| File name: | f0418184.dll |
| Full analysis: | https://app.any.run/tasks/4fe00cf6-e32b-4f4e-a9f2-a184c6fa6999 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 18:19:39 |
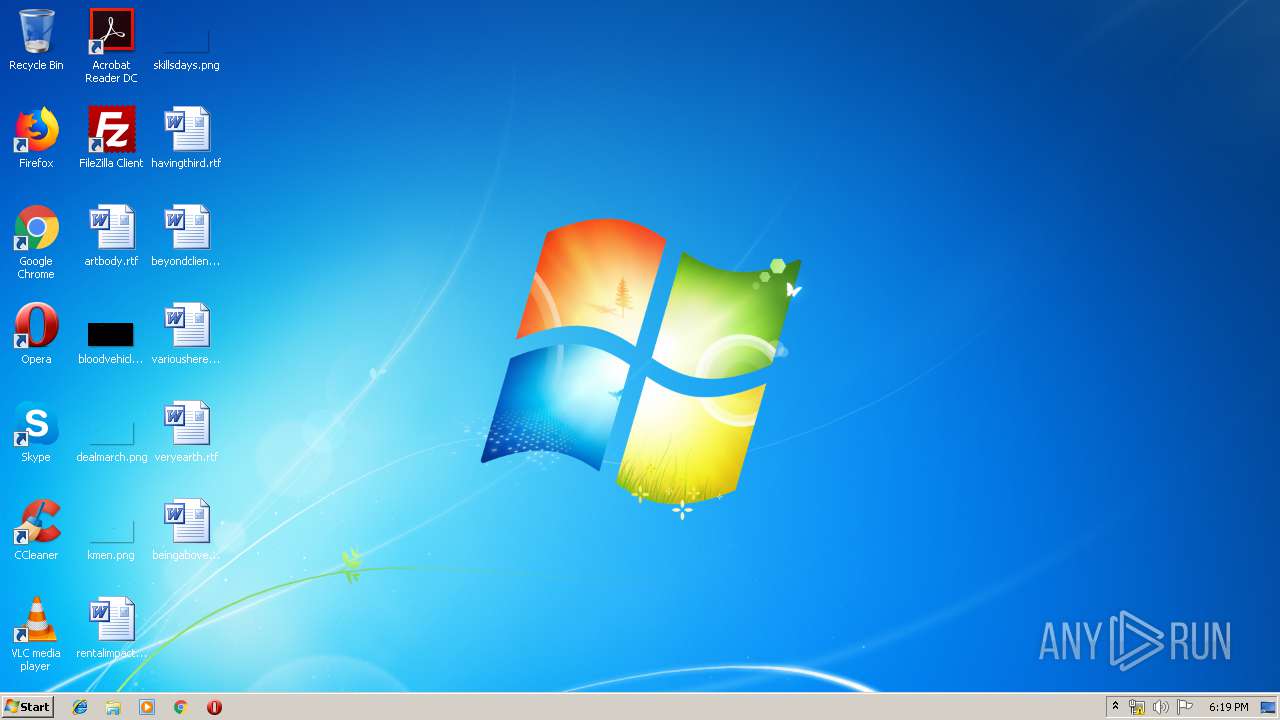
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 0D5EA703418FC342FDD262586466135B |
| SHA1: | C37F6859354910D762AEDDF362D86C7A26CA39A5 |
| SHA256: | 101E5870564E81B4111A0B6D55B3C444F15E6C6BBE1BF73B4AE4BE72D760301C |
| SSDEEP: | 1536:by81P3/cRbnmKSuL4muVMry33ASbR2JMxK5JuOESigMgkopUrFU5nKG+XTicLCRL:bjl3Sn1Si4muVMs3ASb4ys5JBx/pUpUp |
MALICIOUS
Runs injected code in another process
- rundll32.exe (PID: 748)
Application was injected by another process
- explorer.exe (PID: 352)
Changes appearance of the explorer extensions
- rundll32.exe (PID: 748)
Loads dropped or rewritten executable
- explorer.exe (PID: 352)
Changes the autorun value in the registry
- explorer.exe (PID: 352)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 352)
Uses NETSH.EXE for network configuration
- explorer.exe (PID: 352)
Executed via COM
- explorer.exe (PID: 2260)
Executable content was dropped or overwritten
- explorer.exe (PID: 352)
Reads Internet Cache Settings
- explorer.exe (PID: 352)
Checks for external IP
- explorer.exe (PID: 352)
INFO
Loads main object executable
- rundll32.exe (PID: 748)
Reads settings of System Certificates
- explorer.exe (PID: 352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (38.2) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (37.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.2) |
| .exe | | | Win32 Executable (generic) (6.3) |
| .exe | | | Clipper DOS Executable (2.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1999:10:13 18:01:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 81920 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 20480 |
| EntryPoint: | 0x19aa0 |
| OSVersion: | 4 |
| ImageVersion: | 5.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Oct-1999 16:01:44 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 13-Oct-1999 16:01:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00005000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00006000 | 0x00014000 | 0x00013E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.79202 |
UPX2 | 0x0001A000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.66952 |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.DLL |
MSVCRT.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
37
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\f0418184.dll.exe", DllMain | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2260 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2764 | netsh interface tcp set global autotuning=disabled | C:\Windows\system32\netsh.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
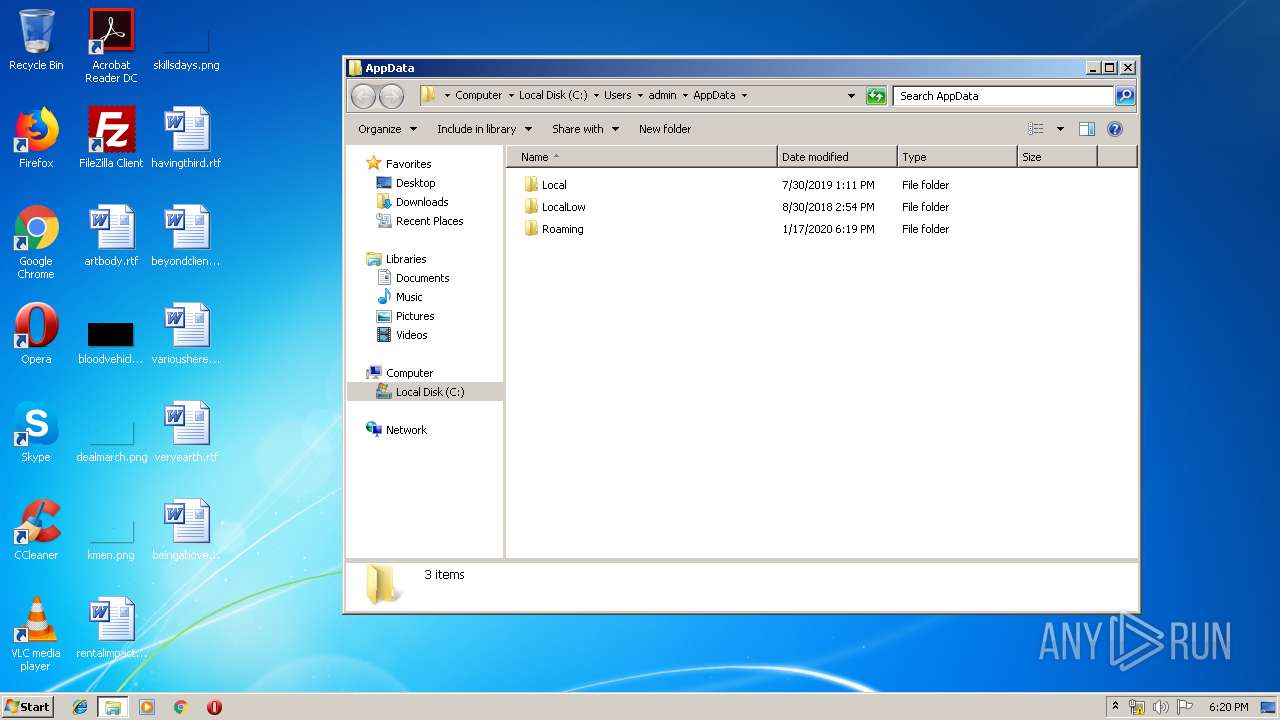
| 3812 | explorer C:\Users\admin\AppData | C:\Windows\explorer.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
777
Read events
661
Write events
116
Delete events
0
Modification events
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | iowmjosoi |
Value: rundll32.exe "C:\Users\admin\AppData\Roaming\hmcencx.dll",bpbudske | |||
| (PID) Process: | (2764) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2764) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (2764) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (2764) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (2764) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (2764) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
| (PID) Process: | (2764) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2764) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2764) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 352 | explorer.exe | C:\Users\admin\AppData\Roaming\hmcencx.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
4
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
352 | explorer.exe | GET | 301 | 104.28.24.179:80 | http://www.whatismyip.org/ | US | — | — | suspicious |
352 | explorer.exe | GET | 200 | 216.146.43.70:80 | http://checkip.dyndns.org/ | US | html | 106 b | shared |
352 | explorer.exe | GET | 200 | 35.186.238.101:80 | http://www.whatsmyipaddress.com/ | US | html | 800 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
352 | explorer.exe | 35.186.238.101:80 | www.whatsmyipaddress.com | Google Inc. | US | whitelisted |
352 | explorer.exe | 104.28.24.179:80 | www.whatismyip.org | Cloudflare Inc | US | shared |
352 | explorer.exe | 104.28.24.179:443 | www.whatismyip.org | Cloudflare Inc | US | shared |
352 | explorer.exe | 216.146.43.70:80 | checkip.dyndns.org | Dynamic Network Services, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.whatsmyipaddress.com |
| whitelisted |
www.getmyip.org |
| malicious |
www.whatismyip.org |
| suspicious |
checkip.dyndns.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
352 | explorer.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (whatismyip .org) |
352 | explorer.exe | Attempted Information Leak | ET POLICY IP Check Domain (whatismyip in HTTP Host) |
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.dyndns. Domain |
1080 | svchost.exe | Misc activity | AV INFO Query to checkip.dyndns. Domain |
352 | explorer.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup - checkip.dyndns.org |
352 | explorer.exe | Potentially Bad Traffic | ET POLICY DynDNS CheckIp External IP Address Server Response |