| File name: | WinRAR-701.exe |
| Full analysis: | https://app.any.run/tasks/7a4c305a-62df-4507-89bf-88a333a49ae3 |
| Verdict: | Malicious activity |
| Analysis date: | December 12, 2024, 19:11:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 23385F5D8F429CF550B695FC85617715 |
| SHA1: | 771CAF448BB09CC8CED2E20B64909046D27F6D63 |
| SHA256: | 0FFFA41E4CC2D9AB93E6839483DC97523CD33920127B4B15EE4B574093C7203A |
| SSDEEP: | 98304:eoO7qljvh30eoGBePBsxDY8OtTZo+2U5dWFn7hfAd393XmOORqEBlIYwURRYuVA7:Tus0uSN |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 6844)
Bypass execution policy to execute commands
- powershell.exe (PID: 6844)
Changes powershell execution policy (Bypass)
- WinRAR-701.exe (PID: 6360)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- WinRAR-701.exe (PID: 6360)
Executable content was dropped or overwritten
- WinRAR-701.exe (PID: 6360)
- wrarinstaller.exe (PID: 7020)
The process bypasses the loading of PowerShell profile settings
- WinRAR-701.exe (PID: 6360)
The process hide an interactive prompt from the user
- WinRAR-701.exe (PID: 6360)
Starts POWERSHELL.EXE for commands execution
- WinRAR-701.exe (PID: 6360)
The process executes Powershell scripts
- WinRAR-701.exe (PID: 6360)
Drops 7-zip archiver for unpacking
