| File name: | HWID Spoofer.exe |
| Full analysis: | https://app.any.run/tasks/835490e6-bb5e-438c-89dc-fc6e41c69999 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 16:08:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B43985CA33D03D270512B878DCE29E8C |
| SHA1: | AA71FB53A6C000ED059E935280A7A985E6665230 |
| SHA256: | 1034EF5AA89EC1637D31B3DFF062063B1DA6A69F038EC2801D3604896FEB6C2D |
| SSDEEP: | 49152:DNQ6j0NQSd6vuoF3PZ6x9jDR3lUPmdm7OTOMsf7deXHBo0Ms:DNQ6oNQSd6vuodatF1wmdmgfwxOBo0Ms |
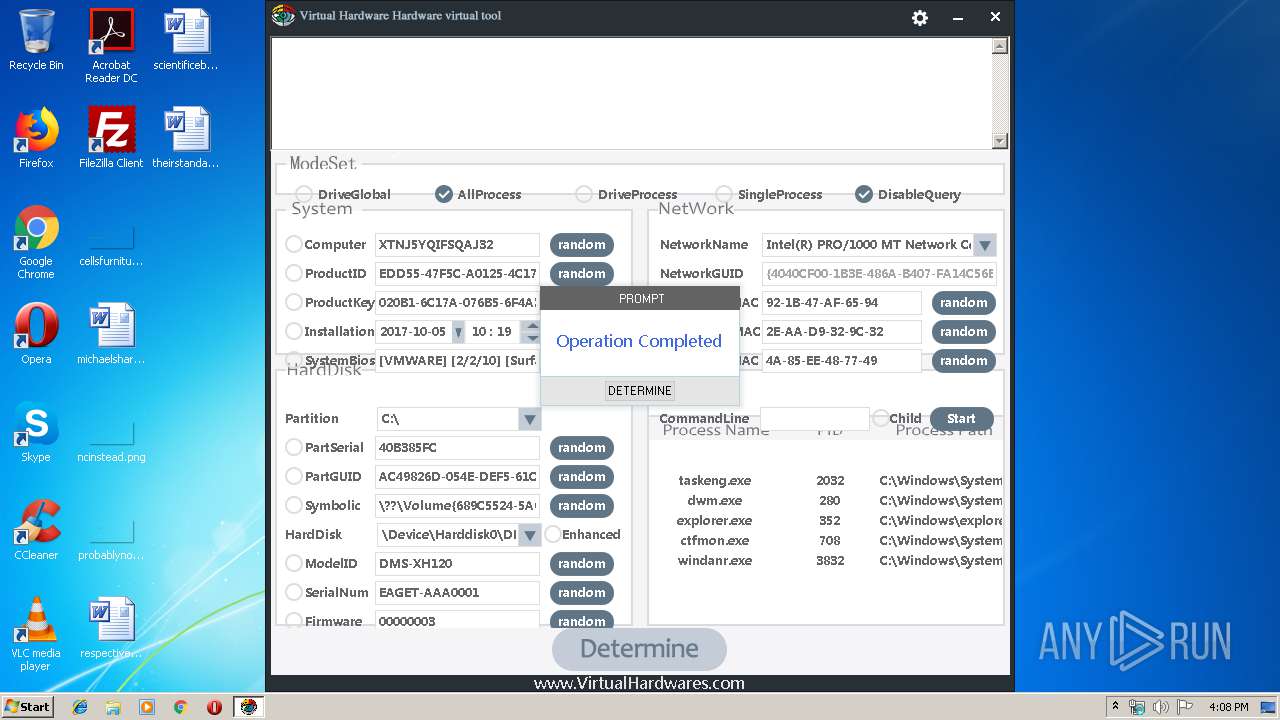
MALICIOUS
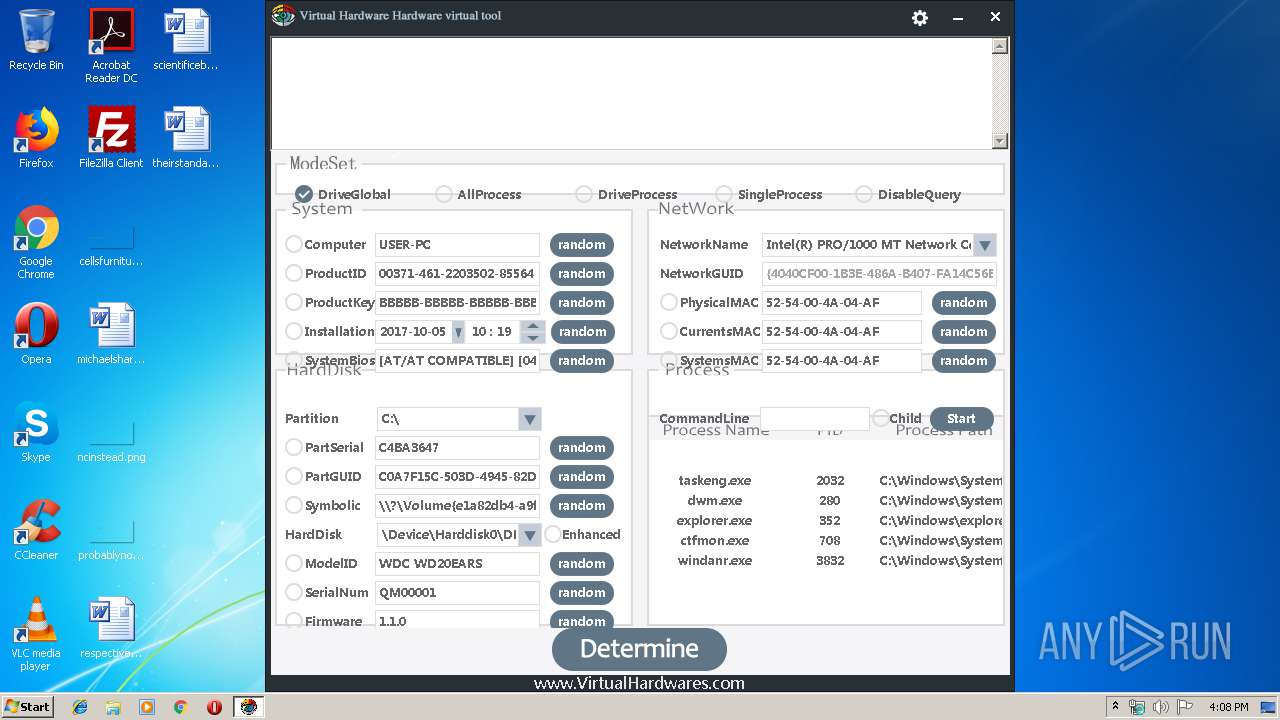
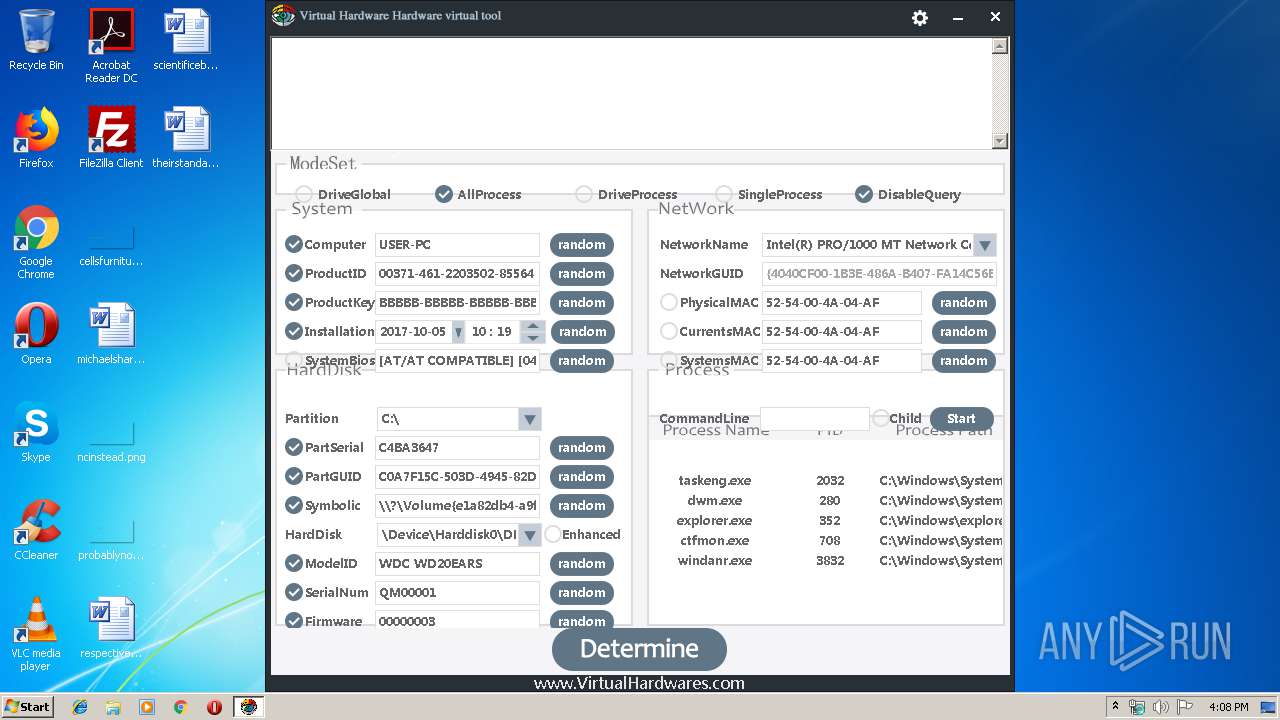
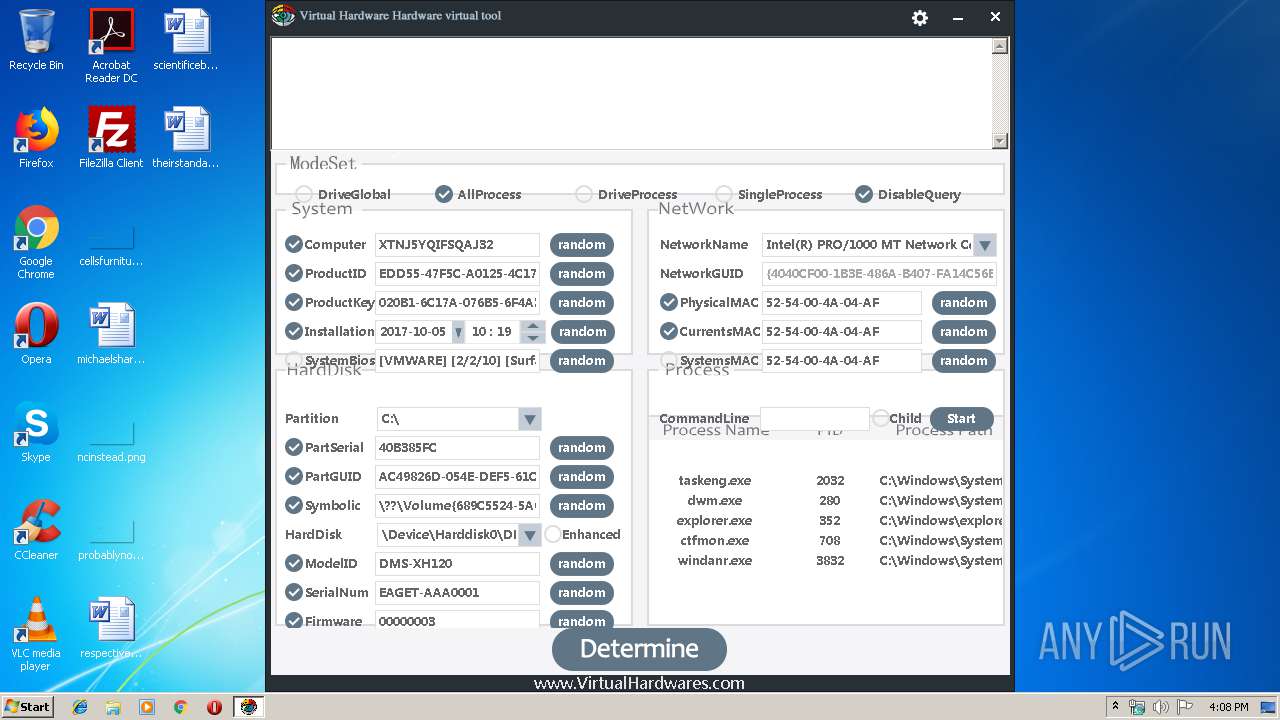
Loads dropped or rewritten executable
- ctfmon.exe (PID: 708)
- dwm.exe (PID: 280)
- windanr.exe (PID: 3832)
- taskeng.exe (PID: 2032)
Runs injected code in another process
- HWID Spoofer.exe (PID: 4064)
Application was injected by another process
- windanr.exe (PID: 3832)
- ctfmon.exe (PID: 708)
- dwm.exe (PID: 280)
- taskeng.exe (PID: 2032)
SUSPICIOUS
Executable content was dropped or overwritten
- HWID Spoofer.exe (PID: 4064)
Reads internet explorer settings
- HWID Spoofer.exe (PID: 4064)
Low-level read access rights to disk partition
- HWID Spoofer.exe (PID: 4064)
Executed via COM
- iexplore.exe (PID: 3508)
Creates files in the user directory
