| File name: | RADMIN22.EXE |
| Full analysis: | https://app.any.run/tasks/052dbf71-ceee-4048-891a-f39ca43a4462 |
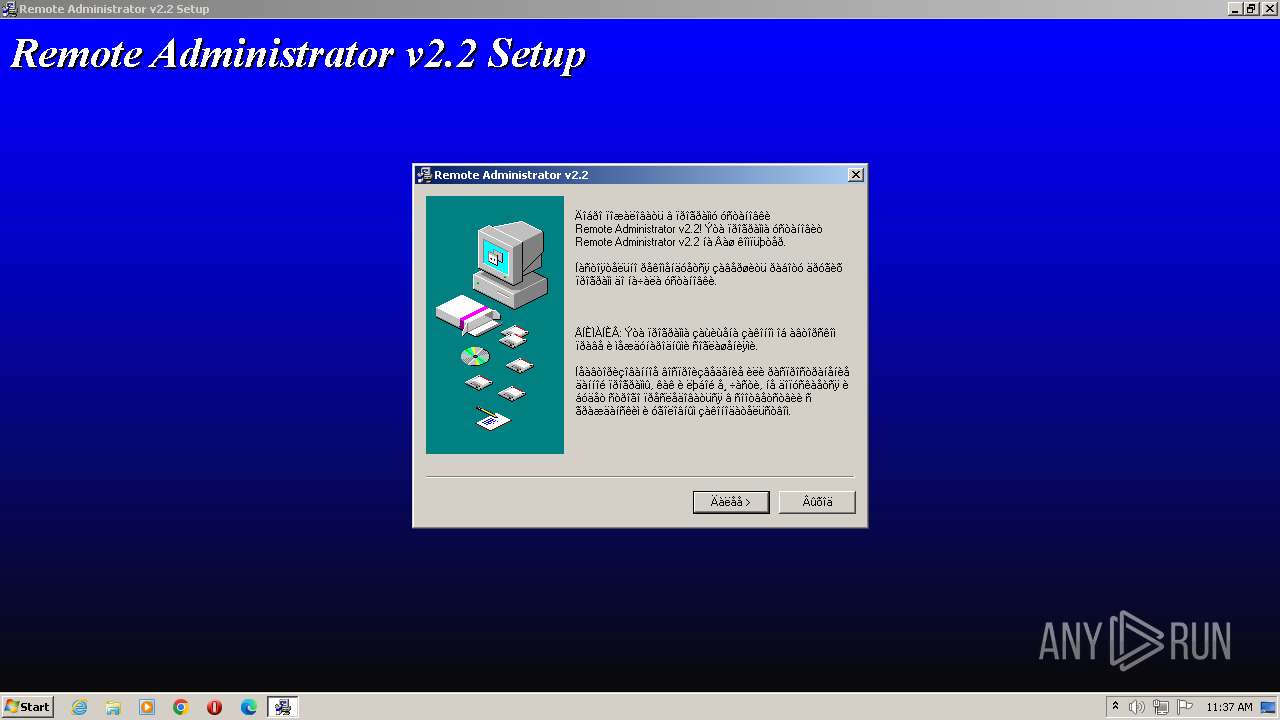
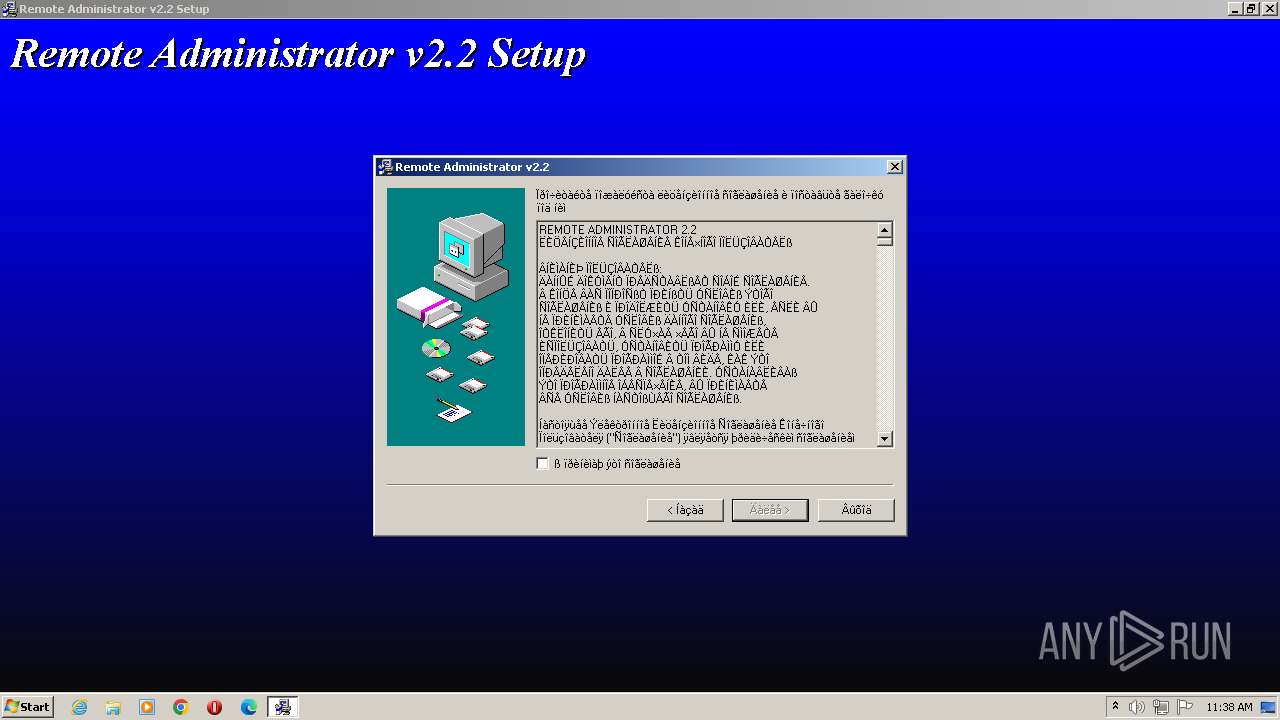
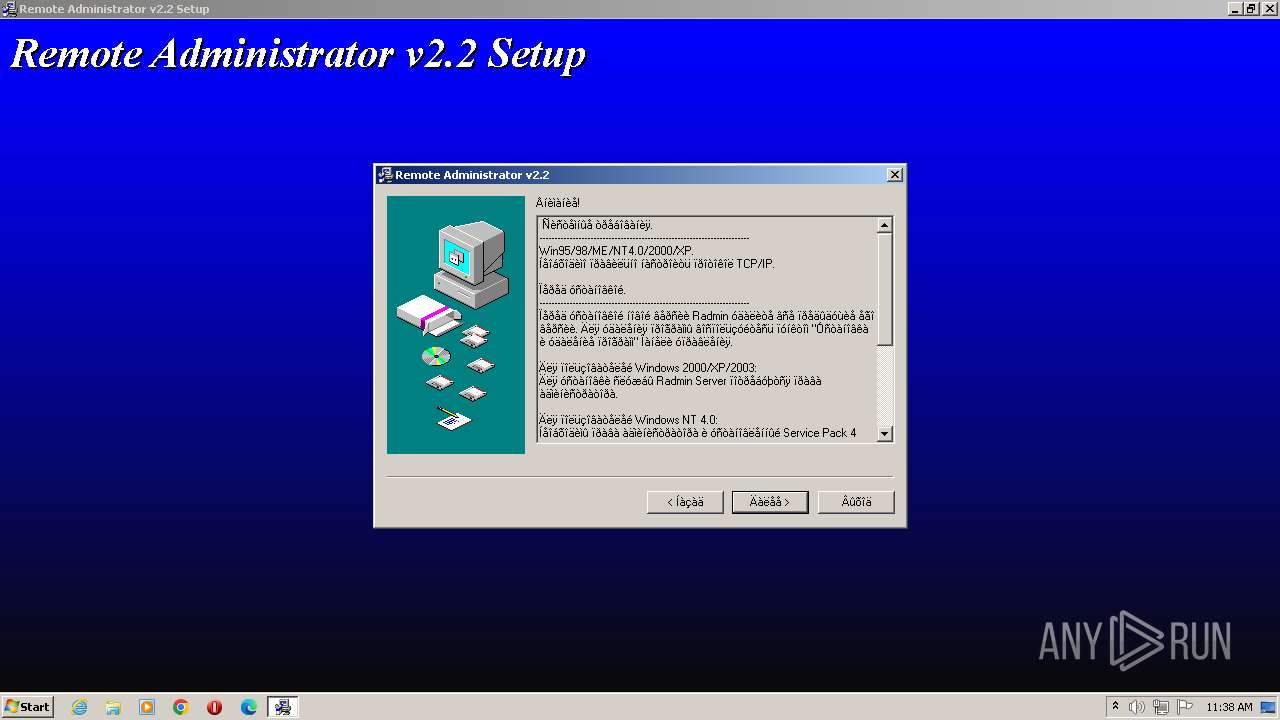
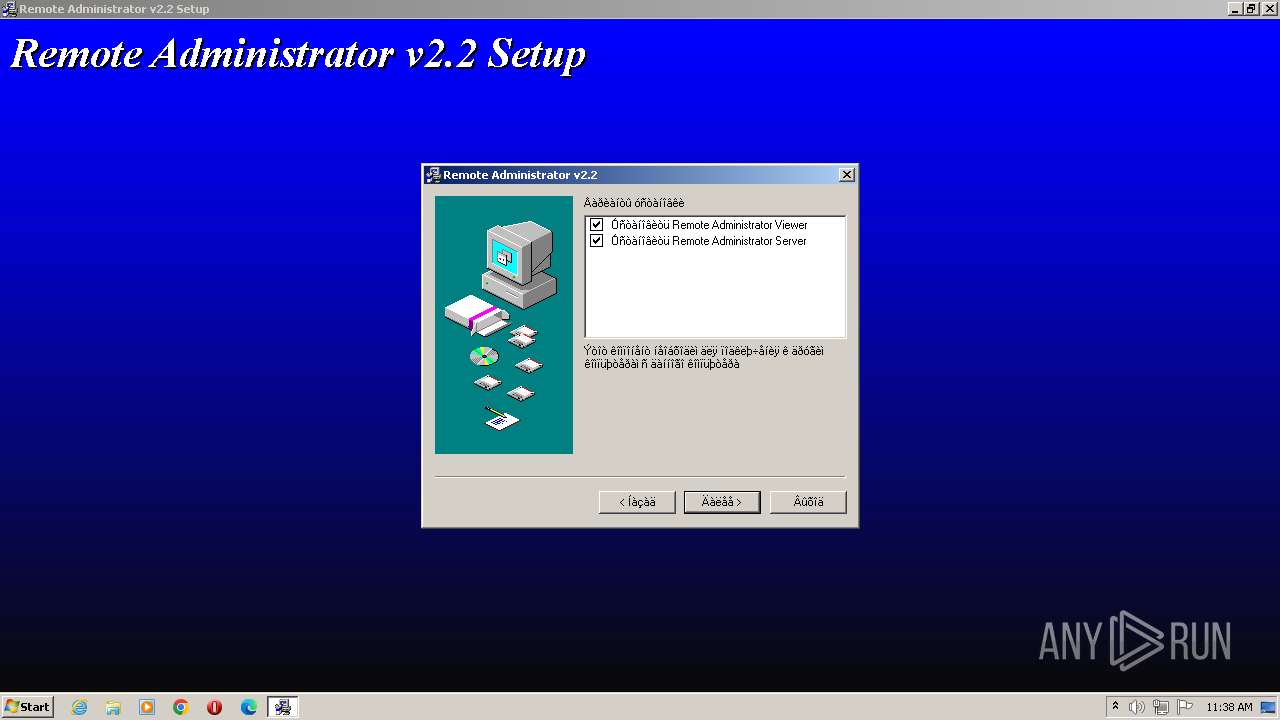
| Verdict: | Malicious activity |
| Analysis date: | August 24, 2023, 10:37:49 |
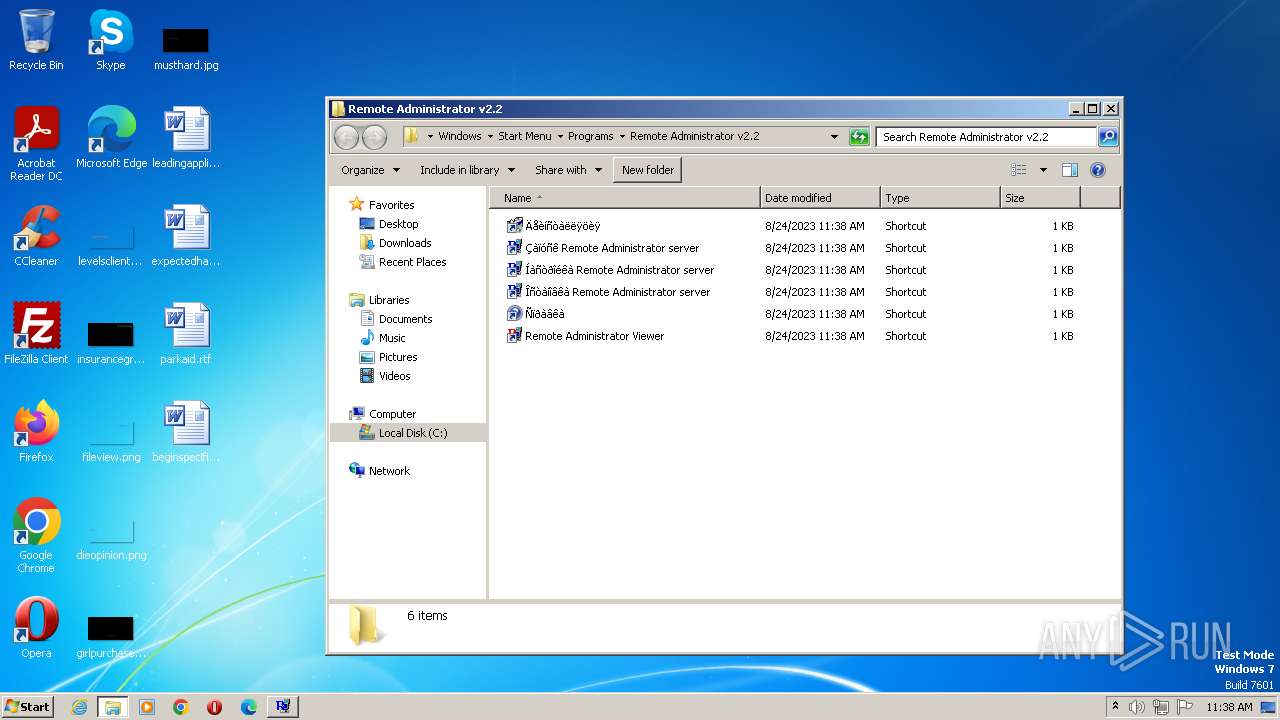
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D71470833BBF70CC97B082FB86E9899E |
| SHA1: | A1A6A9AF5053471085D98FE079B7017C7A992EDD |
| SHA256: | 101FB872A1114015A4FE6341E95CCB2250E2BFA3476EAD0B15BE68A7F6D6183A |
| SSDEEP: | 49152:jbYJ8gRB64LM3og0CKzCK9hnlTaBewulyRIlJwQ4oGURi:oJBBRY47CKD9HkU3z8 |
MALICIOUS
Loads dropped or rewritten executable
- RADMIN22.EXE (PID: 2708)
Application was dropped or rewritten from another process
- r_server.exe (PID: 2844)
