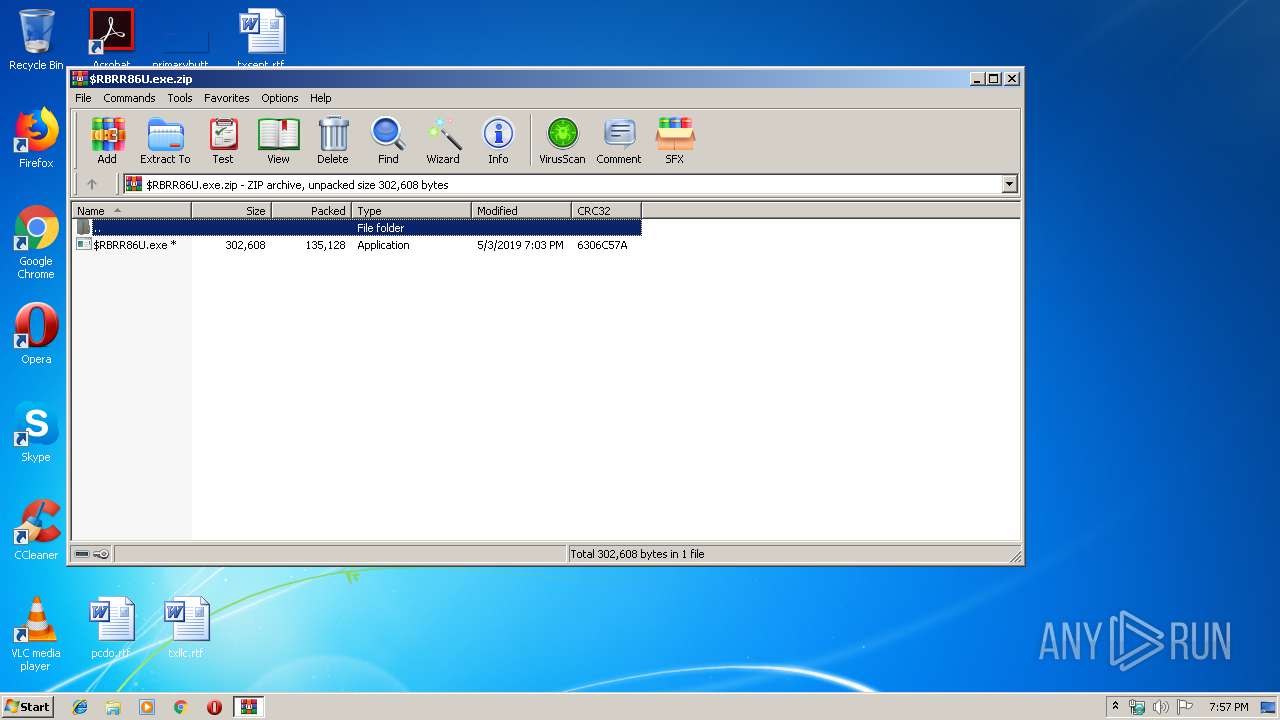
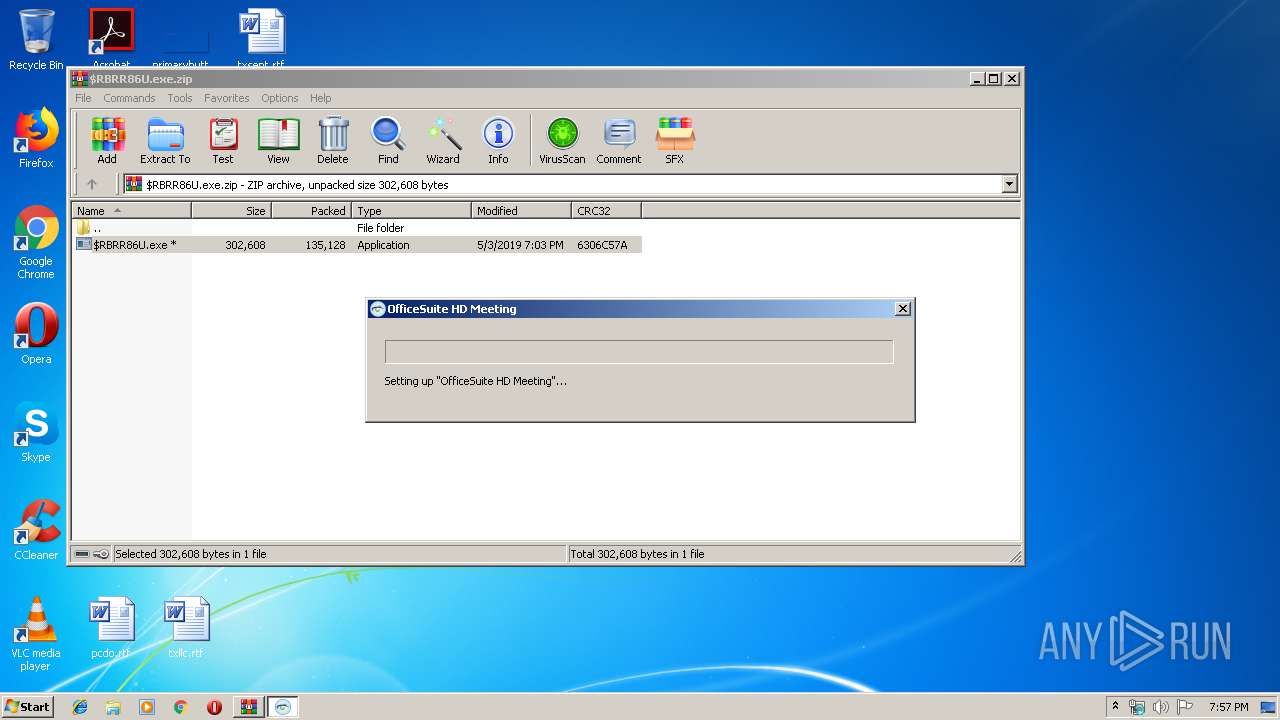
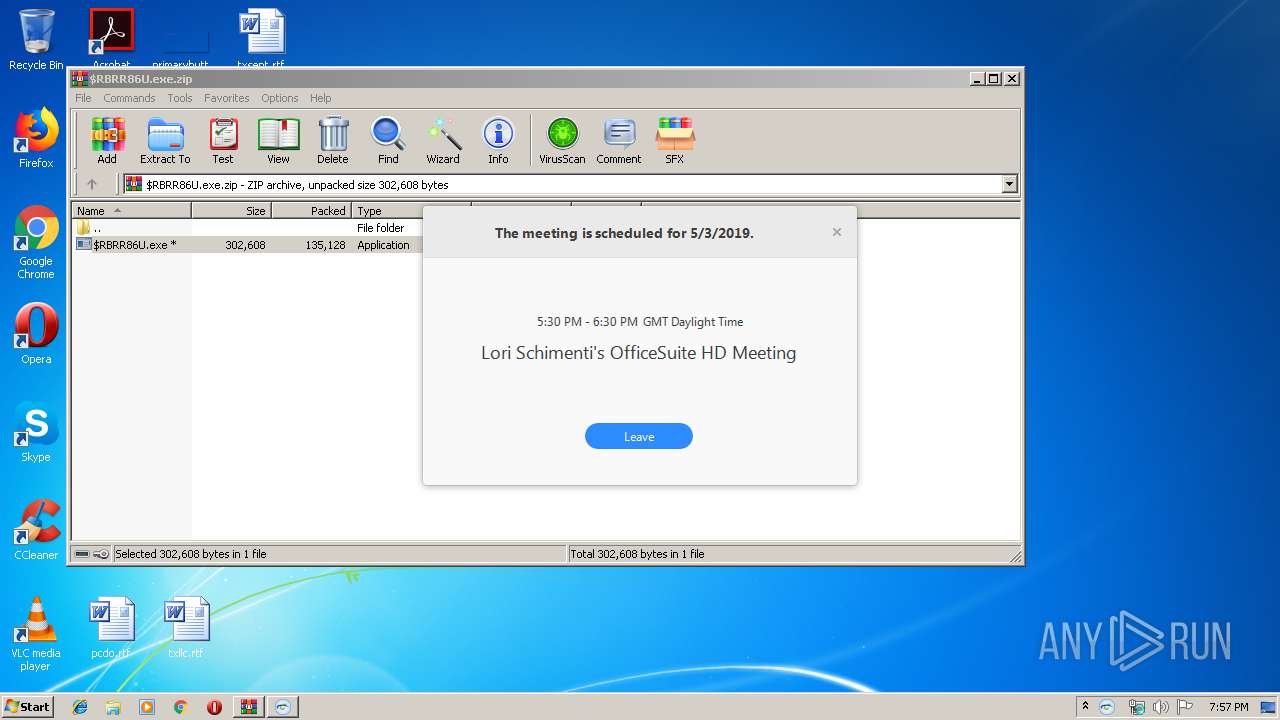
| File name: | $RBRR86U.exe.zip |
| Full analysis: | https://app.any.run/tasks/fdc3da0a-b1a9-4478-aede-9107866d0f63 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 18:56:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 395E89A948660B763D4B8DD733B98EE3 |
| SHA1: | 2F15809BF966615064A1CEE0D3F214C88BFEE148 |
| SHA256: | 0FF15B863B58C8D7C946E0ED403E01EB967FE457EE602A08FA9CEAF55DBBF39F |
| SSDEEP: | 3072:YibEhJ6de903XTzmcIrZTRAYEEO1Ce9Wj85xpiIOBWuUNR9MtaXqjW/ldlp:jbECkif0hGJy6opUVMcqolh |
MALICIOUS
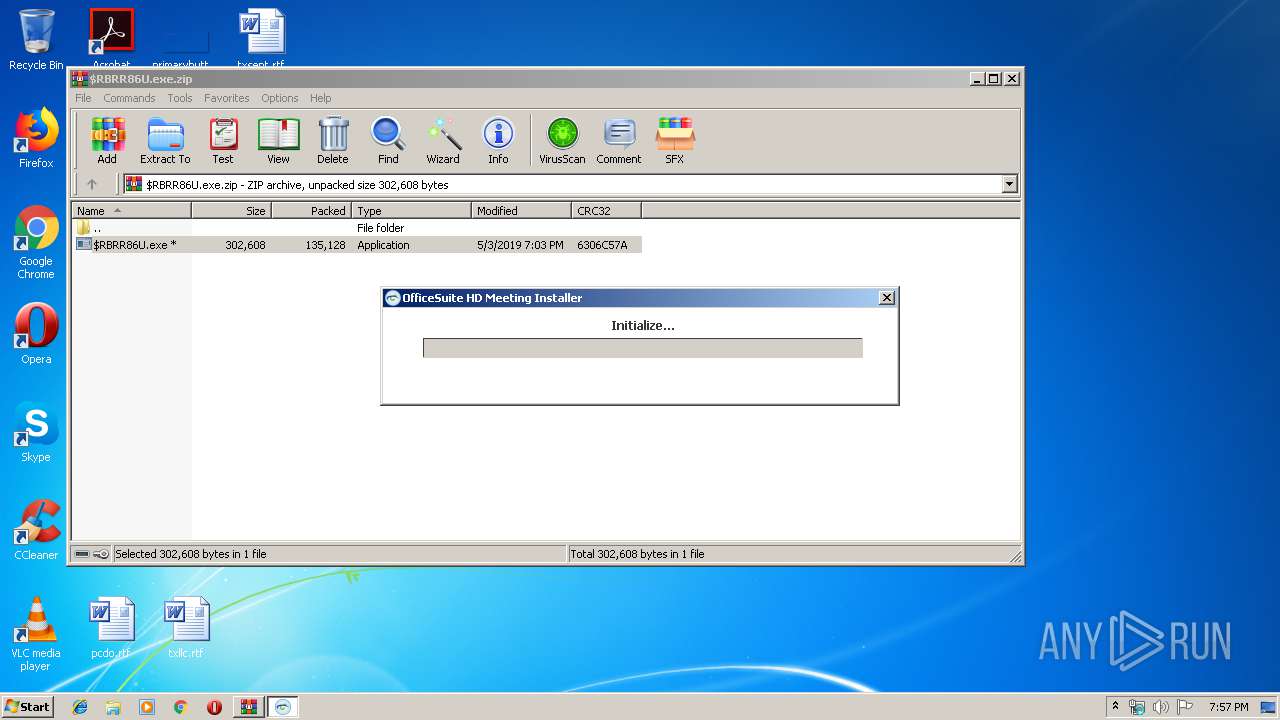
Application was dropped or rewritten from another process
- $RBRR86U.exe (PID: 3144)
- Installer.exe (PID: 2756)
- OfficeSuiteHDMeeting.exe (PID: 2596)
- OfficeSuiteHDMeeting.exe (PID: 3304)
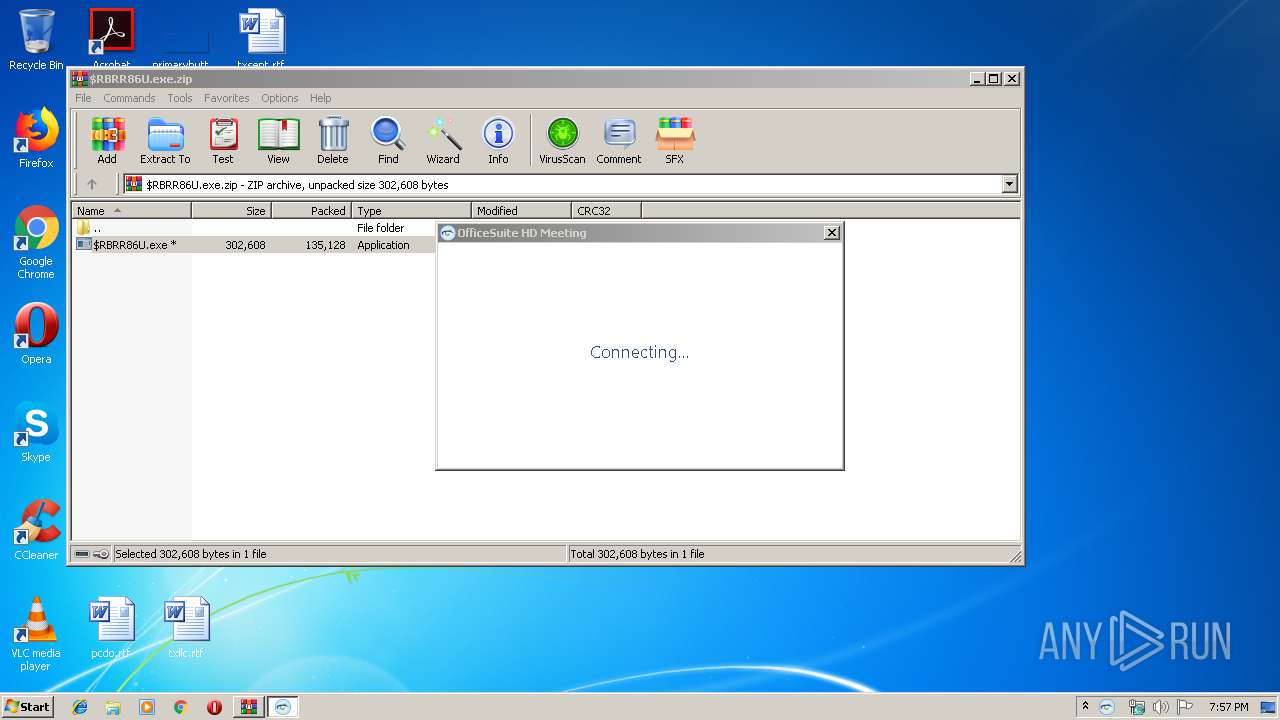
