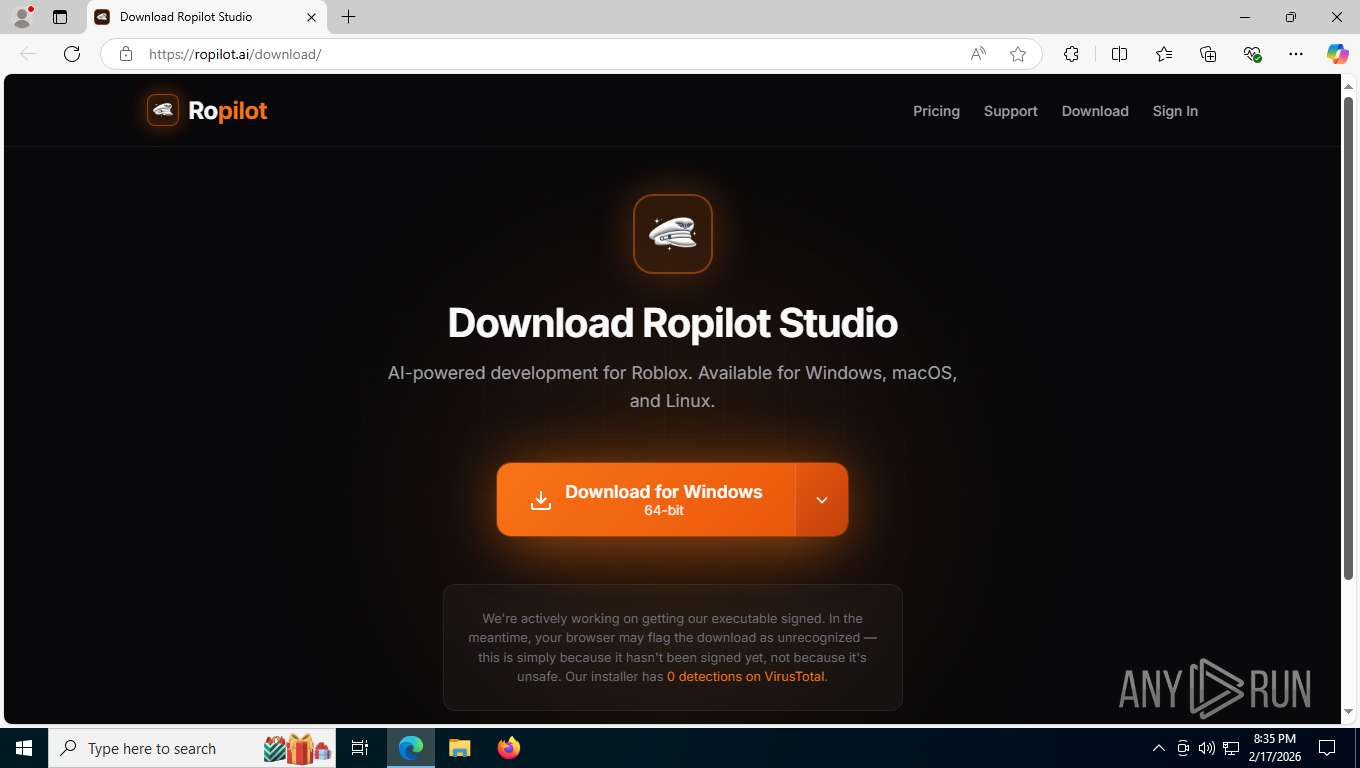
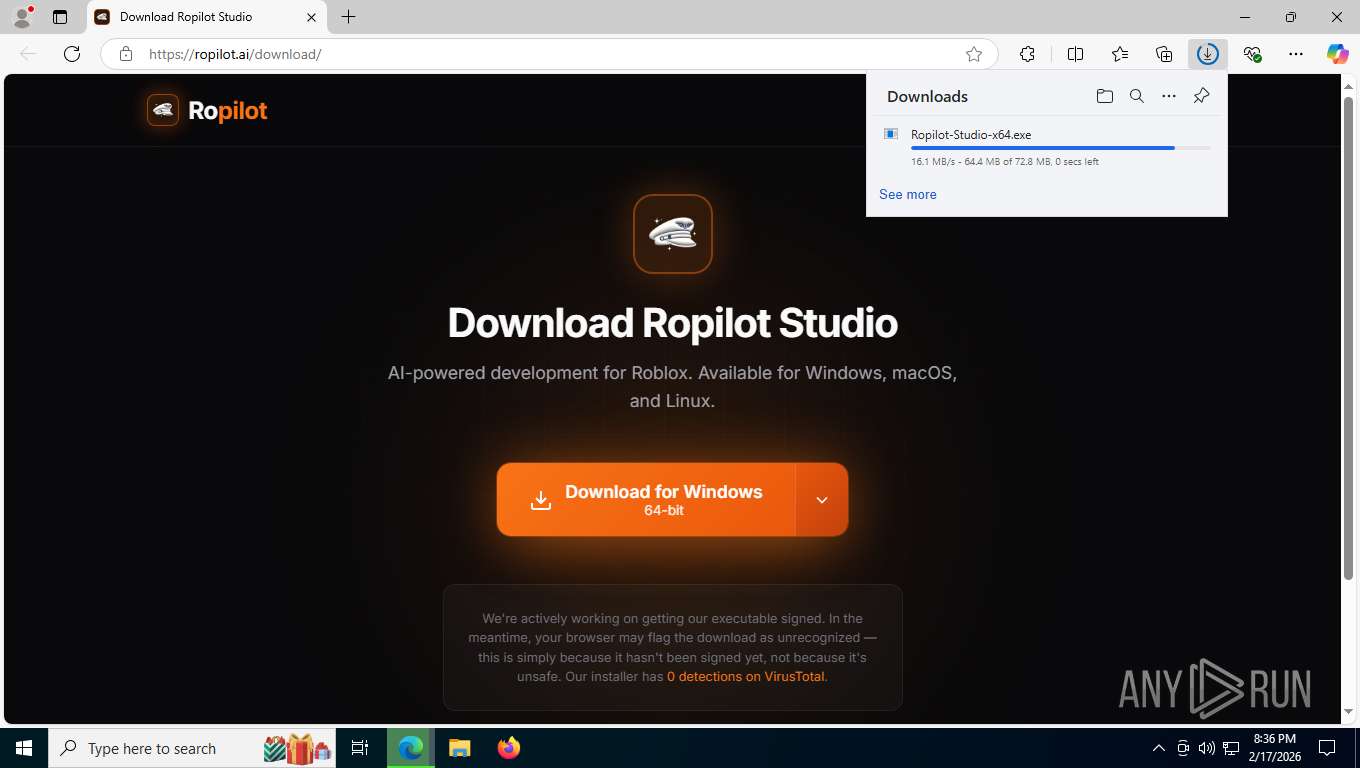
| URL: | https://ropilot.ai/downloads |
| Full analysis: | https://app.any.run/tasks/cf38557d-91bb-4f94-b6be-bb90c5123949 |
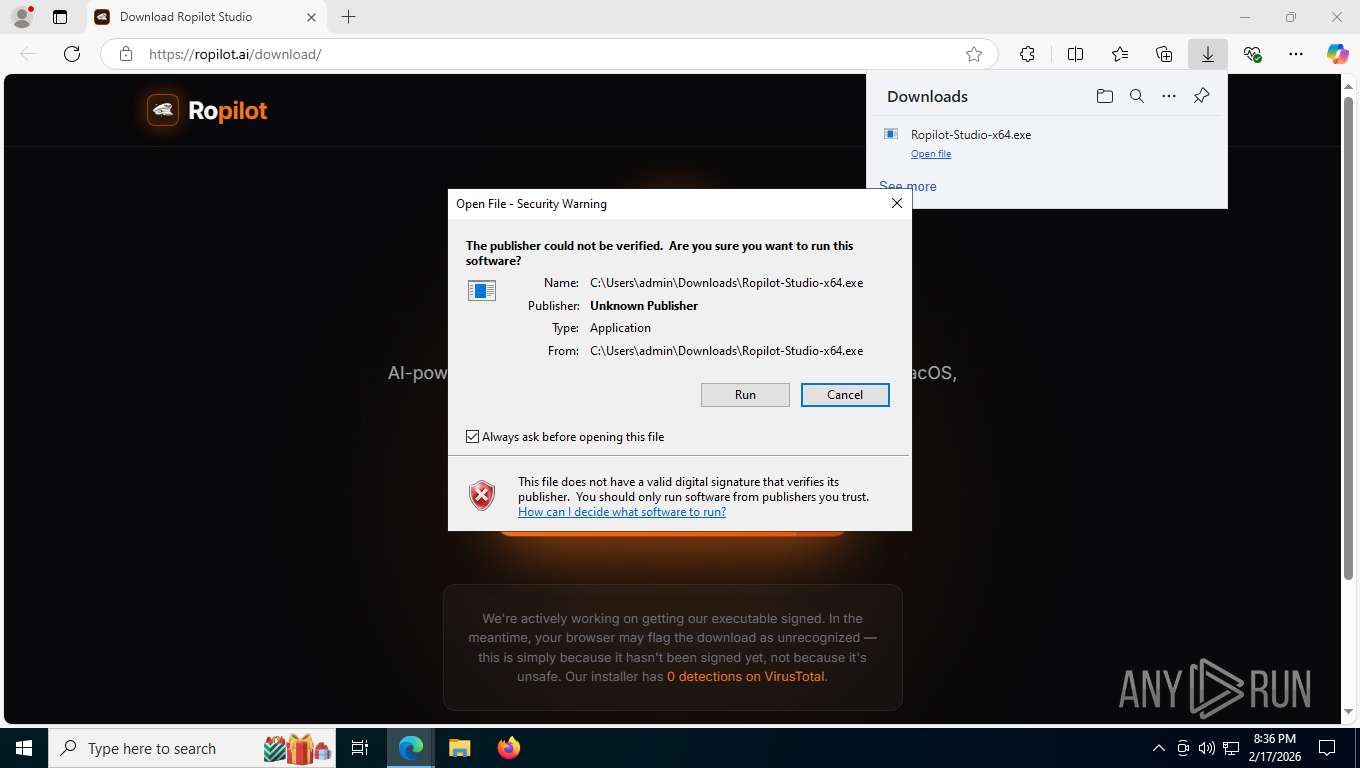
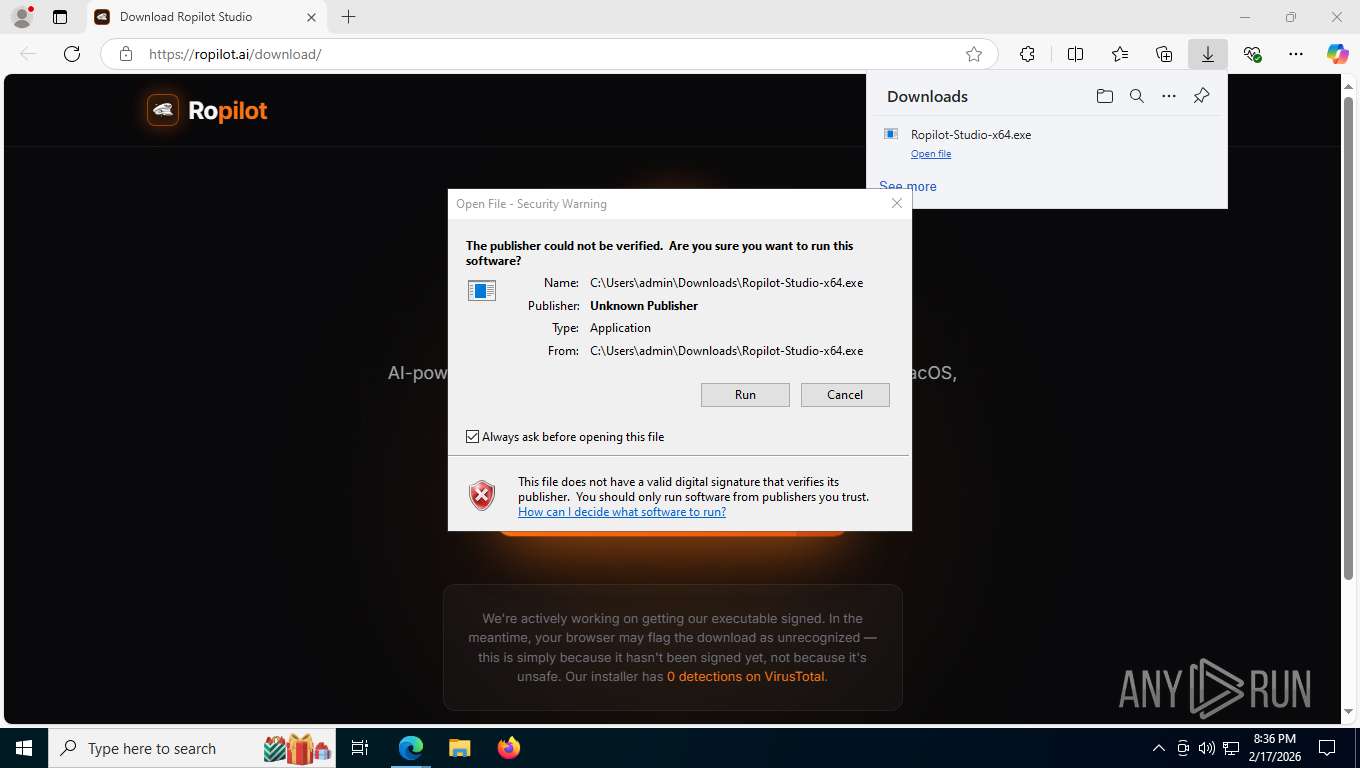
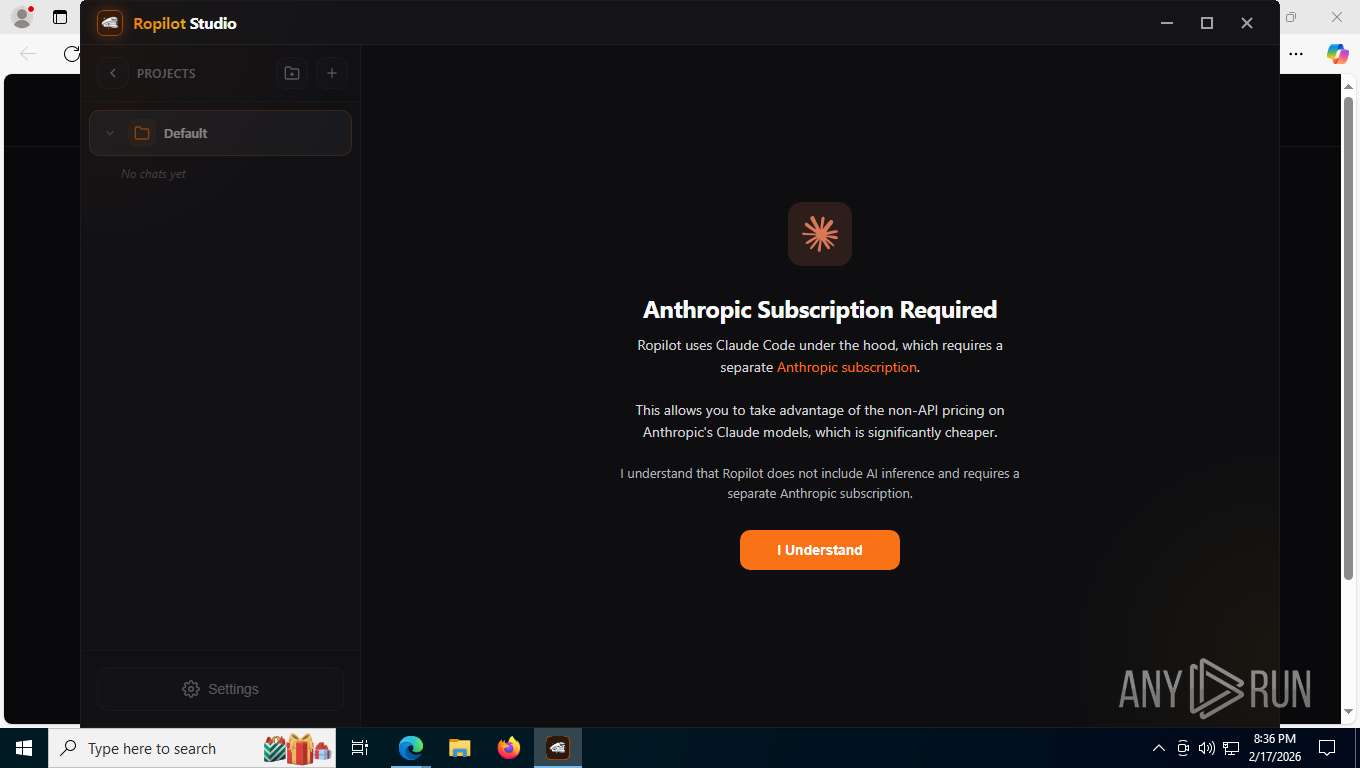
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2026, 01:35:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C3C446CAADAA47014EF5A042A22102CB |
| SHA1: | EA51AA9AAD1285D1DD8AF66BD00C5751F1285B6B |
| SHA256: | 0FEF709664B66D2BFF2D7379946DA5F11B7E5EEA2131ADD00034C41780B20752 |
| SSDEEP: | 3:N8MIKnSLJ4n:2bKX |
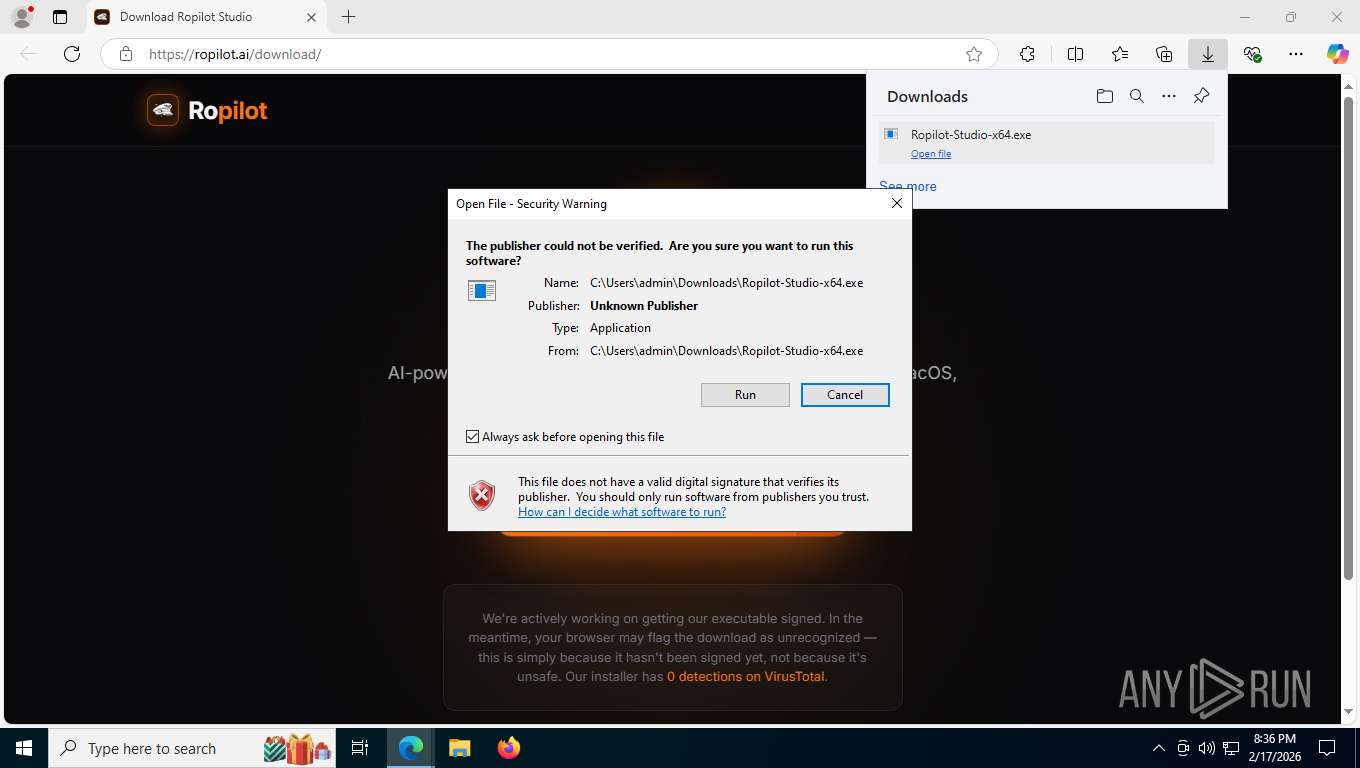
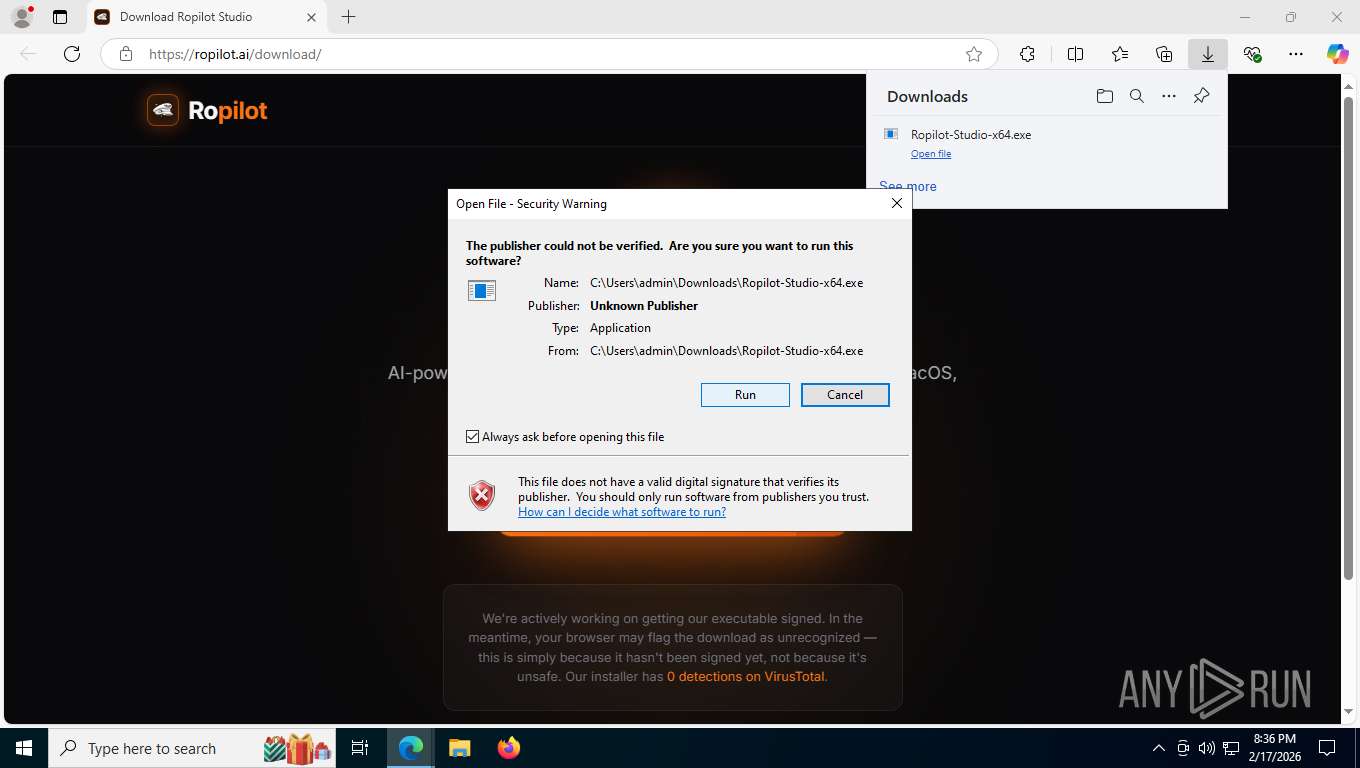
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 2148)
SUSPICIOUS
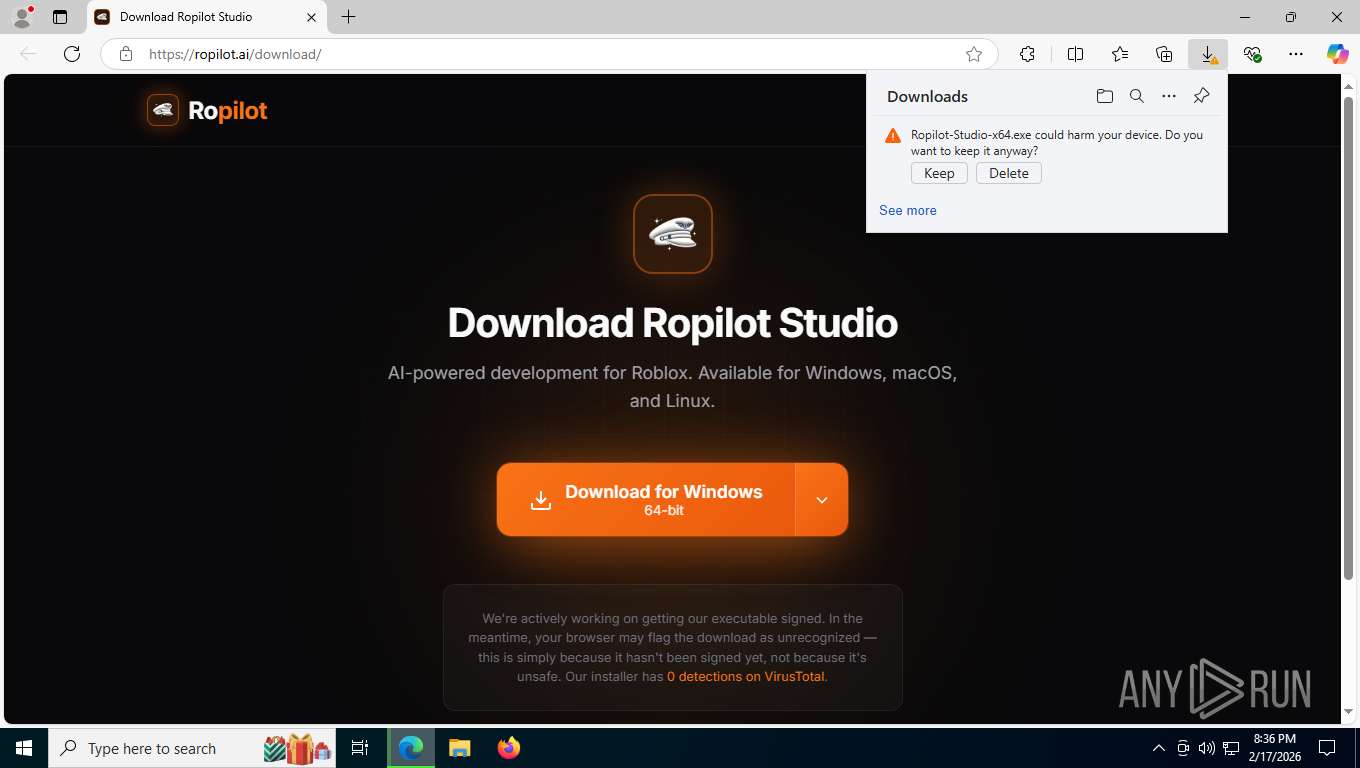
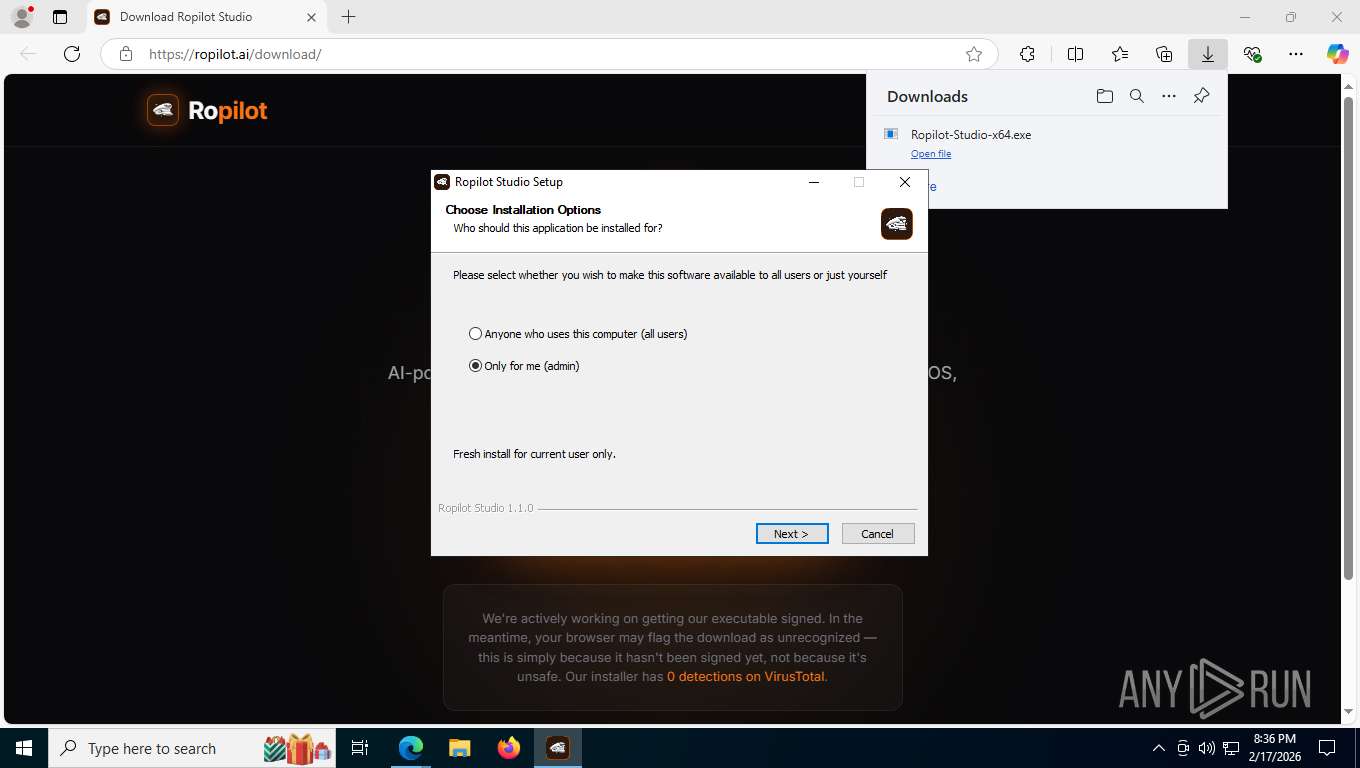
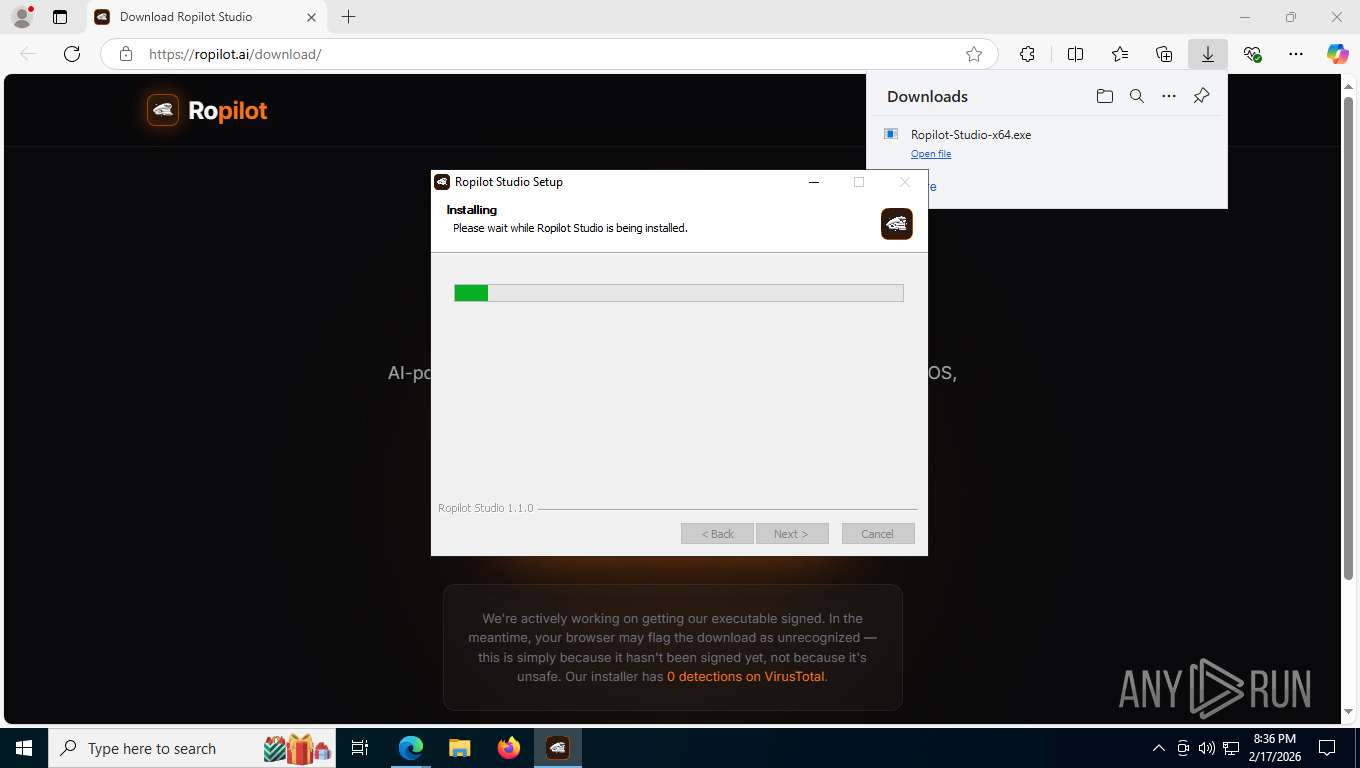
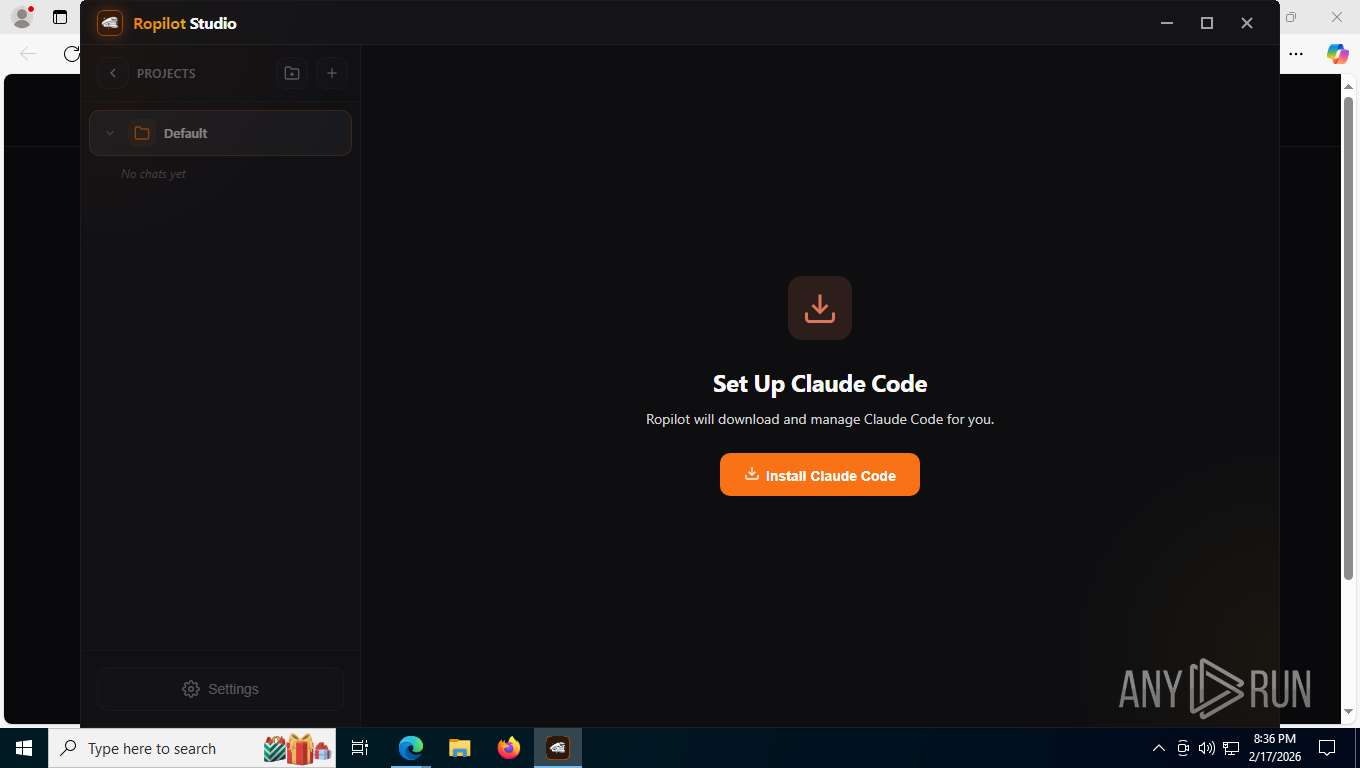
Malware-specific behavior (creating "System.dll" in Temp)
- Ropilot-Studio-x64.exe (PID: 4940)
