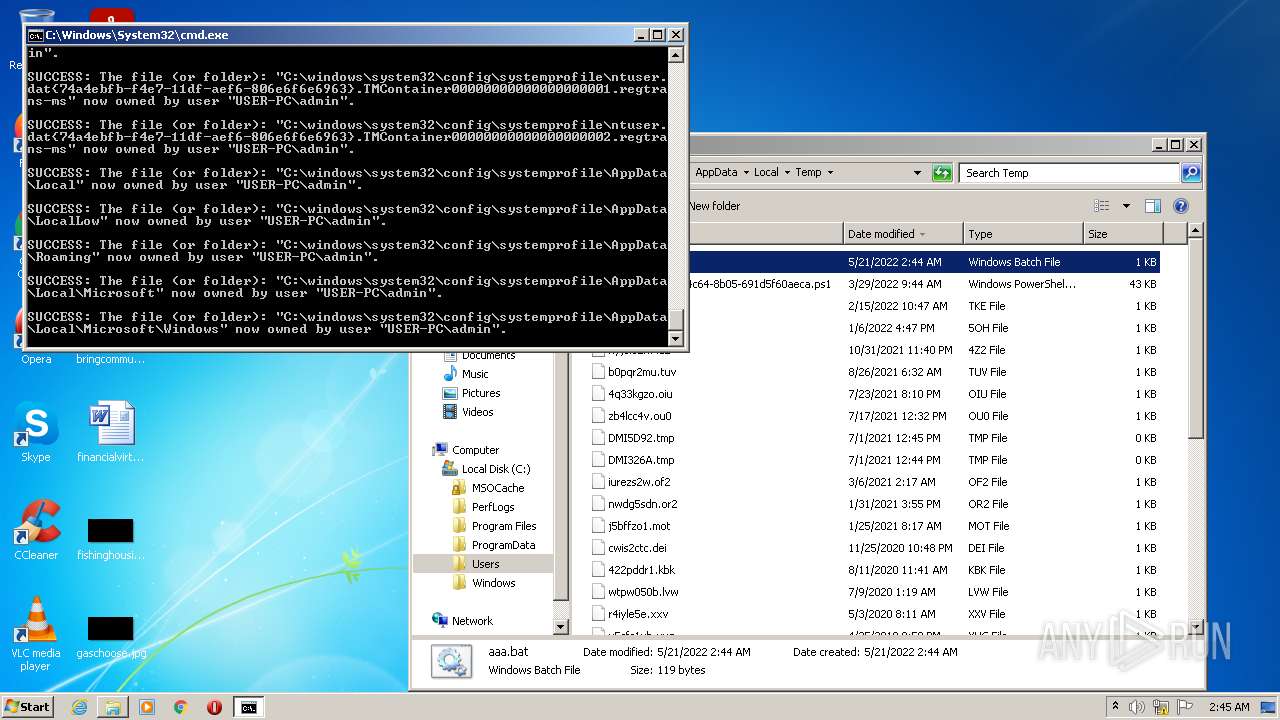
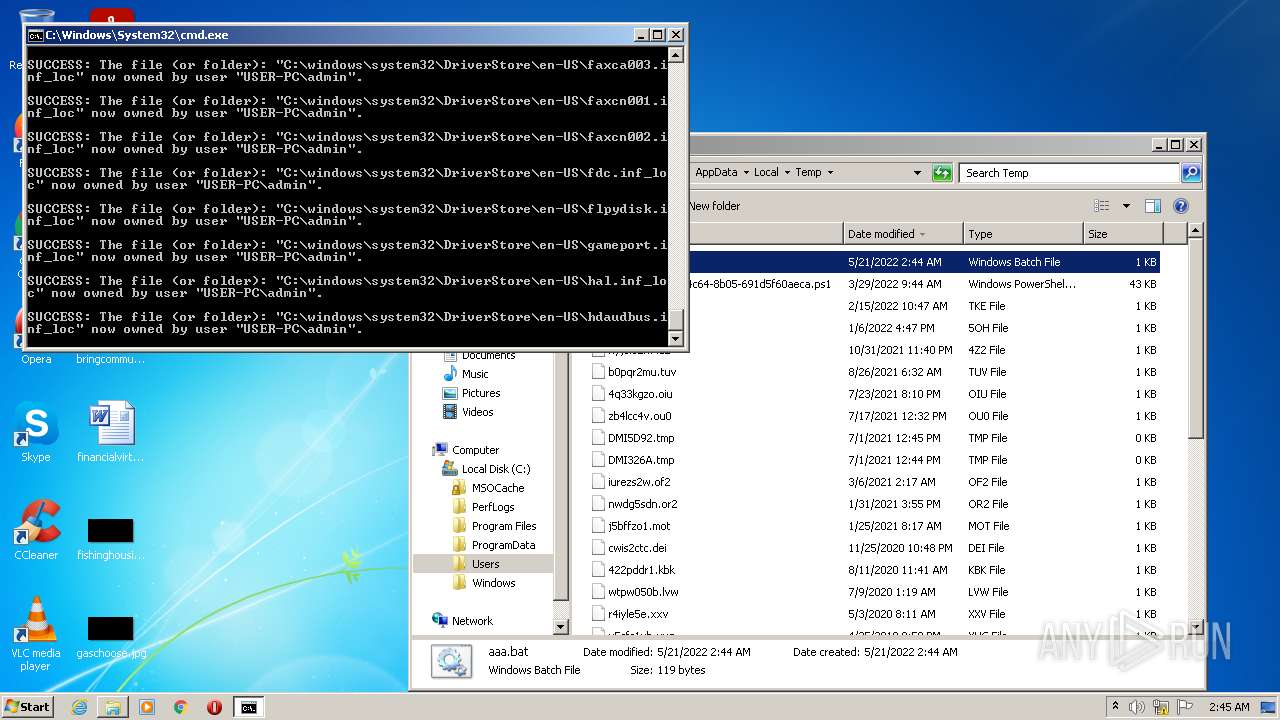
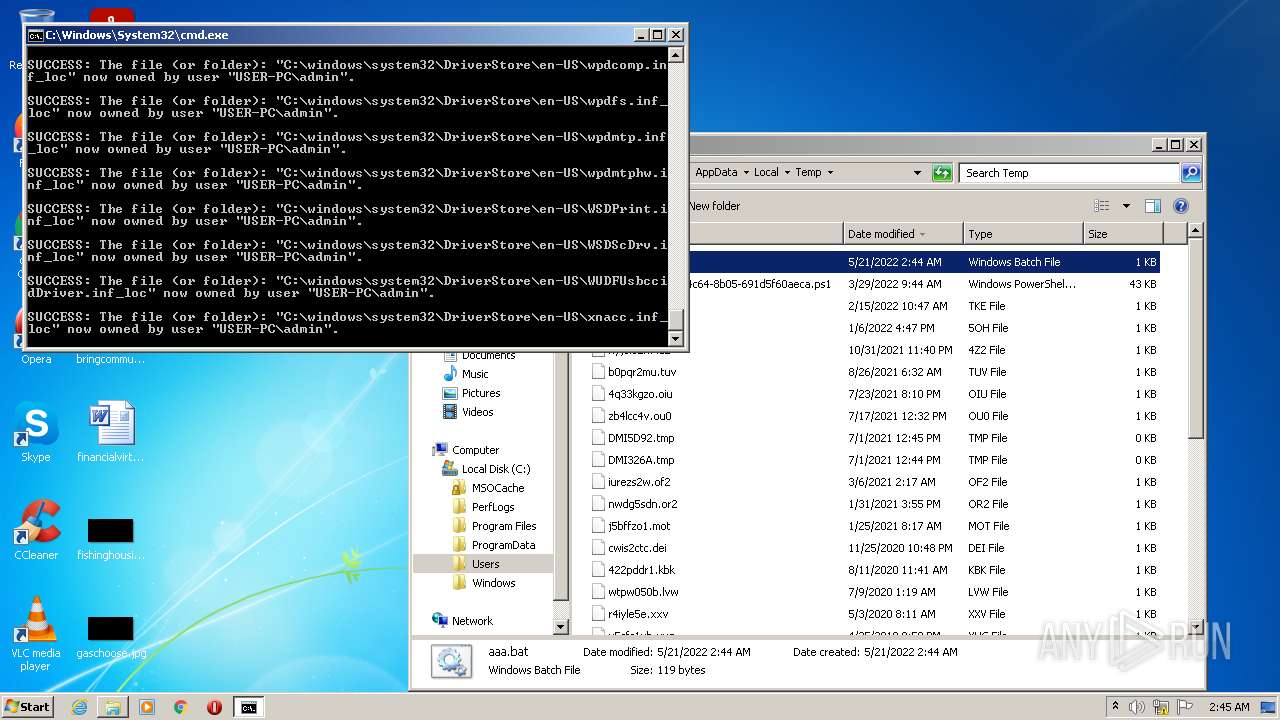
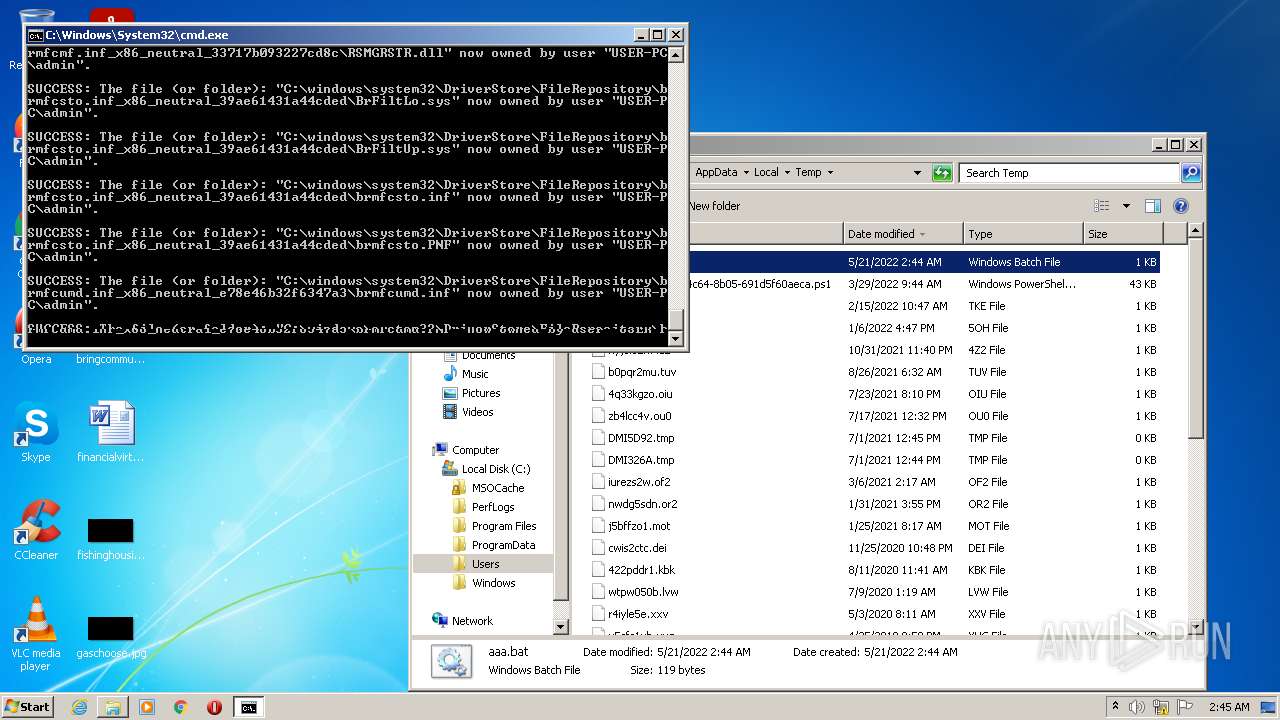
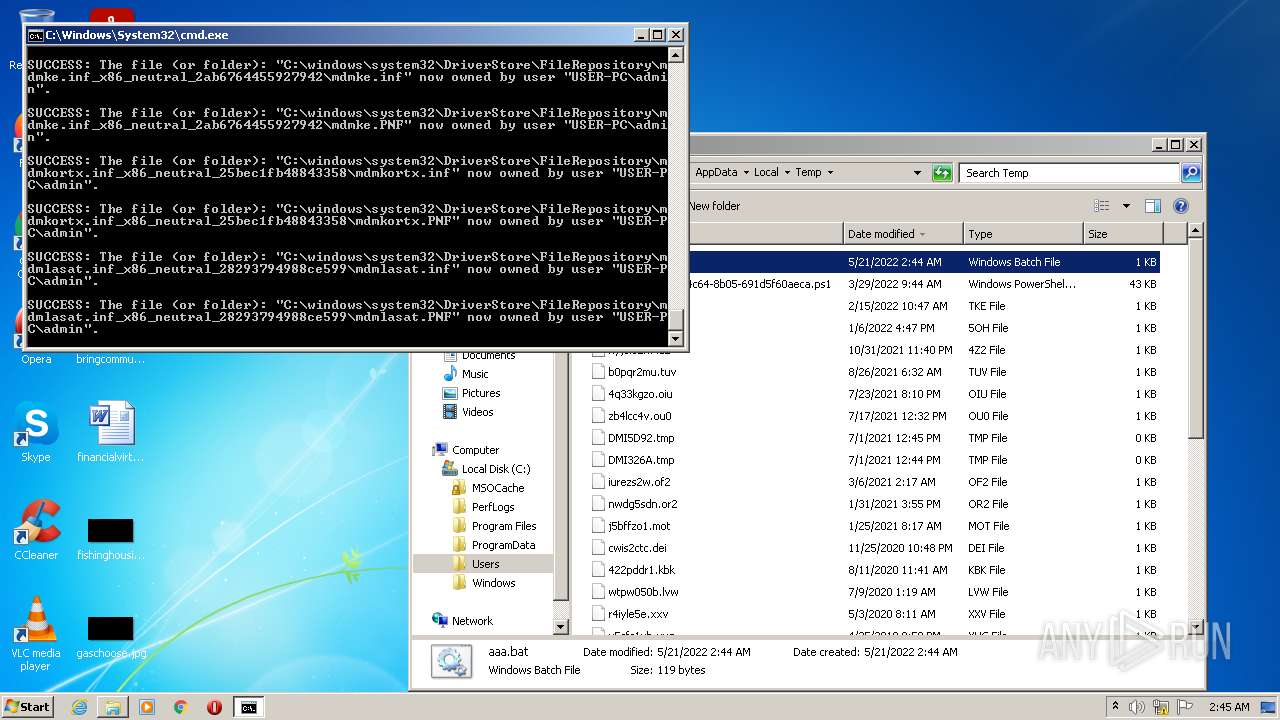
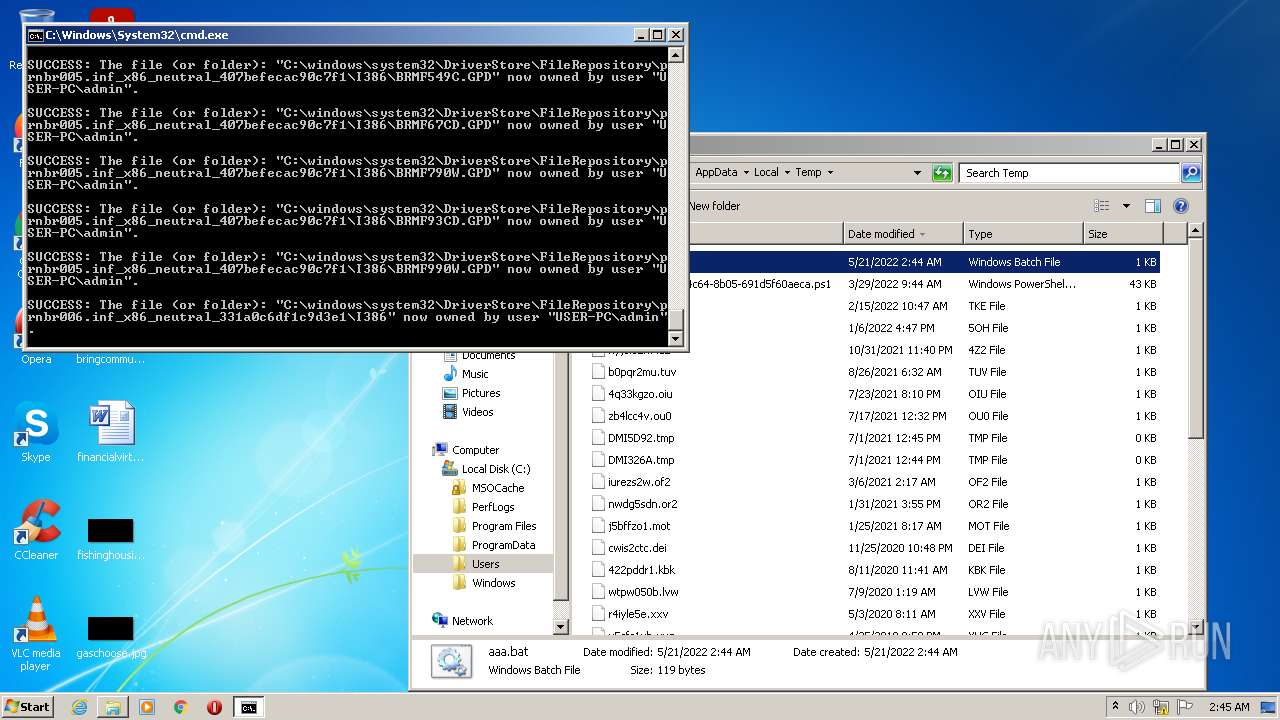
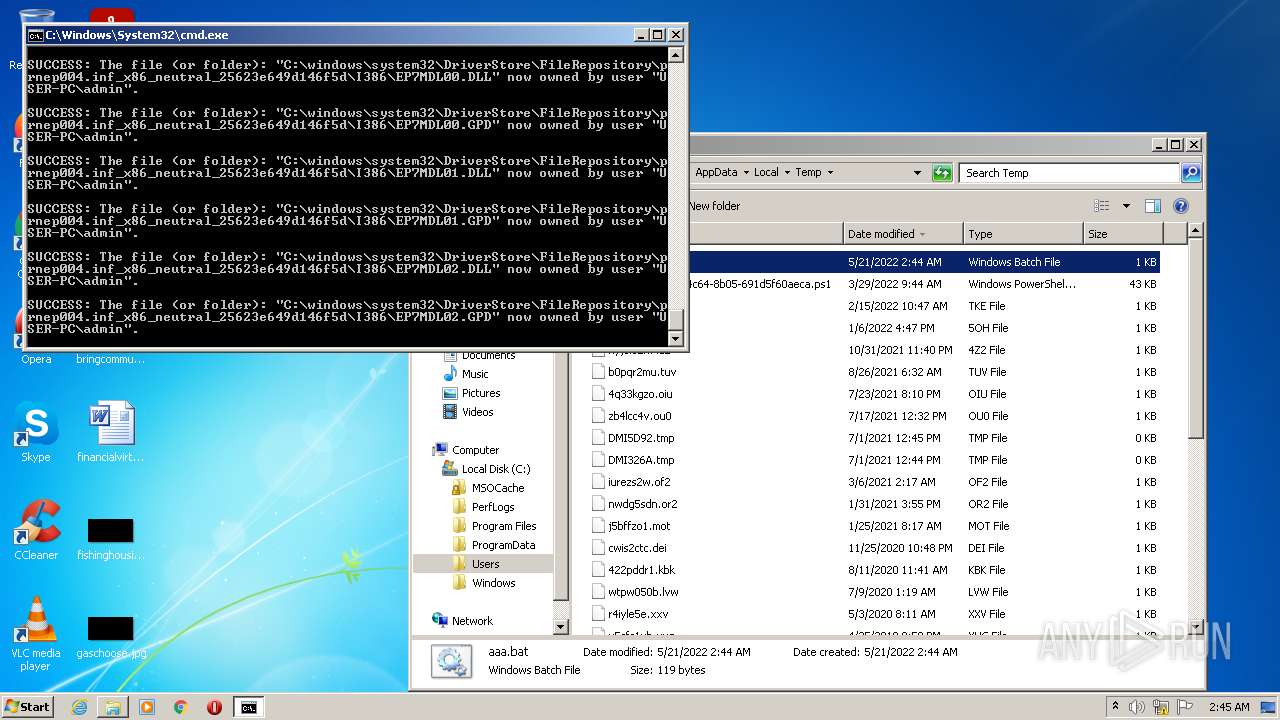
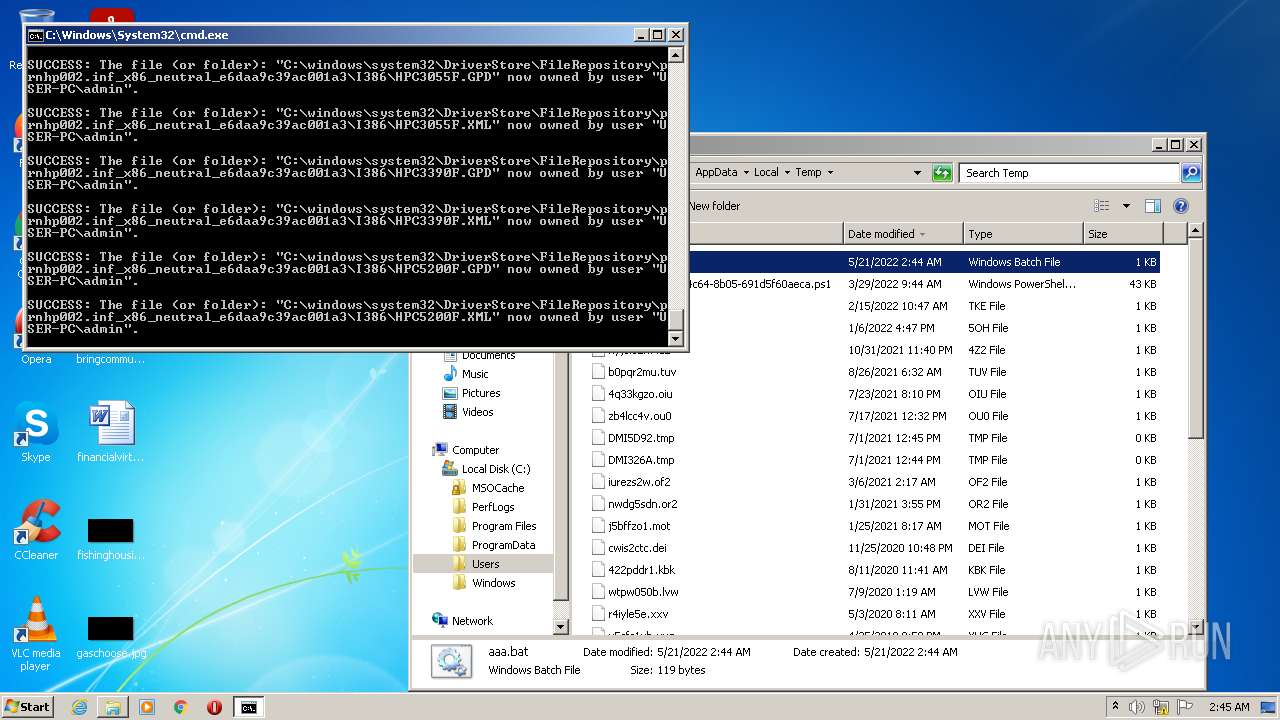
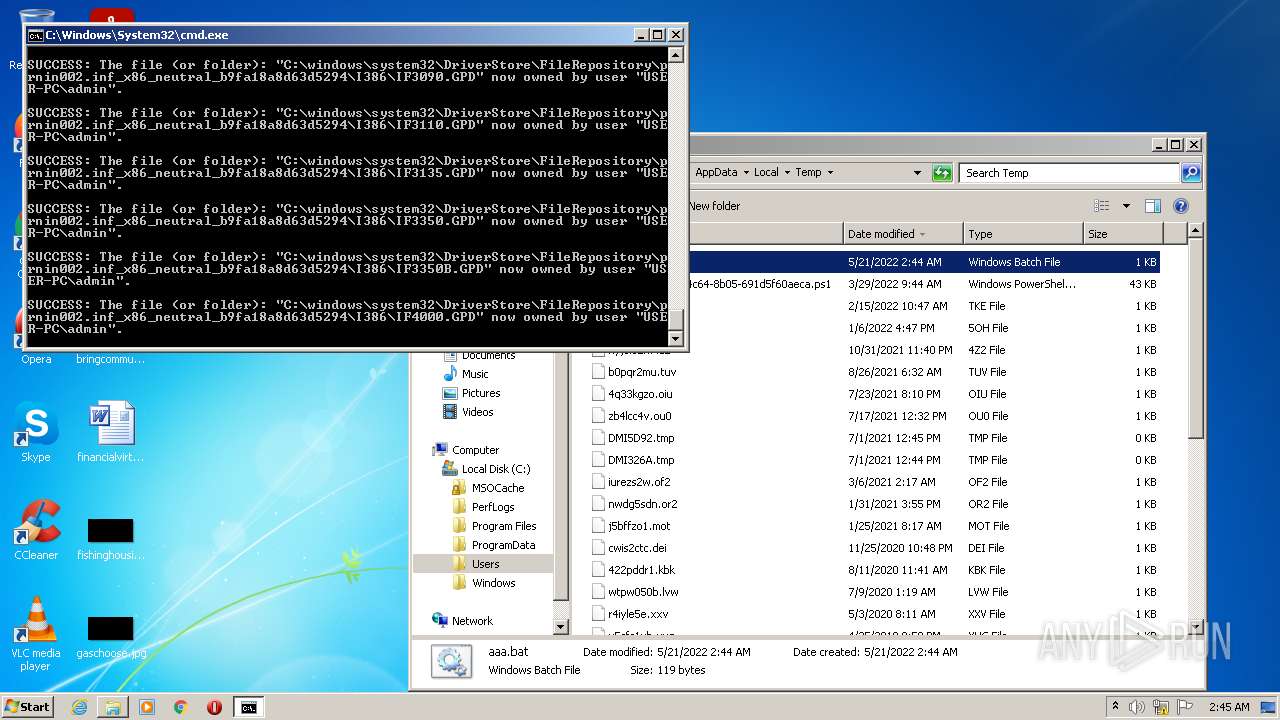
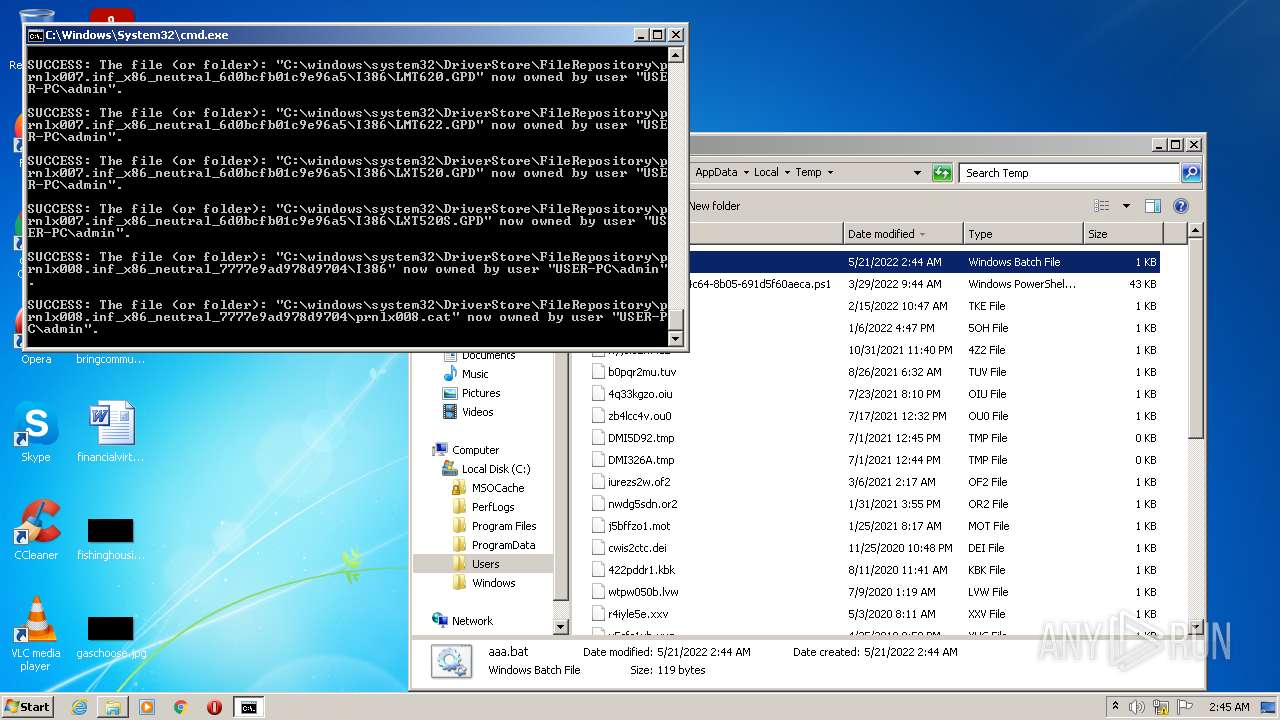
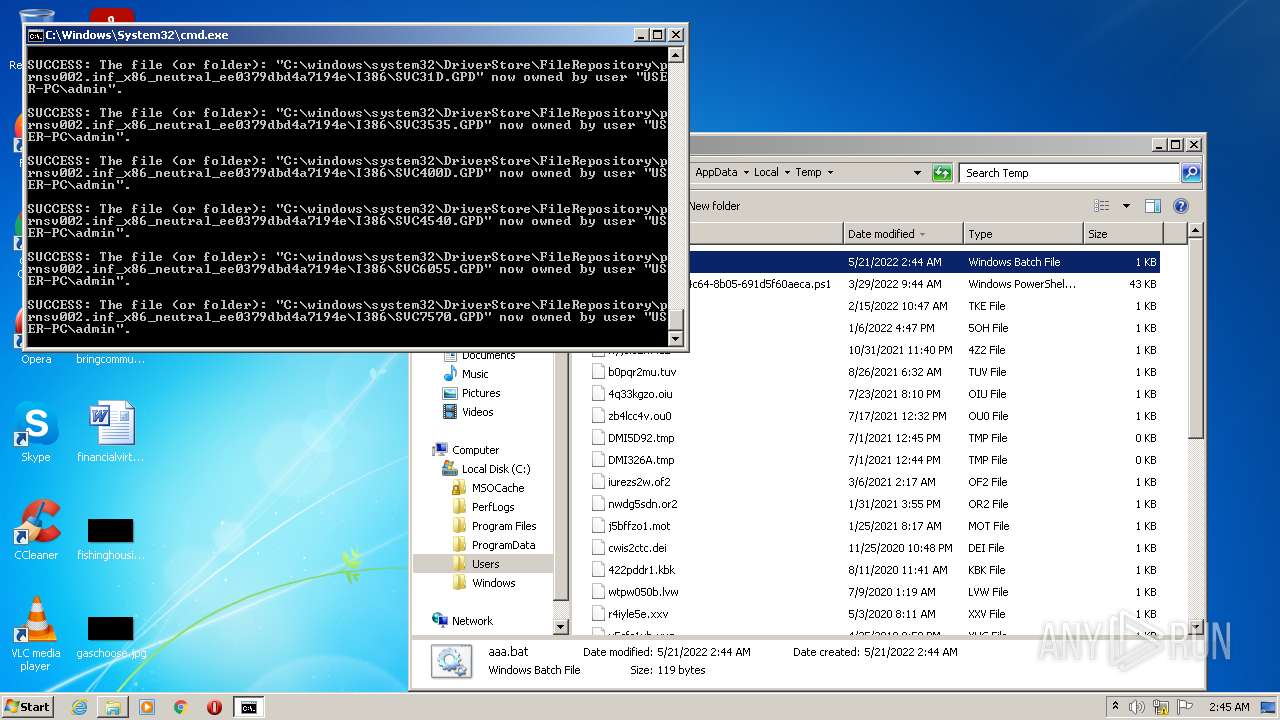
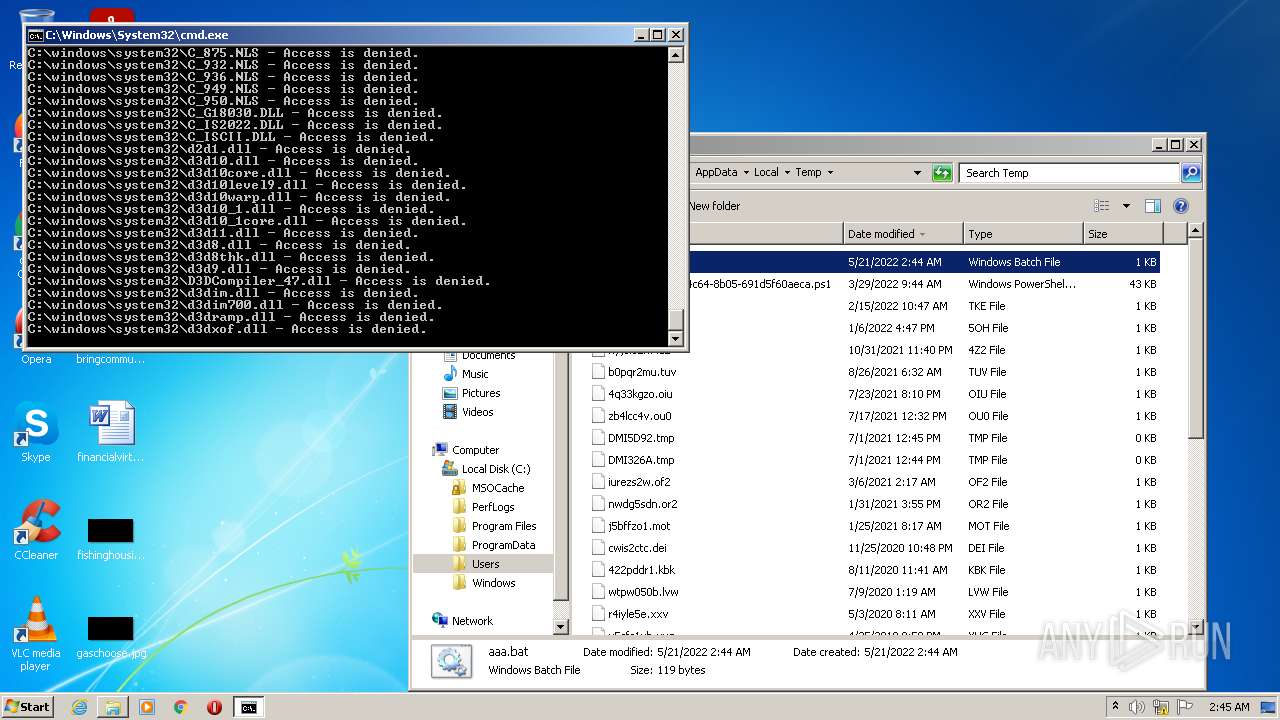
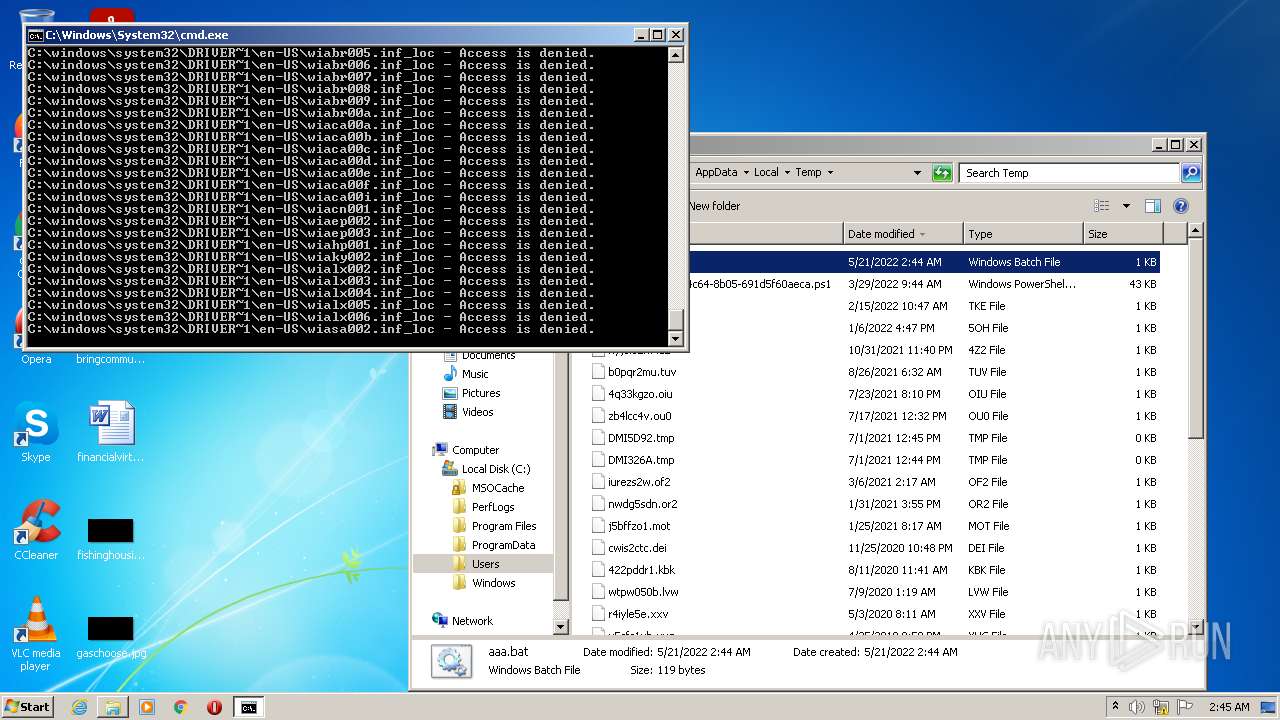
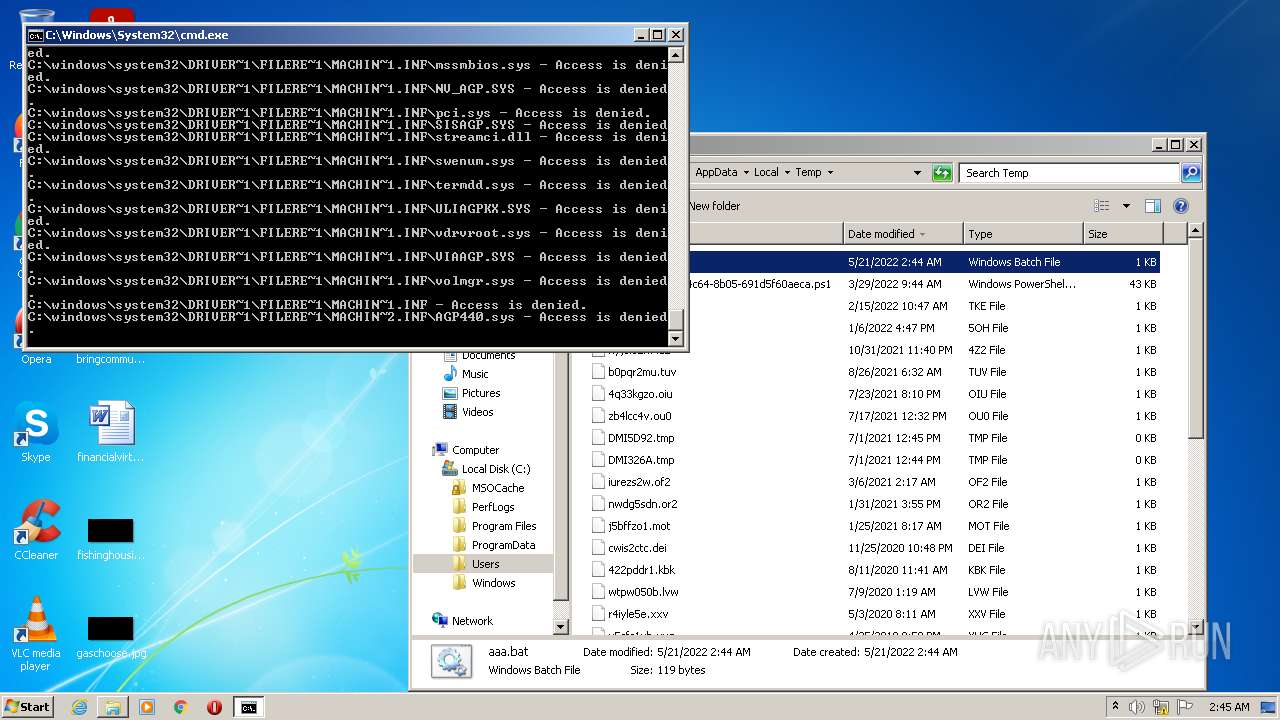
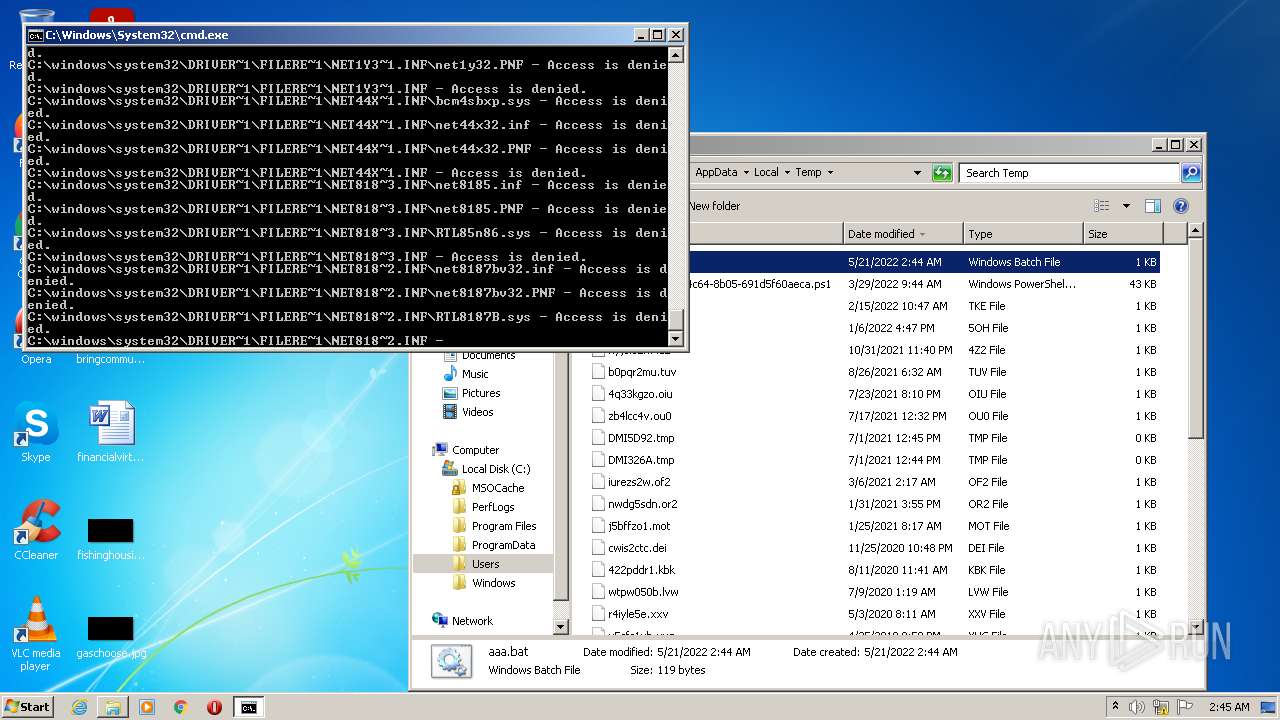
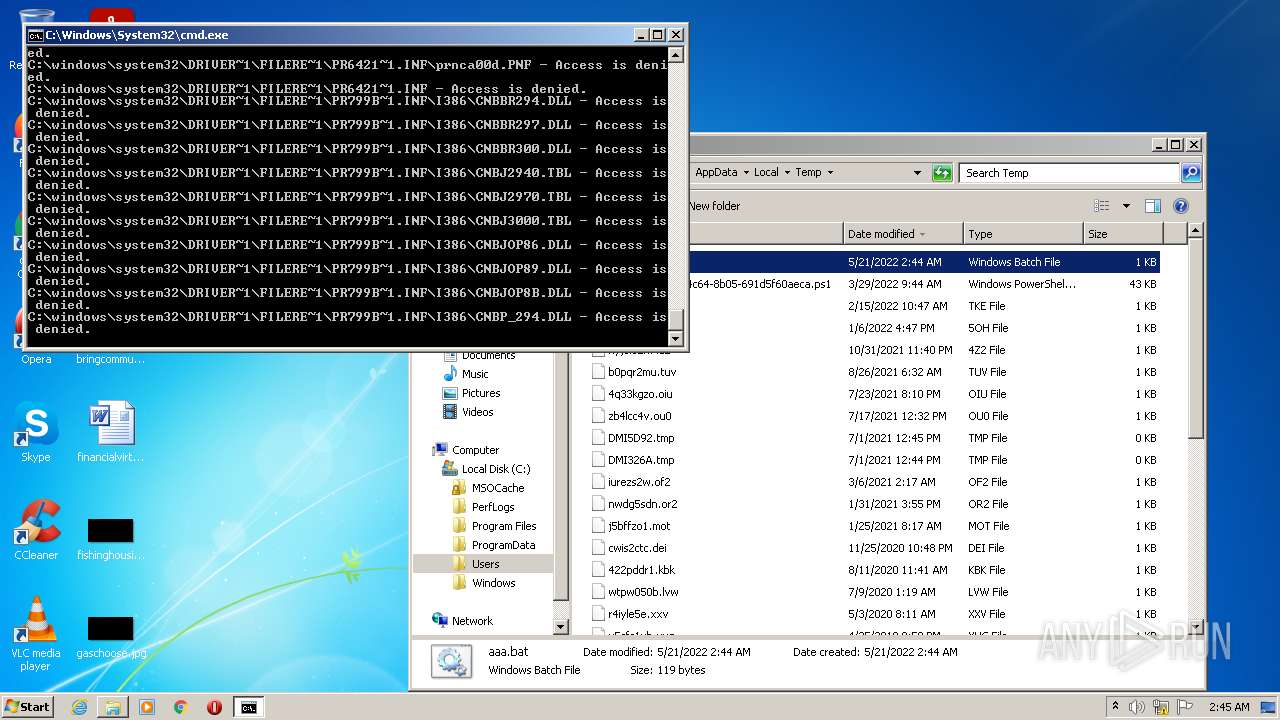
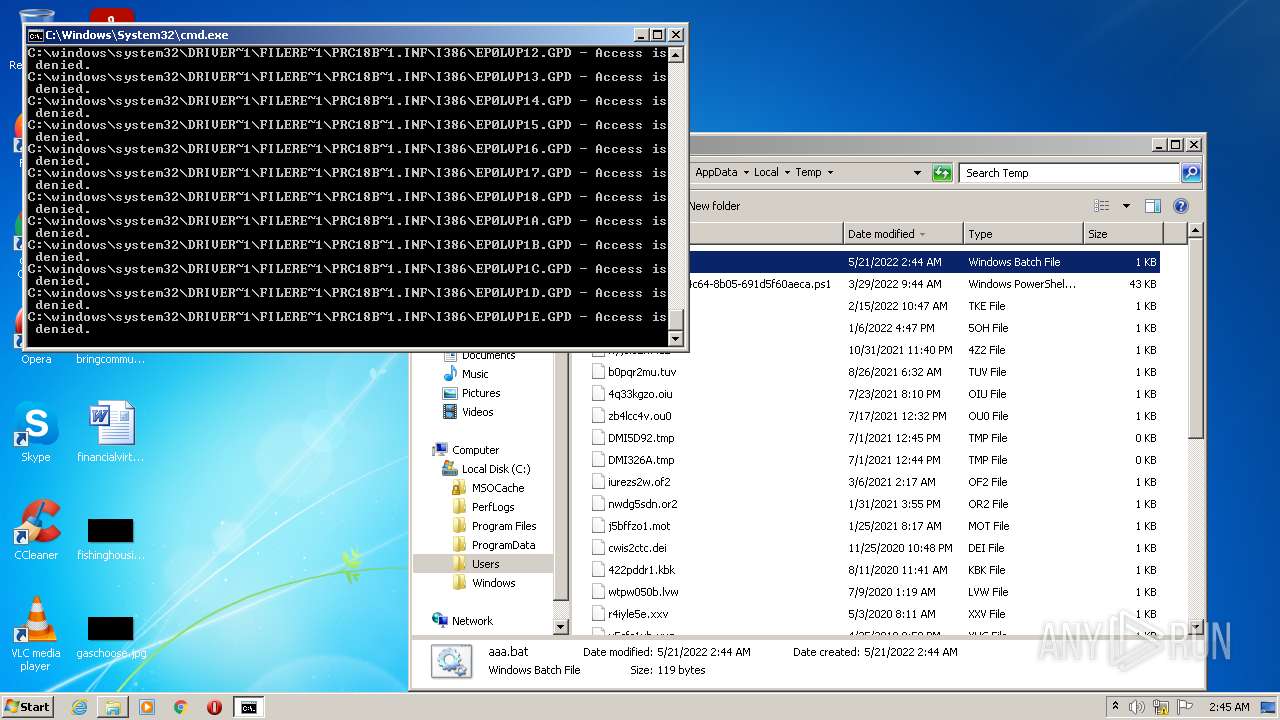
