| download: | MSPA4NCentral-7.00.17-20200715.exe |
| Full analysis: | https://app.any.run/tasks/f0bcbbbc-5865-4aa3-875b-6a000e3bac5b |
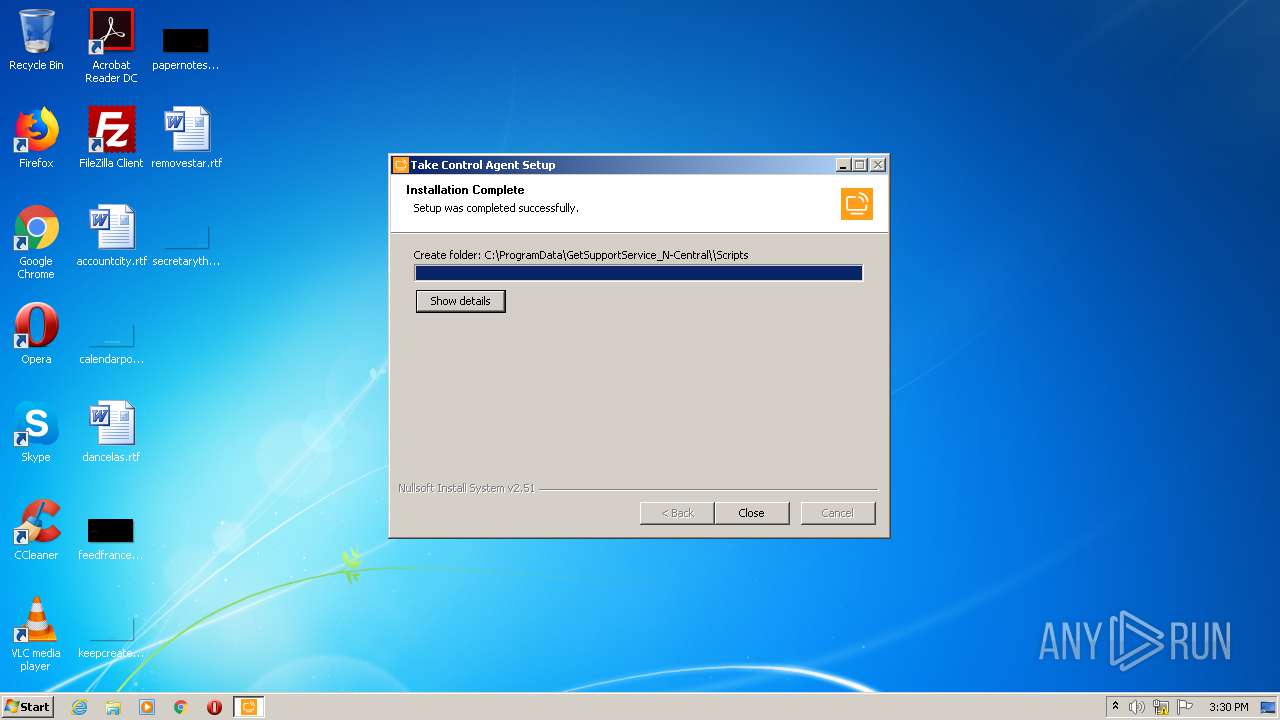
| Verdict: | Malicious activity |
| Analysis date: | August 31, 2020, 14:28:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
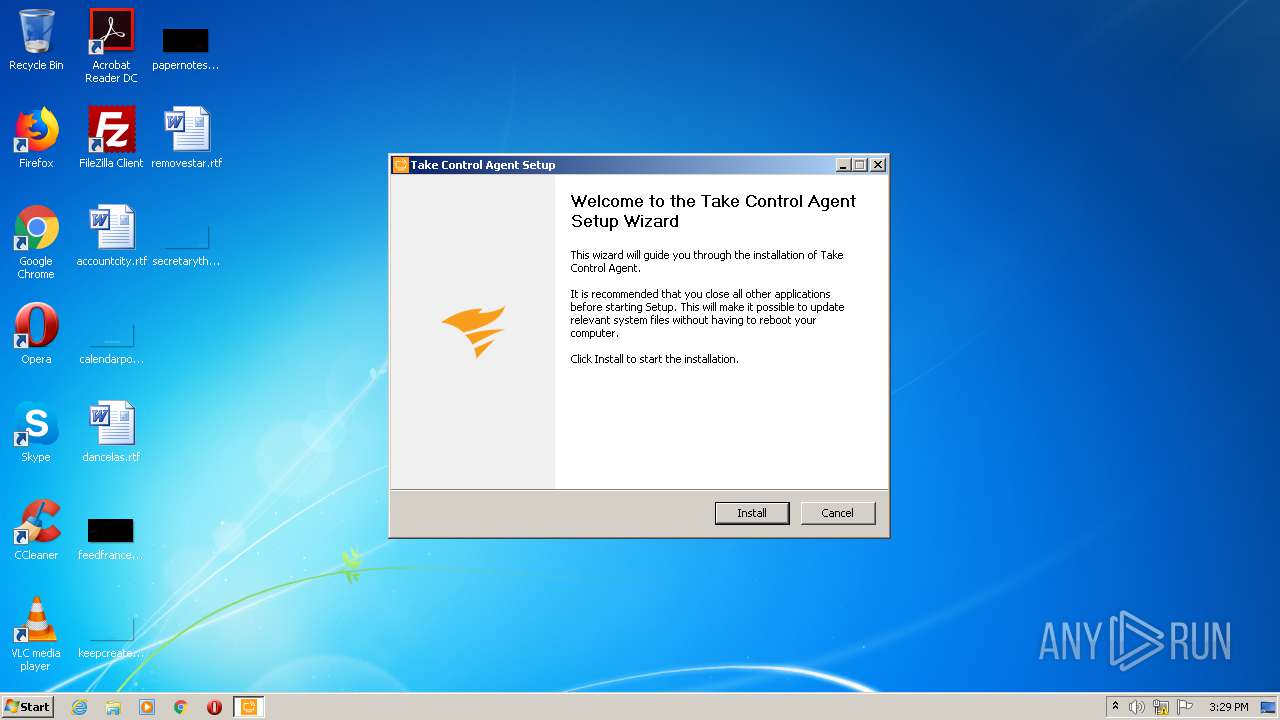
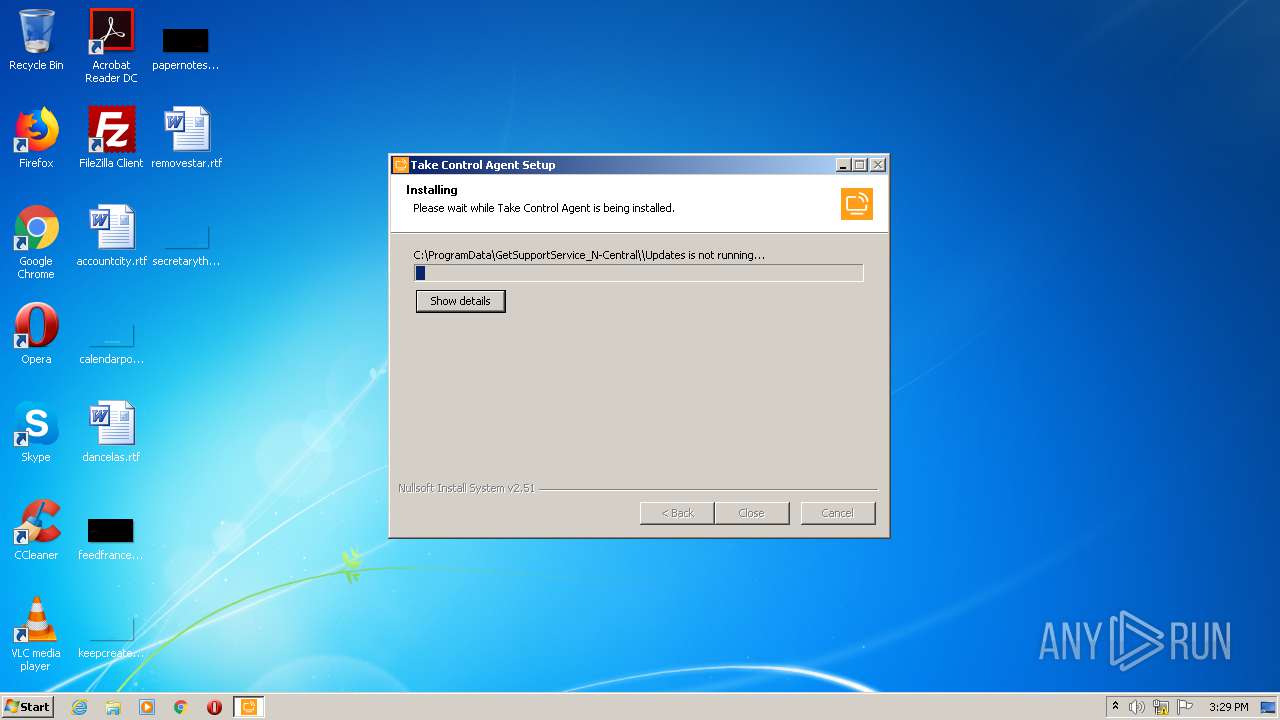
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A2B3A80D319D6958E4D6A76DA69A4E57 |
| SHA1: | 8DE22444F2FCE5BF467D0CBE0E719CA9E59632BD |
| SHA256: | 100DF140988F08CE19D644F26803359A565778296A63DD6170F88FCFE73B727B |
| SSDEEP: | 196608:+yW+JbqhUIIVuSUX2+/iZwnzAHVKExlryD97cjqtVXDdcMupi0NxKkd1zAG+7bpI:+y7JbqhCxwUGiByDXHDeh5xKwxIK1R |
MALICIOUS
Loads dropped or rewritten executable
- MSPA4NCentral-7.00.17-20200715.exe (PID: 2360)
- BASupSrvc.exe (PID: 2320)
- BASupSrvcCnfg.exe (PID: 3328)
Application was dropped or rewritten from another process
- BASupSrvc.exe (PID: 2320)
- BASupSrvcCnfg.exe (PID: 3328)
Changes the autorun value in the registry
- MSPA4NCentral-7.00.17-20200715.exe (PID: 2360)
Changes settings of System certificates
- MSPA4NCentral-7.00.17-20200715.exe (PID: 2360)
SUSPICIOUS
Creates files in the program directory
- BASupSrvc.exe (PID: 2320)
- MSPA4NCentral-7.00.17-20200715.exe (PID: 2360)
Creates COM task schedule object
- MSPA4NCentral-7.00.17-20200715.exe (PID: 2360)
Creates files in the Windows directory
- MSPA4NCentral-7.00.17-20200715.exe (PID: 2360)
Creates or modifies windows services
- BASupSrvc.exe (PID: 2320)
Adds / modifies Windows certificates
- MSPA4NCentral-7.00.17-20200715.exe (PID: 2360)
Reads Internet Cache Settings
- MSPA4NCentral-7.00.17-20200715.exe (PID: 2360)
Executable content was dropped or overwritten
- MSPA4NCentral-7.00.17-20200715.exe (PID: 2360)
INFO
Reads settings of System Certificates
- MSPA4NCentral-7.00.17-20200715.exe (PID: 2360)
Dropped object may contain Bitcoin addresses
- MSPA4NCentral-7.00.17-20200715.exe (PID: 2360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 05:20:09+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x326c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.17.0 |
| ProductVersionNumber: | 7.0.17.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| Comments: | - |
| CompanyName: | Solarwinds N-able |
| FileDescription: | Solarwinds N-able MSP Anywhere for N-central |
| FileVersion: | 7.00.17 |
| LegalCopyright: | © Solarwinds N-able |
| LegalTrademarks: | - |