- wrarinstaller.exe (PID: 7020)
Reads security settings of Internet Explorer
- wrarinstaller.exe (PID: 7020)
Searches for installed software
- Uninstall.exe (PID: 7108)
Creates a software uninstall entry
- Uninstall.exe (PID: 7108)
Reads the date of Windows installation
- wrarinstaller.exe (PID: 7020)
INFO
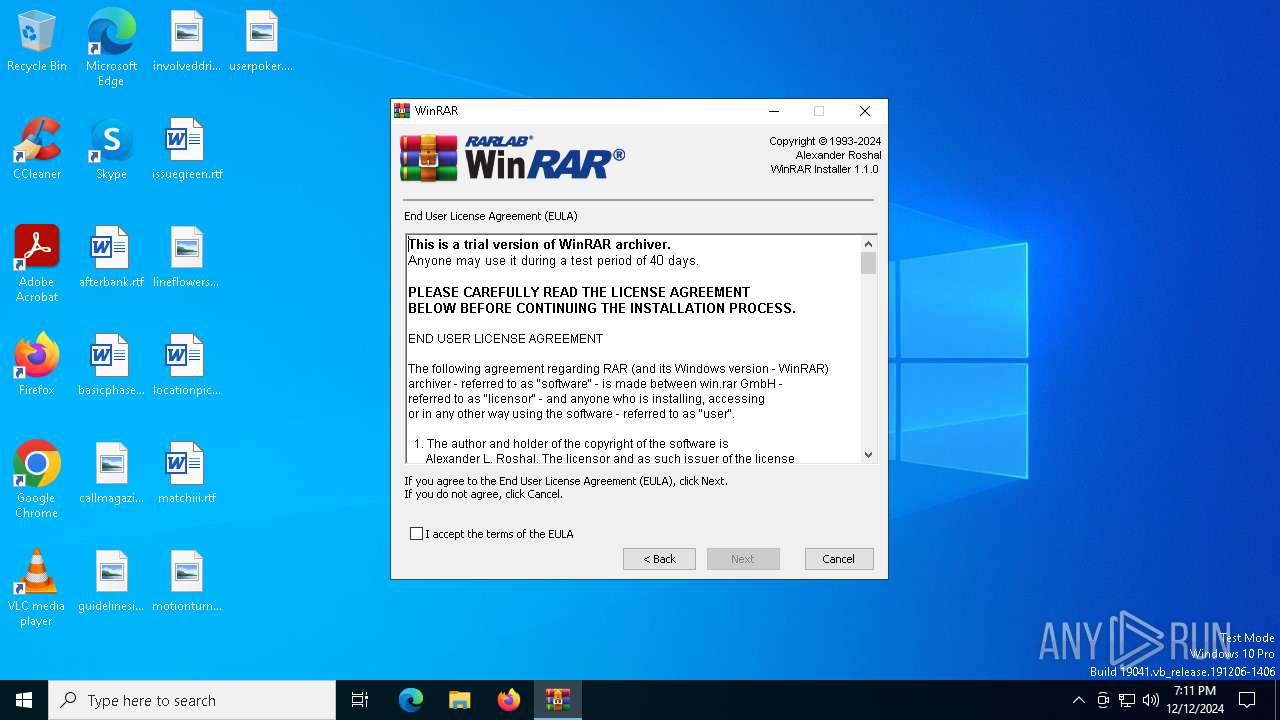
The sample compiled with english language support
- WinRAR-701.exe (PID: 6360)
- wrarinstaller.exe (PID: 7020)
Checks supported languages
- WinRAR-701.exe (PID: 6360)
- wrarinstaller.exe (PID: 7020)
- Uninstall.exe (PID: 7108)
Create files in a temporary directory
- WinRAR-701.exe (PID: 6360)
The process uses the downloaded file
- powershell.exe (PID: 6844)
Reads the computer name
- wrarinstaller.exe (PID: 7020)
- Uninstall.exe (PID: 7108)
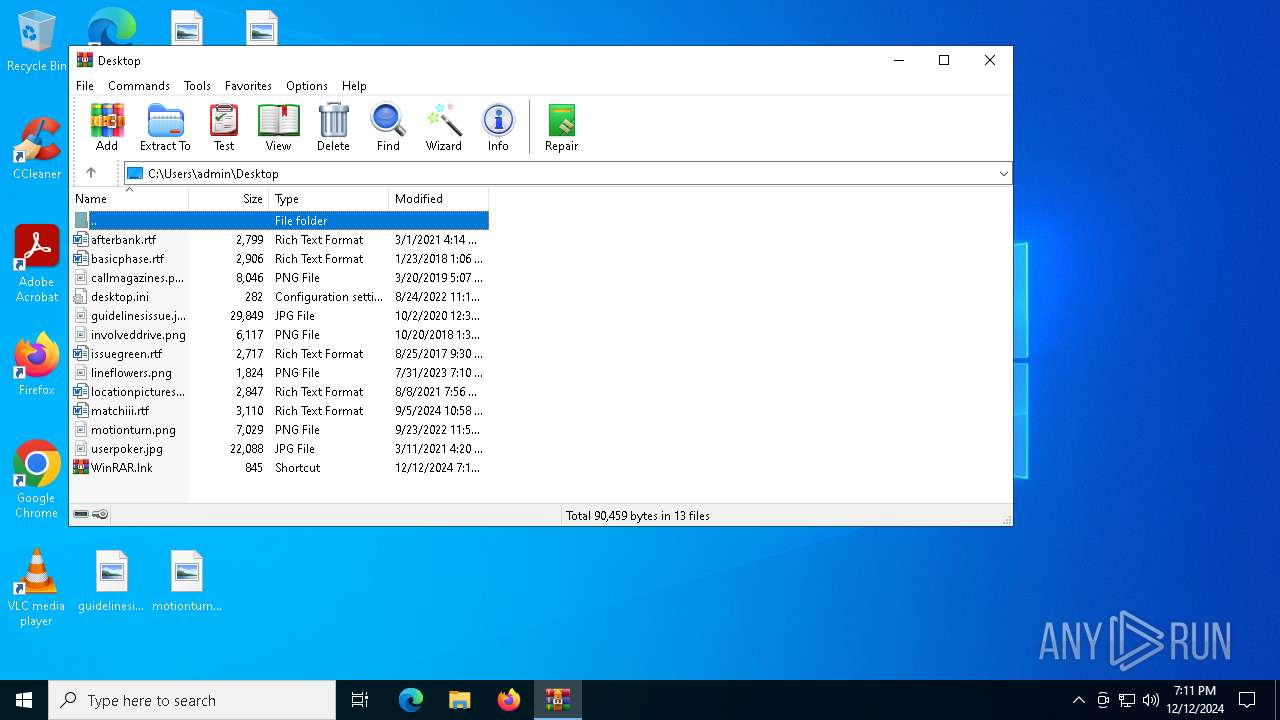
Creates files in the program directory
- wrarinstaller.exe (PID: 7020)
- Uninstall.exe (PID: 7108)
Process checks computer location settings
- wrarinstaller.exe (PID: 7020)
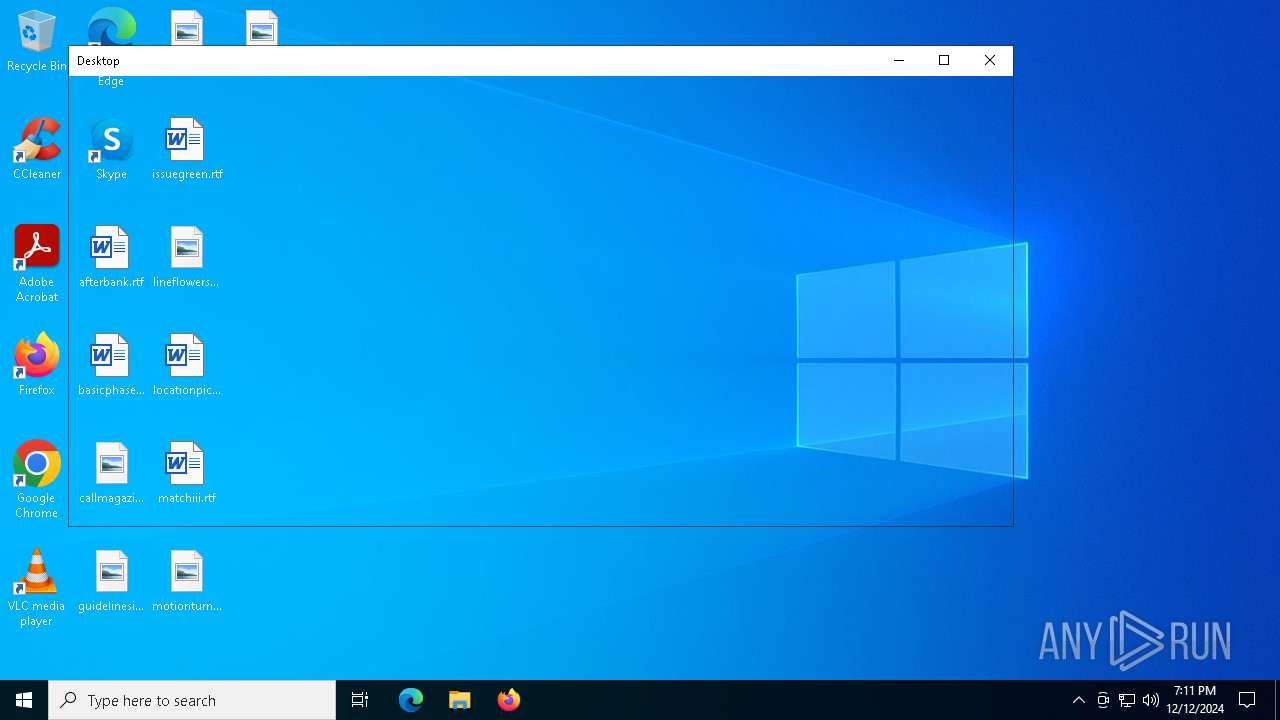
Creates files or folders in the user directory
- Uninstall.exe (PID: 7108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:16 00:50:59+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x33fa |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.3.0 |