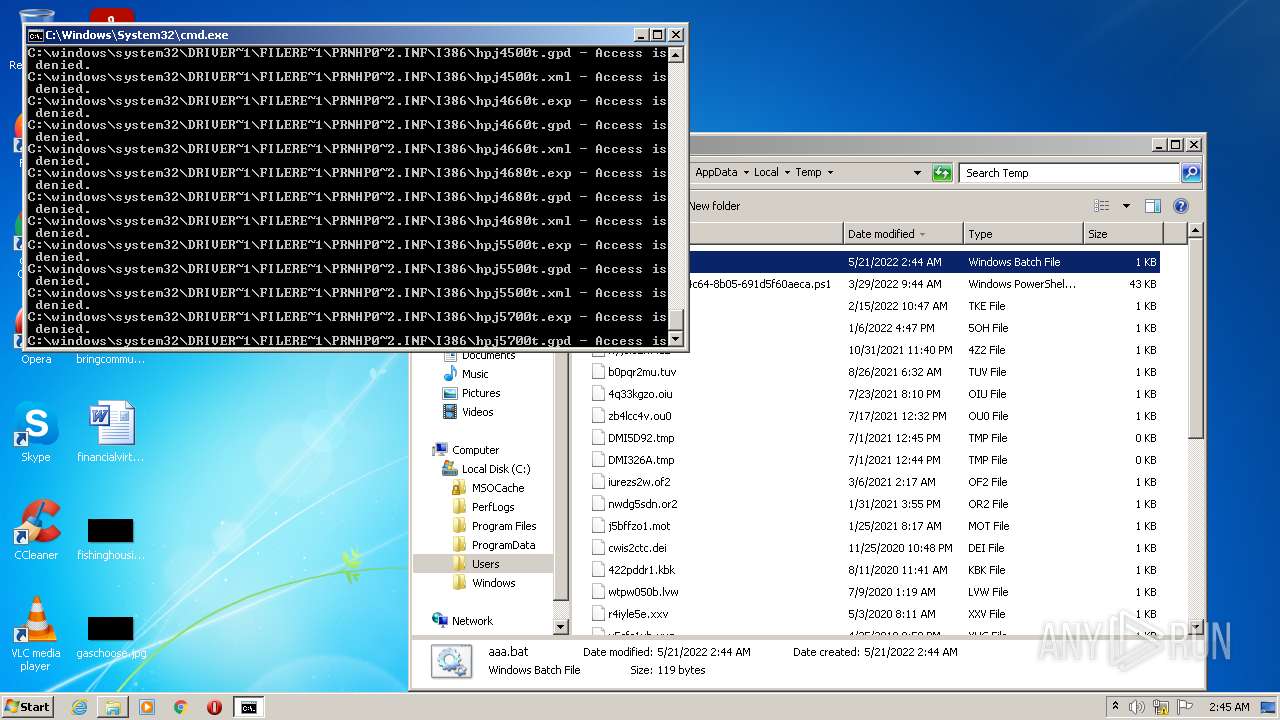
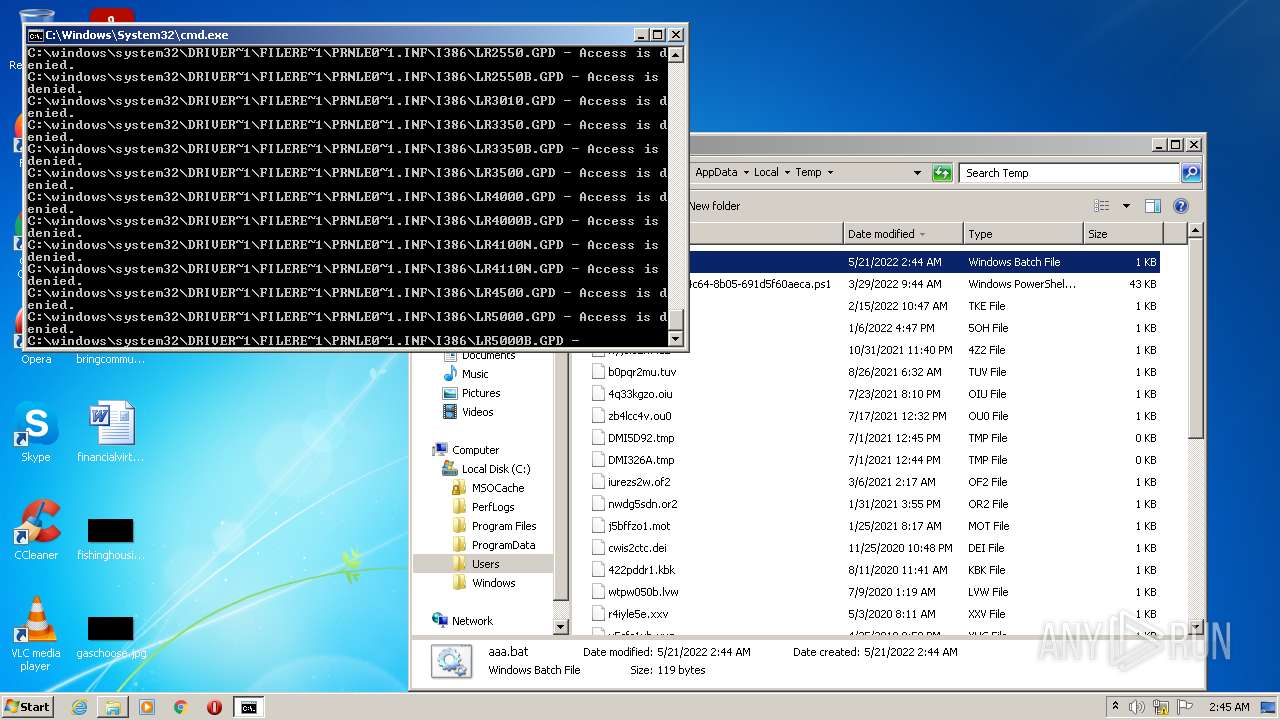
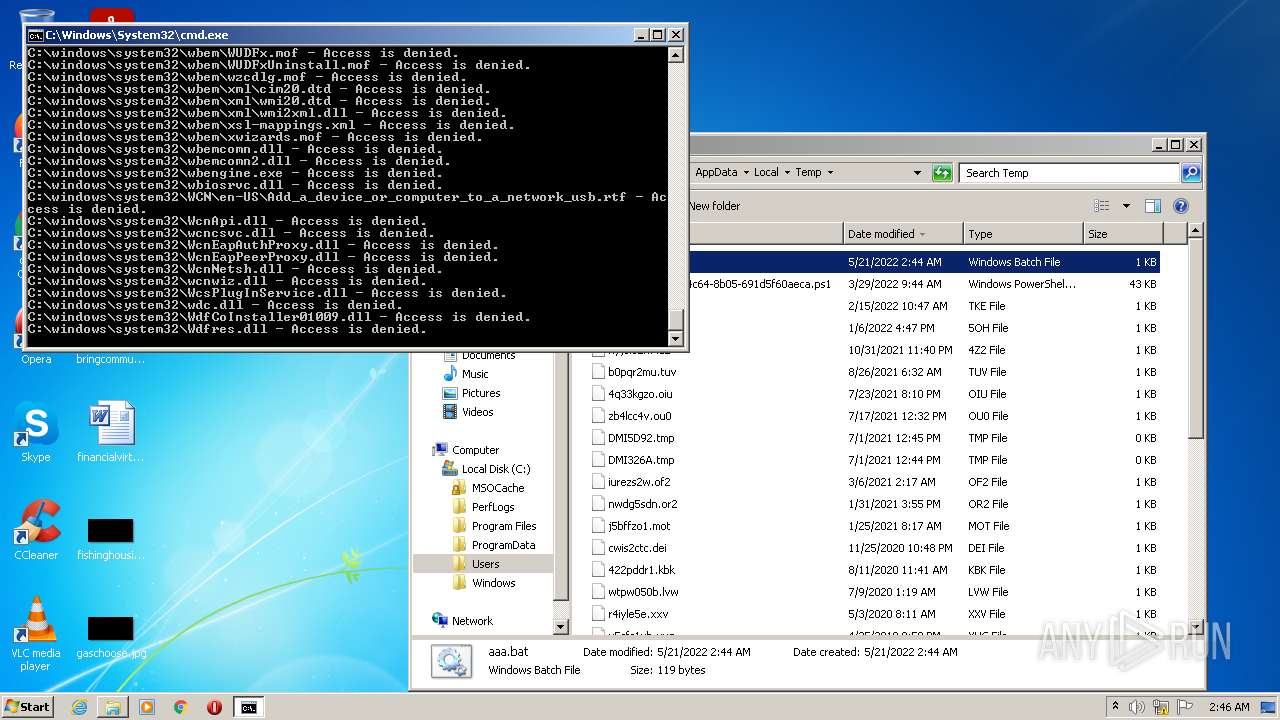
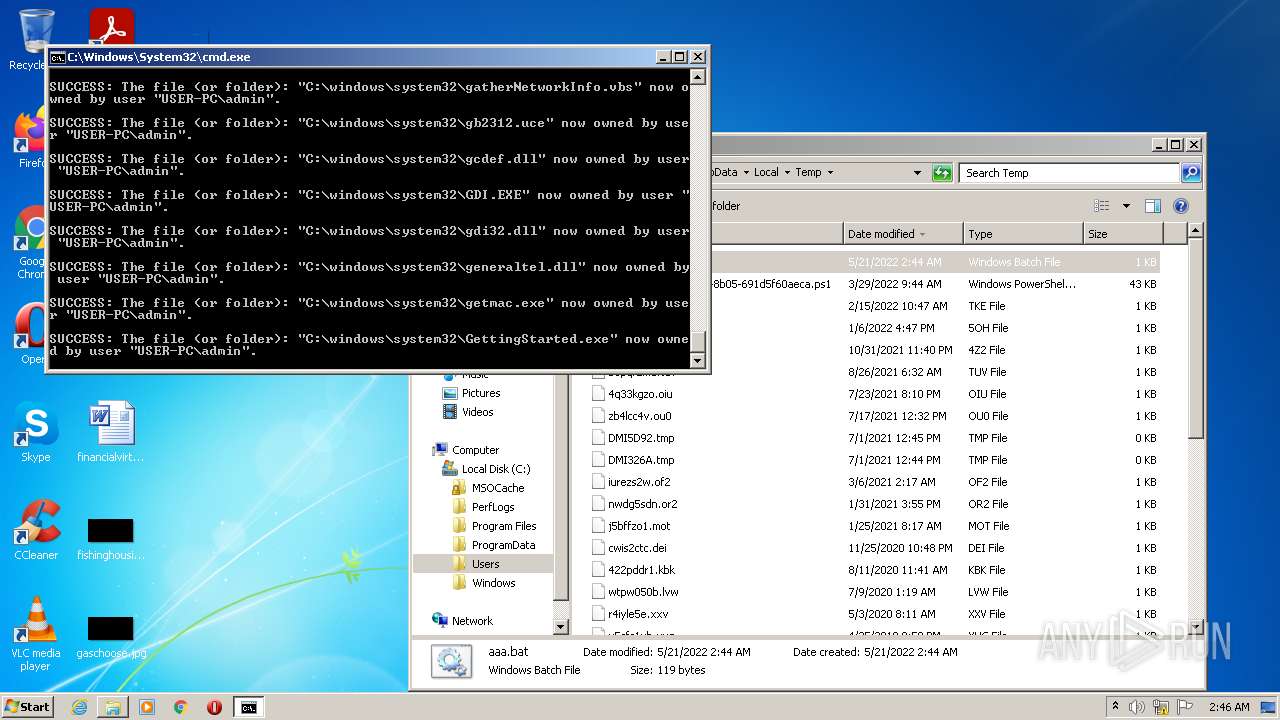
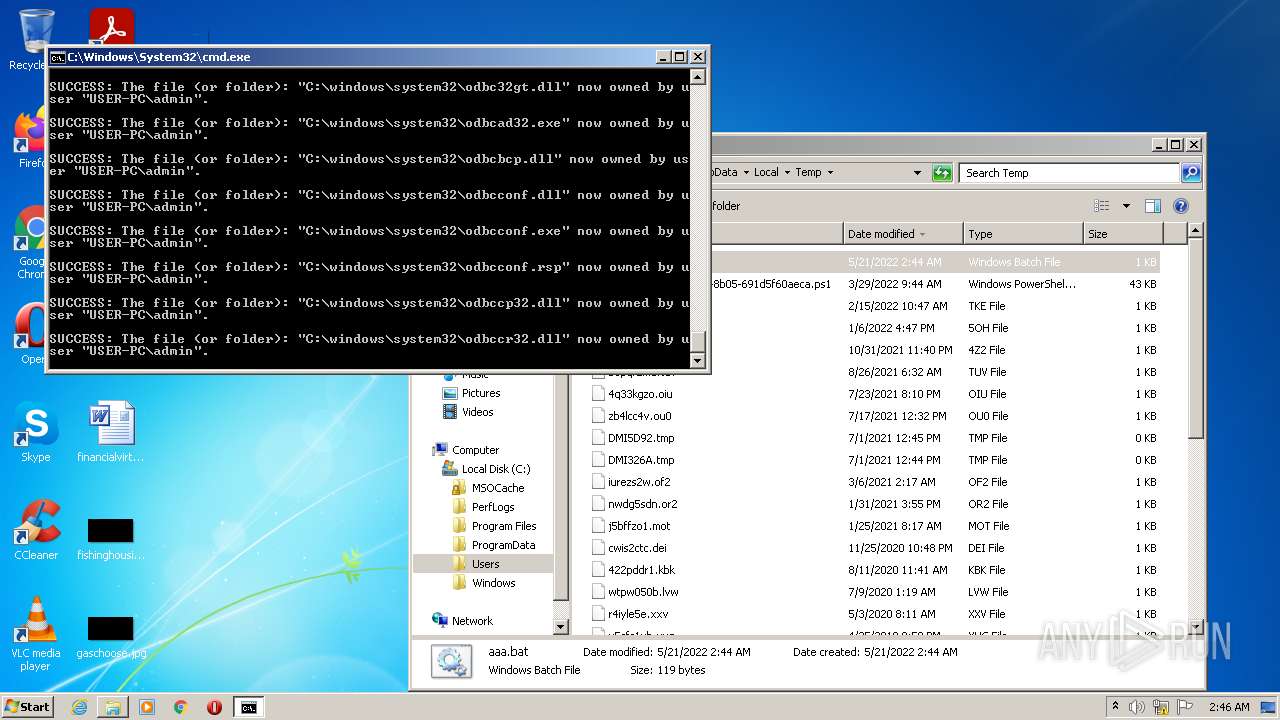
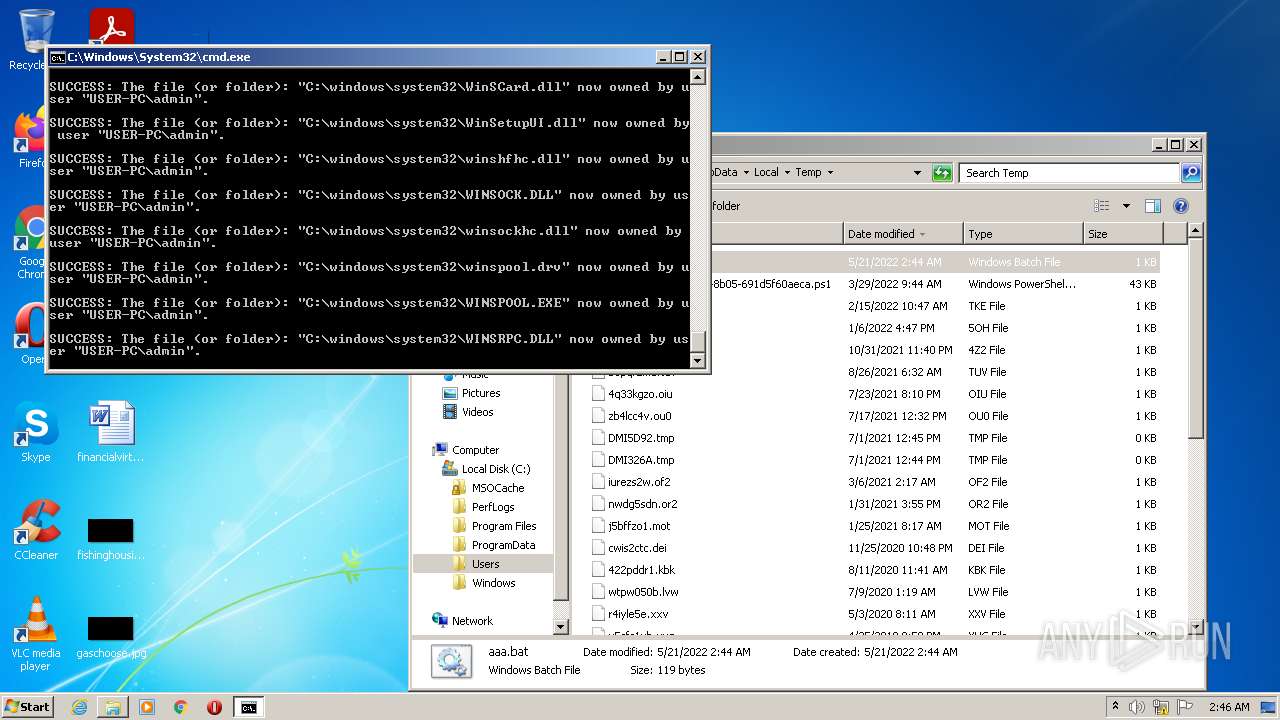
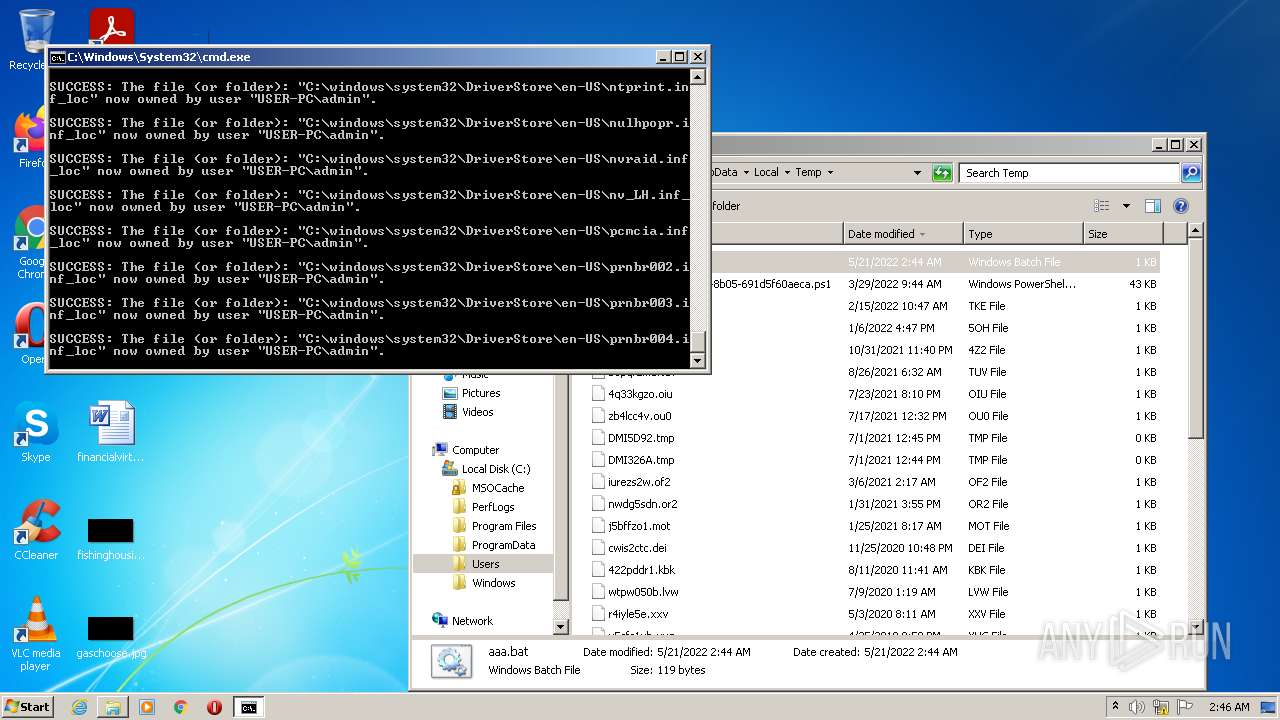
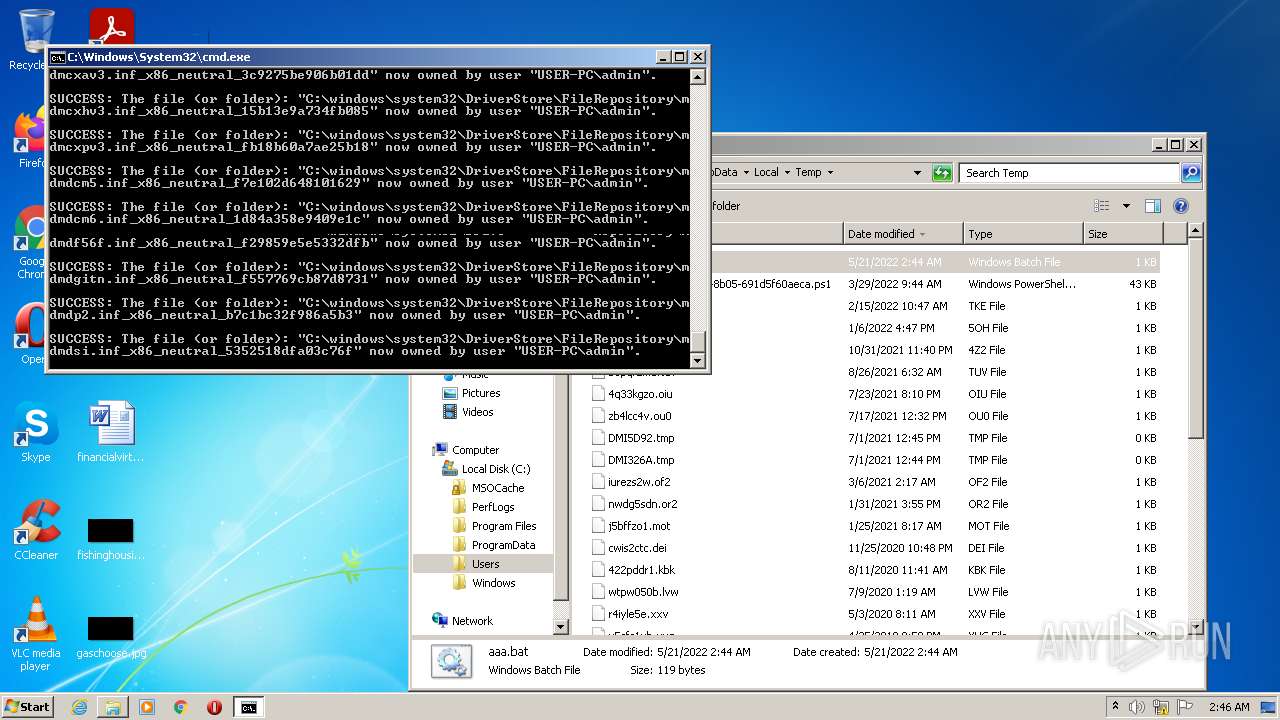
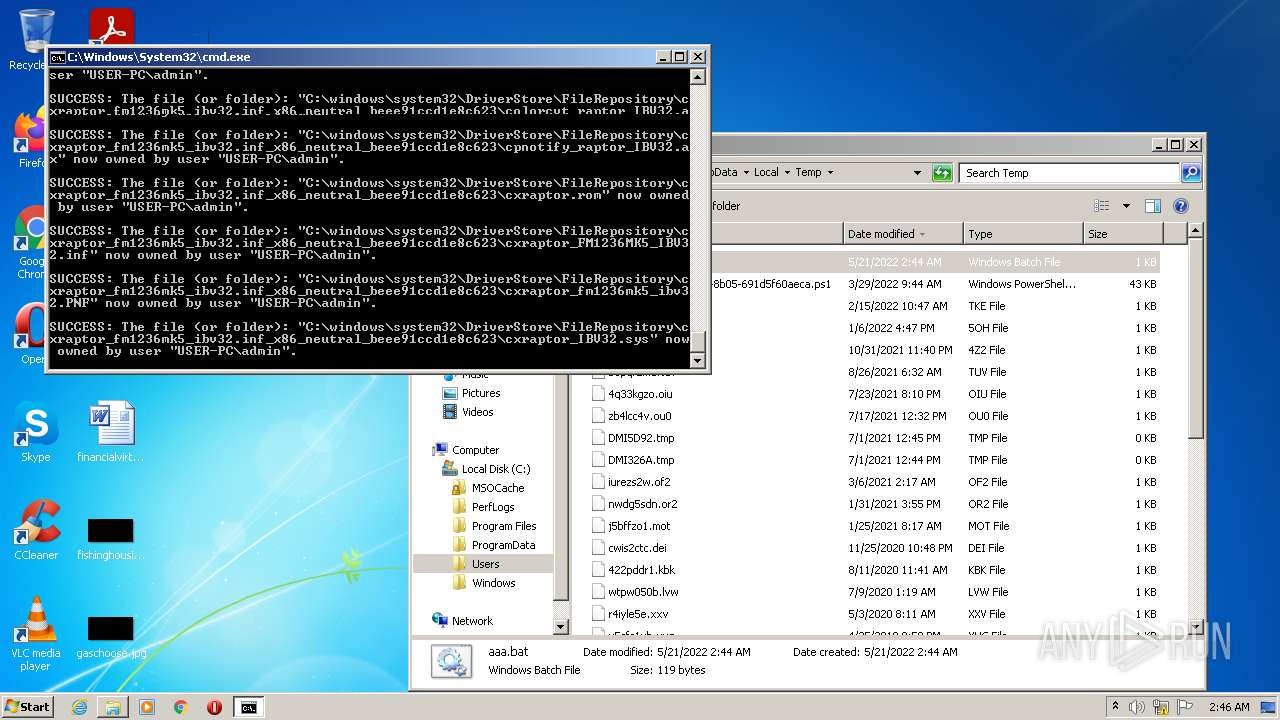
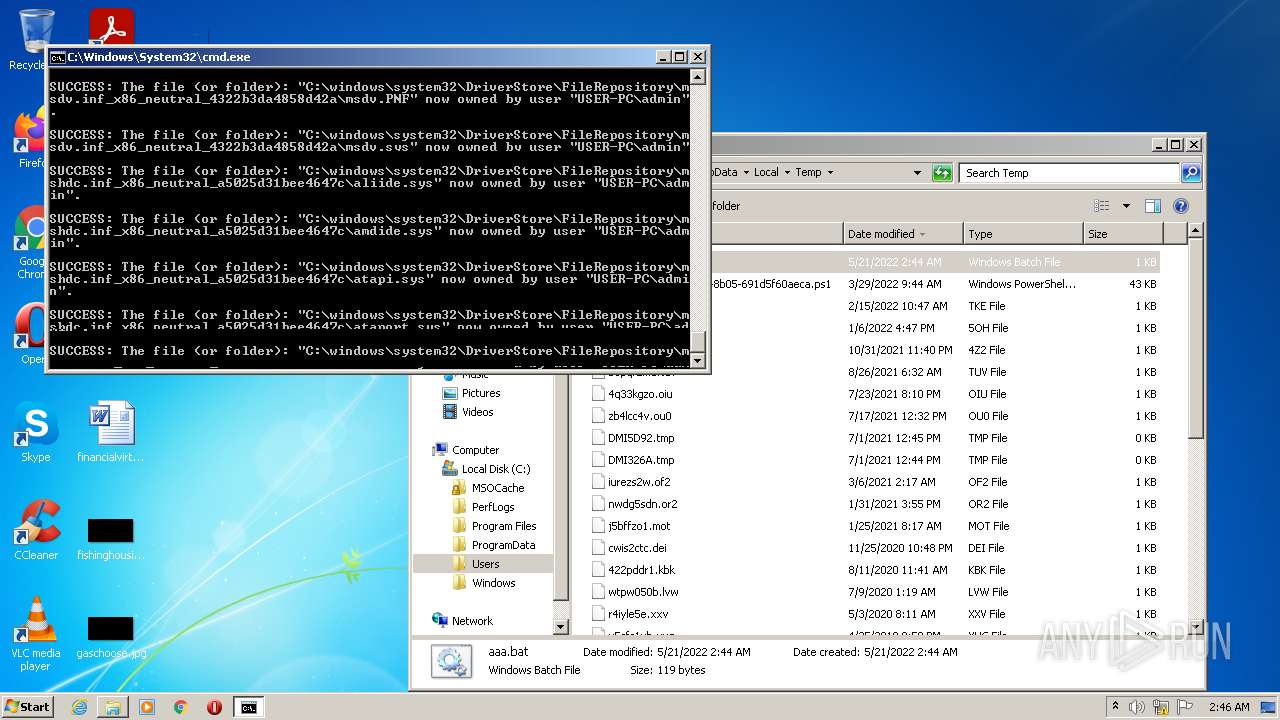
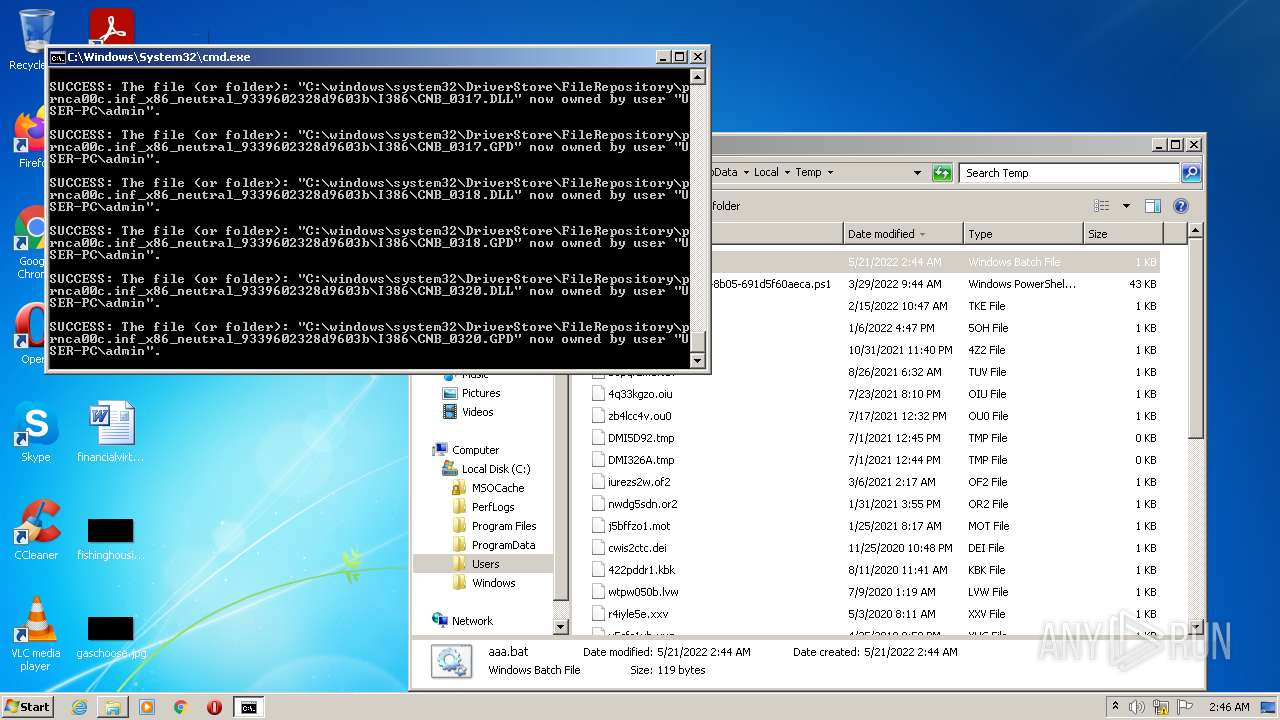
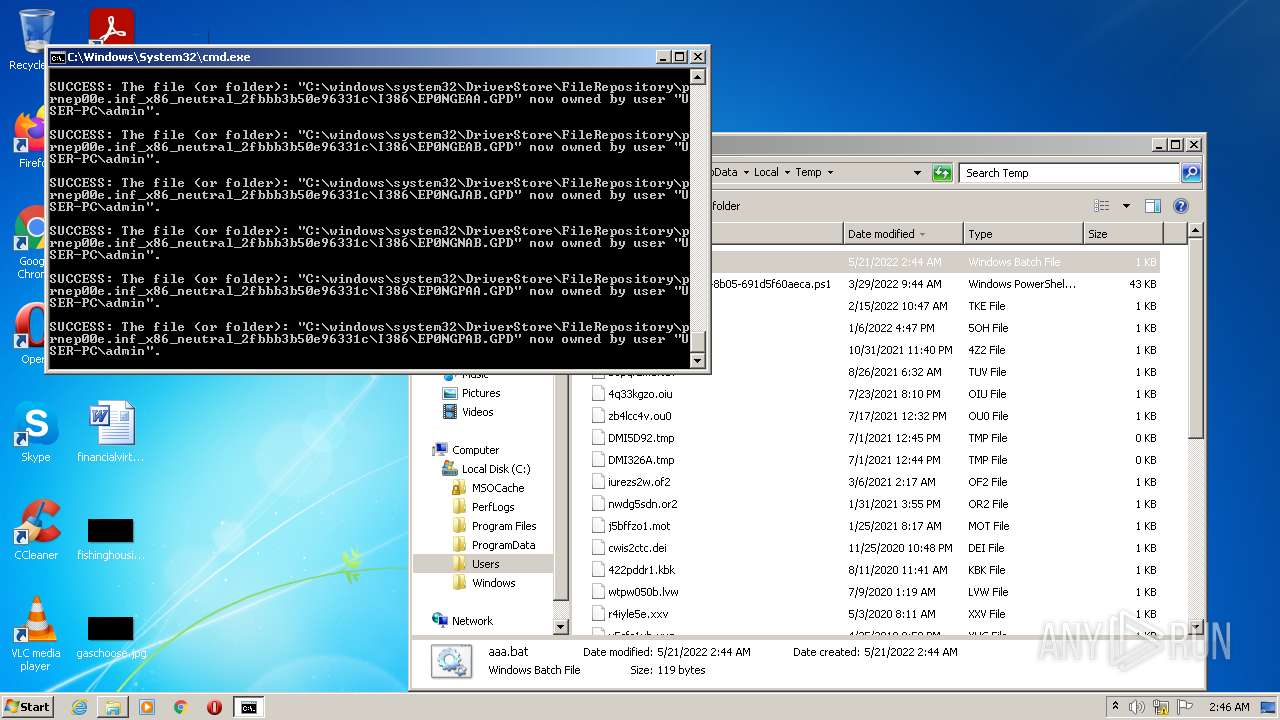
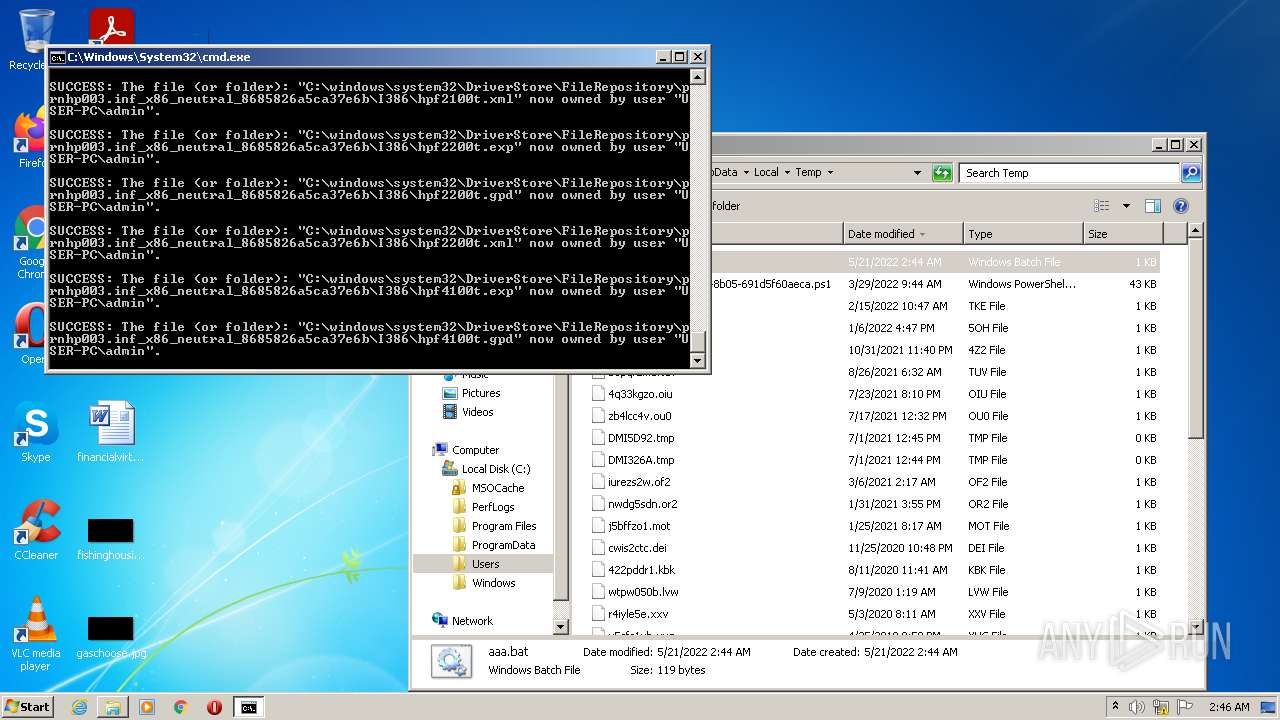
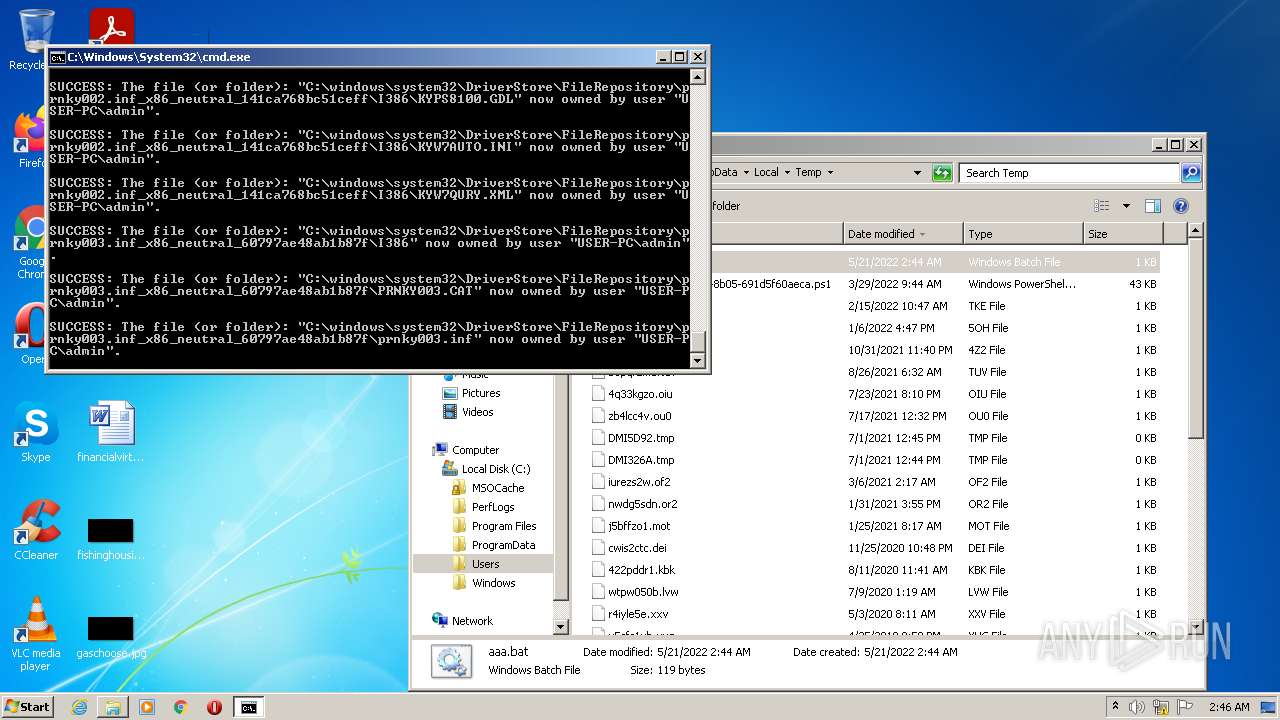
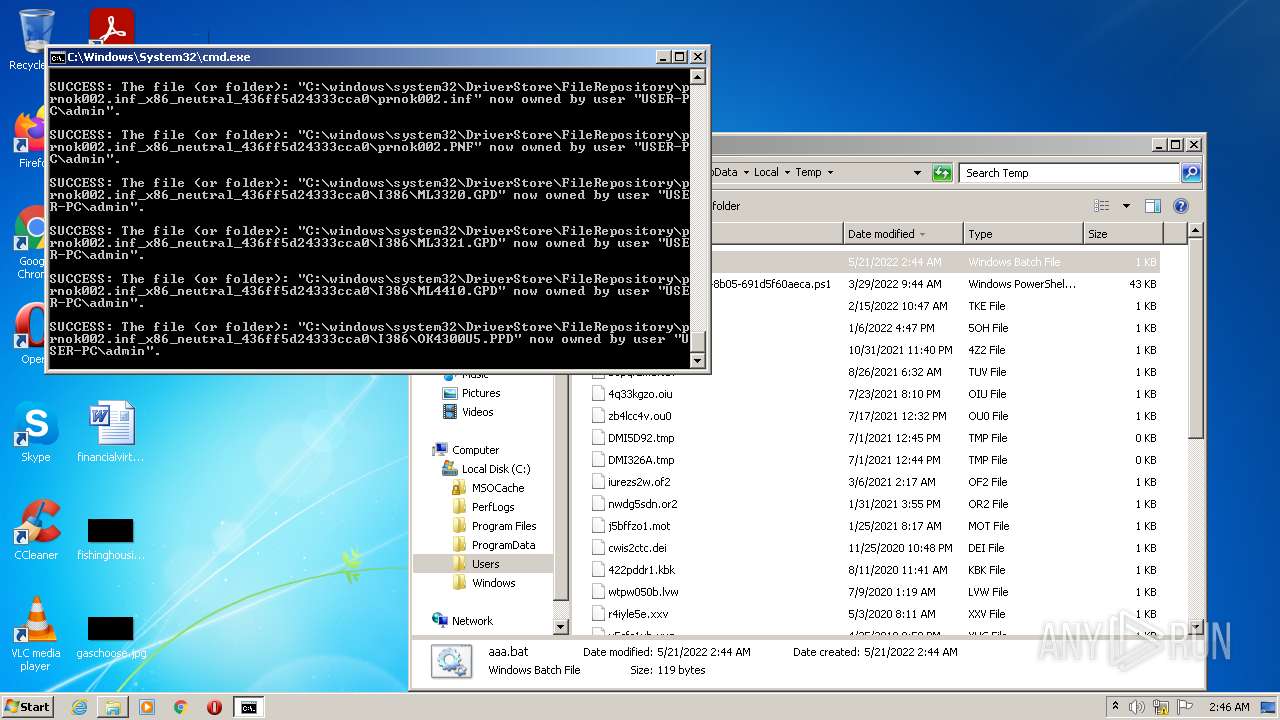
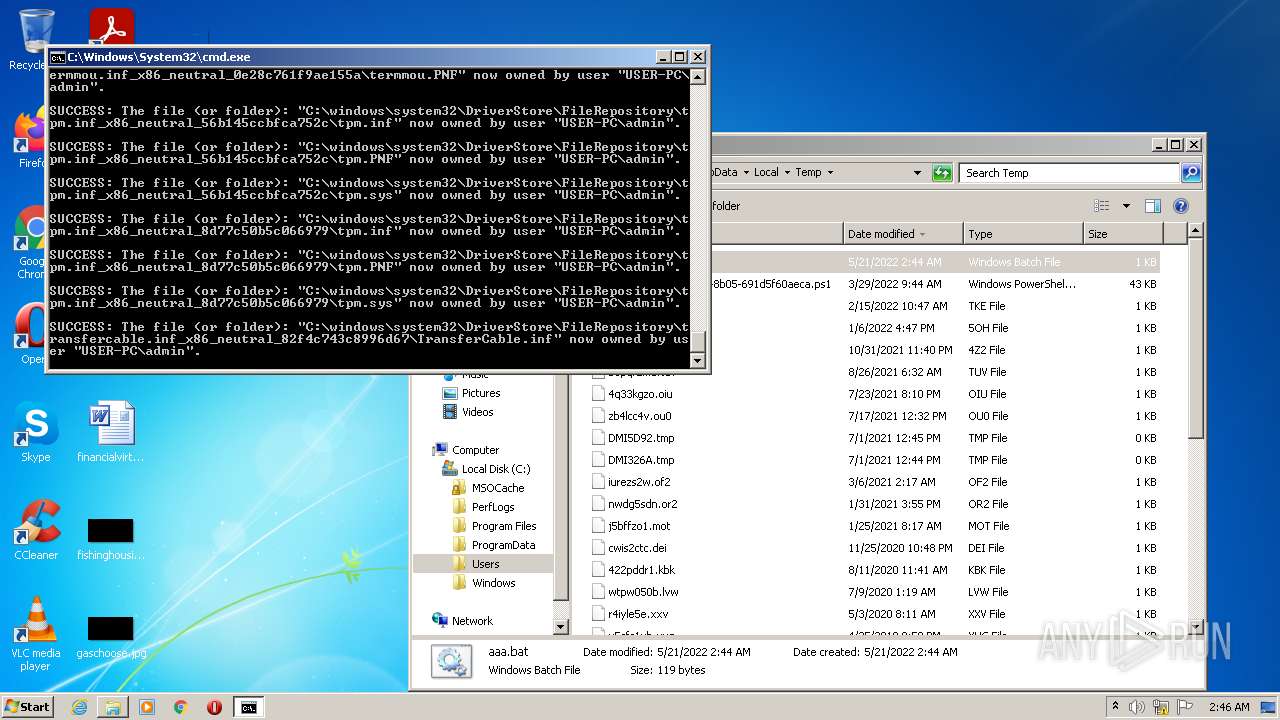