| ProductName: | Solarwinds N-able MSP Anywhere for N-central |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 03:20:09 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Solarwinds N-able |
| FileDescription: | Solarwinds N-able MSP Anywhere for N-central |
| FileVersion: | 7.00.17 |
| LegalCopyright: | © Solarwinds N-able |
| LegalTrademarks: | - |
| ProductName: | Solarwinds N-able MSP Anywhere for N-central |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Apr-2016 03:20:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C74 | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41039 |
.rdata | 0x00007000 | 0x00001196 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.20374 |
.data | 0x00009000 | 0x0001B058 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.13053 |
.ndata | 0x00025000 | 0x0000B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00030000 | 0x00048660 | 0x00048800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.99933 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21417 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.30735 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 2.25928 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 2.60413 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 2.17171 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 1.71938 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 2.80408 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.71787 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
41
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2320 | "C:\Program Files\BeAnywhere Support Express\GetSupportService_N-Central\BASupSrvc.exe" /install /silent | C:\Program Files\BeAnywhere Support Express\GetSupportService_N-Central\BASupSrvc.exe | — | MSPA4NCentral-7.00.17-20200715.exe | |||||||||||
User: admin Company: SolarWinds Take Control Integrity Level: HIGH Description: SolarWinds Take Control Agent Exit code: 0 Version: 7.0.17.1117 Modules
| |||||||||||||||
| 2360 | "C:\Users\admin\AppData\Local\Temp\MSPA4NCentral-7.00.17-20200715.exe" | C:\Users\admin\AppData\Local\Temp\MSPA4NCentral-7.00.17-20200715.exe | explorer.exe | ||||||||||||
User: admin Company: Solarwinds N-able Integrity Level: HIGH Description: Solarwinds N-able MSP Anywhere for N-central Exit code: 0 Version: 7.00.17 Modules
| |||||||||||||||