Loads dropped or rewritten executable
- OfficeSuiteHDMeeting.exe (PID: 2596)
- OfficeSuiteHDMeeting.exe (PID: 3304)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2828)
- $RBRR86U.exe (PID: 3144)
- Installer.exe (PID: 2756)
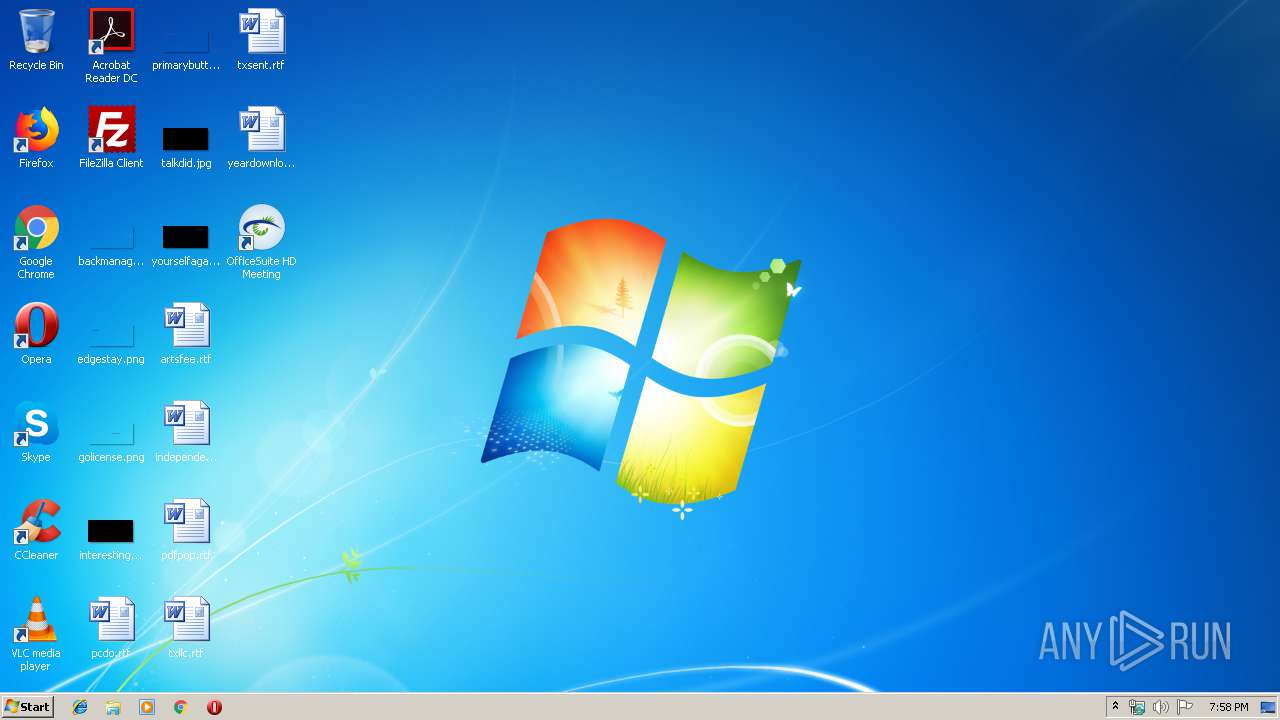
Creates files in the user directory
- $RBRR86U.exe (PID: 3144)
- OfficeSuiteHDMeeting.exe (PID: 2596)
- OfficeSuiteHDMeeting.exe (PID: 3304)
- Installer.exe (PID: 2756)
Creates a software uninstall entry
- Installer.exe (PID: 2756)
Changes IE settings (feature browser emulation)
- Installer.exe (PID: 2756)
Modifies the open verb of a shell class
- Installer.exe (PID: 2756)
Application launched itself
- OfficeSuiteHDMeeting.exe (PID: 2596)
INFO
Dropped object may contain Bitcoin addresses
- Installer.exe (PID: 2756)
Reads settings of System Certificates
- OfficeSuiteHDMeeting.exe (PID: 3304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