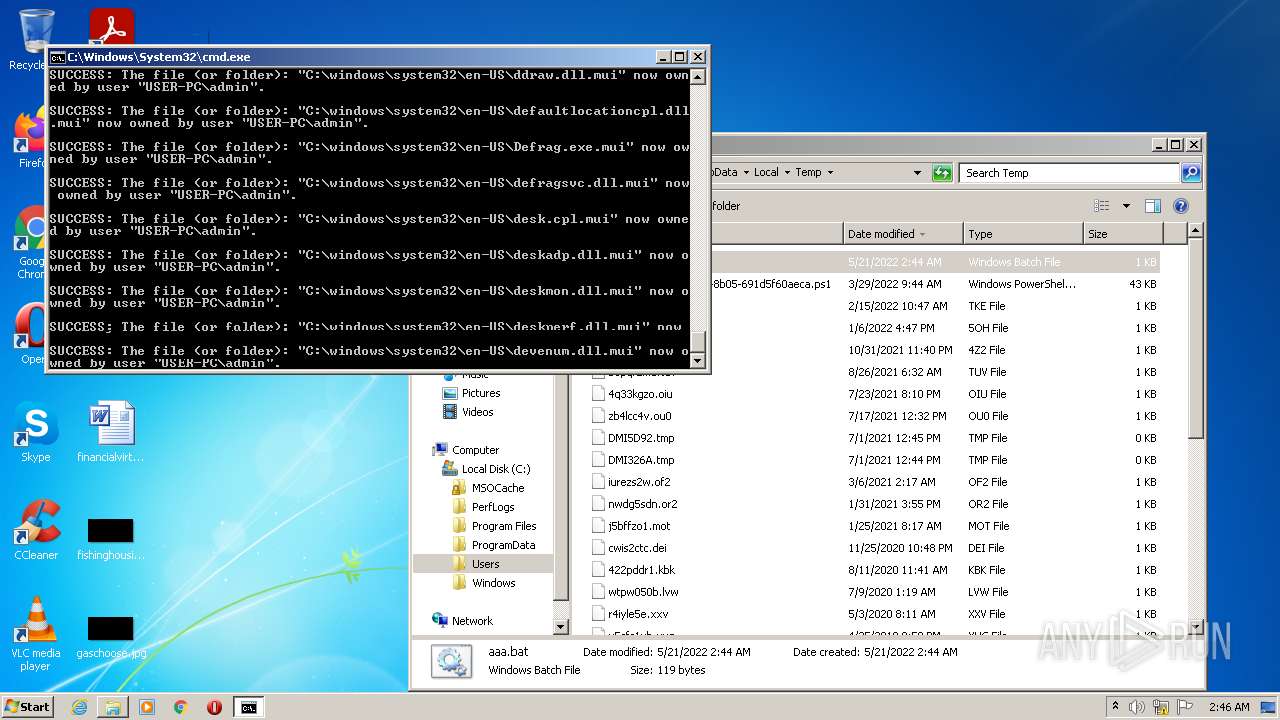
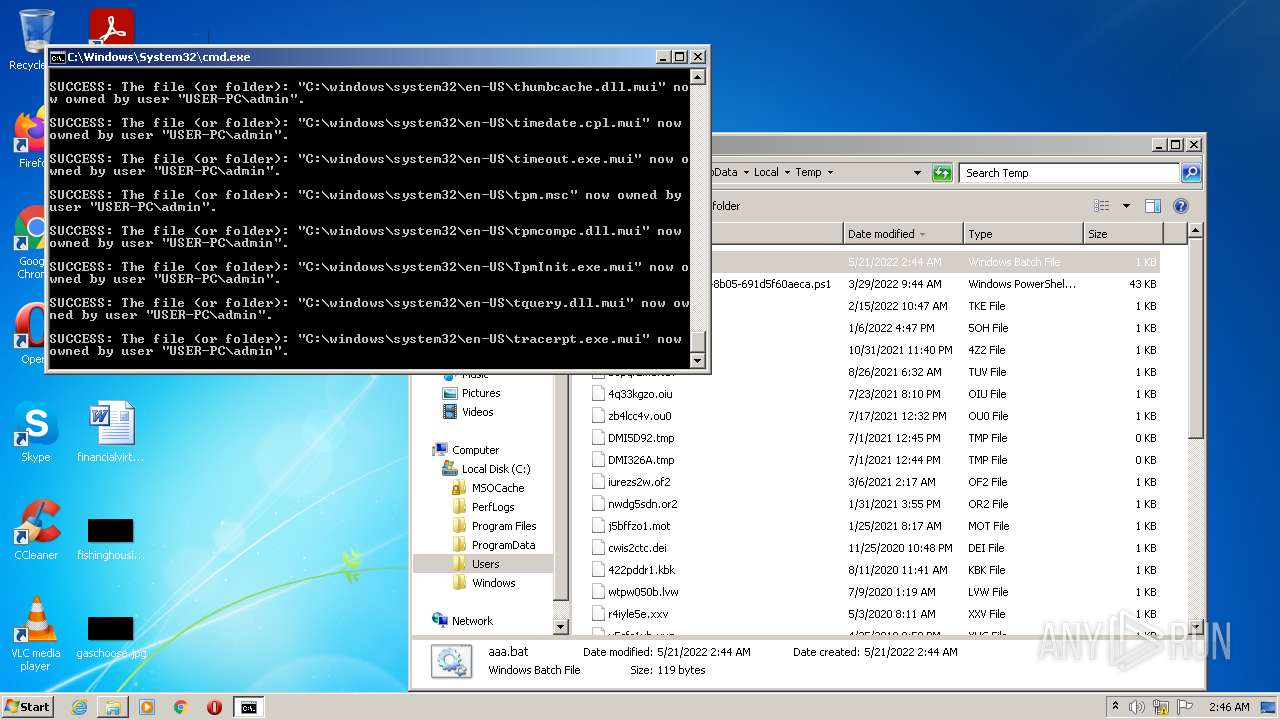
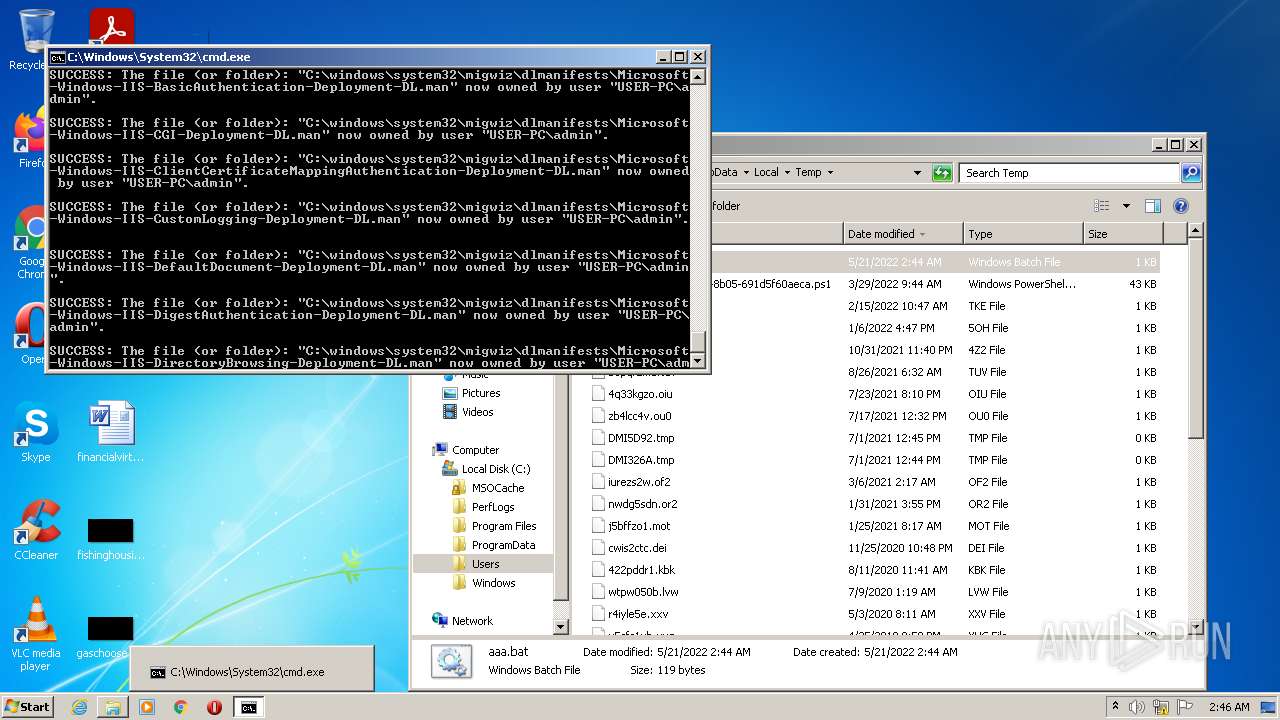
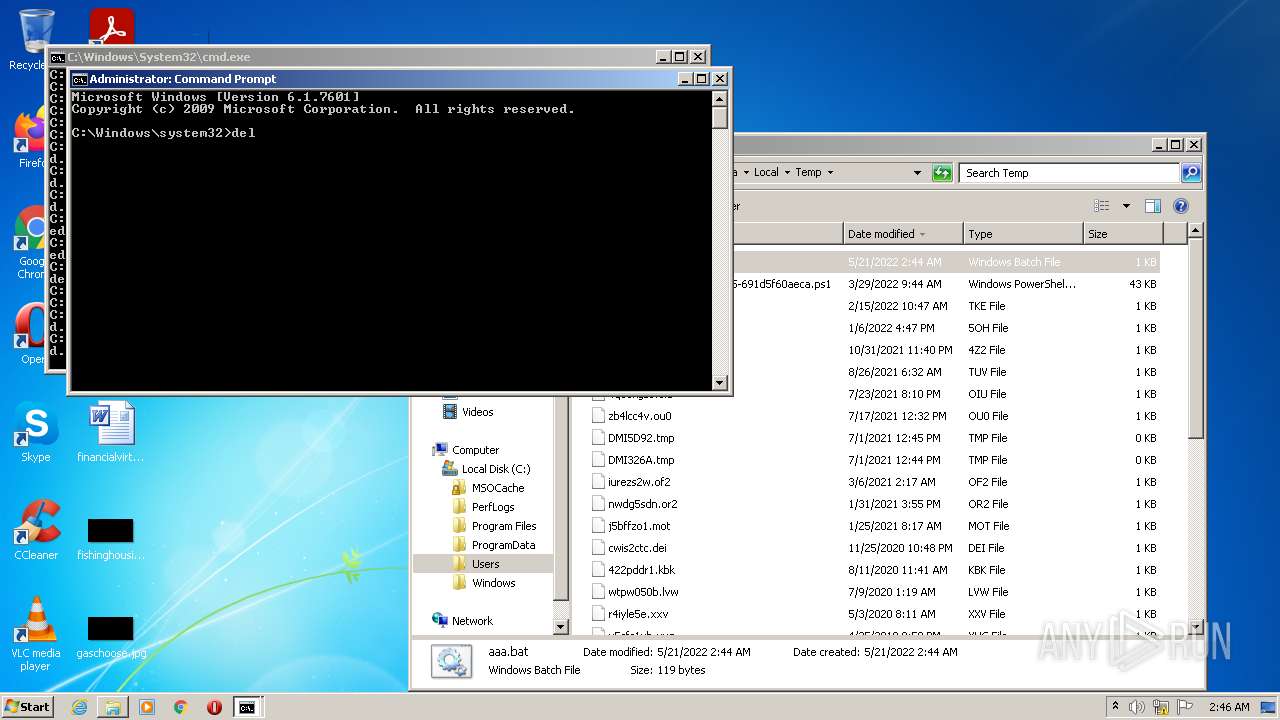
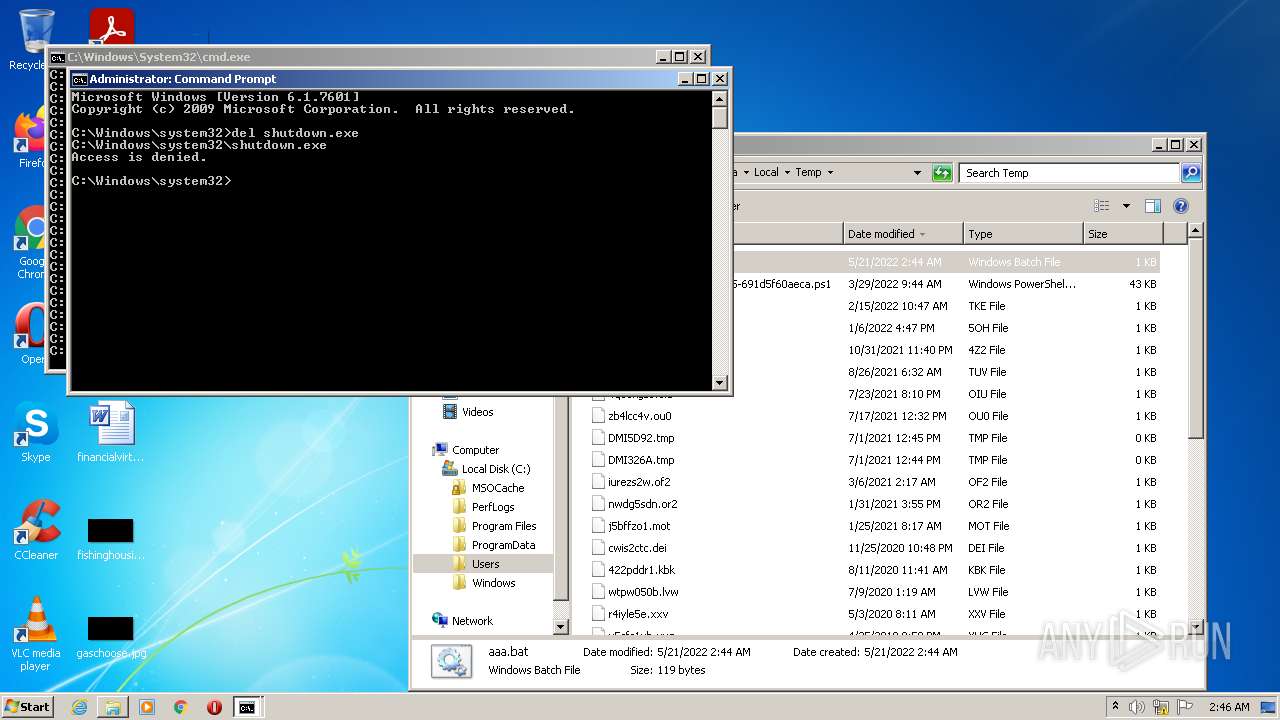
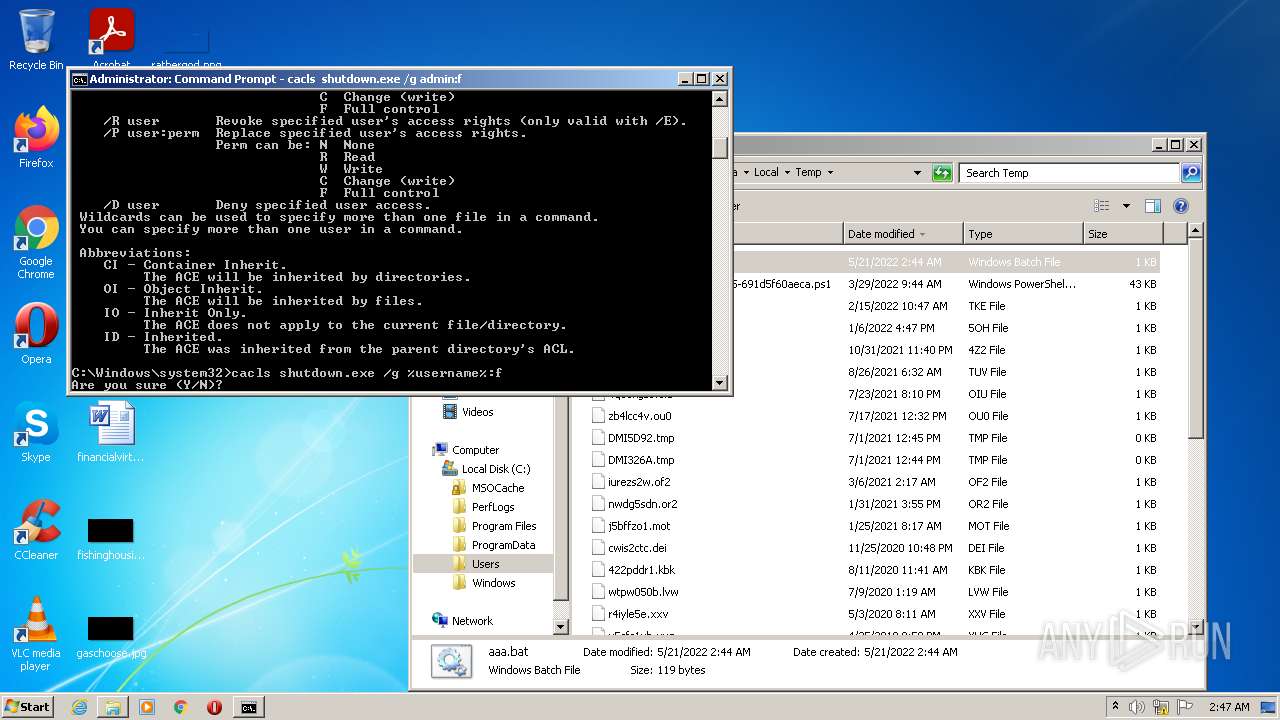
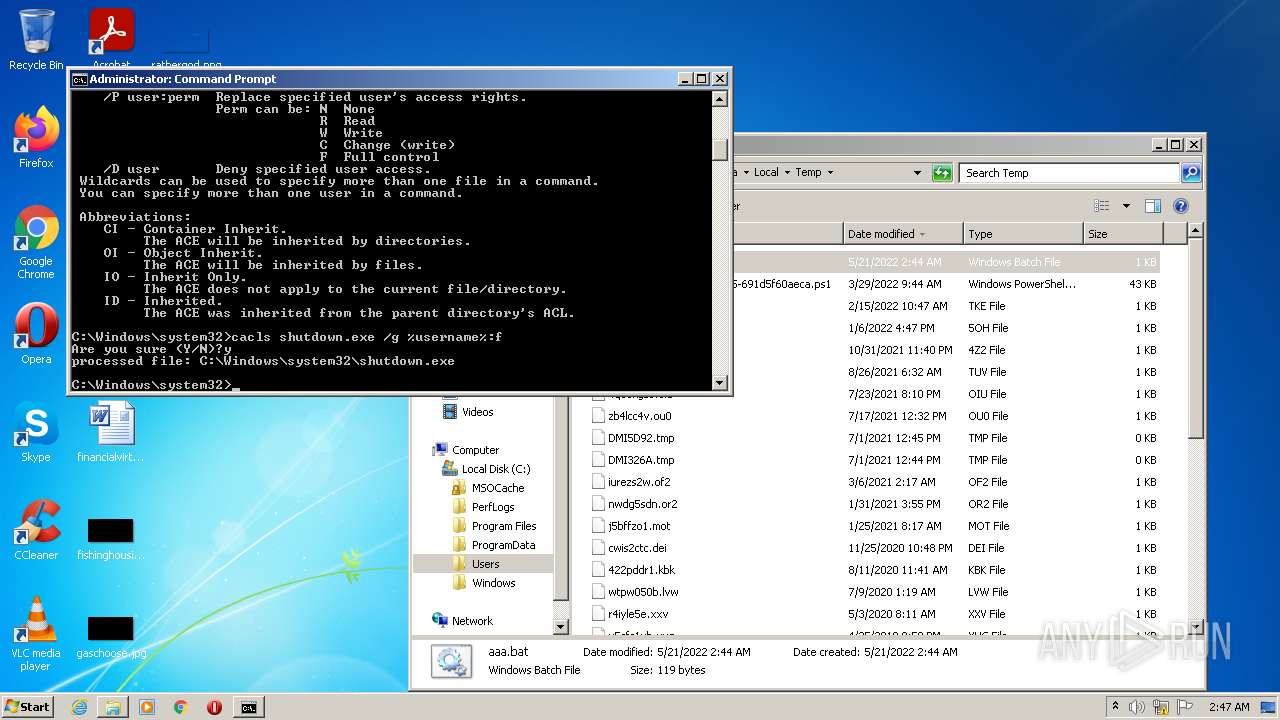
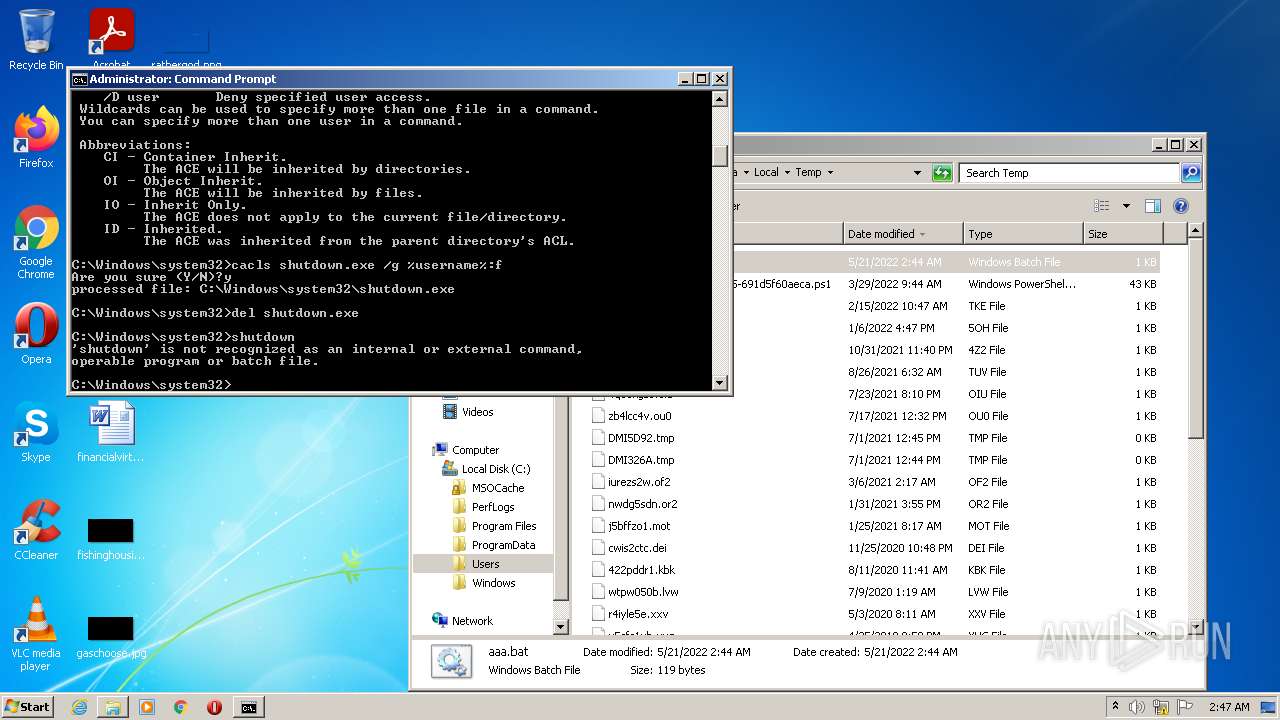
MALICIOUS
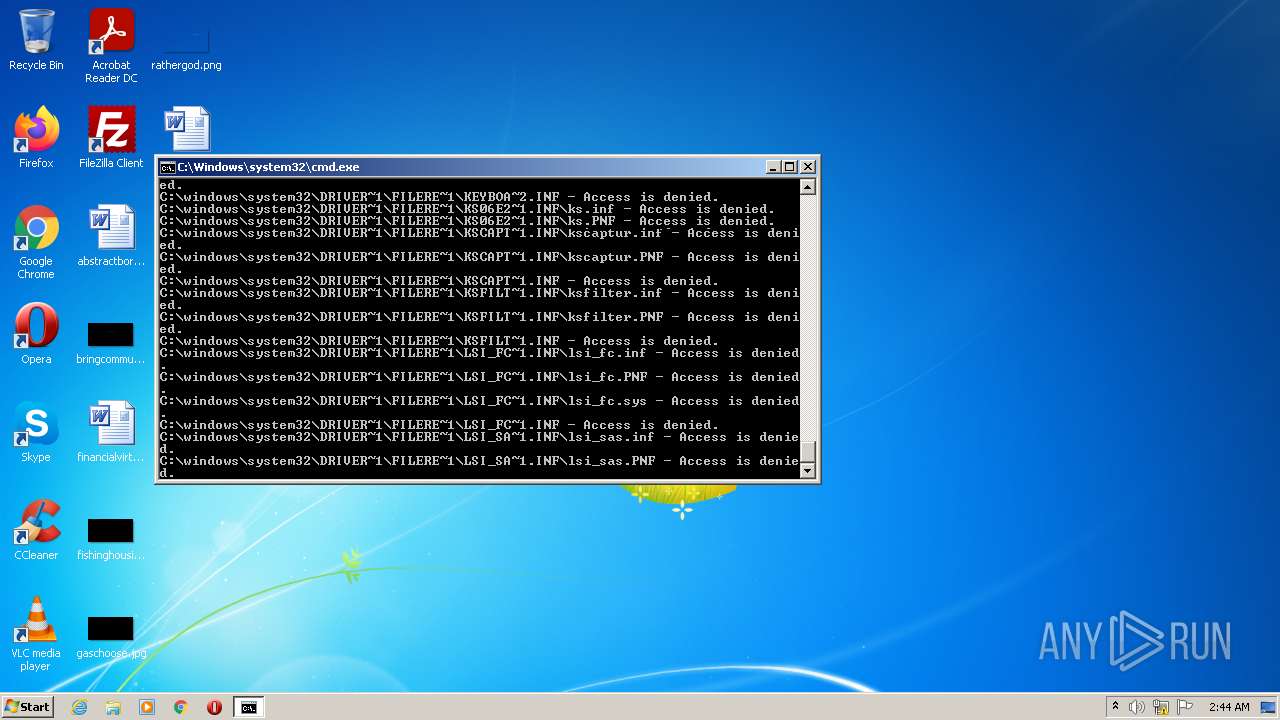
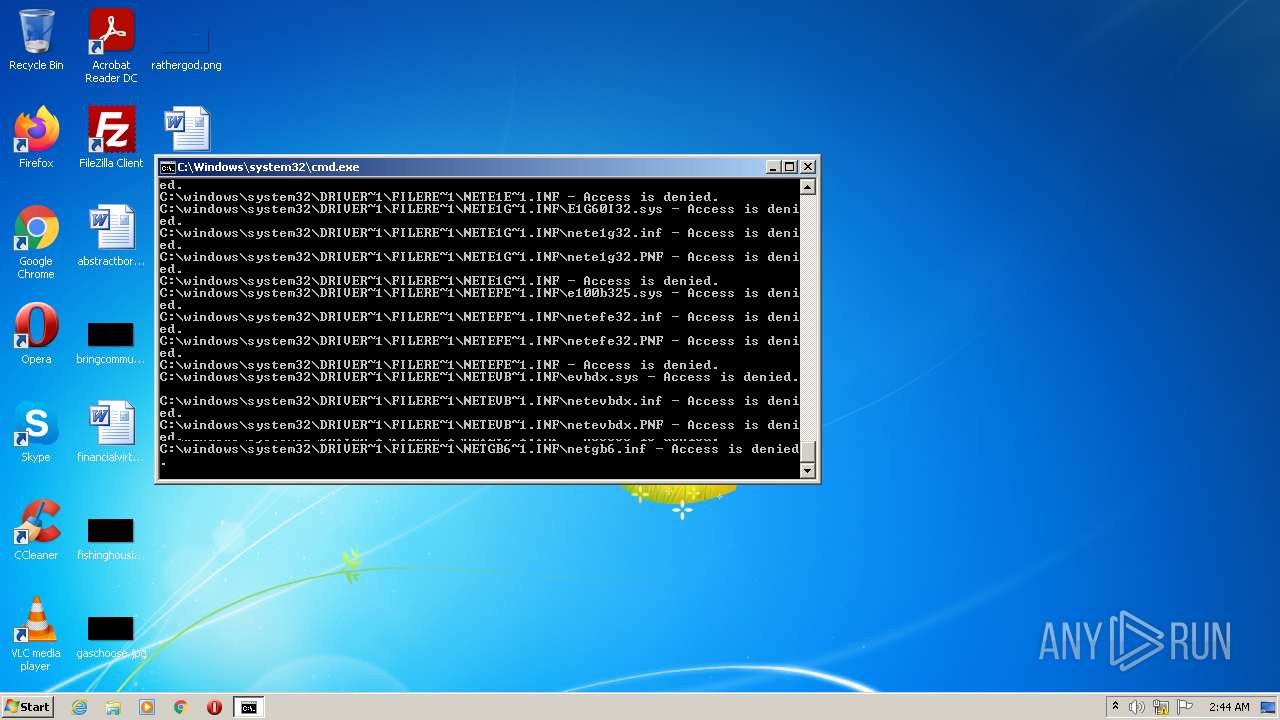
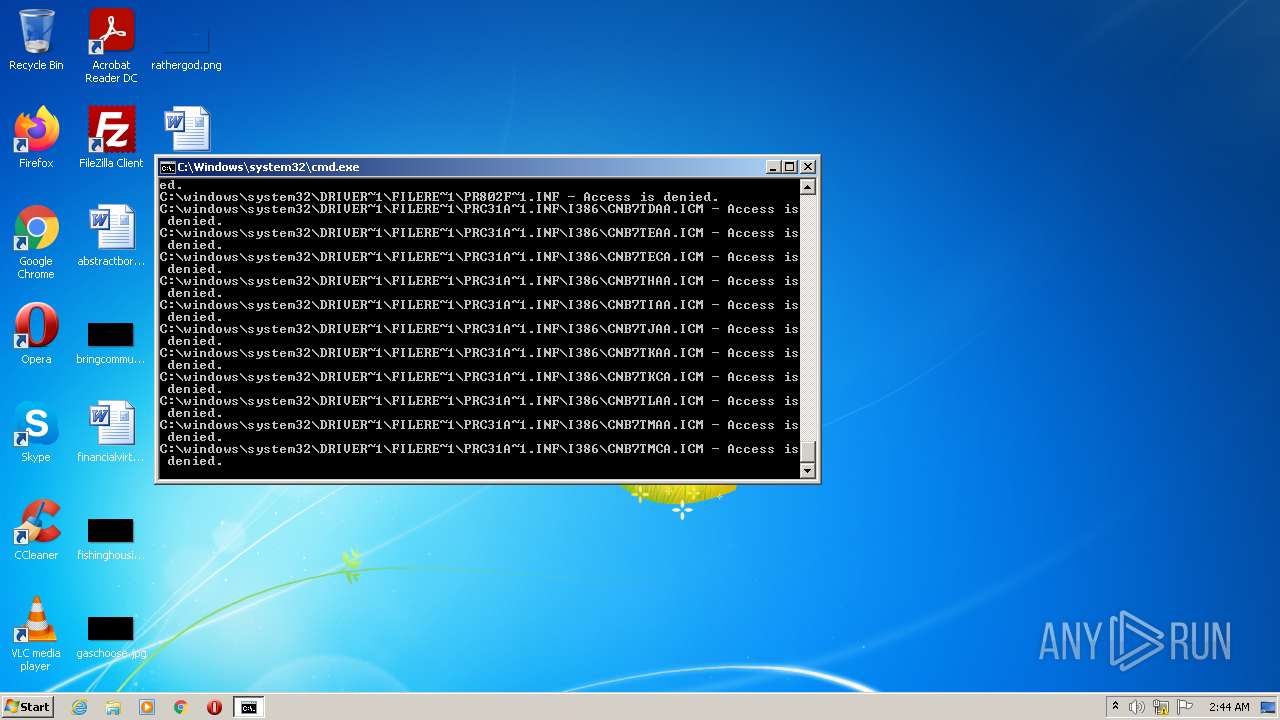
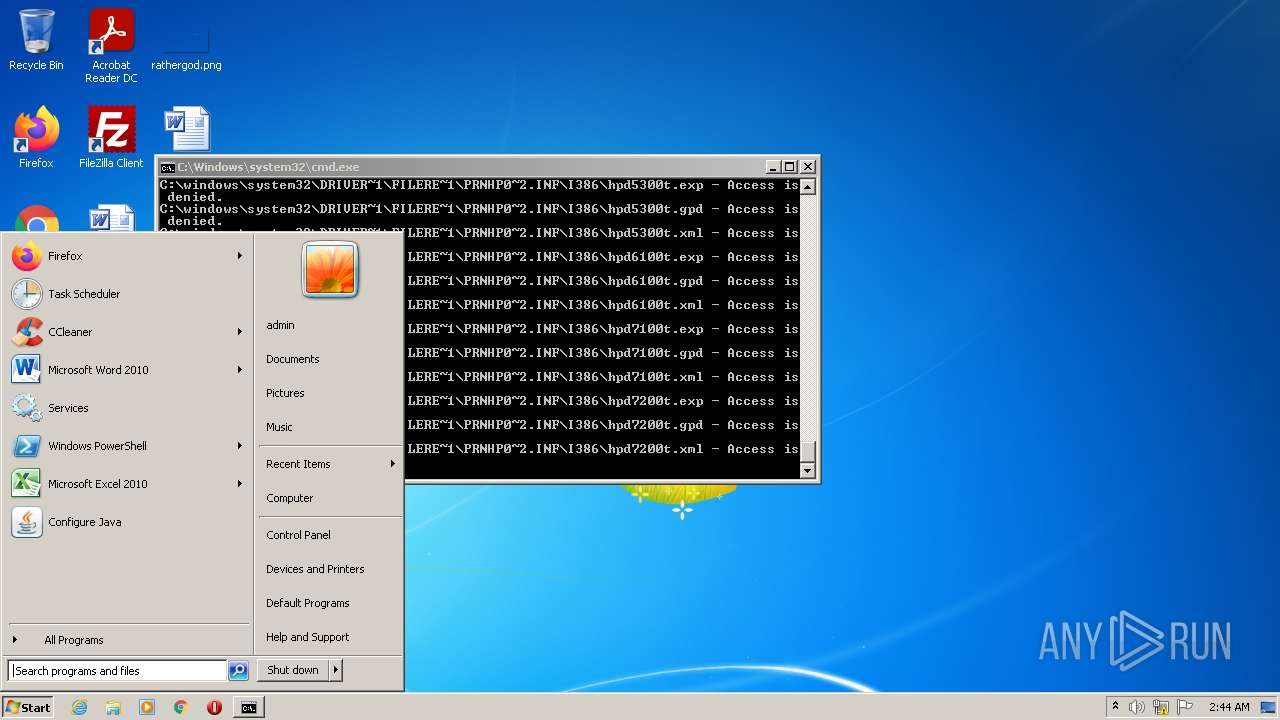
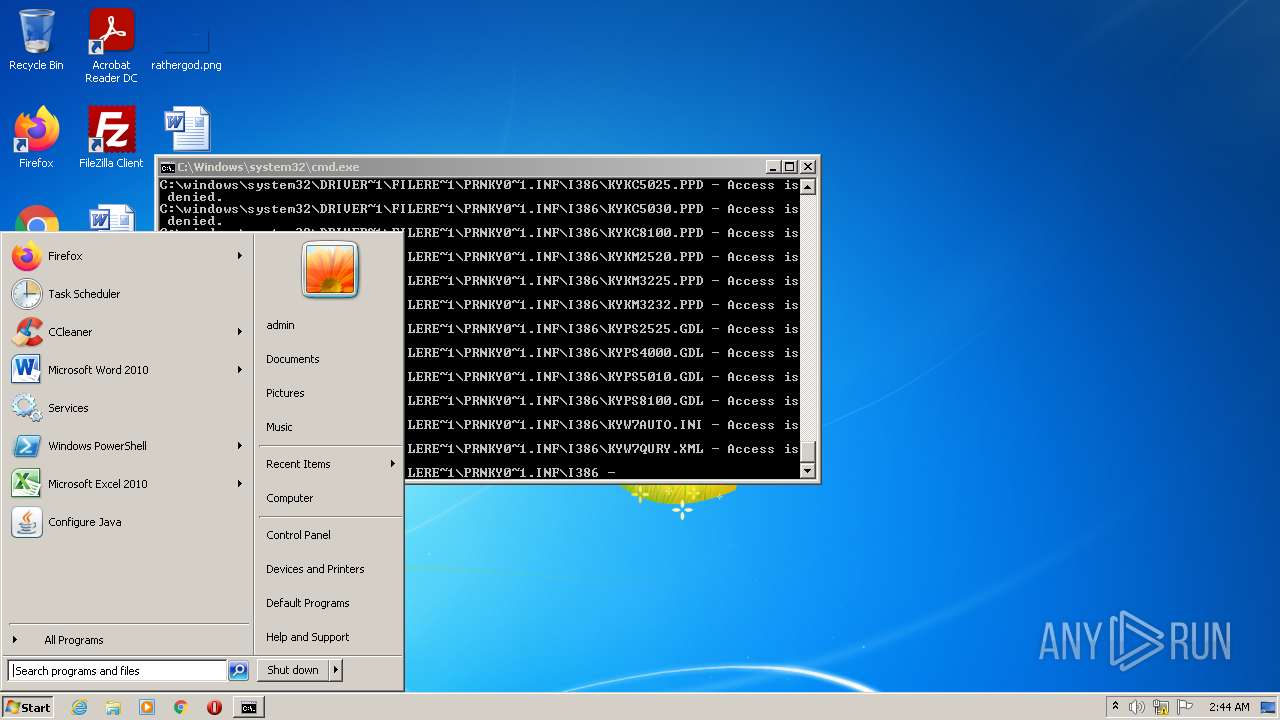
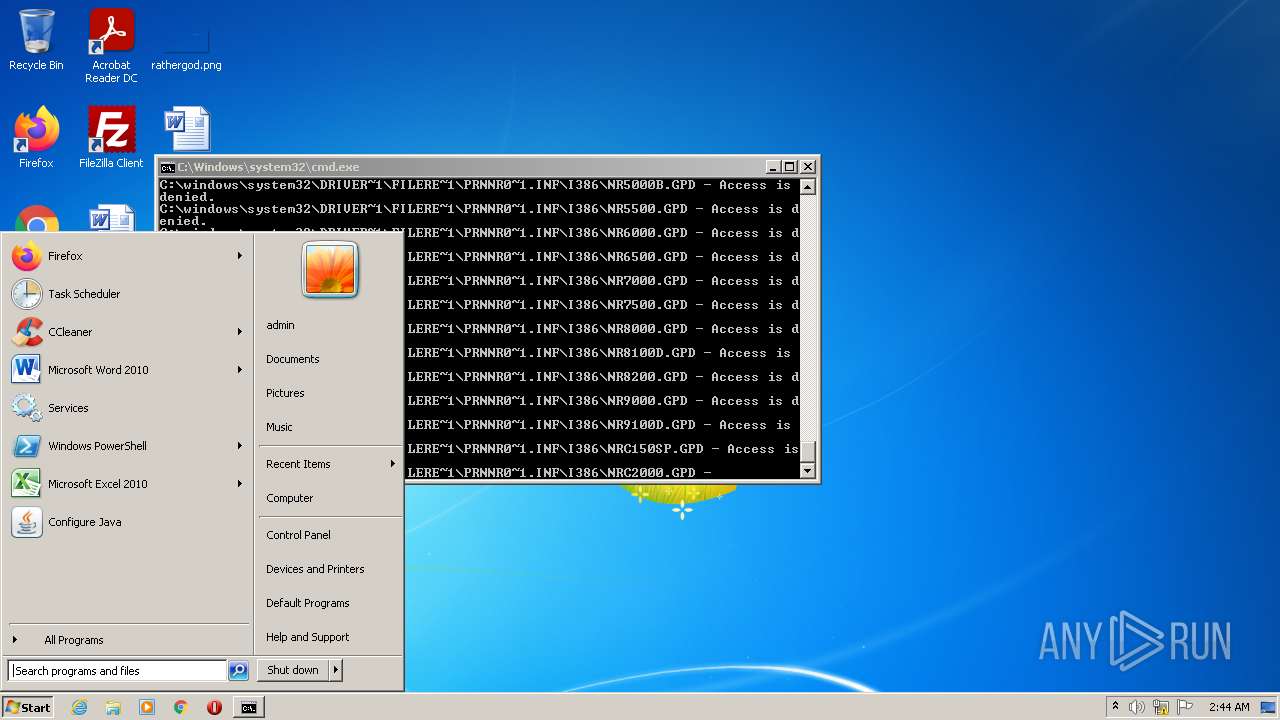
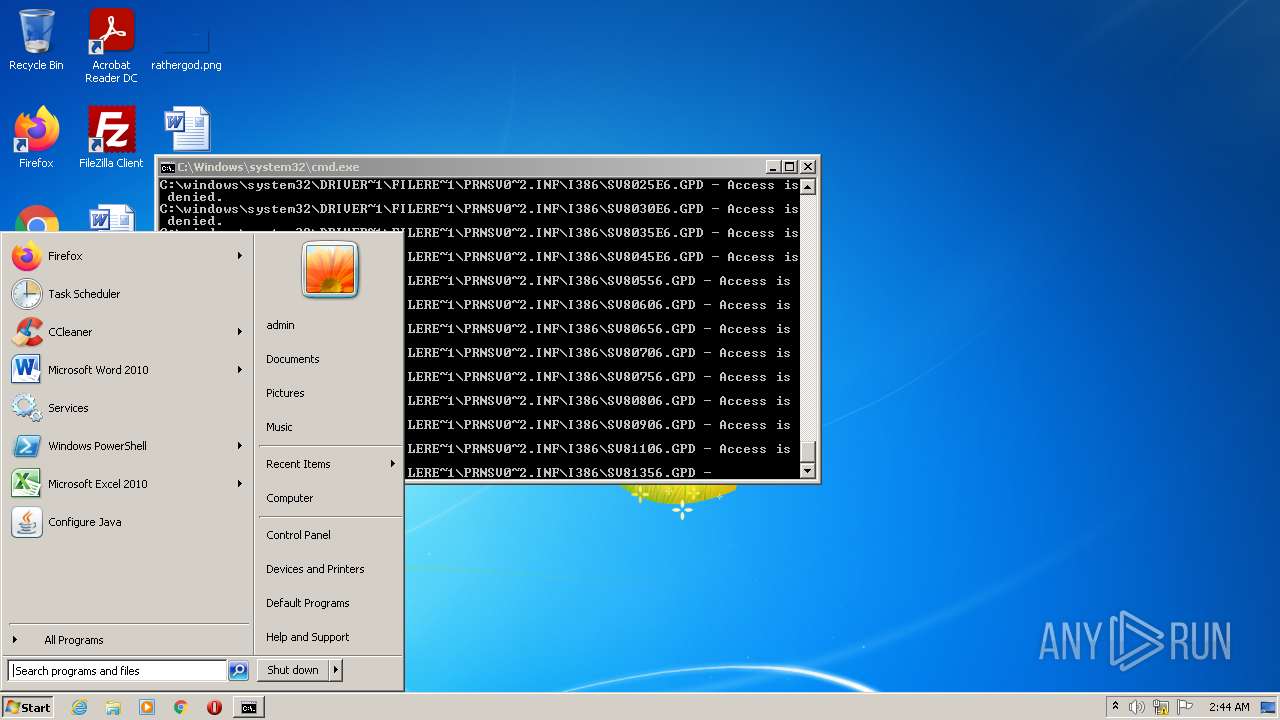
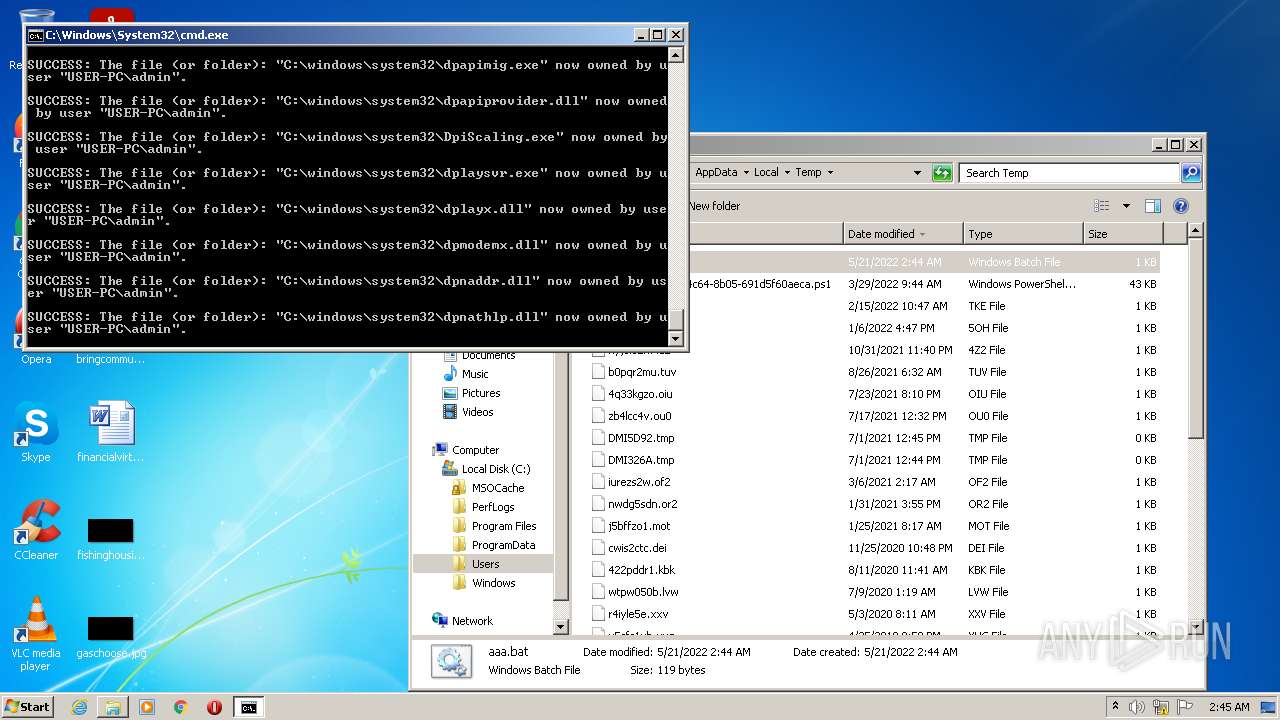