| 3328 | "C:\Program Files\BeAnywhere Support Express\GetSupportService_N-Central\BASupSrvcCnfg.exe" /setup | C:\Program Files\BeAnywhere Support Express\GetSupportService_N-Central\BASupSrvcCnfg.exe | — | MSPA4NCentral-7.00.17-20200715.exe | |||||||||||
User: admin Company: SolarWinds Take Control Integrity Level: HIGH Description: SolarWinds Take Control Agent Exit code: 0 Version: 7.0.17.1117 Modules
| |||||||||||||||
| 3644 | "C:\Users\admin\AppData\Local\Temp\MSPA4NCentral-7.00.17-20200715.exe" | C:\Users\admin\AppData\Local\Temp\MSPA4NCentral-7.00.17-20200715.exe | — | explorer.exe | |||||||||||
User: admin Company: Solarwinds N-able Integrity Level: MEDIUM Description: Solarwinds N-able MSP Anywhere for N-central Exit code: 3221226540 Version: 7.00.17 Modules
| |||||||||||||||
Total events
427
Read events
390
Write events
37
Delete events
0
Modification events
| (PID) Process: | (2360) MSPA4NCentral-7.00.17-20200715.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2360) MSPA4NCentral-7.00.17-20200715.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2360) MSPA4NCentral-7.00.17-20200715.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2360) MSPA4NCentral-7.00.17-20200715.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2360) MSPA4NCentral-7.00.17-20200715.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2360) MSPA4NCentral-7.00.17-20200715.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2360) MSPA4NCentral-7.00.17-20200715.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2360) MSPA4NCentral-7.00.17-20200715.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\139\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2360) MSPA4NCentral-7.00.17-20200715.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\8DA7F965EC5EFC37910F1C6E59FDC1CC6A6EDE16 |
| Operation: | write | Name: | Blob |
Value: 04000000010000001000000043C6BFAEECFEAD2F18C6886830FCC8E60F00000001000000200000006FC4B8AC3D2B52C08BAF56255E43D22C762962E4FACAB01ACE16D48EC008BE0A0300000001000000140000008DA7F965EC5EFC37910F1C6E59FDC1CC6A6EDE161D000000010000001000000099C508FD54CBC396CC3256BB87829AE01400000001000000140000008418CC8534ECBC0C94942E08599CC7B2104E0A0853000000010000001F000000301D301B060567810C010130123010060A2B0601040182373C0101030200C06200000001000000200000008ECDE6884F3D87B1125BA31AC3FCB13D7016DE7F57CC904FE1CB97C6AE98196E0B000000010000002200000041006D0061007A006F006E00200052006F006F007400200043004100200031000000090000000100000042000000304006082B0601050507030106082B0601050507030206082B0601050507030406082B06010505070308060A2B0601040182