The process creates files with name similar to system file names
- Ropilot-Studio-x64.exe (PID: 4940)
Application launched itself
- Ropilot Studio.exe (PID: 4788)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4140)
Starts CMD.EXE for commands execution
- Ropilot Studio.exe (PID: 4788)
The executable file from the user directory is run by the CMD process
- ropilot-infra.exe (PID: 8088)
INFO
Drops script file
- msedge.exe (PID: 2564)
- Ropilot Studio.exe (PID: 4788)
- ropilot-infra.exe (PID: 8088)
Reads Environment values
- identity_helper.exe (PID: 6904)
- Ropilot Studio.exe (PID: 4788)
Checks supported languages
- identity_helper.exe (PID: 6904)
- Ropilot-Studio-x64.exe (PID: 4940)
- Ropilot Studio.exe (PID: 4788)
- Ropilot Studio.exe (PID: 5520)
- Ropilot Studio.exe (PID: 8344)
- ropilot-infra.exe (PID: 8088)
- Ropilot Studio.exe (PID: 7724)
Application launched itself
- msedge.exe (PID: 2564)
Reads the computer name
- identity_helper.exe (PID: 6904)
- Ropilot-Studio-x64.exe (PID: 4940)
- Ropilot Studio.exe (PID: 4788)
- Ropilot Studio.exe (PID: 5520)
- Ropilot Studio.exe (PID: 8344)