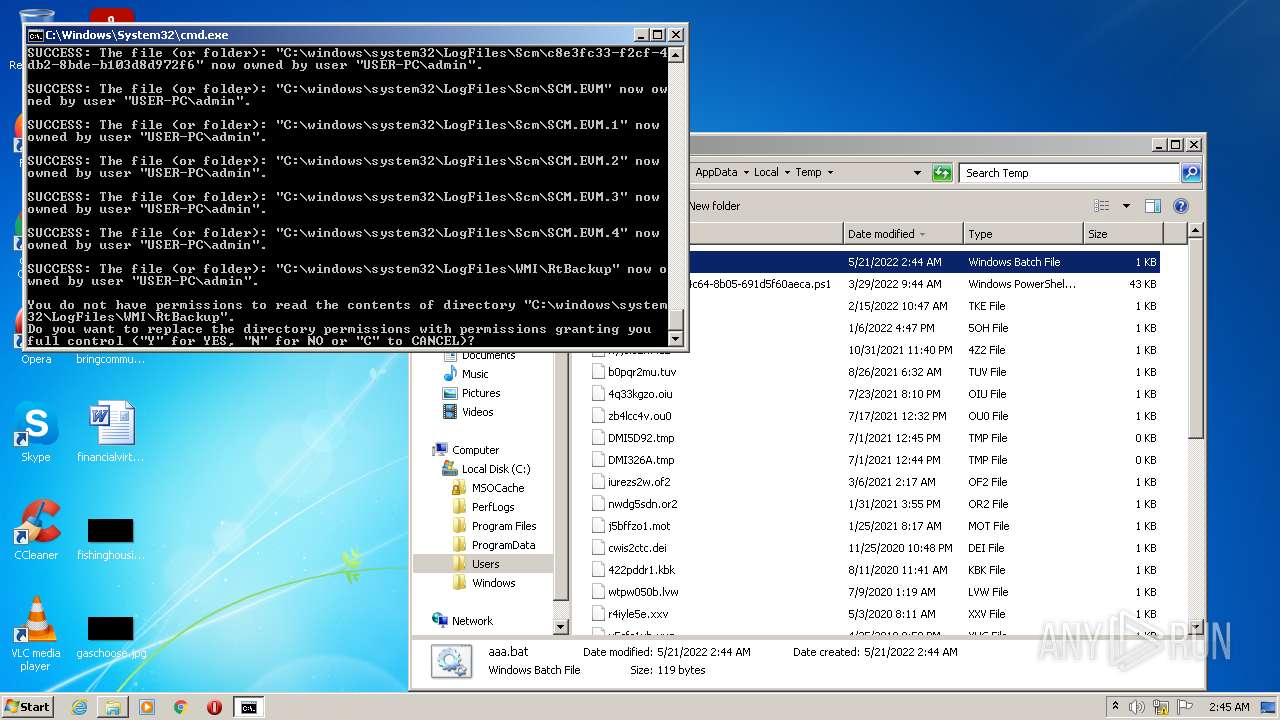
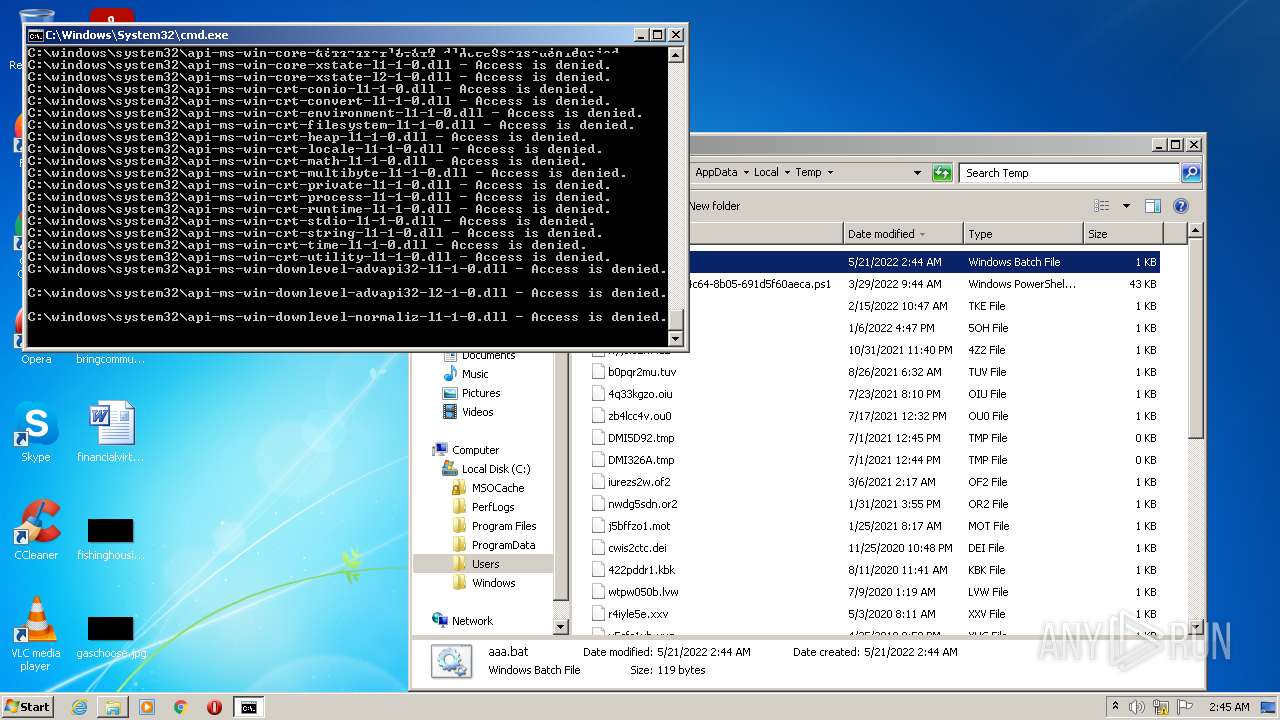
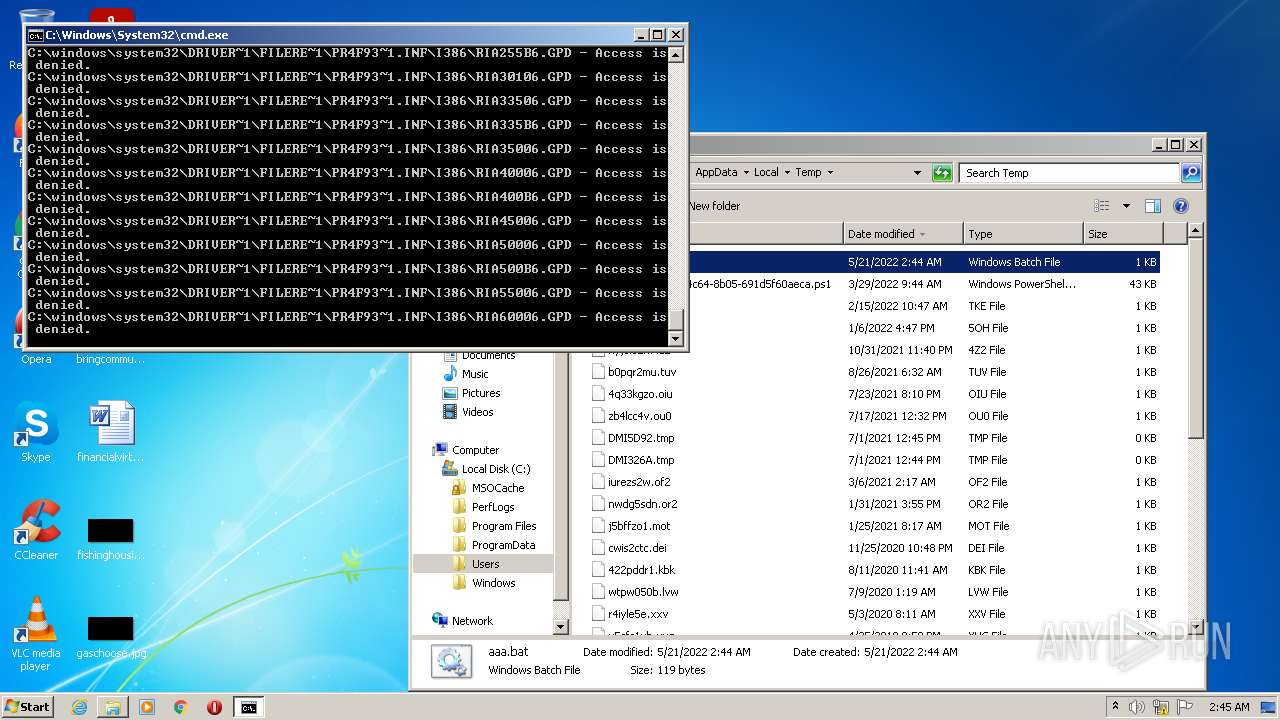
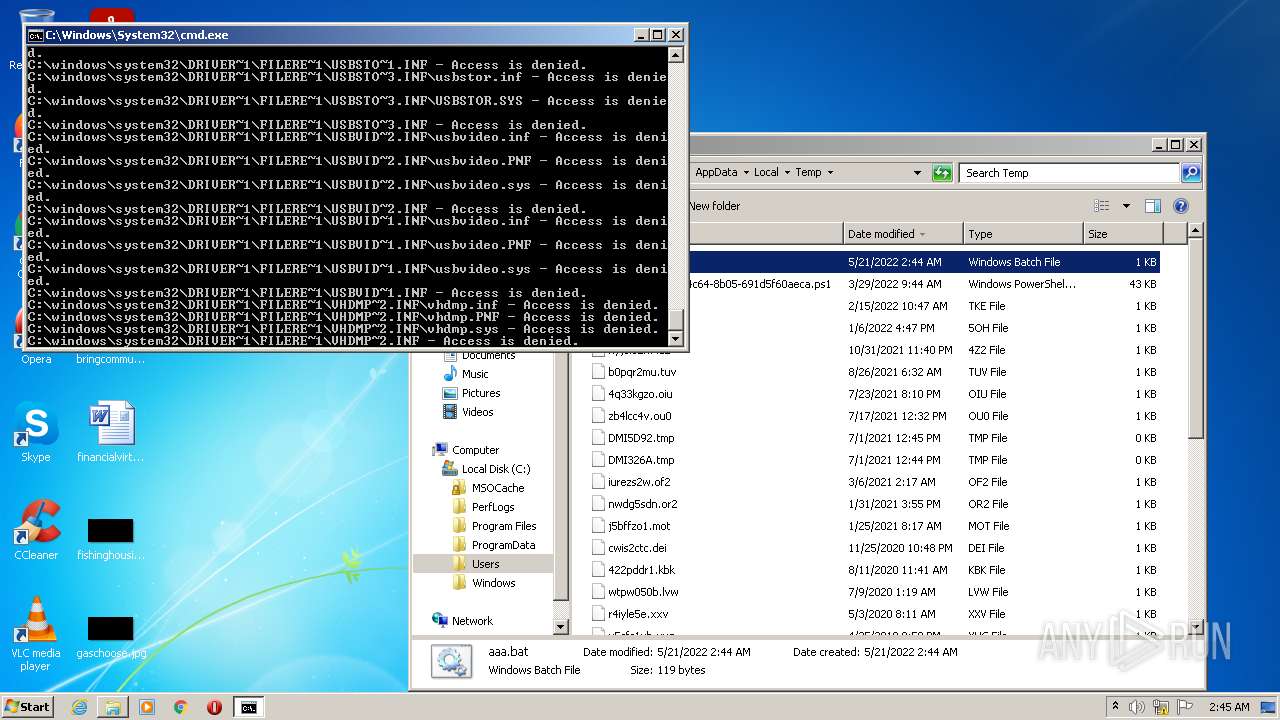
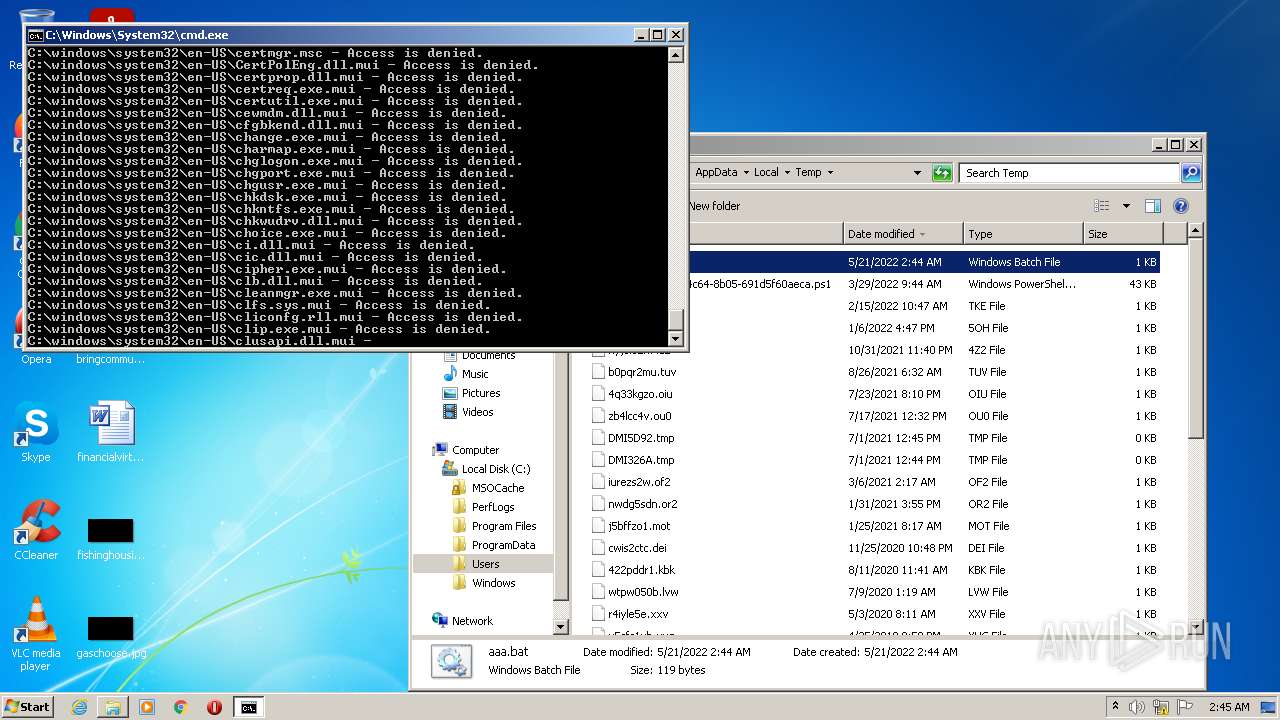
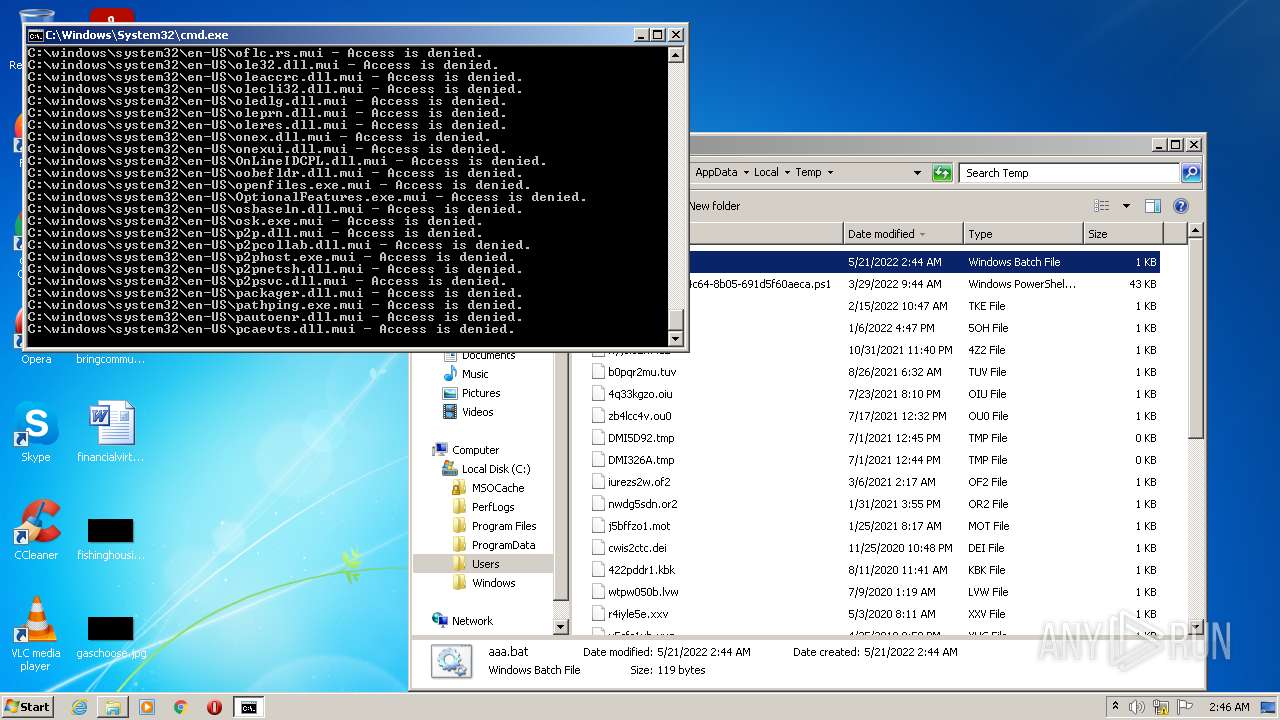
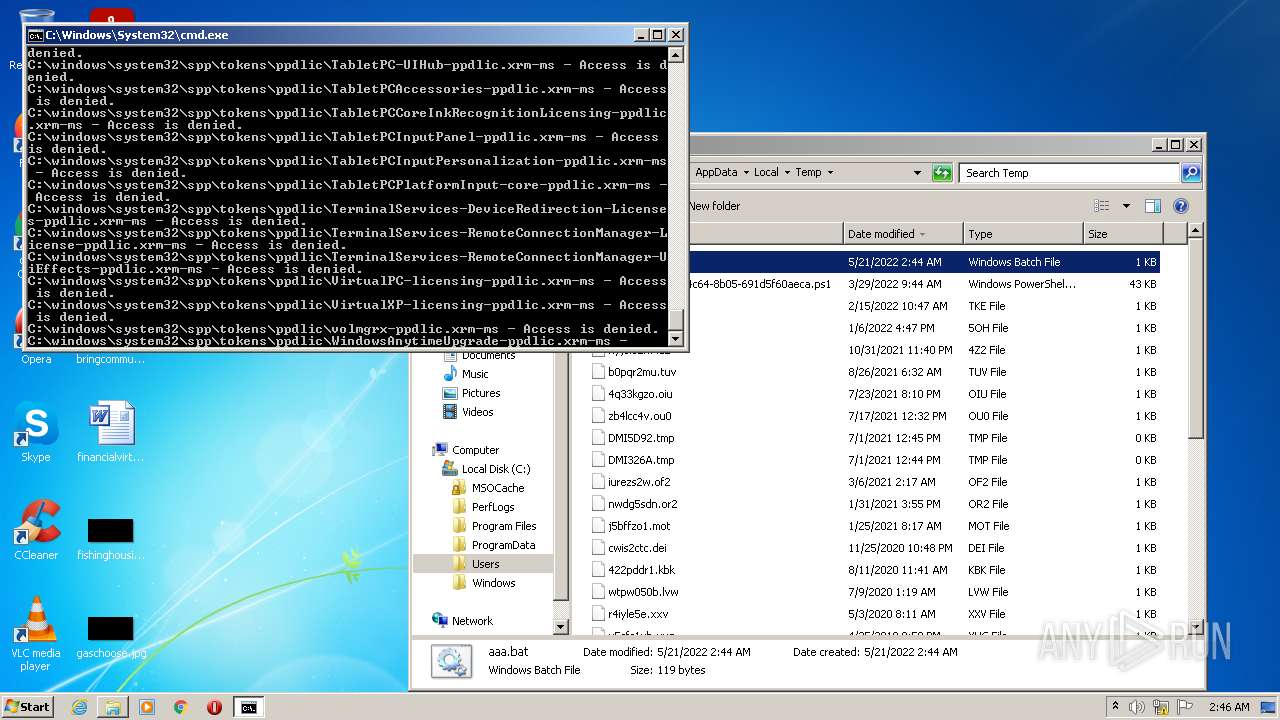
Tries to delete the host file
- cmd.exe (PID: 2328)
SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 3704)
- cmd.exe (PID: 2328)
- cmd.exe (PID: 3080)
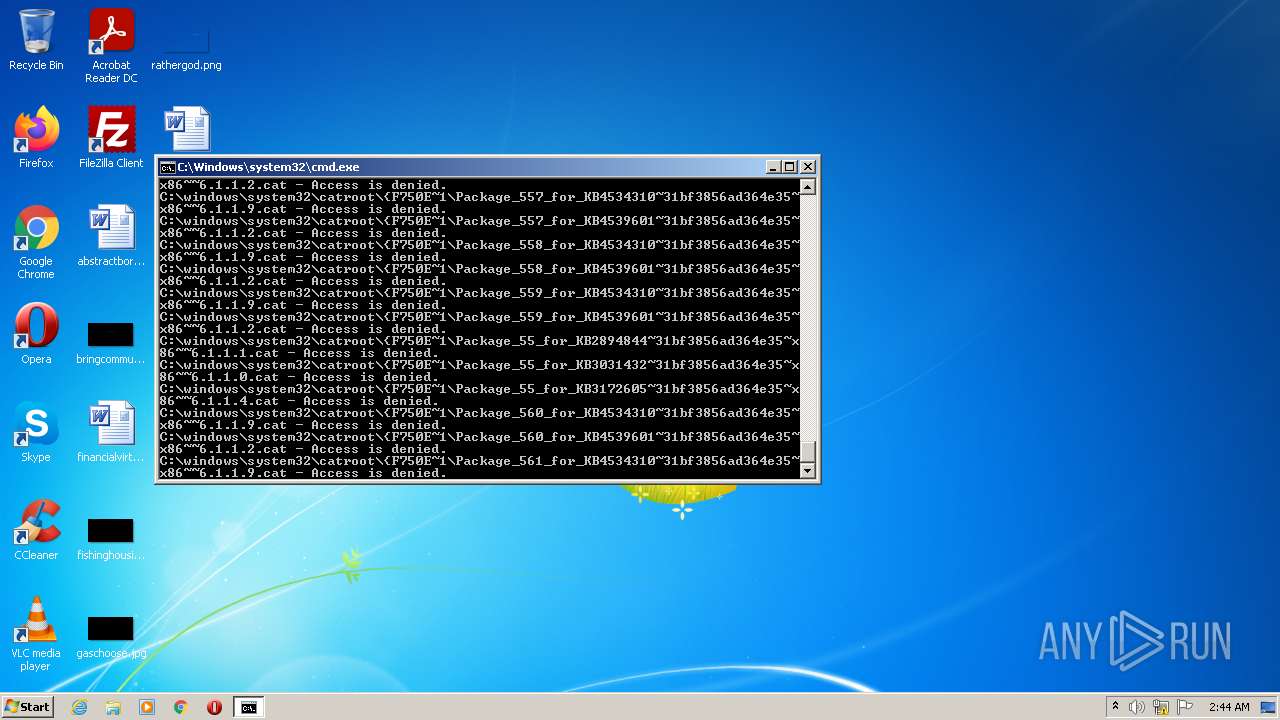
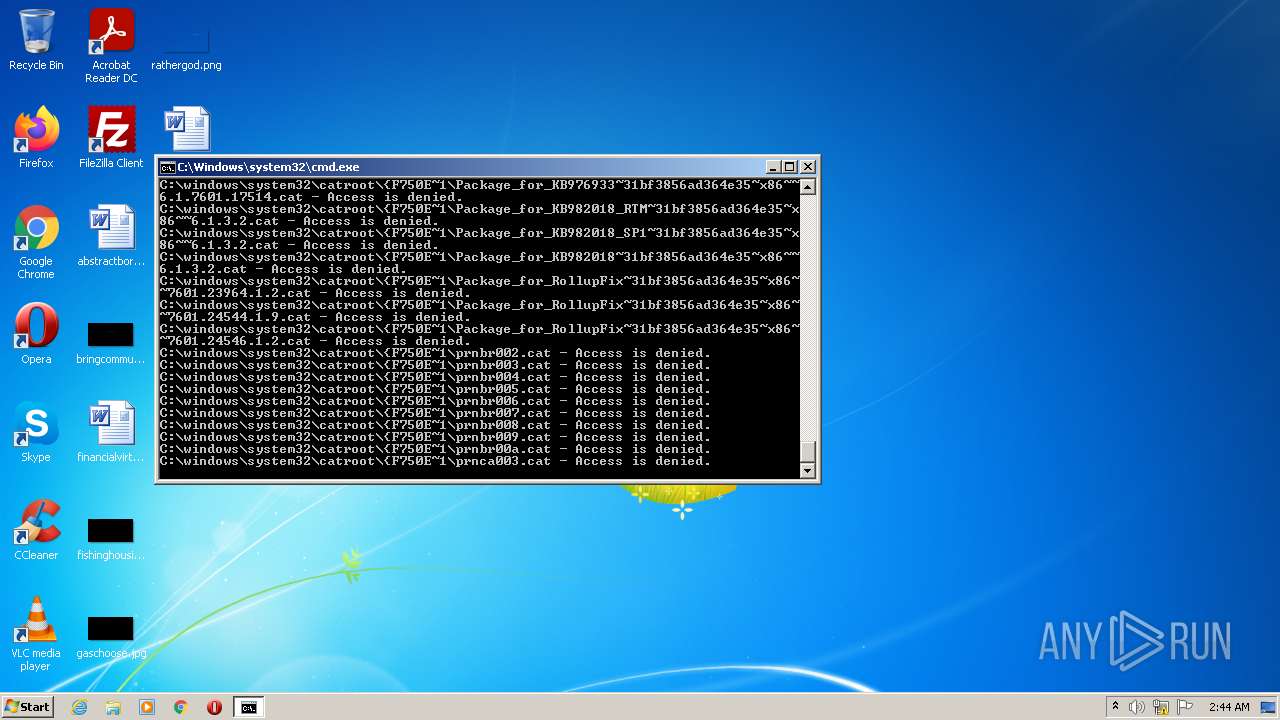
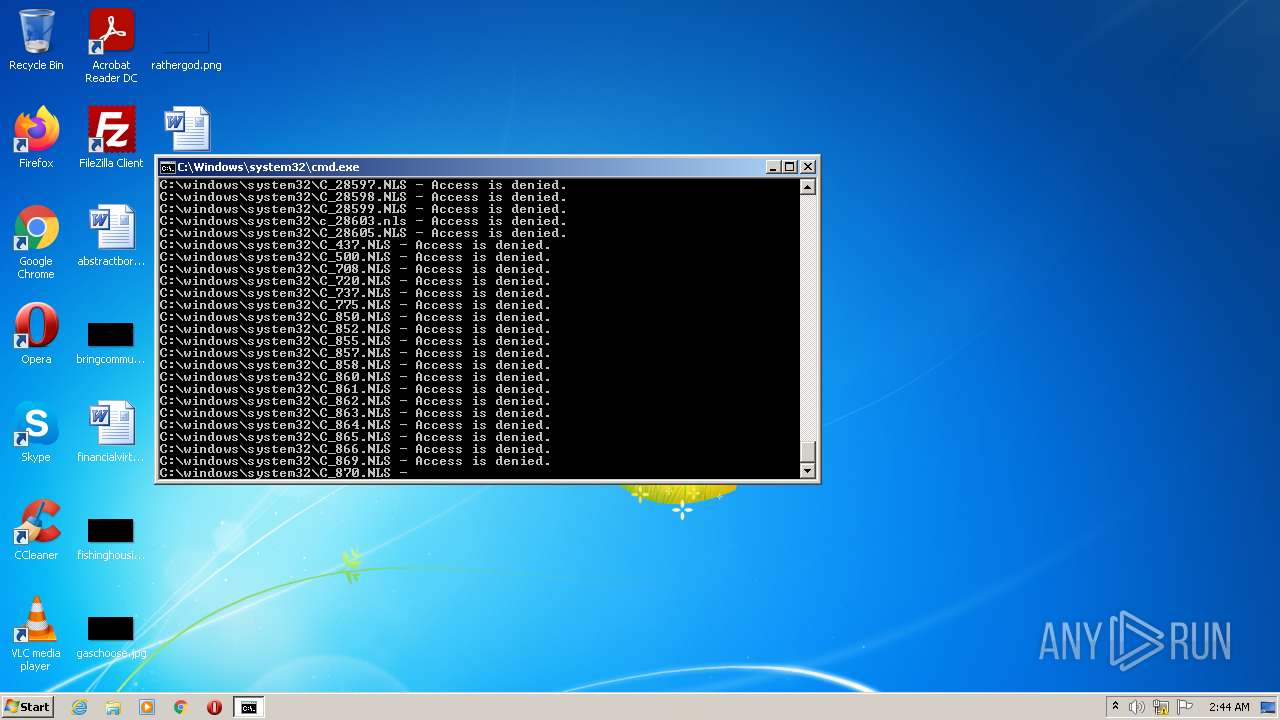
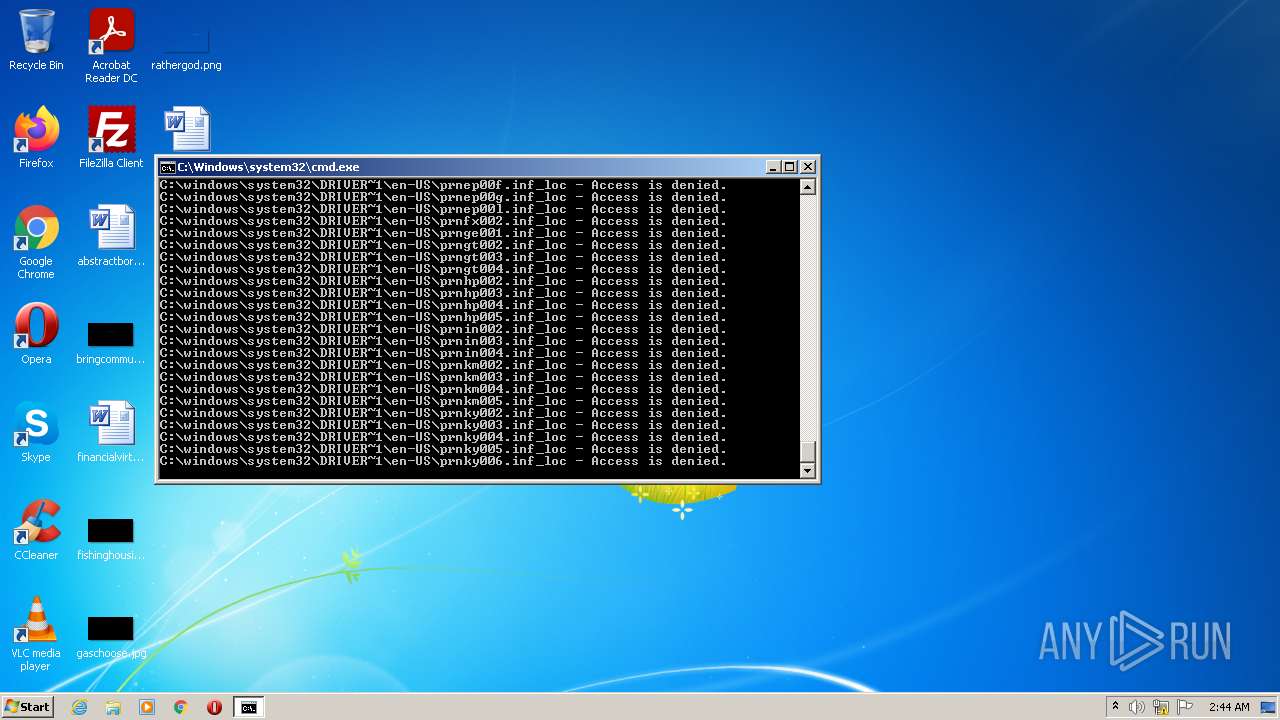
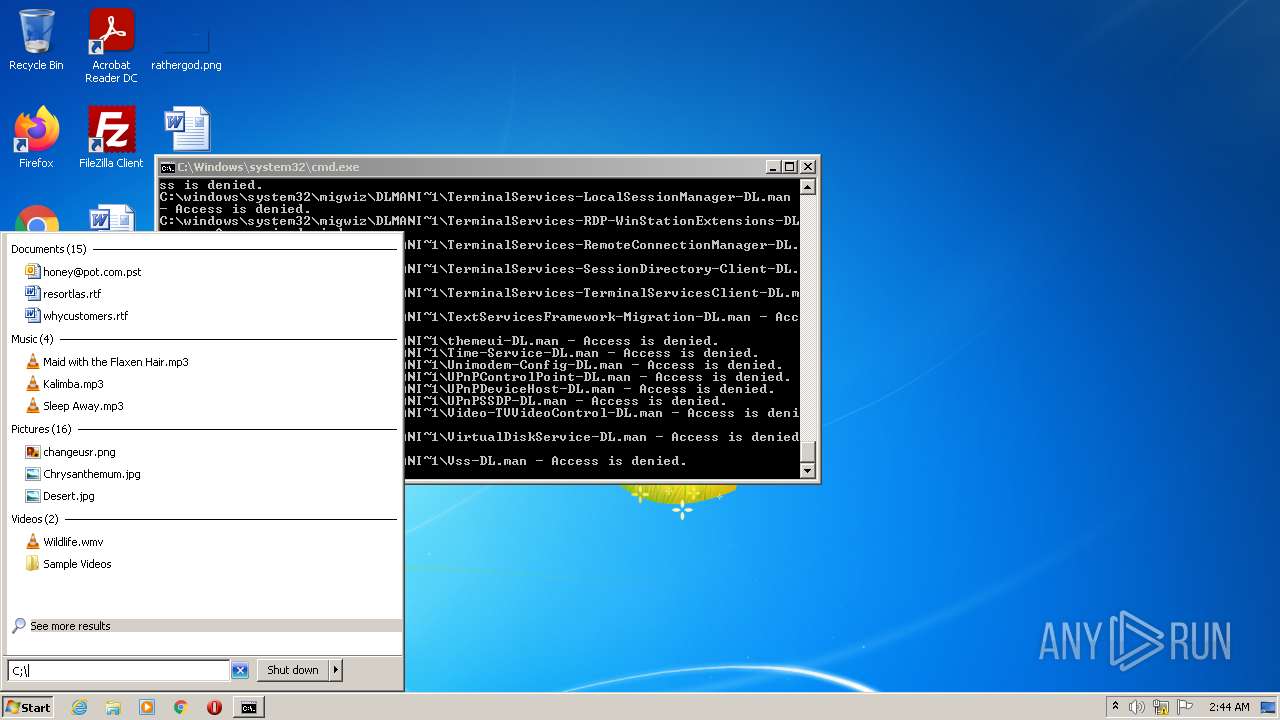
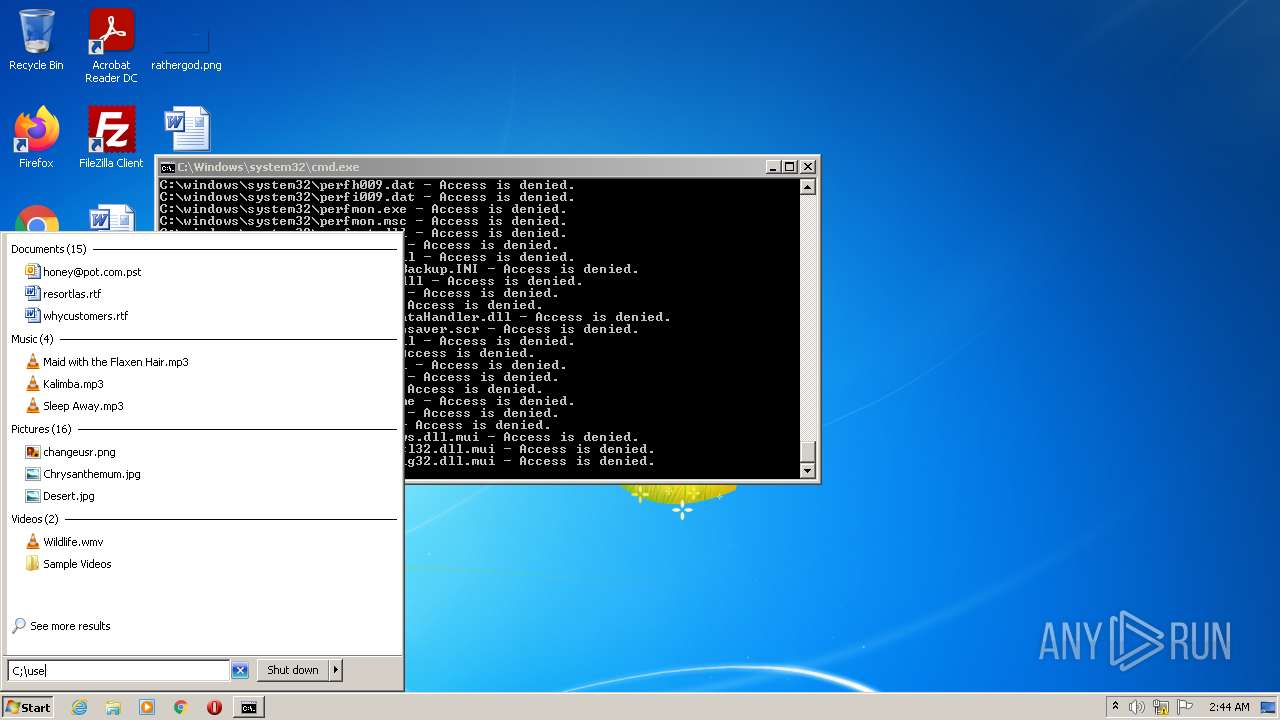