370A0304060A2B0601040182370A030C19000000010000001000000094BA2A8E68434595D5AFF46246C54C122000000001000000450300003082034130820229A0030201020213066C9FCF99BF8C0A39E2F0788A43E696365BCA300D06092A864886F70D01010B05003039310B3009060355040613025553310F300D060355040A1306416D617A6F6E3119301706035504031310416D617A6F6E20526F6F742043412031301E170D3135303532363030303030305A170D3338303131373030303030305A3039310B3009060355040613025553310F300D060355040A1306416D617A6F6E3119301706035504031310416D617A6F6E20526F6F74204341203130820122300D06092A864886F70D01010105000382010F003082010A0282010100B2788071CA78D5E371AF478050747D6ED8D78876F49968F7582160F97484012FAC022D86D3A0437A4EB2A4D036BA01BE8DDB48C80717364CF4EE8823C73EEB37F5B519F84968B0DED7B976381D619EA4FE8236A5E54A56E445E1F9FDB416FA74DA9C9B35392FFAB02050066C7AD080B2A6F9AFEC47198F503807DCA2873958F8BAD5A9F948673096EE94785E6F89A351C0308666A14566BA54EBA3C391F948DCFFD1E8302D7D2D747035D78824F79EC4596EBB738717F2324628B843FAB71DAACAB4F29F240E2D4BF7715C5E69FFEA9502CB388AAE50386FDBFB2D621BC5C71E54E177E067C80F9C8723D63F40207F2080C4804C3E3B24268E04AE6C9AC8AA0D0203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020186301D0603551D0E041604148418CC8534ECBC0C94942E08599CC7B2104E0A08300D06092A864886F70D01010B0500038201010098F2375A4190A11AC57651282036230EAEE628BBAAF894AE48A4307F1BFC248D4BB4C8A197F6B6F17A70C85393CC0828E39825CF23A4F9DE21D37C8509AD4E9A753AC20B6A897876444718656C8D418E3B7F9ACBF4B5A750D7052C37E8034BADE961A0026EF5F2F0C5B2ED5BB7DCFA945C779E13A57F52AD95F2F8933BDE8B5C5BCA5A525B60AF14F74BEFA3FB9F40956D3154FC42D3C7461F23ADD90F48709AD9757871D1724334756E5759C2025C266029CF2319168E8843A5D4E4CB08FB231143E843297262A1A95D5E08D490AEB8D8CE14C2D055F286F6C49343776661C0B9E841D7977860036E4A72AEA5D17DBA109E866C1B8AB95933F8EBC490BEF1B9 | |||
| (PID) Process: | (2360) MSPA4NCentral-7.00.17-20200715.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\925A8F8D2C6D04E0665F596AFF22D863E8256F3F |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000173574AF7B611CEBF4F93CE2EE40F9A20F00000001000000200000001504593902EC8A0BAB29F03BF35C3058B5FD1807A74DAB92CB61ED4A9908AFA4030000000100000014000000925A8F8D2C6D04E0665F596AFF22D863E8256F3F1D000000010000001000000052135310639A10F77F886B229B9F7AFC1400000001000000140000009C5F00DFAA01D7302B3888A2B86D4A9CF2119183620000000100000020000000568D6905A2C88708A4B3025190EDCFEDB1974A606A13C6E5290FCB2AE63EDAB553000000010000002500000030233021060B6086480186FD6E0107180330123010060A2B0601040182373C0101030200C0090000000100000054000000305206082B0601050507030106082B0601050507030206082B0601050507030306082B0601050507030406082B06010505070308060A2B0601040182370A030406082B0601050507030606082B060105050703070B000000010000006200000041006D0061007A006F006E00200053006500720076006900630065007300200052006F006F007400200043006500720074006900660069006300610074006500200041007500740068006F00720069007400790020002D002D00200047003200000019000000010000001000000014D4B19434670E6DC091D154ABB20EDC2000000001000000F3030000308203EF308202D7A003020102020100300D06092A864886F70D01010B0500308198310B30090603550406130255533110300E060355040813074172697A6F6E61311330110603550407130A53636F74747364616C6531253023060355040A131C537461726669656C6420546563686E6F6C6F676965732C20496E632E313B303906035504031332537461726669656C6420536572766963657320526F6F7420436572746966696361746520417574686F72697479202D204732301E170D3039303930313030303030305A170D3337313233313233353935395A308198310B30090603550406130255533110300E060355040813074172697A6F6E61311330110603550407130A53636F74747364616C6531253023060355040A131C537461726669656C6420546563686E6F6C6F676965732C20496E632E313B303906035504031332537461726669656C6420536572766963657320526F6F7420436572746966696361746520417574686F72697479202D20473230820122300D06092A864886F70D01010105000382010F003082010A0282010100D50C3AC42AF94EE2F5BE19975F8E8853B11F3FCBCF9F20136D293AC80F7D3CF76B763863D93660A89B5E5C0080B22F597FF687F9254386E7691B529A90E171E3D82D0D4E6FF6C849D9B6F31A56AE2BB67414EBCFFB26E31ABA1D962E6A3B5894894756FF25A093705383DA847414C3679E04683ADF8E405A1D4A4ECF43913BE756D60070CB52EE7B7DAE3AE7BC31F945F6C260CF1359022B80CC3447DFB9DE90656D02CF2C91A6A6E7DE8518497C664EA33A6DA9B5EE342EBA0D03B833DF47EBB16B8D25D99BCE81D1454632967087DE020E494385B66C73BB64EA6141ACC9D454DF872FC722B226CC9F5954689FFCBE2A2FC4551C75406017850255398B7F050203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E041604149C5F00DFAA01D7302B3888A2B86D4A9CF2119183300D06092A864886F70D01010B050003820101004B36A6847769DD3B199F6723086F0E61C9FD84DC5FD83681CDD81B412D9F60DDC71A68D9D16E86E18823CF13DE43CFE234B3049D1F29D5BFF85EC8D5C1BDEE926F3274F291822FBD82427AAD2AB7207D4DBC7A5512C215EABDF76A952E6C749FCF1CB4F2C501A385D0723EAD73AB0B9B750C6D45B78E94AC9637B5A0D08F15470EE3E883DD8FFDEF410177CC27A9628533F23708EF71CF7706DEC8191D8840CF7D461DFF1EC7E1CEFF23DBC6FA8D554EA902E74711463EF4FDBD7B2926BBA961623728B62D2AF6108664C970A7D2ADB7297079EA3CDA63259FFD68B730EC70FB758AB76D6067B21EC8B9E9D8A86F028B670D4D265771DA20FCC14A508DB128BA | |||