Create files in a temporary directory
- Ropilot-Studio-x64.exe (PID: 4940)
- Ropilot Studio.exe (PID: 4788)
Creates files or folders in the user directory
- Ropilot-Studio-x64.exe (PID: 4940)
- Ropilot Studio.exe (PID: 4788)
- Ropilot Studio.exe (PID: 8344)
- ropilot-infra.exe (PID: 8088)
Reads security settings of Internet Explorer
- Ropilot-Studio-x64.exe (PID: 4940)
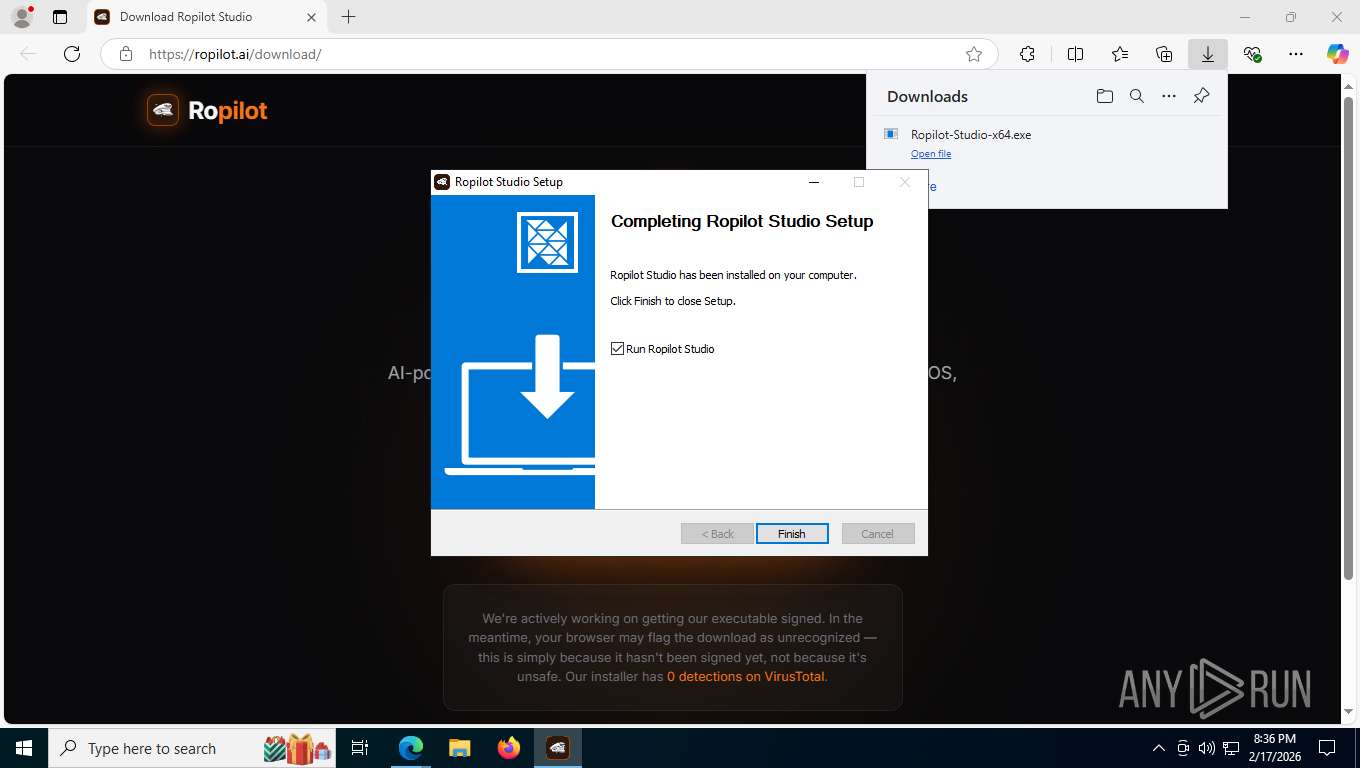
Creates a software uninstall entry
- Ropilot-Studio-x64.exe (PID: 4940)
Manual execution by a user
- Ropilot Studio.exe (PID: 4788)
Reads product name
- Ropilot Studio.exe (PID: 4788)
There is functionality for taking screenshot (YARA)
- Ropilot-Studio-x64.exe (PID: 4940)
Checks proxy server information
- Ropilot Studio.exe (PID: 4788)
- slui.exe (PID: 9088)
Reads the machine GUID from the registry
- Ropilot Studio.exe (PID: 4788)
Drops encrypted JS script (Microsoft Script Encoder)
- ropilot-infra.exe (PID: 8088)
Process checks computer location settings
- Ropilot Studio.exe (PID: 4788)
- Ropilot Studio.exe (PID: 7724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
