| File name: | huyanbao588455.exe |
| Full analysis: | https://app.any.run/tasks/34cac0c1-98de-4a48-9636-c3c247d5e42b |
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2020, 06:34:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3E7DE17D67E8780A2F7ECDA10CD31F7E |
| SHA1: | 0D54F920AC02E2FADE9FFB5D517B7F3474D0DF0F |
| SHA256: | 1043172FA3E173DA7BD3F74C207202085C3DFF4E816150D9A244956D6B4D0EBA |
| SSDEEP: | 49152:JujQA0hDRTNlw7smlt/nox6k79fd8i7tDK4fSUV1goZcNlAF+VQVekH/1gj3Jlvs:JTbpZNl9CHkVVK4fjZbcVQ7/1s3Jlvs |
MALICIOUS
Loads dropped or rewritten executable
- huyanbao588455.exe (PID: 2788)
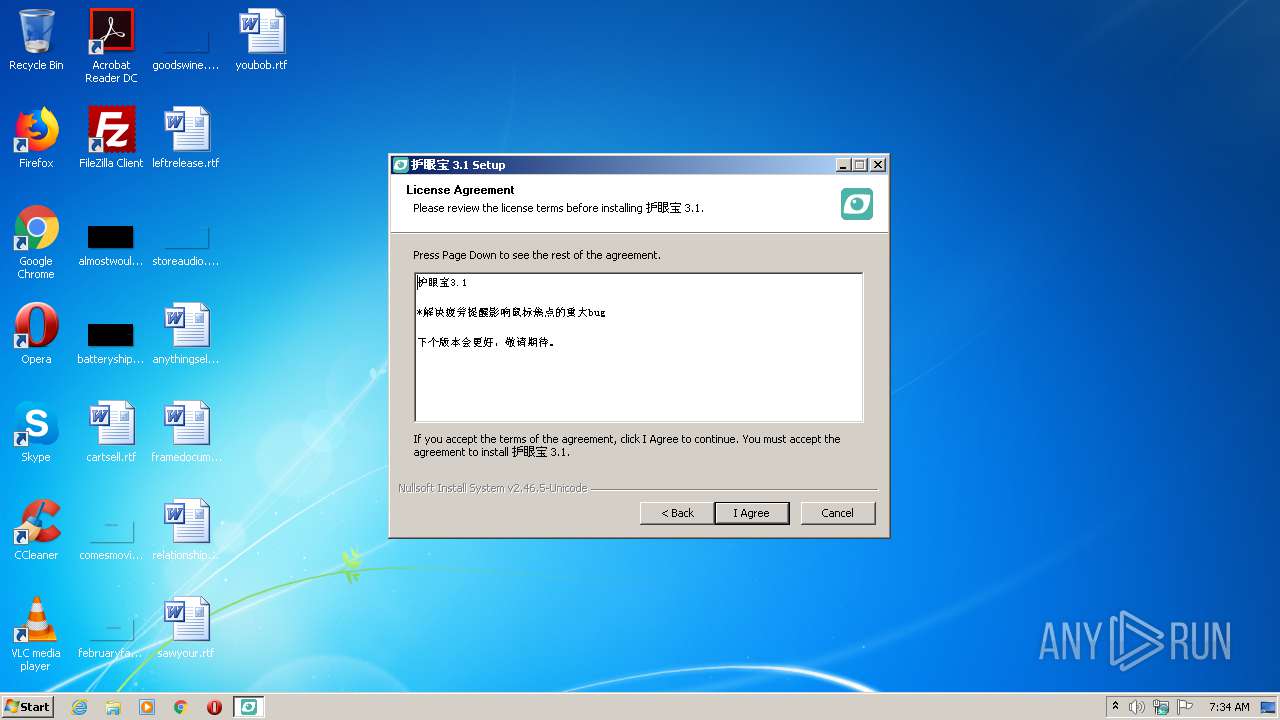
Changes the autorun value in the registry
- huyanbao588455.exe (PID: 2788)
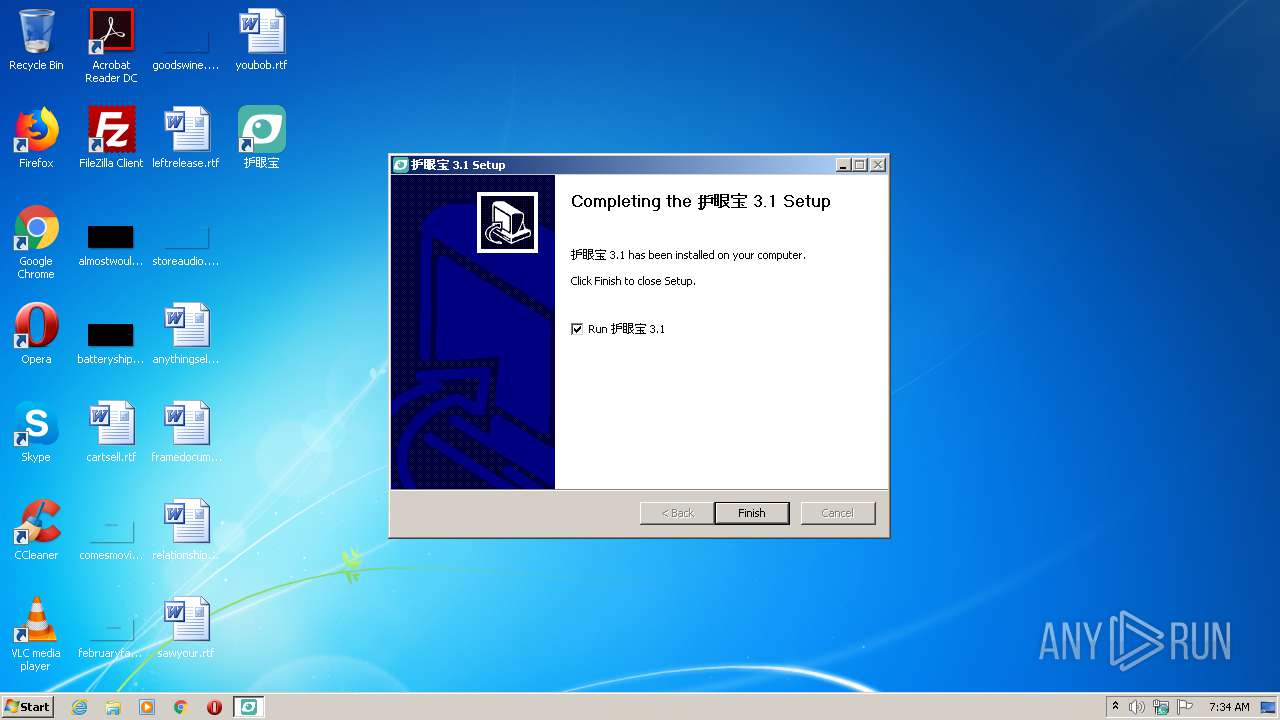
Application was dropped or rewritten from another process
- HuYanBao.exe (PID: 2760)
SUSPICIOUS
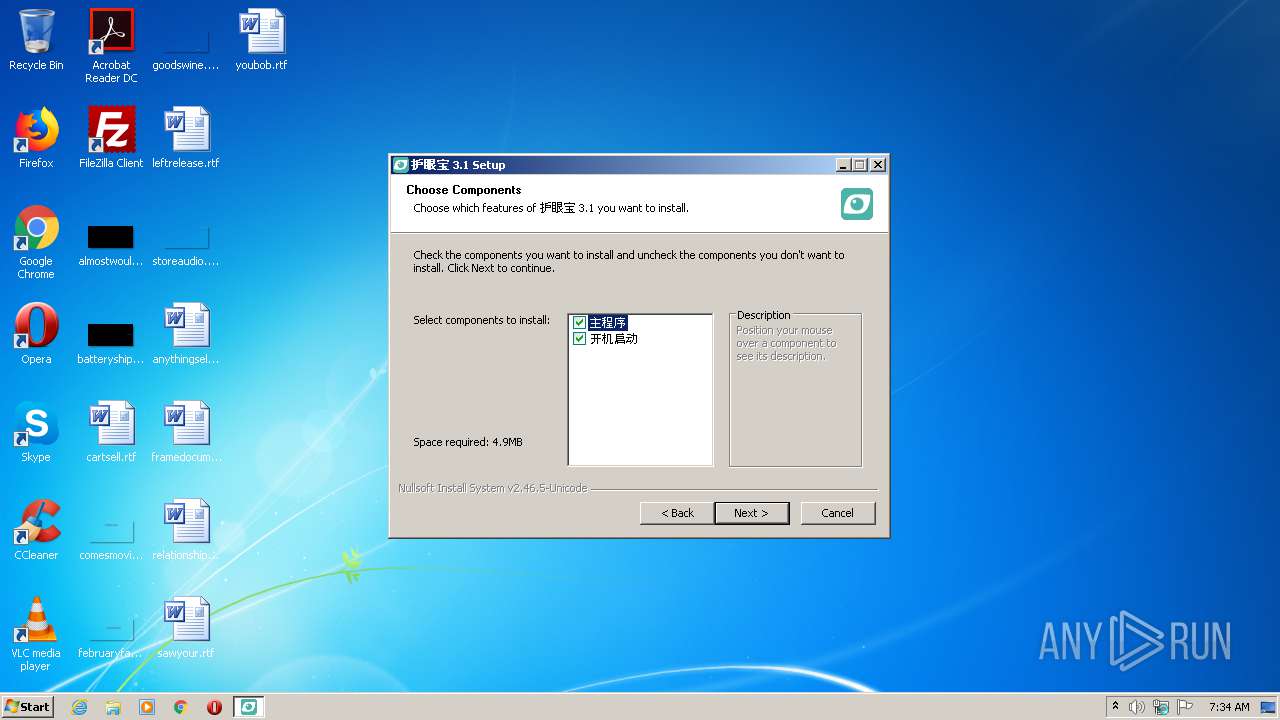
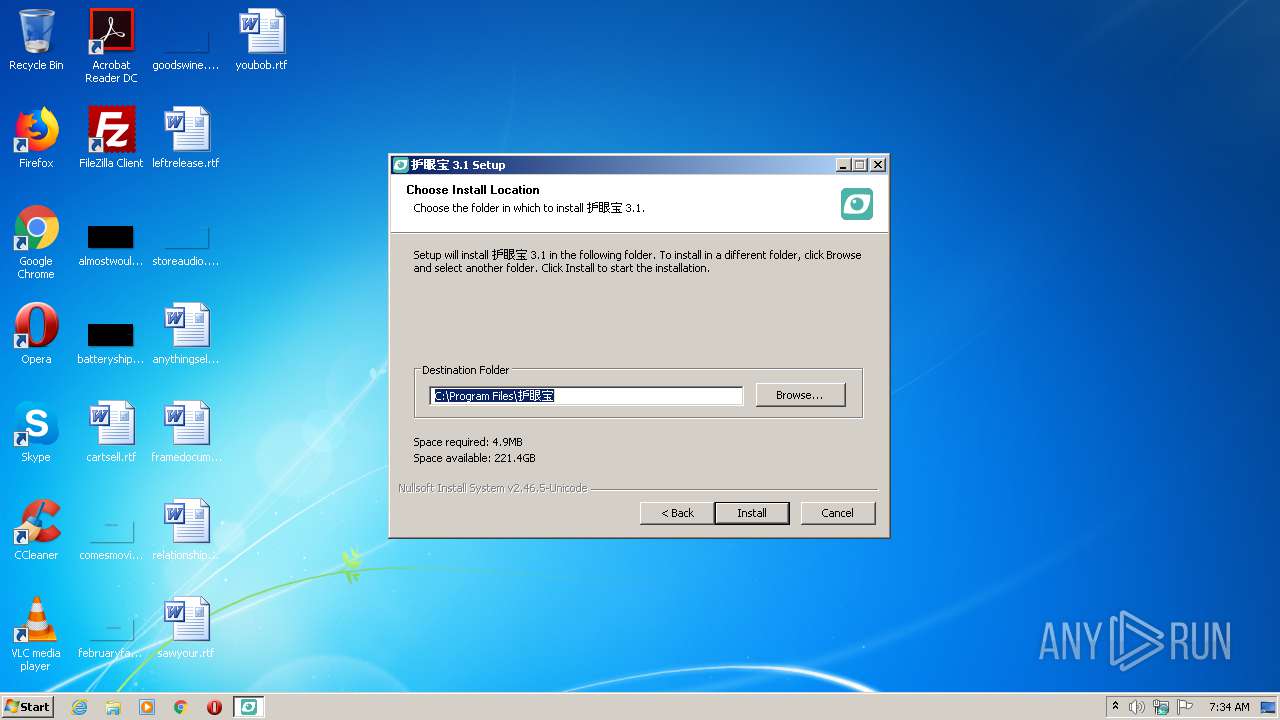
Creates files in the program directory
- huyanbao588455.exe (PID: 2788)