| ProductVersionNumber: | 1.0.3.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
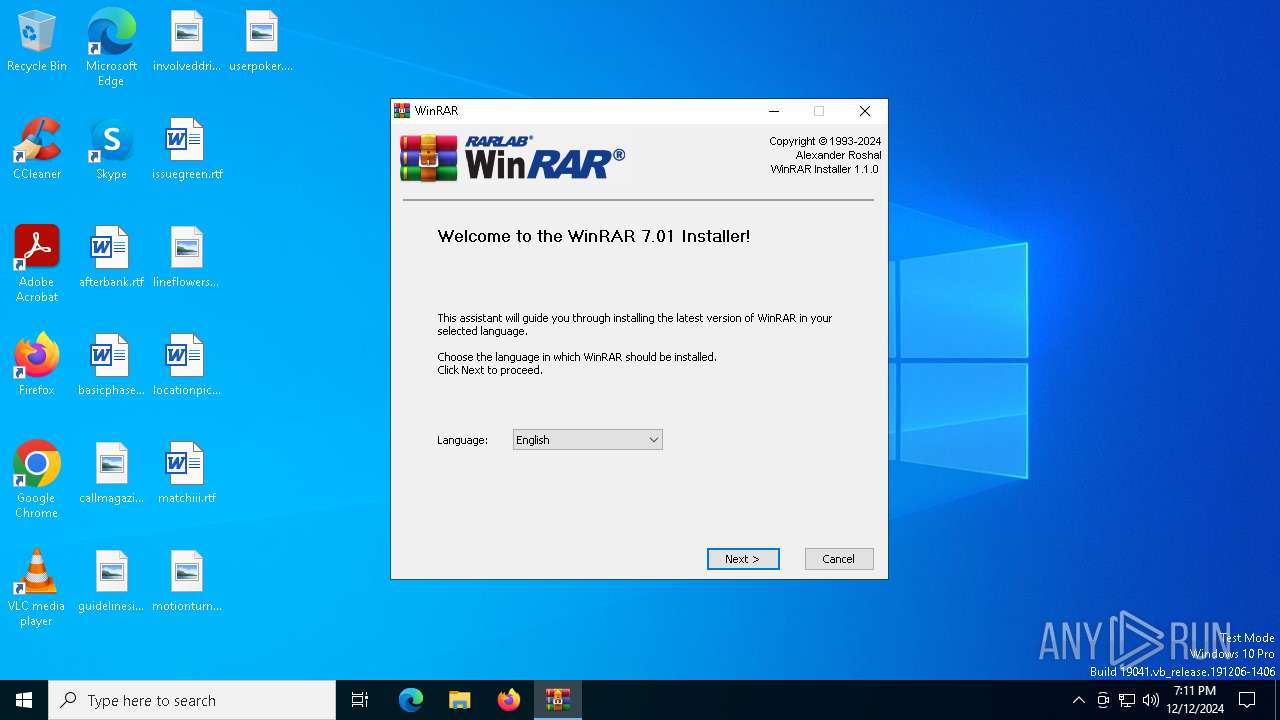
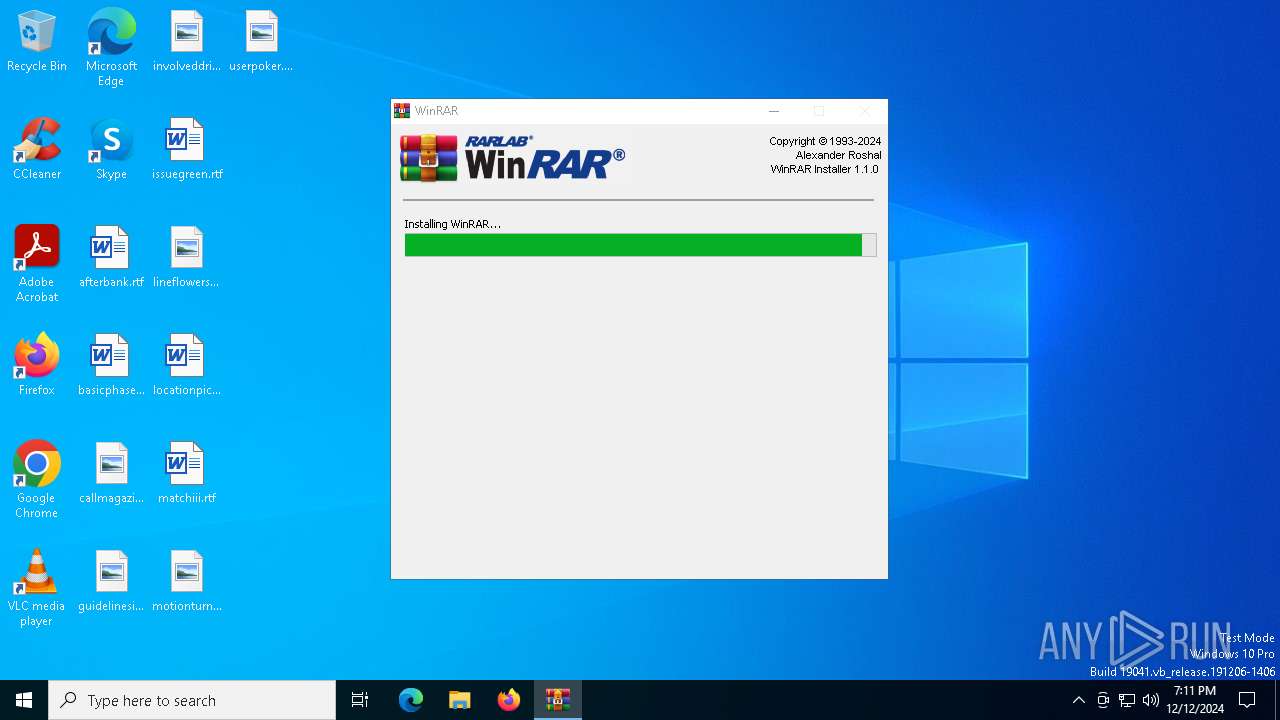
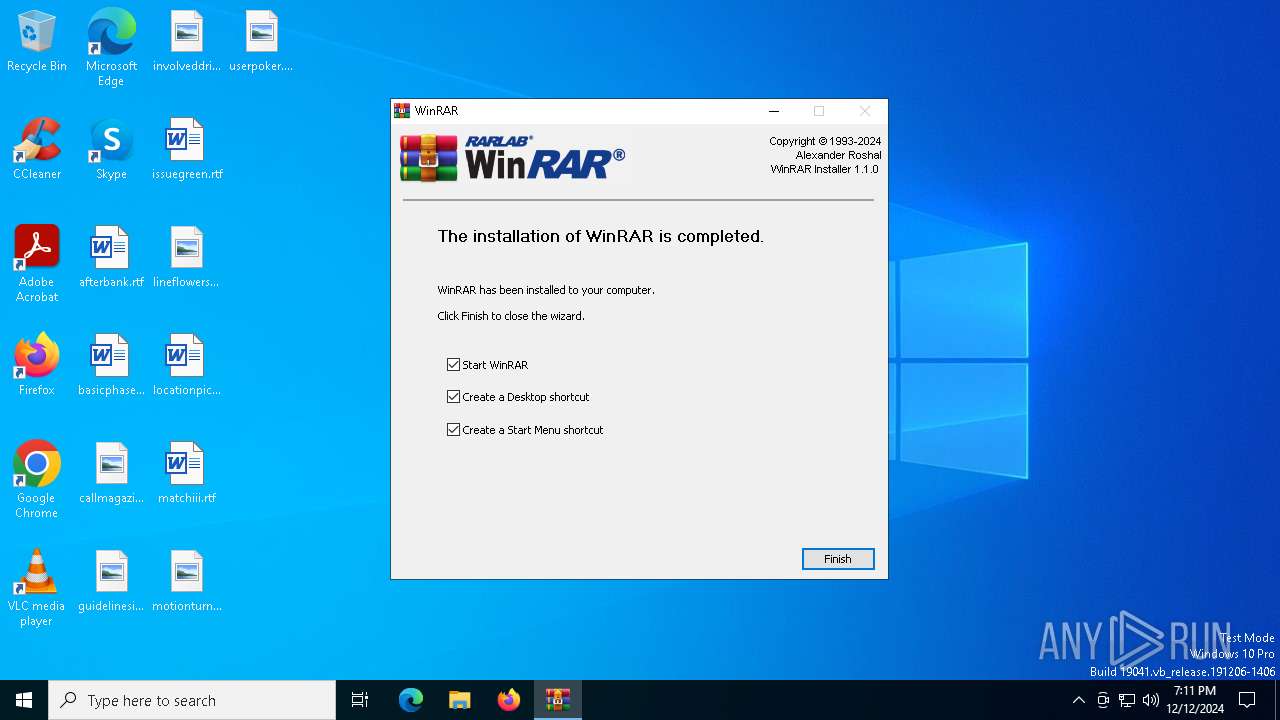
| FileDescription: | WinRAR Installer |
| FileVersion: | 1.0.3.0 |
| LegalCopyright: | Copyright © Alexander Roshal 1993-2024 |
| ProductName: | WinRAR Installer |
| ProductVersion: | 1.1.0 |
Total processes
134
Monitored processes
7
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6192 | "C:\Users\admin\AppData\Local\Temp\WinRAR-701.exe" | C:\Users\admin\AppData\Local\Temp\WinRAR-701.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WinRAR Installer Exit code: 3221226540 Version: 1.0.3.0 Modules
| |||||||||||||||
| 6344 | "C:\Program Files\WinRAR\WinRAR.exe" | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR-701.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR Version: 7.1.0 Modules
| |||||||||||||||
| 6360 | "C:\Users\admin\AppData\Local\Temp\WinRAR-701.exe" | C:\Users\admin\AppData\Local\Temp\WinRAR-701.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: WinRAR Installer Exit code: 0 Version: 1.0.3.0 Modules
| |||||||||||||||