200
Monitored processes
49
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6744,i,5021541392514038812,11568335970001963311,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6224 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1400 | where claude | C:\Windows\System32\where.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Where - Lists location of files Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | findstr :8765 | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1492 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6572,i,5021541392514038812,11568335970001963311,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5532 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1692 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2316,i,5021541392514038812,11568335970001963311,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2448 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5248,i,5021541392514038812,11568335970001963311,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6444 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2564 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --disable-features=HttpsUpgrades,HttpsFirstModeV2,HttpsOnlyMode,HttpsFirstBalancedMode --no-first-run --no-default-browser-check https://ropilot.ai/downloads | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
7 249
Read events
7 218
Write events
13
Delete events
18
Modification events
| (PID) Process: | (4940) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 139 | |||
| (PID) Process: | (4940) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Programs\Ropilot Studio | |||
| (PID) Process: | (4940) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | KeepShortcuts |
Value: true | |||
| (PID) Process: | (4940) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | ShortcutName |
Value: Ropilot Studio | |||
| (PID) Process: | (4940) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | DisplayName |
Value: Ropilot Studio 1.1.0 | |||
| (PID) Process: | (4940) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\Programs\Ropilot Studio\Uninstall Ropilot Studio.exe" /currentuser | |||
| (PID) Process: | (4940) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Users\admin\AppData\Local\Programs\Ropilot Studio\Uninstall Ropilot Studio.exe" /currentuser /S | |||
| (PID) Process: | (4940) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | DisplayVersion |
Value: 1.1.0 | |||
| (PID) Process: | (4940) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\Programs\Ropilot Studio\Ropilot Studio.exe,0 | |||
| (PID) Process: | (4940) Ropilot-Studio-x64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fbb35d3a-0e06-5ecb-aca6-b9f0beaf3d10 |
| Operation: | write | Name: | Publisher |
Value: Ropilot | |||
Executable files
0
Suspicious files
10
Text files
40
Unknown types
384
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e54b5.TMP | — | |
MD5:— | SHA256:— | |||
| 2564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e54b5.TMP | — | |
MD5:— | SHA256:— | |||
| 2564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e54b5.TMP | — | |
MD5:— | SHA256:— | |||
| 2564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e54d4.TMP | — | |