Executable content was dropped or overwritten
- huyanbao588455.exe (PID: 2788)
Creates a software uninstall entry
- huyanbao588455.exe (PID: 2788)
Reads Internet Cache Settings
- HuYanBao.exe (PID: 2760)
INFO
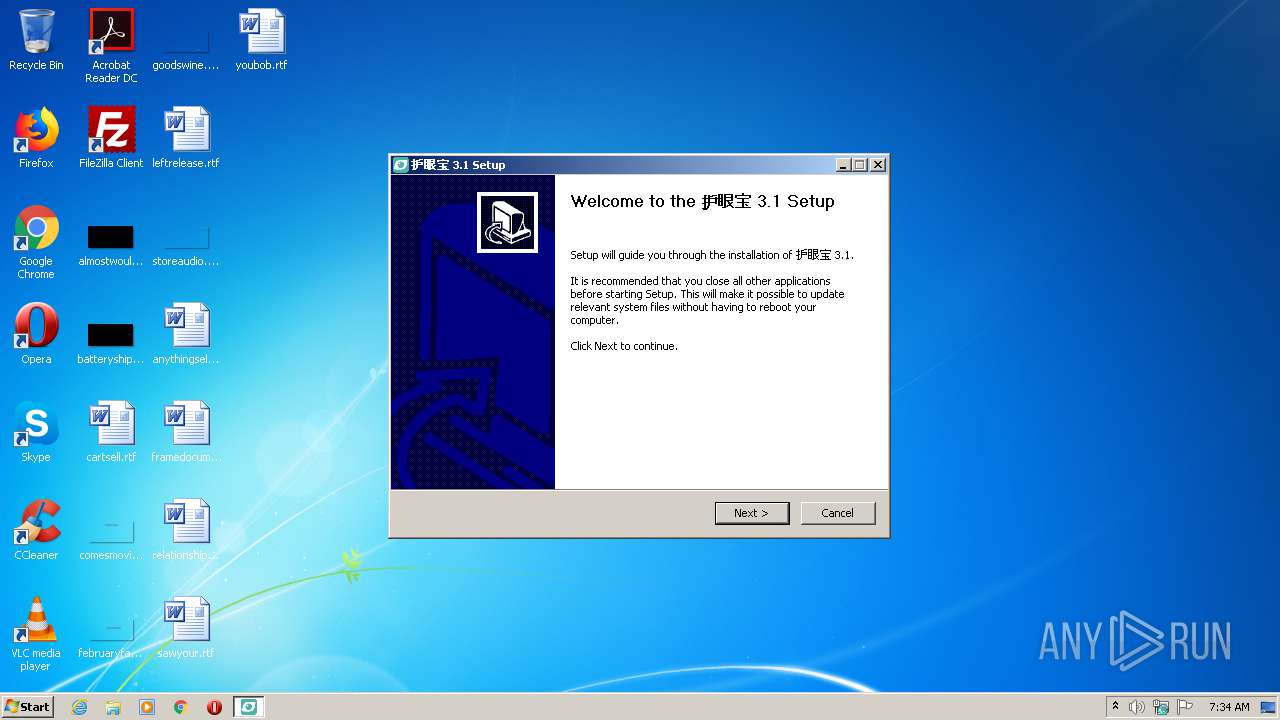
Manual execution by user
- WINWORD.EXE (PID: 3736)
Creates files in the user directory
- WINWORD.EXE (PID: 3736)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:20:04+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 29696 |
| InitializedDataSize: | 489984 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x38af |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:20:04 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:20:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000728C | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49971 |
.rdata | 0x00009000 | 0x00002B6E | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.49793 |
.data | 0x0000C000 | 0x00072B9C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.80494 |
.ndata | 0x0007F000 | 0x00091000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00110000 | 0x00023F10 | 0x00024000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.03381 |
.reloc | 0x00134000 | 0x00000FD6 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 2.54142 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11084 | 543 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.77368 | 38056 | UNKNOWN | English - United States | RT_ICON |
3 | 2.78458 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 2.95889 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 3.33876 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
42
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
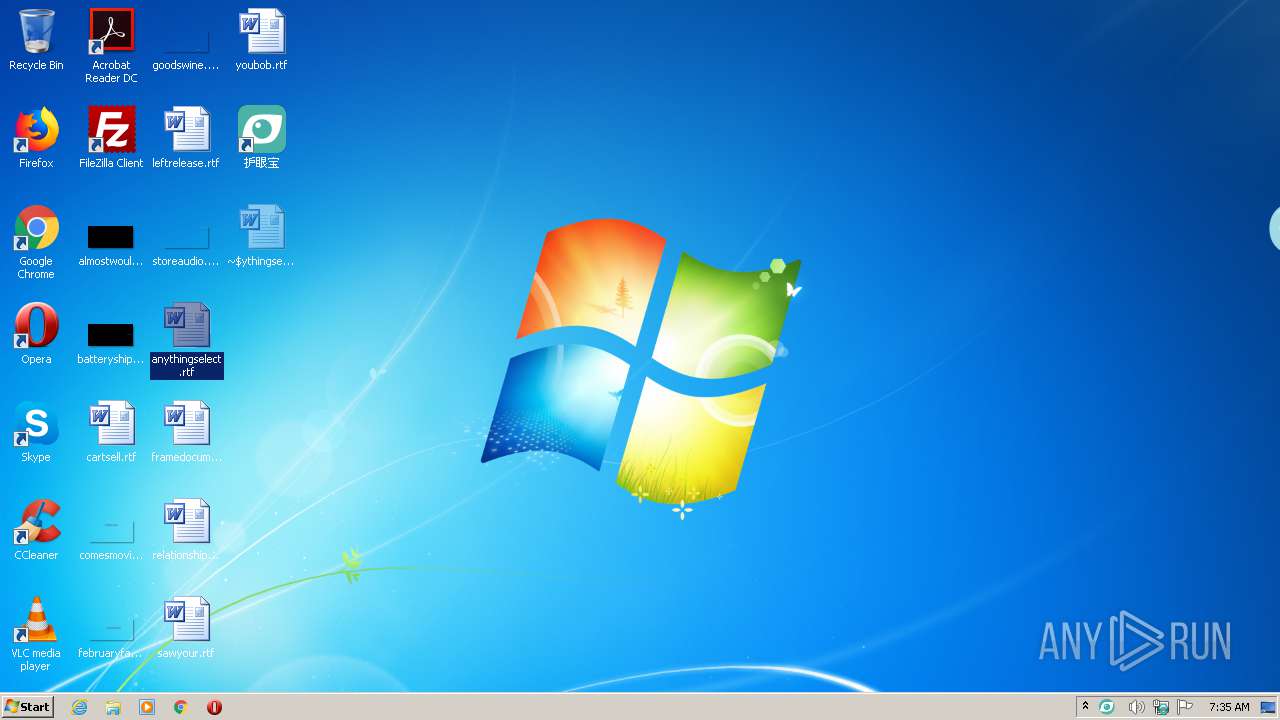
| 996 | "C:\Users\admin\AppData\Local\Temp\huyanbao588455.exe" | C:\Users\admin\AppData\Local\Temp\huyanbao588455.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
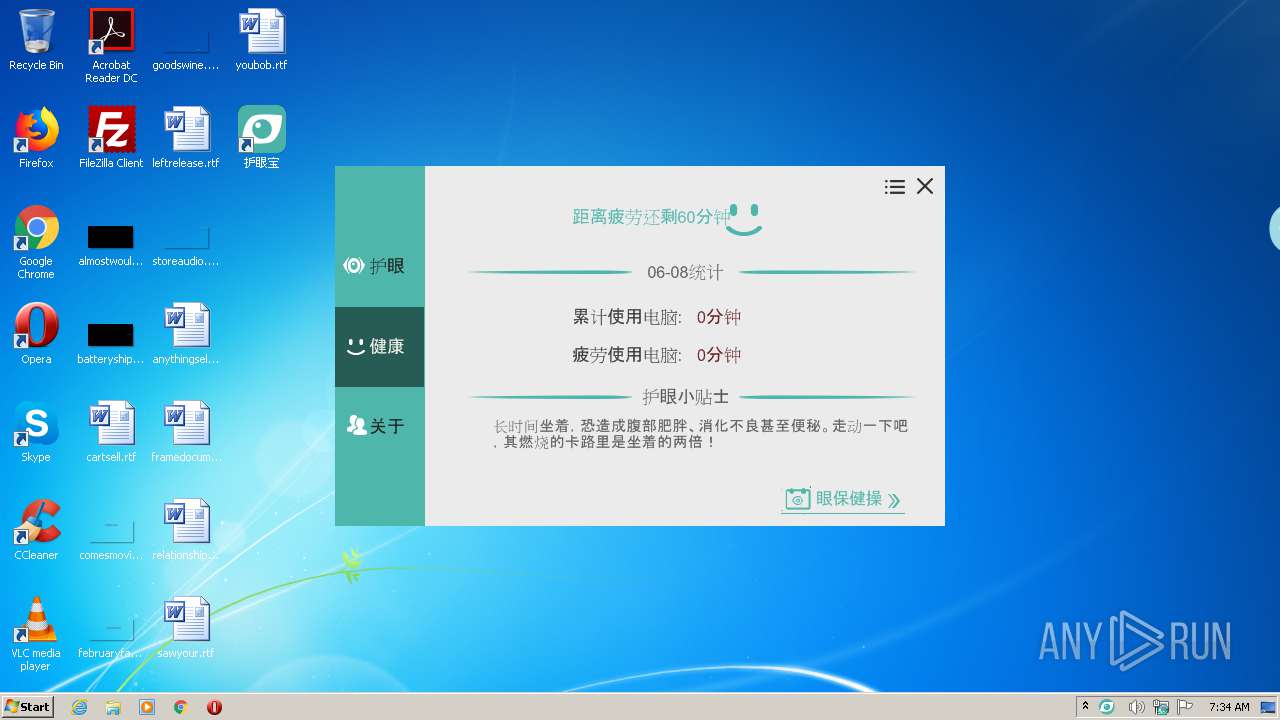
| 2760 | "C:\Program Files\护眼宝\HuYanBao.exe" | C:\Program Files\护眼宝\HuYanBao.exe | huyanbao588455.exe | ||||||||||||