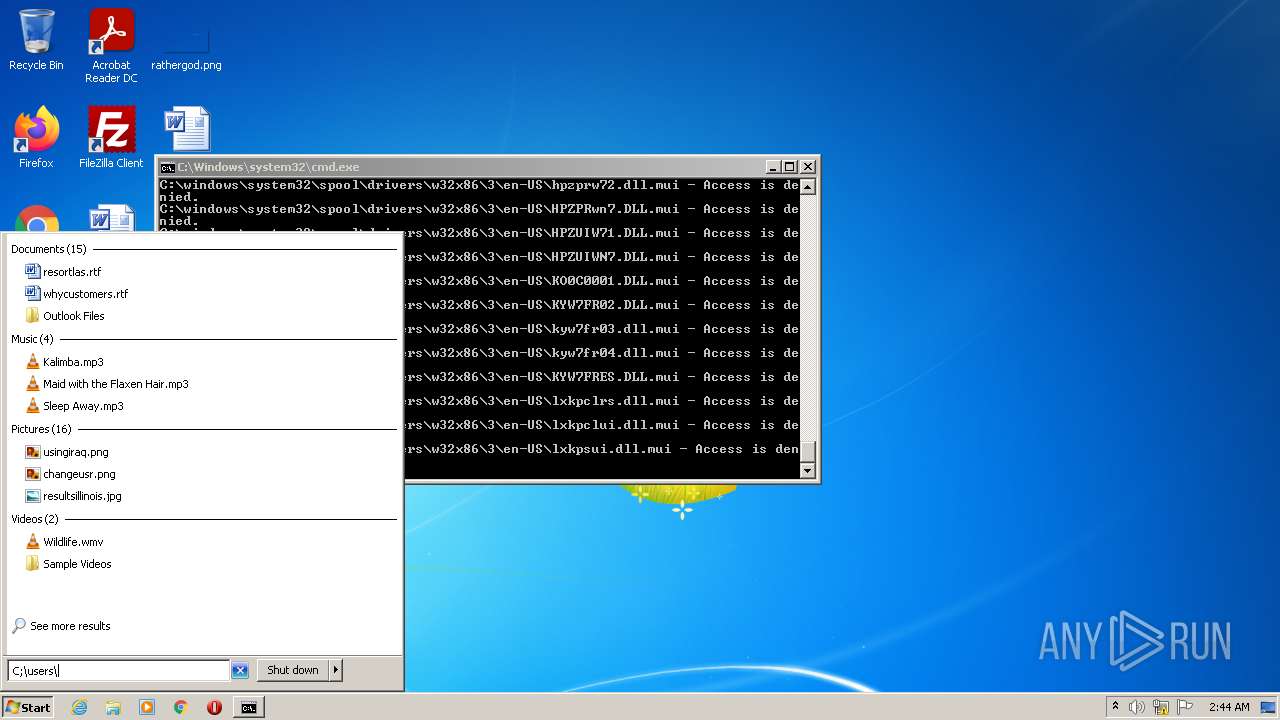
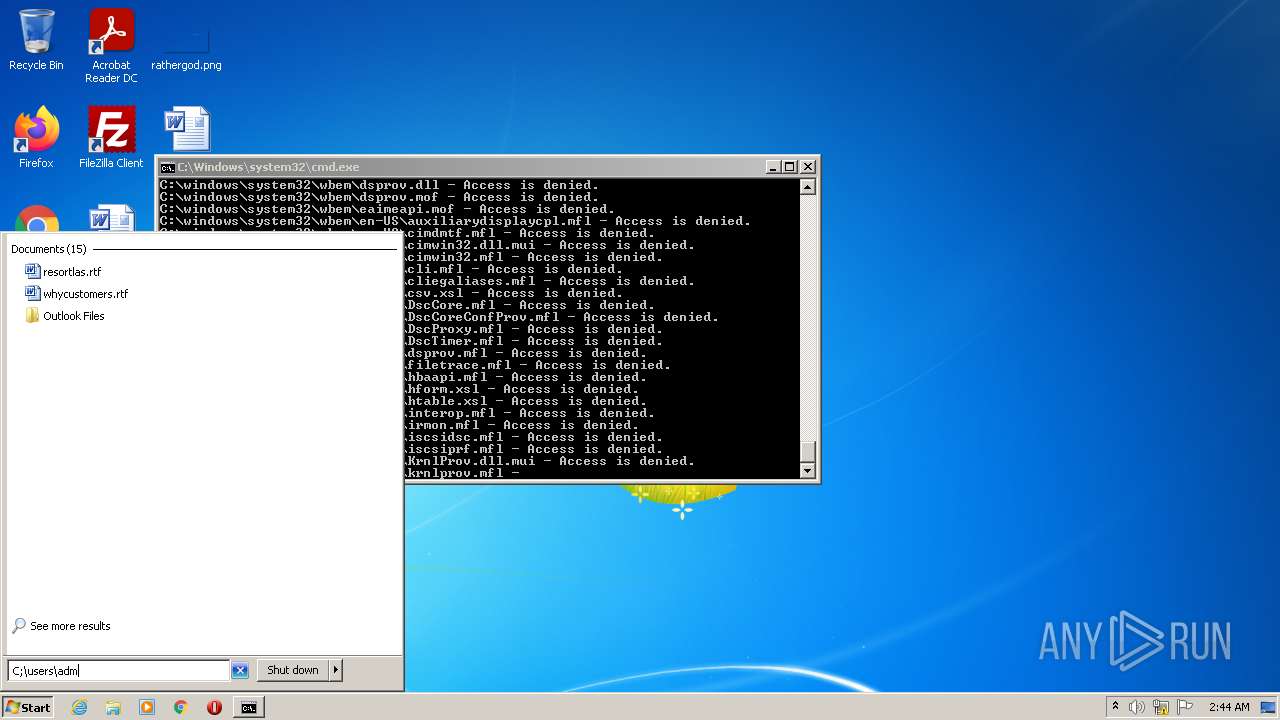
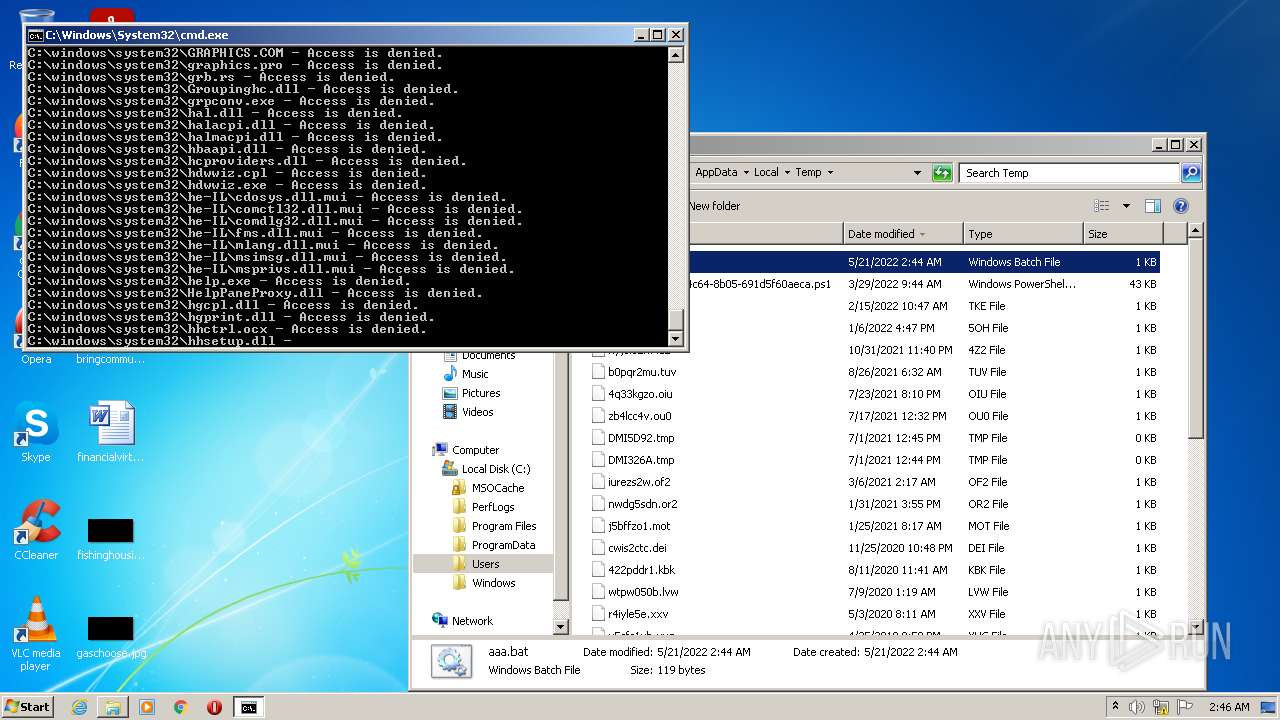
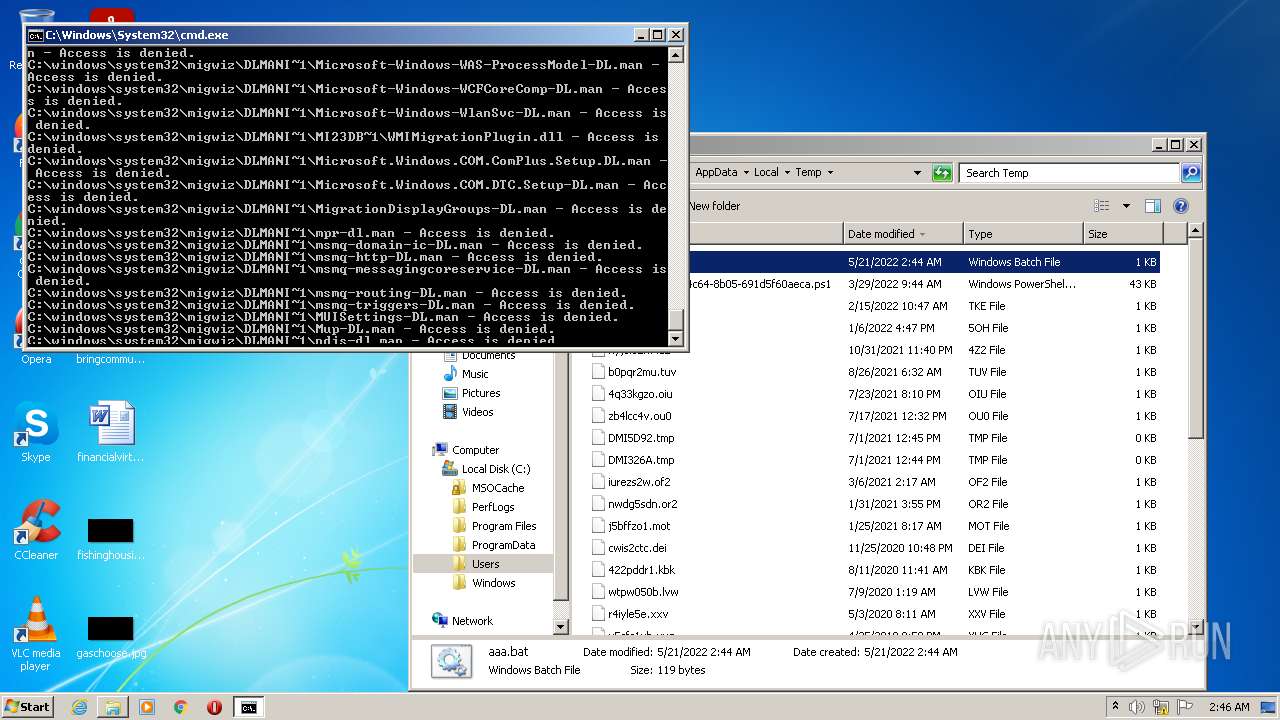
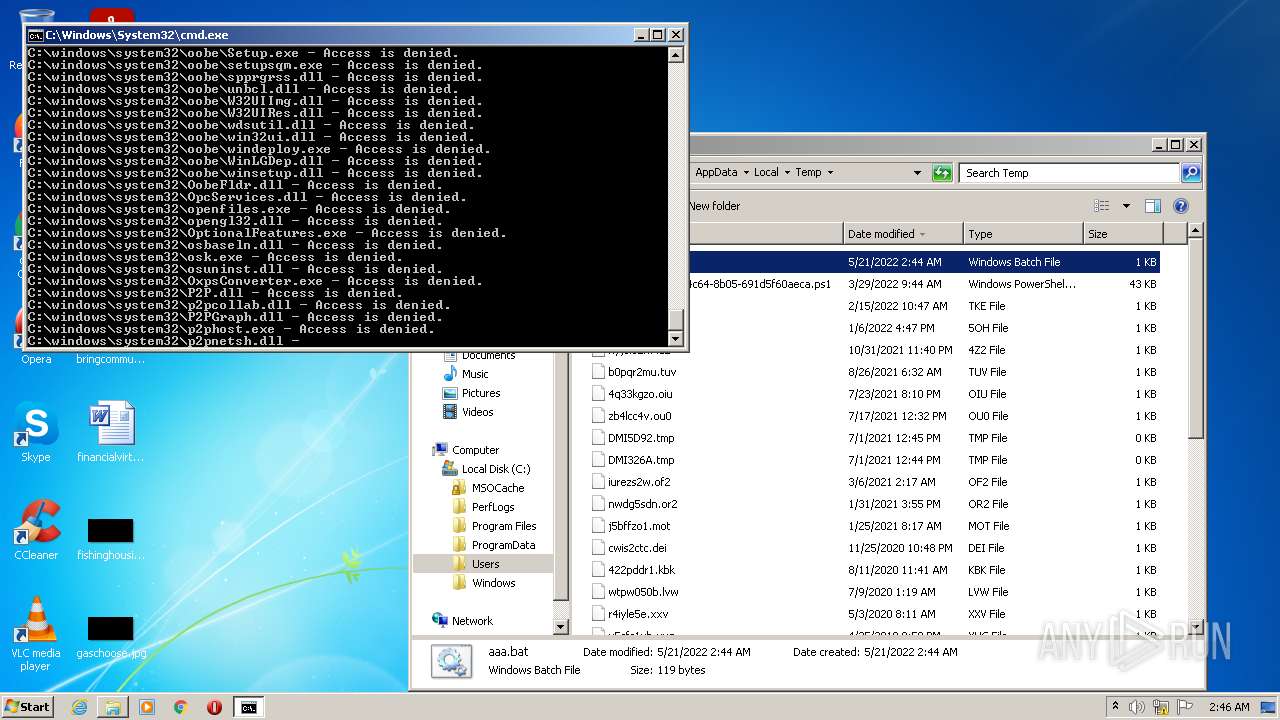
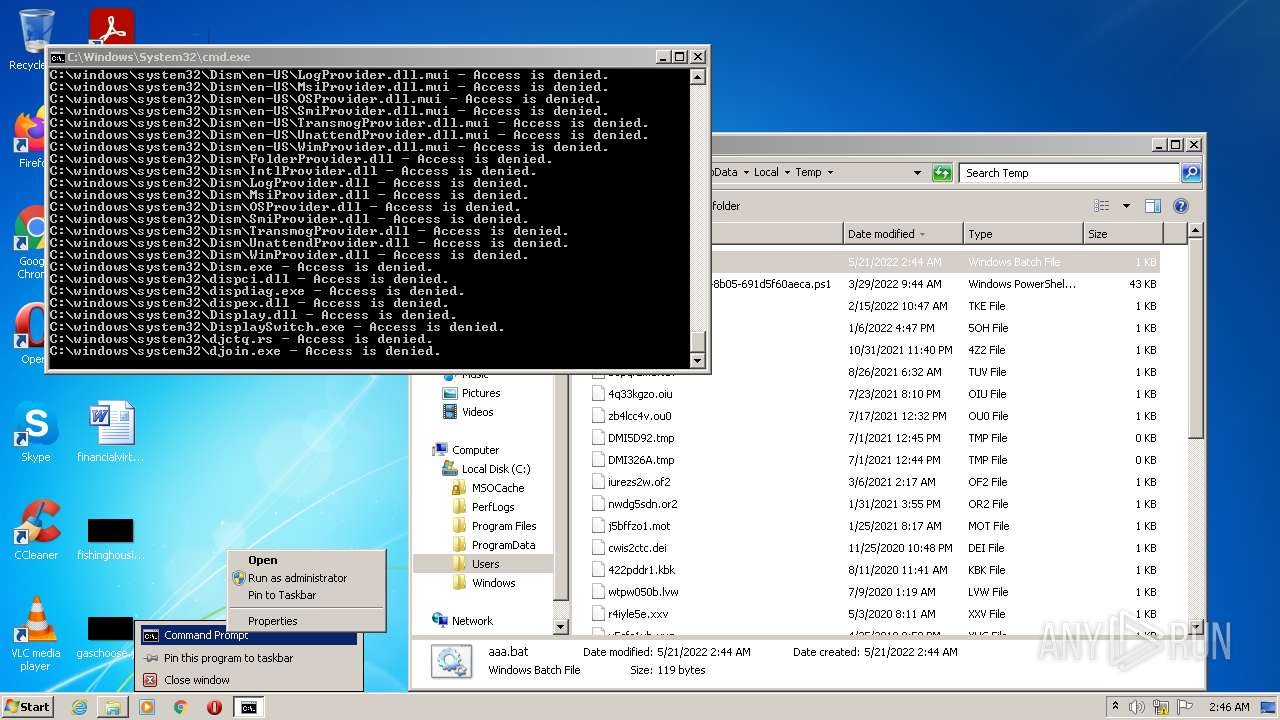
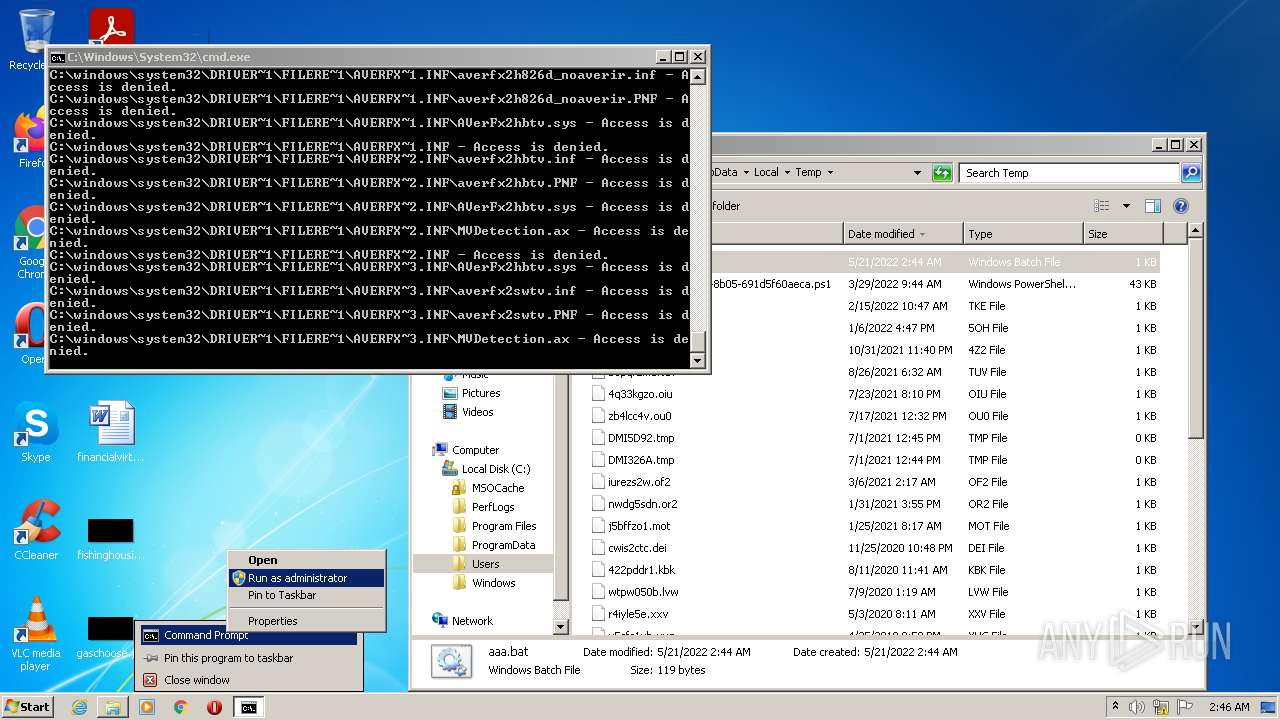
Removes files from Windows directory
- cmd.exe (PID: 3704)
- cmd.exe (PID: 2328)
INFO
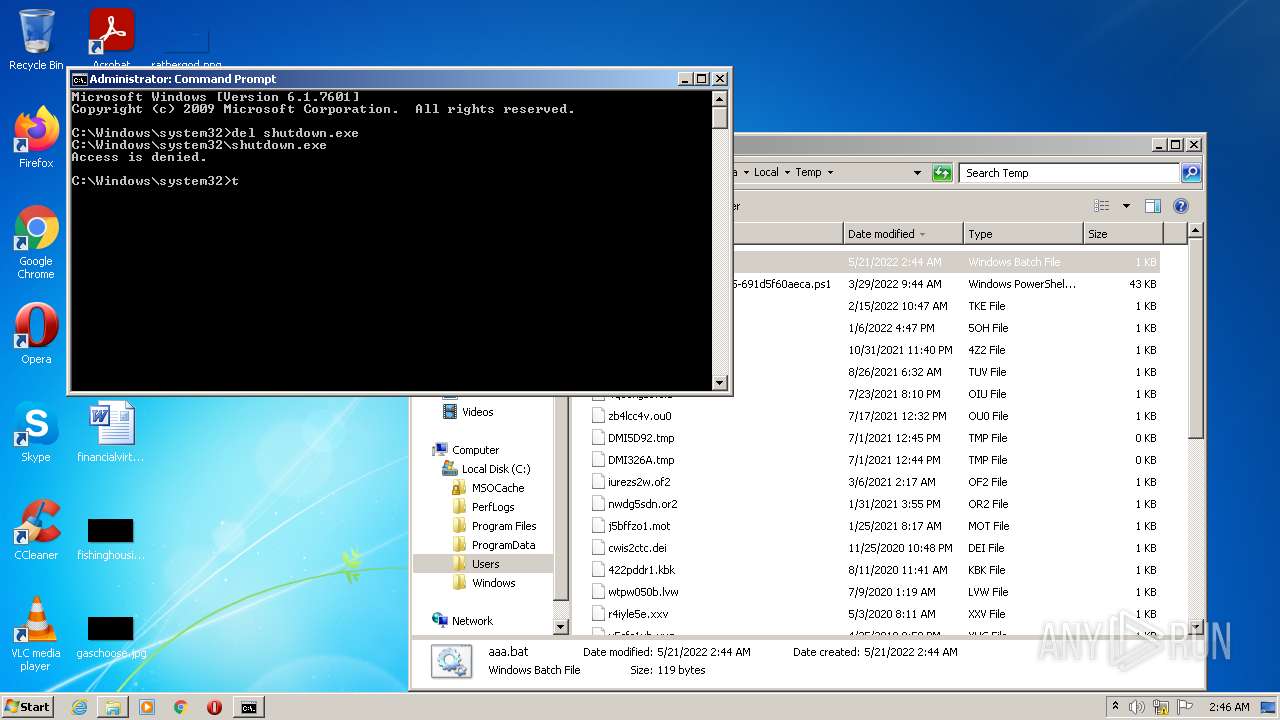
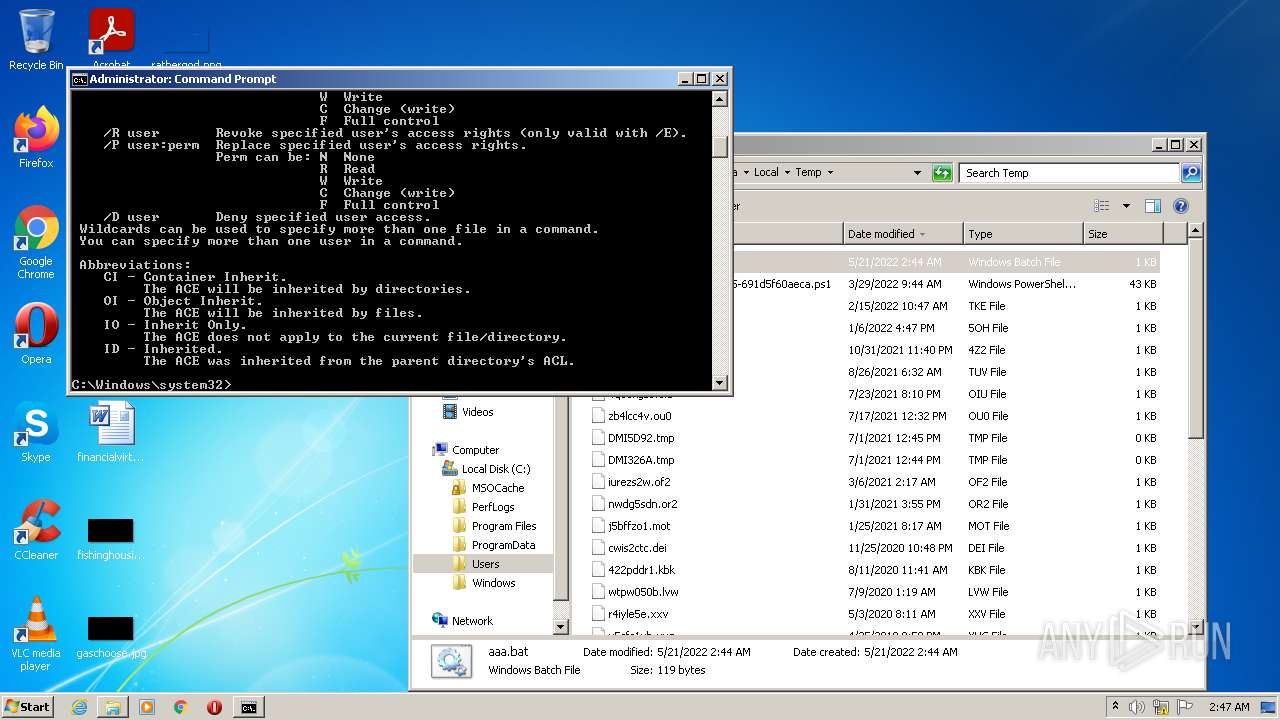
Checks supported languages
- takeown.exe (PID: 1184)
- cacls.exe (PID: 3304)
- takeown.exe (PID: 1884)
- cacls.exe (PID: 2924)
- takeown.exe (PID: 3236)
Reads the computer name
- takeown.exe (PID: 1184)
- cacls.exe (PID: 3304)