| 6844 | powershell -noninteractive -NoProfile -ExecutionPolicy Bypass -WindowStyle Hidden -File .\script.ps1 C:\Users\admin\AppData\Local\Temp\wrtmp\wrarinstaller.exe C:\Users\admin\AppData\Local\Temp\wrtmp\downloadedCertificate.txt -FFFeatureOff | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | WinRAR-701.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6852 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7020 | "C:\Users\admin\AppData\Local\Temp\wrtmp\wrarinstaller.exe" -s1 -d"C:\Program Files\WinRAR" | C:\Users\admin\AppData\Local\Temp\wrtmp\wrarinstaller.exe | WinRAR-701.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR Exit code: 0 Version: 7.1.0 Modules
| |||||||||||||||
| 7108 | "C:\Program Files\WinRAR\uninstall.exe" /setup | C:\Program Files\WinRAR\Uninstall.exe | — | wrarinstaller.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: Uninstall WinRAR Exit code: 0 Version: 7.1.0 Modules
| |||||||||||||||
Total events
12 311
Read events
12 230
Write events
79
Delete events
2
Modification events
| (PID) Process: | (7020) wrarinstaller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR SFX |
| Operation: | write | Name: | C%%Program Files%WinRAR |
Value: C:\Program Files\WinRAR | |||