MD5:— | SHA256:— | |||
| 2564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e54d4.TMP | — | |
MD5:— | SHA256:— | |||
| 2564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
93
TCP/UDP connections
79
DNS requests
85
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2148 | msedge.exe | GET | 301 | 104.21.33.84:443 | https://ropilot.ai/downloads | US | — | — | unknown |
2148 | msedge.exe | GET | 308 | 104.21.33.84:443 | https://ropilot.ai/download | US | — | — | unknown |
2148 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:DAL0NiZieeE6BT96h-ZvEdgpUzUWT-sapRZH1p_B33U&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | binary | 99 b | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
2148 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | binary | 446 b | whitelisted |
2148 | msedge.exe | GET | 200 | 104.21.33.84:443 | https://ropilot.ai/ropilot.png | US | binary | 289 Kb | unknown |
2148 | msedge.exe | GET | 200 | 104.21.33.84:443 | https://ropilot.ai/js/navbar.js | US | binary | 4.89 Kb | unknown |
2148 | msedge.exe | GET | 200 | 104.21.33.84:443 | https://ropilot.ai/download/ | US | binary | 28.0 Kb | unknown |
2148 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | — | 25 b | whitelisted |
2148 | msedge.exe | GET | 200 | 142.251.208.170:443 | https://fonts.googleapis.com/css2?family=Inter:wght@400;500;600;700;800&display=swap | US | binary | 12.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8628 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7304 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.204.161:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2148 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ropilot.ai |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2148 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (.ropilot .ai) |
8628 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2148 | msedge.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
2148 | msedge.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
8344 | Ropilot Studio.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2148 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |