| File name: | Nolex Trainer V2.exe |
| Full analysis: | https://app.any.run/tasks/ec98d16c-ec4b-459c-8eba-d6290c4d1ce6 |
| Verdict: | Malicious activity |
| Analysis date: | July 27, 2020, 18:41:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2405562923AD1EE01C3301E8E9BBC69F |
| SHA1: | E2D4D7F48D2D31FD2F3E05F1E930B663CD9CD8EC |
| SHA256: | 1037AFEA534DE0C0156653EB54D9EEC6EF23542C0B29B8F0323FB17414DA9D07 |
| SSDEEP: | 196608:C5JrQul//BX+NfWc5nU+k63LdONLLIse6RGGM9SJ7Q1xNWeQ+lMPdg8gI9S/:C5JUuxd0WdWpnPGMMJEnQ+lZ8RU/ |
MALICIOUS
Application was dropped or rewritten from another process
- AppServices.exe (PID: 3048)
- Nolex Trainer.exe (PID: 2960)
Changes the autorun value in the registry
- Nolex Trainer V2.exe (PID: 1308)
SUSPICIOUS
Creates files in the user directory
- Nolex Trainer V2.exe (PID: 1308)
- Nolex Trainer.exe (PID: 2960)
Executable content was dropped or overwritten
- Nolex Trainer V2.exe (PID: 1308)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:13 09:26:24+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.14 |
| CodeSize: | 242176 |
| InitializedDataSize: | 465408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1bc5e |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Aug-2018 07:26:24 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 13-Aug-2018 07:26:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003B10F | 0x0003B200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54173 |
.rdata | 0x0003D000 | 0x000111E0 | 0x00011200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.42687 |
.data | 0x0004F000 | 0x000026A4 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.99951 |