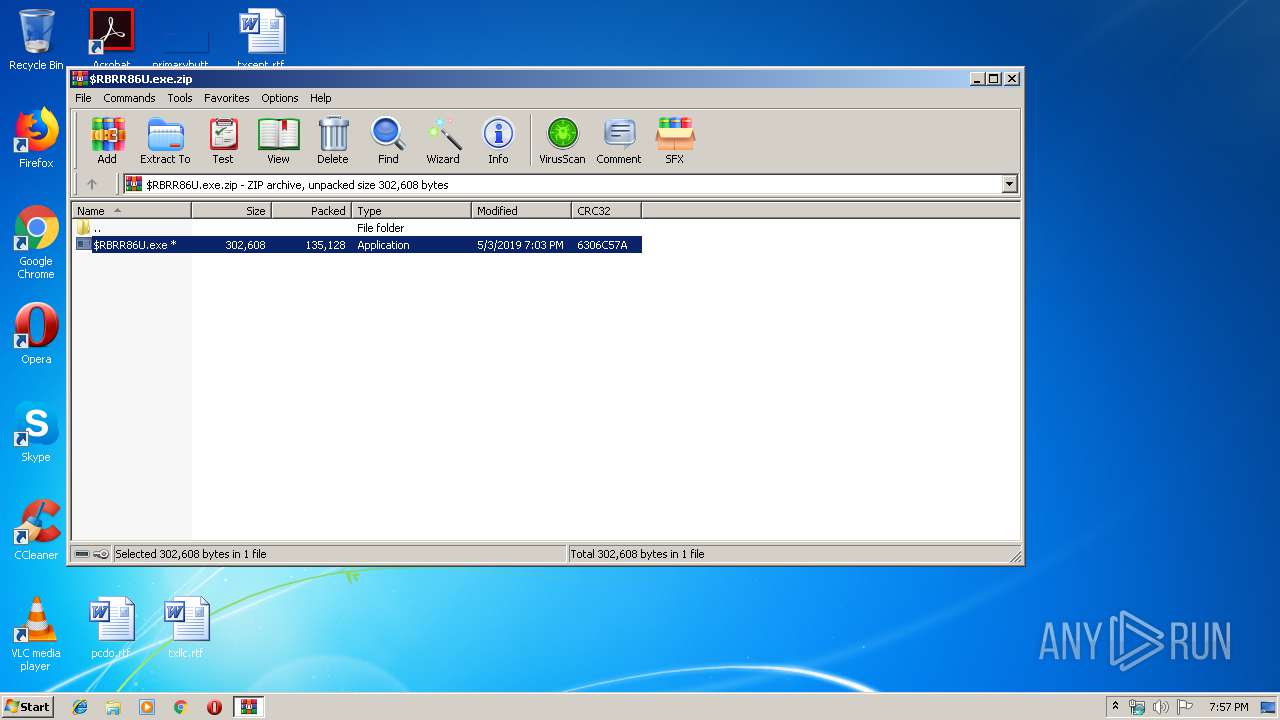
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:03 19:03:14 |
| ZipCRC: | 0x6306c57a |
| ZipCompressedSize: | 135128 |
| ZipUncompressedSize: | 302608 |
| ZipFileName: | $RBRR86U.exe |
Total processes
38
Monitored processes
5
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2596 | "C:\Users\admin\AppData\Roaming\BVNMeetings\bin\OfficeSuiteHDMeeting.exe" C:\Users\admin\AppData\Roaming\BVNMeetings\bin\OfficeSuiteHDMeeting.exe --url=zoombvn://win.launch?confid=dGlkPWpjeHltczNyUVJPSUc4ckdOS0N1c2c%3d&confno=1112094528&browser=firefox&zc=0&action=join& | C:\Users\admin\AppData\Roaming\BVNMeetings\bin\OfficeSuiteHDMeeting.exe | Installer.exe | ||||||||||||
User: admin Company: Broadview Networks, Inc. Integrity Level: MEDIUM Description: OfficeSuite HD Meeting Exit code: 0 Version: 4,1,15397,1225 Modules
| |||||||||||||||