Executable files
98
Suspicious files
8
Text files
38
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2360 | MSPA4NCentral-7.00.17-20200715.exe | C:\Users\admin\AppData\Local\Temp\BASupSrvc.xml | — | |
MD5:— | SHA256:— | |||
| 2360 | MSPA4NCentral-7.00.17-20200715.exe | C:\Users\admin\AppData\Local\Temp\Cab8602.tmp | — | |
MD5:— | SHA256:— | |||
| 2360 | MSPA4NCentral-7.00.17-20200715.exe | C:\Users\admin\AppData\Local\Temp\Tar8603.tmp | — | |
MD5:— | SHA256:— | |||
| 2360 | MSPA4NCentral-7.00.17-20200715.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
| 2360 | MSPA4NCentral-7.00.17-20200715.exe | C:\Users\admin\AppData\Local\Temp\nst4723.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 2360 | MSPA4NCentral-7.00.17-20200715.exe | C:\Users\admin\AppData\Local\Temp\nst4723.tmp\modern-wizard.bmp | image | |
MD5:— | SHA256:— | |||
| 2360 | MSPA4NCentral-7.00.17-20200715.exe | C:\Users\admin\AppData\Local\Temp\nst4723.tmp\WinVersion.dll | executable | |
MD5:— | SHA256:— | |||
| 2360 | MSPA4NCentral-7.00.17-20200715.exe | C:\Users\admin\AppData\Local\Temp\nst4723.tmp\XMLConfigPlugIn.dll | executable | |
MD5:— | SHA256:— | |||
| 2360 | MSPA4NCentral-7.00.17-20200715.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:— | SHA256:— | |||
| 2360 | MSPA4NCentral-7.00.17-20200715.exe | C:\Users\admin\AppData\Local\Temp\nst4723.tmp\XMLCallPlugIn.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2360 | MSPA4NCentral-7.00.17-20200715.exe | GET | 200 | 143.204.208.79:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAy662yLx7LLaJbzMvCk5C0%3D | US | der | 471 b | whitelisted |
2360 | MSPA4NCentral-7.00.17-20200715.exe | GET | 200 | 13.35.253.185:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
2360 | MSPA4NCentral-7.00.17-20200715.exe | GET | 200 | 13.35.253.148:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2360 | MSPA4NCentral-7.00.17-20200715.exe | 34.200.64.61:443 | comserver.global.mspa.n-able.com | Amazon.com, Inc. | US | unknown |
2360 | MSPA4NCentral-7.00.17-20200715.exe | 143.204.208.79:80 | o.ss2.us | — | US | whitelisted |
2360 | MSPA4NCentral-7.00.17-20200715.exe | 13.35.253.148:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
2360 | MSPA4NCentral-7.00.17-20200715.exe | 13.35.253.185:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
comserver.global.mspa.n-able.com |
| unknown |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.sca1b.amazontrust.com |
| whitelisted |