.rsrc | 0x00052000 | 0x0005A921 | 0x0005AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.557483 |
.reloc | 0x000AD000 | 0x000035F8 | 0x00003600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.60972 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0.989259 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 0.537708 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 0.771865 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 0.559915 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 0.642033 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
ICONFINDER_ICON-BROWSER_2867868 | 2.76511 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
WS2_32.dll |
Total processes
40
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1308 | "C:\Users\admin\AppData\Local\Temp\Nolex Trainer V2.exe" | C:\Users\admin\AppData\Local\Temp\Nolex Trainer V2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
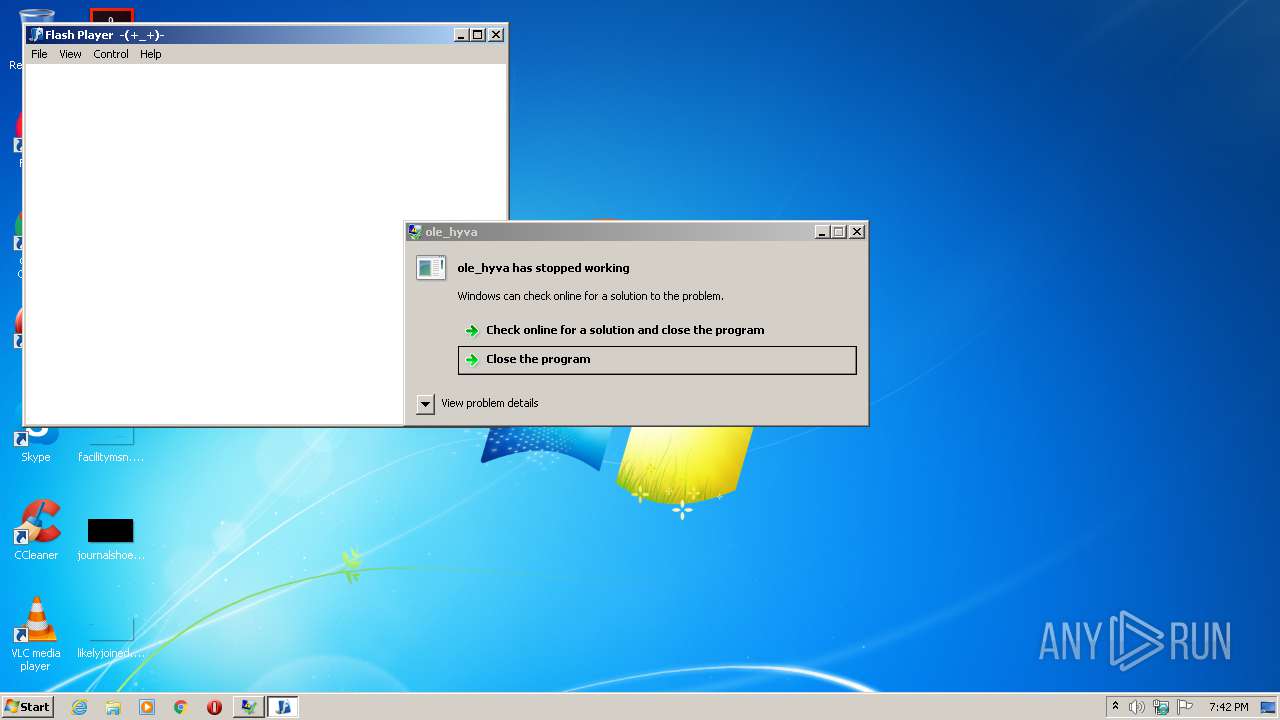
| 2960 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Administrative Tools\Nolex Trainer.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Administrative Tools\Nolex Trainer.exe | — | Nolex Trainer V2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Flash Player 11 Exit code: 0 Version: 11.4.402.278 Modules
| |||||||||||||||
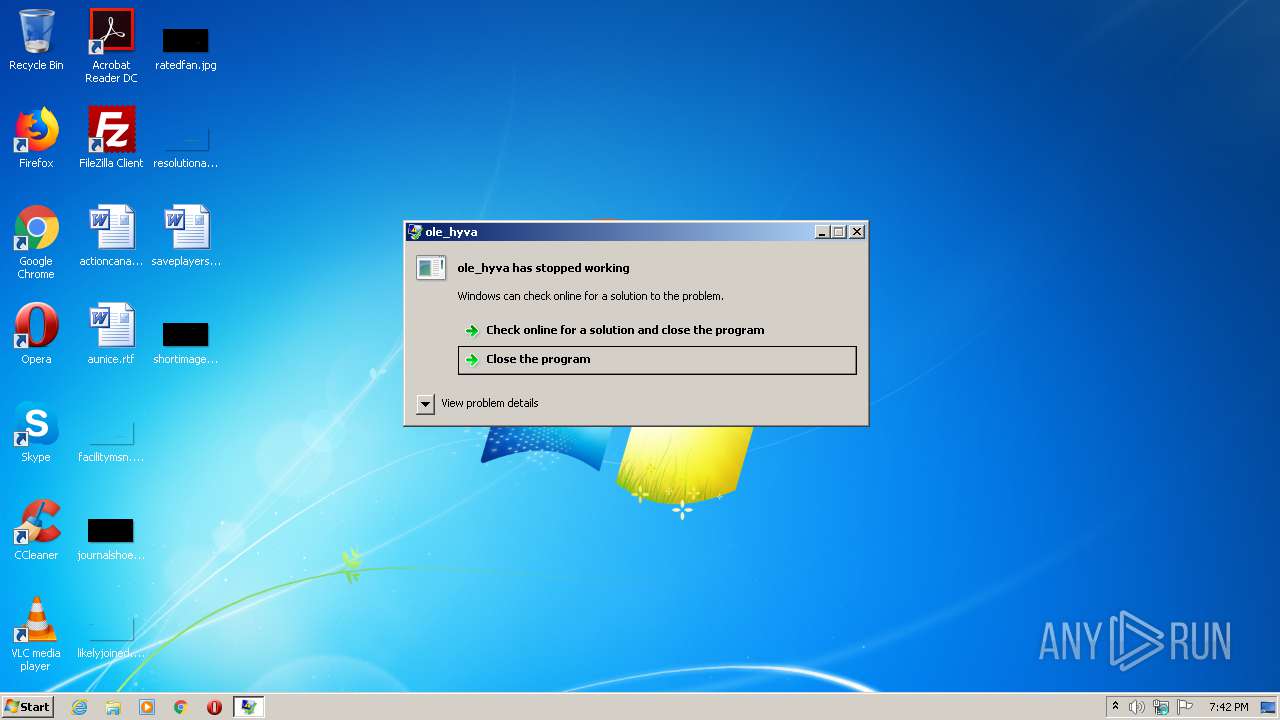
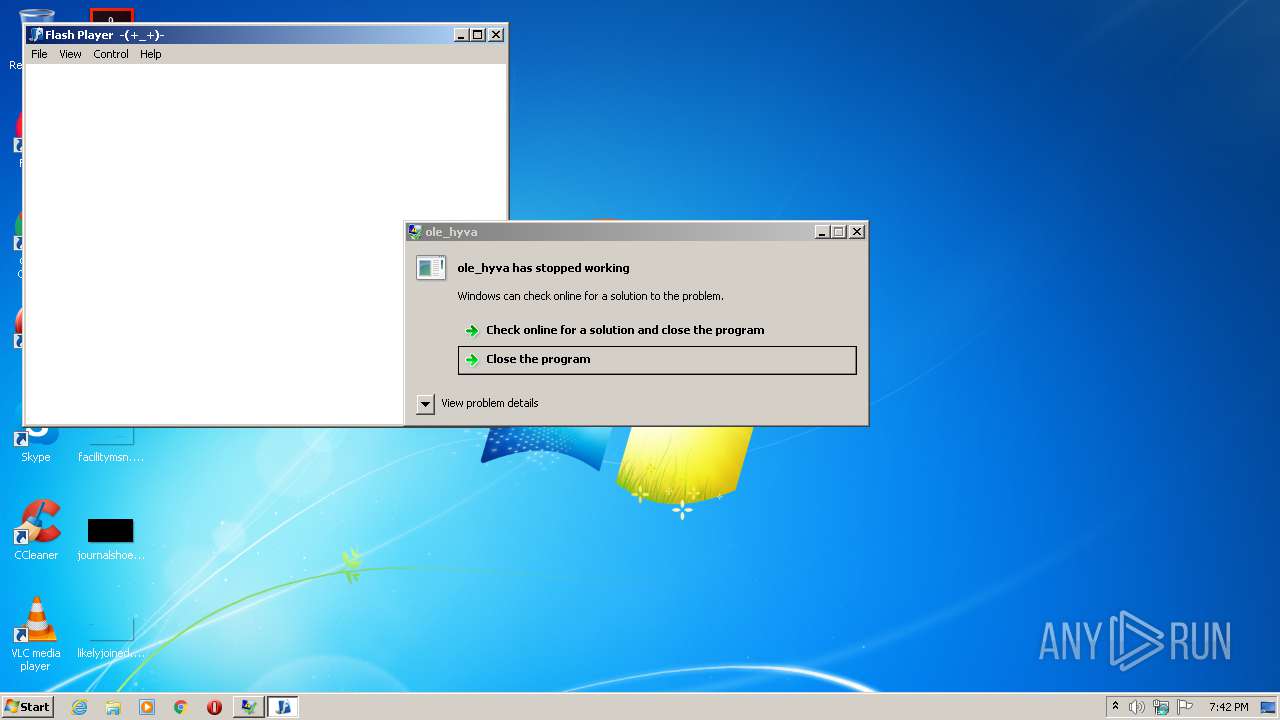
| 3048 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Administrative Tools\AppServices.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Administrative Tools\AppServices.exe | Nolex Trainer V2.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ole_hyva Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
42
Read events