- takeown.exe (PID: 1884)
- cacls.exe (PID: 2924)
- takeown.exe (PID: 3236)
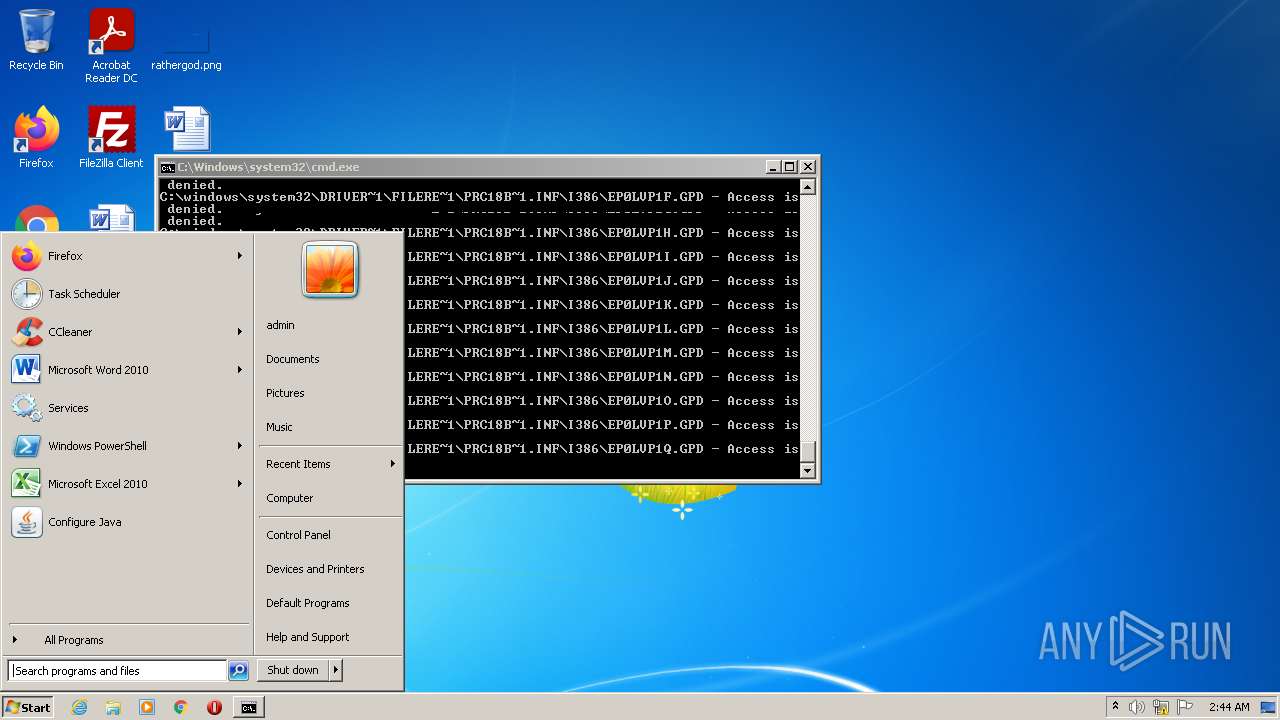
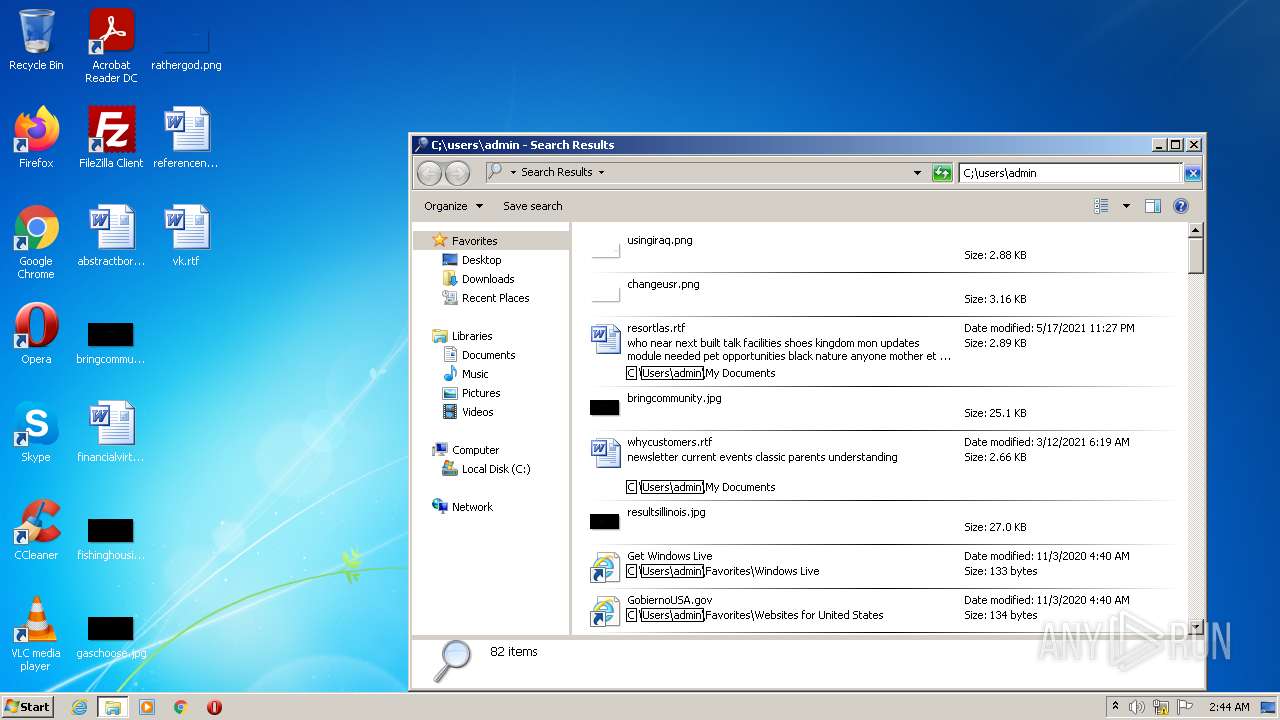
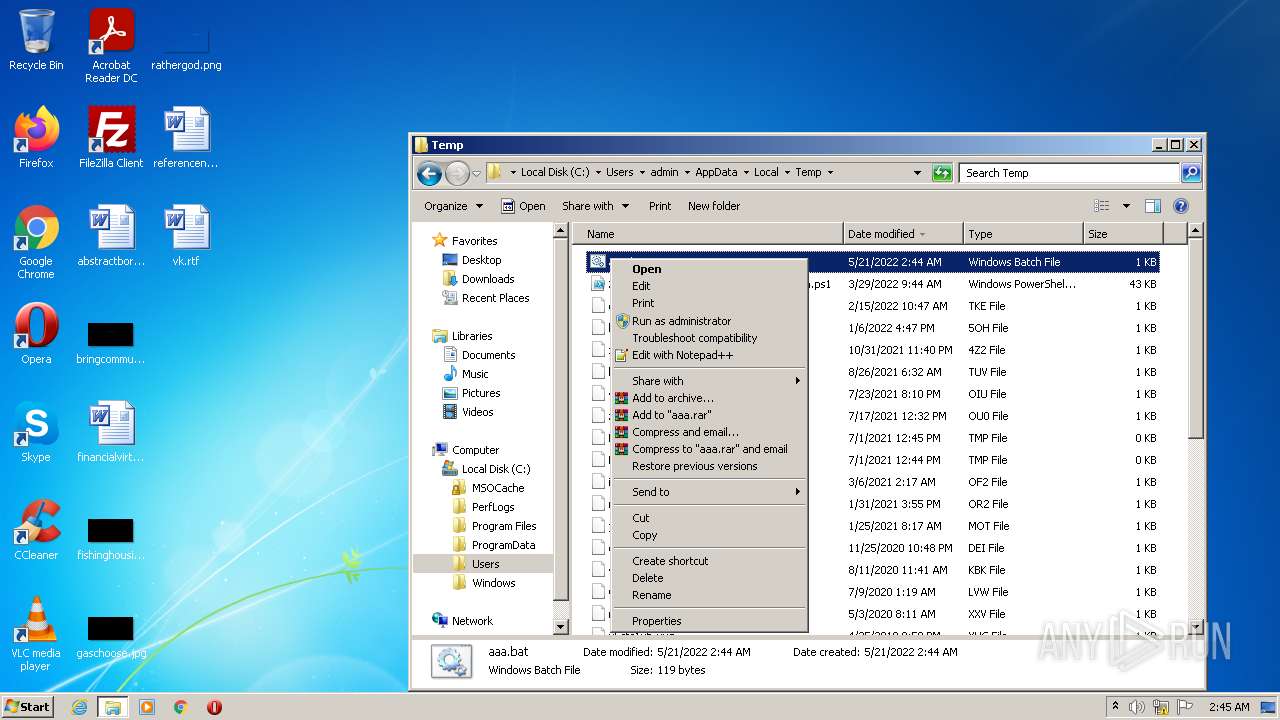
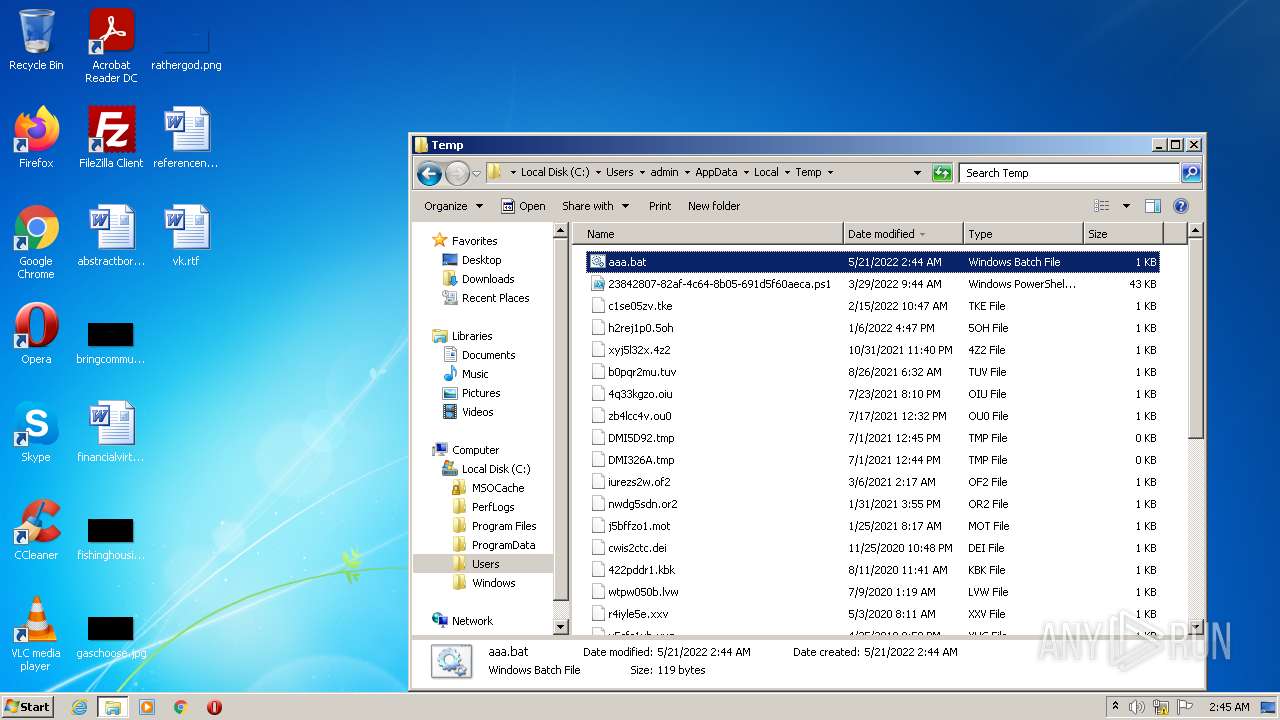
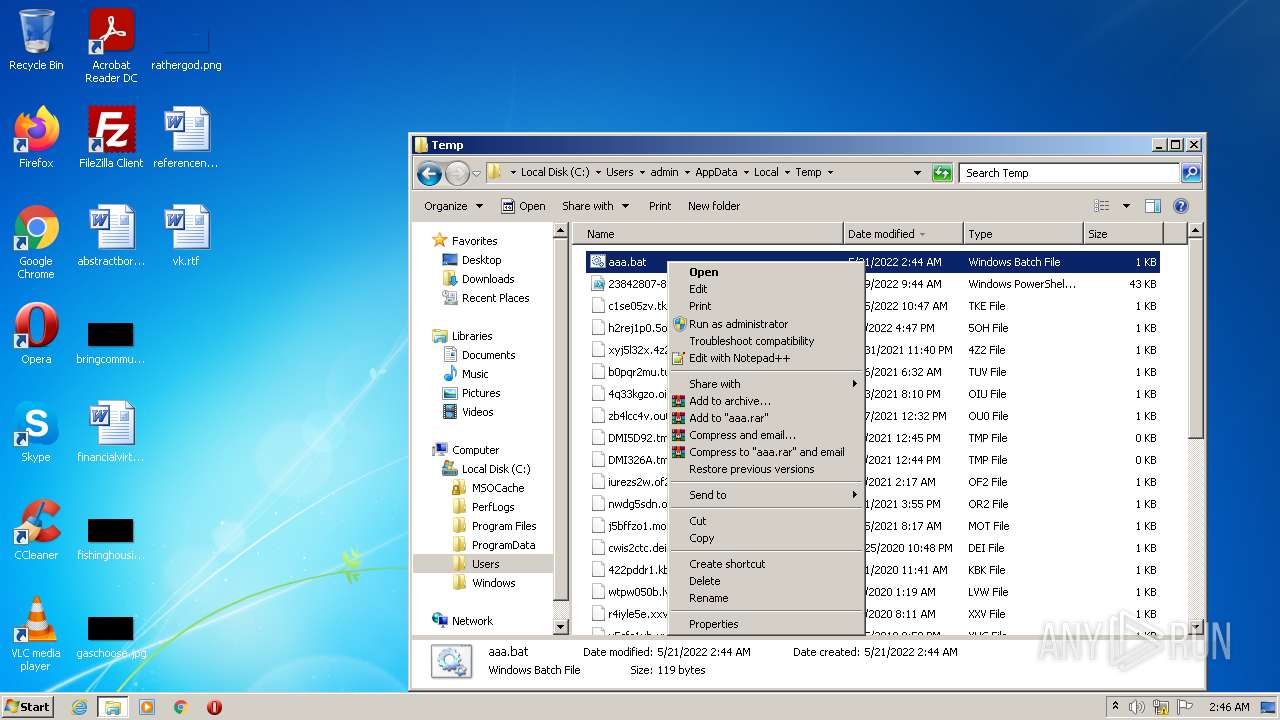
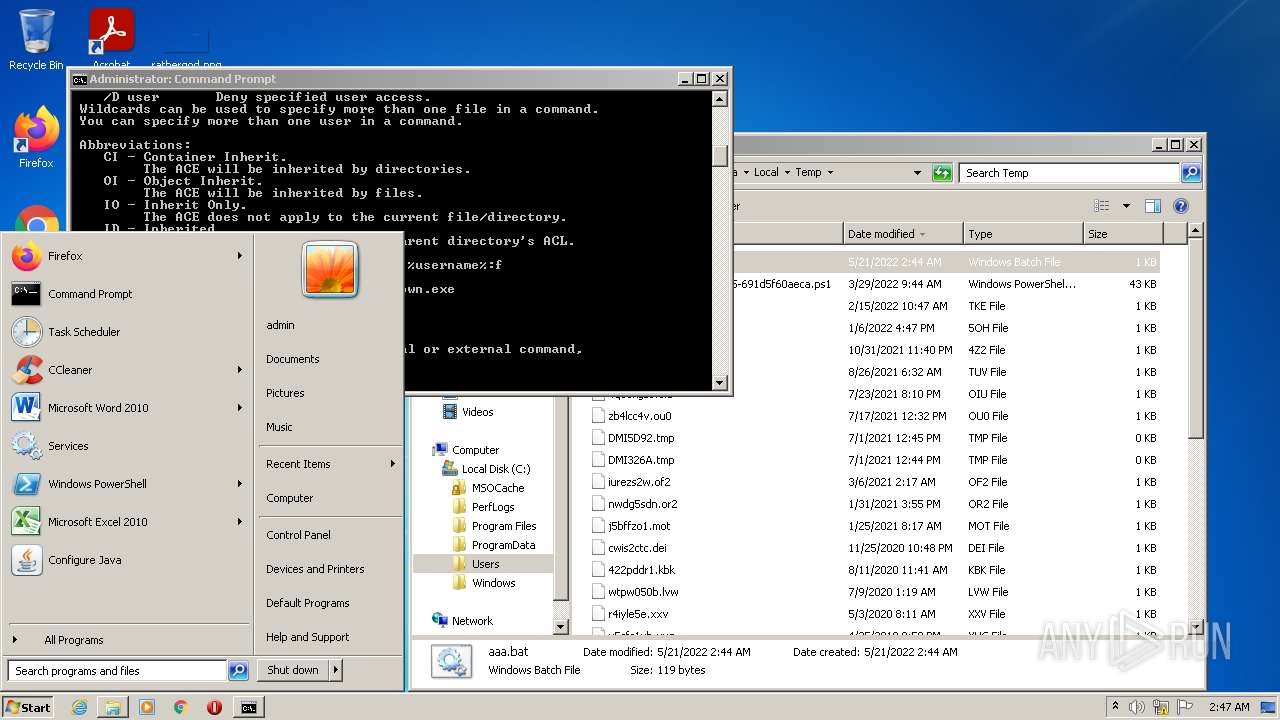
Manual execution by user
- cmd.exe (PID: 2328)
- cmd.exe (PID: 3080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
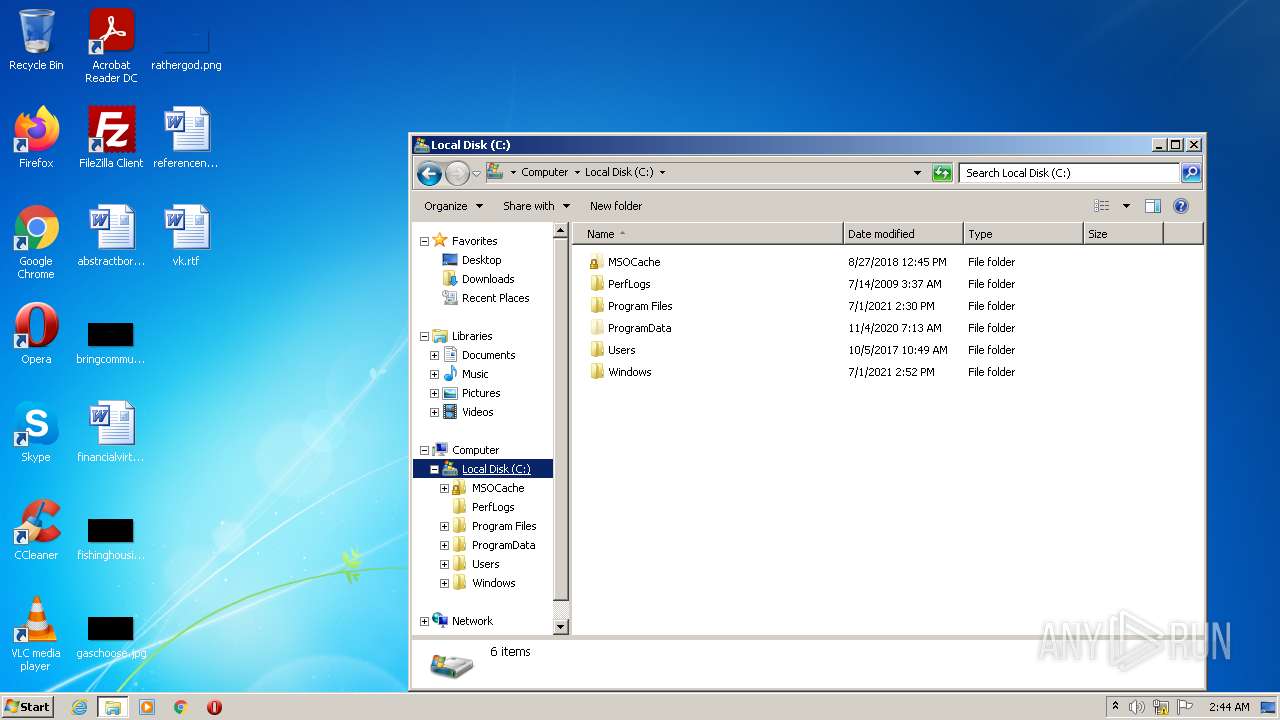
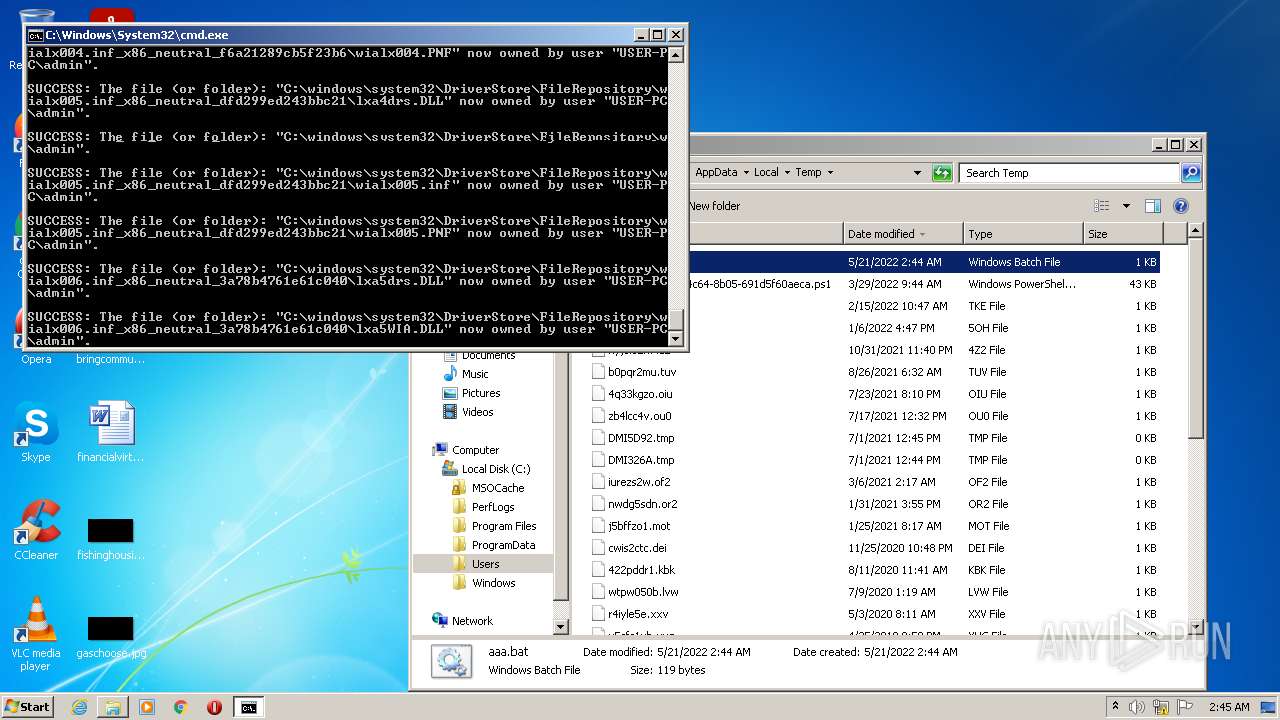
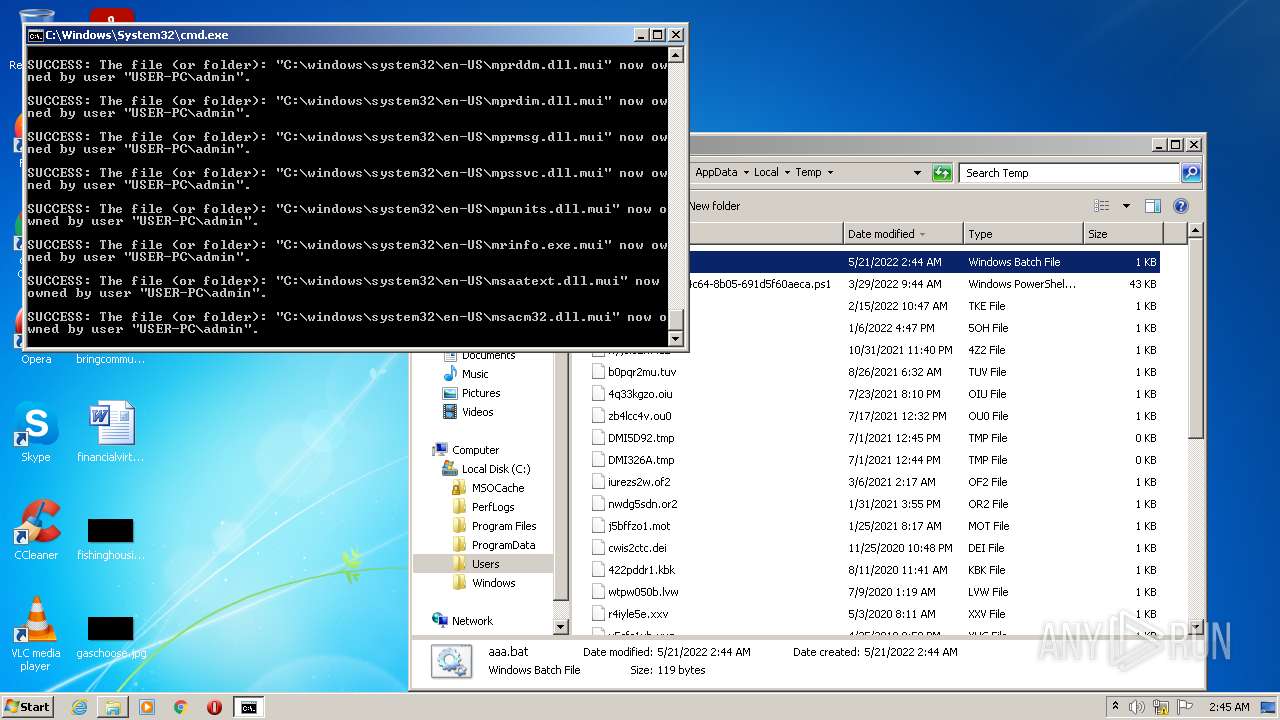
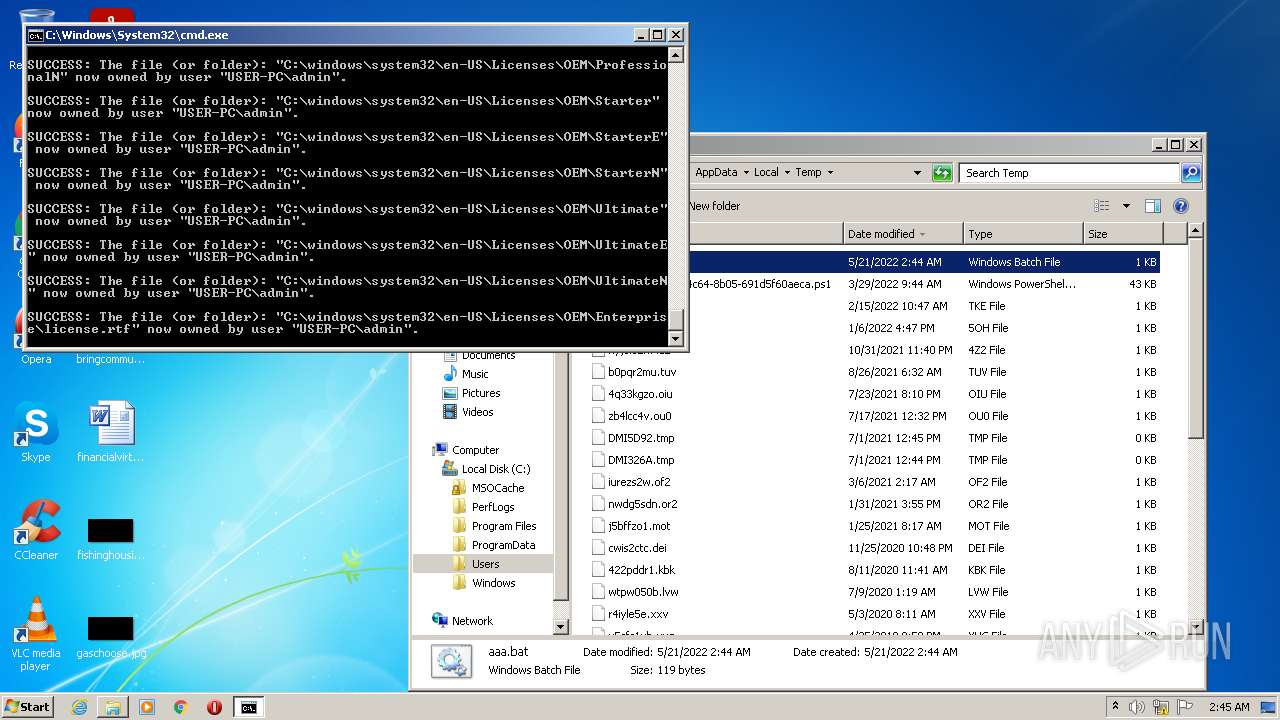
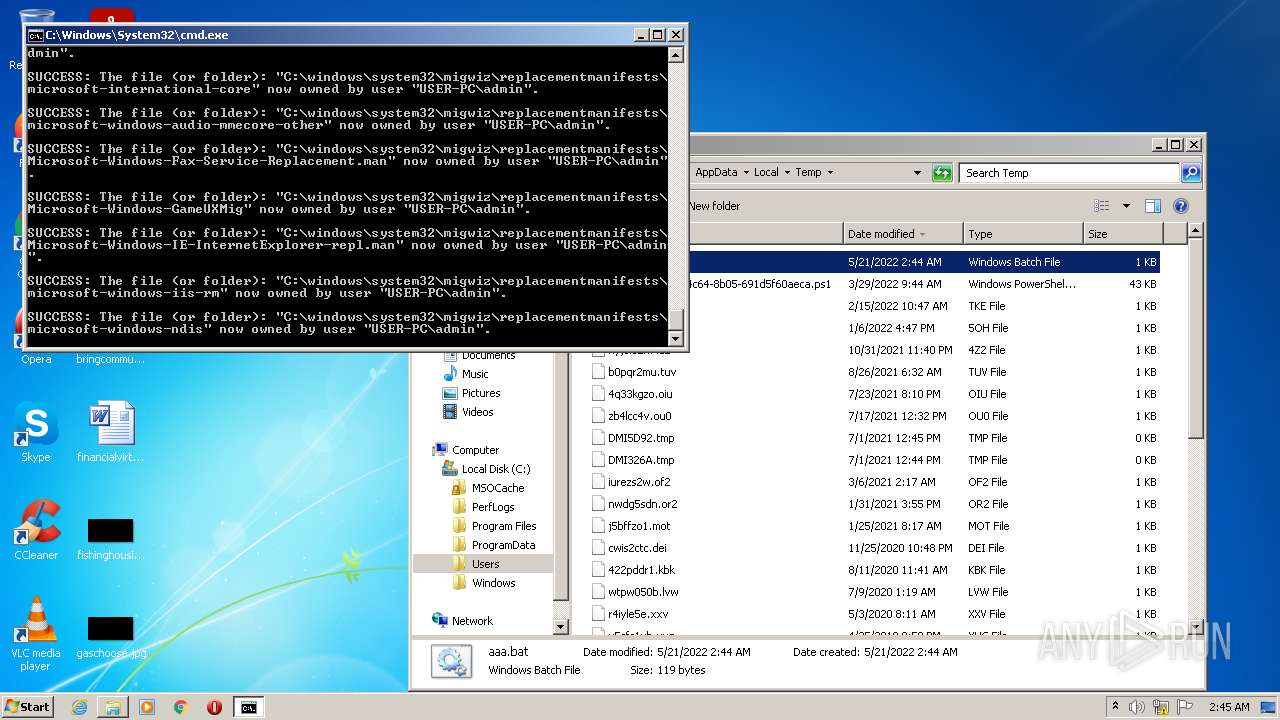
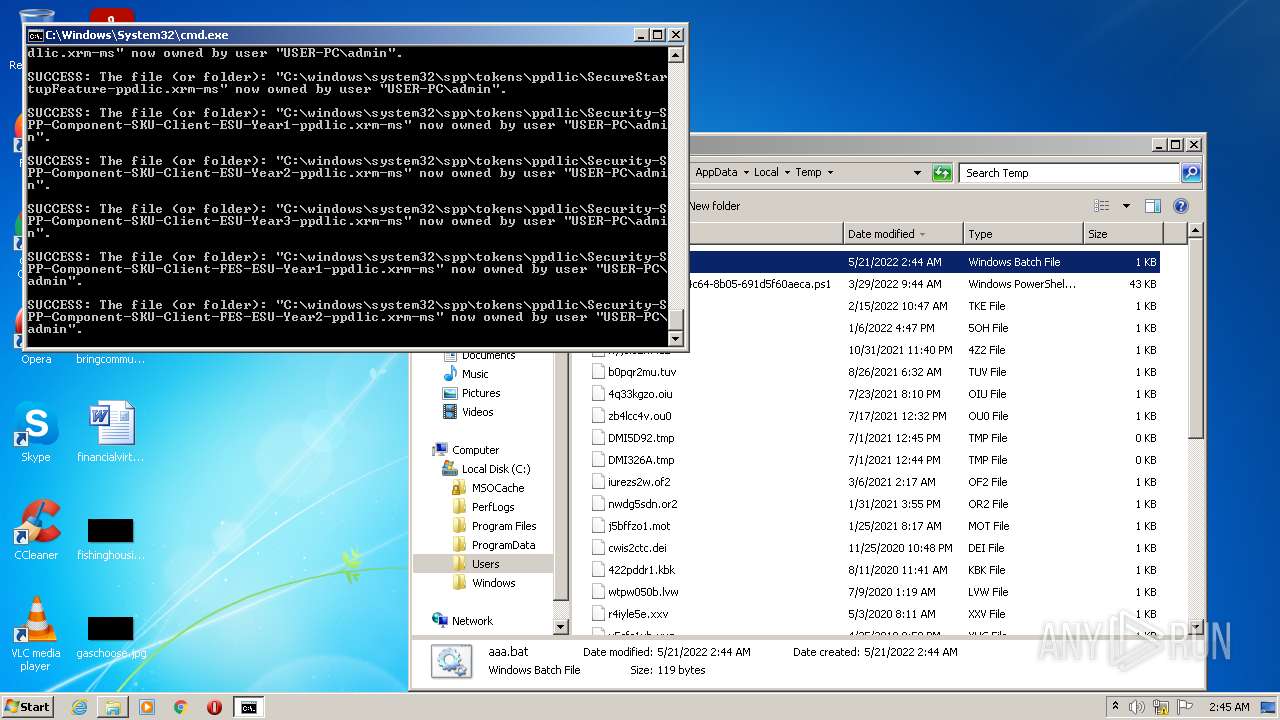