- r_server.exe (PID: 3580)
Creates a writable file the system directory
- RADMIN22.EXE (PID: 2708)
SUSPICIOUS
Executable content was dropped or overwritten
- RADMIN22.EXE (PID: 2708)
INFO
Checks supported languages
- r_server.exe (PID: 2844)
- RADMIN22.EXE (PID: 2708)
- r_server.exe (PID: 3580)
Reads the computer name
- r_server.exe (PID: 2844)
- RADMIN22.EXE (PID: 2708)
- r_server.exe (PID: 3580)
Creates files in the program directory
- RADMIN22.EXE (PID: 2708)
Reads the machine GUID from the registry
- r_server.exe (PID: 2844)
- RADMIN22.EXE (PID: 2708)
- r_server.exe (PID: 3580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (50.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (32.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.6) |
| .exe | | | Win32 Executable (generic) (5.2) |
| .exe | | | Generic Win/DOS Executable (2.3) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1020 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4608 |
| CodeSize: | 2560 |
| LinkerVersion: | 3 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 1999:10:06 10:33:39+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Oct-1999 10:33:39 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 06-Oct-1999 10:33:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000009F8 | 0x00000A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.27597 |
.rdata | 0x00002000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0407808 |
.data | 0x00003000 | 0x0000025C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.07382 |
.idata | 0x00004000 | 0x000002FE | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.83057 |
.Shared | 0x00005000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED, IMAGE_SCN_MEM_WRITE | 0.0659144 |