User: admin Company: 深圳市护眼宝科技有限公司 Integrity Level: HIGH Description: 深圳市护眼宝科技有限公司 Exit code: 0 Version: 3.1 Modules
| |||||||||||||||
| 2788 | "C:\Users\admin\AppData\Local\Temp\huyanbao588455.exe" | C:\Users\admin\AppData\Local\Temp\huyanbao588455.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
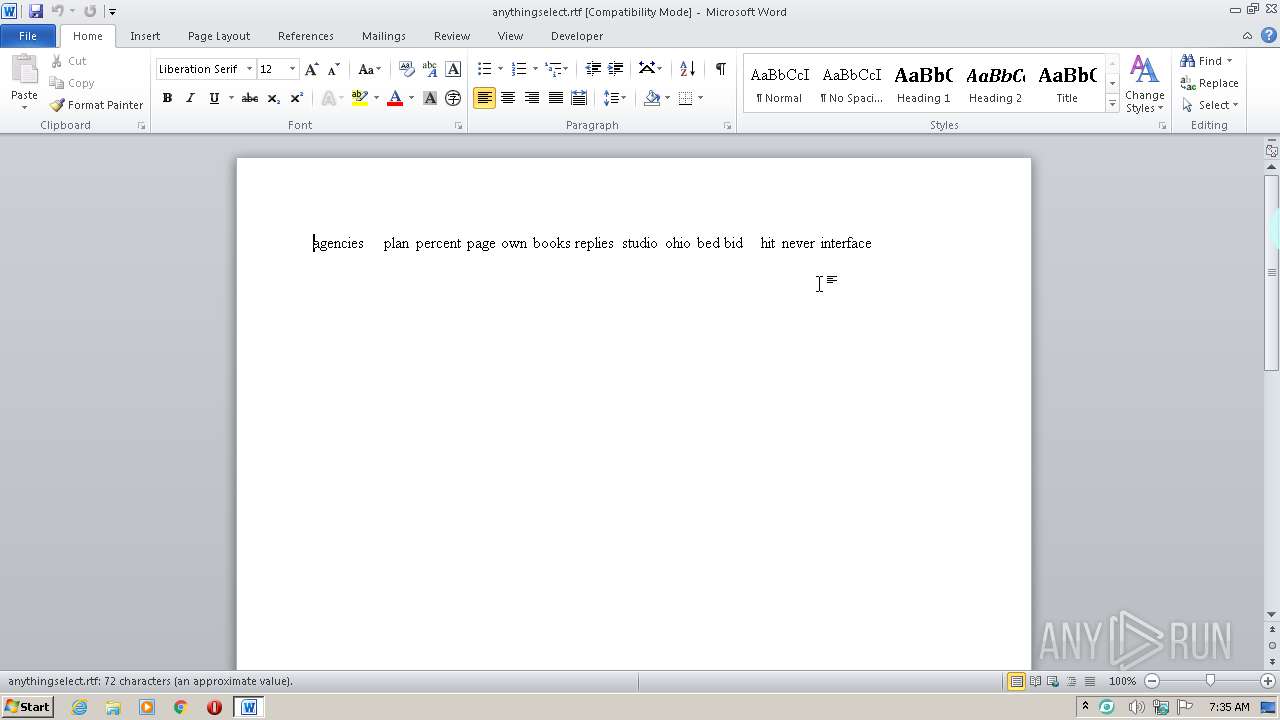
| 3736 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\anythingselect.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
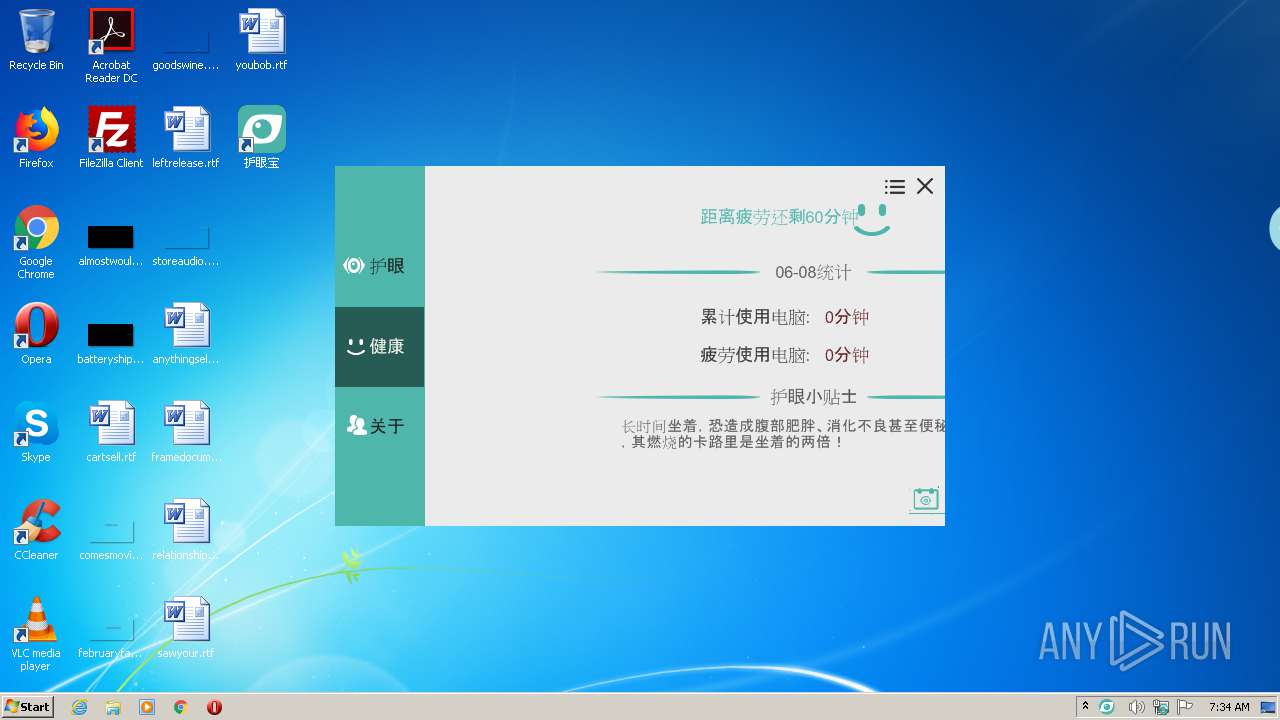
Total events
1 298
Read events
867
Write events
288
Delete events
143
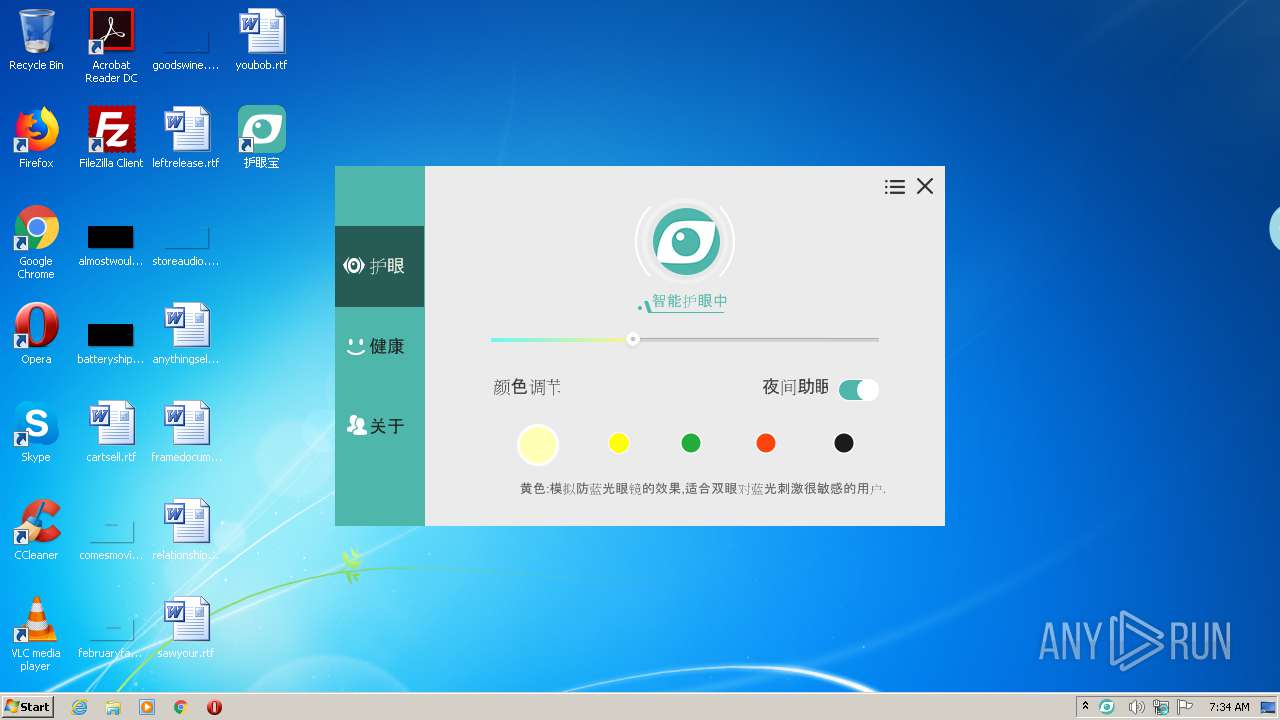
Modification events
| (PID) Process: | (2788) huyanbao588455.exe | Key: | HKEY_CURRENT_USER\Software\HuYanBao\Config |
| Operation: | write | Name: | ActiveTime |
Value: 0 | |||
| (PID) Process: | (2788) huyanbao588455.exe | Key: | HKEY_CURRENT_USER\Software\HuYanBao\Config |
| Operation: | write | Name: | AutoRun |
Value: 0 | |||