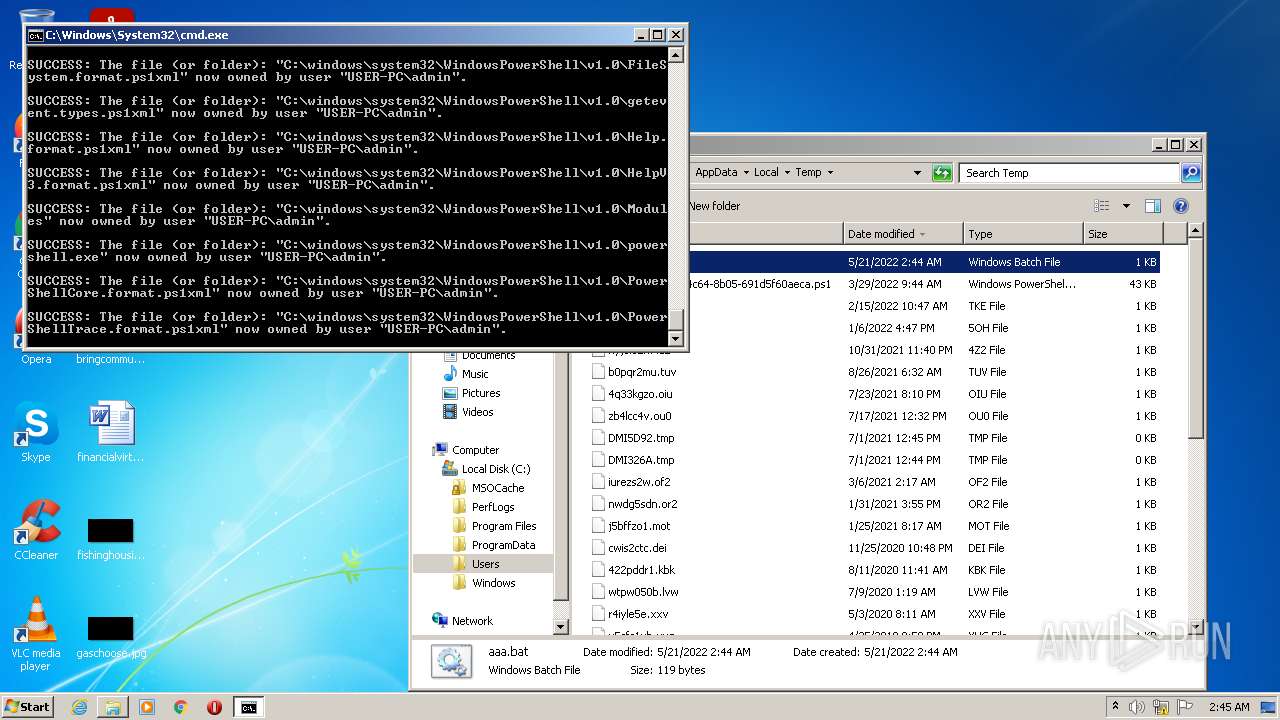
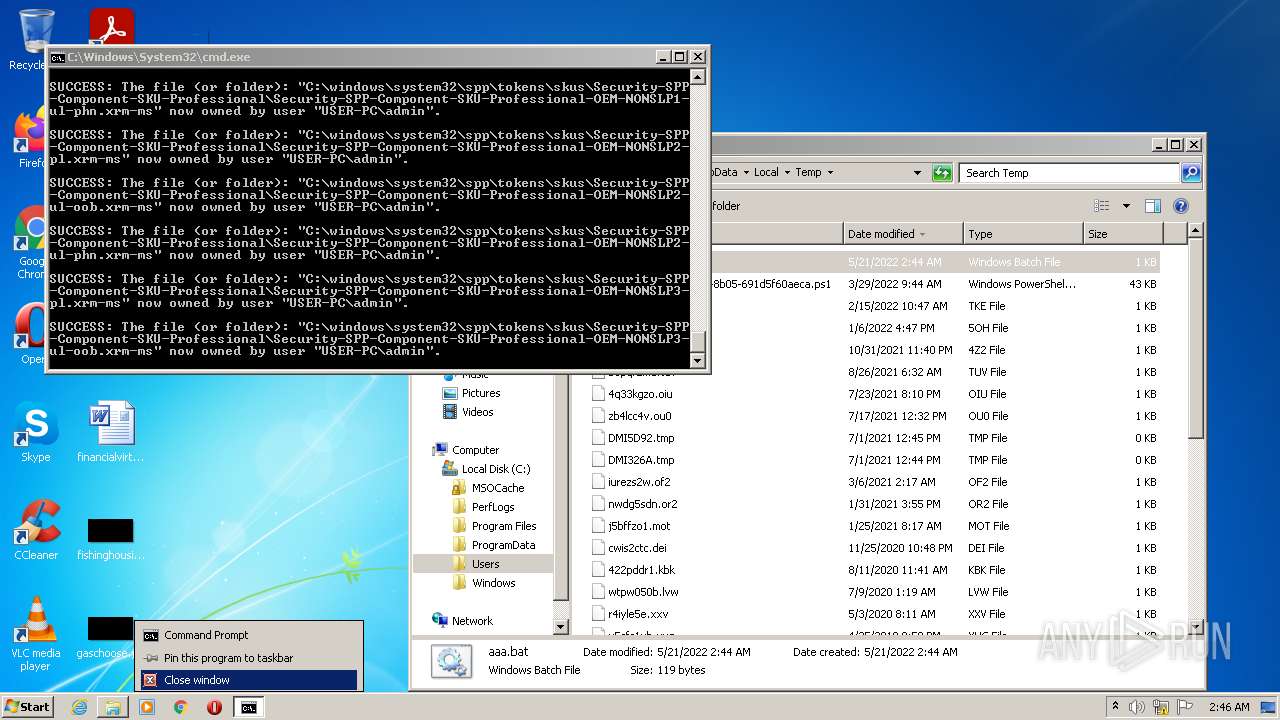
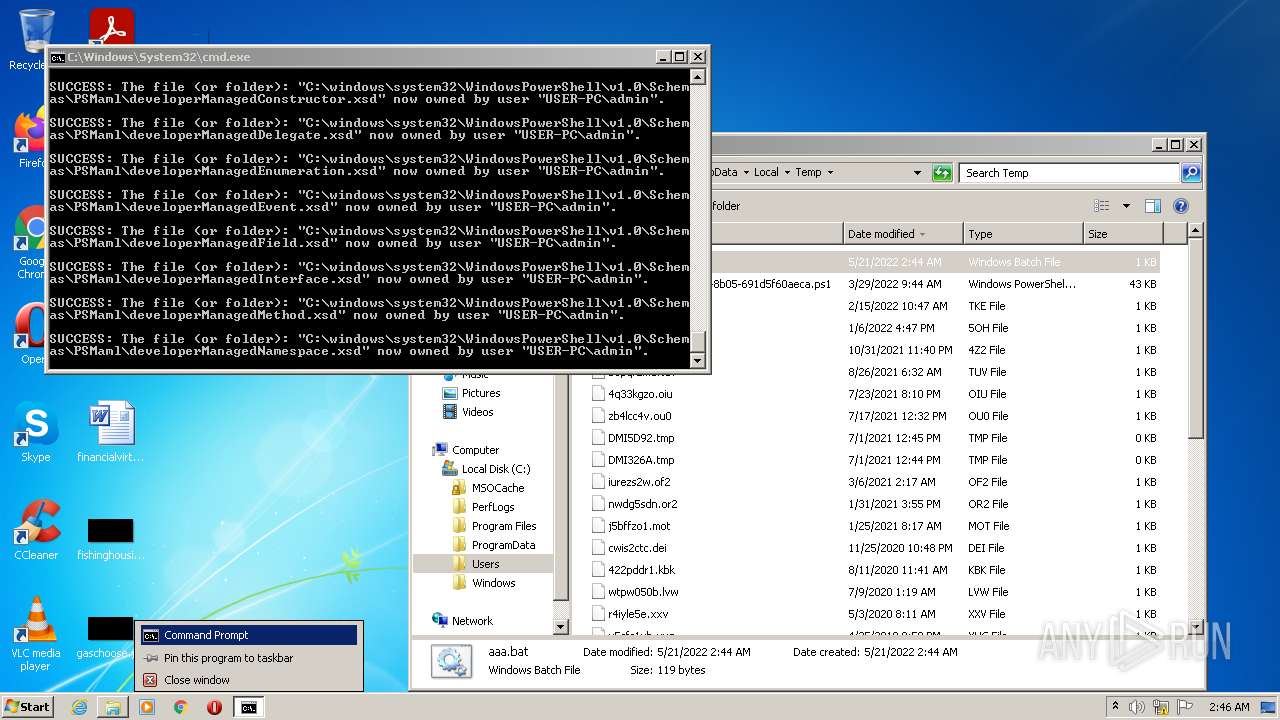
| 1184 | takeown /f C:\windows\system32\ /r | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Takes ownership of a file Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1884 | takeown /f C:\windows\system32\ /r | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
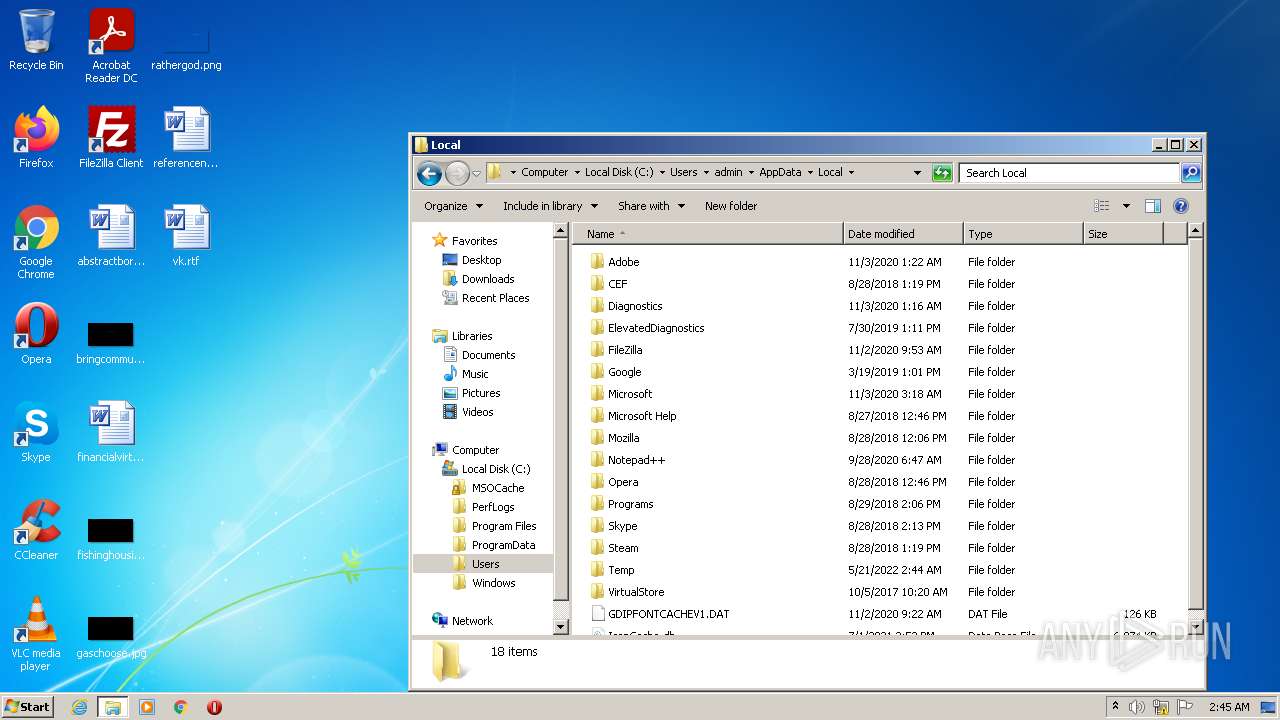
| 2328 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\aaa.bat" | C:\Windows\System32\cmd.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 32 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2924 | cacls C:\windows\system32\ /g "admin":f /t /e /c | C:\Windows\system32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3080 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\aaa.bat" | C:\Windows\System32\cmd.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3236 | takeown /f C:\windows\system32\ /r | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3304 | cacls C:\windows\system32\ /g "admin":f /t /e /c | C:\Windows\system32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3704 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\aaa.bat" " | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
119
Read events
119
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report