.rsrc | 0x00006000 | 0x0000039C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.189 |
.reloc | 0x00007000 | 0x000001B2 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.36734 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.38813 | 744 | UNKNOWN | English - United States | RT_ICON |
101 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
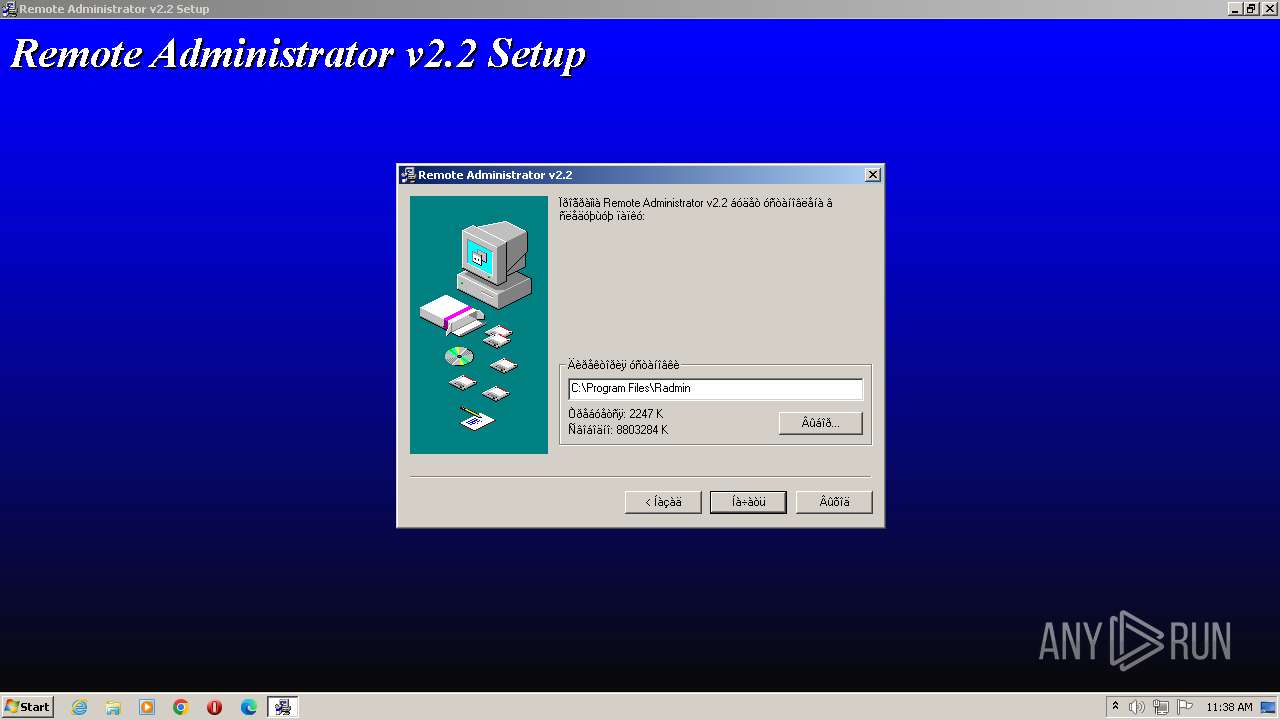
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2708 | "C:\Users\admin\AppData\Local\Temp\RADMIN22.EXE" | C:\Users\admin\AppData\Local\Temp\RADMIN22.EXE | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2844 | "C:\Program Files\Radmin\r_server.exe" /stop | C:\Program Files\Radmin\r_server.exe | — | RADMIN22.EXE | |||||||||||
User: admin Integrity Level: HIGH Description: Remote control tool Exit code: 1 Version: 2, 2, 0, 0 Modules