| (PID) Process: | (2788) huyanbao588455.exe | Key: | HKEY_CURRENT_USER\Software\HuYanBao\Config |
| Operation: | write | Name: | Intelligence |
Value: 1 | |||
| (PID) Process: | (2788) huyanbao588455.exe | Key: | HKEY_CURRENT_USER\Software\HuYanBao\Config |
| Operation: | write | Name: | pilaotixing |
Value: 1 | |||
| (PID) Process: | (2788) huyanbao588455.exe | Key: | HKEY_CURRENT_USER\Software\HuYanBao\Config |
| Operation: | write | Name: | pos |
Value: 50 | |||
| (PID) Process: | (2788) huyanbao588455.exe | Key: | HKEY_CURRENT_USER\Software\HuYanBao\Config |
| Operation: | write | Name: | sleephelper |
Value: 1 | |||
| (PID) Process: | (2788) huyanbao588455.exe | Key: | HKEY_CURRENT_USER\Software\HuYanBao\Config |
| Operation: | write | Name: | uuid |
Value: | |||
| (PID) Process: | (2788) huyanbao588455.exe | Key: | HKEY_CURRENT_USER\Software\HuYanBao\Config |
| Operation: | write | Name: | WindowHiding |
Value: 0 | |||
| (PID) Process: | (2788) huyanbao588455.exe | Key: | HKEY_CURRENT_USER\Software\HuYanBao\Config |