| 2756 | "C:\Users\admin\AppData\Roaming\BVNMeetings\LDownload\Installer.exe" C:\Users\admin\AppData\Roaming\BVNMeetings\LDownload\Installer.exe --cid=dGlkPWpjeHltczNyUVJPSUc4ckdOS0N1c2c= --conf.no=1112094528 --zc=0 --pwd= --pk= --tk= --browser=firefox --sid= --stype= --token= --uid= --uname= --rtoken= --action=join | C:\Users\admin\AppData\Roaming\BVNMeetings\LDownload\Installer.exe | $RBRR86U.exe | ||||||||||||
User: admin Company: Broadview Networks, Inc. Integrity Level: MEDIUM Description: OfficeSuite HD Meeting Exit code: 0 Version: 4,1,15397,1225 Modules
| |||||||||||||||
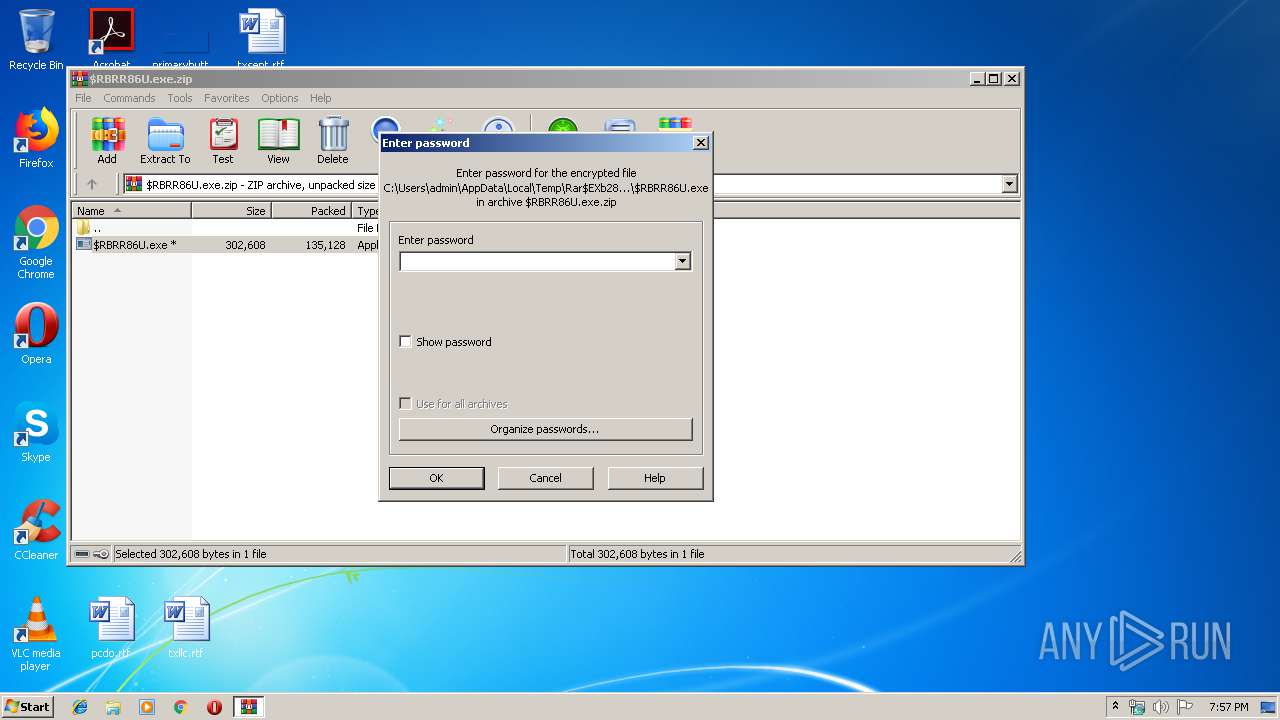
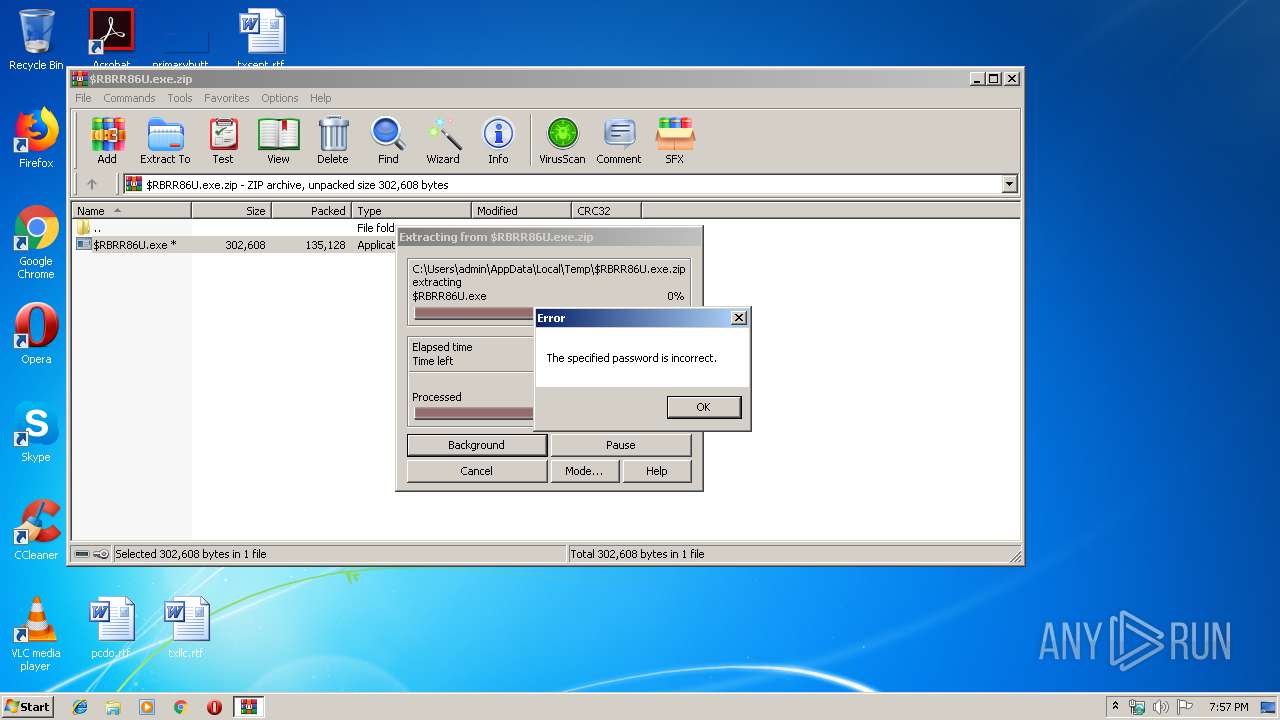
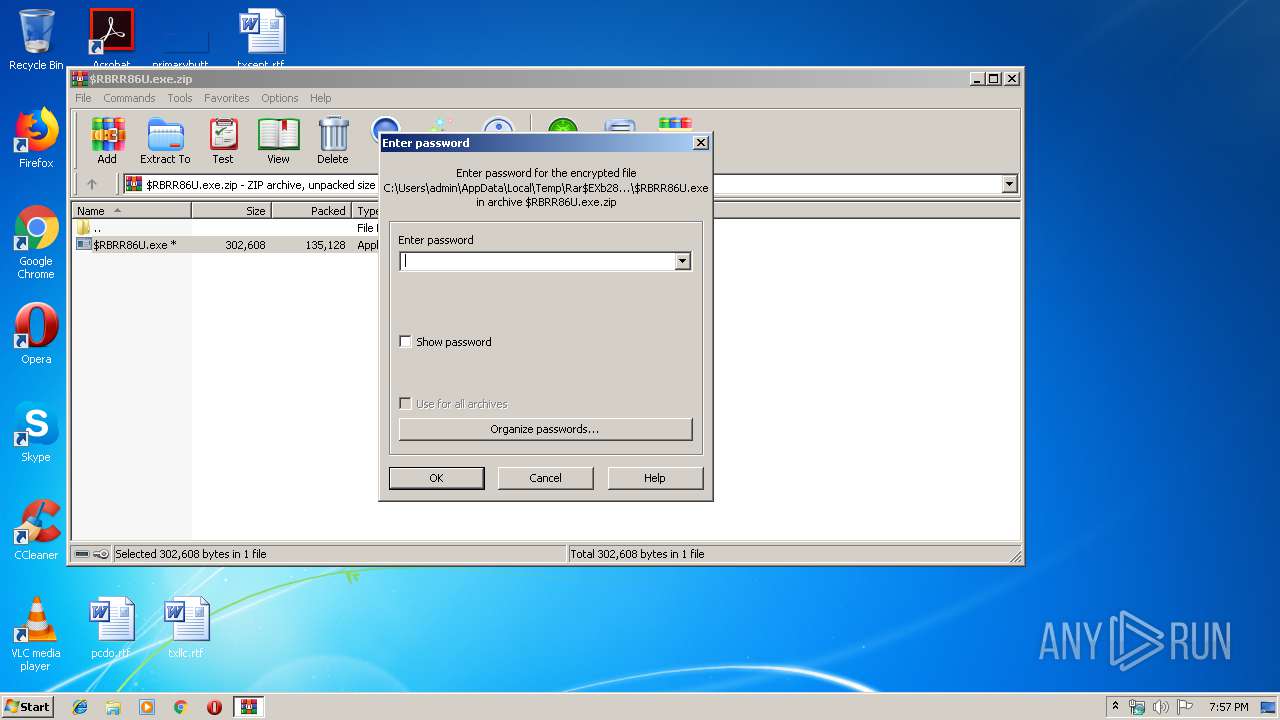
| 2828 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\$RBRR86U.exe.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3144 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2828.24156\$RBRR86U.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2828.24156\$RBRR86U.exe | WinRAR.exe | ||||||||||||