| |||||||||||||||
| 3500 | "C:\Users\admin\AppData\Local\Temp\RADMIN22.EXE" | C:\Users\admin\AppData\Local\Temp\RADMIN22.EXE | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
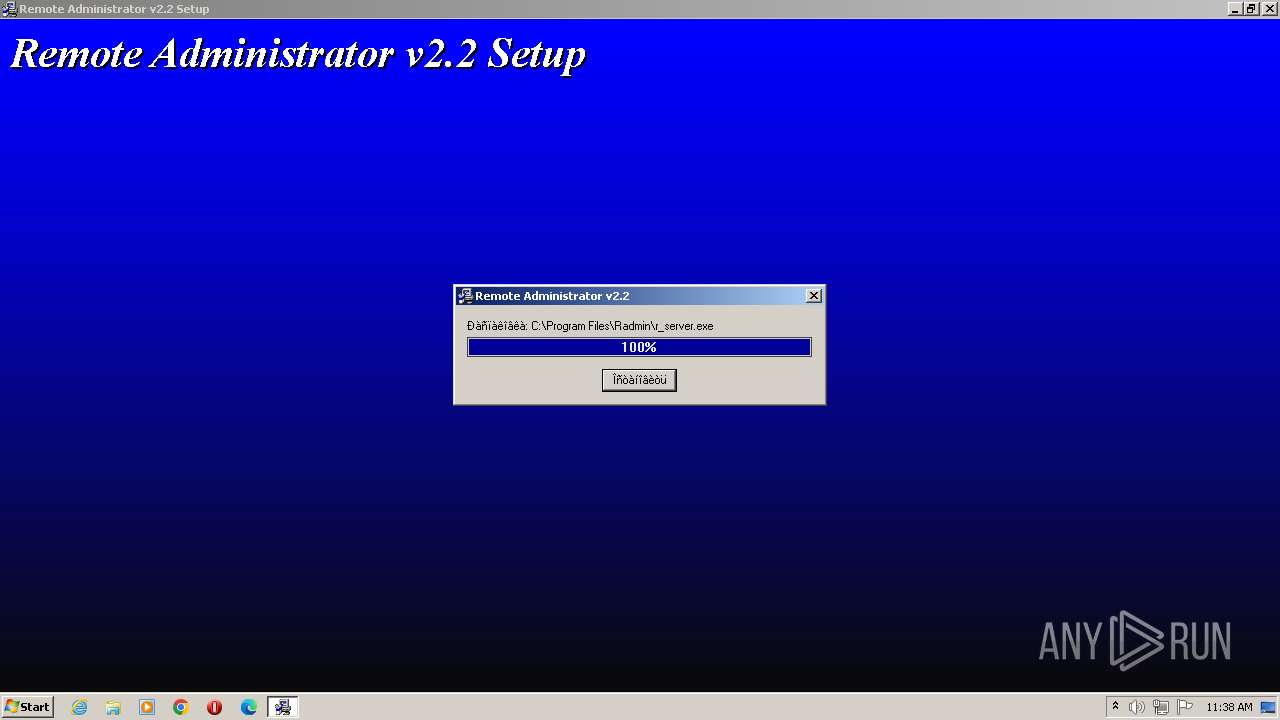
| 3580 | C:\Windows\system32\r_server.exe /intsetup | C:\Windows\System32\r_server.exe | — | RADMIN22.EXE | |||||||||||
User: admin Integrity Level: HIGH Description: Remote control tool Exit code: 0 Version: 2, 2, 0, 0 Modules
| |||||||||||||||
Total events
1 193
Read events
1 193
Write events
0
Delete events
0
Modification events
Executable files
8
Suspicious files
8
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
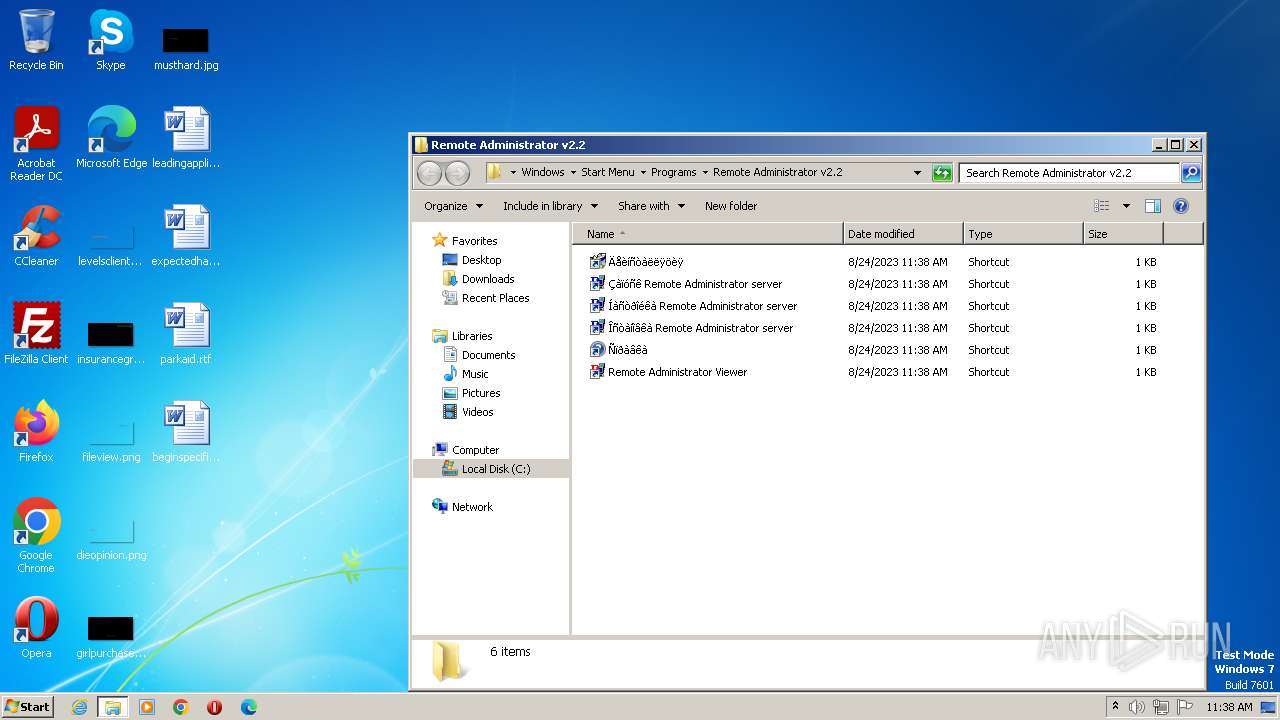
| 2708 | RADMIN22.EXE | C:\Program Files\Radmin\radmin.exe | executable | |
MD5:EC4EA16E47CF556BD6CCB7A7E74A80D2 | SHA256:E8FD3F4B61A48A35F0CAC95E9A8A7210A8A6D02DB4B4B00107833124013B94E5 | |||