| (PID) Process: | (7108) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.rar |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (7108) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.zip |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (7108) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.cab |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (7108) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.arj |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (7108) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.lz |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (7108) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.lzh |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (7108) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.7z |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (7108) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.tar |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (7108) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.gz |
| Operation: | write | Name: | Set |
Value: 1 | |||
Executable files
23
Suspicious files
14
Text files
25
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6360 | WinRAR-701.exe | C:\Users\admin\AppData\Local\Temp\nsf58D2.tmp\InstallOptionsEx.dll | executable | |
MD5:B8C7FDA6EC3C8A8EAD7D7ECCAE0B17F7 | SHA256:B03CEDB899C8737FABB3EFB1D02BB8330EE73CE667AA406A5E52A10AFF180DB7 | |||
| 6360 | WinRAR-701.exe | C:\Users\admin\AppData\Local\Temp\nsf58D2.tmp\nsArray.dll | executable | |
MD5:DA4BC09439ED21FAF7620A53433AAC92 | SHA256:216D68D3F0B37BB2203B3A438A84A089E8C388608F46377AD7E7D6A2709CF9B0 | |||
| 6360 | WinRAR-701.exe | C:\Users\admin\AppData\Local\Temp\nsf58D2.tmp\ioSpecial.ini | text | |
MD5:C98EB8FF445544FD614C7C276F819BE7 | SHA256:6003514D0104BF7F406A451FC7872C9ADFF0045073318C2AEE60D66EC064B97B | |||
| 6360 | WinRAR-701.exe | C:\Users\admin\AppData\Local\Temp\wrtmp\cacert.pem | text | |
MD5:694CCFB21BBE1B997E3E4217D0256EBB | SHA256:1BF458412568E134A4514F5E170A328D11091E071C7110955C9884ED87972AC9 | |||
| 6360 | WinRAR-701.exe | C:\Users\admin\AppData\Local\Temp\nsf58D2.tmp\Header.bmp | image | |
MD5:6107DCFB93CAD5B9EA18A60C37E3C837 | SHA256:30B2605B256DF27BAA509EE27209CEC3F28EE1FCFE721484BC63DBE644B961BD | |||
| 6360 | WinRAR-701.exe | C:\Users\admin\AppData\Local\Temp\nsf58D2.tmp\System.dll | executable | |
MD5:8CF2AC271D7679B1D68EEFC1AE0C5618 | SHA256:6950991102462D84FDC0E3B0AE30C95AF8C192F77CE3D78E8D54E6B22F7C09BA | |||
| 6360 | WinRAR-701.exe | C:\Users\admin\AppData\Local\Temp\nsf58D2.tmp\nsisXML.dll | executable | |
MD5:C5285D861243F3B41648AF5C0FFD5678 | SHA256:35E54B12771F671BD8D9677369EB8216B54DE0608A07A92EF17A4C29A841935F | |||
| 6360 | WinRAR-701.exe | C:\Users\admin\AppData\Local\Temp\nsf58D2.tmp\nsExec.dll | executable | |
MD5:F27689C513E7D12C7C974D5F8EF710D6 | SHA256:1F18F4126124B0551F3DBCD0FEC7F34026F930CA509F04435657CEDC32AE8C47 | |||
| 6360 | WinRAR-701.exe | C:\Users\admin\AppData\Local\Temp\nsf58D2.tmp\MINIMAL.bmp | image | |
MD5:6444555530EEFC9DDCF6EAD1B8E2029E | SHA256:65754B587A6BC8E2B415F93F03997311577394558020798FE63FED2D505A953D | |||
| 6844 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dnkl5qjk.jkz.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
35
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4864 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4864 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3732 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2548 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.182:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6360 | WinRAR-701.exe | 51.195.68.163:443 | www.win-rar.com | OVH SAS | FR | whitelisted |
1176 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.win-rar.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
umami.win-rar.com |
| malicious |