User: admin Company: Broadview Networks, Inc. Integrity Level: MEDIUM Description: OfficeSuite HD Meeting Exit code: 0 Version: 4,1,15397,1225 Modules
| |||||||||||||||
| 3304 | C:\Users\admin\AppData\Roaming\BVNMeetings\bin\OfficeSuiteHDMeeting.exe --action=join --runaszvideo=TRUE | C:\Users\admin\AppData\Roaming\BVNMeetings\bin\OfficeSuiteHDMeeting.exe | OfficeSuiteHDMeeting.exe | ||||||||||||
User: admin Company: Broadview Networks, Inc. Integrity Level: MEDIUM Description: OfficeSuite HD Meeting Exit code: 0 Version: 4,1,15397,1225 Modules
| |||||||||||||||
Total events
1 701
Read events
1 586
Write events
115
Delete events
0
Modification events
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\$RBRR86U.exe.zip | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2828) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
99
Suspicious files
13
Text files
14
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3144 | $RBRR86U.exe | C:\Users\admin\AppData\Local\Temp\Cab2E6D.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | $RBRR86U.exe | C:\Users\admin\AppData\Local\Temp\Tar2E6E.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | $RBRR86U.exe | C:\Users\admin\AppData\Local\Temp\Cab2E8E.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | $RBRR86U.exe | C:\Users\admin\AppData\Local\Temp\Tar2E8F.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | $RBRR86U.exe | C:\Users\admin\AppData\Local\Temp\Cab2F7B.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | $RBRR86U.exe | C:\Users\admin\AppData\Local\Temp\Tar2F8B.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | $RBRR86U.exe | C:\Users\admin\AppData\Roaming\BVNMeetings\LDownload\Zoom.msi | — | |
MD5:— | SHA256:— | |||