| Operation: | write | Name: | hycolor |
Value: 1 | |||
| (PID) Process: | (2788) huyanbao588455.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | huyanbao |
Value: C:\Program Files\护眼宝\HuYanBao.exe -a | |||
Executable files
4
Suspicious files
0
Text files
38
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR21EC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{7AA72689-12DB-4673-8CC6-F46D1C21535D}.tmp | — | |
MD5:— | SHA256:— | |||
| 3736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{CD5C73FC-9805-48E1-8E4A-9A35C4B336D6}.tmp | — | |
MD5:— | SHA256:— | |||
| 3736 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{C831D024-8D25-4723-81F2-A4D2587B7B5C}.tmp | — | |
MD5:— | SHA256:— | |||
| 2788 | huyanbao588455.exe | C:\Program Files\护眼宝\HuYanBao.exe | executable | |
MD5:— | SHA256:— | |||
| 2788 | huyanbao588455.exe | C:\Users\admin\AppData\Local\Temp\nss7D9F.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 2788 | huyanbao588455.exe | C:\Users\Administrator\NTUSER.DAT.LOG1 | log | |
MD5:— | SHA256:— | |||
| 3736 | WINWORD.EXE | C:\Users\admin\Desktop\~$ythingselect.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3736 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2788 | huyanbao588455.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat | hiv | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
5
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2760 | HuYanBao.exe | GET | — | 121.42.48.1:8080 | http://server.huyanbao.com:8080/statistics/onEvent.do?platType=0&eventName=protect_night_true | CN | — | — | unknown |
2760 | HuYanBao.exe | GET | — | 121.42.48.1:8080 | http://server.huyanbao.com:8080/statistics/dau.do?platType=0 | CN | — | — | unknown |
2760 | HuYanBao.exe | GET | — | 121.42.48.1:8080 | http://server.huyanbao.com:8080/statistics/newInstall.do?platType=0&uuid=9D151762-6818-44AF-AFAC-E55634CA2BD4 | CN | — | — | unknown |
2760 | HuYanBao.exe | GET | — | 121.42.48.1:8080 | http://server.huyanbao.com:8080/statistics/onEvent.do?platType=0&eventName=main_health | CN | — | — | unknown |