40
Write events
2
Delete events
0
Modification events
| (PID) Process: | (1308) Nolex Trainer V2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | AppServices.exe |
Value: "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Administrative Tools\AppServices.exe" | |||
| (PID) Process: | (2960) Nolex Trainer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Nolex Trainer.exe | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | Nolex Trainer.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 2960 | Nolex Trainer.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\#local\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 2960 | Nolex Trainer.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\#SharedObjects\FG4YA5TZ\localhost\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Administrative Tools\Nolex Trainer.exe\Scratch.sxx | — | |
MD5:— | SHA256:— | |||
| 1308 | Nolex Trainer V2.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Administrative Tools\Nolex Trainer.exe | executable | |
MD5:— | SHA256:— | |||
| 1308 | Nolex Trainer V2.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Administrative Tools\AppServices.exe | executable | |
MD5:— | SHA256:— | |||
| 2960 | Nolex Trainer.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sol | sol | |
MD5:B3A2C15833ED3013C1C8F09A3090613B | SHA256:1E6364E1A33CCE9395071C75F7D8DF3759DC475BAA6F677422F29C9BCF3E6869 | |||
| 2960 | Nolex Trainer.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\#local\settings.sol | sol | |
MD5:A6CDC076C738534E45C0D597BE2DD3E5 | SHA256:2A3F42A0F6AB8F7FE9C09FA9759452F1B6D20D91B74D0C98E3B529FB4BF90DA0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report