| 3144 | $RBRR86U.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\94308059B57B3142E455B38A6EB92015 | compressed | |
MD5:— | SHA256:— | |||
| 3144 | $RBRR86U.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94308059B57B3142E455B38A6EB92015 | binary | |
MD5:— | SHA256:— | |||
| 2756 | Installer.exe | C:\Users\admin\AppData\Roaming\BVNMeetings\install_src\CmmBrowserEngine.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
6
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3144 | $RBRR86U.exe | GET | 200 | 195.138.255.8:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | DE | compressed | 56.1 Kb | whitelisted |
3144 | $RBRR86U.exe | GET | 200 | 195.138.255.8:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/8CF427FD790C3AD166068DE81E57EFBB932272D4.crt | DE | der | 1.06 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3144 | $RBRR86U.exe | 34.233.223.210:443 | meeting.broadviewnet.com | Amazon.com, Inc. | US | unknown |
3144 | $RBRR86U.exe | 195.138.255.8:80 | www.download.windowsupdate.com | AS33891 Netzbetrieb GmbH | DE | suspicious |
2596 | OfficeSuiteHDMeeting.exe | 34.233.223.210:443 | meeting.broadviewnet.com | Amazon.com, Inc. | US | unknown |
3304 | OfficeSuiteHDMeeting.exe | 34.233.223.210:443 | meeting.broadviewnet.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
meeting.broadviewnet.com |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
Threats
Process | Message |
|---|---|
$RBRR86U.exe | WinMain start, lpCmdLine is: |
$RBRR86U.exe | WinMain start, parameter is: |
$RBRR86U.exe | CZpDownloadMgr::FindParam |
$RBRR86U.exe | CZpDownloadMgr::FindParam |
$RBRR86U.exe | package.name |
$RBRR86U.exe | BinFull.cab |
$RBRR86U.exe | CZpDownloadMgr::FindParam |
$RBRR86U.exe | package.version |
$RBRR86U.exe | latest |
$RBRR86U.exe | CZpDownloadMgr::FindParam |