- HWID Spoofer.exe (PID: 4064)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3508)
Reads internet explorer settings
- iexplore.exe (PID: 1048)
Creates files in the user directory
- iexplore.exe (PID: 1048)
Application launched itself
- iexplore.exe (PID: 3508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (18) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (2.9) |
| .exe | | | Generic Win/DOS Executable (1.3) |
| .exe | | | DOS Executable Generic (1.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:02 08:51:31+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 446976 |
| InitializedDataSize: | 1221120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5346c |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | hardware |
| FileDescription: | hardware |
| FileVersion: | 1, 0, 0, 0 |
| InternalName: | hardware.exe |
| LegalCopyright: | (C) virtualhardwares All Rights Reserved |
| OriginalFileName: | hardware |
| ProductName: | hardware |
| ProductVersion: | 1, 0, 0, 0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Aug-2018 06:51:31 |
| Detected languages: |
|
| CompanyName: | hardware |
| FileDescription: | hardware |
| FileVersion: | 1, 0, 0, 0 |
| InternalName: | hardware.exe |
| LegalCopyright: | (C) virtualhardwares All Rights Reserved |
| OriginalFilename: | hardware |
| ProductName: | hardware |
| ProductVersion: | 1, 0, 0, 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Aug-2018 06:51:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0006D11E | 0x0006D200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60589 |
.rdata | 0x0006F000 | 0x00017E7E | 0x00018000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.35541 |
.data | 0x00087000 | 0x00009BD8 | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.20731 |
.rsrc | 0x00091000 | 0x00104F3C | 0x00105000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.82038 |
.reloc | 0x00196000 | 0x000086B8 | 0x00008800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.70908 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.01229 | 633 | Latin 1 / Western European | English - United States | RT_MANIFEST |
5 | 1.91924 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
10 | 5.19906 | 19973 | Latin 1 / Western European | English - United States | XML |
11 | 4.97839 | 463 | Latin 1 / Western European | English - United States | XML |
13 | 5.31532 | 1302 | Latin 1 / Western European | English - United States | XML |
14 | 5.19827 | 782 | Latin 1 / Western European | English - United States | XML |
15 | 5.01732 | 7630 | Latin 1 / Western European | English - United States | XML |
100 | 7.71276 | 16407 | Latin 1 / Western European | Chinese - PRC | PNG |
106 | 7.81787 | 205312 | Latin 1 / Western European | English - United States | RC_DATA |
107 | 7.79408 | 261632 | Latin 1 / Western European | English - United States | RC_DATA |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
OLEAUT32.dll |
PSAPI.DLL |
USER32.dll |
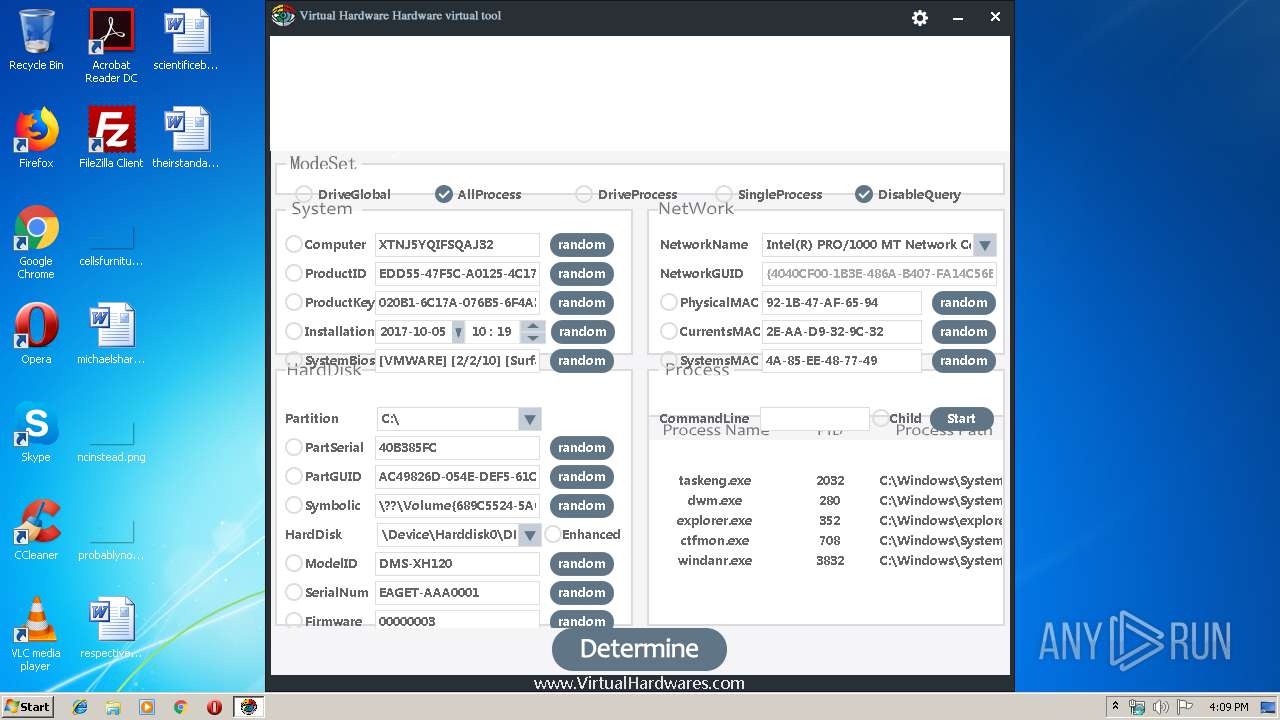
Total processes
41
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 708 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3508 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2032 | taskeng.exe {532150F8-214C-4D30-9483-0A3BC3E44D0E} | C:\Windows\System32\taskeng.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2660 | "C:\Users\admin\AppData\Local\Temp\HWID Spoofer.exe" | C:\Users\admin\AppData\Local\Temp\HWID Spoofer.exe | — | explorer.exe | |||||||||||
User: admin Company: hardware Integrity Level: MEDIUM Description: hardware Exit code: 3221226540 Version: 1, 0, 0, 0 Modules
| |||||||||||||||
| 3508 | "C:\Program Files\Internet Explorer\iexplore.exe" -startmediumtab -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3832 | "windanr.exe" | C:\Windows\system32\windanr.exe | qemu-ga.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4064 | "C:\Users\admin\AppData\Local\Temp\HWID Spoofer.exe" | C:\Users\admin\AppData\Local\Temp\HWID Spoofer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
524
Read events
421
Write events
101
Delete events
2
Modification events
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3832) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
1
Suspicious files
2
Text files
12
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1048 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\i8pan9a[1].htm | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6B1F39B5C6203865.TMP | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFED932DAA88FAE73F.TMP | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB38526C077AC235D.TMP | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\{AB4A4ACE-3943-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8A1F581A9D8AFF3D.TMP | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\RecoveryStore.{AB4A4ACD-3943-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 4064 | HWID Spoofer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\gg[1].htm | html | |
MD5:— | SHA256:— | |||
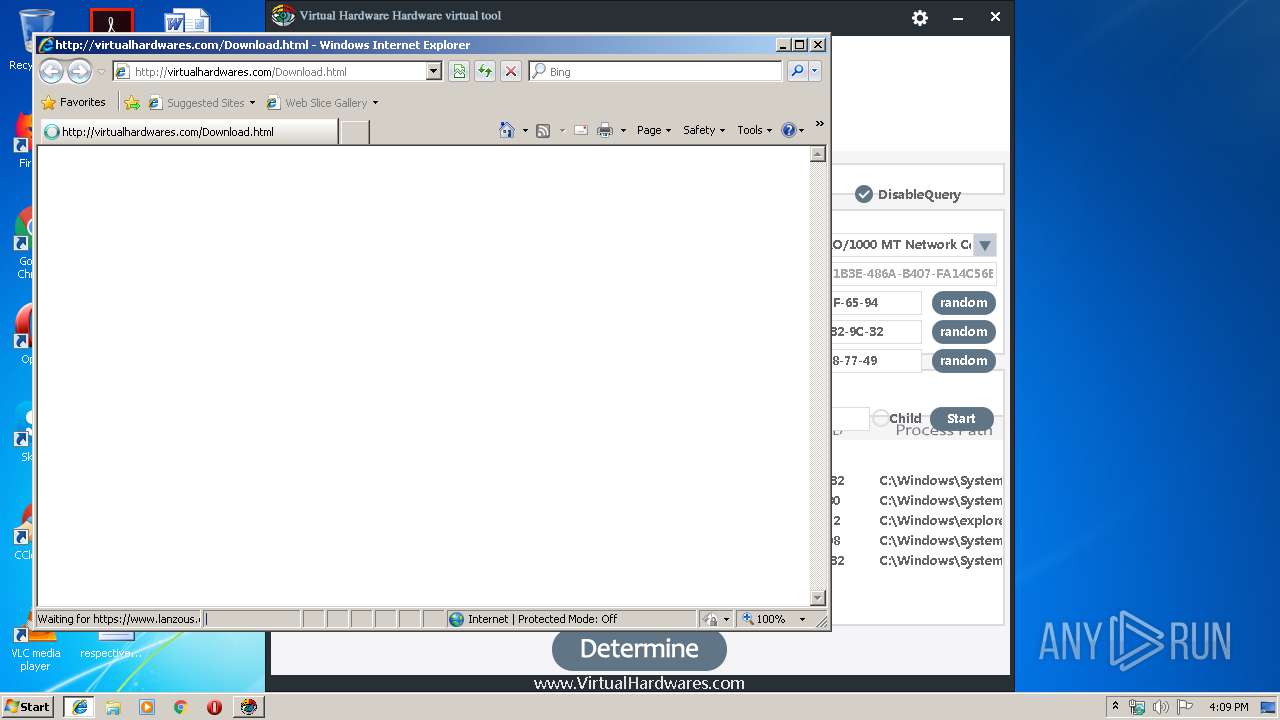
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
8
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1048 | iexplore.exe | GET | 200 | 137.59.148.97:80 | http://virtualhardwares.com/Download.html | IN | html | 111 b | malicious |
1048 | iexplore.exe | GET | 404 | 137.59.148.97:80 | http://virtualhardwares.com/favicon.ico | IN | text | 613 b | malicious |
3508 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4064 | HWID Spoofer.exe | 137.59.148.97:80 | www.virtualhardwares.com | PDR | IN | malicious |
4064 | HWID Spoofer.exe | 58.215.145.249:443 | s22.cnzz.com | AS Number for CHINANET jiangsu province backbone | CN | unknown |
4064 | HWID Spoofer.exe | 58.215.145.248:443 | s22.cnzz.com | AS Number for CHINANET jiangsu province backbone | CN | unknown |
4064 | HWID Spoofer.exe | 203.119.129.114:443 | z1.cnzz.com | — | CN | malicious |
3508 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4064 | HWID Spoofer.exe | 198.11.132.221:443 | cnzz.mmstat.com | Alibaba (China) Technology Co., Ltd. | US | suspicious |
1048 | iexplore.exe | 137.59.148.97:80 | www.virtualhardwares.com | PDR | IN | malicious |
1048 | iexplore.exe | 61.158.239.147:443 | www.lanzous.com | CHINA UNICOM China169 Backbone | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.virtualhardwares.com |
| unknown |
s22.cnzz.com |
| suspicious |
z1.cnzz.com |
| whitelisted |
c.cnzz.com |
| whitelisted |
cnzz.mmstat.com |
| whitelisted |
www.bing.com |
| whitelisted |
virtualhardwares.com |
| unknown |
www.lanzous.com |
| malicious |
Threats
Process | Message |
|---|---|
taskeng.exe | DllMain--DLL_PROCESS_ATTACH
|
dwm.exe | DllMain--DLL_PROCESS_ATTACH
|
windanr.exe | DllMain--DLL_PROCESS_ATTACH
|
ctfmon.exe | DllMain--DLL_PROCESS_ATTACH
|