2760 | HuYanBao.exe | GET | 405 | 185.232.59.133:80 | http://huyanbaostatic.b0.upaiyun.com/pc/tips?rd=BD269EBF-6F4F-4800-888C-00F43F01EAFE | unknown | text | 44 b | suspicious |
2760 | HuYanBao.exe | GET | 405 | 185.232.59.133:80 | http://huyanbaostatic.b0.upaiyun.com/pc/lastVersionEng?rd=97A1C354-7220-46D4-81E3-2FF50AE86BD9 | unknown | text | 44 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2760 | HuYanBao.exe | 121.42.48.1:8080 | server.huyanbao.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2760 | HuYanBao.exe | 185.232.59.133:80 | huyanbaostatic.b0.upaiyun.com | — | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
server.huyanbao.com |
| unknown |
huyanbaostatic.b0.upaiyun.com |
| suspicious |
Threats
Process | Message |
|---|---|
HuYanBao.exe | 1
|
HuYanBao.exe | 1
|
HuYanBao.exe | 1
|
HuYanBao.exe | 1
|
HuYanBao.exe | 1
|
HuYanBao.exe | 1
|
HuYanBao.exe | 1
|
HuYanBao.exe | 1
|
HuYanBao.exe | 1
|
HuYanBao.exe | 1
|