| 2708 | RADMIN22.EXE | C:\Program Files\Radmin\help.hlp | binary | |
MD5:00BA4056D431B646807AE0A184B0C350 | SHA256:259E82F8C07FFBC27A29E435180E2C7F4C92233492F7FA1F3B72A359A56C1EB5 | |||
| 2708 | RADMIN22.EXE | C:\ginstall.dll | executable | |
MD5:38A9142BA7B74DB9A68B3691C970BD89 | SHA256:ED866C7802EDC00235BD25AA2AE2EC6658EB8CB74301B930A96AB9AB42ED93A2 | |||
| 2708 | RADMIN22.EXE | C:\Program Files\Radmin\1049.lng | executable | |
MD5:6531CE0B4AB7F56EFBF02E2C7AAAD7AB | SHA256:9B6E5D25630C23651E2FDC5FA2ED8724423E849BD5EF9D98F1EE488CD021D808 | |||
| 2708 | RADMIN22.EXE | C:\Program Files\Radmin\license.txt | text | |
MD5:18B4690037A291B129471EAF1C3BE679 | SHA256:F1014D4F8C89DC43727AD06DC7E8293E00A85A54D8CEC052A072DF41A6BFE672 | |||
| 2708 | RADMIN22.EXE | C:\temp\Default.bmp | binary | |
MD5:F372B11FF99BFFED4CD279C0155ADEDE | SHA256:D9D5E28EB445E7986BDEF4D409868AF205D525F2F0729427DFE3E33A7251B15D | |||
| 2708 | RADMIN22.EXE | C:\temp\license.txt | text | |
MD5:18B4690037A291B129471EAF1C3BE679 | SHA256:F1014D4F8C89DC43727AD06DC7E8293E00A85A54D8CEC052A072DF41A6BFE672 | |||
| 2708 | RADMIN22.EXE | C:\Program Files\Radmin\help.cnt | text | |
MD5:37FC4286E91747AE742E6AA717C9FAC4 | SHA256:4B130DB1982D312BE315A41362CDFC1FAFFD27F4CE7448B6FDBCBBD62820AED8 | |||
| 2708 | RADMIN22.EXE | C:\temp\0readme.txt | text | |
MD5:3DDAFF138F4C0260ACBD50E43982FF65 | SHA256:BC863F514B44E12050E6C85453D9C4B292B871E49C6AC6DD2998D28EED5640BB | |||
| 2708 | RADMIN22.EXE | C:\Program Files\Radmin\readme.txt | text | |
MD5:9411A07C4B503F3D736C7FED42069F1B | SHA256:9B19BA9D49B4E7219776B2039B5E66655EAFD2154125D2D3492D92A5F3C05812 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |